LDAKM-EIoT: Lightweight Device Authentication and Key Management Mechanism for Edge-Based IoT Deployment
Abstract
1. Introduction
- The exchanged messages among different communicating parties (i.e., “IoT device”, “edge node”, and “cloud server”) should be protected against several known attacks (for example, “replay”, “man-in-the-middle”, “impersonation”, “offline or online password guessing”, and some other kinds of “bypassing attacks”).
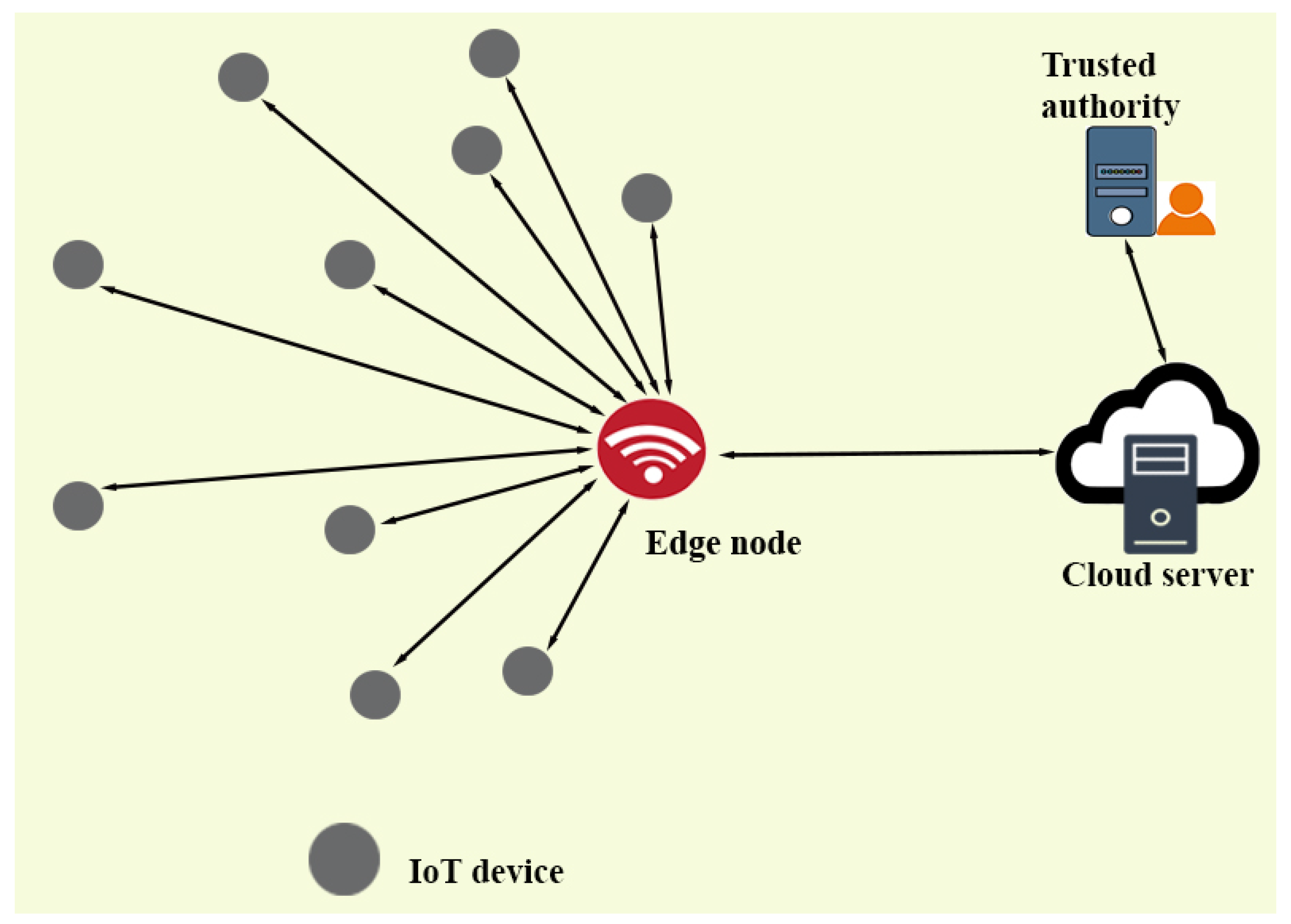
- The edge node receives and processes the data, which are sent by the IoT devices. After the required processing, the edge node sends the data to the cloud server(s) for further processing and storage. Sometimes, the sent data are very critical and important, and any kind of disclosure of the data creates big trouble. Therefore, we need strong secure privacy preservation techniques to protect the data in the edge based IoT environment.
- As existing authentication protocols have security flaws that make them vulnerable to some known attacks (for example, “privileged insider attack”, “online and offline password guessing”, etc.), consequently, it becomes important to enhance the security of the authentication protocols, for instance in the case of “new device addition or revocation”, other communicating parties of the network should also be informed by the concerned (trusted) authority so that they can become aware about this activity and can update their memories accordingly [1,4]. Hence, it is an exigent task to provide a design for such a kind of protocol that supports “dynamic installation/update” without compromising the security of the system [4].
- In the edge based IoT environment, there is a possibility that some IoT devices may be “physically stolen/captured” by the adversary . After the physical capturing, can use a “power analysis attack” [13] to obtain the data from the memory of the captured smart IoT devices. Later on, this drawn out information is used for other malicious works, such as deriving the “session key” among an IoT device and cloud server. can replace the physical captured device with his/her own malicious device(s) that he/she has cloned in the laboratory. We should be more careful while going for the design of authentication and key management techniques in case some IoT devices are physically compromised so that there should not be any affect on the security of communication happening in the rest of the network [1,4].
