An Improved Forwarding of Diverse Events with Mobile Sinks in Underwater Wireless Sensor Networks
Abstract
:1. Introduction
- Depth Threshold: Depth threshold is a global depth parameter to control the number of nodes involved in forwarding process. Greater the values of depth threshold lesser the number of nodes involved in forwarding process. Value of depth threshold is always less than the transmission range.
- Forwarding Functions: Forwarding function is a routing metric which can be dependent on different parameters of nodes, like absolute depth, depth difference, residual energy, transmission range and depth threshold. Different forwarding functions have been defined in literature and included in details in the next sections.
- Holding Time: Holding time is assigned to each node to avoid redundant transmissions and collision. It is the time during which a node holds the packet and avoids any transmission.
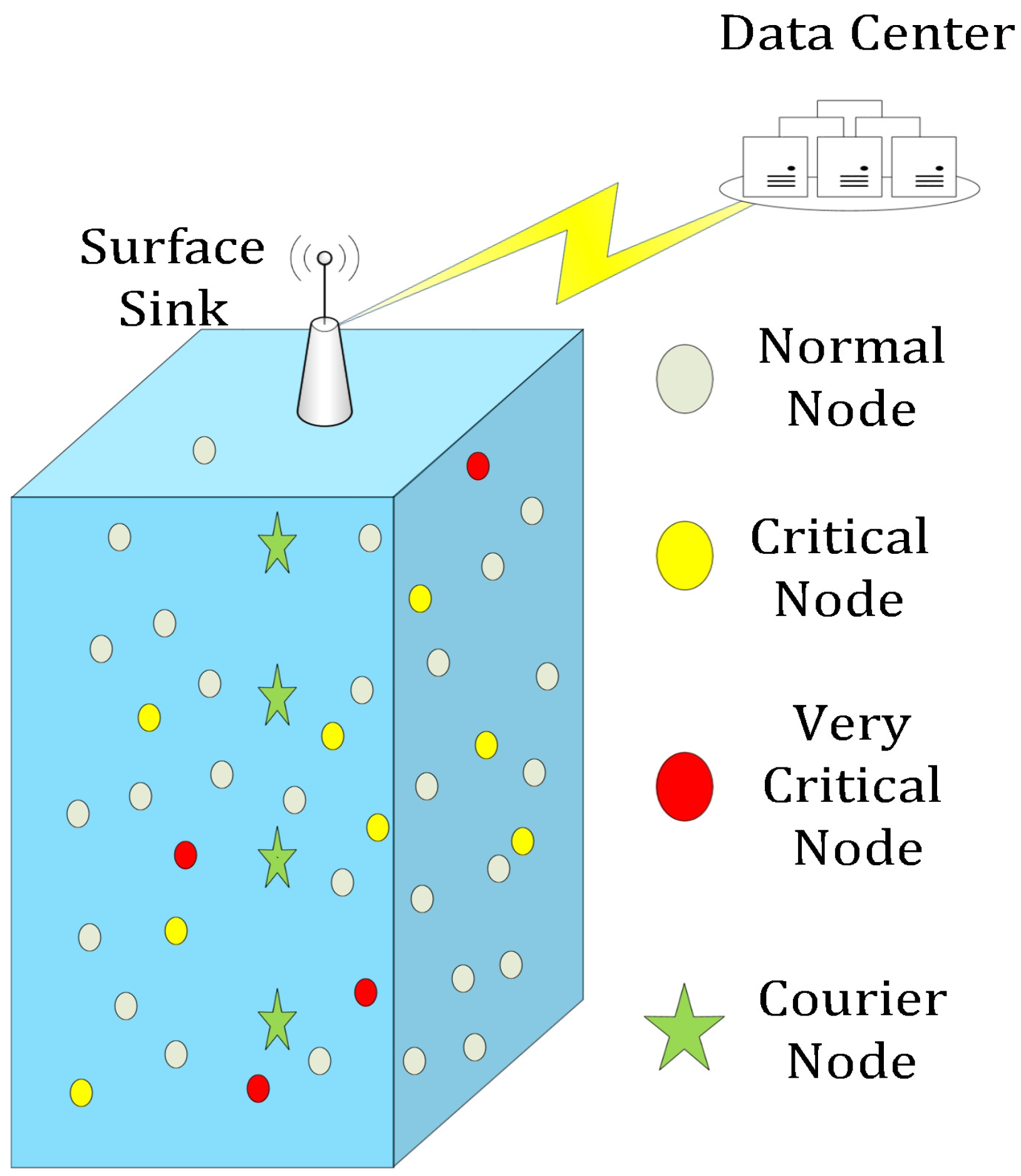
- We have considered a diverse environment in which multiple types of events are occurring in the sensing field. These events are named as critical, very critical and normal. Critical and very critical events are delay sensitive in nature so forwarding to surface sink is planned for these types of event using respective forwarding functions in different depth regions. Normal events are sent to the mobile sinks (AUV: Autonomous Underwater Vehicle or CN: Courier Node) patrolling in the network.
- Forwarding functions defined in literature use different parameters in different depth regions. However the values of different forwarding functions must be comparable with each other to ensure the steady flow of packets. Analysis on the range of previously defined forwarding function reveals the incomparable ranges of different forwarding functions. Hence the forwarding functions are redefined to ensure their comparable values in different depth region for the steady flow of packets.
- Mobile sinks are deployed to collect the data from the nodes which has sensed normal events. Hence mobility of these nodes is influenced by the distribution and rate of data generation of normal nodes. We have proposed two different mobility schemes for the mobile sinks.
2. Background and Related Work
2.1. Localization Based Routing Protocols
2.2. Localization Free Routing Protocols
3. Underwater Channel Model
- Transmission delay: Transmission delay to a packet of length l caused by a node n is given by following formula.where r is data rate with value 250,000 bps.
- Propagation delay: Propagation delay of an acoustic signal moving with velocity v between a sender i and receiver j separated by distance is given by:The speed of acoustic signal 1500 ms which is calculated using Equation (8). Sum of both type of delay constitutes to one hop delay.
