Mobile Sinks Assisted Geographic and Opportunistic Routing Based Interference Avoidance for Underwater Wireless Sensor Network
Abstract
:1. Introduction
- The distribution of the network field into small cubes is performed to make local routing decisions for efficient energy consumption.
- The distributive geo-opportunistic routing in geo-spatial network field avoids the interference by restricting number of nodes.
- In order to minimize traffic load on intermediate nodes, mobile sinks gather data directly from underwater nodes and also use to recover data from void hole.
- An optimal holding time is formulated to ensure that successful transmission acknowledgement receives before the time expires of an individual node.
2. Related Works
2.1. Geographic Routing
2.1.1. Sender-Based Geographic Routing
2.1.2. Receiver-Based Geographic Routing Algorithms
2.1.3. Opportunistic Routing Protocols
3. Preliminaries
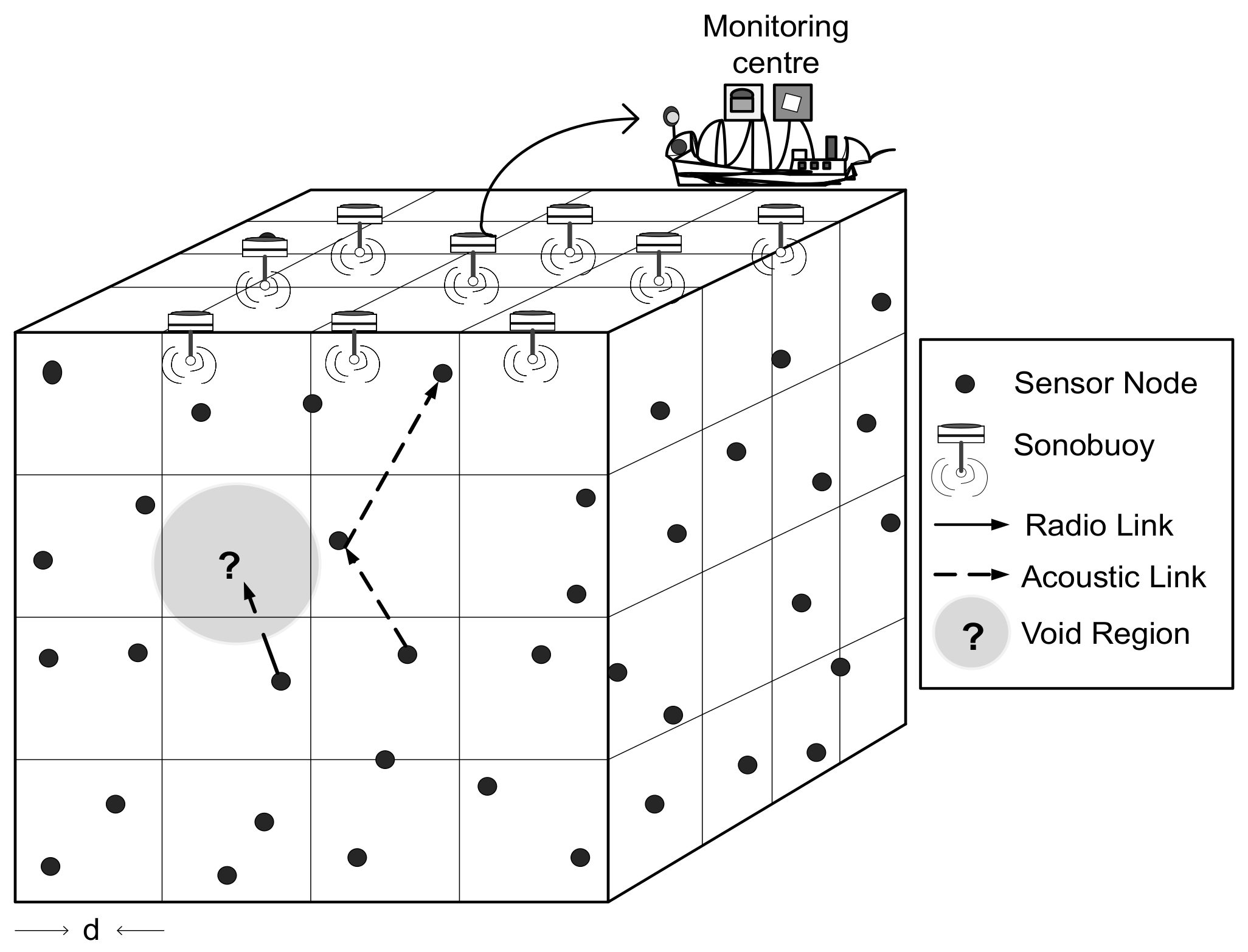
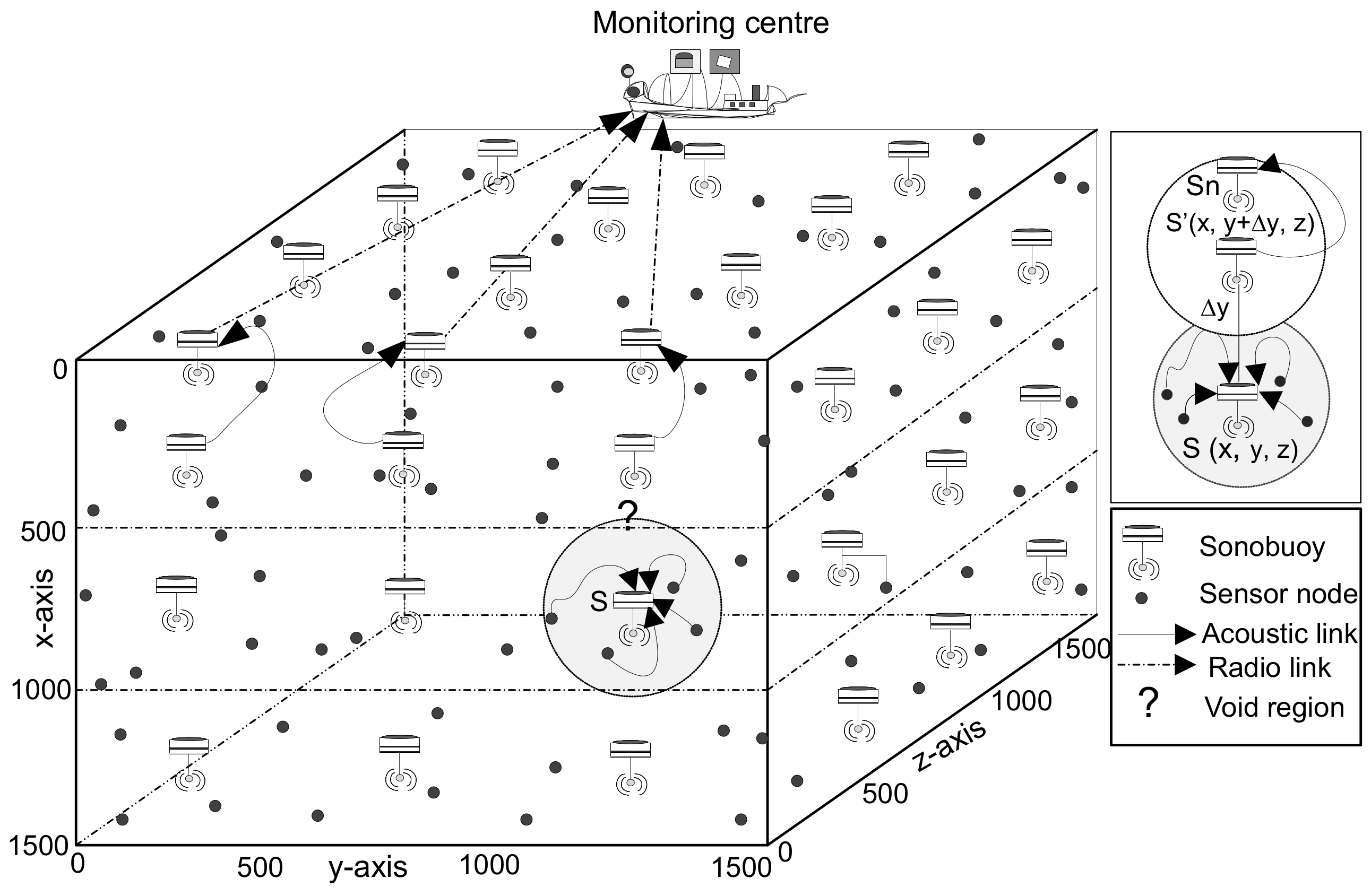
3.1. Network Architecture
3.2. Beacon Message Types
3.3. Potential Neighbor Set Selection
3.4. Geospatial Division Model
- Two cubes are adjacent to each other at common vertex, that is vertex adjacent.
- Two cubes are neighbor with common one edge, that is edge adjacent.
- If two cubes have adjacent surface to one another, that is surface adjacent.
- Otherwise, cubes are completely disjoint.
