An Authentication Protocol for Future Sensor Networks
Abstract
:1. Introduction
2. Related Work
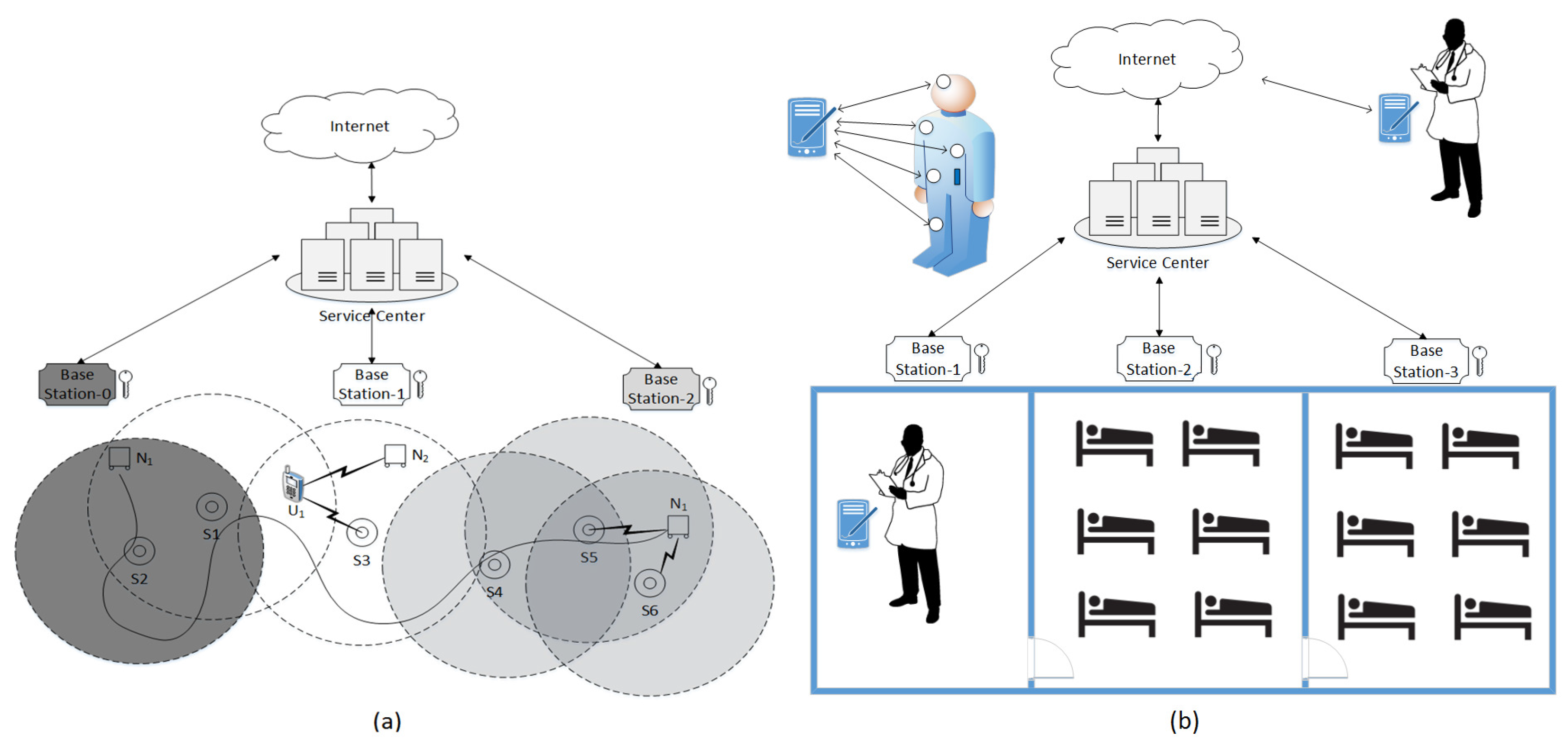
3. System Overview and Problem Statement
3.1. System Architecture
3.2. Problem Statement
3.3. Notations
- = The jth base station
- = The jth sink
- = The ith sensor node
- = The ith user node
- = A is associated with B such that B is controlling authority
- = Group of all associated entities of jth
- = Group of all non-associated entities of jth BS who knows the
- = The time-based key generated at ith interval by
- = A group key generated by
- = session key generated at ith interval
- = private session key
- = Temporary session key
- = Encryption of ’m’, using key
- = The index value for interval i
- = The kth Ticket
- = An intruder Z mimicking the entity A
- = ith nonce in a message exchange
4. Proposed Scheme
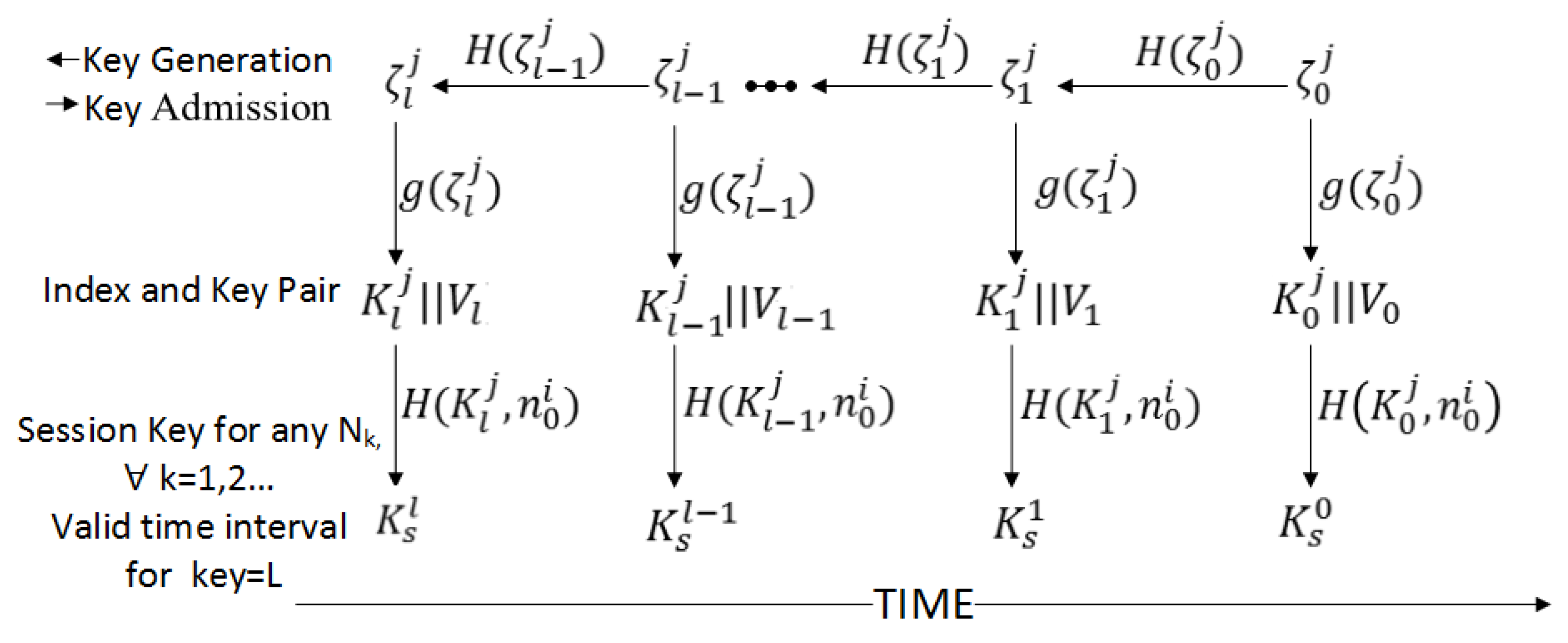
4.1. Keying Protocol Suite
4.1.1. Key Agreement Protocol
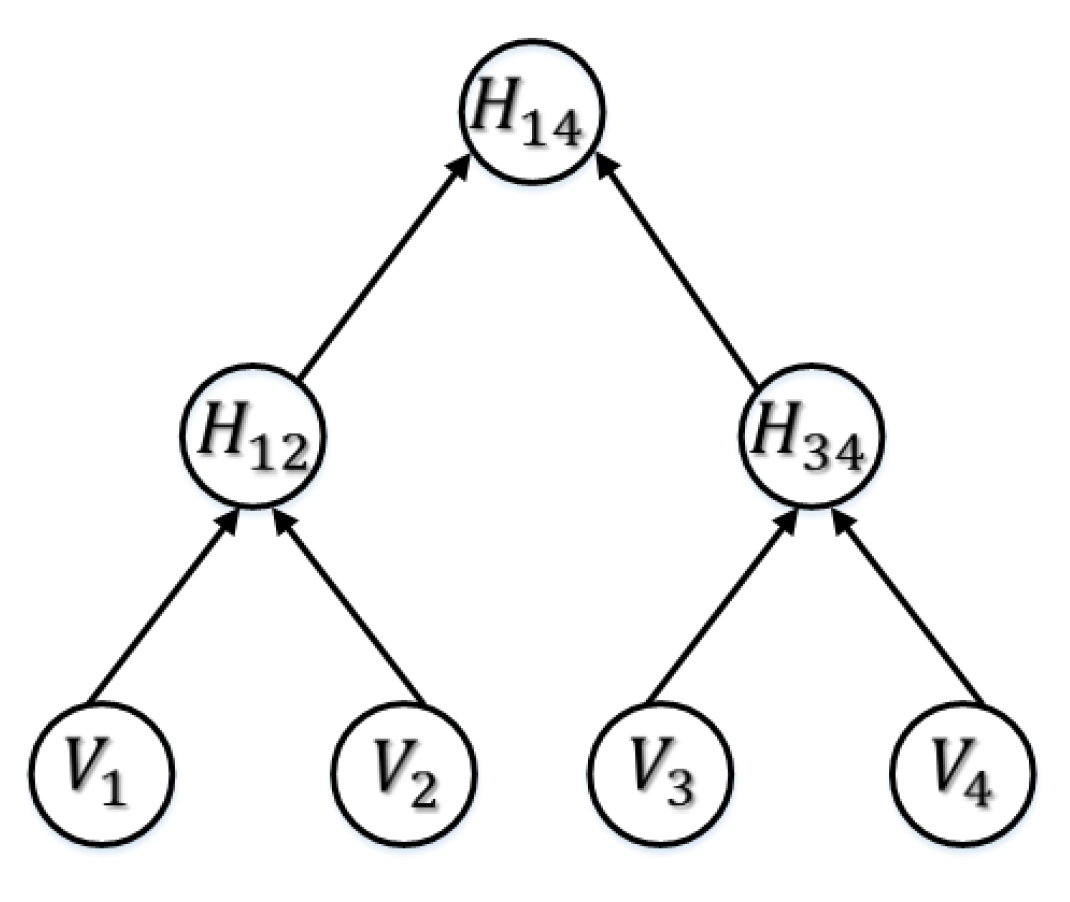
4.1.2. The Key Retrieval Protocol
- Start from the root and move down
- Ignore appended values and follow the path of the reconstructed node
- Continue until level is reached
- At level , select the appended value that is the index value.