4. Problem Statement and Motivation
- Initially, we present a comprehensive analysis on the ranges of forwarding functions defined in previous protocols. We have identified problems in those forwarding functions and redefined them in next section. These redefined forwarding functions causes much better and systematic forwarding.
- In second part of this section we explain broadcasting overhead issue in deep sea acoustic networks and motivation for event segregation approach.
4.1. Forwarding Functions Analysis
4.2. Motivation for Event Segregation Approach
5. ESDR: Event Segregation Based Delay Sensitive Routing
- In first subsection network initialization and node deployment is explained.
- Motivation for event segregation and its positive impacts on network are explained in this subsection.
- Improvements in terms of forwarding function calculation process and holding time calculation process is explained in subsequent subsections.
- Mobility of mobile sink is also impacted by event segregation approach. Mobility of deployed courier nodes in ESDR is explained in this subsection.
5.1. Network Initialization and Node Deployment
5.2. Statistical Event Generation and Segregation
5.3. Packets Forwarding Strategy
5.4. Improvements in Terms of Forwarding Function
5.5. Improvements in Terms of Holding Time
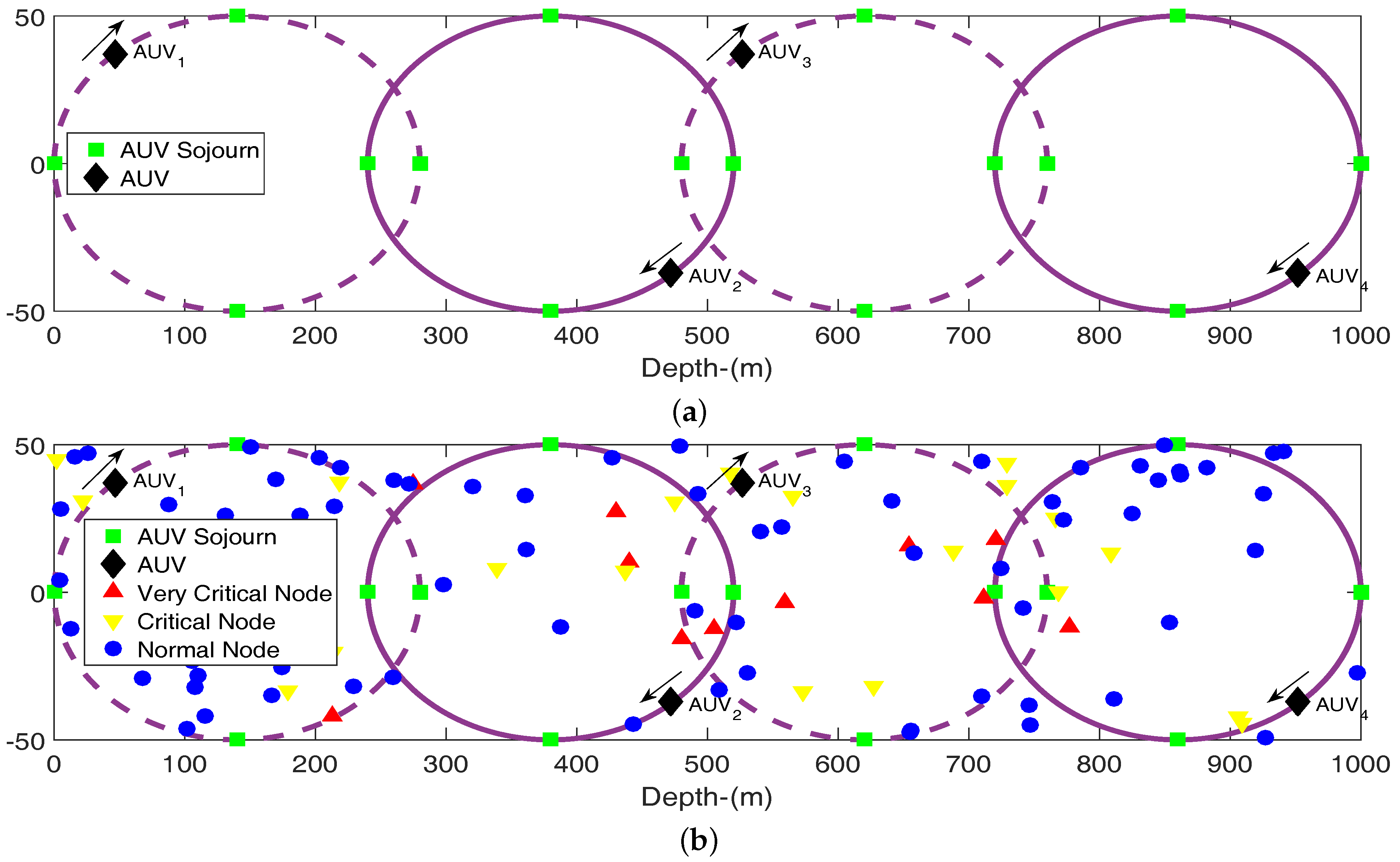
5.6. Mobility of Mobile Sinks
5.6.1. Synchronized and Uniform Mobility of AUV
5.6.2. Adaptive Mobility of Courier Nodes
6. Performance Evaluation
6.1. Performance Evaluation
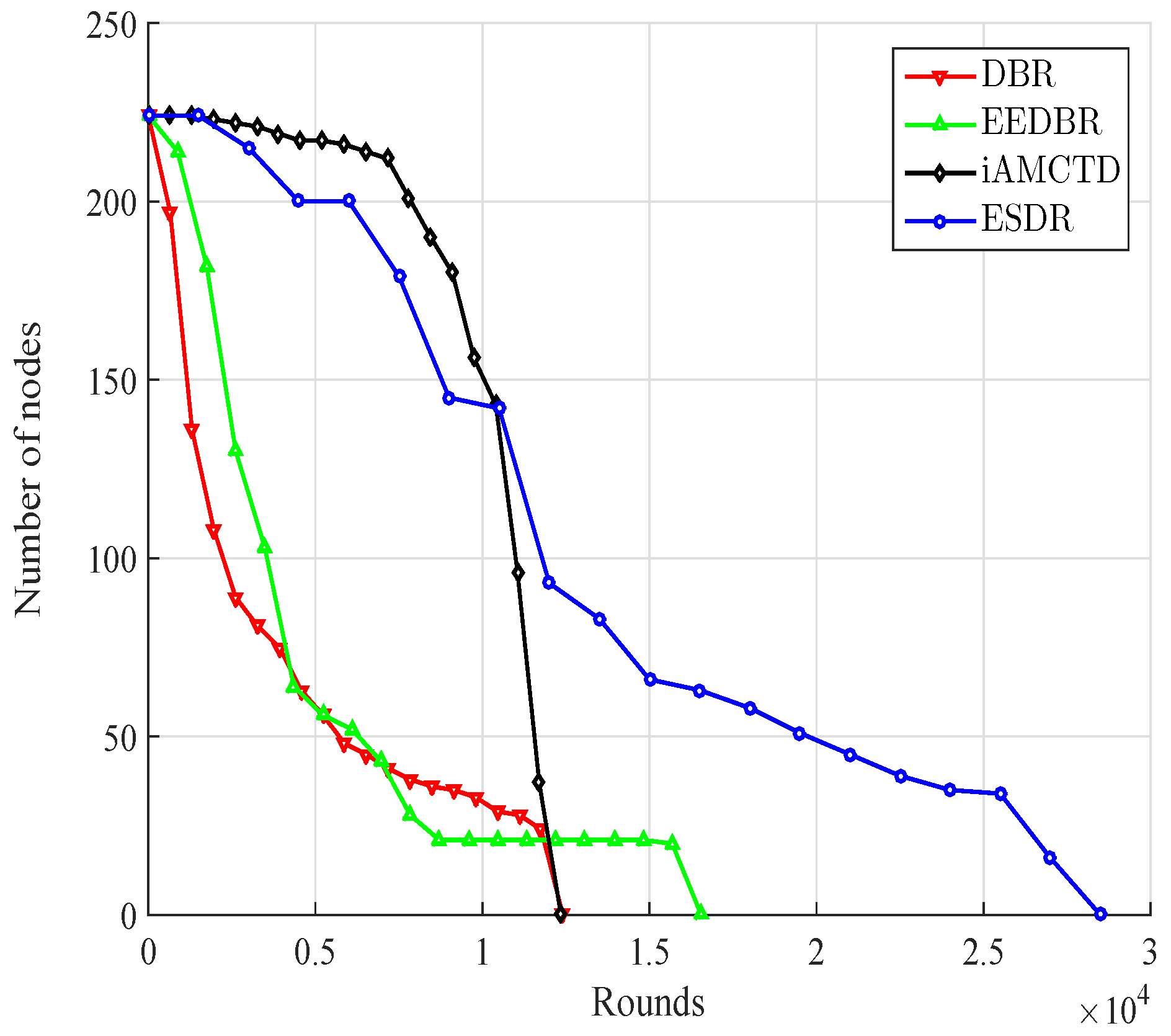
- Stability period: Time from the start of network operation till the death of first nodes is termed as stability period, whereas time from the death of first node till the death of last node is termed as instability period.