4. GDGOR-IA
4.1. Target Cube Selection
| Algorithm 1: Target cube selection. |
 |
4.2. Next-Hop Forwarder Set Selection Criterion
| Algorithm 2: Next-hop forwarder selection. |
 |
5. GRMC-SM
5.1. Data Forwarding and Routing in GRMC-SM
| Algorithm 3: Data forwarding mechanism (DFM). |
 |
5.2. Recovery Mode via Sink Mobility
6. Mathematical Formulation Using Linear Programming
6.1. Energy Consumption Minimization
- at J
- at J
- at J
- at J
- at J
- at J
- at J
- at J
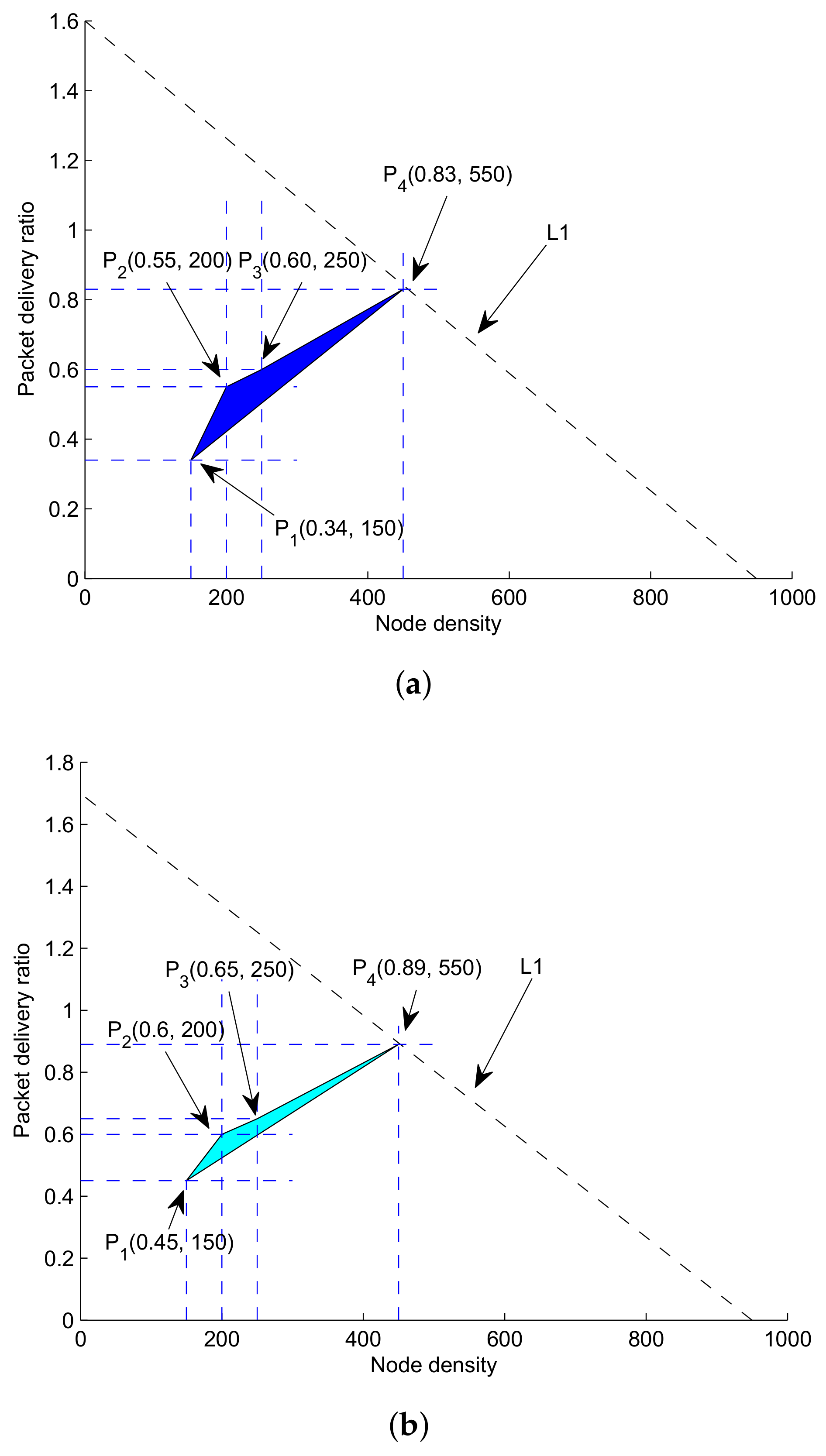
6.2. PDR Maximization
- C1:
- C2:
- C3:
- C4:
- at
- at
- at
- at
- at
- at
- at
- at
6.3. Minimization of Average Delay
- at C1:
- at C2:
- at C3:
- at s
- at s
- at s
- at s
- at s
- at s
- at s
- at s
7. Simulation Results and Discussion
7.1. Simulation Settings
Performance Metrics
- PDR: The ratio of packets successfully received at surface sonobuoys over amount of packets transmitted from each network node during the network operational time. The mathematical expression is given as follows:where, shows the quantity of packets delivered at the destination, while depicts the summation of packets generated from each network node.
- Fraction of void nodes: It is the amount of network nodes fail to deliver the data packet over the acoustic communication channel because of unavailability of further forwarder nodes in there transmission range.
- Energy consumption: It is defined as, the energy utilized in transmitting a data packet by a node within its transmission range. It is measured in joules (J).
- End-to-end delay: Time required for transmitting and propagating data from source to destination is called end-to-end delay and its unit is seconds (s).