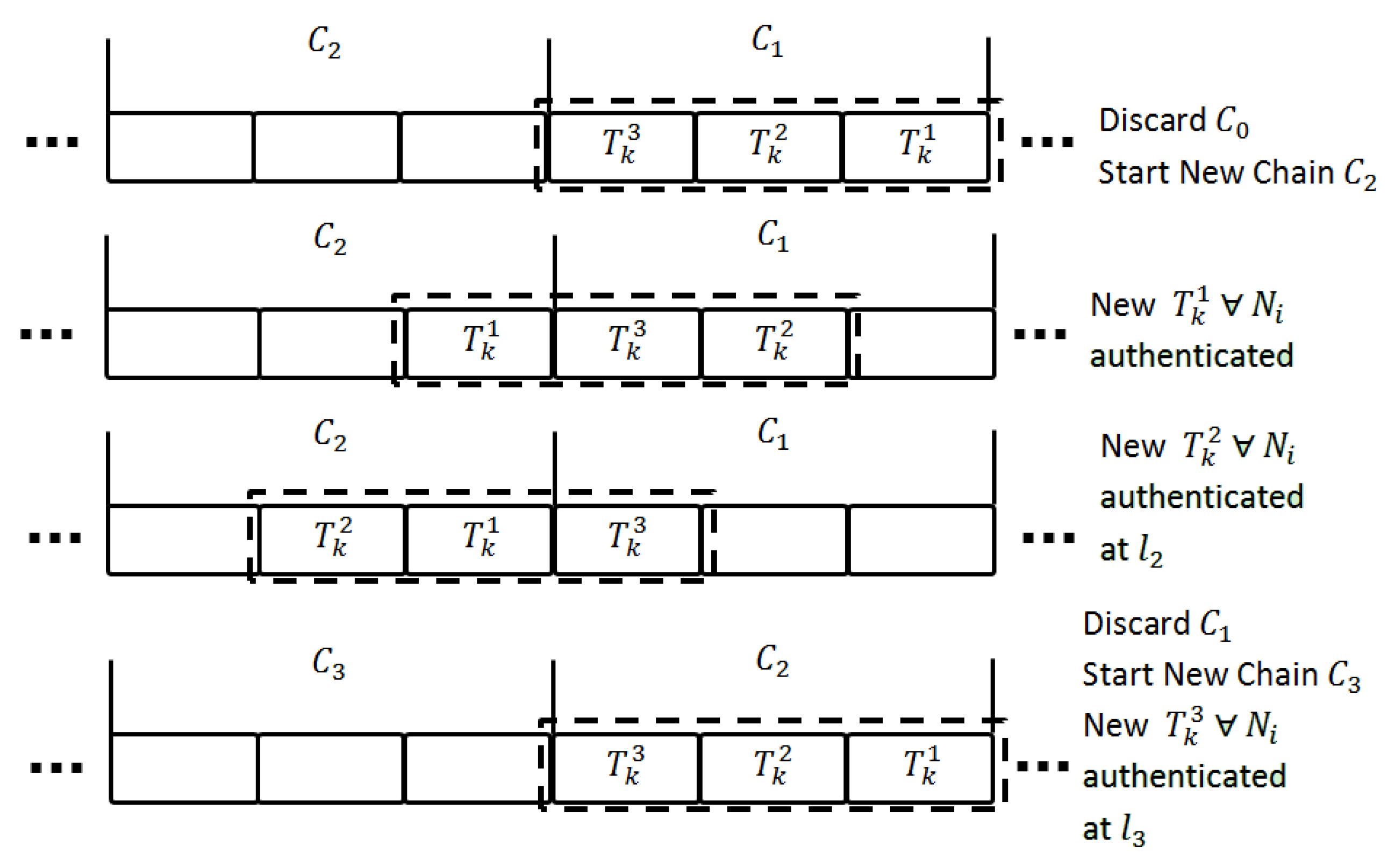
4.1.3. Key Management Protocol for the Sink Node
4.2. Authentication Protocol Suite
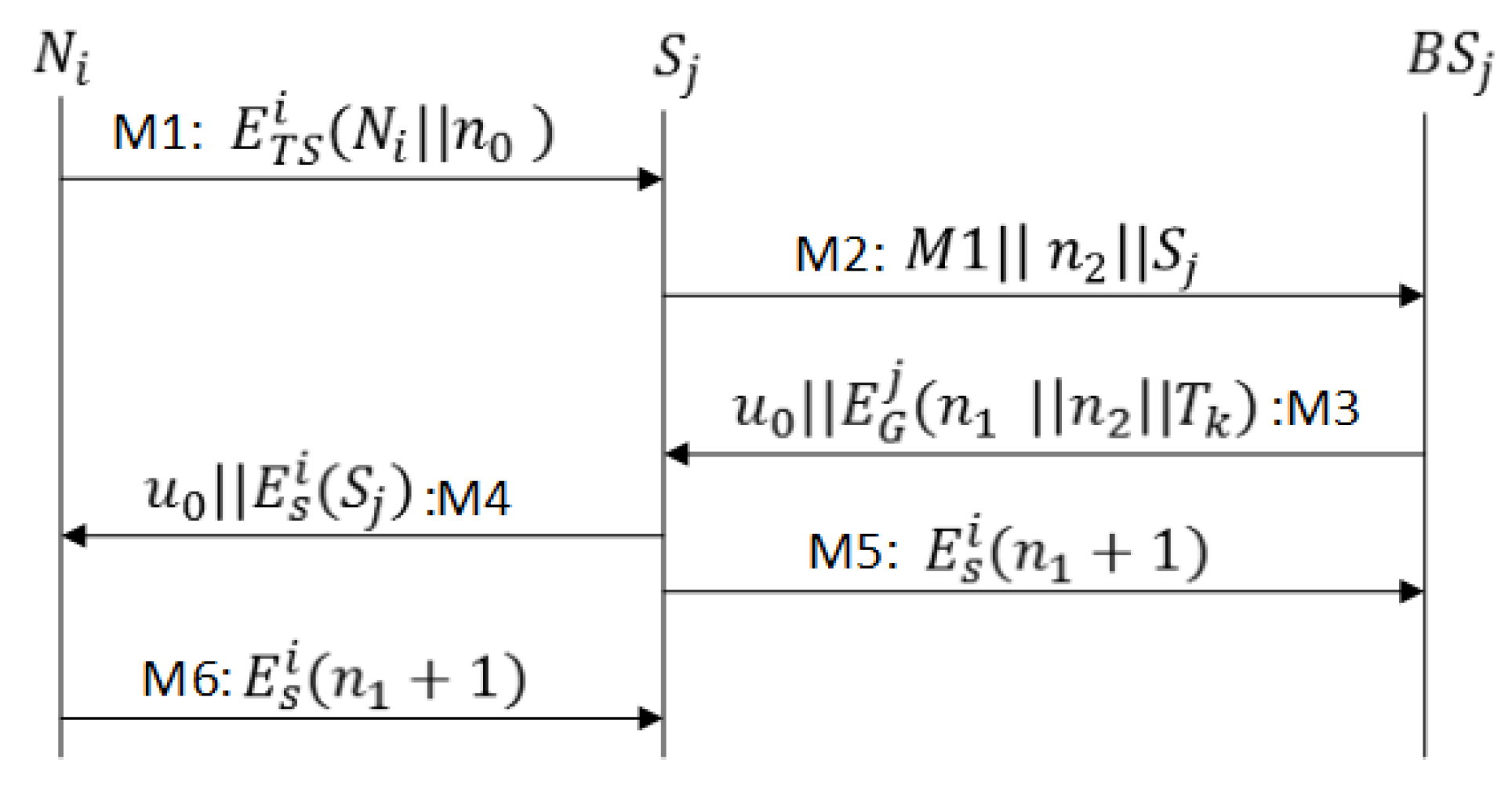
4.2.1. Sensor Activation and Authentication Protocol (SAAP)
- M1
- As shown in Figure 5, sends a JOIN message to sink enclosing and encrypted with the generated encryption key .