- Halflife: Halflife of network is defined as the time till the death of half nodes.
- Lifetime: Lifetime of network is the time till the death of all nodes.
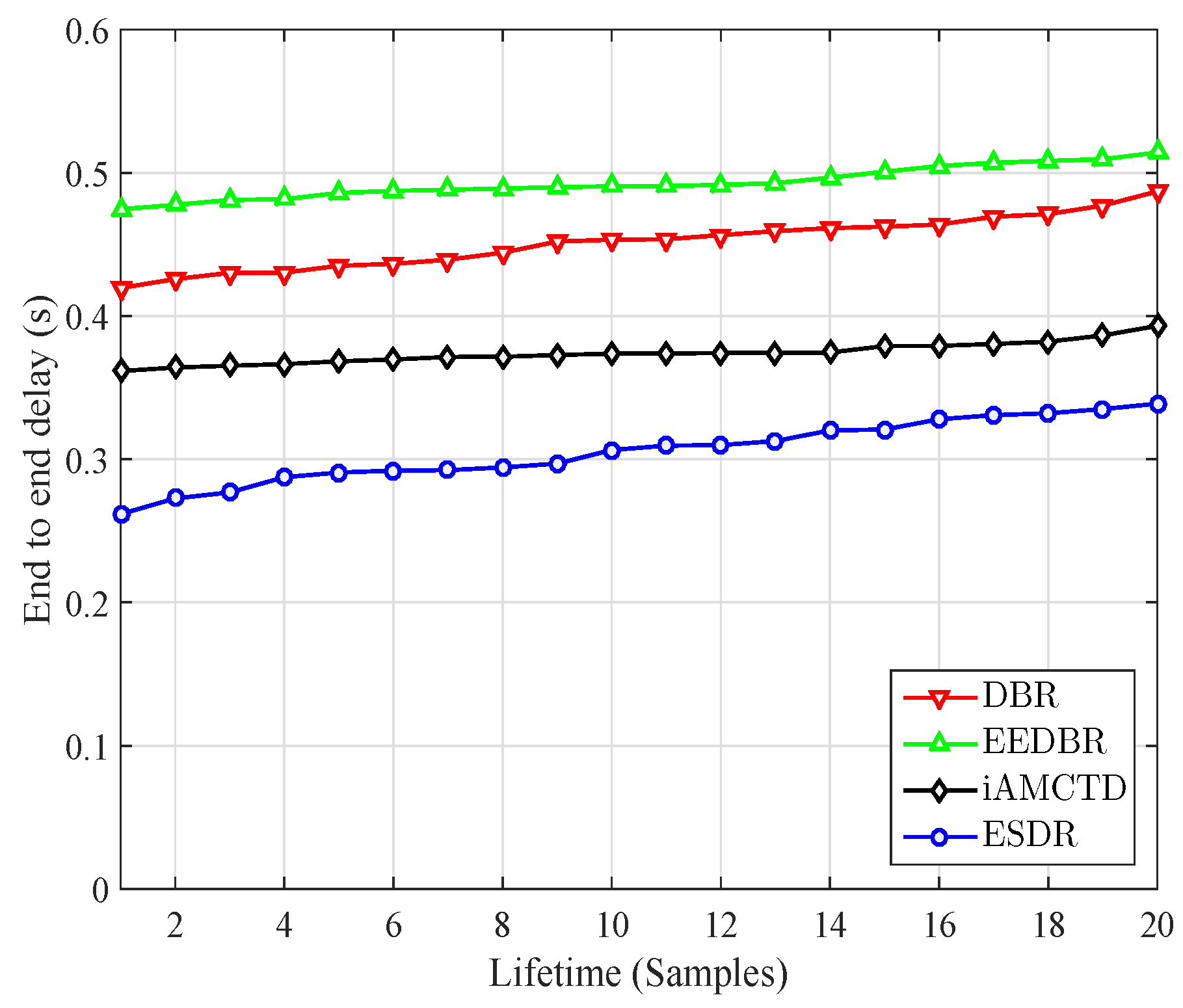
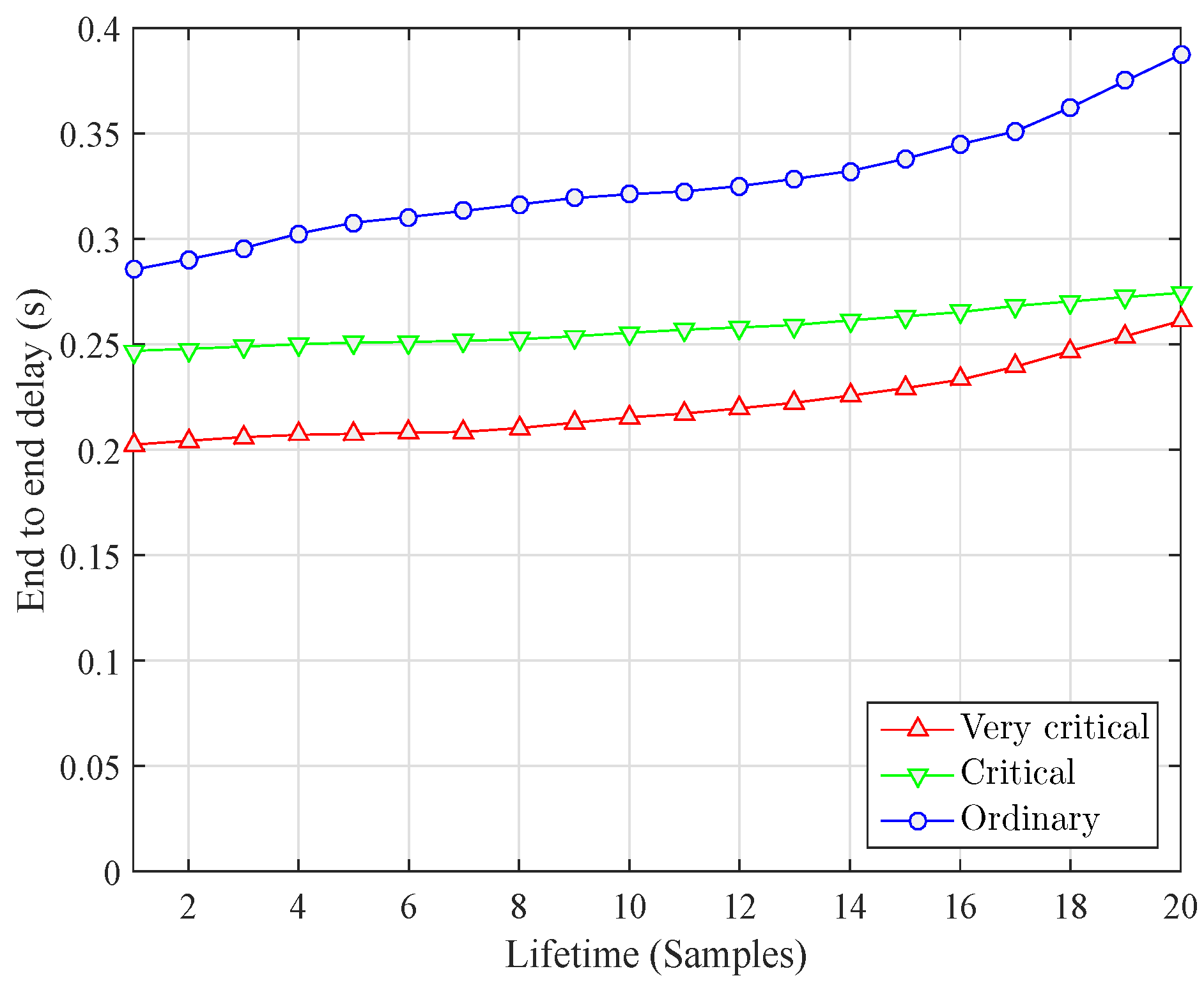
- Average end to end delay: Average end to end delay is mean of accumulated sum of propagation and transmission delays of all nodes.
- Throughput: Throughput is considered in terms of following two aspects:
- Packet sent to and received at sink: Number of packets sent to sink are dependent on type of application. In event driven or threshold sensitive applications some selected nodes are packet generator nodes, while in other type all the nodes have equal probability to generate the packet after some regular interval and sent to sink. Number of packets successively received at sink is less than the number of packets sent to sink.