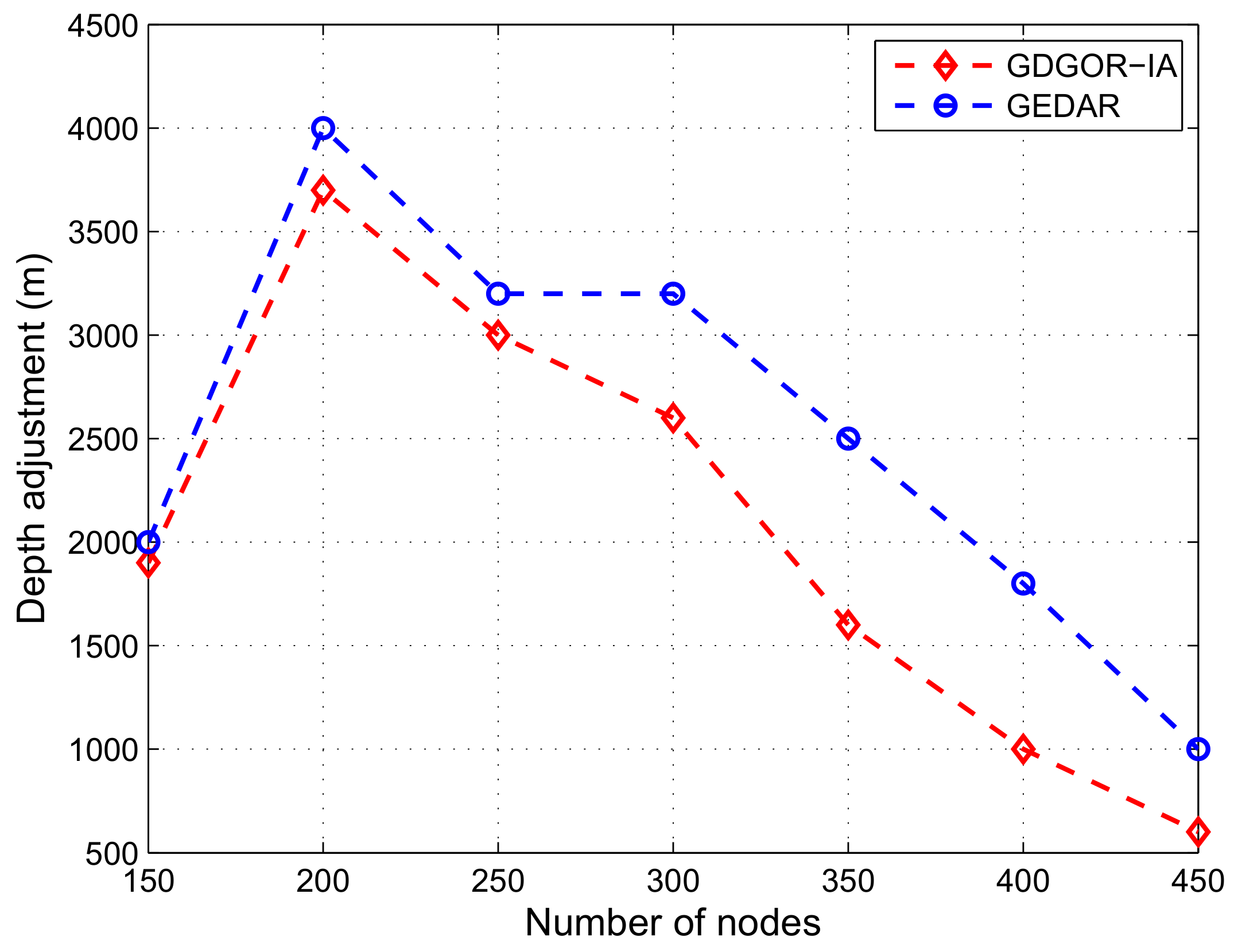
- Depth adjustment: Net distance covered by a void node to find a forwarder node for resuming network operations is called depth adjustment and it is measured in meters (m).
7.2. Analysis of Proposed Scheme Results against Existing State of the Art
7.2.1. Fraction of Void Nodes
7.2.2. Depth Adjustment
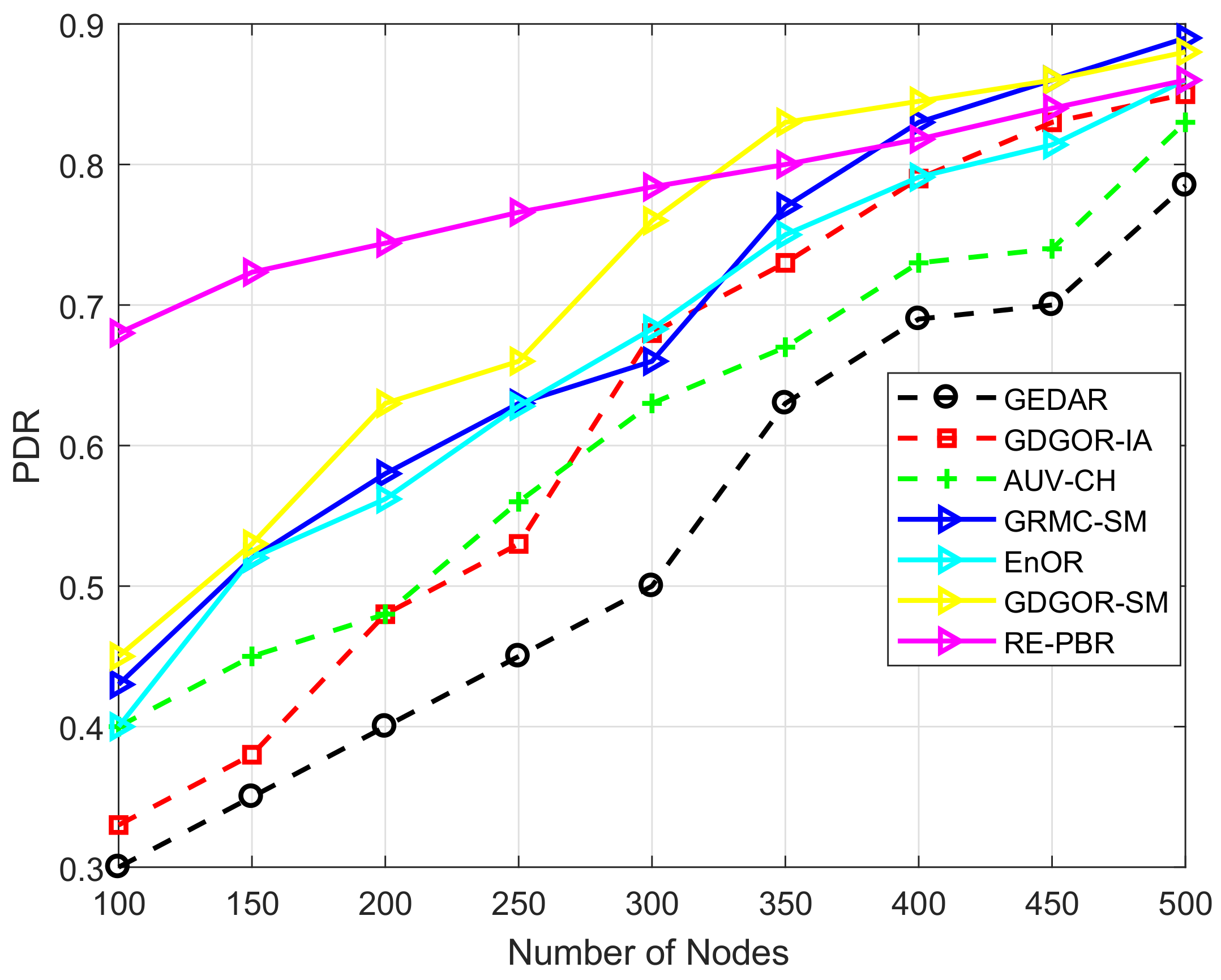
7.2.3. PDR
7.2.4. Energy Consumption
7.2.5. End-To-End Delay
7.2.6. Performance Trade-Offs
7.3. Observations of the Research
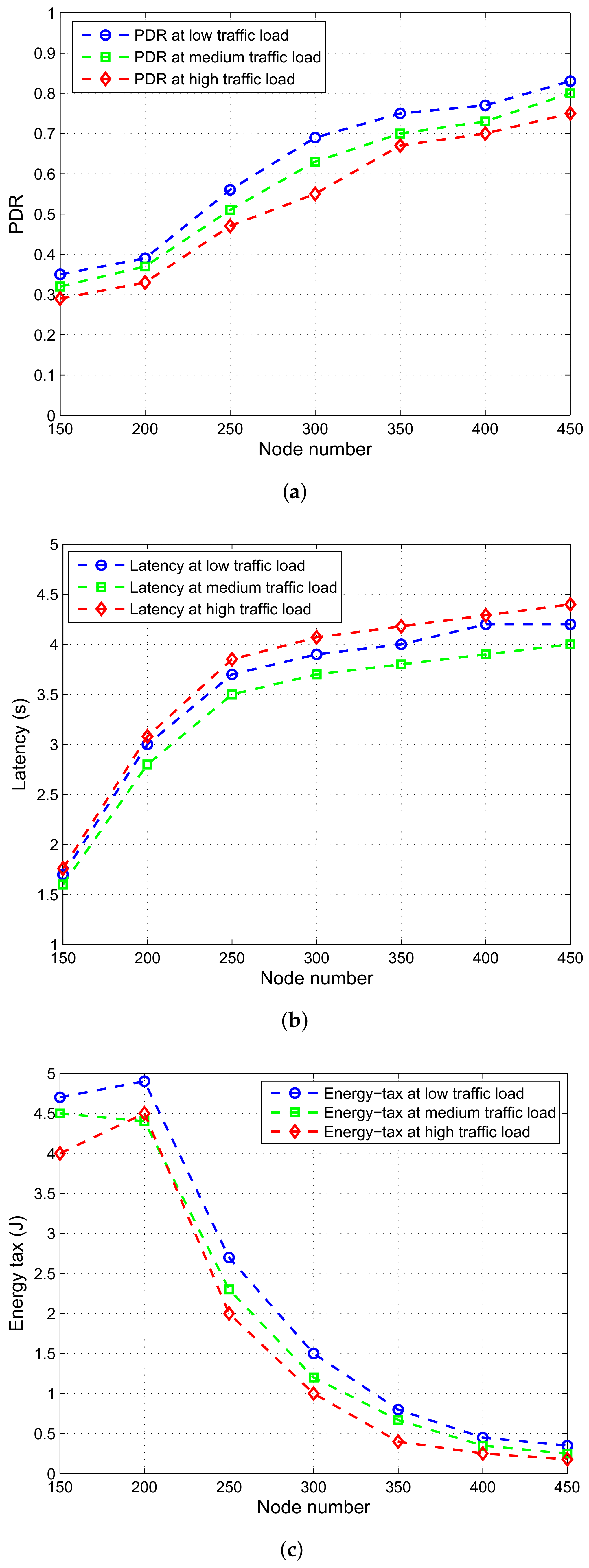
7.3.1. Performance Analysis Based on Varying Traffic Loads
7.3.2. Performance Analysis of GRMC-SM by Varying Number of Sinks
8. Conclusions
Acknowledgments
Author Contributions
Conflicts of Interest
References
- Akyildiz, I.F.; Pompili, D.; Melodia, T. Underwater acoustic sensor networks: Research challenges. Ad Hoc Netw. 2005, 3, 257–279. [Google Scholar]
- Vasilescu, I.; Kotay, K.; Rus, D.; Dunbabin, M.; Corke, P. Data collection, storage, and retrieval with an underwater sensor network. In Proceedings of the 3rd International Conference on Embedded Networked Sensor Systems, San Diego, CA, USA, 2–4 November 2005; pp. 154–165. [Google Scholar]
- Xu, N.; Rangwala, S.; Chintalapudi, K.K.; Ganesan, D.; Broad, A.; Govindan, R.; Estrin, D. A wireless sensor network for structural monitoring. In Proceedings of the 2nd International Conference on Embedded Networked Sensor Systems, Baltimore, MD, USA, 3–5 November 2004; pp. 13–24. [Google Scholar]
- Szewczyk, R.; Mainwaring, A.; Polastre, J.; Anderson, J.; Culler, D. An analysis of a large scale habitat monitoring application. In Proceedings of the 2nd International Conference on Embedded Networked Sensor Systems, Baltimore, MD, USA, 3–5 November 2004; pp. 214–226. [Google Scholar]
- Coutinho, R.W.L.; Boukerche, A.; Vieira, L.F.M.; Loureiro, A.A.F. GEDAR: Geographic and opportunistic routing protocol with depth adjustment for mobile underwater sensor networks. In Proceedings of the 2014 IEEE International Conference on Communications (ICC), Sydney, Australia, 10–14 June 2014; pp. 251–256. [Google Scholar]
- Coutinho, R.W.; Boukerche, A.; Vieira, L.F.; Loureiro, A.A. A novel void node recovery paradigm for long-term underwater sensor networks. Ad Hoc Netw. 2015, 34, 144–156. [Google Scholar] [CrossRef]
- Coutinho, R.W.; Boukerche, A.; Vieira, L.F.; Loureiro, A.A. Geographic and opportunistic routing for underwater sensor networks. IEEE Trans. Comput. 2016, 65, 548–561. [Google Scholar] [CrossRef]