1.1. Contributions of LDAKM-EIoT
- We propose a new “lightweight authentication and key management” scheme for edge based IoT environment (LDAKM-EIoT). In LDAKM-EIoT, we use various efficient operations such as bitwise “exclusive-OR (XOR)” and “one way collision resistant cryptographic hash functions”.
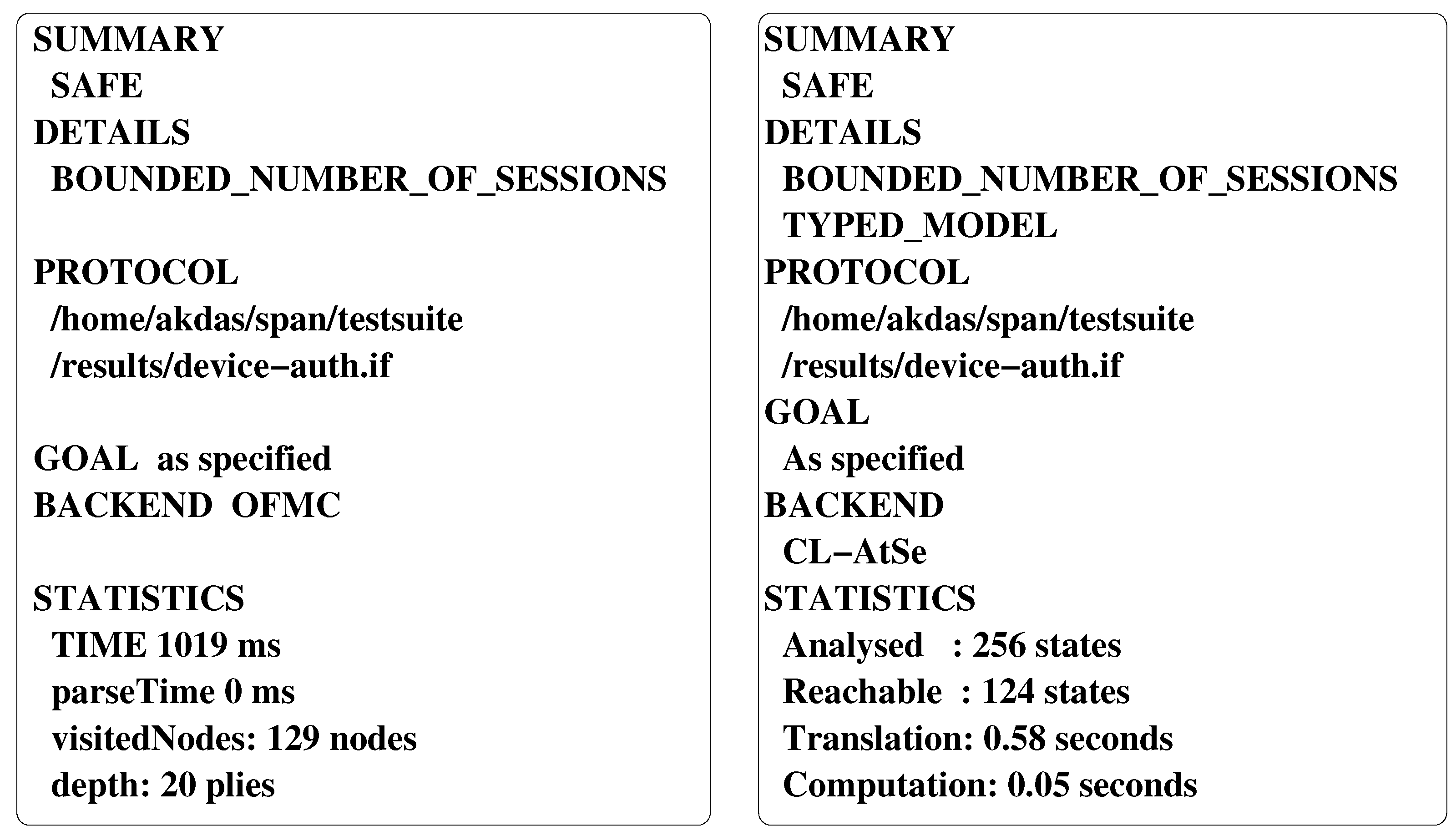
- LDAKM-EIoT is secure against different kinds of attacks by the help of “formal security verification” using the widely used AVISPA tool and also through other mathematical security analysis.
- The detailed comparative investigation among related existing schemes and LDAKM-EIoT evidences that LDAKM-EIoT achieves more security and additional functionality features and LDAKM-EIoT has also less communication and computation costs as compared to the other related schemes.
- The practical simulation study of LDAKM-EIoT is also executed with the help of the broadly used NS2 tool.
