A Hash-Based RFID Authentication Mechanism for Context-Aware Management in IoT-Based Multimedia Systems
Abstract
1. Introduction
2. System Models
2.1. System Communication Model
2.2. Research Motivation
2.3. Enabling Technologies and Its Key Objectives
3. Context-Aware Sensor Management Systems
4. Novel Hash-Based RFID Mutual Authentication Protocol
4.1. Phase I: Pre-Phase Registration
- (1)
- The back-end database server and the tag mutually share their credentials, such as Tag- in the pre-phase registration of the proposed mechanism.
- (2)
- The reader and tag have a unique random number generator to authenticate the services like role assignment. For each tag, the back-end database server collects the parameters, namely and assign the values.
- (3)
- is the secret-session key of the current session tag .
- (4)
- is the secret-session key of the previous session tag , since its initial value is set to null.
- (5)
- Information of the object/role that is tagged to the back-end database server to assign the access privileges.
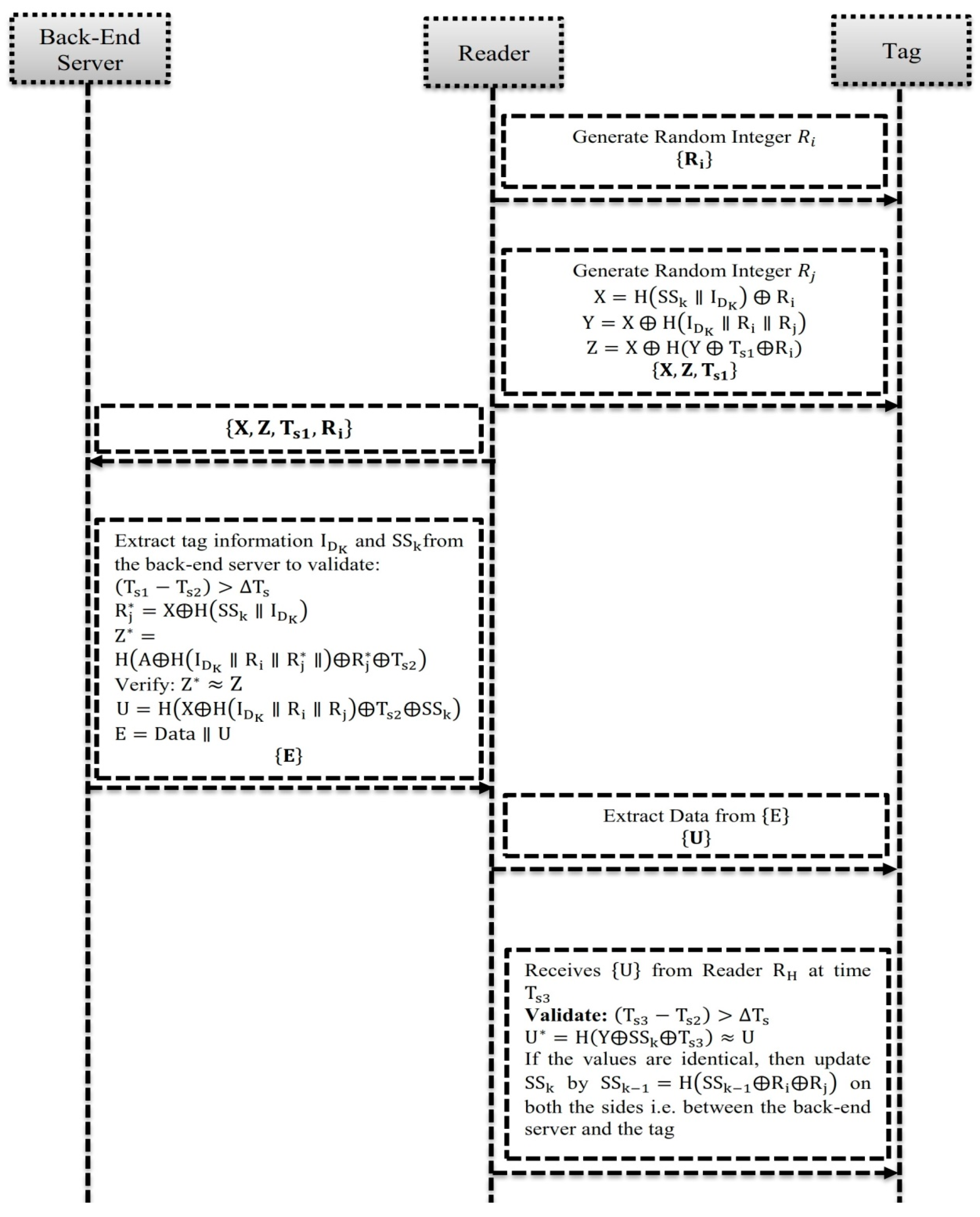
4.2. Phase II: Readers Pro-Tag Request and Response
- (1)
- The reader randomly selects an integer to send a request to the tag.