- Coutinho, R.W.; Boukerche, A.; Vieira, L.F.; Loureiro, A.A. EnOR: Energy balancing routing protocol for underwater sensor networks. In Proceedings of the 2017 IEEE International Conference on Communications (ICC), Paris, France, 21–25 May 2017; pp. 1–6. [Google Scholar]
- Liu, M.; Ji, F.; Guan, Q.; Yu, H.; Chen, F.; Wei, G. On-surface wireless-assisted opportunistic routing for underwater sensor networks. In Proceedings of the 11th ACM International Conference on Underwater Networks and Systems, Shanghai, China, 24–26 October 2016; p. 43. [Google Scholar]
- Menon, V.G.; Prathap, P.M.J. Comparative analysis of opportunistic routing protocols for underwater acoustic sensor networks. In Proceedings of the International Conference on Emerging Technological Trends (ICETT), Kollam, India, 21–22 October 2016; pp. 1–5. [Google Scholar]
- Kartha, J.J.; Jacob, L. Delay and lifetime performance of underwater wireless sensor networks with mobile element based data collection. Int. J. Distrib. Sens. Netw. 2015, 11, 128757. [Google Scholar] [CrossRef]
- Maihofer, C. A survey of geocast routing protocols. IEEE Commun. Surv. Tutor. 2004, 6, 32–42. [Google Scholar] [CrossRef]
- Li, Z.; Yao, N.; Gao, Q. Relative distance based forwarding protocol for underwater wireless networks. Int. J. Distrib. Sens. Netw. 2014, 10, 173089. [Google Scholar] [CrossRef]
- Dhurandher, S.K.; Obaidat, M.S.; Gupta, M. A novel geocast technique with hole detection in underwater sensor networks. In Proceedings of the 2010 IEEE/ACS International Conference on Computer Systems and Applications (AICCSA), Hammamet, Tunisia, 16–19 May 2010; pp. 1–8. [Google Scholar]
- Guo, Z.; Colombi, G.; Wang, B.; Cui, J.H.; Maggiorini, D.; Rossi, G.P. Adaptive routing in underwater delay/disruption tolerant sensor networks. In Proceedings of the Fifth Annual Conference on Wireless on Demand Network Systems and Services (WONS 2008), Garmisch-Partenkirchen, Germany, 23–25 January 2008; pp. 31–39. [Google Scholar]
- Yan, H.; Shi, Z.J.; Cui, J.H. DBR: Depth-based routing for underwater sensor networks. In Proceedings of the International Conference on Research in Networking, Singapore, 5–9 May 2008; pp. 72–86. [Google Scholar]
- Wahid, A.; Lee, S.; Jeong, H.J.; Kim, D. Eedbr: Energy-efficient depth-based routing protocol for underwater wireless sensor networks. In Proceedings of the Advanced Computer Science and Information Technology, Seoul, Korea, 27–29 September 2011; pp. 223–234. [Google Scholar]
- Javaid, N.; Jafri, M.R.; Ahmed, S.; Jamil, M.; Khan, Z.A.; Qasim, U.; Al-Saleh, S.S. Delay-Sensitive Routing Schemes for Underwater Acoustic Sensor Networks. Int. J. Distrib. Sens. Netw. 2015, 2015, 532676. [Google Scholar] [CrossRef]
