S6AE: Securing 6LoWPAN Using Authenticated Encryption Scheme
Abstract
1. Introduction
1.1. Related Work
1.2. Contribution and Paper Organization
- The proposed scheme provides end-to-end security, mobility support, and header integrity.
- Informal security analysis and formal validations using Burrows–Abadi–Needham (BAN) logic and Automated Validation of Internet Security Protocols and Applications (AVISPA) illustrate that S6AE secures 6LoWPANs against various malicious attacks.
- Comparative analysis with eminent existing schemes demonstrates that S6AE is more efficient and provides better security features with less computational and communication overheads, memory utilization, and energy consumption.
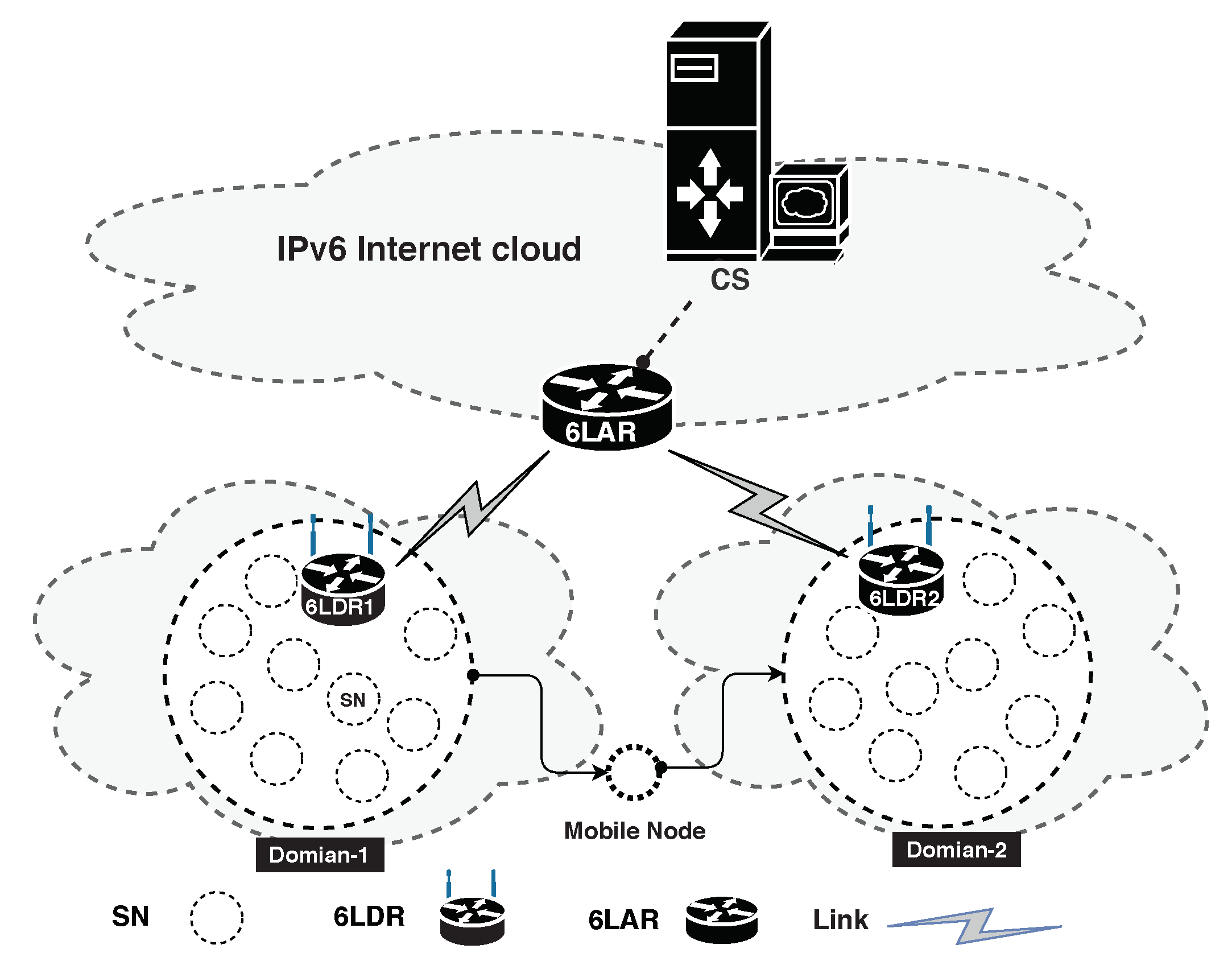
2. System Models
2.1. Network Model and Security Assumptions
2.2. Threat Model
2.3. Preliminaries
2.3.1. Hash Function
- The output of the hash function with two different inputs, n and m, can never be the same, i.e., .