- M2
- Upon receiving the request from , the forwards the request in conjunction with its identity and challenge to base station .
- M3
- retrieves the profile from the database, and if isa legitimate sensor node, generates the key , and sends to in M3. M3 also includes ticket , (a challenge for ), and (challenge response for the sink node), all encrypted with . The sink node verifies the challenge , stores and retrieves the profile and from the ticket.
- M4
- forwards the to After a challenge ( verification, accepts and may start sending data to .
- M5
- sends the challenge response to for the confirmation of a successful protocol run.
- M6
- After challenge ( confirmation, starts accepting sensor data; otherwise, it marks as an invalid ticket.
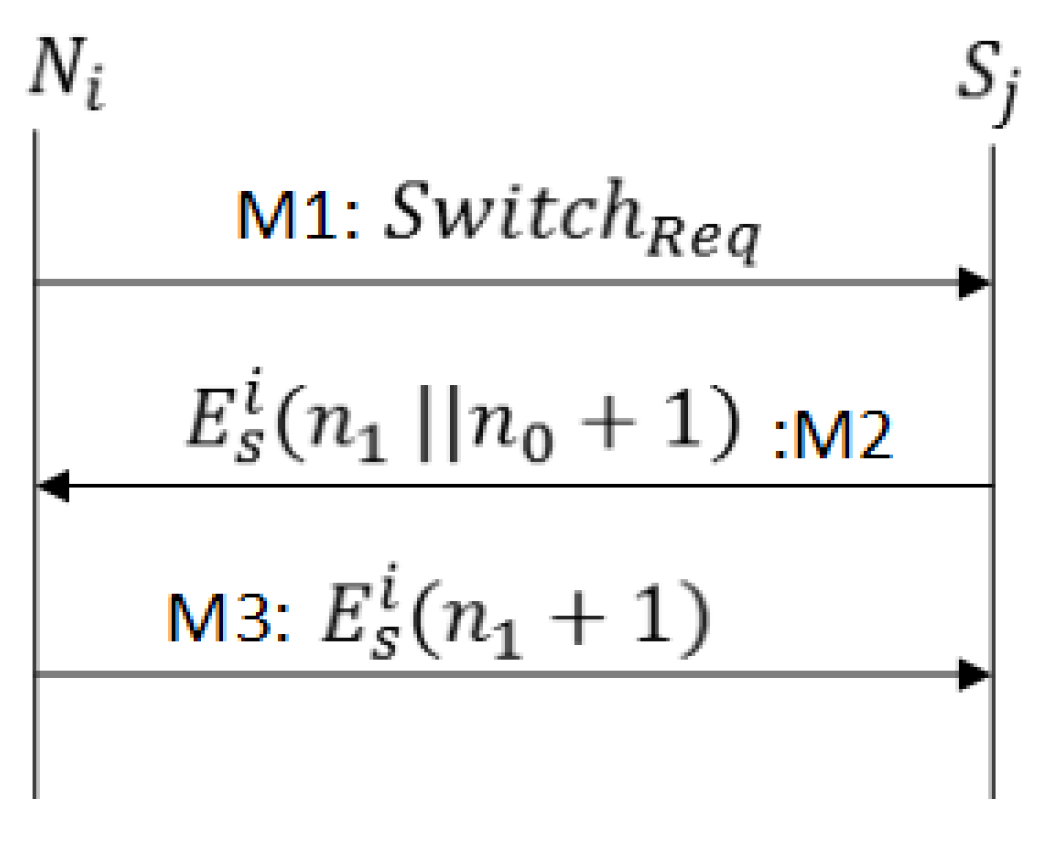
4.2.2. Sensor Re-Authentication Protocol -1 (SRP1)
- M1
- As shown in Figure 6, sends to . The sink decrypts the ticket, retrieves calculates the hash of , and makes a comparison with received in the switch message. If the value does not match, the will ignore the request and otherwise proceed as follows.
- M2
- sends a challenge response along with the new challenge encrypted with session key .
- M3
- sends the challenge response . After challenge confirmation, starts accepting data; otherwise, it marks as an invalid ticket.
4.2.3. Sensor Re-Authentication Protocol -2 (SRP2)
- M1
- As shown in Figure 7, sends to . The sink decrypts the second half of and verifies the identities of and ticket granting base station.
- M2
- After identities verification the sink forwards the request in conjunction with a challenge to base station .
- M3
- retrieves the profile from , and if isa legitimate sensor node, the generates the key , and sends to in M3. M3 also includes ticket , (a challenge for ), and (challenge response for the sink node), all encrypted with . The sink node verifies the challenge , stores and retrieves the profile and from the ticket.
- M4
- forwards to After challenge ( verification accepts and start sending data to .
- M5
- sends the challenge response to ; it confirms a successful protocol run.
- M6
- After challenge ( confirmation start accepting data; otherwise, it marks as an invalid ticket.
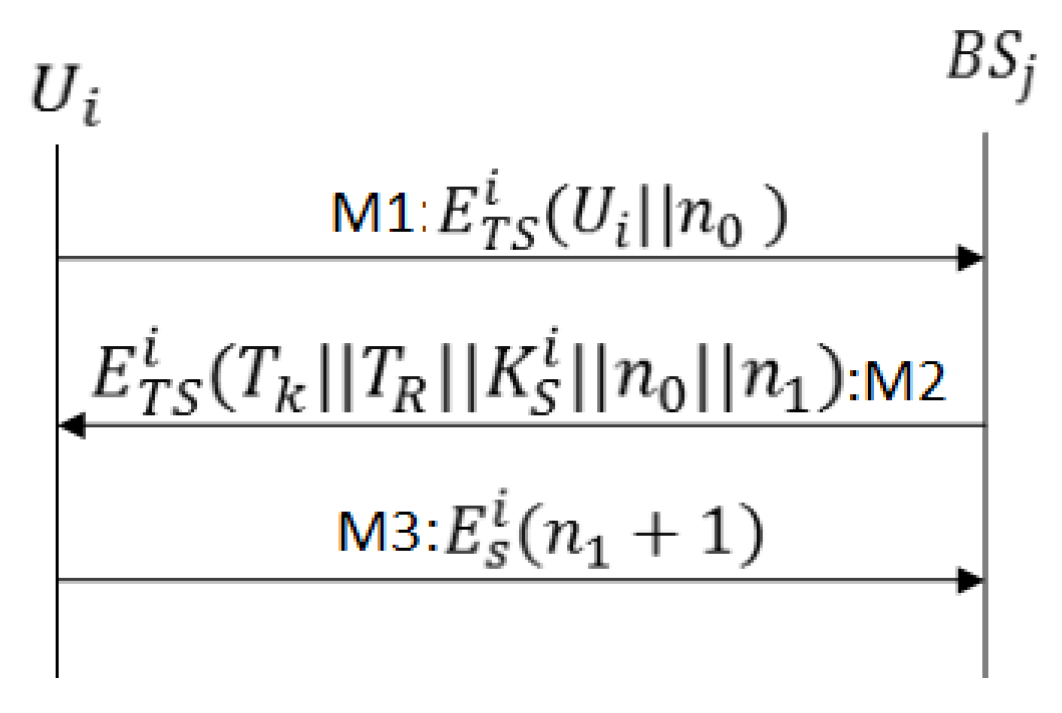
4.2.4. User Activation and Authentication Protocol (UAAP)
- M1
- As shown in Figure 8, sends a JOIN message enclosing and the user identity to base station .
- M2
- retrieves profile from the database, and if is a legitimate user, the generates authentication ticket, and send along with, ( a challenge for ), and (challenge response), all encrypted with . The ticket structure is same except the secret nonce enclosed inside ticket is generated by
- M3
- The user node verifies the challenge , stores and . sends the challenge response to ; it confirms a successful protocol run . After receiving a challenge response the updates the status of from idle to active user.
