1. Introduction
Identification schemes are needed to provide identity of the communicating parties [
1]. In these schemes, there are two parties: prover and verifier. The prover wants to prove to the verifier that he/she is really the person who is communicating. The verifier asks questions to convince the prover’s commitment. The prover tries to convince the verifier without revealing his secret information. Identification schemes are the most important elements for many area, such as devices connected to the Internet. IoT is a popular technology that allows objects to identify and communicate with each other by connecting to Internet [
2]. IoT consists of billions of devices that can communicate, gather and share information, make a decision without human interaction. IoT provides the opportunities for devices to see, hear, think and talk with each other via Internet [
3]. According to Cisco predictions, there will be approximately 50 billion devices connected to the Internet by 2020 [
4]. In this respect, we can say that there is a big demand for IoT applications since IoT has a wide range of applications such as intelligent transportation systems, smart home and building automation, medical and health systems, industrial management, energy systems, environment and infrastructure monitoring [
5,
6,
7,
8]. For understanding of IoT applications, IoT systems need to be divided into small components in view of tasks [
2]. Thus, the first task of IoT systems is to identify and monitor the objects communicating with. The second task is to collect and process the information. In this structure, we have two main problems: identification and (secure) communication. Therefore, we focus on efficient and secure identification in IoT systems in this paper.
Identification is crucial to communicate among devices securely and properly. Radio-frequency identification technology (RFID) serves to identify objects automatically with electromagnetic frequency waves in IoT [
9]. An RFID system consists of two components: the RFID tag which collects the information and transmits the collected data to the application and the RFID reader which stores the information [
10]. Identification schemes used in RFID applications have some properties such as scalability, low memory requirement, communication and computational cost. In addition, an identification scheme has zero-knowledge property that does not allow an intruder verifier to hold communication [
11]. CryptoGPS protocols which are of standard designed commonly use RFID applications [
12,
13]. CryptoGPS is a public key identification scheme which uses modular explementation in a multiplication group or a scalar multiplication in an additive group. Recall that after the quantum computer idea had been introduced, a quantum computer with two qubits was build. Then, the number of qubits increased. Nowadays, we know that Google and D-wave have 72-qubit and 2048-qubit quantum computers, respectively [
14]. In addition, the systems whose security depends on integer factorization or discrete logarithm problems which are used in the identification schemes are called insecure due to Shor’s polynomial time algorithm in quantum computers [
15]. For this reason, there is a big demand to construct quantum secure identification schemes. There are many classes since there is no known polynomial time algorithm to solve multivariate polynomial in any computational area. The cryptosystems based on multivariate polynomials are used in quantum secure areas [
16,
17,
18].
In the literature, identification schemes based on multivariate quadratic polynomials as well as cubic ones have received interest since they are efficient for different platforms [
19,
20,
21]. In [
19], 3 and 5-pass zero-knowledge identification schemes based on multivariate quadratic
polynomials over a finite field were proposed. They defined bilinear functions as polar form of the
polynomial systems. In addition, they indicated whether or not it is able to build an efficient protocol using multivariate polynomials of degrees greater than two. In [
20], 3-pass zero-knowledge identification scheme-based multivariate quadratic polynomials over a finite field by using the same bilinear functions were presented. However, they used a different way to divide secret key. Then, in [
21], these identification schemes were improved in view of communication complexity by using new dividing techniques with the help of bilinearity of a polar form of the
function. Moreover, 3 and 5-pass identification schemes based on multivariate cubic
polynomials over finite field were proposed. A new associated linear-in-one argument form, i.e., polar form of
functions was defined and can be applied to a cubic version of the problem without changing bilinear form. The main difference between [
19] and [
21] is the degree of multivariate polynomial systems.
