Blockchain Evaluation Approaches: State-of-the-Art and Future Perspective
Abstract
1. Introduction
2. Methodology
3. Background and Motivation
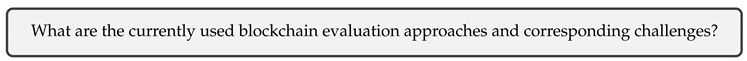
4. Evaluation Strategies and Metrics
5. Analytical and Simulation-Based Approaches
5.1. Queuing Models
5.2. Markov Processes
5.3. Markov Decision Processes
5.4. Random Walks
6. Emulation-Based Approaches
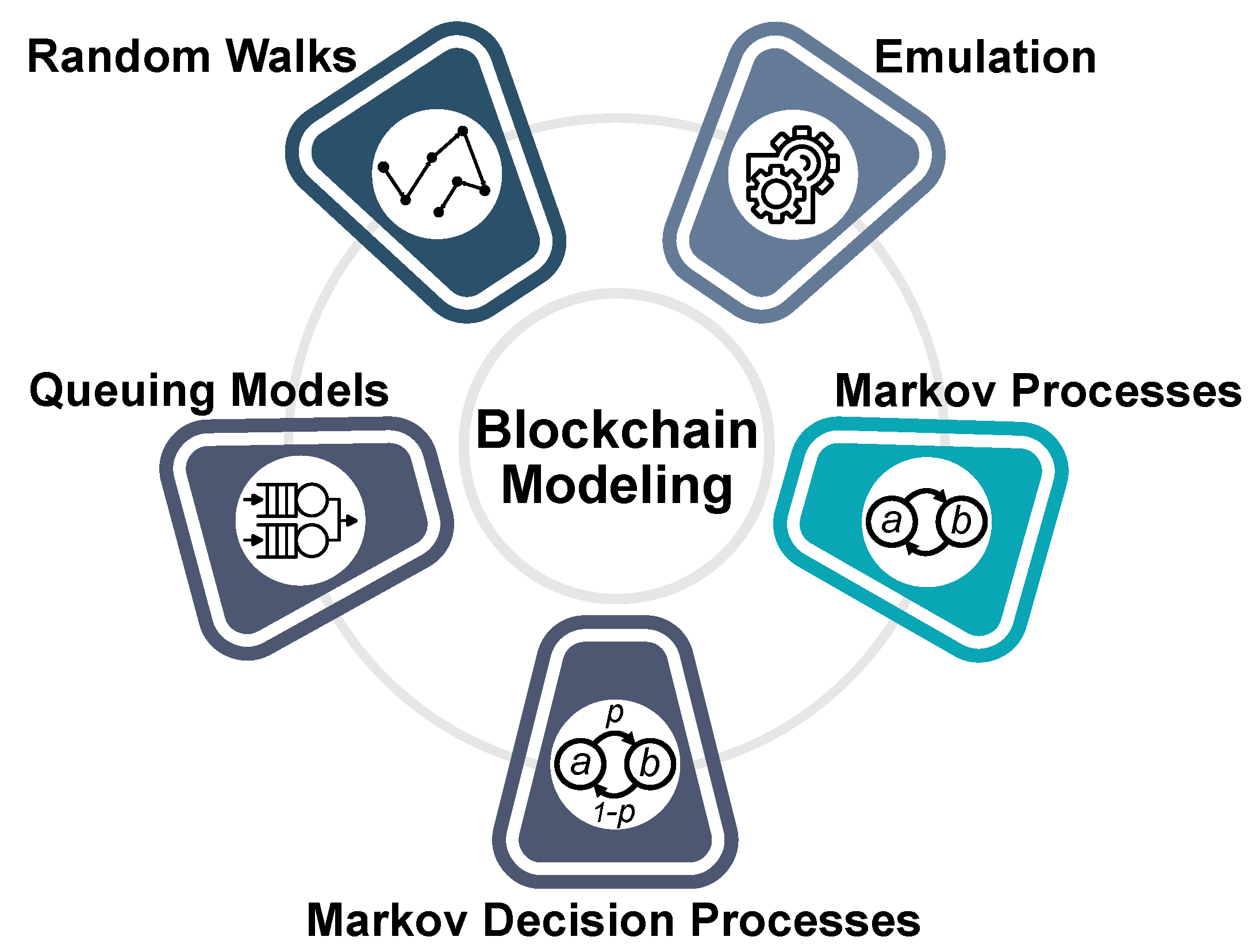
7. Current Challenges and Future Prospects
7.1. Lack of Adoption
7.2. Lack of Expertise
7.3. Lack of Standardization
7.4. A Multi-Task Benchmark for the Models’ Comparison
7.5. Access to the Representative Historical Data of Blockchain Systems
7.6. Abstractions Used in a Simulation Model May Affect the Accuracy of the Model
7.7. Relations Between Blockchain Characteristics
7.8. Resource Constraints
7.9. Machine Learning in Simulation Modeling
8. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Zheng, Z.; Xie, S.; Dai, H.; Chen, X.; Wang, H. An Overview of Blockchain Technology: Architecture, Consensus, and Future Trends. In Proceedings of the IEEE International Congress on Big Data (BigData Congress), Honolulu, HI, USA, 25–30 June 2017; pp. 557–564. [Google Scholar]
- Bellini, E.; Iraqi, Y.; Damiani, E. Blockchain-based Distributed Trust and Reputation Management Systems: A Survey. IEEE Access 2020, 8, 21127–21151. [Google Scholar] [CrossRef]
- Sunyaev, A. Distributed Ledger Technology. In Internet Computing; Springer: Berlin/Heidelberg, Germany, 2020; pp. 265–299. [Google Scholar]
- Khan, M.A.; Salah, K. IoT Security: Review, Blockchain Solutions, and Open Challenges. Future Gener. Comput. Syst. 2018, 82, 395–411. [Google Scholar] [CrossRef]
- WinterGreenResearc, Inc. Blockchain Market Shares, Market Strategies, and Market Forecasts, 2018 to 2024; Industry Survey: Lexington, MA, USA, 2018. [Google Scholar]
- Pawczuk, L.; Massev, R.; Schatsky, D. Breaking Blockchain: Open Deloitte’s 2018 Global Blockchain Survey; Deloitte Consulting: Denver, CO, USA, 2018. [Google Scholar]
- Insights, D. Deloitte’s 2019 Global Blockchain Survey. In Blockchain Gets Down to Business; Deloitte Consulting: Denver, CO, USA, 2019. [Google Scholar]
- IDC. Distribution of Blockchain Market Value Worldwide in 2018. 2018. Available online: https://www.idc.com/getdoc.jsp?containerId=prAP43559618 (accessed on 8 June 2020).
- Researcht, B. Global Blockchain in Agriculture and Food Market: Focus on Stakeholders, Regulations, Application (Supply Chain Tracking, Finance Management, Data Management, and Land and Property Ownership) and Regional Adoption; BIS Research: Fremont, CA, USA, 2018. [Google Scholar]
- PwC. Blockchain Survey. 2018. Available online: https://www.pwc.com/blockchainsurvey (accessed on 8 June 2020).
- Dimitrov, B. What Changed? Enterprise Blockchain Startups Are All of A Sudden Cool. 2020. Available online: https://www.forbes.com/sites/biserdimitrov/2020/02/19/what-changed-enterprise-blockchain-startups-are-all-of-a-sudden-cool/ (accessed on 8 June 2020).