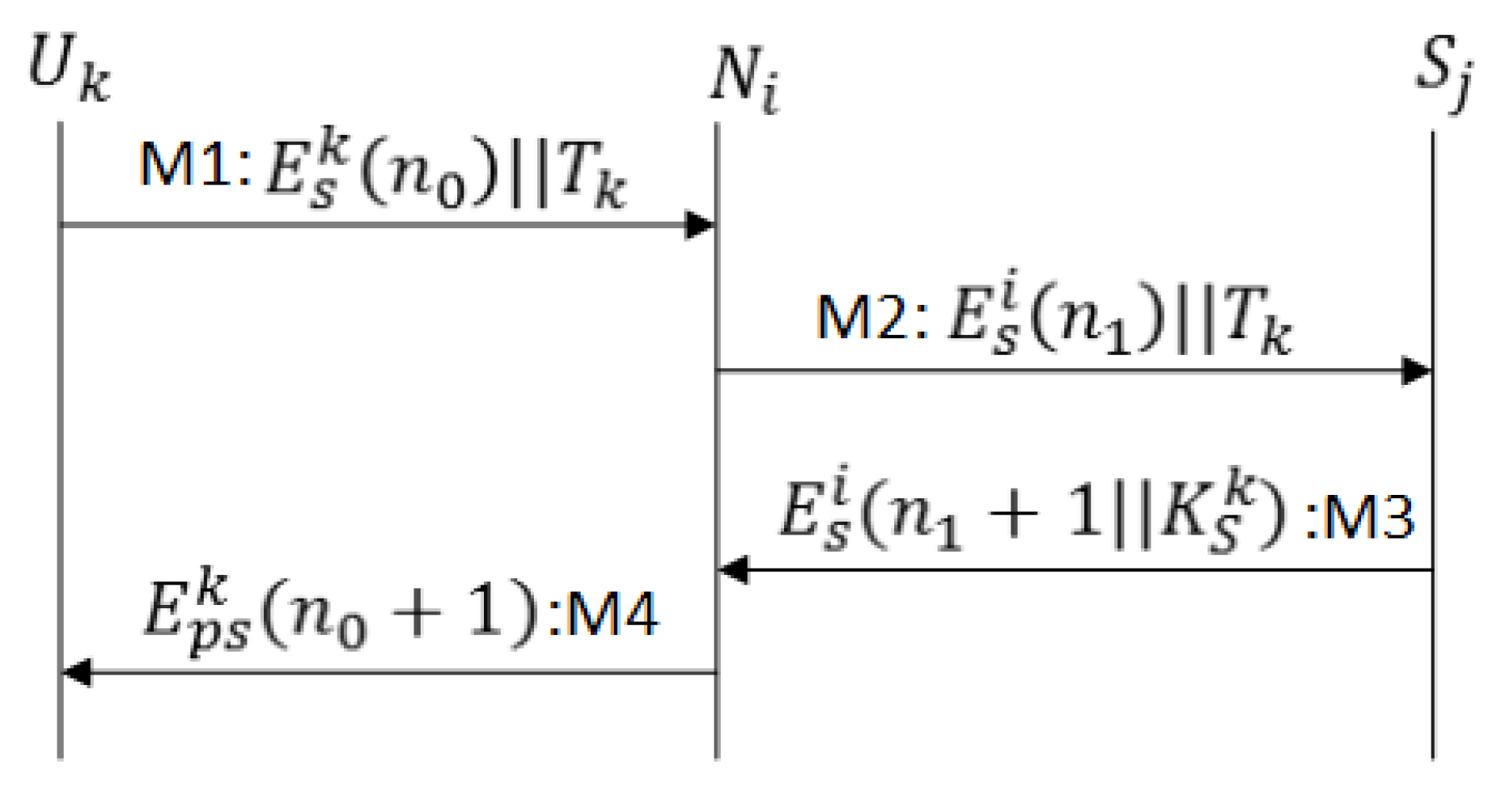
4.2.5. User-Sink Authentication Protocol (USiAP)
4.2.6. User- Sensor Authentication Protocol (USeAP)
- M1
- As shown in Figure 9, sends a JOIN message in conjunction with ticket and challenge encrypted with its ticket centered session key.
- M2
- Upon receiving the request from the forward the ticket and encrypted challenge to sink node
- M3
- Sink decrypts the ticket and retrieves s profile and session key , and if is a legitimate user node, sends and challenge response to .
- M4
- After challenge verification, generates a private session key and sends a challenge response encrypted with the private session key. also generates the private session key and verifies the challenge response.
5. Security Analysis
5.1. Informal Analysis and Discussion
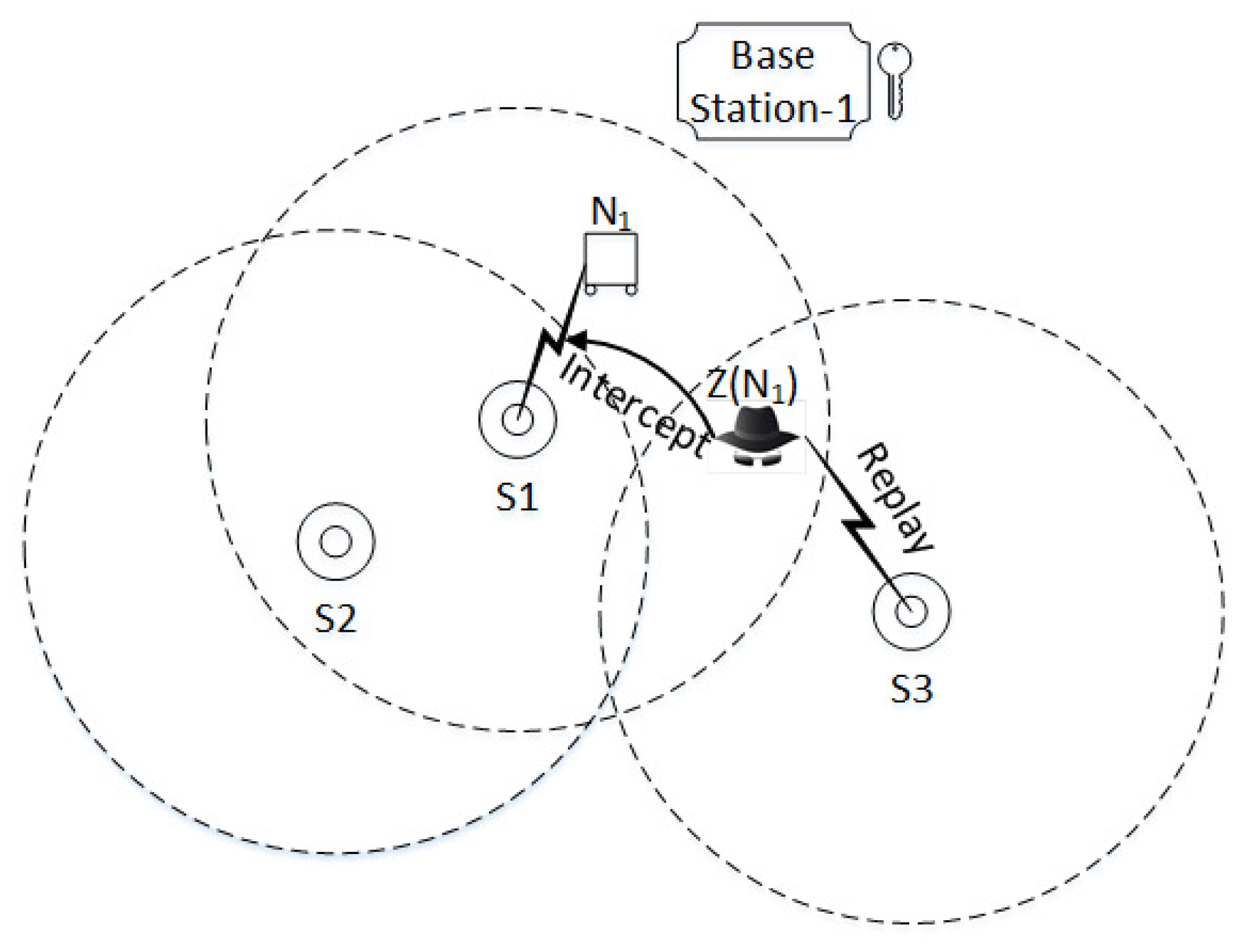
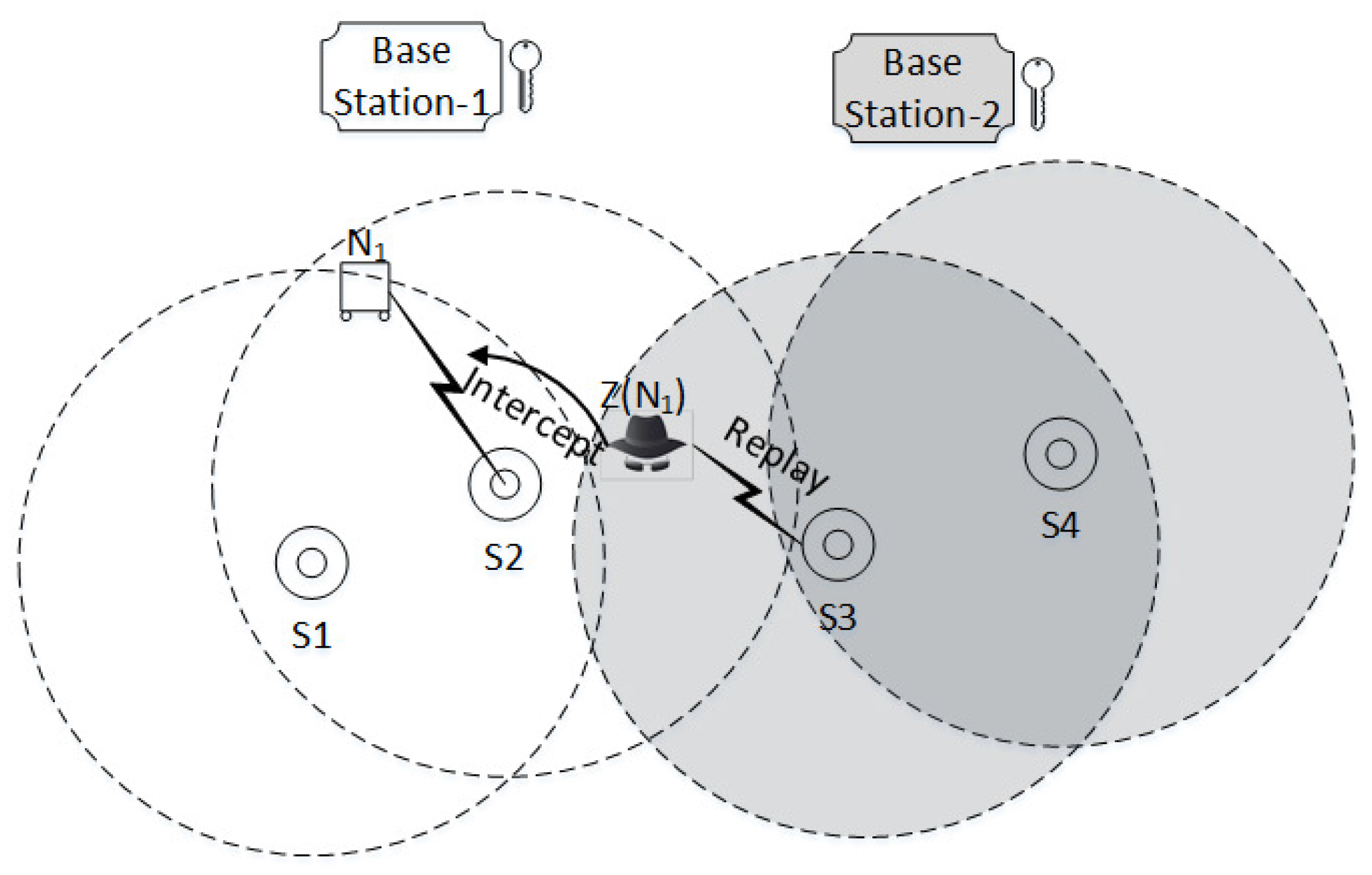
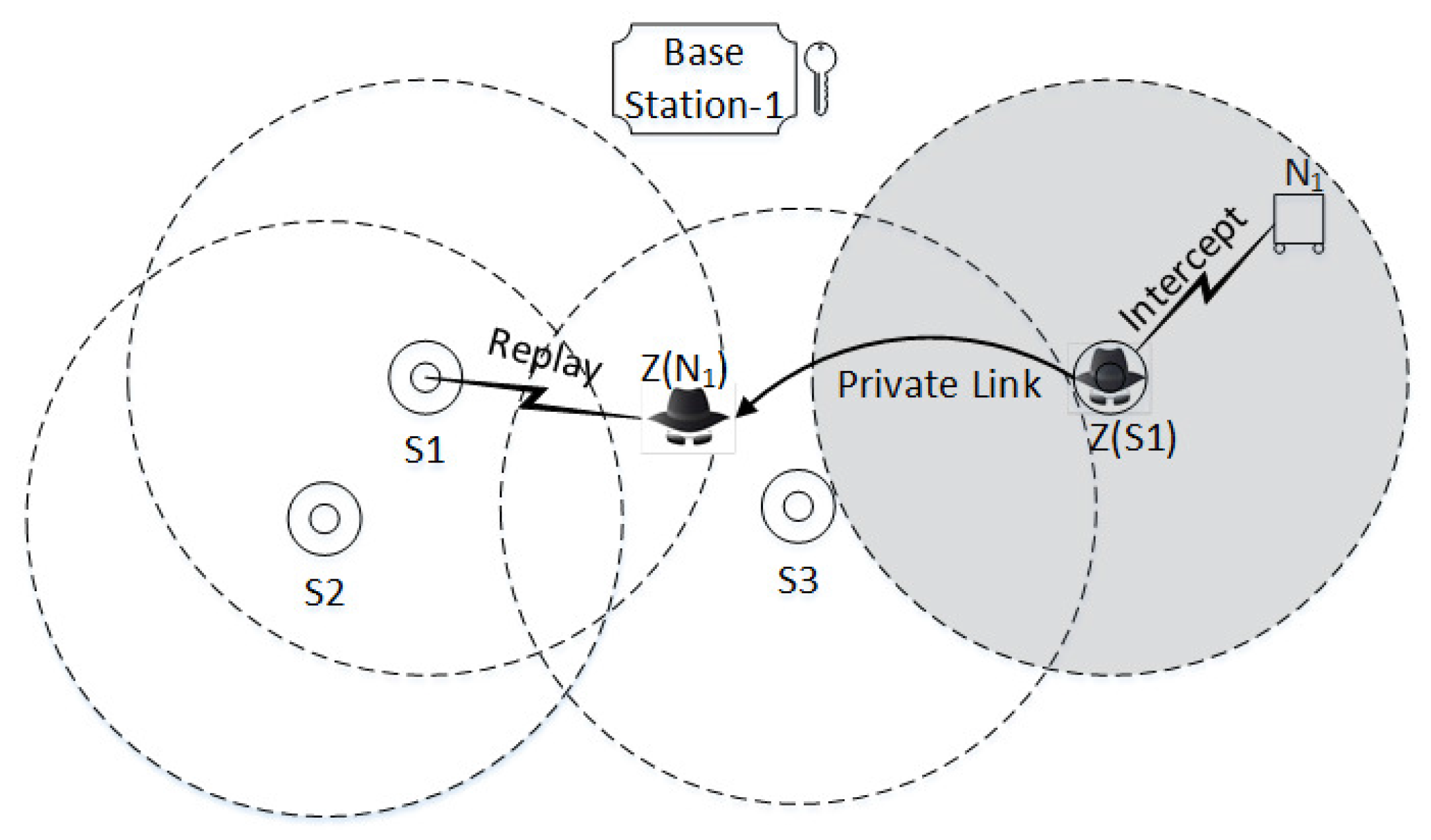
5.1.1. Replay, Multiplicity, Parallel and Man in Middle Attacks Against the SMSN
5.1.2. Black Hole Attack
5.1.3. Wormhole Attack
5.1.4. Analytical Attacks
5.1.5. Topological Centered Attacks
5.2. Formal Analysis Using BAN Logic
- believes X, or P would be enabled to believe X; in conclusion, P can take X as true.
- sees/receives X. P initially has or received a message X and P can see the contents of the message and is capable of repeating X.
- once said P has sent a message including the statement X. However, the freshness of message is unknown.
- controls X and should be trusted for formula/statement X.
- is fresh; it says, X never sent by any principal before.
- and Q shares a key K to communicate in a secure way and K is only known to P, Q and a trusted principal.
- The statement X is encrypted by key
- It stand for X combined with Y is anticipated to be secret and its implicit or explicit presence proves the identity of a principal who completes the .