1.2. Paper Structure
2. Related Work
3. System Models
3.1. Network Model
3.2. Threat Model
4. The Proposed Scheme: LDAKM-EIoT
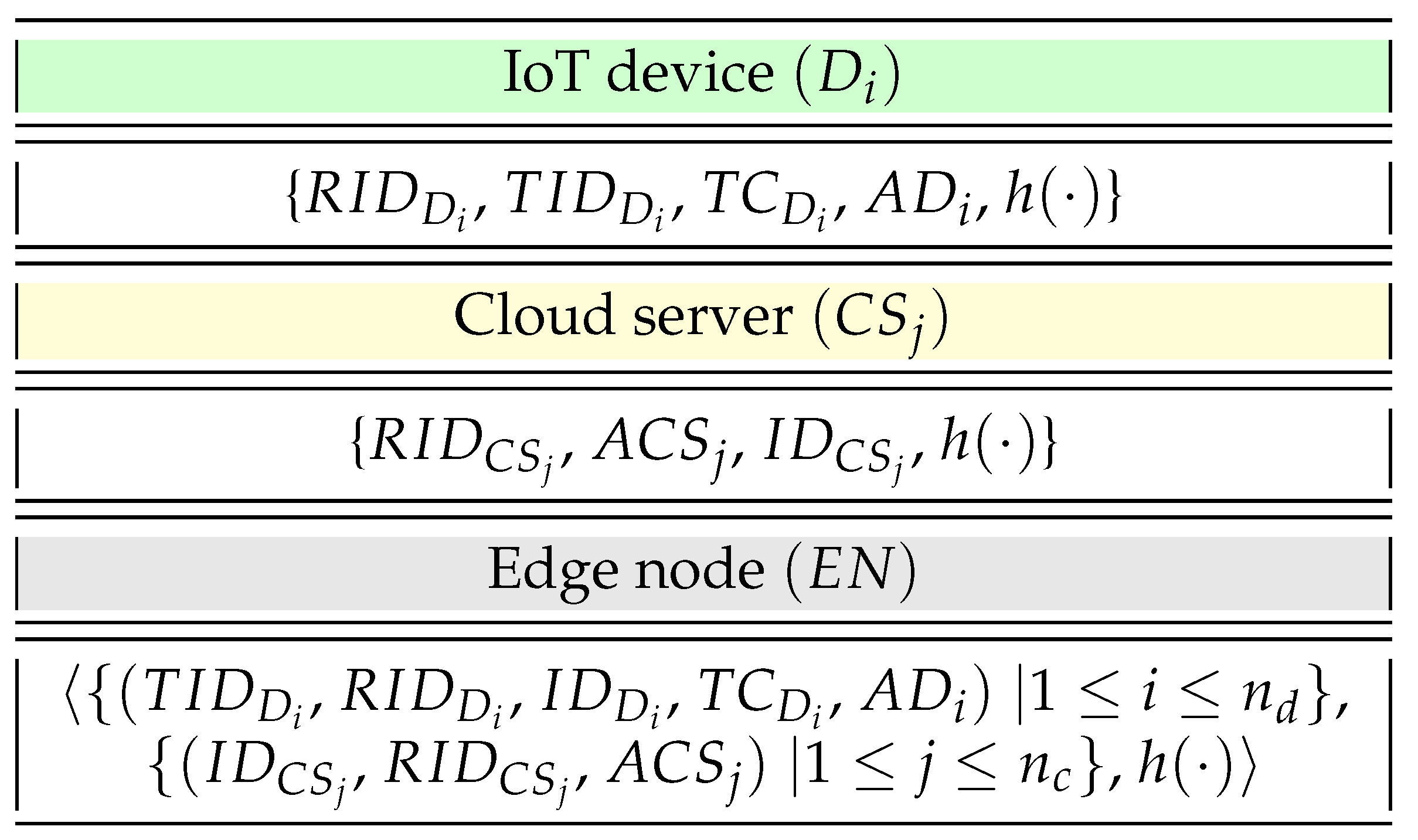
4.1. Pre-Deployment Phase
4.1.1. Registration of IoT Devices
4.1.2. Registration of Cloud Servers
4.1.3. Registration of Edge Node
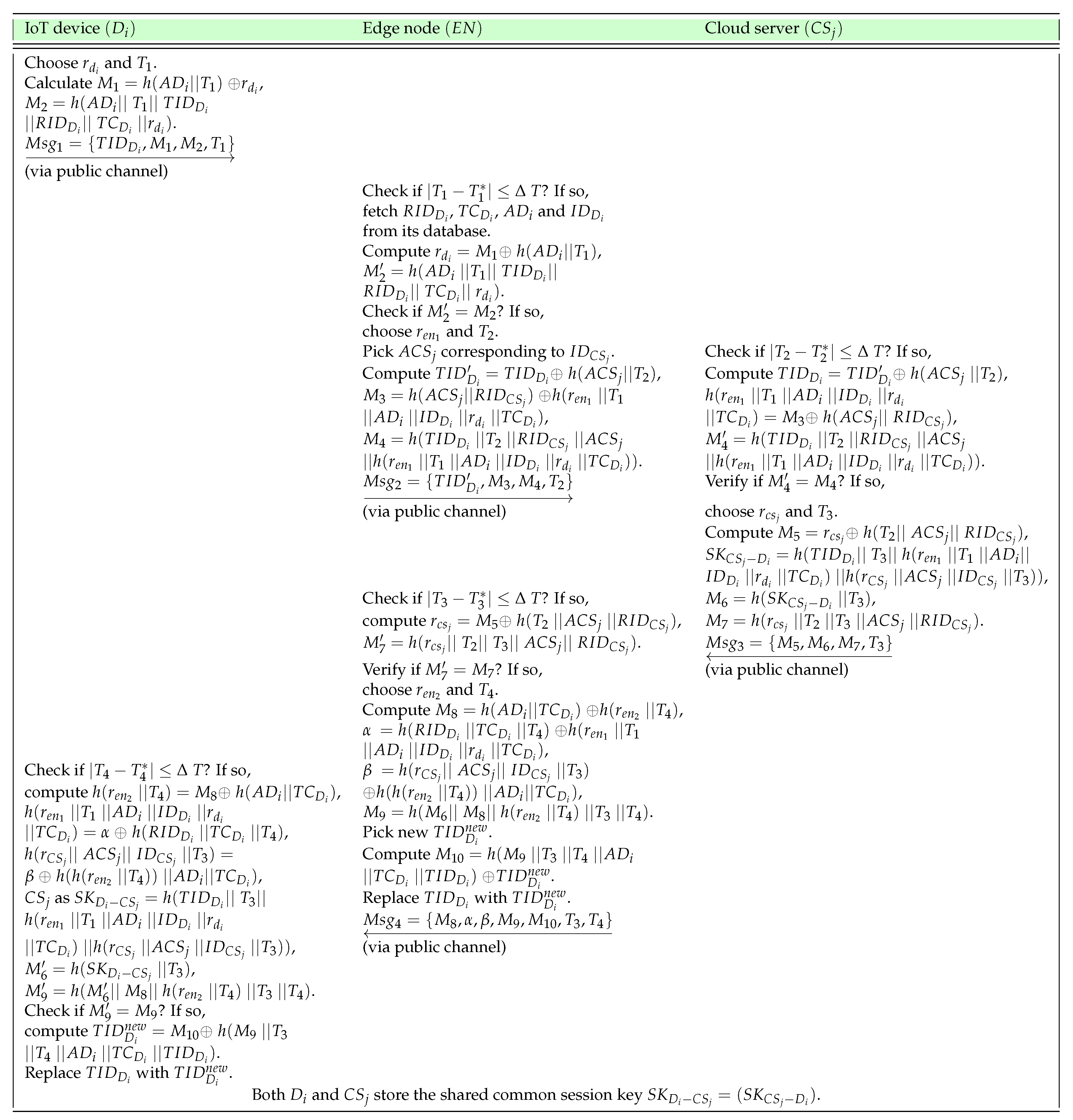
4.2. Authentication and Key Agreement Phase
- A1.
