Security-Related Hardware Cost Optimization for CAN FD-Based Automotive Cyber-Physical Systems
Abstract
:1. Introduction
1.1. Background and Motivations
1.2. Contributions
2. Related Work
3. System Models and Key Assumptions
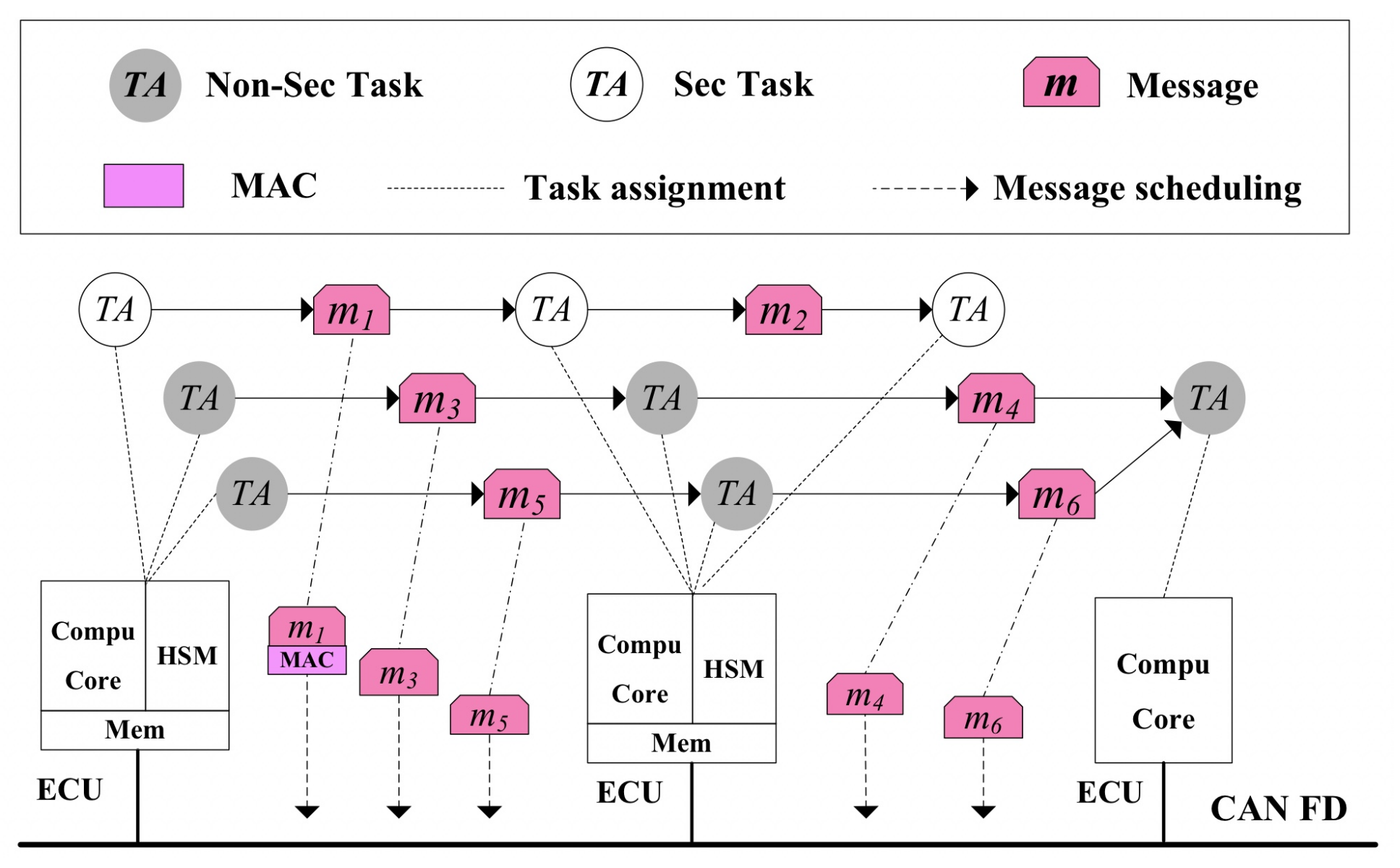
3.1. System Model
3.2. Task Model
3.3. Message Model
4. Hardware Cost Minimization Algorithms
4.1. Stepwise Decreasing Based Heuristic Algorithm
| Algorithm 1: Stepwise Decreasing-Based Heuristic Algorithm. |