- Bizinger, D. EU Startups: Blockchain. 2020. Available online: https://www.eu-startups.com/tag/blockchain/ (accessed on 8 June 2020).
- CBI Insights. Blockchain in Review: Investment Trends And Opportunities; Technical Report; CB Information Services, Inc.: New York, NY, USA, 2019. [Google Scholar]
- Lawrence, L.; Joel, J. Investments in Blockchain 2019: $23.7 Billion Raised by 3738 Blockchain Companies Since 2013. 2019. Available online: https://outlierventures.io/research/investments-in-blockchains-2019-23-7-billion-raised-by-3738-blockchain-companies-since-2013/ (accessed on 8 June 2020).
- CoinDesk. ICO Tracker. 2018. Available online: https://www.coindesk.com/ico-tracker/ (accessed on 8 June 2020).
- Blechschmidt, B.B. Blockchain in Europe: Closing the Strategy Gap. Cognizant. 2018. Available online: https://www.cognizant.com/whitepapers/blockchain-in-europe-closing-the-strategy-gap-codex3320.pdf (accessed on 8 June 2020).
- Blockchain White Paper—China Academy of Information and Communication Technology. 2018. Available online: http://www.caict.ac.cn/english/yjcg/bps/201901/P020190131402018699770.pdf (accessed on 8 June 2020).
- Gartner. Organizations’ Blockchain Plans. 2018. Available online: https://www.gartner.com/newsroom/id/3873790 (accessed on 8 June 2020).
- Blockchain Market Cap. 2019. Available online: https://www.blockchain.com/charts/market-cap (accessed on 8 June 2020).
- TradingView. Cryptocurrency Market. 2019. Available online: https://www.tradingview.com/markets/cryptocurrencies/global-charts/ (accessed on 8 June 2020).
- Alphand, O.; Amoretti, M.; Claeys, T.; Dall’Asta, S.; Duda, A.; Ferrari, G.; Rousseau, F.; Tourancheau, B.; Veltri, L.; Zanichelli, F. IoTChain: A Blockchain Security Architecture for the Internet of Things. In Proceedings of the IEEE Wireless Communications and Networking Conference (WCNC), Barcelona, Spain, 15–18 April 2018; pp. 1–6. [Google Scholar]
- De Vries, A. Bitcoin’s Growing Energy Problem. Joule 2018, 2, 801–805. [Google Scholar] [CrossRef]
- Nakamoto, S. Bitcoin: A Peer-to-Peer Electronic Cash System. White Papper; Manubot: Panama City, Panama, 2019. [Google Scholar]
- Busanelli, S.; Cirani, S.; Melegari, L.; Picone, M.; Rosa, M.; Veltri, L. A Sidecar Object for the Optimized Communication Between Edge and Cloud in Internet of Things Applications. Future Internet 2019, 11, 145. [Google Scholar] [CrossRef]
- Mäkitalo, N.; Ometov, A.; Kannisto, J.; Andreev, S.; Koucheryavy, Y.; Mikkonen, T. Safe, Secure Executions at the Network Edge: Coordinating Cloud, Edge, and Fog Computing. IEEE Softw. 2017, 35, 30–37. [Google Scholar] [CrossRef]
- Hyperledger Blockchain Performance Metrics: White Paper. 2018. Available online: https://www.hyperledger.org/wp-content/uploads/2018/10/HL_Whitepaper_Metrics_PDF_V1.01.pdf (accessed on 8 June 2020).