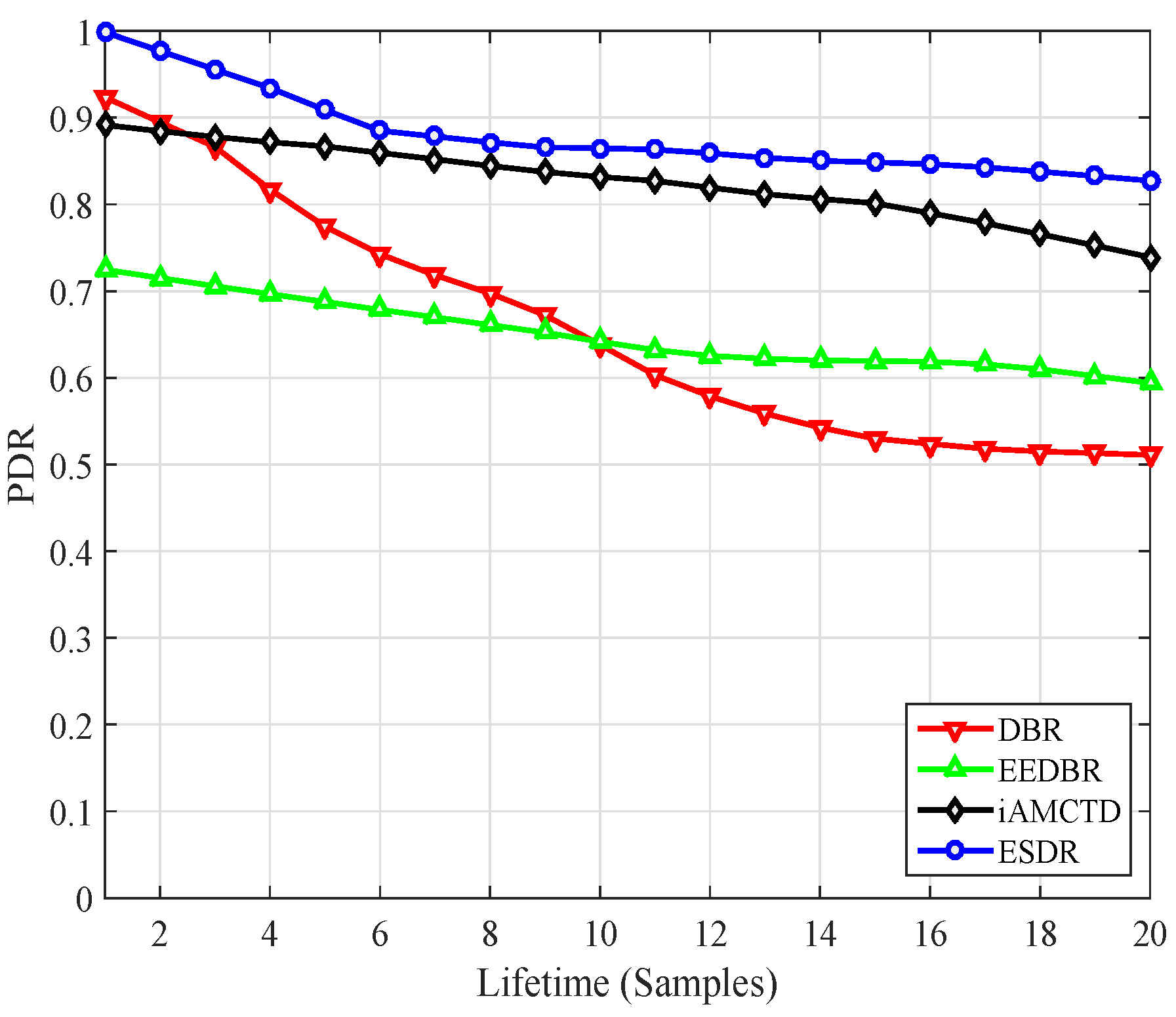
- PDR—Packet Delivery Ratio: PDR is the ratio of number of packets received at sink to number of packets sent to sink. In ideal case where no packet is dropped PDR is equal 1, otherwise its value is less than 1 and greater than 0.
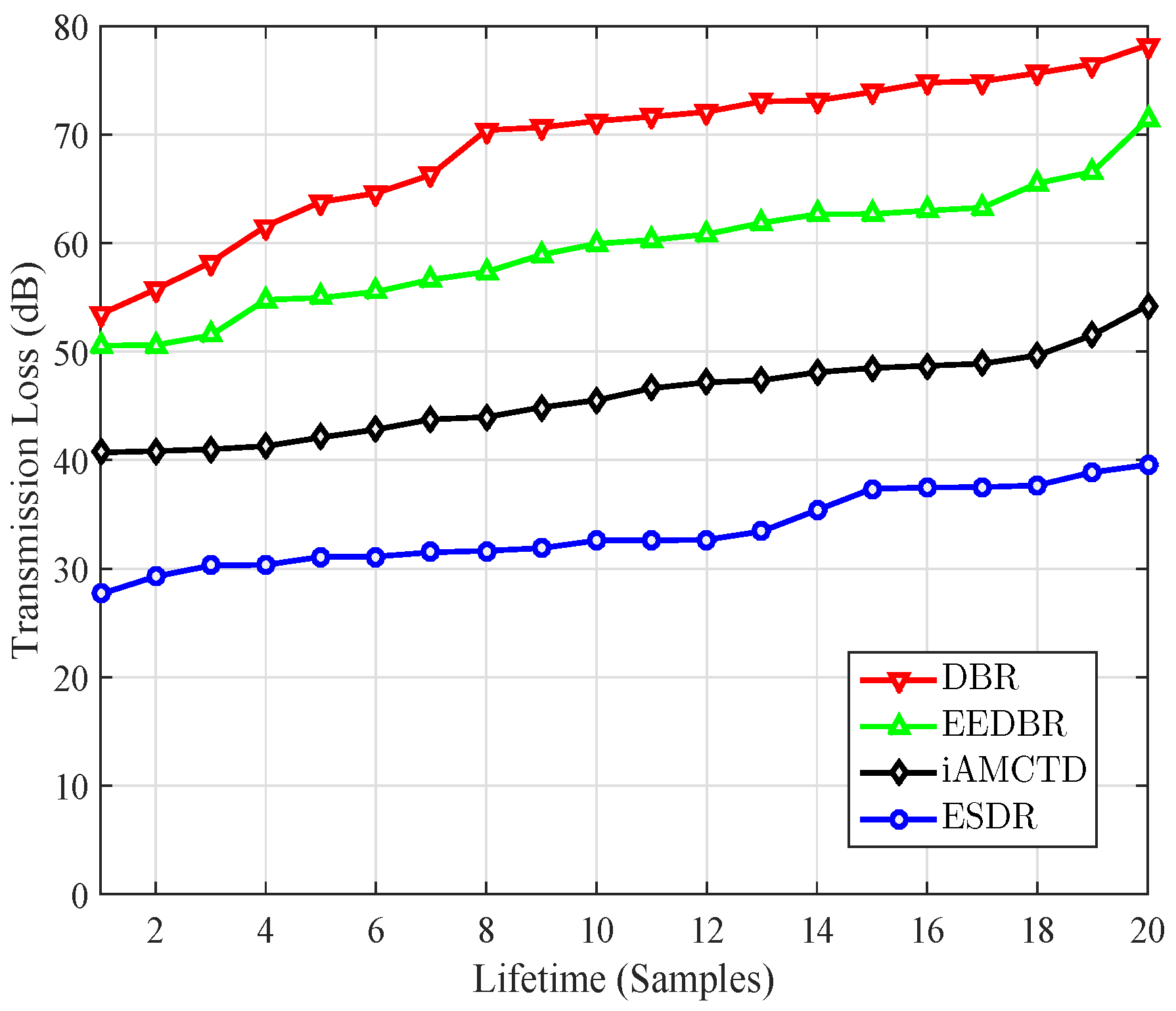
- Transmission loss: Transmission loss is the average decrease in sound energy/intensity level as it propagates through water.
6.1.1. Network Lifetime
6.1.2. Average End to End Delay
6.1.3. Throughput
6.1.4. Transmission Loss
7. Conclusions and Future Work
Acknowledgments
Author Contributions
Conflicts of Interest
References
- Manjula, R.B.; Manvi, S.S. Issues in underwater acoustic sensor networks. Int. J. Comput. Electr. Eng. 2011, 3, 101–110. [Google Scholar]
- Ahmad, A.; Wahid, A.; Kim, D. AEERP: AUV aided energy efficient routing protocol for underwater acoustic sensor network. In Proceedings of the 8th ACM Workshop on Performance Monitoring and Measurement of Heterogeneous Wireless and Wired Networks, Barcelona, Spain, 3–8 November 2013; pp. 53–60.
- Anand, J.; Titus, S. Analysis of depth based routing protocols in under water sensor networks. Int. Rev. Comput. Softw. 2013, 8, 2389–2402. [Google Scholar]
- Jayakumar, G.; Gopinath, G. Ad hoc mobile wireless networks routing protocols—A review. J. Comput. Sci. 2007, 3, 574–582. [Google Scholar] [CrossRef]
- Kaur, R.; Sharma, C. Review paper on performance analysis of AODV, DSDV, OLSR on the basis of packet delivery. IOSR J. Comput. Eng. 2013, 11, 51–55. [Google Scholar] [CrossRef]
- Jacquet, P.; Mühlethaler, P.; Clausen, T.; Laouiti, A.; Qayyum, A.; Viennot, L. Optimized link state routing protocol for ad hoc networks. In Proceedings of the IEEE International Multi Topic Conference 2001: Technology for the 21st Century, Lahore, Pakistan, 28–30 December 2001; pp. 62–68.
- Perkins, C.E.; Bhagwat, P. Highly dynamic destination-sequenced distance-vector routing (DSDV) for mobile computers. ACM SIGCOMM Comput. Commun. Rev. 1994, 24, 234–244. [Google Scholar] [CrossRef]