A different polar form is used with the same bilinear property. In [
22], identification schemes based on multivariate polynomials over a finite field in the literature were surveyed. 3 and 5-pass identification schemes based on multivariate quadratic and cubic polynomials were given with the dividing technique of the secret key and polar form construction. In addition, all identification schemes based on multivariate polynomials were compared in view of memory requirements, communication length, and computation time. In [
23], a new identification scheme based on multivariate quadratic polynomials was presented by using a different dividing technique of the secret key. Then, the proposed identification scheme was transformed to the signature scheme.
1.1. Motivation
In [
21], efficient constructions based on multivariate polynomials of degree
are given as an open problem (see
Section 2.1). The hardness of this problem comes from the nonlinear terms in
. In [
24], a solution with a different perspective was proposed for the open problem. They denoted a polarization identity for a system of multivariate polynomials of any degree
d. The function
is given as follows:
By Equation (
1), polar form of the system of multivariate polynomials in
linear form was obtained. They also generalized identification protocol for multivariate
degree polynomials with this perspective.
Variants of CryptoGPS are used in RFID applications. However, these protocols are not quantum secure. There is a need to construct identification schemes that are secure against quantum attacks.
1.2. Our Contribution
We propose a solution for the open problem with a different perspective. We generalize polar form for any degree of multivariate polynomials using bilinear functions. We define how the polar function will be when any degree of multivariate polynomials is used with Theorem 1. The idea comes from the bilinear functions used in both multivariate quadratic [
19,
20] and cubic [
21] polynomials over a finite field. We present a generic identification scheme based on any degree of multivariate polynomials. In addition, we provide a comparison for the cryptoGPS standard and identification schemes based on multivariate polynomials. The generic identification scheme framework can be used to construct identification scheme for RFID applications due to the zero-knowledge property.
1.3. Organization
The rest of this paper is organized as follows. In
Section 2, we give some definitions and then explain our solution proposal for the open problem. Moreover, we express our solution with examples and compare it to the other approach [
24] for the open problem. We give a generic scheme for identification construction when using any degree of multivariate polynomials. Then, we compare curve-based cryptoGPS and identification schemes based on multivariate polynomial. The conclusion and future works are stated in
Section 3.
2. A Novel Method for Polar Form of Multivariate Polynomials of Any Degree
In this section, we first review some definitions and notations. We recall the open problem given in [
24]. Then, we express our method for polar form of multivariate polynomials and give examples. We compare our solution and the other approach [
24].
2.1. Mathematical Background
Multivariate cryptography depends on solving systems of multivariate polynomials of degree
d over a finite field. For
or
, then it is called
or
, respectively. The system of multivariate polynomials of degree
d with
n variables and
m equations can be given as follows:
where the coefficients (
and
for
) are in a finite field. Note that the
problem, which is NP-complete, can be defined as follows:
Definition 1. [15] Given m multivariate quadratic polynomials as shown in Equation (
2)
, find a vector such that . The hardness of
problem depends on the hardness of solving nonlinear equations over finite field [
15]. In Definition 2, the polar form of the
function is given.
Definition 2. [19] Let , be multivariate quadratic function for and Then polar form of the function is . Definition 3. Let be a bilinear function. Then, G satisfies the following properties:
and
and
where , and a is a constant.
Remark 1. The function G in Definition 2 is bilinear since , where are dimension vectors. Because of the bilinearity of , , where and . Note that this is only valid for systems. It is difficult to control the terms in degree of elements because the number of terms increases when higher-order functions are used.
In Definition 4, polar form of function which is a natural extension of ones is given.
Definition 4. [21] Let and is the polar form of F for , and where are dimension vectors over . Moreover, G is a bilinear function and is obtained from Now, we recall the open problem given in [
21].
Open Problem. In [19,20,21], identification schemes based on multivariate quadratic and cubic polynomials were given. In [21], an open problem was defined: Is there any general method to construct polar form of multivariate polynomials of degree in an efficient way? By considering [
19,
20,
21], we have polar forms of multivariate quadratic and cubic polynomials. By using bilinear functions, polar forms of multivariate polynomials of degree of
can be obtained.