- When an IoT device, say , wants to initiate secure data transmission to a cloud server, first of all, needs to compute the following parameters. picks a random nonce and current timestamp and calculates and . Next, sends the message to the edge node via an open channel.
- A2.
- After the arrival of message at time , the checks the timeliness of with the verifying condition . If it is valid, the fetches , , , and corresponding to received and computes , and checks whether . If it is valid, is authenticated by the and can access its resources to get access to a cloud server selected by the . Next, the chooses a random nonce and current timestamp , picks from its database corresponding to , and computes , and . After that, the sends the message to via an open channel.
- A3.
- After the arrival of message at time , verifies the timeliness of by checking if is valid. After successful verification of , computes , and . After that, checks whether is satisfied. If it is valid, the is authenticated by . Otherwise, halts the session with the immediately. Furthermore, picks up a random nonce and current timestamp and computes . Then, computes the session key shared with as , , and . After computing these values, sends the message to the via an open channel.
- A4.
- After arrival of message at time , the verifies the timeliness of by checking if is valid. Upon successful validation of , the calculates and . Next, the checks whether , and if it holds, is authenticated by the . Otherwise, the halts the session with instantly. Furthermore, the selects a random nonce along with current timestamp and computes , , and . After computing these values, the picks a new temporary identity for and calculates . The also replaces with in its database. Finally, the sends the message to via an open channel.
- A5.
- After arrival of message at time , verifies the timeliness of by checking if is valid. After successful validation of , calculates , , , the shared session key with as . In addition, also calculates and . Then, checks whether , and if it is legitimate, the , as well as are authenticated by , and the computed session key is treated as the valid one. Thus, both and will maintain the same computed shared session key for secret communications. Moreover, calculates the new temporary identity as and will use this new identity in all its future communications with the and . It is worth noticing that the new temporary identity generation mechanism makes the proposed scheme prevent the traceability attack.
4.3. Dynamic Node Addition Phase
4.3.1. Dynamic IoT Device Addition
4.3.2. Dynamic Cloud Server Addition
5. Security Analysis of LDAKM-EIoT
6. Formal Security Verification Using AVISPA
7. Comparative Analysis with Existing Schemes
7.1. Comparative Study of Communication Costs