- It is not possible to compute the input, z, from the output of a hash function, , i.e., .
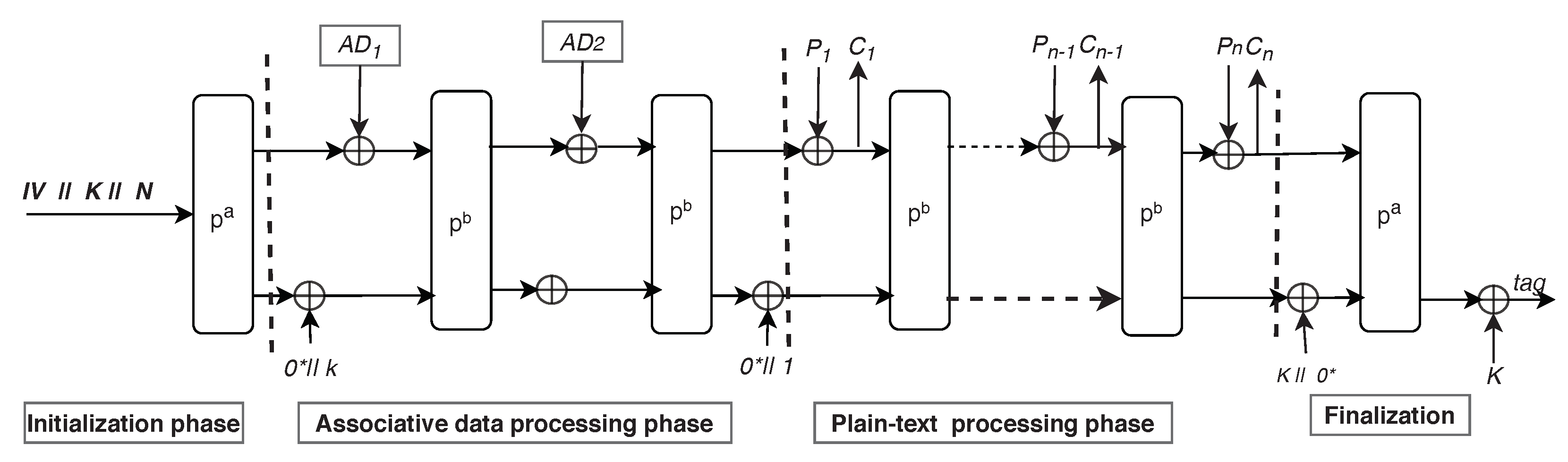
2.3.2. ASCON
3. The Proposed S6AE Scheme
3.1. Sensor Registration Phase
- calculates the master key by computing , where is the real identity of and is a random number. divides into four equal chunks of 64 bits, namely , , , and , and computes , where is a temporary key for .
- assigns a unique of 64 bits for .
- picks a key of 64 bits for and computes the pseudo-identity .
- computes and derives security parameter by computing , where , , , and are four equal chunks of 64 bit .
3.2. Sponge State Generation
- generates a random number of 64 bits and time stamp of 32 bits,
- computes , where is an initialization vector for ,
- computes and derives , where is the first 24 bytes of . The size of is 320 bits ( = 24 bytes + = 16 bytes), which is served as input to the encryption algorithm during the initialization phase.
3.3. Associative Data Generation
- computes . It then divides into two equal parts, i.e., and each of 128 bits.
- computes and divides into two equal parts, i.e., and , each of 64 bits.
- The encryption algorithm takes and as the inputs at the associative data processing phase to preserve their integrity.