2.2. Another Look At Open Problem
Our aim is to generalize polar form for multivariate d-degree polynomials over a finite field. In Theorem 1, we introduce the generalization of linear-in-one-argument for the function of degree which is a modified construction derived from the and . Note that by recursive approach, one can obtain the linear form.
Theorem 1. Let be a finite field, and , be any degree of multivariate polynomial. Let be a permutation with elements which contains j times x and times y in any positions for a vector with i elements. Then, the generalization of linear-in-one-argument form for the function of degree is defined as , whereand Proof. Both Definition 2 and Definition 4 have the same structure in terms of the usage of the functions. In other words, is complement of in view of commutativity.
Our observation is that the polar form defined for the quadratic and cubic versions can be generalized for any degree of multivariate polynomial systems since and can be obtained by using this idea. We combine this observation with the complementary property of the function. The formula can be classified for any z by considering even or odd case. In this step, we have two cases:
When i is odd, it is obvious to compute and since the number of the outputs of the P permutation is odd and the number of x and y in the output of the P permutation is not equal.
When i is even, we need to consider whether the number of x vectors equals the number of y vectors. In this case, we need to take half of the existing terms to be complementary. For this reason, the even case is different from the odd case.
Then, the number of distinct elements in or is due to the Pascal triangle. To compute each part of or , distinct elements having two vectors (only x and y) up to d vectors ( times x and j times y) are computed. For case, the permutation P permutes the positions of x and y in the element. Note that some terms are complement the other, i.e., is complement of . This completes the proof. □
Now, we look at the following examples to compare our solution with the other approach [
24]. In Example 1, we apply Theorem 1 to multivariate cubic polynomials (
case) and show that this is the same in Definition 4.
Example 1 (bilinear polar form of degree 3)
. For , we haveBy using Theorem 1, and These and polynomials are same in [21] and in Definition 4. In Example 2, we compare bilinear polar form by using Theorem 1 with trilinear polar form given in [
24]. Since the idea is totally different, we have distinct polar forms.
Example 2 (trilinear polar form)
. When we use trilinear functions for , we haveAccording to [24], where and z are dimension vectors over a finite field and . From Examples 1 and 2, we see that fewer terms are needed to in the use of bilinear functions than trilinear ones. To compute , by using bilinear function four functions are needed to be computed. However, by using trilinear function one needs seven functions. Note that the bilinear polar form is simpler and more controllable.
In Example 3, we apply Theorem 1 to multivariate quartic polynomials ( case).
Example 3. Let . Then, multivariate quartic polynomials system F is in the following form: .
By using Theorem 1, the linear-in-one-argument form of F is: computed in Equation (
3)
is the complement of in view of variables given in Equation (
4)
, i.e., . In a similar manner, all permutation used in are selected as a complement of those used in . 2.3. Comparison
Now, we compare the proposed solution with
linear form in terms of the required number of the functions in
Table 1.
The number of partitions of
s secret key is constant in the proposed method because of the bilinearity. However, in [
24] it depends on the degree
d. The number of
F and
G functions to compute
in bilinear polar form is
, where
r is recursion number, whereas it is
for
linear form [
24]. When
is computed, one needs to calculate two
F functions. In addition, one must compute two
G polar form according to the proposed generalization form given in Theorem 1. Note that
r is the loop number required to obtain each
G polar form. For example, the secret key is divided into two parts as
x and
y. Then, we compute
by using polar form given in Definition 4. According to the proposed solution, the recursive construction is used for the calculation of
. Let
be the degree of multivariate polynomials. The recursion number is
since we run
function for
and
. Then,
function is obtained by adding quadratic terms.
is computed similarly. Actually, we use a divide-and-conquer approach for computing
and
function. The number of
F and
G functions is
by adding the number of
F functions. The number of
F and
G functions is the main factor to determine the computation time in the identification scheme based multivariate polynomial systems (for more details, see [
20]). Note that for efficiency reasons, the number of
F and
G functions should be as small as possible due to the arithmetic operations. Memory requirements in bilinear form and
linear form are
or
, respectively, where
m is bit size of the output of
F and
G functions.