- Lao, L.; Li, Z.; Hou, S.; Xiao, B.; Guo, S.; Yang, Y. A Survey of IoT Applications in Blockchain Systems: Architecture, Consensus, and Traffic Modeling. ACM Comput. Surv. (CSUR) 2020, 53, 1–32. [Google Scholar] [CrossRef]
- Dinh, T.; Anh, T.; Wang, J.; Chen, G.; Liu, R.; Ooi, C.; Tan, K.L. Blockbench: A Framework for Analyzing Private Blockchains. In Proceedings of the 2017 ACM International Conference on Management of Data, Chicago, IL USA, 14–19 May 2017; pp. 1085–1100. [Google Scholar]
- Chen, C.; Qi, Z.; Liu, Y.; Lei, K. Using Virtualization for Blockchain Testing. In International Conference on Smart Computing and Communication; Springer: Berlin/Heidelberg, Germany, 2017; pp. 289–299. [Google Scholar]
- Zhidanov, K.; Bezzateev, S.; Afanasyeva, A.; Sayfullin, M.; Vanurin, S.; Bardinova, Y.; Ometov, A. Blockchain Technology for Smartphones and Constrained IoT Devices: A Future Perspective and Implementation. In Proceedings of the 21st Conference on Business Informatics (CBI), Moscow, Russia, 15–17 July 2019; Volume 2, pp. 20–27. [Google Scholar]
- Ometov, A.; Bardinova, Y.; Afanasyeva, A.; Masek, P.; Zhidanov, K.; Vanurin, S.; Sayfullin, M.; Shubina, V.; Komarov, M.; Bezzateev, S. An Overview on Blockchain for Smartphones: State-of-the-Art, Consensus, Implementation, Challenges and Future Trends. IEEE Access [Early Access] 2020. [Google Scholar] [CrossRef]
- Faria, C.; Correia, M. BlockSim: Blockchain Simulator. In Proceedings of the IEEE International Conference on Blockchain (Blockchain), Atlanta, GA, USA, 14–17 July 2019; pp. 439–446. [Google Scholar]
- Moher, D.; Liberati, A.; Tetzlaff, J.; Altman, D.G. Preferred Reporting Items for Systematic Reviews and Meta-analyses: The PRISMA Statement. Ann. Intern. Med. 2009, 151, 264–269. [Google Scholar] [CrossRef]
- Miraz, M.H.; Ali, M. Blockchain Enabled Smart Contract Based Applications: Deficiencies with the Software Development Life Cycle Models. arXiv 2020, arXiv:2001.10589. [Google Scholar]
- Memon, R.A.; Li, J.P.; Ahmed, J. Simulation model for blockchain systems using queuing theory. Electronics 2019, 8, 234. [Google Scholar] [CrossRef]
- Banks, J. Discrete Event System Simulation; Pearson Education: London, UK, 2005. [Google Scholar]
- Sokolowski, J.A.; Banks, C.M. Principles of Modeling and Simulation: A Multidisciplinary Approach; John Wiley & Sons: Hoboken, NJ, USA, 2011. [Google Scholar]
- Pirmagomedov, R.; Ometov, A.; Moltchanov, D.; Lu, X.; Kovalchukov, R.; Olshannikova, E.; Andreev, S.; Koucheryavy, Y.; Dohler, M. Applying Blockchain Technology for User Incentivization in mmWave-based Mesh Networks. IEEE Access 2020, 8, 50983–50994. [Google Scholar] [CrossRef]
- Law, A.; Kelton, D. Simulation Modeling and Analysis; McGraw-Hill Education: Frisco, TX, USA, 2000; Volume 5. [Google Scholar]
- Li, Q.L.; Ma, J.Y.; Chang, Y.X.; Ma, F.Q.; Yu, H.B. Markov Processes in Blockchain Systems. Comput. Soc. Netw. 2019, 6, 1–28. [Google Scholar] [CrossRef]
- Kawase, Y.; Kasahara, S. Transaction-confirmation Time for Bitcoin: A Queueing Analytical Approach to Blockchain Mechanism. In Proceedings of the International Conference on Queueing Theory and Network Applications, Qinhuangdao, China, 21–23 August 2017; Springer: Berlin/Heidelberg, Germany, 2017; pp. 75–88. [Google Scholar]
- Kasahara, S.; Kawahara, J. Effect of Bitcoin Fee on Transaction-confirmation Process. J. Ind. Manag. Optim. 2019, 15, 365–386. [Google Scholar] [CrossRef]
- Li, Q.L.; Ma, J.Y.; Chang, Y.X. Blockchain Queue Theory. In Proceedings of the International Conference on Computational Social Networks, Shanghai, China, 18–20 December 2018; Springer: Berlin/Heidelberg, Germany, 2018; pp. 25–40. [Google Scholar]
- Memon, R.A.; Li, J.; Ahmed, J.; Khan, A.; Nazir, M.I.; Mangrio, M.I. Modeling of Blockchain Based Systems Using Queuing Theory Simulation. In Proceedings of the 15th International Computer Conference on Wavelet Active Media Technology and Information Processing (ICCWAMTIP), Chengdu, China, 14–16 December 2018; pp. 107–111. [Google Scholar]