7.2. Comparative Study of Computation Costs
7.3. Comparative Study of Security and Functionality Attributes
8. NS2 Simulation Study
8.1. Simulation Parameters
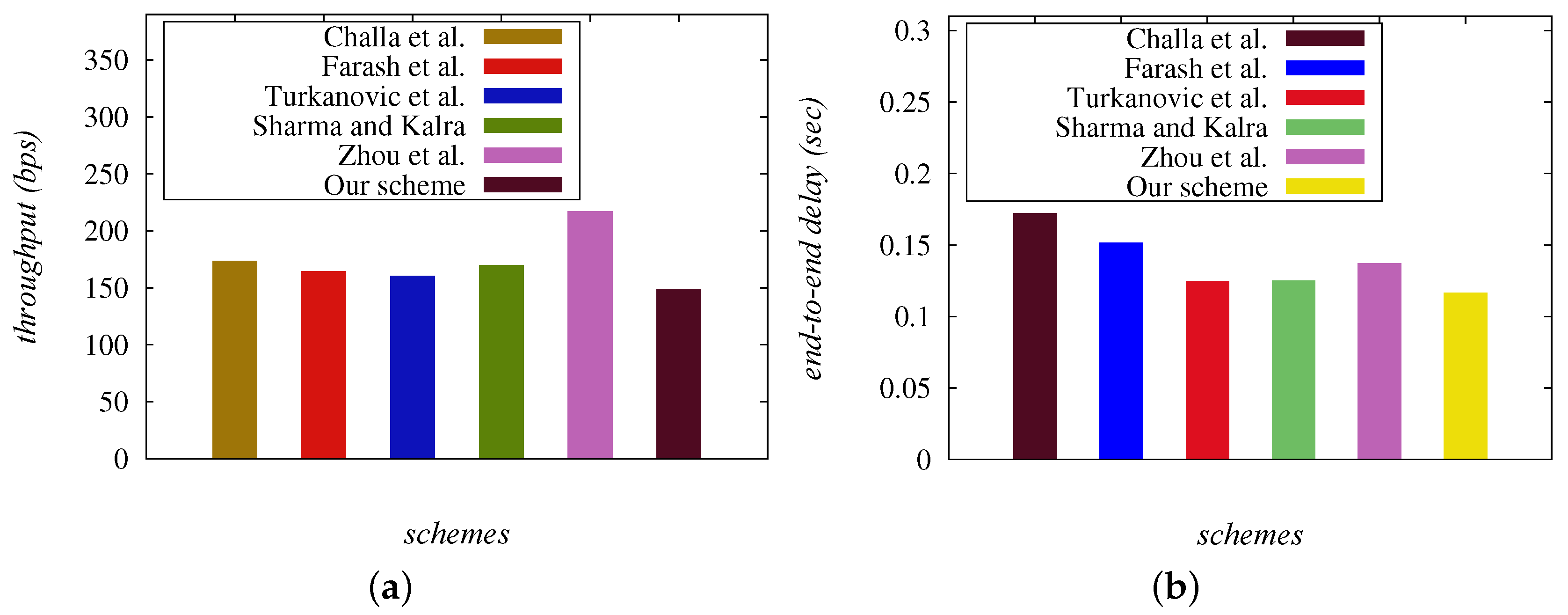
8.2. Comparative Analysis of the Simulation Results
8.2.1. Comparative Analysis of the Network Throughput
8.2.2. Comparative Analysis of the End-to-End Delay
9. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- Wazid, M.; Das, A.K.; Odelu, V.; Kumar, N.; Susilo, W. Secure Remote User Authenticated Key Establishment Protocol for Smart Home Environment. IEEE Trans. Dependable Secur. Comput. 2017. [Google Scholar] [CrossRef]
- Wazid, M.; Das, A.K.; Odelu, V.; Kumar, N.; Conti, M.; Jo, M. Design of Secure User Authenticated Key Management Protocol for Generic IoT Networks. IEEE Internet Things J. 2018, 5, 269–282. [Google Scholar] [CrossRef]
- Challa, S.; Wazid, M.; Das, A.K.; Kumar, N.; Reddy, A.G.; Yoon, E.; Yoo, K. Secure Signature-Based Authenticated Key Establishment Scheme for Future IoT Applications. IEEE Access 2017, 5, 3028–3043. [Google Scholar] [CrossRef]
- Wazid, M.; Das, A.K.; Hussain, R.; Succi, G.; Rodrigues, J.J. Authentication in cloud-driven IoT based big data environment: Survey and outlook. J. Syst. Archit. 2019, 97, 185–196. [Google Scholar] [CrossRef]
- Das, A.K.; Zeadally, S.; He, D. Taxonomy and analysis of security protocols for Internet of Things. Future Gener. Comput. Syst. 2018, 89, 110–125. [Google Scholar] [CrossRef]
- Zeadally, S.; Das, A.K.; Sklavos, N. Cryptographic technologies and protocol standards for Internet of Things. Internet Things 2019, 100075. [Google Scholar] [CrossRef]
- Glissa, G.; Meddeb, A. 6LowPSec: An end-to-end security protocol for 6LoWPAN. Ad Hoc Netw. 2019, 82, 100–112. [Google Scholar] [CrossRef]
- Makitalo, N.; Ometov, A.; Kannisto, J.; Andreev, S.; Koucheryavy, Y.; Mikkonen, T. Safe, Secure Executions at the Network Edge: Coordinating Cloud, Edge, and Fog Computing. IEEE Softw. 2018, 35, 30–37. [Google Scholar] [CrossRef]
- Yuan, J.; Li, X. A Reliable and Lightweight Trust Computing Mechanism for IoT Edge Devices Based on Multi-Source Feedback Information Fusion. IEEE Access 2018, 6, 23626–23638. [Google Scholar] [CrossRef]
- Khan, W.Z.; Ahmed, E.; Hakak, S.; Yaqoob, I.; Ahmed, A. Edge computing: A survey. Future Gener. Comput. Syst. 2019, 97, 219–235. [Google Scholar] [CrossRef]
- Esposito, C.; Castiglione, A.; Pop, F.; Choo, K.R. Challenges of Connecting Edge and Cloud Computing: A Security and Forensic Perspective. IEEE Cloud Comput. 2017, 4, 13–17. [Google Scholar] [CrossRef]
- Butler, B. What is Edge Computing and How It’s Changing the Network. Available online: https://www.cio.co.nz/article/627635/what-edge-computing-how-it-changing-network/ (accessed on 12 December 2019).