- (2)
- Then, the tag generates a random integer to compute: ; ; and , where is the current timestamp of the tag.
- (3)
- After the computation of , the tag sends its response message as to the reader.
- (4)
- After receiving the response message from the reader, the reader sends the message of response to the back-end server, after being added to the computational integer of .
4.3. Phase III: Tag Mutual Session-Key Authentication
- (1)
- If , then the back-end server terminates the login request of the user, where is the current timestamp in the remote-server and is the expected transmission delay.
- (2)
- Compute:
- (3)
- Validate:
- (4)
- Repeat the execution steps (1) and (5) till the value of is equal to from the response message of reader. If the values are equaled, then the right tag will be found.
- (5)
- Compute:
- (1)
- The back-end server forms a new message format as , where is the information of the tag to be communicated to the reader to ensure the property of mutual authenticity. If the back-end server fails to deduce a valid right tag, then the server deduces that there is an invalid message authentication to terminate the user session. After the execution of new message , the reader executes the following steps to maintain the communication:
- (2)
- The back-end server sends the new message of to the reader.
- (3)
- Upon receiving the new message of from the back-end server, the reader excludes the parameter of and sends the parameter of to the tag to maintain the communication.
4.4. Phase IV: Back-End Server Key Authentication and Session-Key Updation
- (1)
- If , then the tag terminates the login request of the user, where is the current timestamp in the tag and is the expected transmission delay.