- Ayaz, M.; Abdullah, A.; Faye, I.; Batira, Y. An efficient dynamic addressing based routing protocol for underwater wireless sensor networks. Comput. Commun. 2012, 35, 475–486. [Google Scholar] [CrossRef]
- Ali, T.; Jung, L.T.; Faye, I. Diagonal and vertical routing protocol for underwater wireless sensor network. Procedia Soc. Behav. Sci. 2014, 129, 372–379. [Google Scholar] [CrossRef]
- Xie, P.; Cui, J.H.; Lao, L. VBF: Vector-based forwarding protocol for underwater sensor networks. In NETWORKING 2006. Networking Technologies, Services, and Protocols; Performance of Computer and Communication Networks; Mobile and Wireless Communications Systems; Boavida, F., Plagemann, T., Stiller, B., Westphal, C., Monteiro, E., Eds.; Springer: Berlin/Heidelberg, Germany, 2006; pp. 1216–1221. [Google Scholar]
- Liang, W.; Luo, J.; Xu, X. Prolonging network lifetime via a controlled mobile sink in wireless sensor networks. In Proceedings of the 2010 IEEE Global Telecommunications Conference (GLOBECOM 2010), Miami, FL, USA, 6–10 December 2010; pp. 1–6. [Google Scholar]
- Baruah, P.; Urgaonkar, R.; Drishnamachari, B. Learning-enforced time domain routing to mobile sinks in wireless sensor fields. In Proceedings of the IEEE EmNets, Tampa, FL, USA, 16–18 November 2004; pp. 525–534. [Google Scholar]
- Kumar, V.N.; Kumar, M.S.; Rajakumari, J.; Mohanarangan, S. Opportunistic Void Avoidance Routing for Underwater Sensor Networks. Int. J. Sci. Res. Comput. Sci. Eng. Inf. Technol. 2017, 2, 924–930. [Google Scholar]
- Hsu, C.C.; Liu, H.H.; Gómez, J.L.G.; Chou, C.F. Delay-sensitive opportunistic routing for underwater sensor networks. IEEE Sens. J. 2015, 15, 6584–6591. [Google Scholar] [CrossRef]
- Noh, Y.; Lee, U.; Lee, S.; Wang, P.; Vieira, L.F.M.; Cui, J.; Gerla, M.; Kim, K. Hydrocast: Pressure routing for underwater sensor networks. IEEE Trans. Veh. Technol. 2016, 65, 333–347. [Google Scholar] [CrossRef]
- Lee, U.; Wang, P.; Noh, Y.; Vieira, L.F.M.; Gerla, M.; Cui, J. Pressure routing for underwater sensor networks. In Proceedings of the 2010 Proceedings IEEE INFOCOM, San Diego, CA, USA, 14–19 March 2010; pp. 1–9. [Google Scholar]
- Khasawneh, A.; Latiff, M.S.B.A.; Chizari, H. A reliable energy-efficient pressure-based routing protocol for underwater wireless sensor network. Wirel. Netw. 2017, 1–15. [Google Scholar] [CrossRef]
- Khan, J.U.; Cho, H.S. A distributed data-gathering protocol using AUV in underwater sensor networks. Sensors 2015, 15, 19331–19350. [Google Scholar] [CrossRef] [PubMed]
- Erol, M.; Vieira, L.F.M.; Gerla, M. Localization with Dive’N’Rise (DNR) beacons for underwater acoustic sensor networks. In Proceedings of the Second Workshop on Underwater Networks, Montreal, QC, Canada, 14 September 2007; pp. 97–100. [Google Scholar]