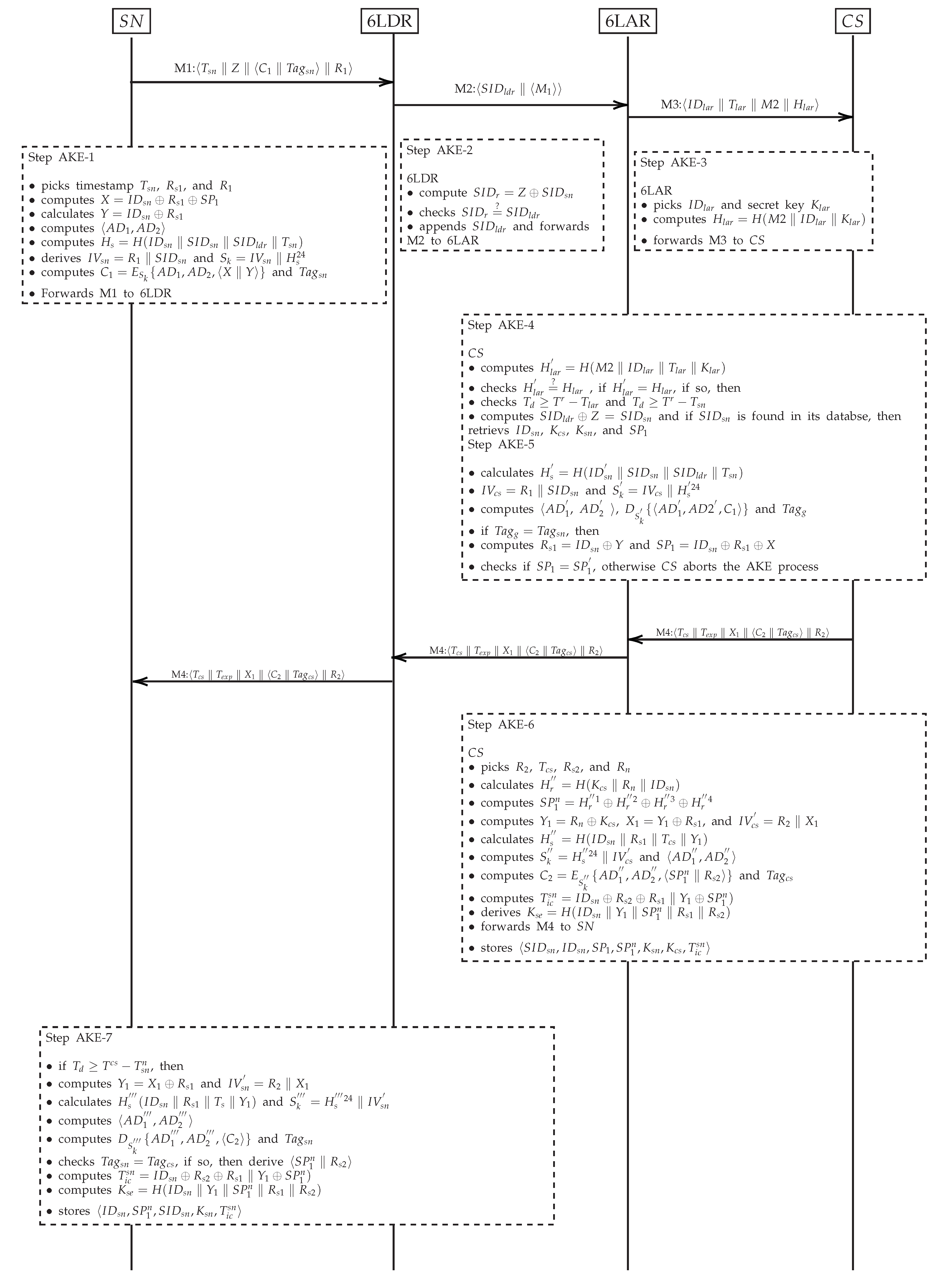
3.4. Authentication and Key Exchange
3.4.1. Step AKE-1
3.4.2. Step AKE-2
3.4.3. Step AKE-3
3.4.4. Step AKE-4
3.4.5. Step AKE-5
3.4.6. Step AKE-6
3.4.7. Step AKE-7
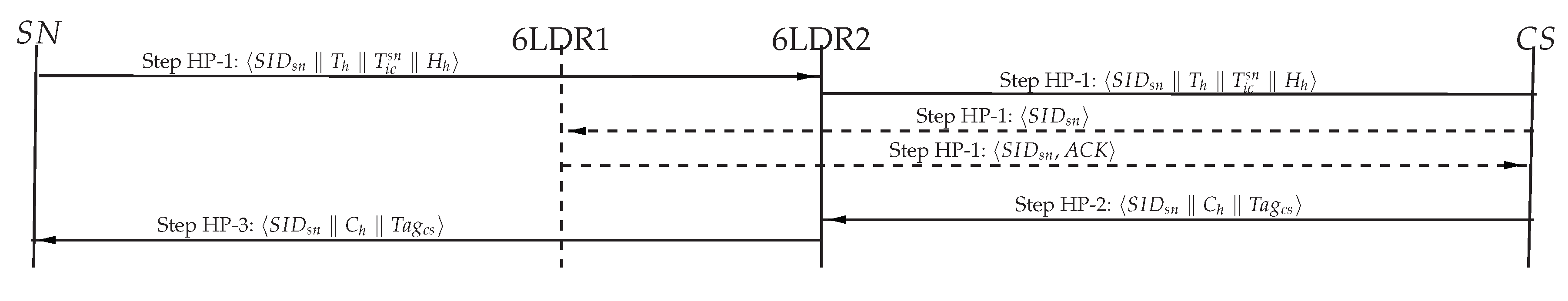
3.5. Handover Phase
3.5.1. Step HP-1
3.5.2. Step HP-2
3.5.3. Step HP-3
4. Security Analysis
4.1. Informal Security Analysis
4.1.1. Header Verification
4.1.2. DoS Attack
4.1.3. Replay Attack
4.1.4. Man-in-the-Middle (MITM) Attack
4.1.5. Sensor Impersonation Attack
4.1.6. Server Impersonation Attack
4.1.7. Identity Privacy Preservation
4.1.8. Unlinkability/Anonymity
4.1.9. Sybil Attack
4.1.10. Forward/Backward Secrecy
4.1.11. Ephemeral Secret Leakage (ESL) Attack
4.2. Crypt-Analysis Using BAN Logic
4.2.1. Assumptions
- AS-1:
- AS-2:
- AS-3:
- AS-4:
- AS-5:
- AS-6:
- AS-7:
- AS-8:
- AS-9:
- AS-10:
- AS-11:
- AS-12:
- AS-13:
- AS-14:
- AS-15:
4.2.2. Goals
- G1:
- G2:
- G3:
- G4:
4.2.3. Protocol Idealized Form
- IF1: :
- IF2: :
4.2.4. Formal Verification
- VF-1: From IF1, AS-7, AS-8, and by applying Message-Meaning-Rules, it is possible to achieve
- VF-2: From IF1, AS-2 and by applying Freshness-Rule concludes
- VF-3: Using VF-1, VF-2 and by applying the Nonce-Verification-Rule, it is possible to obtain
- VF-4: From VF-3 and by applying the Belief-Rule, the goal G1 can be achieved as
- VF-5: The goal G2 can be accomplished by utilizing VF-4, AS-13, and by employing the Jurisdiction-Rule from
- VF-6: From IF2, AS-11, and by applying Message-Meaning-Rules, it is possible to derive
- VF-7: By using IF2, AS-1, and utilizing the Freshness-Rule, we get