- Perkins, C.; Belding-Royer, E.; Das, S. Ad Hoc On-Demand Distance Vector (AODV) Routing. No. RFC 3561. Available online: https://tools.ietf.org/html/rfc3561 (accessed on 2 November 2016).
- Higaki, H.; Umeshima, S. Multiple-route ad hoc on-demand distance vector (MRAODV) routing protocol. In Proceedings of the 18th International Parallel & Distributed Processing Symposium, Santa Fe, NM, USA, 26–30 April 2004; p. 237.
- Johnson, D.B.; Maltz, D.A.; Broch, J. DSR: The dynamic source routing protocol for multi-hop wireless ad hoc networks. Ad Hoc Netw. 2001, 5, 139–172. [Google Scholar]
- Ade, S.; Tijare, P. Performance comparison of AODV, DSDV, OLSR and DSR routing protocols in mobile ad hoc networks. Int. J. Inf. Technol. Knowl. Manag. 2010, 2, 545–548. [Google Scholar]
- Arun Kumar, B.R.; Lokanatha, C.R.; Prakash, S.H. Performance comparison of wireless mobile ad-hoc network routing protocols. Int. J. Comput. Sci. Netw. Secur. 2008, 8, 337. [Google Scholar]
- Ahmed, S.; Khan, I.; Rasheed, M.B.; Ilahi, M.; Khan, R.; Bouk, S.H.; Javaid, N. Comparative analysis of routing protocols for under water wireless sensor networks. arXiv 2013. [Google Scholar]
- Han, G.; Jiang, J.; Shu, L.; Xu, Y.; Wang, F. Localization algorithms of underwater wireless sensor networks: A survey. Sensors 2012, 12, 2026–2061. [Google Scholar] [CrossRef] [PubMed]
- Guo, Y.; Liu, Y. Localization for anchor-free underwater sensor networks. Comput. Electr. Eng. 2013, 39, 1812–1821. [Google Scholar] [CrossRef]
- Han, G.; Qian, A.; Zhang, C.; Wang, Y.; Rodrigues, J.J. Localization algorithms in large-scale underwater acoustic sensor networks: A quantitative comparison. Int. J. Distrib. Sens. Netw. 2014, 2014, 379382. [Google Scholar] [CrossRef]
- Misra, S.; Ojha, T.; Mondal, A. Game-theoretic topology controlfor opportunistic localizationin sparse underwater sensor networks. IEEE Trans. Mob. Comput. 2015, 14, 990–1003. [Google Scholar] [CrossRef]
- Carlson, E.; Beaujean, P.-P.; An, E. Location-aware routing protocol for underwater acoustic networks. In Proceedings of the OCEANS 2006, Boston, MA, USA, 18–21 September 2006; pp. 1–6.