- Message meaning rules: ,
- Nonce verification rule:
- Jurisdiction rule:
- Freshness rule:
- Believe rule:
- Session key rule:
5.2.1. BAN Logic Analysis of SAAP
- G1
- G2
- G3
- G4
- I1
- I2
- I3
- I4
- I5
- I6
- A1
- A2
- A3
- A4
- A5
- A6
- A7
- A8
- A9
- A10
- A11
- A12
- G1
- G2
- G3
- I1
- I2
- I3
- A1
- A2
- A3
- A4
- A5
- A6
5.3. Verifying Protocol Using Scyther Tool
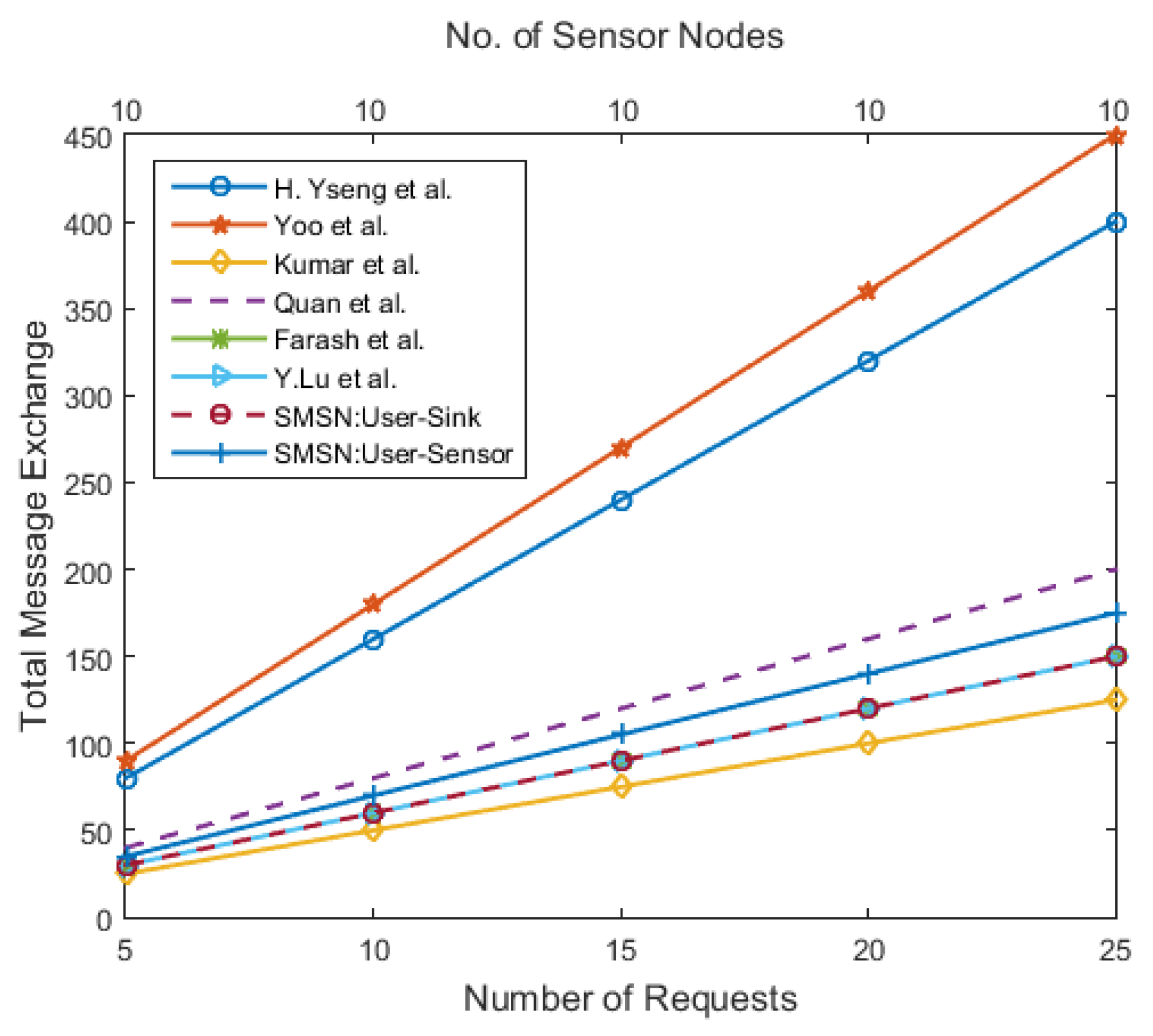
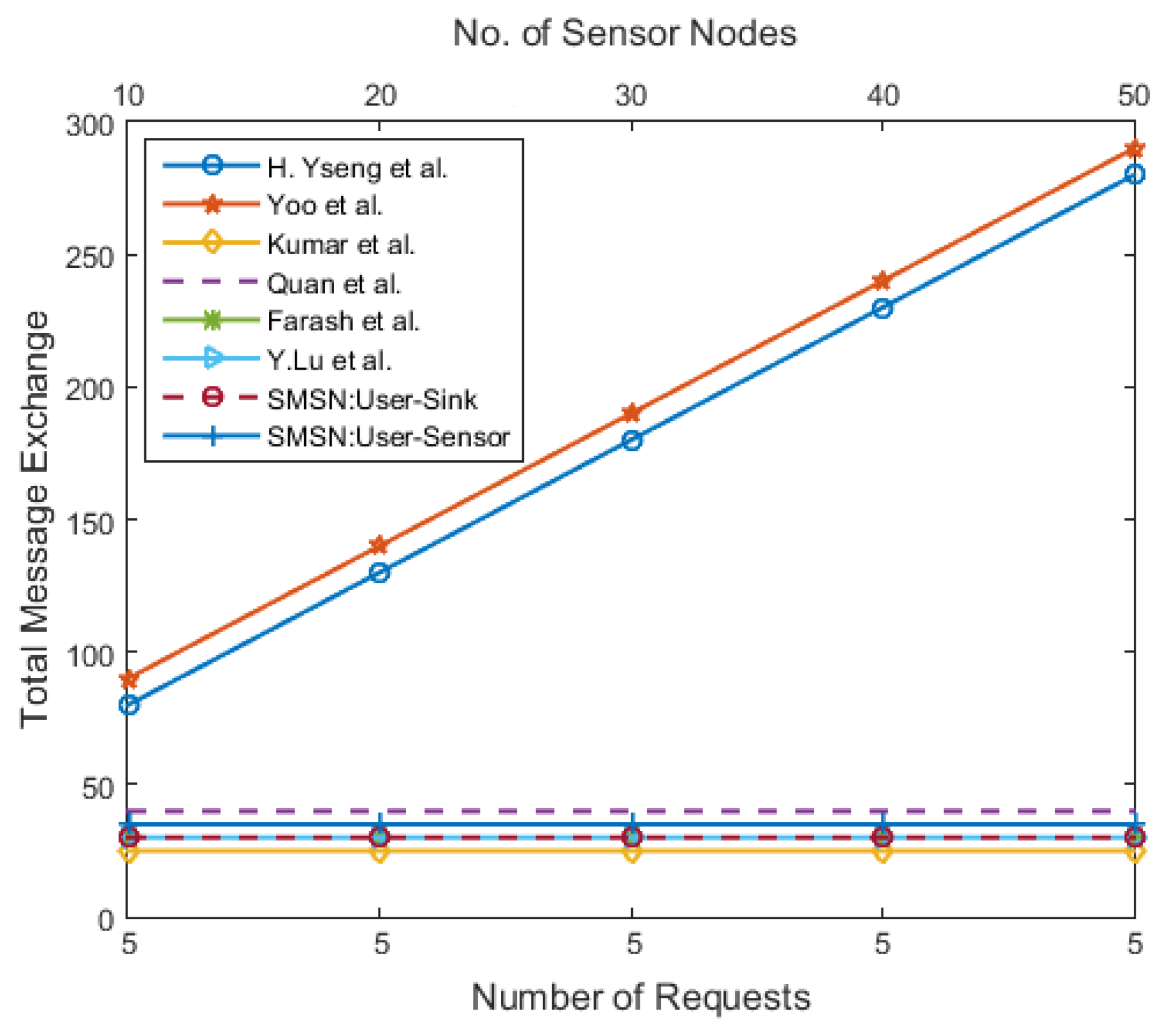
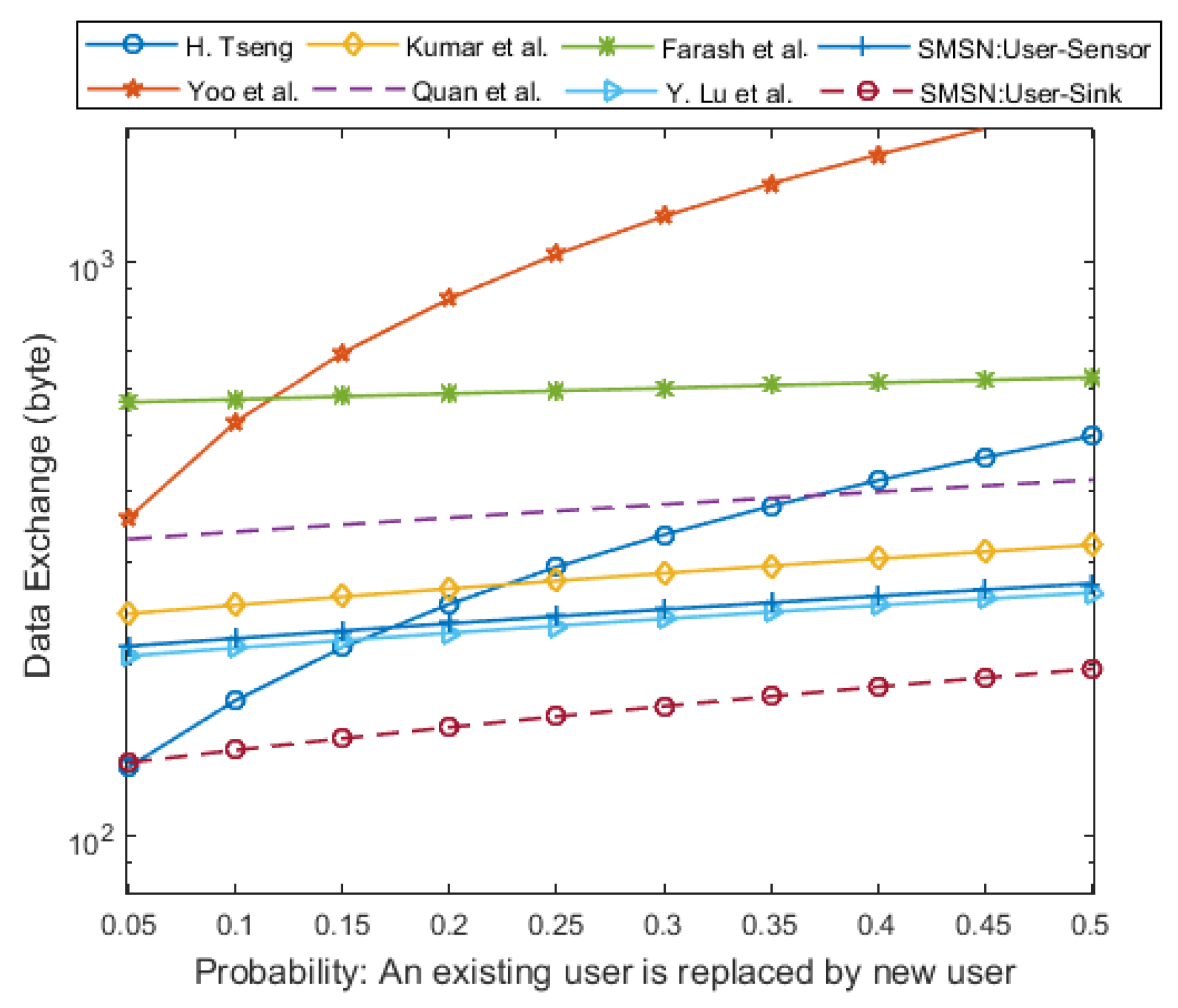
6. Performance Analysis
7. Conclusions
Acknowledgments
Author Contributions
Conflicts of Interest
Abbreviations
| WSN | Wireless Sensor Network |
| IoT | Internet of Things |
| SMSN-Protocol | Secure Mobile Sensor Network Protocol |
| BAN-logic | Burrows Abadi Needham logic |
| SAAP | Sensor Activation and Authentication Protocol |
| SRP1 | Sensor Re-Authentication Protocol-1 |
| SRP2 | Sensor Re-Authentication Protocol-2 |
| UAAP | User Activation and Authentication Protocol |
| USiAP | User-Sink Authentication Protocol |
| USeAP | User- Sensor Authentication Protocol |
References
- Koyama, K.; Maurer, U.M.; Okamoto, T.; Vanstone, S.A. New public-key schemes based on elliptic curves over the ring Zn. In Advances in Cryptology—CRYPTO ’91; Springer: Berlin/Heidelberg, Germany, 1992; pp. 252–266. [Google Scholar]
- Rivest, R.L. The RC5 encryption algorithm. In International Workshop on Fast Software Encryption; Springer: Berlin/Heidelberg, Germany, 1994; pp. 86–96. [Google Scholar]
- Wong, Y.; Attebury, G.; Ramamurthy, B.A. Survey of security issues in wireless sensor networks. IEEE Commun. Surv. 2006, 8, 2–23. [Google Scholar] [CrossRef]
- Zhang, J.; Varadharajan, V. Wireless sensor network key management survey and taxonomy. J. Netw. Comput. Appl. 2010, 33, 63–75. [Google Scholar] [CrossRef]
- Panic, G.; Stecklina, O.; Stamenkovic, Z. An embedded sensor node microcontroller with crypto-processors. Sensors 2016, 16, 607. [Google Scholar] [CrossRef] [PubMed]
- Kim, D.; An, S. PKC-Based DoS attacks-resistant scheme in wireless sensor networks. IEEE Sens. J. 2016, 16, 2217–2218. [Google Scholar] [CrossRef]
- Hancke, G.P.; Silva, B.C.; Hancke, G.P., Jr. The Role of Advanced Sensing in Smart Cities. Sensors 2012, 13, 393–425. [Google Scholar] [CrossRef] [PubMed]
- Sagl, G.; Resch, B.; Blaschke, T. Contextual sensing: Integrating contextual information with human and technical geo-sensor information for smart cities. Sensors 2015, 15, 17013–17035. [Google Scholar] [CrossRef] [PubMed]
- Flammini, A.; Sisinni, E. Wireless sensor networking in the internet of things and cloud computing era. Procedia Eng. 2014, 87, 672–679. [Google Scholar] [CrossRef]
- Bilal, M.; Kang, S.G. Time-Assisted authentication protocol. Int. J. Commun. Syst. 2017. [Google Scholar] [CrossRef]
- Tseng, H.R.; Jan, R.H.; Yang, W. An improved dynamic user authentication scheme for wireless sensor networks. In Proceedings of the IEEE Global Communications Conference, Washington, DC, USA, 26–30 November 2007. [Google Scholar]
- Yoo, S.G.; Park, K.Y.; Kim, J. A security-performance-balanced user authentication scheme for wireless sensor networks. Int. J. Distrib. Sens. Netw. 2012, 2012, 382810. [Google Scholar] [CrossRef]
- Kumar, P.; Gurtov, A.; Ylianttila, M.; Lee, S.; Lee, H. A strong authentication scheme with user privacy for wireless sensor networks. ETRI J. 2013, 35, 889–899. [Google Scholar] [CrossRef]
- Zhou, Q.; Tang, C.; Zhen, X.; Rong, C. A secure user authentication protocol for sensor network in data capturing. J. Cloud Comput. Adv. Syst. Appl. 2015, 4, 6. [Google Scholar]
- Farash, M.S.; Turkanovi, M.; Kumari, S.; Hölbl, M. An efficient user authentication and key agreement scheme for heterogeneous wireless sensor network tailored for the Internet of Things environment. Ad Hoc Netw. 2016, 36, 152–176. [Google Scholar] [CrossRef]
- Lu, Y.; Li, L.; Peng, H.; Yang, Y. An energy efficient mutual authentication and key agreement scheme preserving anonymity for wireless sensor networks. Sensors 2016, 16, 837. [Google Scholar] [CrossRef] [PubMed]
- Cremers, C. The scyther tool: Verification, falsification, and analysis of security protocols. In International Conference on Computer Aided Verification; Springer: Berlin/Heidelberg, Germany, 2008; pp. 414–418. [Google Scholar]