- Papadis, N.; Borst, S.; Walid, A.; Grissa, M.; Tassiulas, L. Stochastic Models and Wide-Area Network Measurements for Blockchain Design and Analysis. In Proceedings of the IEEE Conference on Computer Communications (INFOCOM ), Honolulu, HI, USA, 16–19 April 2018; pp. 2546–2554. [Google Scholar]
- Ricci, S.; Ferreira, E.; Menasche, D.S.; Ziviani, A.; Souza, J.E.; Vieira, A.B. Learning Blockchain Delays: A Queueing Theory Approach. ACM SIGMETRICS Perform. Eval. Rev. 2019, 46, 122–125. [Google Scholar] [CrossRef]
- Frolkova, M.; Mandjes, M. A Bitcoin-inspired Infinite-server Model with a Random Fluid Limit. Stoch. Models 2019, 35, 1–32. [Google Scholar] [CrossRef]
- King, C. The Fluid Limit of a Random Graph Model for a Shared Ledger. arXiv 2019, arXiv:1902.05050. [Google Scholar]
- Bolch, G.; Greiner, S.; De Meer, H.; Trivedi, K.S. Queueing Networks and Markov Chains: Modeling and Performance Evaluation with Computer Science Applications; John Wiley & Sons: Hoboken, NJ, USA, 2006. [Google Scholar]
- Bharucha-Reid, A.T. Elements of the Theory of Markov Processes and Their Applications; Courier Corporation: New York, NY, USA, 2010. [Google Scholar]
- Eyal, I.; Sirer, E.G. Majority is Not Enough: Bitcoin Mining is Vulnerable. In Proceedings of the International Conference on Financial Cryptography and Data Security, Christ Church, Barbados, 3–7 March 2014; Springer: Berlin/Heidelberg, Germany, 2014; pp. 436–454. [Google Scholar]
- Nayak, K.; Kumar, S.; Miller, A.; Shi, E. Stubborn Mining: Generalizing Selfish Mining and Combining with an Eclipse Attack. In Proceedings of the IEEE European Symposium on Security and Privacy (EuroS P), Saarbrucken, Germany, 21–24 March 2016; pp. 305–320. [Google Scholar] [CrossRef]
- Bai, Q.; Zhou, X.; Wang, X.; Xu, Y.; Wang, X.; Kong, Q. A Deep Dive into Blockchain Selfish Mining. In Proceedings of the IEEE International Conference on Communications (ICC), Shanghai, China, 20–24 May 2019; pp. 1–6. [Google Scholar]
- Kiffer, L.; Rajaraman, R.; Shelat, A. A Better Method to Analyze Blockchain Consistency. In Proceedings of the ACM SIGSAC Conference on Computer and Communications Security, Toronto, ON, Canada, 15–19 October 2018; pp. 729–744. [Google Scholar]
- Garay, J.; Kiayias, A.; Leonardos, N. The Bitcoin Backbone Protocol with Chains of Variable Difficulty. In Proceedings of the Annual International Cryptology Conference, Santa Barbara, CA, USA, 20–24 August 2017; Springer: Berlin/Heidelberg, Germany, 2017; pp. 291–323. [Google Scholar]
- Pass, R.; Seeman, L.; Shelat, A. Analysis of the Blockchain Protocol in Asynchronous Networks. In Proceedings of the Annual International Conference on the Theory and Applications of Cryptographic Techniques, Paris, France, 30 April–4 May 2017; Springer: Berlin/Heidelberg, Germany, 2017; pp. 643–673. [Google Scholar]
- Sapirshtein, A.; Sompolinsky, Y.; Zohar, A. Optimal Selfish Mining Strategies in Bitcoin. In Proceedings of the International Conference on Financial Cryptography and Data Security, Christ Church, Barbados, 22–26 February 2016; Springer: Berlin/Heidelberg, Germany, 2016; pp. 515–532. [Google Scholar]
- Gervais, A.; Karame, G.O.; Wüst, K.; Glykantzis, V.; Ritzdorf, H.; Capkun, S. On the Security and Performance of Proof of Work Blockchains. In Proceedings of the ACM SIGSAC Conference on Computer and Communications Security, Vienna, Austria, 24–28 October 2016; pp. 3–16. [Google Scholar]
- Zhang, R.; Preneel, B. Publish or Perish: A Backward-compatible Defense Against Selfish Mining in Bitcoin. In Proceedings of the Cryptographers’ Track at the RSA Conference, San Francisco, CA, USA, 14–17 February 2017; Springer: Berlin/Heidelberg, Germany, 2017; pp. 277–292. [Google Scholar]
- NS-3. Network Simulator. 2019. Available online: https://www.nsnam.org/ (accessed on 8 June 2018).