- Messerges, T.S.; Dabbish, E.A.; Sloan, R.H. Examining smart-card security under the threat of power analysis attacks. IEEE Trans. Comput. 2002, 51, 541–552. [Google Scholar] [CrossRef]
- Wolf, M.; Serpanos, D. Safety and Security in Cyber-Physical Systems and Internet-of-Things Systems. Proc. IEEE 2018, 106, 9–20. [Google Scholar] [CrossRef]
- Ni, J.; Zhang, K.; Lin, X.; Shen, X.S. Securing Fog Computing for Internet of Things Applications: Challenges and Solutions. IEEE Commun. Surv. Tutor. 2018, 20, 601–628. [Google Scholar] [CrossRef]
- Yeh, H.L.; Chen, T.H.; Liu, P.C.; Kim, T.H.; Wei, H.W. A secured authentication protocol for wireless sensor networks using elliptic curves cryptography. Sensors 2011, 11, 4767–4779. [Google Scholar] [CrossRef] [PubMed]
- Shi, W.; Gong, P. A new user authentication protocol for wireless sensor networks using elliptic curves cryptography. Int. J. Distrib. Sens. Netw. 2013, 2013, 730831. [Google Scholar] [CrossRef]
- Turkanovic, M.; Brumen, B.; Holbl, M. A novel user authentication and key agreement scheme for heterogeneous ad hoc wireless sensor networks, based on the Internet of Things notion. Ad Hoc Netw. 2014, 20, 96–112. [Google Scholar] [CrossRef]
- Amin, R.; Biswas, G.P. A secure light weight scheme for user authentication and key agreement in multi-gateway based wireless sensor networks. Ad Hoc Netw. 2016, 36, 58–80. [Google Scholar] [CrossRef]
- Khalil, N.; Abid, M.R.; Benhaddou, D.; Gerndt, M. Wireless sensors networks for Internet of Things. In Proceedings of the IEEE Ninth International Conference on Intelligent Sensors, Sensor Networks and Information Processing (ISSNIP), Singapore, 21–24 April 2014; pp. 1–6. [Google Scholar]
- Farash, M.S.; Turkanovic, M.; Kumari, S.; Holbl, M. An efficient user authentication and key agreement scheme for heterogeneous wireless sensor network tailored for the Internet of Things environment. Ad Hoc Netw. 2016, 36, 152–176. [Google Scholar] [CrossRef]
- Amin, R.; Islam, S.H.; Biswas, G.; Khan, M.K.; Leng, L.; Kumar, N. Design of an anonymity-preserving three-factor authenticated key exchange protocol for wireless sensor networks. Comput. Netw. 2016, 101, 42–62. [Google Scholar] [CrossRef]
- Srinivas, J.; Mukhopadhyay, S.; Mishra, D. Secure and efficient user authentication scheme for multi-gateway wireless sensor networks. Ad Hoc Netw. 2017, 54, 147–169. [Google Scholar] [CrossRef]
- Jiang, Q.; Zeadally, S.; Ma, J.; He, D. Lightweight Three-Factor Authentication and Key Agreement Protocol for Internet-Integrated Wireless Sensor Networks. IEEE Access 2017, 5, 3376–3392. [Google Scholar] [CrossRef]
- Hsieh, W.B.; Leu, J.S. A Robust User Authentication Scheme Using Dynamic Identity in Wireless Sensor Networks. Wirel. Pers. Commun. 2014, 77, 979–989. [Google Scholar] [CrossRef]
- Das, M.L. Two-factor user authentication in wireless sensor networks. IEEE Trans. Wirel. Commun. 2009, 8, 1086–1090. [Google Scholar] [CrossRef]
- Khan, M.K.; Alghathbar, K. Cryptanalysis and Security Improvements of ‘Two-Factor User Authentication in Wireless Sensor Networks’. Sensors 2010, 10, 2450–2459. [Google Scholar] [CrossRef]
- Vaidya, B.; Makrakis, D.; Mouftah, H.T. Improved Two-Factor User Authentication in Wireless Sensor Networks. In Proceedings of the Second International Workshop on Network Assurance and Security Services in Ubiquitous Environments (NASSUE’10), Niagara Falls, ON, Canada, 12 October 2010; pp. 600–606. [Google Scholar]
- Wu, F.; Xu, L.; Kumari, S.; Li, X. A privacy-preserving and provable user authentication scheme for wireless sensor networks based on Internet of Things security. J. Ambient Intell. Hum. Comput. 2017, 8, 101–116. [Google Scholar] [CrossRef]
- Li, N.; Liu, D.; Nepal, S. Lightweight Mutual Authentication for IoT and Its Applications. IEEE Trans. Sustain. Comput. 2017, 2, 359–370. [Google Scholar] [CrossRef]
- Santos, M.L.B.A.; Carneiro, J.C.; Franco, A.M.R.; Teixeira, F.A.; Henriques, M.A.A.; Oliveira, L.B. A Federated Lightweight Authentication Protocol for the Internet of Things. arXiv 2019, arXiv:1907.05527. [Google Scholar]
- Gope, P.; Sikdar, B. Lightweight and Privacy-Preserving Two-Factor Authentication Scheme for IoT Devices. IEEE Internet Things J. 2019, 6, 580–589. [Google Scholar] [CrossRef]
- Dodis, Y.; Reyzin, L.; Smith, A. Fuzzy extractors: How to generate strong keys from biometrics and other noisy data. In Proceedings of the Advances in Cryptology (Eurocrypt’04), Interlaken, Switzerland, 2–6 May 2004; Volume 3027, pp. 523–540. [Google Scholar]