- VF-8: Using VF-6, VF-7 and by applying the Nonce-Verification-Rule, it is possible to obtain
- VF-9: G3 can be achieved by using VF-8 and by employing the Belief-Rule from
- VF-10: From (11) G4 can be derived by utilizing AS-12 and by employing Jurisdiction-Rule
4.3. Crypt-Analysis Using AVISPA
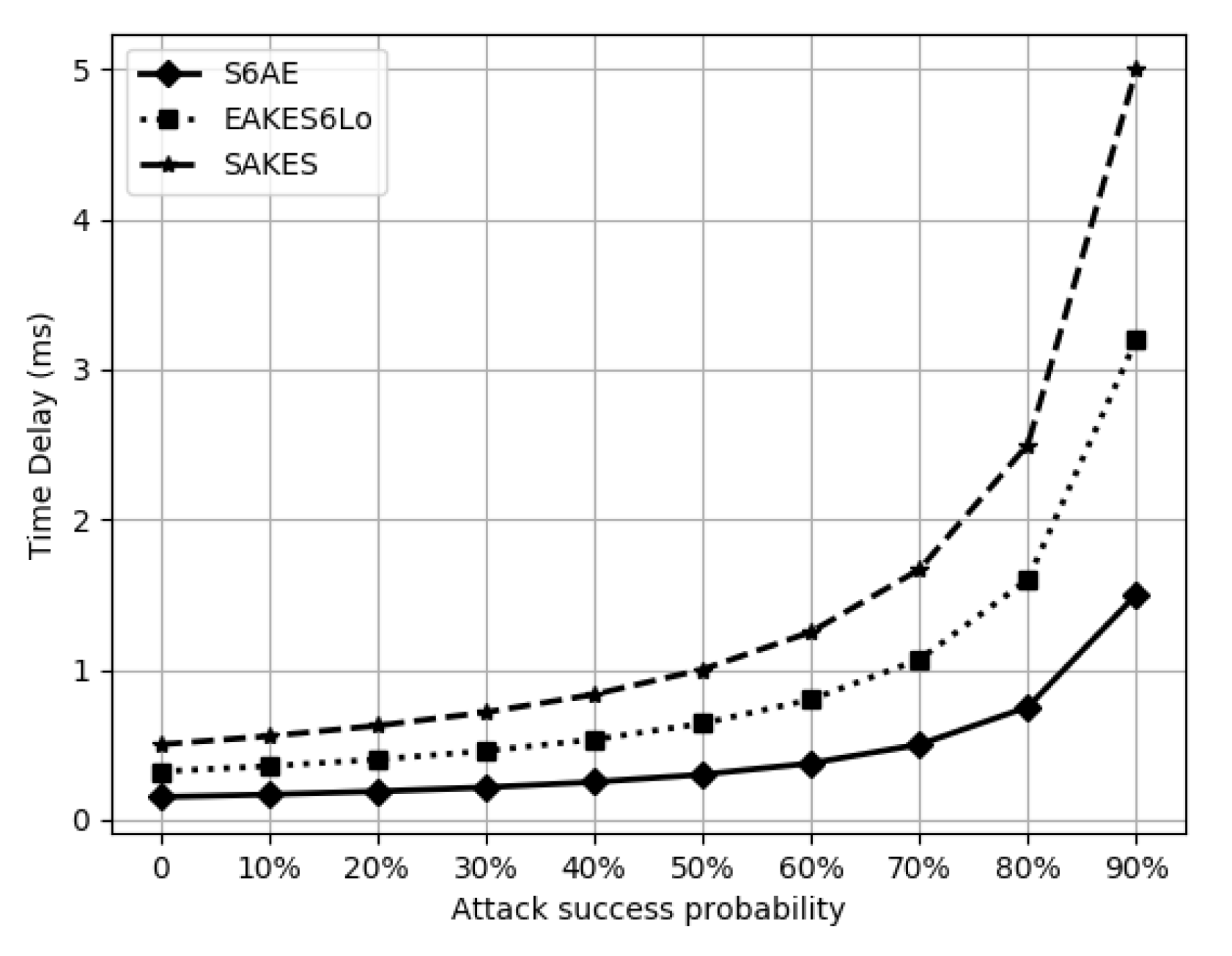
5. Performance Evaluation
5.1. Security Comparison
5.2. Computational Overhead
5.3. Communication Overhead and Energy Consumption
5.4. Storage Overhead Comparison
5.5. Handover Phase Comparison
5.6. Discussion
6. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Miguel, M.; Jamhour, E.; Pellenz, M.; Penna, M. SDN architecture for 6LoWPAN wireless sensor networks. Sensors 2018, 18, 3738. [Google Scholar] [CrossRef] [PubMed]
- Nait Hamoud, O.; Kenaza, T.; Challal, Y. Security in device-to-device communications: A survey. IET Netw. 2018, 7, 14–22. [Google Scholar] [CrossRef]
- Gomes, T.; Salgado, F.; Pinto, S.; Cabral, J.; Tavares, A. A 6LoWPAN accelerator for Internet of Things endpoint devices. IEEE Internet Things J. 2017, 5, 371–377. [Google Scholar] [CrossRef]
- Gomez, C.; Paradells, J.; Bormann, C.; Crowcroft, J. From 6LoWPAN to 6Lo: Expanding the universe of IPv6-supported technologies for the Internet of Things. IEEE Commun. Mag. 2017, 55, 148–155. [Google Scholar] [CrossRef]
- Hennebert, C.; Santos, J.D. Security protocols and privacy issues into 6LoWPAN stack: A synthesis. IEEE Internet Things J. 2014, 1, 384–398. [Google Scholar] [CrossRef]
- Li, Y.; Wang, X. Green content communications in 6LoWPAN. IET Netw. 2020, 9, 38–42. [Google Scholar] [CrossRef]