- Cremers, C.; Mauw, S. Security properties. In Operational Semantics and Verification of Security Protocols; Springer Science & Business Media: Berlin/Heidelberg, Germany, 2012. [Google Scholar]
- Lowe, G. A hierarchy of authentication specifications. In Proceedings of the 10th on Computer Security Foundations workshop, Canton, MA, USA, 10–12 June 1997. [Google Scholar]
- Cremers, C.; Mauw, S.; De Vink, E.P. Injective synchronisation: An extension of the authentication hierarchy. Theor. Comput. Sci. 2006, 367, 139–161. [Google Scholar] [CrossRef]
- Wong, K.H.M.; Zheng, Y.; Cao, J.; Wang, S. A dynamic user authentication scheme for wireless sensor networks. In Proceedings of the IEEE International Conference on Sensor Networks, Ubiquitous, and Trustworthy Computing, Taichung, Taiwan, 5–7 June 2006. [Google Scholar]
- Das, M.L. Two-Factor user authentication in wireless sensor networks. IEEE Trans. Wirel. Commun. 2009, 8, 1086–1090. [Google Scholar] [CrossRef]
- Han, K.; Kim, K.; Shon, T. Untraceable mobile node authentication in WSN. Sensors 2010, 10, 4410–4429. [Google Scholar] [CrossRef] [PubMed]
- Han, K.; Shon, T. Efficient mobile sensor authentication in smart home and WPAN. IEEE Trans. Consum. Electron. 2010, 56, 591–596. [Google Scholar] [CrossRef]
- Yeh, H.; Chen, T.; Liu, P.; Kim, T.; Wei, H. A secured authentication protocol for wireless sensor networks using elliptic curves cryptography. Sensors 2011, 11, 4767–4779. [Google Scholar] [CrossRef] [PubMed]
- Kumari, S.; Om, H. Authentication protocol for wireless sensor networks applications like safety monitoring in coal mines. Compu. Netw. 2016, 104, 137–154. [Google Scholar] [CrossRef]
- Kumari, S.; Khan, M.K.; Atiquzzaman, M. User authentication schemes for wireless sensor networks: A review. Ad Hoc Netw. 2015, 27, 159–194. [Google Scholar] [CrossRef]
- Xie, M.; Han, S.; Tian, B.; Parvin, S. Anomaly detection in wireless sensor networks: A survey. J. Netw. Comput. Appl. 2011, 34, 1302–1325. [Google Scholar] [CrossRef]
- Ko, L. A novel dynamic user authentication scheme for wireless sensor networks. In Proceedings of the IEEE International Symposium on Wireless Communication Systems, Reykjavik, Iceland, 21–24 October 2008. [Google Scholar]
- Chen, T.; Shih, W. A robust mutual authentication protocol for wireless sensor networks. ETRI J. 2010, 32, 704–712. [Google Scholar] [CrossRef]
- Khan, M.K.; Alghathbar, K. Cryptanalysis and security improvements of ’two-factor user authentication in wireless sensor networks’. Sensors 2010, 10, 2450–2459. [Google Scholar] [CrossRef] [PubMed]
- Burrows, M.; Abadi, M.; Needham, R.M. A logic of authentication. In Proceedings of the Royal Society of London A: Mathematical, Physical and Engineering Sciences; The Royal Society: London, UK, 1989; Volume 426, pp. 233–271. [Google Scholar]
- Lee, C.-C.; Li, C.-T.; Chen, S.-D. Two attacks on a two-factor user authentication in wireless sensor network. Parallel Process. Lett. 2011, 21, 21–26. [Google Scholar] [CrossRef]
- Gligor, V.D.; Kailar, R.; Stubblebine, S.; Gong, L. Logics for cryptographic protocols-virtues and limitations. In Proceedings of the IEEE Computer Security Foundations Workshop IV, Franconia, NH, USA, 18–20 June 1991; pp. 219–226. [Google Scholar]
- Boyd, C.; Mao, W. On a limitation of BAN logic. In Advances in Cryptology- EUROCRYPT ’93; Springer: Berlin/Heidelberg, Germany, 1993; pp. 240–247. [Google Scholar]
- Kumar, P.; Lee, S.; Lee, H. E-SAP: Efficient-Strong authentication protocol for healthcare applications using wireless medical sensor networks. Sensors 2012, 12, 1625–1647. [Google Scholar] [CrossRef] [PubMed]
- He, D.; Kumar, N.; Chen, J.; Lee, C.; Chilamkurti, N.; Yeo, S. Robust anonymous authentication protocol for health-care applications using wireless medical sensor networks. Multimed. Syst. 2015, 21, 49–60. [Google Scholar] [CrossRef]
- Armando, A.; Basin, D.; Boichut, Y. The AVISPA Tool for the Automated Validation of Internet Security Protocols and Applications. Available online: https://www.inf.ethz.ch/personal/basin/pubs/avispa05.pdf (accessed on 22 September 2016).