| Input:Z, EN Output:EN 1: HN = EN, HN′ = EN; 2: flag = TRUE; 3: while (HN′ ≥ 1) ∧ (flag = true do; 4: Result = Task_Allocation (Z, EN, HN′); 5: PRavg = E2EWCRT_Analysis(Result); 6: Tini = 3 ∗ EN, Tter = 0.5, step_num = 5 ∗ TN ∗ MN, θ = 0.98; 7: T = Tini; 8: while T = > Tter do 9: for i = 1 to step_num do 10: Result′ = Heuristic_Task_Move (Result); 11: PRavg′ = E2EWCRT_Analysis (Result); 12: if (PRavg′ < PRavg) ∨ (exp((PRavg − PRavg′)/T > Rand (0, 1)) then 13: PRavg = PRavg′; 14: Result = Result′ 15: end if 16: if (PR < PD) then 17: flag = TRUE; 18: HN = HN′ 19: HN′ = HN′ − 1 20: break; 21: else 22: flag = FALSE; 23: end if 24: end for 25: T = T ∗ θ; 26: end while 27: end while |
4.2. Interference Balancing Based Heuristic Algorithm
| Algorithm 2: Interference Balancing-Based Heuristic Algorithm. |
| Input:Z, EN Output:HN 1: HN = EN, flag = TRUE; 2: Task_Sort (Z); 3: while (HN ≥ 1) ∧ (flag = TRUE) do 4: Interval = Min_Period (Z; 5: for i = 1 to TN do 6: Variance = W (1, TN); 7: if Qi == 1 then 8: for k = 1 to HN do 9: Result = Task_Allocation (Ti, Ek); 10: if Ti is scheduleable then 11: Variance (1, k) = Variance_Analysis (Interval); 12: end if 13: end for 14: else 15: for k = 1 to EN do 16: Result = Task_Allocation (Ti, Ek); 17: if Ti is schedulable then 18: Variance (1, k) = Variance_Analysis (Interval); 19: end if 20: end for 21: end if 22: (Min_Variance, k) = min (Variance); 23: if Min_Variance < W then 24: flag = TRUE; 25: Allocate Ti to the Ek; 26: Interval = Pi; 27: else 28: flag = false; 29: break; 30: end if 31: end for 32: if system is schedulable then 33: HN = HN-1; 34: else 35: break; 36: end if 37: end while |
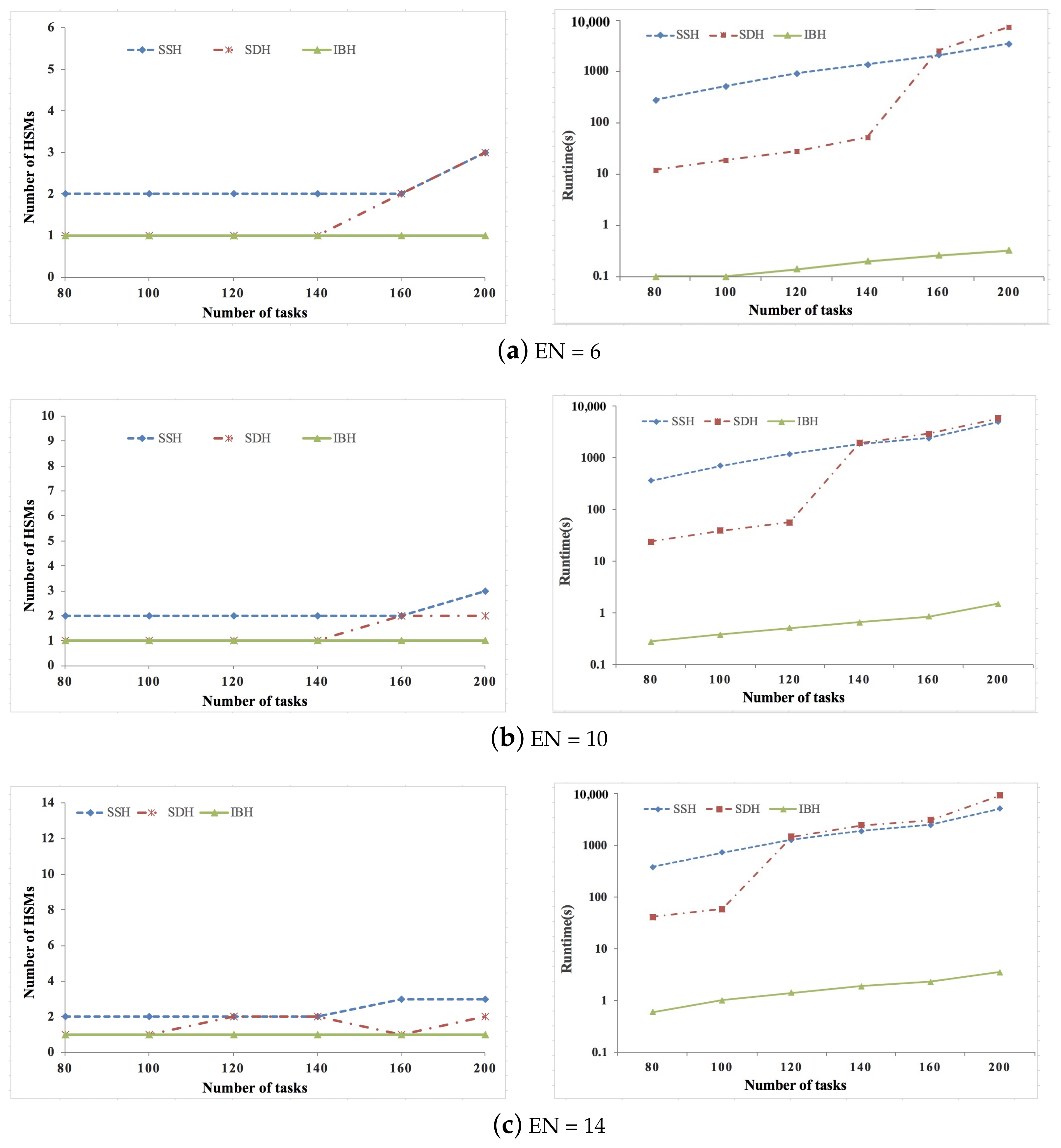
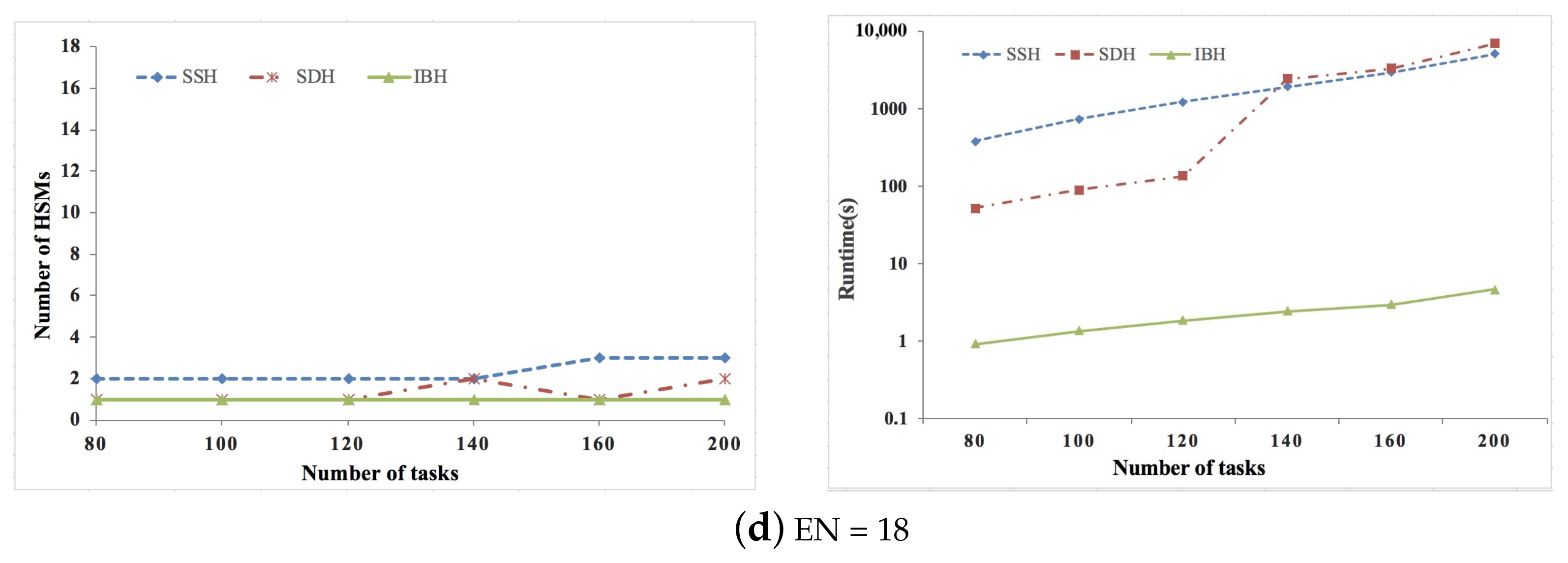
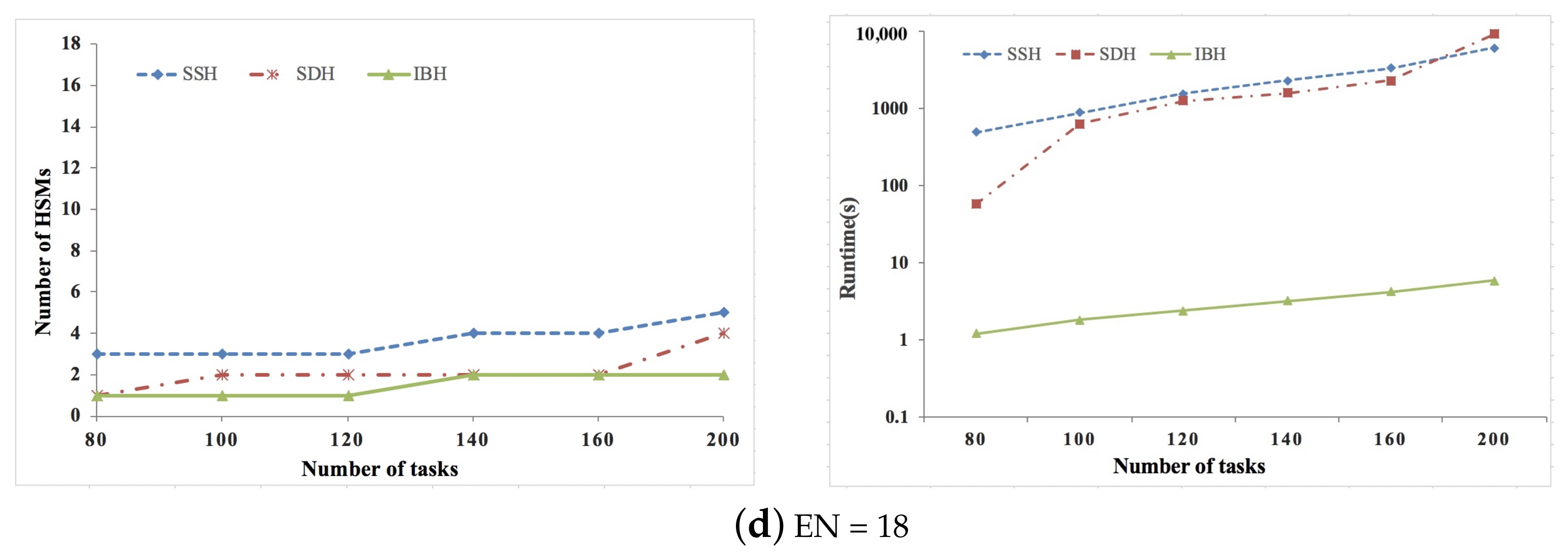
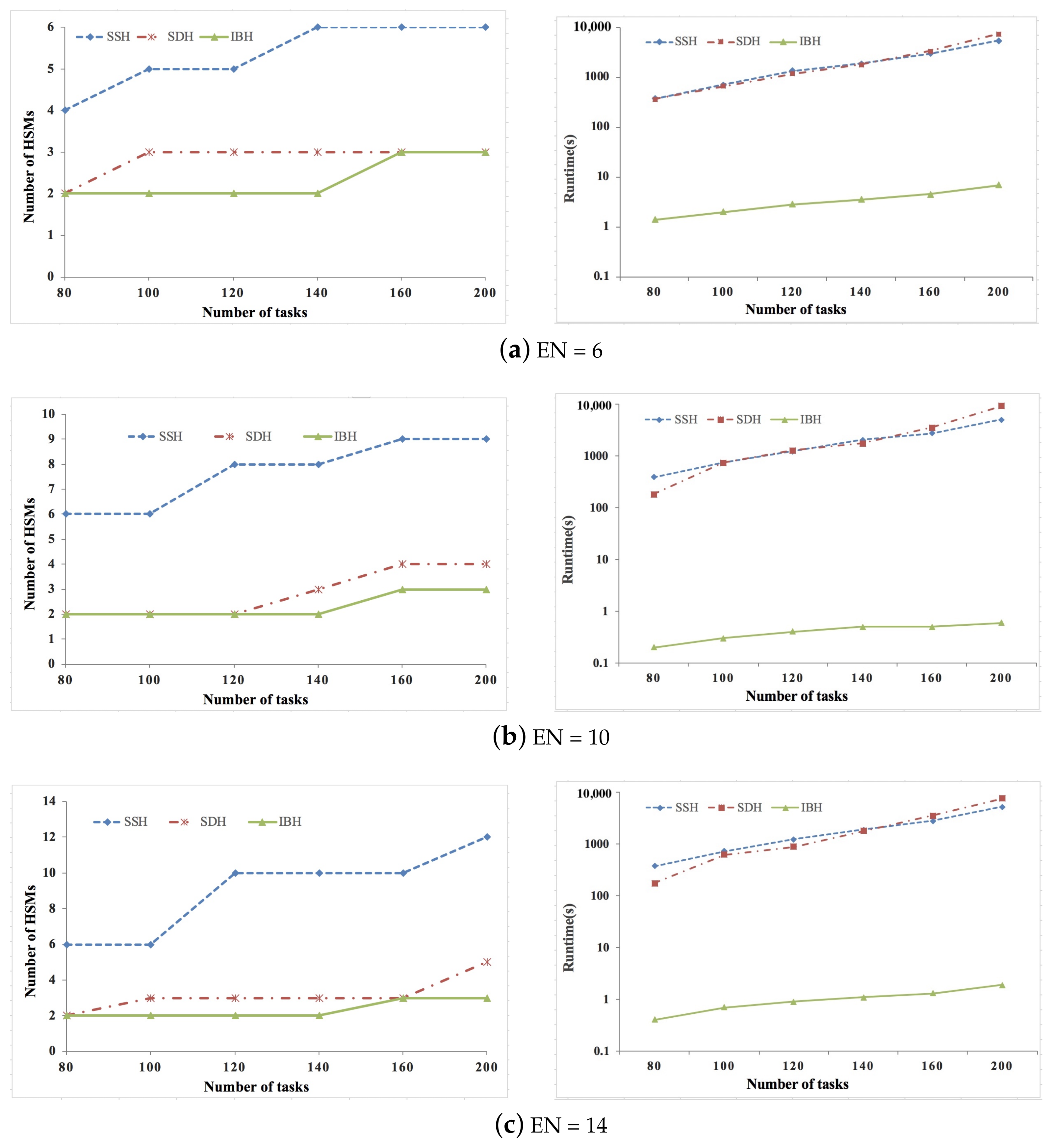
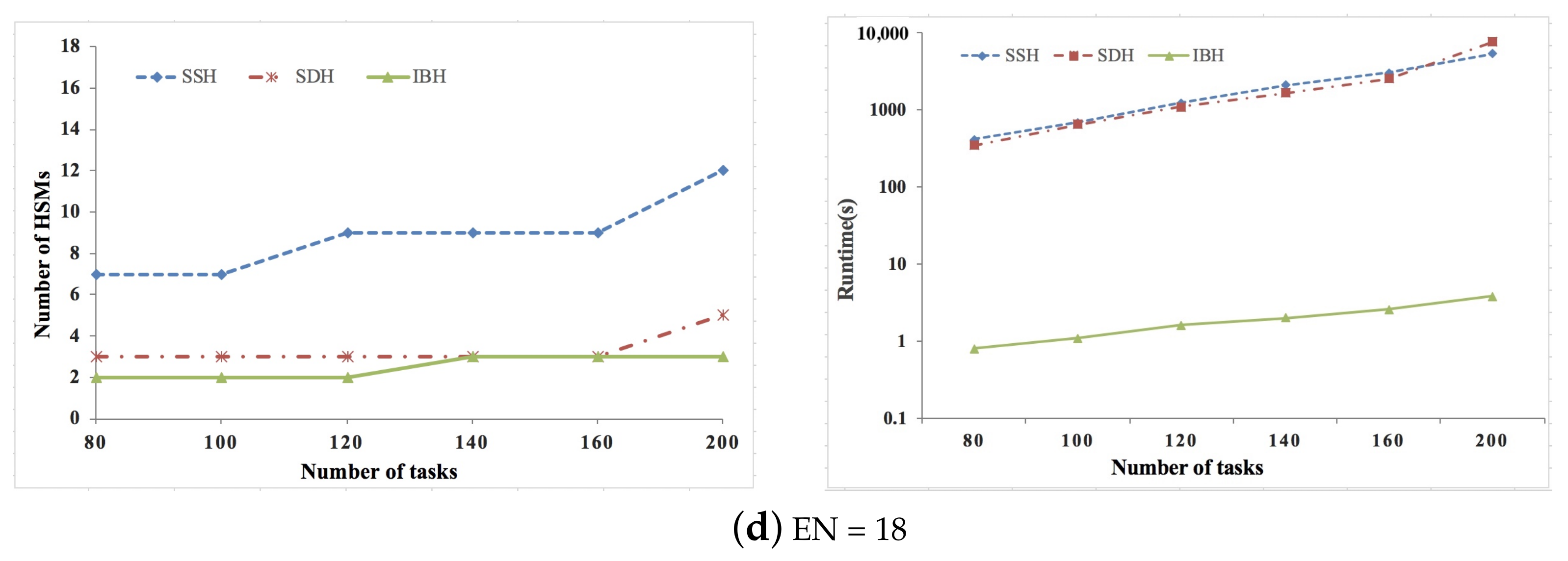
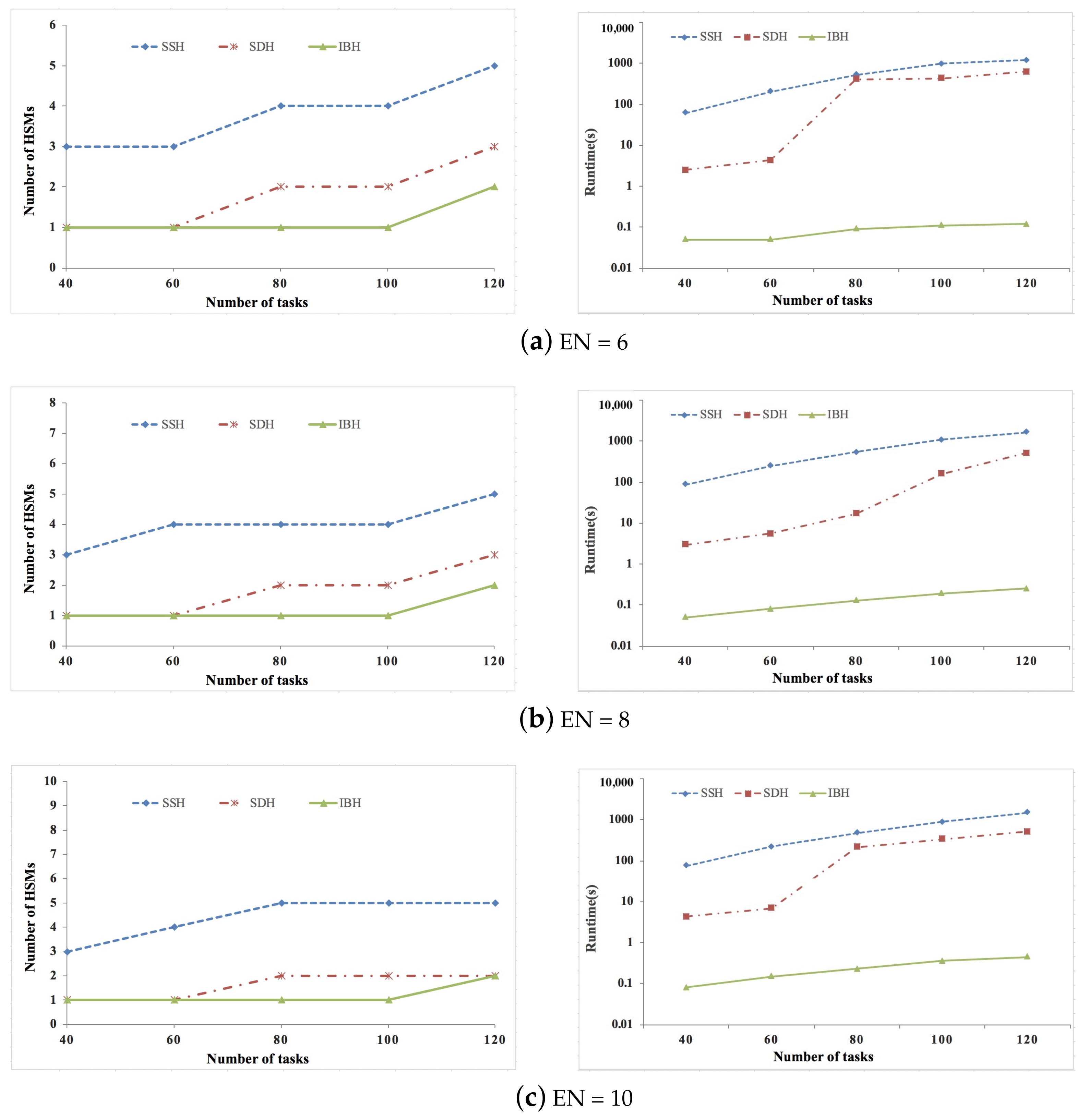
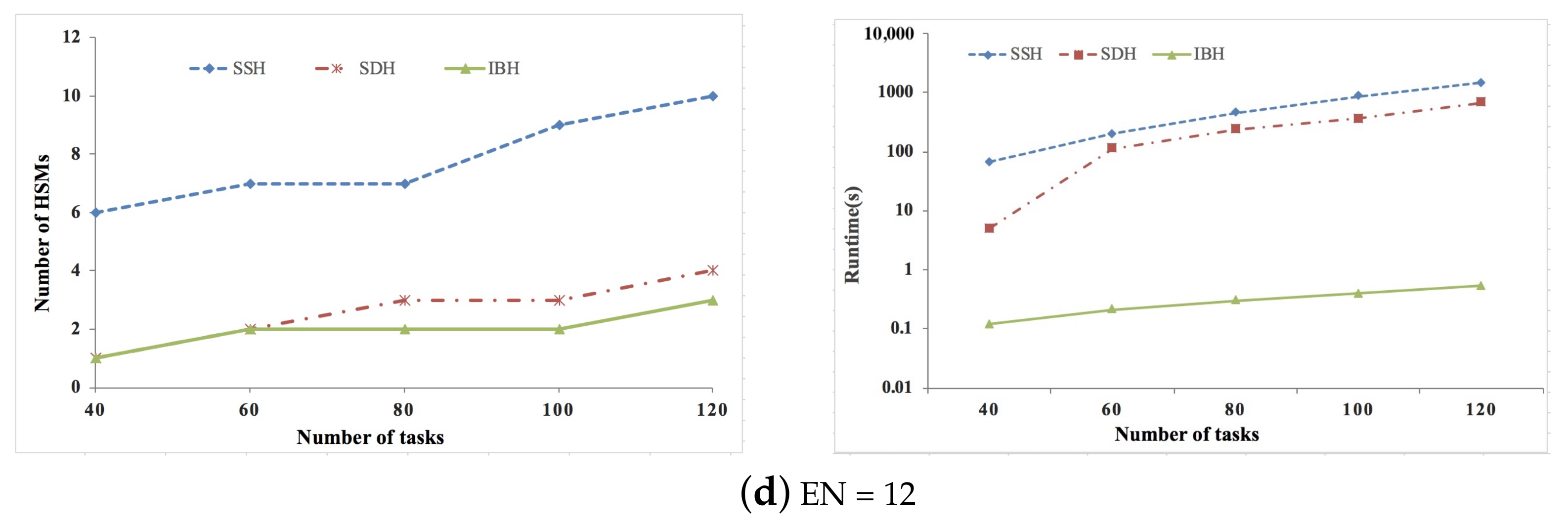
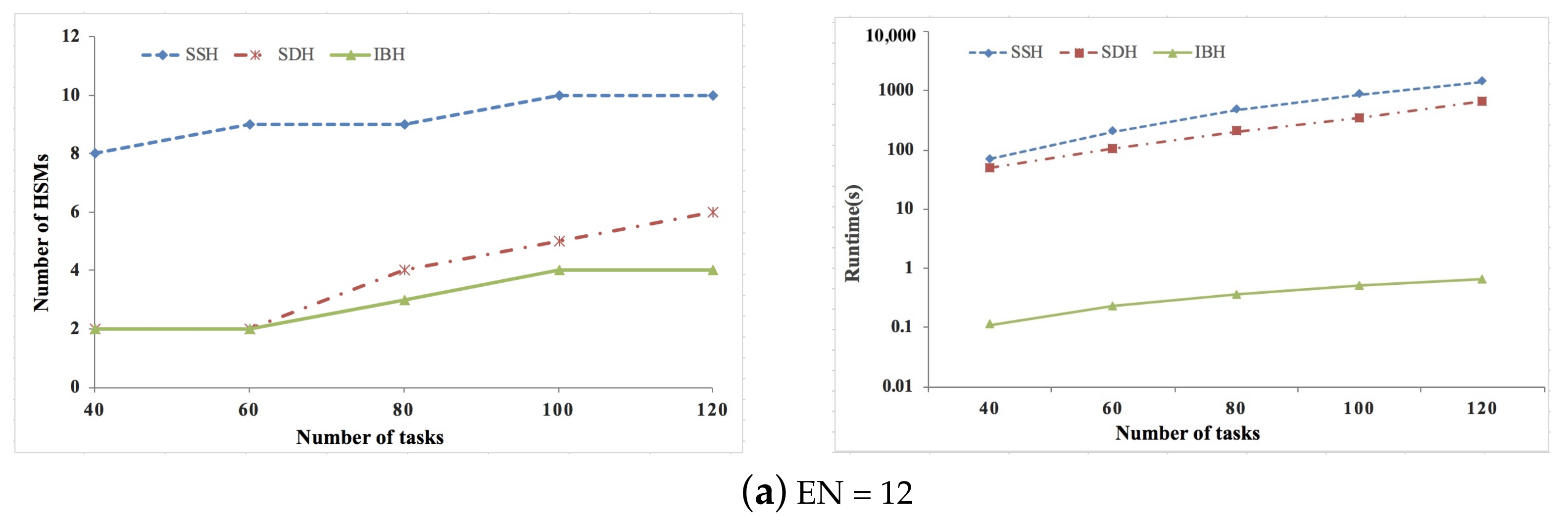
5. Experiment Results
6. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Koscher, K.; Czeskis, A.; Roesner, F.; Patel, S.; Kohno, T.; Checkoway, S.; McCoy, D.; Kantor, B.; Anderson, D.; Shacham, H.; et al. Experimental Security Analysis of a Modern Automobile. In Proceedings of the 2010 IEEE Symposium on Security and Privacy, Oakland, CA, USA, 16–19 May 2010; pp. 447–462. [Google Scholar]
- Hartwich, F. CAN with Flexible Data-Rate. In Proceedings of the International CAN Conference, Hombach Castle, Germany, 10–11 October 2012; p. 14. [Google Scholar]
- With “Recall” Fiat Chrysler Makes Its Car Hack Worse. Available online: www.networkworld.com/article/2953836/security/with-recall-fiat-chrysler-makes-its-car-hack-worse (accessed on 30 November 2016).