- Kushalnagar, N.; Montenegro, G. Transmission of IPv6 packets over IEEE 802.15. 4 networks. IEEE Commun. Mag. 2007, 4944, 130. [Google Scholar]
- Ishaq, I.; Carels, D.; Teklemariam, G.K.; Hoebeke, J.; Abeele, F.V.D.; Poorter, E.D.; Moerman, I.; Demeester, P. IETF standardization in the field of the Internet of Things (IoT): A survey. J. Sens. Actuator Netw. 2013, 2, 235–287. [Google Scholar] [CrossRef]
- Yeole, A.; Kalbande, D.; Sharma, A. Security of 6LoWPAN IoT Networks in hospitals for medical data exchange. Procedia Comput. Sci. 2019, 152, 212–221. [Google Scholar] [CrossRef]
- Sha, K.; Wei, W.; Yang, T.A.; Wang, Z.; Shi, W. On security challenges and open issues in Internet of Things. Future Gener. Comput. Syst. 2018, 83, 326–337. [Google Scholar] [CrossRef]
- Butun, I.; Österberg, P.; Song, H. Security of the Internet of Things: Vulnerabilities, attacks and countermeasures. IEEE Commun. Surv. Tutor. 2019, 22, 616–644. [Google Scholar] [CrossRef]
- Raza, S.; Duquennoy, S.; Chung, T.; Yazar, D.; Voigt, T.; Roedig, U. Securing communication in 6LoWPAN with compressed IPsec. In Proceedings of the 2011 International Conference on Distributed Computing in Sensor Systems and Workshops (DCOSS), Barcelona, Spain, 27–29 June 2011; pp. 1–8. [Google Scholar]
- Raza, S.; Seitz, L.; Sitenkov, D.; Selander, G. S3K: Scalable security with symmetric keys-DTLS key establishment for the Internet of Things. IEEE Trans. Autom. Sci. Eng. 2016, 13, 1270–1280. [Google Scholar] [CrossRef]