- O’Rourke, M.; Basha, E.; Detweiler, C. Multi-modal communications in underwater sensor networks using depth adjustment. In Proceedings of the Seventh ACM International Conference on Underwater Networks and Systems, Los Angeles, CA, USA, 5–6 November 2012; pp. 31:1–31:5. [Google Scholar]
- Yu, Z.; Xiao, C.; Zhou, G. Multi-objectivization-based localization of underwater sensors using magnetometers. IEEE Sens. J. 2014, 14, 1099–1106. [Google Scholar] [CrossRef]
- Kleerekoper, A.; Filer, N. Revisiting blacklisting and justifying the unit disk graph model for energy-efficient position-based routing in wireless sensor networks. In Proceedings of the 2012 IFIP Wireless Days (WD), Dublin, Ireland, 21–23 November 2012; pp. 1–3. [Google Scholar]
- Melodia, T.; Pompili, D.; Akyildiz, I.F. Optimal local topology knowledge for energy efficient geographical routing in sensor networks. In Proceedings of the Twenty-Third Annual Joint Conference of the IEEE Computer and Communications Societies (INFOCOM 2004), Hong Kong, China, 7–11 March 2004; Volume 3, pp. 1705–1716. [Google Scholar]
- Yu, H.; Yao, N.; Liu, J. An adaptive routing protocol in underwater sparse acoustic sensor networks. Ad Hoc Netw. 2015, 34, 121–143. [Google Scholar] [CrossRef]
- Lee, S.; Bhattacharjee, B.; Banerjee, S. Efficient geographic routing in multihop wireless networks. In Proceedings of the 6th ACM International Symposium on Mobile Ad Hoc Networking and Computing, Urbana-Champaign, IL, USA, 25–27 May 2005; pp. 230–241. [Google Scholar]
- Xie, P.; Zhou, Z.; Peng, Z.; Yan, H.; Hu, T.; Cui, J.H.; Shi, Z.; Fei, Y.; Zhou, S. Aqua-Sim: An NS-2 based simulator for underwater sensor networks. In Proceedings of the MTS/IEEE Biloxi-Marine Technology for Our Future: Global and Local Challenges (OCEANS 2009), Biloxi, MS, USA, 26–29 October 2009; pp. 1–7. [Google Scholar]









| Symbols | Description |
|---|---|
| Number of logical cubes | |
| Total nodes deployed | |
| A set of sonobuoys | |
| Flag to indicate that latest neighbor information | |
| Potential forwarder nodes set | |
| Current cube | |
| Neighbor cube | |
| Target cube | |
| Bit error rate probability | |
| Probability of collision rate | |
| Advancement towards destination | |
| Processing time at each node | |
| Propagation delay | |
| Normalized advancement towards destination | |
| Number of mobile sonobuoys deployed in the network | |
| Data forwarding | |
| Transmission energy | |
| Receiving energy | |
| Straight line distance from node i to node j | |