- (2)
- Compute: , if the condition is valid, then the tag authenticates the back-end server to confirm that the computed hash value is identical to incur the value of from the reader.
5. Security and Efficiency Analysis
5.1. BAN Logic Analysis
- (1)
- (2)
- (3)
- (4)
- , where
- (5)
- , where
- (1)
- (2)
- (3)
- , ,
- (4)
- ,
- (a)
- ,
- (b)
- ,
- (c)
5.2. Informal Analysis
5.3. Performance Analysis
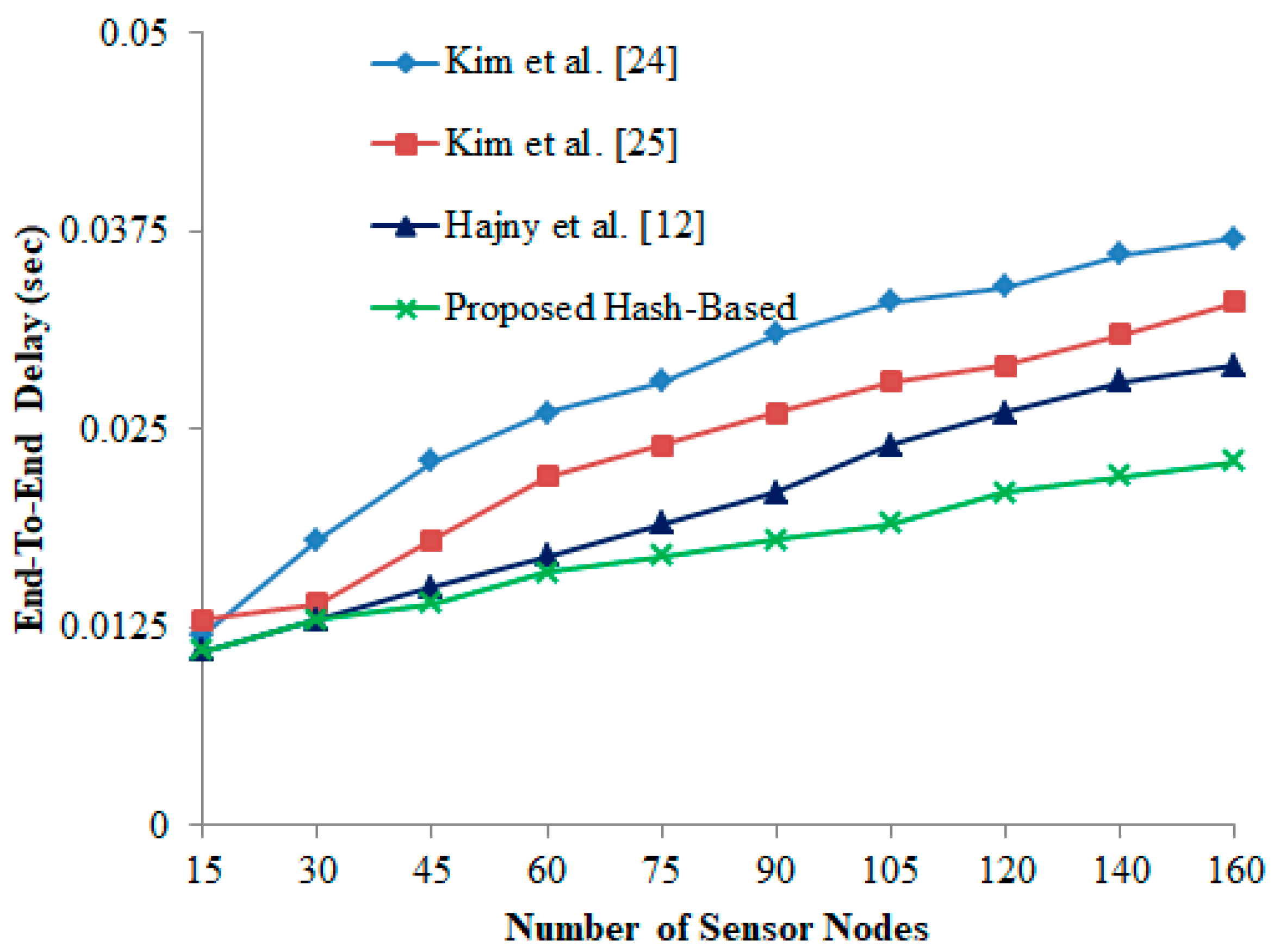
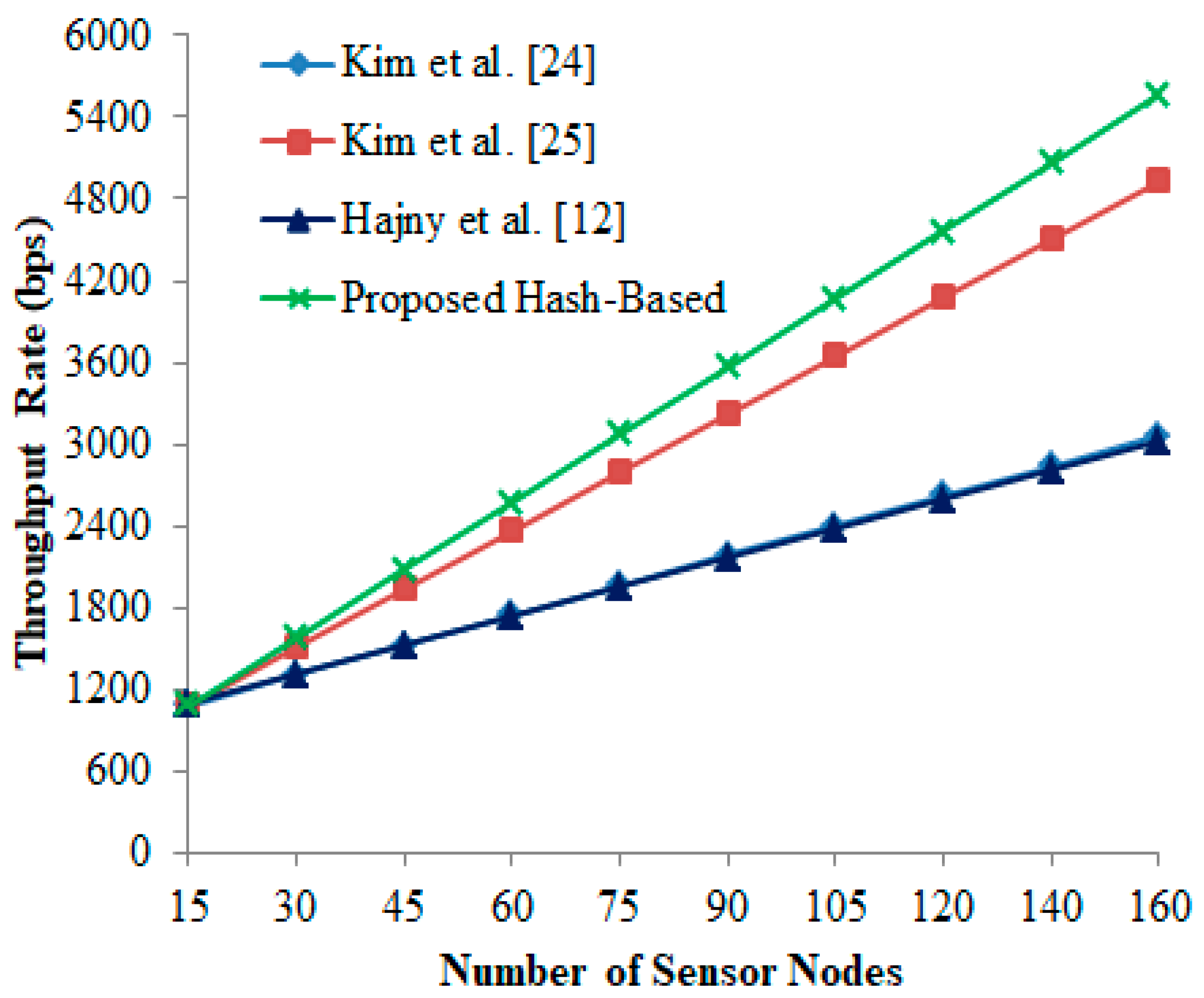
6. Experimental Study
6.1. Packet Delivery (PR) Ratio
6.2. End-To-End (E2E) Delay
6.3. Throughput Rate (TR)
7. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- El-Hajj, M.; Chamoun, M.; Fadlallah, A.; Serhrouchni, A. Analysis of authentication techniques in Internet of Things (IoT). In Proceedings of the 2017 1st Cyber Security in Networking Conference (CSNet), Rio de Janeiro, Brazil, 18–20 October 2017; pp. 1–3. [Google Scholar]
- El-hajj, M.; Chamoun, M.; Fadlallah, A.; Serhrouchni, A. Taxonomy of authentication techniques in Internet of Things (IoT). In Proceedings of the 2017 IEEE 15th Student Conference on Research and Development (SCOReD), Putrajaya, Malaysia, 13–14 December 2017; pp. 67–71. [Google Scholar]
- Al-Turjman, F.; Malekoo, A. Smart Parking in IoT-enabled Cities: A Survey. Sustain. Cities Soc. 2019, 49, 101608. [Google Scholar] [CrossRef]
- Campioni, F.; Choudhury, S.; Al-Turjman, F. Scheduling RFID Networks in the IoT and Smart Health Era. J. Ambient Intell. Hum. Comput. 2019. [Google Scholar] [CrossRef]
- Smartphone Usage Global Stats. Available online: https://www.emarketer.com/Article/Mobile-PhoneSmartphone-Usage-Varies-Globally/1014738 (accessed on 1 April 2018).