- Chuang, M.C.; Lee, J.F.; Chen, M.C. SPAM: A secure password authentication mechanism for seamless handover in proxy mobile IPv6 networks. IEEE Syst. J. 2012, 7, 102–113. [Google Scholar] [CrossRef]
- Perrig, A.; Szewczyk, R.; Tygar, J.D.; Wen, V.; Culler, D.E. SPINS: Security protocols for sensor networks. Wirel. Netw. 2002, 8, 521–534. [Google Scholar] [CrossRef]
- Hussen, H.R.; Tizazu, G.A.; Ting, M.; Lee, T.; Choi, Y.; Kim, K.H. SAKES: Secure authentication and key establishment scheme for M2M communication in the IP-based wireless sensor network (6LoWPAN). In Proceedings of the 2013 Fifth International Conference on Ubiquitous and Future Networks (ICUFN), Da Nang, Vietnam, 2–5 July 2013; pp. 246–251. [Google Scholar]
- Qiu, Y.; Ma, M. A mutual authentication and key establishment scheme for M2M communication in 6LoWPAN networks. IEEE Trans. Ind. Inform. 2016, 12, 2074–2085. [Google Scholar] [CrossRef]
- Roselin, A.G.; Nanda, P.; Nepal, S. Lightweight authentication protocol (LAUP) for 6LoWPAN Wireless Sensor Networks. In Proceedings of the 2017 IEEE Trustcom/BigDataSE/ICESS, Sydney, NSW, Australia, 1–4 Auguest 2017; pp. 371–378. [Google Scholar]
- Wang, X.; Mu, Y. Communication security and privacy support in 6LoWPAN. J. Inf. Secur. Appl. 2017, 34, 108–119. [Google Scholar] [CrossRef]
- Glissa, G.; Meddeb, A. 6LowPSec: An end-to-end security protocol for 6LoWPAN. Ad Hoc Netw. 2019, 82, 100–112. [Google Scholar] [CrossRef]
- Hui, J.; Thubert, P. Compression Format for IPv6 Datagrams over IEEE 802.15.4-Based Networks. Available online: https://www.hjp.at/doc/rfc/rfc6282.html (accessed on 18 March 2020).