2.4. A Generic Identification Scheme Based on Multivariate Polynomials
In this section, we present a generic scheme for identification construction based on any degree of multivariate polynomials. The identification schemes are compared with the cryptoGPS standard. A 3-pass identification scheme is given in
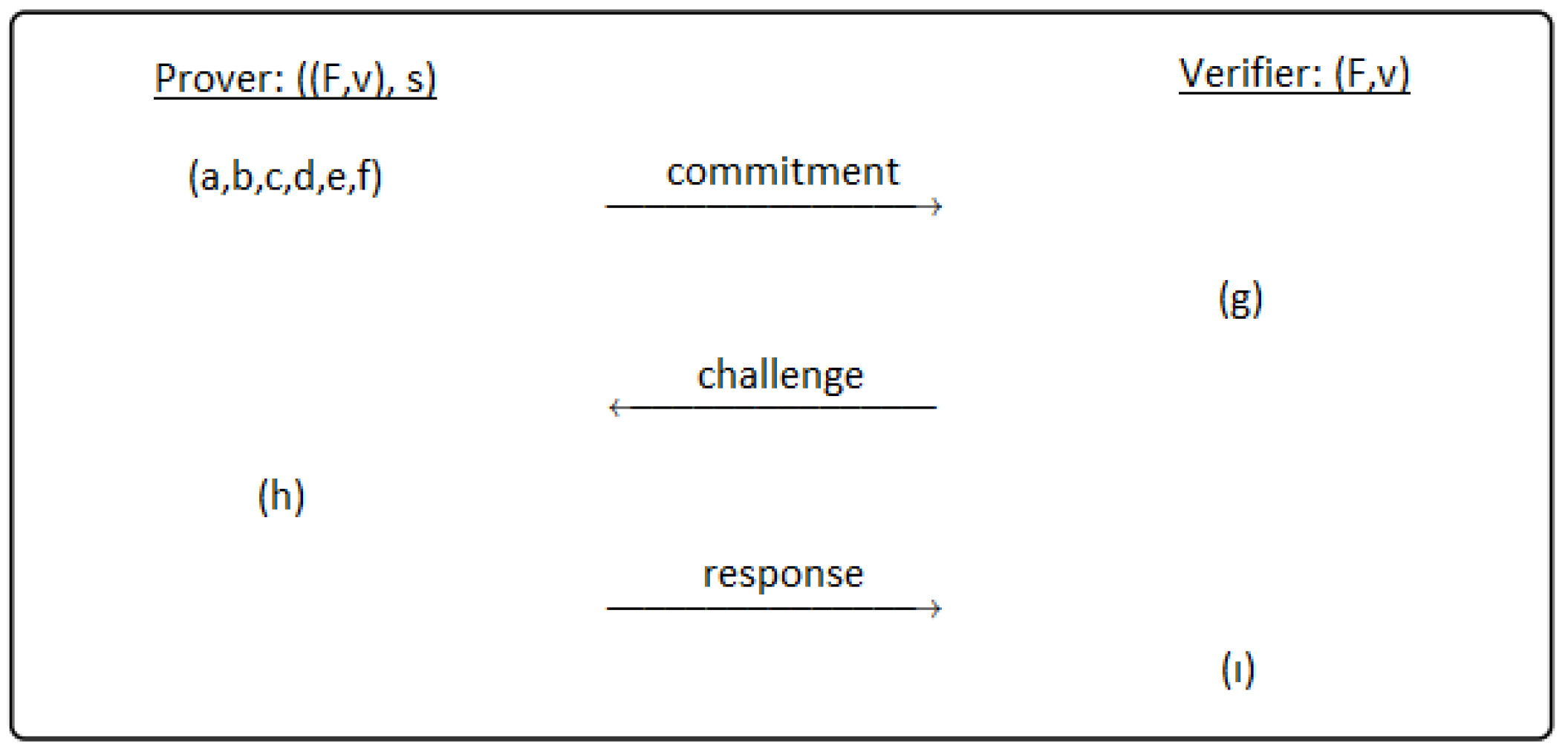
Figure 1.