- Xu, W. Mobile applications based on smart wearable devices. In Proceedings of the 13th ACM Conference on Embedded Networked Sensor Systems, Seoul, Korea, 1–4 November 2015; pp. 505–506. [Google Scholar]
- NIST. Federal information processing standards publication (FIPS 197). In Advanced Encryption Standard (AES); NIST: Gaithersburg, MD, USA, 2001. [Google Scholar]
- Vera, S.D.; Bayo, A.; Medrano, N.; Calvo, B.; Celma, S. A Programmable Plug & Play Sensor Interface for WSN Applications. Sensors 2011, 11, 9009–9032. [Google Scholar] [PubMed]
- Hussain, S.A.; Gurkan, D. Management and Plug and Play of Sensor Networks Using SNMP. IEEE Trans. Instrum. Meas. 2011, 60, 1830–1837. [Google Scholar] [CrossRef]
- Spiekermann, S.; Evdokimov, S. Critical RFID privacy-enhancing technologies. IEEE Secur. Privacy 2009, 7, 56–62. [Google Scholar] [CrossRef]
- Higuera, J.; Polo, J.; Gasulla, M. A ZigBee wireless sensor network compliant with the IEEE1451 standard. In Proceedings of the 2009 IEEE Sensors Applications Symposium, New Orleans, LA, USA, 17–19 February 2009. [Google Scholar]
- Hajny, J.; Dzurenda, P.; Malina, L. Multidevice Authentication with Strong Privacy Protection. Wirel. Commun. Mob. Comput. 2018. [Google Scholar] [CrossRef]
- Song, E.Y.; Lee, K. Understanding IEEE 1451-Networked smart transducer interface standard-What is a smart transducer? IEEE Instru Meas Mag 2008, 11, 11–17. [Google Scholar] [CrossRef]
- 1451.7-IEEE Standard for a Smart Transducer Interface for Sensors and Actuators—Transducers to Radio Frequency Identification (RFID) Systems Communication Protocols and Transducer Electronic Data Sheet Formats; IEEE: Piscataway, NJ, USA, 2010; pp. 1–87.