- Bitnodes. Global Bitcoin Nodes Distribution. 2020. Available online: https://bitnodes.earn.com/ (accessed on 8 June 2018).
- Wang, X.; Al-Mamun, A.; Yan, F.; Zhao, D. Toward Accurate and Efficient Emulation of Public Blockchains in the Cloud. In Proceedings of the International Conference on Cloud Computing, San Diego, CA, USA, 25–30 June 2019; Springer: Berlin/Heidelberg, Germany, 2019; pp. 67–82. [Google Scholar]
- Orlov, Y.; Kirina-Lilinskaya, E.; Samuylov, A.; Ometov, A.; Moltchanov, D.; Gaimamaka, Y.; Andreev, S.; Samouylov, K. Time-Dependent SIR Analysis in Shopping Malls Using Fractal-Based Mobility Models; Springer: Cham, Switzerland, 2017; pp. 16–25. [Google Scholar]
- Spitzer, F. Principles of Random Walk; Springer: New York, NY, USA, 2013; Volume 34. [Google Scholar]
- Goffard, P.O. Fraud Risk Assessment within Blockchain Transactions. Adv. Appl. Probab. 2019, 51, 443–467. [Google Scholar] [CrossRef]
- Grunspan, C.; Pérez-Marco, R. On Profitability of Nakamoto double spend. arXiv 2019, arXiv:1912.06412. [Google Scholar]
- Jang, J.; Lee, H.N. Profitable Double-Spending Attacks. arXiv 2019, arXiv:1903.01711. [Google Scholar]
- Dhillon, V.; Metcalf, D.; Hooper, M. The Hyperledger Project. In Blockchain Enabled Applications; Springer: Berlin/Heidelberg, Germany, 2017; pp. 139–149. [Google Scholar]
- Welcome to Hyperledger Composer GitHub Repository. 2020. Available online: https://hyperledger.github.io/composer/v0.19/introduction/introduction.html (accessed on 8 June 2018).
- Thakkar, P.; Nathan, S.; Viswanathan, B. Performance Benchmarking and Optimizing Hyperledger Fabric Blockchain Platform. In Proceedings of the 26th International Symposium on Modeling, Analysis, and Simulation of Computer and Telecommunication Systems (MASCOTS), Milwaukee, WI, USA, 25–28 September 2018; pp. 264–276. [Google Scholar]
- Stoykov, L.; Zhang, K.; Jacobsen, H.A. VIBES: Fast Blockchain Simulations for Large-Scale Peer-to-Peer Networks. In Proceedings of the ACM/IFIP/USENIX Middleware Conference: Posters and Demos, Las Vegas, NV, USA, 11–15 December 2017; pp. 19–20. [Google Scholar]
- Bitcoin-Simulator, Capable of Simulating Any Re-parametrization of Bitcoin. 2016. Available online: https://github.com/arthurgervais/Bitcoin-Simulator (accessed on 8 June 2018).
- Pongnumkul, S.; Siripanpornchana, C.; Thajchayapong, S. Performance Analysis of Private Blockchain Platforms in Varying Workloads. In Proceedings of the 26th International Conference on Computer Communication and Networks (ICCCN), Vancouver, BC, Canada, 31 July–3 August 2017; pp. 1–6. [Google Scholar]
- Ethereum for Enterprise. 2020. Available online: https://ethereum.org/enterprise/ (accessed on 8 June 2018).
- Ethereum Tester GitHub Repository. 2020. Available online: https://github.com/ethereum/eth-tester (accessed on 8 June 2018).
- Truffle: Smart Contracts made Sweeter. 2020. Available online: https://www.trufflesuite.com/truffle (accessed on 8 June 2018).
- Sahu, M. What is Truffle Suite? Features, How to Install, How to Run Smart Contracts. 2020. Available online: https://www.upgrad.com/blog/what-is-truffle-suite/ (accessed on 8 June 2018).
- Brown, R.G. The Corda Platform: An Introduction; White Paper; Corda: Dublin, Ireland, 2018. [Google Scholar]
- R3 Ltd. Corda Enterprise 4.2: Sizing and Performance. 2020. Available online: https://docs.corda.net/docs/corda-enterprise/4.2/sizing-and-performance.html (accessed on 8 June 2018).
- Exonum Documentation. 2020. Available online: https://exonum.com/doc/version/latest/ (accessed on 8 June 2018).
- Manticore GitHub Repository. 2020. Available online: https://github.com/trailofbits/manticore (accessed on 8 June 2018).