- Han, J.; Kim, J. A lightweight authentication mechanism between IoT devices. In Proceedings of the International Conference on Information and Communication Technology Convergence (ICTC’17), Jeju Island, Korea, 15–17 October 2017; pp. 1153–1155. [Google Scholar]
- Kung, Y.; Hsiao, H. GroupIt: Lightweight Group Key Management for Dynamic IoT Environments. IEEE Internet Things J. 2018, 5, 5155–5165. [Google Scholar] [CrossRef]
- Raza, S.; Magnusson, R.M. TinyIKE: Lightweight IKEv2 for Internet of Things. IEEE Internet Things J. 2019, 6, 856–866. [Google Scholar] [CrossRef]
- Jia, X.; He, D.; Li, L.; Choo, K.K.R. Signature based three-factor authenticated key exchange for Internet of Things applications. Multimed. Tools Appl. 2018, 77, 18355–18382. [Google Scholar] [CrossRef]
- Malani, S.; Srinivas, J.; Das, A.K.; Srinathan, K.; Jo, M. Certificate-Based Anonymous Device Access Control Scheme for IoT Environment. IEEE Internet Things J. 2019. [Google Scholar] [CrossRef]
- Sharma, G.; Kalra, S. A Lightweight User Authentication Scheme for Cloud-IoT Based Healthcare Services. Iran. J. Sci. Technol. Trans. Electr. Eng. 2019, 43, 619–636. [Google Scholar] [CrossRef]
- Canetti, R.; Krawczyk, H. Universally Composable Notions of Key Exchange and Secure Channels. In Advances in Cryptology—EUROCRYPT; Knudsen, L.R., Ed.; Springer: Berlin/Heidelberg, Germany, 2002; pp. 337–351. [Google Scholar]
- Zhou, L.; Li, X.; Yeh, K.H.; Su, C.; Chiu, W. Lightweight IoT based authentication scheme in cloud computing circumstance. Future Gener. Comput. Syst. 2019, 91, 244–251. [Google Scholar] [CrossRef]
- Martinez-Pelaez, R.; Toral-Cruz, H.; Parra-Michel, J.R.; Garcia, V.; Mena, L.J.; Felix, V.G.; Ochoa-Brust, A. An Enhanced Lightweight IoT based Authentication Scheme in Cloud Computing Circumstances. Sensors 2019, 19, 2098. [Google Scholar] [CrossRef]
- Dolev, D.; Yao, A. On the security of public key protocols. IEEE Trans. Inf. Theory 1983, 29, 198–208. [Google Scholar] [CrossRef]
- Kumar, P.; Gurtov, A.; Iinatti, J.; Ylianttila, M.; Sain, M. Lightweight and Secure Session-Key Establishment Scheme in Smart Home Environments. IEEE Sens. J. 2016, 16, 254–264. [Google Scholar] [CrossRef]
- Bertino, E.; Shang, N.; Wagstaff, S.S., Jr. An Efficient Time-Bound Hierarchical Key Management Scheme for Secure Broadcasting. IEEE Trans. Dependable Secur. Comput. 2008, 5, 65–70. [Google Scholar] [CrossRef]
- Das, A.K.; Wazid, M.; Kumar, N.; Vasilakos, A.V.; Rodrigues, J.J.P.C. Biometrics-Based Privacy-Preserving User Authentication Scheme for Cloud-Based Industrial Internet of Things Deployment. IEEE Internet Things J. 2018, 5, 4900–4913. [Google Scholar] [CrossRef]
- Chang, C.C.; Le, H.D. A provably secure, efficient, and flexible authentication scheme for ad hoc wireless sensor networks. IEEE Trans. Wirel. Commun. 2016, 15, 357–366. [Google Scholar] [CrossRef]
- Wazid, M.; Das, A.K.; Kumar, N.; Vasilakos, A.V.; Rodrigues, J.J.P.C. Design and Analysis of Secure Lightweight Remote User Authentication and Key Agreement Scheme in Internet of Drones Deployment. IEEE Internet Things J. 2019, 6, 3572–3584. [Google Scholar] [CrossRef]
- Gope, P.; Lee, J.; Quek, T.Q.S. Resilience of DoS Attacks in Designing Anonymous User Authentication Protocol for Wireless Sensor Networks. IEEE Sens. J. 2017, 17, 498–503. [Google Scholar] [CrossRef]
- Das, A.K.; Sharma, P.; Chatterjee, S.; Sing, J.K. A dynamic password based user authentication scheme for hierarchical wireless sensor networks. J. Netw. Comput. Appl. 2012, 35, 1646–1656. [Google Scholar] [CrossRef]
- Kumari, S.; Das, A.K.; Wazid, M.; Li, X.; Wu, F.; Choo, K.K.R.; Khan, M.K. On the design of a secure user authentication and key agreement scheme for wireless sensor networks. Concurr. Comput. Pract. Exp. 2017, 29, 1–24. [Google Scholar] [CrossRef]
- Armando, A.; Basin, D.; Boichut, Y.; Chevalier, Y.; Compagna, L.; Cuéllar, J.; Drielsma, H.P.; Heám, P.C.; Kouchnarenko, O.; Mantovani, J.; et al. Automated validation of Internet security protocols and applications. Notes Comput. Sci. 2005, 3576, 281–285. [Google Scholar]
- Wazid, M.; Das, A.K.; Kumar, N.; Odelu, V.; Reddy, A.G.; Park, K.; Park, Y. Design of Lightweight Authentication and Key Agreement Protocol for Vehicular Ad Hoc Networks. IEEE Access 2017, 5, 14966–14980. [Google Scholar] [CrossRef]
- SPAN, the Security Protocol ANimator for AVISPA. Available online: http://people.irisa.fr/Thomas.Genet/span (accessed on 12 December 2019).
- Secure Hash Standard. FIPS PUB 180-1. National Institute of Standards and Technology (NIST), U.S. Department of Commerce, April 1995. Available online: http://nvlpubs.nist.gov/nistpubs/FIPS/NIST.FIPS.180-4.pdf (accessed on 19 January 2019).