- Xie, P.; Cui, J.-H.; Lao, L. VBF: Vector-based forwarding protocol for underwater sensor networks. In Proceedings of the Networking 2006—Networking Technologies, Services, and Protocols; Performance of Computer and Communication Networks; Mobile and Wireless Communications Systems, Coimbra, Portugal, 15–19 May 2006; pp. 1216–1221.
- Xie, P.; Zhou, Z.; Nicolaou, N.; See, A.; Cui, J.-H.; Shi, Z. Efficient vector-based forwarding for underwater sensor networks. EURASIP J. Wirel. Commun. Netw. 2010, 2010, 195910. [Google Scholar] [CrossRef] [PubMed]
- Xiao, X.; Ji, X.P.; Yang, G.; Cong, Y.P. LE-VBF: Lifetime-extended vector-based forwarding routing. In Proceedings of the 2012 International Conference on Computer Science and Service System (CSSS), Nanjing, China, 11–13 August 2012; pp. 1201–1203.
- Xie, P.; Zhou, Z.; Peng, Z.; Cui, J.-H.; Shi, Z. Void avoidance in three-dimensional mobile underwater sensor networks. In Wireless Algorithms, Systems, and Applications; Springer: Berlin/Heidelberg, Germany, 2009; pp. 305–314. [Google Scholar]
- Imran, M.; Alnuem, M.A.; Fayed, M.S.; Alamri, A. Localized algorithm for segregation of critical/non-critical nodes in mobile ad hoc and sensor networks. Procedia Comput. Sci. 2013, 19, 1167–1172. [Google Scholar] [CrossRef]
- Shin, D.; Hwang, D.; Kim, D. DFR: An efficient directional flooding-based routing protocol in underwater sensor networks. Wirel. Commun. Mob. Comput. 2012, 12, 1517–1527. [Google Scholar] [CrossRef]
- Chen, Y.-D.; Lien, C.-Y.; Wang, C.-H.; Shih, K.-P. DARP: A depth adaptive routing protocol for large-scale underwater acoustic sensor networks. In Proceedings of the OCEANS 2012, Yeosu, Korea, 21–24 May 2012; pp. 1–6.
- Li, Z.; Yao, N.; Gao, Q. Relative distance based forwarding protocol for underwater wireless networks. Int. J. Distrib. Sens. Netw. 2014, 2014, 173089. [Google Scholar] [CrossRef]
- Zhou, Z.; Peng, Z.; Cui, J.-H.; Shi, Z. Efficient multipath communication for time-critical applications in underwater acoustic sensor networks. IEEE/ACM Trans. Netw. 2011, 19, 28–41. [Google Scholar] [CrossRef]
- Yan, H.; Shi, Z.J.; Cui, J.-H. Dbr: Depth-based routing for underwater sensor networks. In Proceedings of the NETWORKING 2008 Ad Hoc and Sensor Networks, Wireless Networks, Next Generation Internet, Singapore, 5–9 May 2008; pp. 72–86.
- Liu, G.; Li, Z. Depth-based multi-hop routing protocol for underwater sensor network. In Proceedings of the 2010 2nd International Conference on Industrial Mechatronics and Automation (ICIMA), Wuhan, China, 30–31 May 2010; pp. 268–270.
- Yu, H.; Yao, N.; Wang, T.; Li, G.; Gao, Z.; Tan, G. WDFAD-DBR: Weighting depth and forwarding area division DBR routing protocol for UASNs. Ad Hoc Netw. 2016, 37, 256–282. [Google Scholar] [CrossRef]
- Lee, U.; Wang, P.; Noh, Y.; Vieira, L.F.; Gerla, M.; Cui, J.-H. Pressure routing for underwater sensor networks. In Proceedings of the IEEE INFOCOM 2016, San Diego, CA, USA, 14–19 March 2010; pp. 1–9.
- Noh, Y.; Lee, U.; Wang, P.; Choi, B.S.C.; Gerla, M. VAPR: Void-aware pressure routing for underwater sensor networks. IEEE Trans. Mob. Comput. 2013, 12, 895–908. [Google Scholar] [CrossRef]
- Hu, T.; Fei, Y. QELAR: A machine-learning-based adaptive routing protocol for energy-efficient and lifetime-extended underwater sensor networks. IEEE Trans. Mob. Comput. 2010, 9, 796–809. [Google Scholar]
- Gopi, S.; Kannan, G.; Chander, D.; Desai, U.; Merchant, S. PULRP: Path unaware layered routing protocol for underwater sensor networks. In Proceedings of the IEEE International Conference on Communications (ICC ’08), Beijing, China, 19–23 May 2008; pp. 3141–3145.
- Gopi, S.; Govindan, K.; Chander, D.; Desai, U.B.; Merchant, S. E-PULRP: Energy optimized path unaware layered routing protocol for underwater sensor networks. IEEE Trans. Wirel. Commun. 2010, 9, 3391–3401. [Google Scholar] [CrossRef]
- Wahid, A.; Kim, D. An energy efficient localization-free routing protocol for underwater wireless sensor networks. Int. J. Distrib. Sens. Netw. 2012, 2012, 307246. [Google Scholar] [CrossRef]
- Ayaz, M.; Abdullah, A. Hop-by-hop dynamic addressing based (H2-DAB) routing protocol for underwater wireless sensor networks. In Proceedings of the International Conference on Information and Multimedia Technology (ICIMT ’09), San Francisco, CA, USA, 20–22 October 2009; pp. 436–441.