- Mossberg, M.; Manzano, F.; Hennenfent, E.; Groce, A.; Grieco, G.; Feist, J.; Brunson, T.; Dinaburg, A. Manticore: A User-friendly Symbolic Execution Framework for Binaries and Smart Contracts. In Proceedings of the 34th IEEE/ACM International Conference on Automated Software Engineering (ASE), San Diego, CA, USA, 11–15 November 2019; pp. 1186–1189. [Google Scholar]
- Permenev, A.; Dimitrov, D.; Tsankov, P.; Drachsler-Cohen, D.; Vechev, M. VerX: Safety Verification of Smart Contracts. In Proceedings of the IEEE Symposium on Security and Privacy, Genoa, Italy, 18–20 May 2020; pp. 18–20. [Google Scholar]
- Hildenbrandt, E.; Saxena, M.; Zhu, X.; Rodrigues, N.; Daian, P.; Guth, D.; Rosu, G. KEVM: A Complete Semantics of the Ethereum Virtual Machine. In Proceedings of the IEEE 31st Computer Security Foundations Symposium (CSF), Oxford, UK, 9–12 July 2018; pp. 204–217. [Google Scholar]
- Mohanty, D. Frameworks: Truffle and Embark. In Ethereum for Architects and Developers; Springer: Berlin/Heidelberg, Germany, 2018; pp. 181–195. [Google Scholar]
- Geth GitHub Repository. 2019. Available online: https://github.com/ethereum/go-ethereum/wiki/geth (accessed on 8 June 2018).
- EthereumJS Monorepo GitHub Repository. 2020. Available online: https://github.com/ethereumjs/ethereumjs-vm (accessed on 8 June 2018).
- bitcoinj GitHub Repository. 2020. Available online: https://github.com/bitcoinj/bitcoinj (accessed on 8 June 2018).
- Houben, R.; Snyers, A. Cryptocurrencies and Blockchain: Legal Context and Implications for Financial Crime, Money Laundering and Tax Evasion. In Technical Report, IPOL|Policy Department for Economic, Scientific and Quality of Life Policies; European Parlaiment: Brussels, Belgium, 2018. [Google Scholar]
- Maurer, B.; Nelms, T.C.; Swartz, L. “When Perhaps the Real Problem is Money Itself!”: The Practical Materiality of Bitcoin. Soc. Semiot. 2013, 23, 261–277. [Google Scholar] [CrossRef]
- Janssen, M.; Weerakkody, V.; Ismagilova, E.; Sivarajah, U.; Irani, Z. A Framework for Analysing Blockchain Technology Adoption: Integrating Institutional, Market and Technical Factors. Int. J. Inf. Manag. 2020, 50, 302–309. [Google Scholar] [CrossRef]
- Clohessy, T.; Acton, T. Investigating the influence of organizational factors onblockchain adoption: An innovation theory perspective. Ind. Manag. Data Syst. 2019, 119, 1457–1491. [Google Scholar] [CrossRef]
- Akram, S.V.; Malik, P.K.; Singh, R.; Anita, G.; Tanwar, S. Adoption of Blockchain Technology in Various Realms: Opportunities and Challenges. Secur. Priv. 2020, e109. [Google Scholar] [CrossRef]
- Wang, A.; Singh, A.; Michael, J.; Hill, F.; Levy, O.; Bowman, S. GLUE: A Multi-Task Benchmark and Analysis Platform for Natural Language Understanding. In Proceedings of the 7th International Conference on Learning Representations, New Orleans, LA, USA, 6–9 May 2019. [Google Scholar]
- Alsahan, L.; Lasla, N.; Abdallah, M. Local Bitcoin Network Simulator for Performance Evaluation Using Lightweight Virtualization. arXiv 2020, arXiv:2002.01243. [Google Scholar]
- Aoki, Y.; Otsuki, K.; Kaneko, T.; Banno, R.; Shudo, K. SimBlock: A Blockchain Network Simulator. In Proceedings of the IEEE Conference on Computer Communications Workshops (INFOCOM WKSHPS), Moscow, Russia, 23–27 September 2019; pp. 325–329. [Google Scholar]
- Kannengießer, N.; Lins, S.; Dehling, T.; Sunyaev, A. Mind the Gap: Trade-offs between Distributed Ledger Technology Characteristics. arXiv 2019, arXiv:1906.00861. [Google Scholar]
- Recknagel, F. Applications of Machine Learning to Ecological Modelling. Ecol. Model. 2001, 146, 303–310. [Google Scholar] [CrossRef]
- Tariq, H.; Al-Sahaf, H.; Welch, I. Modelling and Prediction of Resource Utilization of Hadoop Clusters: A Machine Learning Approach. In Proceedings of the 12th IEEE/ACM International Conference on Utility and Cloud Computing, Auckland, New Zealand, 2–5 December 2019; pp. 93–100. [Google Scholar]
- Dueben, P.D.; Bauer, P. Challenges and Design Choices for Global Weather and Climate Models Based on Machine Learning. Geosci. Model Dev. 2018, 11, 3999–4009. [Google Scholar] [CrossRef]
- Mosavi, A.; Salimi, M.; Faizollahzadeh Ardabili, S.; Rabczuk, T.; Shamshirband, S.; Varkonyi-Koczy, A.R. State of the Art of Machine Learning Models in Energy Systems, a Systematic Review. Energies 2019, 12, 1301. [Google Scholar] [CrossRef]
- Awiszus, M.; Rosenhahn, B. Markov Chain Neural Networks. In Proceedings of the IEEE Conference on Computer Vision and Pattern Recognition Workshops, Salt Lake City, UT, USA, 18–22 June 2018; pp. 2180–2187. [Google Scholar]
- Duell, S.; Hans, A.; Udluft, S. The Markov Decision Process Extraction Network. In Proceedings of the European Symposium On Artificial Neural Networks, Computational Intelligence and Machine Learning, Haifa, Israel, 21–24 June 2010. [Google Scholar]
| Metric | Type | Description | Main Challenge | |
|---|---|---|---|---|
| Consensus | P | The distributed process by which a network of nodes provides a guaranteed unique order of transactions and validates the block of transactions. | Inappropriate selection of a consensus algorithm may have a tremendous negative impact on the node and system operation. | |