- Li, C.-T.; Weng, C.-Y.; Lee, C.-C. An advanced temporal credential-based security scheme with mutual authentication and key agreement for wireless sensor networks. Sensors 2013, 13, 9589–9603. [Google Scholar] [CrossRef] [PubMed]
- Bilal, M.; Kang, S.G. A secure key agreement protocol for dynamic group. Clust. Comput. 2017. [Google Scholar] [CrossRef]
- Perrig, A.; Canetti, R.; Tygar, J.D.; Song, D. The TESLA Broadcast Authentication Protocol. Available online: https://www.cs.berkeley.edu/~tygar/papers/TESLA_broadcast_authentication_protocol.pdf (accessed on 16 June 2016).
- Daemen, J.; Rijmen, V. AES Proposal: Rijndael. National Institute of Standards and Technology. Available online: https://csrc.nist.gov/archive/aes/rijndael/Rijndael-ammended.pdf (accessed on 25 September 2016).
- Schneier, B.; Kelsey, J.; Whiting, D.; Wagner, D.; Hal, C. Twofish: A 128-bit Block Cipher. Available online: https://www.schneier.com/academic/paperfiles/paper-twofish-paper.pdf (accessed on 25 September 2016).
- Burwick, C.; Coppersmith, D.; D’Avignon, E.; Gennaro, R.; Halevi, S.; Jutla, C.; Matyas, S.M.; O’Connor, L.; Peyravian, M.; Safford, D.; et al. MARS-a Candidate Cipher for AES. Available online: http://www.nada.kth.se/kurser/kth/2D1449/99-00/mars.pdf (accessed on 25 September 2016).
- Schneier, B. Description of a new variable-length key, 64-bit block cipher (Blowfish). In Fast Software Encryption; Springer: Berlin/Heidelberg, Cermany, 1994; pp. 191–204. [Google Scholar]
- Kumar, V.; Kumar, R. An adaptive approach for detection of blackhole attack in mobile Ad hoc network. Proced. Comput. Sci. 2015, 48, 472–479. [Google Scholar] [CrossRef]
- Misra, S.; Bhattarai, K.; Xue, G. BAMBi: Blackhole attacks mitigation with multiple base stations in wireless sensor networks. In Proceedings of the IEEE International Conference on Communications, Kyoto, Japan, 5–9 June 2011. [Google Scholar]
- Poongodi, T.; Karthikeyan, M. Localized secure routing architecture against cooperative black hole attack in mobile Ad hoc networks. Wirel. Pers. Commun. 2016, 90, 1039–1050. [Google Scholar] [CrossRef]
- Hu, Y.; Perrig, A.; Johnson, D.B. Wormhole attacks in wireless networks. IEEE J. Sel. Areas Commun. 2006, 24, 370–380. [Google Scholar]
- Imran, M.; Khan, F.A.; Jamal, T.; Durad, M.H. Analysis of detection features for wormhole attacks in MANETs. Proced. Comput. Sci. 2015, 56, 384–390. [Google Scholar] [CrossRef]
- Choi, Y.; Lee, Y.; Won, D. Advances in computer science and ubiquitous computing. In Cryptanalysis on Symmetric Key Techniques Based Authentication Scheme for Wireless Sensor Networks; Springer: Berlin/Heidelberg, Germany, 2015; Volume 373, pp. 7–13. [Google Scholar]
- Zhou, Y.; Fang, Y. Defend against topological attacks in sensor networks. In Proceedings of the IEEE Military Communications Conference, Atlantic City, NJ, USA, 17–20 October 2005. [Google Scholar]
- Gabrielli, A.; Mancini, L.V.; Setia, S.; Jajodia, S. Securing Topology Maintenance Protocols for sensor networks. IEEE Trans. Dependable Secur. Comput. 2011, 8, 450–465. [Google Scholar] [CrossRef]
- Bouk, H.S.; Ahmed, S.H.; Kim, D.; Song, H. Named-Data-Networking-Based ITS for smart cities. IEEE Commun. Mag. 2017, 55, 105–111. [Google Scholar] [CrossRef]
- Bilal, M.; Kang, S.G. A cache management scheme for efficient content eviction and replication in cache networks. IEEE Access 2017, 5, 1692–1701. [Google Scholar] [CrossRef]
- Ahmed, S.H.; Bouk, H.S.; yaqub, M.A.; Kim, D.; Song, H. CODIE: Controlled data and interest evaluation in vehicular named data networks. IEEE Trans. Veh. Technol. 2016, 65, 3954–3963. [Google Scholar] [CrossRef]
- Bilal, M.; Kang, S.G. Time aware least recent used (TLRU) cache management policy in ICN. In Proceedings of the IEEE 16th International Conference on Advanced Communications Technology, Pyeongchang, Korea, 16–19 February 2014; pp. 528–532. [Google Scholar]
- Ahmed, S.H.; Bouk, H.S.; Kim, D. RUFS: RobUst forwarder selection in vehicular content-centric networks. IEEE Commun. Lett. 2015, 19, 1616–1619. [Google Scholar] [CrossRef]
- Ahmed, S.H.; Kim, D. Named data networking-based smart home. ICT Express 2016, 2, 130–134. [Google Scholar] [CrossRef]

| Parameter | Settings |
|---|---|
| Number of Runs | 1∼3 |
| Matching Type | Find all Type Flaws |
| Search pruning | Find All Attacks |
| Number of pattern per claim | 10 |
| Claims | H. Tseng [11] | Yoo et al. [12] | Kumar et al. [13] | Quan et al. [14] | Farash et al. [15] | Y. Lu et al. [16] | SMSN | ||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Aliveness | N | N | N | N | N | N | Y | N | N | Y | N | N | Y | Y | N | N | N | Y | Y | Y | Y |
| Weak Agreement | N | N | N | N | N | N | Y | N | N | Y | N | N | Y | Y | N | N | N | Y | O | Y | Y |
| Non-injective Agreement | N | N | N | N | N | N | O | N | N | Y | N | N | Y | Y | N | N | N | Y | O | Y | Y |
| Non-injective Synch. | N | N | N | N | N | N | O | N | N | Y | N | N | Y | Y | N | N | N | Y | O | Y | Y |
| Schemes | Phase | Comp. Complexity | Comm. Complexity | Comm. Cost in Bytes | Time Synch. |
|---|---|---|---|---|---|
| H. Tseng [11] | Registration | - | |||
| Login-Authentication | |||||
| Yoo et al. [12] | Registration | - | |||
| Login-Authentication | |||||
| Kumar et al. [13] | Registration | - | |||
| Login-Authentication | |||||
| Quan et al. [14] | Registration | ||||
| Login-Authentication | |||||
| Farash et al. [15] | Registration | ||||
| Login-Authentication | |||||
| Y. Lu et al. [16] | Registration | - | |||
| Login-Authentication | |||||
| SMSN (User-Sink) | Registration | - | |||
| Login-Authentication | |||||
| SMSN (User-Sensor) | Registration | - | |||
| Login-Authentication |
© 2017 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Bilal, M.; Kang, S.-G. An Authentication Protocol for Future Sensor Networks. Sensors 2017, 17, 979. https://doi.org/10.3390/s17050979
Bilal M, Kang S-G. An Authentication Protocol for Future Sensor Networks. Sensors. 2017; 17(5):979. https://doi.org/10.3390/s17050979
Chicago/Turabian StyleBilal, Muhammad, and Shin-Gak Kang. 2017. "An Authentication Protocol for Future Sensor Networks" Sensors 17, no. 5: 979. https://doi.org/10.3390/s17050979
APA StyleBilal, M., & Kang, S.-G. (2017). An Authentication Protocol for Future Sensor Networks. Sensors, 17(5), 979. https://doi.org/10.3390/s17050979