- Xie, Y.; Liu, L.J.; Li, R.F.; Hu, J.Q.; Han, Y.; Peng, X. Security-aware signal packing algorithm for CAN-based automotive cyber-physical systems. IEEE/CAA J. Autom. Sin. 2015, 2, 248–257. [Google Scholar]
- Xie, Y.; Zeng, G.; Kurachi, R.; Takada, H.; Xie, G.Q. Security/Timing-aware design space exploration of CAN FD for automotive cyber-physical systems. IEEE Trans. Ind. Inform. 2019, 15, 1094–1104. [Google Scholar] [CrossRef]
- AUTOSAR Specification of Module Secure Onboard Communication, Version 4.4.0. Available online: https://www.autosar.org/fileadmin/Releases_TEMP/Classic_Platform_4.4.0/Communication.zip (accessed on 20 November 2020).
- Munir, A.; Koushanfar, F. Design and analysis of secure and dependable automotive CPS: A steer-by-wire case study. IEEE Trans. Depend. Secur. Comput. 2018, 17, 813–827. [Google Scholar] [CrossRef] [Green Version]
- Xie, G.Q.; Li, R.F.; Hu, S.Y. Security-aware obfuscated priority assignment for CAN FD messages in real-time parallel automotive applications. IEEE Trans. CAD Integr. Circuits Syst. 2020, 39, 4413–4425. [Google Scholar] [CrossRef]
- Xie, Y.; Zhou, Y.; Xu, J.; Zhou, J.; Chen, X.; Xiao, F. Cybersecurity protection on in-vehicle networks for distributed automotive cyber-physical systems: State of the art and future challenges. Softw. Pract. Exp. 2021, 51, 2108–2127. [Google Scholar] [CrossRef]
- Stumpf, F.; Pohl, C.; Hoettges, D.; Klein, T. Introducing HSM-Based Secure On-Board Communication in Vehicles-Challenges and Lessons Learned. In Proceedings of the Escar Europe, Stuttgart, Germany, 19–20 November 2019; pp. 1–4. [Google Scholar]
- Wu, Z.; Zhao, J.; Zhu, Y.; Li, Q. Research on Vehicle Cybersecurity Based on Dedicated Security Hardware and ECDH Algorithm; SAE Technical Paper, No. 2017-01-2005; SAE International: Warrendale, PA, USA, 2017. [Google Scholar]
- Chip Price. Available online: https://www.arrow.com (accessed on 23 May 2020).
- Shimizu, N. Fujitsu Develops Platforms for Toyota’s, Honda’s Cryptographic Technologies. 2018. Available online: http://tech.nikkeibp.co.jp/atcl/nxt/column/18/00213/00003/ (accessed on 12 July 2019).
- Xie, G.; Chen, Y.; Liu, Y.; Wei, Y.; Li, R.; Li, K. Resource consumption cost minimization of reliable parallel applications on heterogeneous embedded systems. IEEE Trans. Ind. Inform. 2017, 13, 1629–1640. [Google Scholar] [CrossRef]
- Gan, J.; Pop, P.; Madsen, J. Tradeoff Analysis for Dependable Real-Time Embedded Systems during the Early Design Phases. Ph.D. Thesis, Technical University of Denmark, Department of Informatics and Mathematical Modeling, Lyngby, Denmark, 2014. [Google Scholar]
- Tamas-Selicean, D.; Pop, P. Design optimization of mixed-criticality real-time embedded systems. ACM Trans. Embed. Comput. Syst. 2015, 14, 50. [Google Scholar] [CrossRef]
- Xie, G.; Wu, W.; Zeng, G.; Li, R.; Hu, S. Risk Assessment and Development Cost Optimization in Software Defined Vehicles. IEEE Trans. Intell. Transp. Syst. 2021, 22, 3675–3686. [Google Scholar] [CrossRef]
- Xie, G.; Chen, Y.; Li, R.; Li, K. Hardware cost design optimization for functional safety-critical parallel applications on heterogeneous distributed embedded systems. IEEE Trans. Ind. Inform. 2018, 14, 2418–2431. [Google Scholar] [CrossRef]
- Zou, W.; Li, R.; Wu, W.; Zeng, L. Hardware Cost and Energy Consumption Optimization for Safety-Critical Applications on Heterogeneous Distributed Embedded Systems. In Proceedings of the 24th IEEE International Conference on Parallel and Distributed Systems, Singapore, 11–13 December 2018; pp. 527–536. [Google Scholar]
- Xie, G.; Ma, W.; Peng, H.; Li, R.; Li, K. Price performance-driven hardware cost optimization under functional safety requirement in large-scale heterogeneous distributed embedded systems. IEEE Trans. Ind. Electron. 2021, 68, 4485–4497. [Google Scholar] [CrossRef]
- Salimi, M.; Majd, A.; Loni, M.; Seceleanu, T.; Seceleanu, C.; Sirjani, M.; Daneshtalab, M.; Troubitsyna, E. Multi-Objective Optimization of Real-Time Task Scheduling Problem for Distributed Environments. In Proceedings of the 6th Conference on the Engineering of Computer Based Systems, Bucharest, Romania, 2–3 September 2019; pp. 1–9. [Google Scholar]
- Niknam, S.; Wang, P.; Stefanov, T.P. Resource optimization for real-time streaming applications using task replication. IEEE Trans. Comput. Aided Des. Integr. Circuits Syst. 2018, 37, 2755–2767. [Google Scholar] [CrossRef]
- Cho, H.; Kim, C.; Sun, J.; Easwaran, A.; Park, J.-D.; Choi, B.-C. Scheduling parallel real-time tasks on the minimum number of processors. IEEE Trans. Parallel Distrib. Syst. 2020, 31, 171–186. [Google Scholar] [CrossRef]