| Transaction throughput | M | The rate at which valid transactions are committed by the blockchain network in a defined time period, commonly transactions per second (tps). | Careful selection of the system parameters is required in order to achieve the desired tps. | |
| Transaction type/size | P | The amount of data in the transaction to be added in the next block. | Inappropriate selection may have increased transaction fees in public blockchains. | |
| Blockchain metrics | Block size | P | Defined size of the block, essentially the number of transactions to be included. It could be used to control the blockchain operation. | Larger blocks may have a negative impact on OPEX and decrease the tps. |
| Chain size | M | The total size of the blockchain minus database indexes in megabytes. | A chain that is too long significantly decreases its distribution time to allow the new node to start the operation. | |
| Network-wide latency (commit time or transactional Latency) | M | The amount of time taken for a transaction to take effect to be used across the network. | Commit parameters may vary in different systems, e.g., 90% in public blockchains or 100% in enterprise private blockchains. | |
| Finality time | M | The moment when a transaction is committed and can no longer be reversed, i.e., the data cannot be rolled back to the previous state. | Defined in a consensus algorithm, and a threshold should be carefully selected during the evaluation. Otherwise, the finality time should significantly decrease the system efficiency. | |
| Network size (number of active peers) | M/P | The number of validating nodes participating in consensus excluding observer nodes. | n/a | |
| Network metrics | Volume of P2P traffic | M | The amount of cumulative traffic generated by active nodes in the system. | Operation over public networks may have a tremendous negative impact on energy consumption, connection quality, as well as increased OPEX. |
| Structure of underlying traffic | P | The structure of blockchain-related packets (data, service, etc.). | Inefficient selection may cause unnecessary traffic overheads. | |
| Packet loss ratio | M | The ratio between lost and sent packets related to blockchain operation. | Increased packet loss may increase delays and decrease tps. | |
| CPU/GPU | M | Hardware utilized for blockchain-related data processing. | Has a significant impact on the involvement in the blockchain operation, as well as on the Capital Expenditures (CAPEX) and OPEX. | |
| Memory | M | The amount of RAM required for efficient transaction/block processing. | ||
| Storage volume | M | Local storage space required for the blockchain. | ||
| Node metrics | Connectivity | M | Various metrics of the selected communications technology, its channel quality, reliability, latency, etc. | |
| Read latency | M | The time between the read request submission until the reply is received. | n/a | |
| Read throughput | M | A measure of how many read operations are completed in a defined time period expressed as reads per second (rps). | n/a | |
| Cache Hit Ratio (CHR) | M | Measurement of how many content requests a cache is able to fill successfully, compared to how many requests it receives. | Low CHR, mainly caused by hardware, may have an impact on the operational speed of a specific node. |
| # | Field of Study | Str. | Specifics |
|---|---|---|---|
| [41,42] | Bitcoin: Transaction-confirmation time | QM | The authors made the assumption that the times of the transaction confirmation follow a continuous probability distribution function. |
| [43] | Bitcoin: The queuing theory of blockchain systems under a dynamic behavior setting. | QM | Analysis of the average mean of transactions in the Memory Pool (MemPool), mean number of transactions in a block, and mean transaction-confirmation time. It is noted that considering more general blockchain queuing systems is required in the future. |
| [44] | Bitcoin: Behavior of blockchain-based applications before deploying them over the blockchain network | QM | The authors assumed that the number of arrivals to the system was a little more than those serviced at the mining station; however, in Bitcoin systems, the number of accumulated unconfirmed transactions can be observed to increase throughout the day. |
| [45] | Ethereum: valuation of selfish mining strategies’ impact. | QM | The work was focused on measurements, blockchain design, and analysis. It was stated that careful examination of the various system parameters’ relationships and related trade-offs should be a base for similar models’ development. |
| [46] | Bitcoin: Profitability of double spending attacks and delays. | QM | The authors assumed no off-chain payment mechanism with no simplified payment verification during the transaction confirmation. They stated that QMs were the most suitable for the analysis of transaction delays. |
| [47] | Bitcoin: The fluid limit of a random graph model for a shared ledger. | QM | It was stated that a more realistic FIFO-batch departure discipline is required in order to analyze a natural -like Bitcoin queue variant of the -like Bitcoin. |