- ISO/IEC Std FDIS 24753:2010. Information Technology—Radio Frequency Identification (RFID) for Item Management—Application Protocol: Encoding and Processing Rules for Sensors and Batteries; ISO: Geneva, Switzerland, 2010; pp. 1–72. [Google Scholar]
- Finkenzeller, K. RFID Handbook, 2nd ed.; Wiley & Sons: Hoboken, NJ, USA, 2002. [Google Scholar]
- EPC Radio-Frequency Identity Protocols Class-1 Generation-2 UHF RFID Protocol for Communications at 860 MHz–960 MHz Version 1.2.0. Available online: https://www.gs1.org/sites/default/files/docs/epc/uhfc1g2_1_2_0-standard-20080511.pdf (accessed on 12 April 2018).
- Juels, A. RFID security and privacy: A research survey. IEEE J. Sel. Areas Commun. 2006, 24, 381–394. [Google Scholar] [CrossRef]
- ISO/IEC/IEEE Std 21451-7. Information Technology—Smart Transducer Interface for Sensors and Actuators—Part 7: Transducer to Radio Frequency Identification (RFID) Systems Communication Protocols and Transducer Electronic Data Sheet (TEDS) Formats; ISO: Geneva, Switzerland, 2011; pp. 1–82. [Google Scholar]
- Bröring, A.; Echterhoff, J.; Jirka, S.; Simonis, I.; Everding, T.; Stasch, C.; Liang, S.; Lemmens, R. New Generation Sensor Web Enablement. Sensors 2011, 11, 2652–2699. [Google Scholar] [CrossRef]
- Botts, M. OGC Implementation Specification 07-000: OpenGIS Sensor Model Language (SensorML); Open Geospatial Consortium, Inc.: Wayland, MA, USA, 2007; Available online: http://www.opengeospatial.org/standards/sensorml (accessed on 15 July 2014).
- Compton, M.; Barnaghi, P.; Bermudez, L. The SSN Ontology of the W3C Semantic Sensor Network Incubator Group. Web Semant. 2012, 17, 25–32. [Google Scholar] [CrossRef]
- Chien, H.Y.; Yang, C.C.; Wu, T.C.; Lee, C.F. Two rfid-based solutions to enhance inpatient medication safety. J. Med. Syst. 2011, 35, 369–375. [Google Scholar] [CrossRef] [PubMed]
- Kim, H.S. Enhanced hash-based RFID mutual authentication protocol. Commun. Comput. Inf. Sci. 2012, 339, 70–77. [Google Scholar]
- Kim, H.S. RFID mutual authentication protocol based on synchronized secret. Int. J. Secur. Appl. 2013, 7, 37–49. [Google Scholar]
- Amin, R.; Kumar, N.; Biswas, G.P.; Iqbal, R.; Chang, V. A light weight authentication protocol for IoT-enabled devices in distributed cloud computing environment. Future Gener. Comput. Syst. 2018, 78, 1005–1019. [Google Scholar] [CrossRef]
- Noura, M.; Atiquzzman, M.; Gaedke, M. Interoperability in internet of things: Taxonomies and open challenges. Mob. Netw. Appl. 2019, 24, 796–809. [Google Scholar] [CrossRef]
- Foster, I.; Zhao, Y.; Raicu, I.; Lu, S. Cloud computing and grid computing 360-degree compared. In Proceedings of the Workshop on Grid Computing Environments (GCE), Austin, TX, USA, 12–16 November 2008. [Google Scholar]
- Fernández Maimó, L.; Huertas Celdrán, A.; Perales Gómez, A.L.; García Clemente, F.J.; Weimer, J.; Lee, I. Intelligent and dynamic ransomware spread detection and mitigation in integrated clinical environments. Sensors 2019, 19, 1114. [Google Scholar] [CrossRef] [PubMed]
- Baker, S.B.; Xiang, W.; Atkinson, I. Internet of things for smart healthcare: Technologies, challenges, and opportunities. IEEE Access 2017, 5, 26521–26544. [Google Scholar] [CrossRef]
- Jang, Q.; Ma, J.; Yang, C.; Ma, X.; Shen, J.; Chaudhry, S.A. Efficient end-to-end authentication protocol for wearable health monitoring systems. Comput. Electr. Eng. 2017, 63, 182–195. [Google Scholar] [CrossRef]
- Al-Turjman, F.; Abujubbeh, M. IoT-enabled Smart Grid via SM: An Overview. Future Gener. Comput. Syst. 2019, 96, 579–590. [Google Scholar] [CrossRef]