- Gu, Z.; Han, G.; Zeng, H.; Zhao, Q. Security-aware mapping and scheduling with hardware co-processors for FlexRay-based distributed embedded systems. IEEE Trans. Parallel Distrib. Syst. 2016, 27, 3044–3057. [Google Scholar] [CrossRef]
- Saidi, S.; Steinhorst, S.; Hamann, A.; Ziegenbein, D.; Wolf, M. Future Automotive Systems Design: Research Challenges and Opportunities. In Proceedings of the International Conference on Hardware/Software Codesign and System Synthesis, Torino, Italy, 30 September–5 October 2018; pp. 1–7. [Google Scholar]
- Corbett, C.; Brunner, M.; Schmidt, K.; Schneider, R.; Bannebaum, U. Leveraging Hardware Security to Secure Connected Vehicles; SAE Technical Paper, 2018-01-0012; SAE International: Warrendale, PA, USA, 2018. [Google Scholar]
- Wyglinski, A.M.; Huang, X.; Padir, T.; Lai, L.; Eisenbarth, T.R.; Venkatasubramanian, K. Security of autonomous systems employing embedded computing and sensors. IEEE Micro 2013, 33, 80–86. [Google Scholar] [CrossRef]
- Nilsson, D.K.; Phung, P.H.; Larson, U.E. Vehicle ECU Classification Based on Safety-Security Characteristics. In Proceedings of the IET Road Transport Information and Control Conference, Manchester, UK, 20–22 May 2008; pp. 1–7. [Google Scholar]
- Joshi, P.; Zeng, H.B.; Bordoloi, U.D.; Samii, S.; Ravi, S.S.; Shukla, S.K. The Multi-Domain Frame Packing Problem for CAN-FD. In Proceedings of the Euromicro Conference on Real-Time Systems, Dubrovnik, Croatia, 27–30 June 2017; pp. 12:1–12:22. [Google Scholar]
- Xie, Y.; Zeng, G.; Kurachi, R.; Peng, X.; Xie, G.Q.; Hiroaki, T. Balancing bandwidth utilization and interrupts: Two heuristic algorithms for the optimized design of automotive CPS. IEEE Trans. Ind. Inform. 2020, 16, 2382–2392. [Google Scholar] [CrossRef]
- Xie, Y.; Zeng, G.; Kurachi, R.; Peng, X.; Xie, G.Q.; Hiroaki, T. Optimizing Extensibility of CAN FD for Automotive Cyber-Physical Systems. IEEE Trans. Intell. Transp. Syst. 2021. [Google Scholar] [CrossRef]
- Natale, M.D.; Meschi, A. Scheduling messages with earliest deadline techniques. J.-Real-Time Syst. 2001, 20, 255–285. [Google Scholar] [CrossRef]
- Davis, R.I.; Burns, A.; Bril, R.J.; Lukkien, J.J. Controller Area Network(CAN) schedulability analysis: Refuted, revisited and revised. J. -Real-Time Syst. 2007, 35, 239–272. [Google Scholar] [CrossRef] [Green Version]
- Davare, A.; Zhu, Q.; Natale, M.D.; Pinello, C.; Kanajan, S.; Sangiovanni-Vincentelli, A.L. Period Optimization for Hard Real-time Distributed Automotive Systems. In Proceedings of the 44th Design Automation Conference, San Diego, CA, USA, 4–8 June 2007; pp. 278–283. [Google Scholar]
- AUTOSAR Specification of Crypto Service Manager, Version 4.4.0. Available online: https://www.autosar.org/fileadmin/Releases_TEMP/Classic_Platform_4.4.0/Crypto.zip (accessed on 20 November 2020).
- McLean, S.D.; Craciunas, S.S.; Hansen, E.A.J.; Pop, P. Mapping and Scheduling Automotive Applications on ADAS Platforms Using Metaheuristics. In Proceedings of the IEEE International Conference on Emerging Technologies and Factory Automation, Vienna, Austria, 8–11 September 2020; pp. 329–336. [Google Scholar]
- Task Graph Generator. Available online: https://sourceforge.net/projects/taskgraphgen/ (accessed on 1 August 2021).
- Kramer, S.; Ziegenbein, D.; Hamann, A. Real World Automotive Bench-Mark for Free. In Proceedings of the 6th International Workshop on Analysis Tools and Methodologies for Embedded and Real-time Systems (WATERS), Lund, Sweden, 7 July 2015. [Google Scholar]



Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Xie, Y.; Guo, Y.; Yang, S.; Zhou, J.; Chen, X. Security-Related Hardware Cost Optimization for CAN FD-Based Automotive Cyber-Physical Systems. Sensors 2021, 21, 6807. https://doi.org/10.3390/s21206807
Xie Y, Guo Y, Yang S, Zhou J, Chen X. Security-Related Hardware Cost Optimization for CAN FD-Based Automotive Cyber-Physical Systems. Sensors. 2021; 21(20):6807. https://doi.org/10.3390/s21206807
Chicago/Turabian StyleXie, Yong, Yili Guo, Sheng Yang, Jian Zhou, and Xiaobai Chen. 2021. "Security-Related Hardware Cost Optimization for CAN FD-Based Automotive Cyber-Physical Systems" Sensors 21, no. 20: 6807. https://doi.org/10.3390/s21206807
APA StyleXie, Y., Guo, Y., Yang, S., Zhou, J., & Chen, X. (2021). Security-Related Hardware Cost Optimization for CAN FD-Based Automotive Cyber-Physical Systems. Sensors, 21(20), 6807. https://doi.org/10.3390/s21206807