- Wahid, A.; Kim, D. Connectivity-based routing protocol for underwater wireless sensor networks. In Proceedings of the 2012 International Conference on Proceedings of the ICT Convergence (ICTC), Jeju Island, Korea, 15–17 October 2012; pp. 589–590.
- Basagni, S.; Petrioli, C.; Petroccia, R.; Spaccini, D. Channel-aware routing for underwater wireless networks. In Proceedings of the OCEANS 2012, Yeosu, Korea, 21–24 May 2012; pp. 1–9.
- Jafri, M.R.; Ahmed, S.; Javaid, N.; Ahmad, Z.; Qureshi, R. AMCTD: Adaptive mobility of courier nodes in threshold-optimized DBR protocol for underwater wireless sensor networks. In Proceedings of the 2013 Eighth International Conference on Broadband and Wireless Computing, Communication and Applications (BWCCA), Compiegne, France, 28–30 October 2013; pp. 93–99.
- Javaid, N.; Jafri, M.R.; Khan, Z.; Qasim, U.; Alghamdi, T.A.; Ali, M. iAMCTD: Improved adaptive mobility of courier nodes in threshold-optimized DBR protocol for underwater wireless sensor networks. Int. J. Distrib. Sens. Netw. 2014, 2014, 213012. [Google Scholar] [CrossRef]
- Han, J.; Meng, C.; Cao, F. Simulated research on passive sonar range using different hydrographic conditions. In Proceedings of the MATEC Web of Conferences, Lisbon, Portugal, 23–25 November 2015; Volume 35.
- Stojanovic, M. On the relationship between capacity and distance in an underwater acoustic communication channel. ACM SIGMOBILE Mob. Comput. Commun. Rev. 2007, 11, 34–43. [Google Scholar] [CrossRef]
- Harris, A.F., III; Zorzi, M. Modeling the underwater acoustic channel in NS2. In Proceedings of the 2nd International Conference on Performance Evaluation Methodologies and Tools, Nantes, France, 22–26 October 2007; p. 18.
- Villarino, M.B. Ramanujan’s perimeter of an ellipse. arXiv, 2008; arXiv:math/0506384. [Google Scholar]



| Properties | Minimum Values | Maximum Value | ||
|---|---|---|---|---|
| m | m | m | ||
| Deptd Difference | 20 m | 40 m | 60 m | 100 m |
| Absolute Depth | 100 m | 100 m | 100 m | 500 m |
| Absorption Coefficient (Abc) (km) | dB | dB | dB | dB |
| Scattering Coefficient (Sc) (km) | dB | dB | dB | dB |
| (Scm) | dB | dB | dB | 30 dB |
| Total Attenuation (At) | dB | dB | dB | dB |
| dB | dB | dB | dB | |
| Attenuation A(l,f) | ||||
| 93.6 m | 277.3 m | 533.2 m | 1245.4 m | |
| Noise | 20.925 dBrePa or 1.12 Pa | |||
| Attenuation Noise Product A(l,f) | ||||
| Protocol | Forwarding Function | Minimum Value | Maximum Values | ||
|---|---|---|---|---|---|
| 70 | 70 | 70 | |||
| AMCTD | 500 | 500 | 500 | ||
| 70 | 70 | 70 | |||
| iAMCTD | |||||
| 0 | |||||
| 0 | 70 | 70 | 70 | ||
| 0 | |||||
| i | ||
|---|---|---|
| 1 | 0 | 140 |
| 2 | 0 | 380 |
| 3 | 0 | 620 |
| 4 | 0 | 860 |
| Parameter Name | Value |
|---|---|
| Initial Energy () | 70 J |
| Number of nodes | 224 |
| Number of courier nodes | 4 |
| Maximum Depth () | 1000 m |
| Depth Margin 1 () | 250 m |
| Depth Margin 2 () | 750 m |
| First Death threshold | 75 |
| Second Death threshold | 150 |
| Depth threshold 1 () | 60 m |
| Depth threshold 2 () | 40 m |
| Depth threshold 3 () | 20 m |
| Transmission Range () | 100 m |
| Speed of acoustic signal (v) | 1500 ms |
| Priority value for very critical nodes () | 2 |
| Priority value for critical nodes () | |
© 2016 by the authors; licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC-BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Raza, W.; Arshad, F.; Ahmed, I.; Abdul, W.; Ghouzali, S.; Niaz, I.A.; Javaid, N. An Improved Forwarding of Diverse Events with Mobile Sinks in Underwater Wireless Sensor Networks. Sensors 2016, 16, 1850. https://doi.org/10.3390/s16111850
Raza W, Arshad F, Ahmed I, Abdul W, Ghouzali S, Niaz IA, Javaid N. An Improved Forwarding of Diverse Events with Mobile Sinks in Underwater Wireless Sensor Networks. Sensors. 2016; 16(11):1850. https://doi.org/10.3390/s16111850
Chicago/Turabian StyleRaza, Waseem, Farzana Arshad, Imran Ahmed, Wadood Abdul, Sanaa Ghouzali, Iftikhar Azim Niaz, and Nadeem Javaid. 2016. "An Improved Forwarding of Diverse Events with Mobile Sinks in Underwater Wireless Sensor Networks" Sensors 16, no. 11: 1850. https://doi.org/10.3390/s16111850
APA StyleRaza, W., Arshad, F., Ahmed, I., Abdul, W., Ghouzali, S., Niaz, I. A., & Javaid, N. (2016). An Improved Forwarding of Diverse Events with Mobile Sinks in Underwater Wireless Sensor Networks. Sensors, 16(11), 1850. https://doi.org/10.3390/s16111850