- Perera, C.; Harold Liu, C.; Jayawardena, S.; Chen, M. A survey on internet of things from industrial market perspective. IEEE Access 2015, 2, 1660–1679. [Google Scholar] [CrossRef]
- Al-Turjman, F. Edge Computing: From Hype to Reality; Springer: Cham, Switzerland, 2019; ISBN 978-3-319-99060-6. [Google Scholar]
- Jiang, Q.; Qian, Y.; Ma, J.; Ma, X.; Cheng, Q.; Wei, F. User centric three-factor authentication protocol for cloud-assited wearable devices. Int. J. Commun. Syst. 2009, 9, e3900. [Google Scholar]
- Alam, M.M.; Malik, H.; Khan, M.I.; Pardy, T.; Kuusik, A.; Le Moullec, Y. A survey on the roles of communication technologies in IoT-based personalized healthcare applications. IEEE Access 2018, 6, 36611–36631. [Google Scholar] [CrossRef]
- Ferrag, M.A.; Maglaras, L.A.; Janicke, H.; Jiang, J.; Shu, L. Authentication protocols for internet of things: A comprehensive survey. Secur. Commun. Netw. 2017, 2017. [Google Scholar] [CrossRef]
- El-Hajj, M.; Fadlallah, A.; Chamoun, M.; Serhrouchni, A. A survey of internet of things (IoT) Authentication schemes. Sensors 2019, 19, 1141. [Google Scholar] [CrossRef] [PubMed]
- Madhusudhan, R.; Mittal, R.C. Dynamic id-based remote user password authentication schemes using smart cards: A review. J. Netw. Comput. Appl. 2012, 35, 1235–1248. [Google Scholar] [CrossRef]
- Chien, H.Y. SASI: A New Ultralightweight RFID Authentication Protocol Providing Strong Authentication and Strong Integrity. IEEE Trans. Dependable Secur. Comput. 2007, 4, 337–340. [Google Scholar] [CrossRef]
- Cao, T.; Bertino, E.; Lei, H. Security Analysis of the SASI Protocol. IEEE Trans. Dependable Secur. Comput. 2009, 6, 73–77. [Google Scholar]
- Phan, R.C.W. Cryptanalysis of A New Ultralightweight RFID Authentication Protocol—SASI. IEEE Trans. Dependable Secur. Comput. 2009, 6, 316–320. [Google Scholar] [CrossRef]
- Sun, H.M.; Ting, W.C.; Wang, K.H. On the Security of Chien’s Ultralightweight RFID Authentication Protocol. IEEE Trans. Dependable Secur. Comput. 2011, 8, 315–317. [Google Scholar] [CrossRef]
- Peris-Lopez, P.; Hernandez-Castro, J.C.; Tapiador, J.M.; Ribagorda, A. Advances in Ultralightweight Cryptography for Low-cost RFID Tags: Gossamer Protocol. In Proceedings of the 9th International Workshop on Information Security Applications, Jeju Island, Korea, 23–25 September 2008; pp. 56–68. [Google Scholar]
- Bilal, Z.; Masood, A.; Kausar, F. Security Analysis of Ultra-Lightweight Cryptographic Protocol for Low-cost RFID Tags: Gossamer Protocol. In Proceedings of the 2009 International Conference on Network-Based Information Systems, Indianapolis, IN, USA, 19–21 August 2009; pp. 260–267. [Google Scholar]
- Fan, K.; Ge, N.; Gong, Y.; Li, H.; Su, R.; Yang, Y. An Ultra-lightweight RFID Authentication Scheme for Mobile Commerce. Peer Peer Netw. Appl. 2017, 10, 368–376. [Google Scholar] [CrossRef]
- Aghili, S.F.; Mala, H. Security Analysis of an Ultra-lightweight RFID Authentication Protocol for M-commerce. Int. J. Commun. Syst. 2019, 32, 3837–3852. [Google Scholar] [CrossRef]
- Xu, H.; Ding, J.; Li, P.; Zhu, F.; Wang, R. A Lightweight RFID Mutual Authentication Protocol Based on Physical Unclonable Function. Sensors 2018, 18, 760. [Google Scholar] [CrossRef] [PubMed]
- Bendavid, Y.; Bagheri, N.; Safkhani, M.; Rostampour, S. IoT Device Security: Challenging A Lightweight RFID Mutual Authentication Protocol Based on Physical Unclonable Function. Sensors 2018, 18, 4444. [Google Scholar] [CrossRef] [PubMed]