- Vanstone, S. Responses to NIST’s proposal. Commun. ACM 1992, 35, 50–52. [Google Scholar]
- Odelu, V.; Das, A.K.; Goswami, A. An efficient biometric based privacy-preserving three-party authentication with key agreement protocol using smart cards. Secur. Commun. Netw. 2015, 8, 4136–4156. [Google Scholar] [CrossRef]
- Perkins, C.E.; Royer, E.M. Ad-hoc on-demand distance vector routing. In Proceedings of the Second IEEE Workshop on Mobile Computing Systems and Applications (WMCSA’99), New Orleans, LA, USA, 25–26 February 1999; pp. 90–100. [Google Scholar]
| Symbol | Meaning |
|---|---|
| , | ith IoT device and its identity, respectively |
| , | jth cloud server and its identity, respectively |
| , | Edge node and its identity, respectively |
| , | Trusted authority and its identity, respectively |
| , | Pseudo identities of and , respectively |
| Temporary identity of | |
| 1024 bit shared secret key of the IoT device and edge node generated by | |
| 1024 bit shared secret key of the edge node and cloud server generated by | |
| n | 160 bit secret secret of , which is only known to . |
| Registration timestamp of | |
| Number of IoT devices and cloud servers deployed initially, respectively | |
| , , , | 128 bit random numbers of , , and , respectively |
| Current timestamps generated by different entities | |
| “Maximum transmission delay” associated with a message | |
| “Collision resistant cryptographic one way hash function” | |
| Session key between and | |
| , ⊕ | Concatenation and bitwise operations, respectively |
| Protocol | No. of Messages | No. of Bits |
|---|---|---|
| LDAKM-EIoT | 4 | 2400 |
| Challa et al. [3] | 3 | 2528 |
| Farash et al. [21] | 4 | 2752 |
| Sharma and Kalra [39] | 4 | 2912 |
| Zhou et al. [41] | 4 | 3840 |
| Turkanovic et al. [18] | 4 | 2720 |
| Scheme | User/Smart | Gateway Node/ | Sensing Device | Total Cost |
|---|---|---|---|---|
| IoT Device | Edge Node | /Cloud Server | ||
| LDAKM-EIoT | ||||
| ms | ms | ms | ms | |
| Challa et al. [3] | ||||
| ms | ms | ms | ||
| Farash et al. [21] | ||||
| ms | ms | ms | ms | |
| Sharma and Kalra [39] | ||||
| ms | ms | ms | ms | |
| Zhou et al. [41] | ||||
| ms | ms | ms | ms | |
| Turkanovic et al. [18] | ||||
| ms | ms | ms | ms |
| Feature | Farash | Challa | Turkanovic | Sharma and | Zhou | LDAKM-EIoT |
|---|---|---|---|---|---|---|
| et al. [21] | et al. [3] | et al. [18] | Kalra [39] | et al. [41] | ||
| × | ✓ | ✓ | × | ✓ | ✓ | |
| × | ✓ | × | × | × | ✓ | |
| × | ✓ | × | × | ✓ | ✓ | |
| × | ✓ | × | × | ✓ | NA | |
| ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | |
| × | ✓ | × | ✓ | × | NA | |
| ✓ | ✓ | ✓ | ✓ | × | ✓ | |
| ✓ | ✓ | ✓ | ✓ | × | ✓ | |
| ✓ | ✓ | ✓ | ✓ | × | ✓ | |
| ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | |
| ✓ | × | × | ✓ | ✓ | ✓ | |
| ✓ | ✓ | ✓ | ✓ | NA | ✓ | |
| ✓ | ✓ | ✓ | ✓ | × | NA | |
| ✓ | × | ✓ | ✓ | NA | ✓ | |
| NA | ✓ | × | × | × | NA | |
| ✓ | ✓ | × | ✓ | ✓ | ✓ | |
| × | ✓ | × | × | × | NA | |
| × | ✓ | ✓ | × | × | ✓ |
| Parameter | Description |
|---|---|
| Platform | Ubuntu 14.04 LTS |
| Tool used | NS2 2.35 |
| Number of gateway nodes/edge nodes | 1 |
| (whenever applicable) | |
| Number of users or IoT device | 9 |
| (whenever applicable) | |
| Number of sensors or cloud server | 10 |
| (whenever applicable) | |
| Simulation time | 1800 s |
| Communication range of sensors/IoT devices | 100 m |
| Routing protocol | AODV [58] |
| Exchanged Messages between Network Entities | Challa | Farash | Turkanovic | Sharma | Zhou | LDAKM-EIoT |
|---|---|---|---|---|---|---|
| et al. [3] | et al. [21] | et al. [18] | and Kalra [39] | et al. [41] | ||
| 992 bits | 512 bits | 672 bits | 672 bits | 800 bits | 512 bits | |
| / | 1024 bits | 1024 bits | 1024 bits | 1024 bits | 1600 bits | 512 bits |
| / | − | 672 bits | 576 bits | 672 bits | 960 bits | 512 bits |
| − | 544 bits | 448 bits | 544 bits | 480 bits | 864 bits | |
| / | 512 bits | − | − | − | − | − |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Wazid, M.; Das, A.K.; Shetty, S.; J. P. C. Rodrigues, J.; Park, Y. LDAKM-EIoT: Lightweight Device Authentication and Key Management Mechanism for Edge-Based IoT Deployment. Sensors 2019, 19, 5539. https://doi.org/10.3390/s19245539
Wazid M, Das AK, Shetty S, J. P. C. Rodrigues J, Park Y. LDAKM-EIoT: Lightweight Device Authentication and Key Management Mechanism for Edge-Based IoT Deployment. Sensors. 2019; 19(24):5539. https://doi.org/10.3390/s19245539
Chicago/Turabian StyleWazid, Mohammad, Ashok Kumar Das, Sachin Shetty, Joel J. P. C. Rodrigues, and Youngho Park. 2019. "LDAKM-EIoT: Lightweight Device Authentication and Key Management Mechanism for Edge-Based IoT Deployment" Sensors 19, no. 24: 5539. https://doi.org/10.3390/s19245539
APA StyleWazid, M., Das, A. K., Shetty, S., J. P. C. Rodrigues, J., & Park, Y. (2019). LDAKM-EIoT: Lightweight Device Authentication and Key Management Mechanism for Edge-Based IoT Deployment. Sensors, 19(24), 5539. https://doi.org/10.3390/s19245539