| [48] | IOTA: The fluid limit of a random graph model for a shared ledger. | QM | The author attempted to analyze IOTA scholastically and find the differential equation for the delays in the system, i.e., a converged fluid limit. |
| [51] | Bitcoin: Incentive-compatible property of Blockchain systems. | MP | The authors highlighted the importance of the chain-quality property since if the adversary controls a suitably limited amount of hashing power, then the adversary is also limited in terms of the number of blocks it has added. |
| [52] | Bitcoin: Selfish mining attack. | MP | The authors stressed that a malicious user in this system would eventually succeed in case he/she executed double-spending simultaneously, thus defining a new research direction of stubborn mining. |
| [53] | Bitcoin: Selfish mining attack. | MP | The work observed the relation of the number of malicious selfish miners vs. the selected one success rate. |
| [54] | GHOST(Ethereum): Consistency properties of blockchain protocols. | MP | The work proposed a model that considered various attacks and aspects of the protocols’ operation. The authors assumed that some random genesis blocks were available from the initial trusted setup. They also stated that Markov models needed to be extremely complex in order to capture the dynamics of such complicated systems. |
| [57] | Bitcoin: Selfish mining attack. | MDP | Profit threshold for selfish mining attacks aimed at capturing different blockchain instances, which have various stale block rates and confirmations. The authors stressed that a malicious user in this system would eventually succeed in case he/she executed double-spending simultaneously. |
| [58] | Bitcoin, Litecoin, and Dogecoin: Selfish mining attack. | MDP | The authors proposed a flexible model with flexible integration of different PoW blockchain instances. It was supported by a standalone security abstraction layer. The systems allowed executing various attacks, corresponding optimal execution strategies, and the impact on the operation. |
| [59] | Bitcoin: Selfish mining attack defense strategy. | MDP | The authors analyzed the current fork resolution issue and highlighted the need for its revision by introducing the fork-resolving policy based on weights. |
| [65] | Bitcoin: Double spending attack. | RW | The author proposed to analyze probabilistically the executability of the attack. The implementing block confirmation mechanism was considered as a significant potential improvement [67]. |
| [66] | Bitcoin: Double spending attack. | RW | The authors proposed the analysis of the different mining strategies’ profitabilities, in particular with the honest strategy. It was mentioned that difficulty adjustment during the attack should be considered in more detail when similar techniques are developed. |
| # | Tool | Type | Scalability | Main Application | Main Challenge |
|---|---|---|---|---|---|
| [28] | Blockbench | PU/PR | Low | First academia-driven framework allowing analyzing different blockchains, e.g, Ethereum, Parity, and Hyperledger Fabric. | The project is inactive. |
| [62] | BlockLite | PU | Low | An academia-driven work aimed to allow the emulation of the blockchain on a single node. | The project is inactive. |
| [79] | Corda Testing Tools | PR | High | Enterprise solution allowing evaluating Corda operation, as well as new DApps before the actual integration. | Limited to R3 Corda. |
| [74] | Ethereum Tester | PR | n/a | Ethereum-driven open-source library allowing testing DApps and smart contracts. | Designed specifically for Ethereum developers and lacks community support. |
| [80] | Exonum Testkit | PR | High | Private (enterprise) Exonum blockchain emulator. | Limited to Exonum. |
| [69] | Hyperledger Tools | PR | High | Community-driven private blockchain performance analysis toolbox supporting high tps and various implementations. | Extreme complexity of the development environment. |
| [76] | Truffle Suite | PR | High | Allows flexible development of Ethereum-based DApps and smart contracts’ operation with strong community support. | n/a |
| [71] | VIBES | PU | Medium | An academia-driven emulator developed for Bitcoin system analysis. An excellent educational example with detailed explanations of the system operation. | The project is inactive. |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Smetanin, S.; Ometov, A.; Komarov, M.; Masek, P.; Koucheryavy, Y. Blockchain Evaluation Approaches: State-of-the-Art and Future Perspective. Sensors 2020, 20, 3358. https://doi.org/10.3390/s20123358
Smetanin S, Ometov A, Komarov M, Masek P, Koucheryavy Y. Blockchain Evaluation Approaches: State-of-the-Art and Future Perspective. Sensors. 2020; 20(12):3358. https://doi.org/10.3390/s20123358
Chicago/Turabian StyleSmetanin, Sergey, Aleksandr Ometov, Mikhail Komarov, Pavel Masek, and Yevgeni Koucheryavy. 2020. "Blockchain Evaluation Approaches: State-of-the-Art and Future Perspective" Sensors 20, no. 12: 3358. https://doi.org/10.3390/s20123358
APA StyleSmetanin, S., Ometov, A., Komarov, M., Masek, P., & Koucheryavy, Y. (2020). Blockchain Evaluation Approaches: State-of-the-Art and Future Perspective. Sensors, 20(12), 3358. https://doi.org/10.3390/s20123358