- Gope, P.; Lee, J.; Quek, T.Q. Lightweight and Practical Anonymous Authentication Protocol for RFID Systems Using Physically Unclonable Functions. IEEE Trans. Inf. Forensics Secur. 2018, 13, 2831–2843. [Google Scholar] [CrossRef]
- Wang, W.C.; Yona, Y.; Diggavi, S.N.; Gupta, P. Design and Analysis of Stability-guaranteed PUFs. IEEE Trans. Inf. Forensics Secur. 2017, 13, 978–992. [Google Scholar] [CrossRef]
- Benssalah, M.; Djeddou, M.; Drouiche, K. A provably secure RFID authentication protocol based on elliptic curve signature with message recovery suitable for m-Health environments. Trans Emerg. Telecommun. Technol. 2017, 28, e3166. [Google Scholar] [CrossRef]
- Lee, K. IEEE 1451: A standard in support of smart transducer networking. In Proceedings of the 17th IEEE Instrumentation and Measurement Technology Conference [Cat. No. 00CH37066], Baltimore, MD, USA, 1–4 May 2000; pp. 525–528. [Google Scholar]
- Zhu, F.; Li, M.; Han, H.; Wang, J. RFIDsense: A reconfigurable RFID sensor tag platform conforming to IEEE 1451.7 standard. In Proceedings of the IEEE 2011 9th IEEE International Conference on ASIC, Xiamen, China, 25–28 October 2011; pp. 1074–1077. [Google Scholar]
- Guo, L.; Wu, J.; Xia, Z.; Li, J. Proposed security mechanism for XMPP-based communications of ISO/IEC/IEEE 21451 sensor networks. IEEE Sens. J 2014, 15, 2577–2586. [Google Scholar] [CrossRef]
- Ota, N.; Kramer, W.T. TinyML: Meta-Data for Wireless Networks. Available online: http://www.cs.berkeley.edu/~culler/cs294-f03/finalpapers (accessed on 15 July 2014).
- UPnP Forum. Sensor Management Sensor Data Model Service (Version 1.0). 2013. Available online: http://upnp.org/specs/smgt/ (accessed on 15 July 2014).
- University of Florida. Sensory Dataset Description Language (SDDL) Specification (Version 1.0). 2009. Available online: http://www.icta.ufl.edu/persim/sddl (accessed on 15 July 2014).
- Malewski, C.; Simonis, I.; Terhorst, A.; Bröring, A. StarFL—A modularized metadata language for sensor descriptions. Int. J. Digit. Earth 2014, 7, 450–469. [Google Scholar] [CrossRef]
- Burrows, M.; Abadi, M.; Needham, R.M. A logic of authentication. Proc. R. Soc. Lond. A Math. Phys. Sci. 1989, 426, 233–271. [Google Scholar] [CrossRef]
- Fan, K.; Wang, W.; Wang, Y.; Li, H.; Yang, Y. Cloud-Based Lightweight RFID Healthcare Privacy Protection Protocol. In Proceedings of the 2016 IEEE Global Communications Conference (GLOBECOM), Washington, DC, USA, 4–8 December 2016; pp. 1–6. [Google Scholar]
- Molnar, D.; Wagner, D. Privacy and security in library RFID: Issues, practices, and architectures. In Proceedings of the 11th ACM Conference on Computer and Communications Security, Washington, DC, USA, 25–29 October 2004; pp. 210–219. [Google Scholar]
- Feng, D.G. Research on Theory and Approach of Provable Security. J. Softw. 2005, 16, 1743–1756. [Google Scholar] [CrossRef]
- Syverson, P.F.; Van Oorschot, P.C. On unifying some cryptographic protocol logics. In Proceedings of the 1994 IEEE Computer Society Symposium on Research in Security and Privacy, Oakland, CA, USA, 16–18 May 1994; pp. 14–28. [Google Scholar]
- Gope, P.; Amin, R.; Islam, S.H.; Kumar, N.; Bhalla, V.K. Lightweight and privacy-preserving RFID authentication scheme for distributed IoT infrastructure with secure localization services for smart city environment. Future Gener. Comput. Syst. 2018, 83, 629–637. [Google Scholar] [CrossRef]
- ns3 Network Simulator. Available online: https://www.nsnam.org/ns-3-26/ (accessed on 8 May 2018).