| Energy consumed which includes transmission and reception energies | |
| Data rate | |
| Energy dissipated in data aggregation | |
| Communication range of a node | |
| Transmission power for transmission data packet | |
| A power required to receive a data packet | |
| Packet delivery ratio | |
| The residual energy threshold which must be greater or equal than residual energies | |
| Delay occur in transmitting data packet directly | |
| Delay occur in delivering data packet through multiple hops | |
| Time required to hold a packet |
| Protocols | Void Handling | Geographic Information | Communication Overhead | Energy Efficiency | Delay |
|---|---|---|---|---|---|
| VBF [11] | No | Position information | High | Medium | High |
| DBR [13] | No | Depth information | Low | High | High |
| DS-DBR [14] | No | Depth information | Low | Medium | Low |
| H2-DAB [15] | No | Depth information | Low | High | Medium |
| RDBF [16] | No | Location information | High | High | Low |
| RMTG [17] | By pass void hole | Location information | High | Low | Medium |
| ARP [18] | Avoids void hole | Location information | High | High | Medium |
| DVRP [19] | No | Location information | Medium | High | Medium |
| VAPR [20] | Avoids void hole | Location information | Medium | Low | Medium |
| Hydrocast [21] | Depth recovery | Pressure information | High | Low | Medium |
| Parameter | GDGOR-IA | GRMC-SM | GDGOR-SM |
|---|---|---|---|
| PDR (%) | 4 | 7 | 3 |
| Energy tax (%) | 10 | 51 | 12 |
| Latency (%) | 16 | −48 | 15 |
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Ahmed, F.; Wadud, Z.; Javaid, N.; Alrajeh, N.; Alabed, M.S.; Qasim, U. Mobile Sinks Assisted Geographic and Opportunistic Routing Based Interference Avoidance for Underwater Wireless Sensor Network. Sensors 2018, 18, 1062. https://doi.org/10.3390/s18041062
Ahmed F, Wadud Z, Javaid N, Alrajeh N, Alabed MS, Qasim U. Mobile Sinks Assisted Geographic and Opportunistic Routing Based Interference Avoidance for Underwater Wireless Sensor Network. Sensors. 2018; 18(4):1062. https://doi.org/10.3390/s18041062
Chicago/Turabian StyleAhmed, Farwa, Zahid Wadud, Nadeem Javaid, Nabil Alrajeh, Mohamad Souheil Alabed, and Umar Qasim. 2018. "Mobile Sinks Assisted Geographic and Opportunistic Routing Based Interference Avoidance for Underwater Wireless Sensor Network" Sensors 18, no. 4: 1062. https://doi.org/10.3390/s18041062
APA StyleAhmed, F., Wadud, Z., Javaid, N., Alrajeh, N., Alabed, M. S., & Qasim, U. (2018). Mobile Sinks Assisted Geographic and Opportunistic Routing Based Interference Avoidance for Underwater Wireless Sensor Network. Sensors, 18(4), 1062. https://doi.org/10.3390/s18041062