- Dolev, D.; Yao, A. On the security of public key protocols. Trans. Inform. Theory 1983, 29, 198–208. [Google Scholar] [CrossRef]
- Dobraunig, C.; Eichlseder, M.; Mendel, F.; Schläffer, M. ASCON v1. 2. Available online: https://competitions.cr.yp.to/round3/asconv12.pdf (accessed on 18 March 2020).
- Fivez, M. Energy Efficient Hardware Implementations of CAESAR Submissions. Master’s Thesis, KU Leuven, Leuven, Belgium, 2016. [Google Scholar]
- Diehl, W.; Abdulgadir, A.; Farahmand, F.; Kaps, J.P.; Gaj, K. Comparison of cost of protection against differential power analysis of selected authenticated ciphers. Cryptography 2018, 2, 26. [Google Scholar] [CrossRef]
- Adomnicai, A.; Fournier, J.J.; Masson, L. Masking the lightweight authenticated ciphers ACORN and ASCON in software. IACR 2018, 2018, 708. [Google Scholar]
- Pundir, S.; Wazid, M.; Singh, D.P.; Das, A.K.; Rodrigues, J.J.P.C.; Park, Y. Intrusion Detection Protocols in Wireless Sensor Networks Integrated to Internet of Things Deployment: Survey and Future Challenges. IEEE Access 2020, 8, 3343–3363. [Google Scholar] [CrossRef]
- Yang, Y.; Wu, L.; Yin, G.; Li, L.; Zhao, H. A Survey on Security and Privacy Issues in Internet-of-Things. IEEE Internet Things J. 2017, 4, 1250–1258. [Google Scholar] [CrossRef]
- Khan, R.; Kumar, P.; Jayakody, D.N.K.; Liyanage, M. A survey on security and privacy of 5G technologies: Potential solutions, recent advancements and future directions. IEEE Commun. Surv. Tutor. 2019, 22, 196–248. [Google Scholar] [CrossRef]
- Burrows, M.; Abadi, M.; Needham, R.M. A logic of authentication. R. Soc. Open Sci. 1989, 426, 233–271. [Google Scholar]
- Armando, A.; Basin, D.; Boichut, Y.; Chevalier, Y.; Compagna, L.; Cuéllar, J.; Drielsma, P.H.; Héam, P.C.; Kouchnarenko, O.; Mantovani, J. The AVISPA Tool for the Automated Validation of Internet Security Protocols and Applications; Springer: Berlin/Heidelberg, Germany, 2005; pp. 281–285. [Google Scholar]
- Automated Validation of Internet Security Protocols and Applications AVISPA. Available online: http://www.avispa-project.org/ (accessed on 20 March 2020).
- Kivinen, T.; Kojo, M. More Modular Exponential (MODP) Diffie-Hellman Groups for Internet Key Exchange. Available online: https://www.hjp.at/doc/rfc/rfc3526.html (accessed on 20 March 2020).