- Tian, L.; Deronne, S.; Latre, S.; Famaey, J. Implementation and validation of an IEEE 802.11 ah module for ns-3. In Proceedings of the Workshop on ns-3, Seattle, WA, USA, 15–16 June 2016; pp. 49–56. [Google Scholar]
- Alghamdi, S.; Schyndel, R.V.; Alahmadi, A. Indoor Navigational Aid Using Active RFID and QR-Code For sighted and Blind People. In Proceedings of the 2013 IEEE Eighth International Conference on Intelligent Sensors, Sensor Networks and Information Processing, Melbourne, VIC, Australia, 2–5 April 2013. [Google Scholar]


| Authentication Protocol | Technique Used | Issue Addressed |
|---|---|---|
| Xu et al. [48] | Lightweight Authentication Using Physical Unclonable Function | Susceptible to secret disclosure and desynchronization attack |
| Bendavid et al. [49] | Lightweight Authentication Using Physical Unclonable Function | Perform frequent execution of setup phase to acquire a new set of pseudo-identity; whereby the back-end server experiences performance deprivation |
| Gope et al. [50] | Lightweight Anonymous Based Authentication Using Physical Unclonable Function | |
| Wang et al. [51] | Stability Guaranteed Physical Unclonable Function | |
| Benssalah et al. [52] | Authentication Using Elliptic Curve Signature with Message Recovery | Incur more communication cost and susceptible to untraceability |
| Notation | Description |
|---|---|
| Identity of the k-th Key | |
| Tag identity | |
| Random integer generated by reader | |
| Random integer generated by tag | |
| Secret session-key mutually shared between back-end server and tag | |
| Secret session-key in the k-th session | |
| One-way hash operational function | |
| Bitwise operator | |
| Expected transmission delay | |
| , , | Current timestamps |
| Concatenation operator | |
| Message format |
| Security Properties | Kim et al., 2012 [24] | Kim et al., 2013 [25] | Hajny et al. [12] | Proposed Hash-Based Protocol |
|---|---|---|---|---|
| Mutual Authentication | Not Support | Partial Support | Not Support | Fully Support |
| Resilient to Eavesdropping Attack | No | No | No | Yes |
| Resilient to Tracing Attack | No | No | No | Yes |
| Resilient to Replay Attack | No | No | No | Yes |
| Resilient to Man-in-the-Middle Attack | No | No | No | Yes |
| Resilient to De-Synchronization Attack | No | No | No | Yes |
| Untraceability and Tag-Anonymity | Not Provided | Not Provided | Not Provided | Provided |
| Authentication Protocol | RFID -Tag | Reader | Server | Execution Time (ms) | Communication Session | |
|---|---|---|---|---|---|---|
| Forward Channel | Backward Channel | |||||
| Kim et al. 2012 [24] | 2 | 1 | 4 | 0.45 | 4 | 3 |
| Kim et al. 2013 [25] | 2 | 3 | 4 | 0.61 | 4 | 3 |
| Hajny et al. [12] | 2 | 2 | 4 | 0.57 | 7 | 4 |
| Proposed Hash-Based Protocol | 3 | 1 | 3 | 0.44 | 3 | 3 |
| System Parameter | Values |
|---|---|
| Operating System | Ubuntu 16.04 LTS |
| Simulation Time | 1800 s |
| Area of RFID devices | |
| Availability of Readers | 5 Nos. |
| Availability of Tags | 160 Nos. |
| Transmission Range of a Reader | 200 m |
| Transmission Range of a Tag | 20 m |
| Communication Environment | IEEE 802.11 |
| Speed of Communication device |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
B D, D.; Al-Turjman, F.; Mostarda, L. A Hash-Based RFID Authentication Mechanism for Context-Aware Management in IoT-Based Multimedia Systems. Sensors 2019, 19, 3821. https://doi.org/10.3390/s19183821
B D D, Al-Turjman F, Mostarda L. A Hash-Based RFID Authentication Mechanism for Context-Aware Management in IoT-Based Multimedia Systems. Sensors. 2019; 19(18):3821. https://doi.org/10.3390/s19183821
Chicago/Turabian StyleB D, Deebak, Fadi Al-Turjman, and Leonardo Mostarda. 2019. "A Hash-Based RFID Authentication Mechanism for Context-Aware Management in IoT-Based Multimedia Systems" Sensors 19, no. 18: 3821. https://doi.org/10.3390/s19183821
APA StyleB D, D., Al-Turjman, F., & Mostarda, L. (2019). A Hash-Based RFID Authentication Mechanism for Context-Aware Management in IoT-Based Multimedia Systems. Sensors, 19(18), 3821. https://doi.org/10.3390/s19183821