A generic 3-pass identification scheme between prover and verifier has the following passes:
Commitment: The prover performs this pass.
- (a)
The multivariate polynomial system F is constructed with n variables and m equations.
- (b)
Choose randomly secret key and generate public key .
- (c)
Divide secret key s into parts and sub-parts. Generate randomly the parts of s, not all of them. For example; let s be divided into k parts. According to dividing technique, the sub-parts of the secret key like are generated randomly. Note that the secret key parts must be evaluated in F polynomial system. is satisfied with the help of polar form.
- (d)
Compute the parts of the secret key, not chosen randomly at step c. Thus, all parts of the secret key are obtained before the commitment phase.
- (e)
According to dividing technique and polar form, the commitment values are computed, where . The number of the commitment values is changeable according to the constructed scheme.
- (f)
In this step, the prover sends the commitment values. Thus, the prover commits the verifier. At the end of this step, the first pass of the identification scheme is completed.
Challenge: At the second phase, all operations are performed by the verifier.
- (g)
The verifier makes a challenge to the prover. For example; the verifier chooses a challenge value and sends to the prover.
Response: This phase is performed by the prover.
- (h)
The prover sends the responses which belong to each challenge in order that the verifier computes the commitment values.
At the end of the this step, the verifier carries out the following step and terminates the identification scheme as accepted or rejected.
- (i)
The verifier computes the commitment values after the verifier receives the responses. Then the verifier compares these commitment values with the values which sent as commitment by the prover. If they are equal, the verifier accepts the prover’s commitment. Otherwise, the verifier rejects. When the verifier computes the commitment values, the verifier can compute the same commitment value with different parts of the secret key unlike the prover. Note that the same values are obtained by using polar form.
Remark 2. A zero-knowledge identification scheme provides us to restrict information which is sent from the prover to the verifier. When the verifier has any limited and any useless information, he/she can prove the prover’s commitments. An identification scheme has to satisfy soundness and completeness properties for security and zero-knowledge. If an identification scheme is completed, i.e., the verifier accepts the prover’s commitment, the identification scheme has completeness property [25]. If the verifier can not be deceived by the intruding prover (except negligible probability ϵ > 0), the identification scheme has soundness property [25]. One of the important criteria for identification scheme is impersonation probability. It is defined as the probability that an adversary would impersonate the prover without knowing the secret key. The proposed generic scheme depends on the
dth degree multivariate polynomials. The key pair and communication length are calculated easily with only basic polynomial operations. However, curve-based cryptoGPS identification schemes, which commonly use IoT applications, require scalar-point multiplications. Note that we prove a generic identification scheme framework in
Section 2.4. Thus, we do not have numeric parameters for any security level. However, the comparison is provided by identification schemes based on multivariate quadratic or cubic polynomials presented in [
19,
21,
23] with curve-based cryptoGPS [
26]. In
Table 2, for 80-bit security level, the comparison is given by considering security attacks against quantum attacks, impersonation probability and parameter set including secret key, challenge and response sizes.
In
Table 2, challenge indicates the bit size of challenge which is determined so that the verifier can obtain all commitment values for identification schemes based on multivariate polynomials. When we compare the identification schemes for the size of response, identification schemes given in [
19,
21] have small values. The main reason of small key sizes is the bilinear polar form of multivariate polynomials of degree
. If the identification scheme based on multivariate polynomials is well-organized, it has lower cost than cryptoGPS. Thus, it can be used IoT applications efficiently.