- De Meulenaer, G.; Gosset, F.; Standaert, F.X.; Pereira, O. On the energy cost of communication and cryptography in wireless sensor networks. In Proceedings of the 2008 IEEE International Conference on Wireless and Mobile Computing, Networking and Communications, Avignon, France, 12–14 October 2008; pp. 580–585. [Google Scholar]


| Notation | Description |
|---|---|
| , | Central server and 6LoWPAN sensor node |
| , , | Pseudo-identities of sensor node and 6LDR, respectively |
| , , | Secret real-identities of 6LoWPAN sensor nodes and secret parameter used in authentication process |
| , | Encryption and decryption of message using the secret-key |
| , | Authentication parameter generated by encryption and decryption algorithm at and , respectively |
| , , | Timestamps at , and 6LAR, respectively. |
| , | Initialization vectors at and , respectively |
| , | ASCON initialization states at and , respectively |
| , | Initialization states at and in the handover phase, respectively. |
| , and , | Keys for and random number used in authentication process |
| , | MAC addresses of and , respectively |
| , | Timestamp and random number used in handover phase, respectively |
| , ⊕, ‖ | Cryptographic hash-function, bit-wise XOR, and concatenation, respectively |
| Feature | Description |
|---|---|
| S believes if the formula X is true | |
| S once said X | |
| S sees X | |
| k is a shared-secret between S and H | |
| K is a secret parameter known only S and H | |
| X is fresh. | |
| X is encrypted with the secret key k | |
| X is combine with secret Y | |
| S has jurisdiction over X | |
| If S is true then H is also true |
| Notation | Description | ||
|---|---|---|---|
| Message-Meaning-Rule | |||
| Jurisdiction-Rule | |||
| Belief-Rule | |||
| Nonce-Verification-Rule | |||
| Freshness-Rule |
| Parameter | Size (Bits) | ||||
|---|---|---|---|---|---|
| Encryption Algorithm | ASCON-128a | ||||
| 64 | |||||
| 64 | |||||
| 64 | |||||
| 64 | |||||
| 64 | |||||
| timestamp | 32 | ||||
| HASH Function | SHA-256 | ||||
| Random numbers | 64 |
| SAKES | EAKES6Lo | S6AE | |
|---|---|---|---|
| Header Verification | × | × | ✓ |
| Replay attack | ✓ | ✓ | ✓ |
| Compromised attack | × | ✓ | ✓ |
| IP-Spoofing attack | × | × | ✓ |
| Unlinkability | × | ✓ | ✓ |
| Forward secrecy | × | ✓ | ✓ |
| Sybil attack | ✓ | ✓ | ✓ |
| Impersonation attack | ✓ | ✓ | ✓ |
| DOS attack | ✓ | ✓ | ✓ |
| MITM attack | ✓ | ✓ | ✓ |
| Identity Privacy Preservation | × | × | ✓ |
| Mutual authentication | ✓ | ✓ | ✓ |
| Mobility | × | ✓ | ✓ |
| Scheme | 6LDR | 6LAR | Total Time | ||
|---|---|---|---|---|---|
| SAKES | - | ms | |||
| EAKES6Lo | ms | ||||
| S6AE | ms |
| Security Schemes | |||
|---|---|---|---|
| Exchanged Messages | EAKES6Lo | SAKES | S6AE |
| 672 bits | 688 bits | 496 bits | |
| 784 bits | 2176 bits | 528 bits | |
| Proposed Scheme | Energy Consumption | ||||
|---|---|---|---|---|---|
| S6AE | mJ | ||||
| EAKES6Lo | mJ | ||||
| SAKES | mJ |
| Storage Cost | SAKES | EAKES6Lo | S6AE |
|---|---|---|---|
| Sensor () | 272 bytes | 88 bytes | 46 bytes |
| Server () | 272 bytes | 80 bytes | 54 bytes |
| Computational Overhead | Communication Overhead | |||||
|---|---|---|---|---|---|---|
| Scheme | Computational Time | Time Cost (ms) | No. of Messages | Energy Cost (mJ) | ||
| EAKES6Lo | 11.9366 | 704 bits | 672 bits | 6 | 1.05 | |
| S6AE | 0.2544 | 480 bits | 418 bits | 6 | 0.68 | |
| SAKES | n/a | - | n/a | n/a | n/a | n/a |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Tanveer, M.; Abbas, G.; Abbas, Z.H.; Waqas, M.; Muhammad, F.; Kim, S. S6AE: Securing 6LoWPAN Using Authenticated Encryption Scheme. Sensors 2020, 20, 2707. https://doi.org/10.3390/s20092707
Tanveer M, Abbas G, Abbas ZH, Waqas M, Muhammad F, Kim S. S6AE: Securing 6LoWPAN Using Authenticated Encryption Scheme. Sensors. 2020; 20(9):2707. https://doi.org/10.3390/s20092707
Chicago/Turabian StyleTanveer, Muhammad, Ghulam Abbas, Ziaul Haq Abbas, Muhammad Waqas, Fazal Muhammad, and Sunghwan Kim. 2020. "S6AE: Securing 6LoWPAN Using Authenticated Encryption Scheme" Sensors 20, no. 9: 2707. https://doi.org/10.3390/s20092707
APA StyleTanveer, M., Abbas, G., Abbas, Z. H., Waqas, M., Muhammad, F., & Kim, S. (2020). S6AE: Securing 6LoWPAN Using Authenticated Encryption Scheme. Sensors, 20(9), 2707. https://doi.org/10.3390/s20092707







