Personalized Privacy Assistant: Identity Construction and Privacy in the Internet of Things
Abstract
1. Introduction
- Personalized Privacy Risk Estimation: User privacy risk calculations customized based on knowledge of user-specific identity attributes.
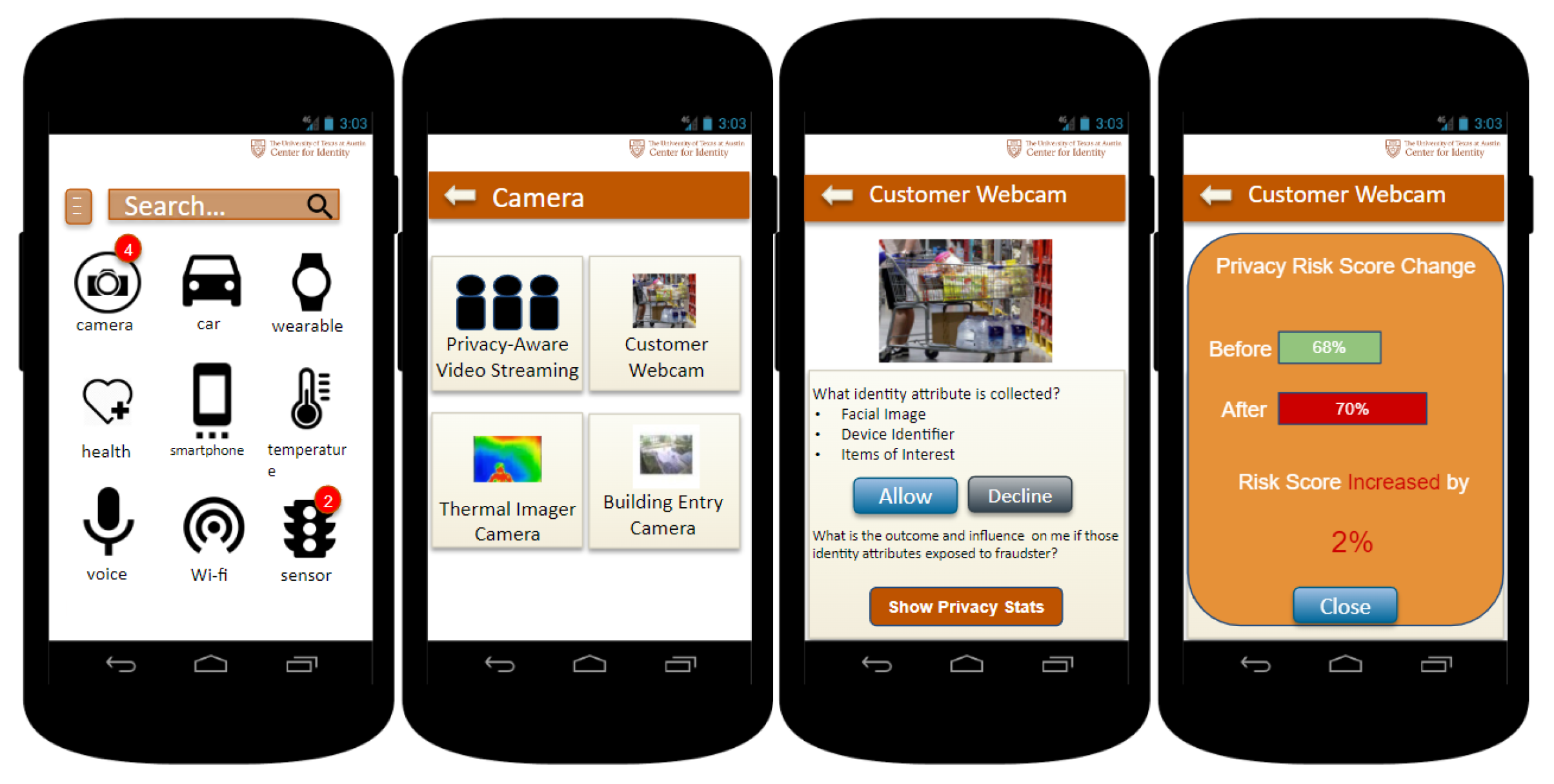
- Personalized Privacy Assistant for IoT: Mobile application that gives privacy risk notifications and recommendation actions for users when an IoT device collects or seeks to connect to their phone and collect the user’s identity attributes.
- Informs users of consequences resulting from IoT Device collection & sharing of identity attributes: Uses knowledge of the IoT Identity Ecosystem to evaluate the consequences of privacy vulnerabilities of mobile apps (sensitive identity attributes collected and shared by IoT).
2. Background
2.1. Center for Identity
2.2. Itap
2.3. Identity Ecosystem
2.4. Iot Privacy Architecture
3. Related Work
3.1. Identity Attributes in General
3.2. Devices and Privacy
3.3. Privacy Risk Estimation
3.4. Privacy Assistant
3.5. Summary
4. Proposed Solution
4.1. Find the Comprehensive List of Identity Attributes for People and Devices
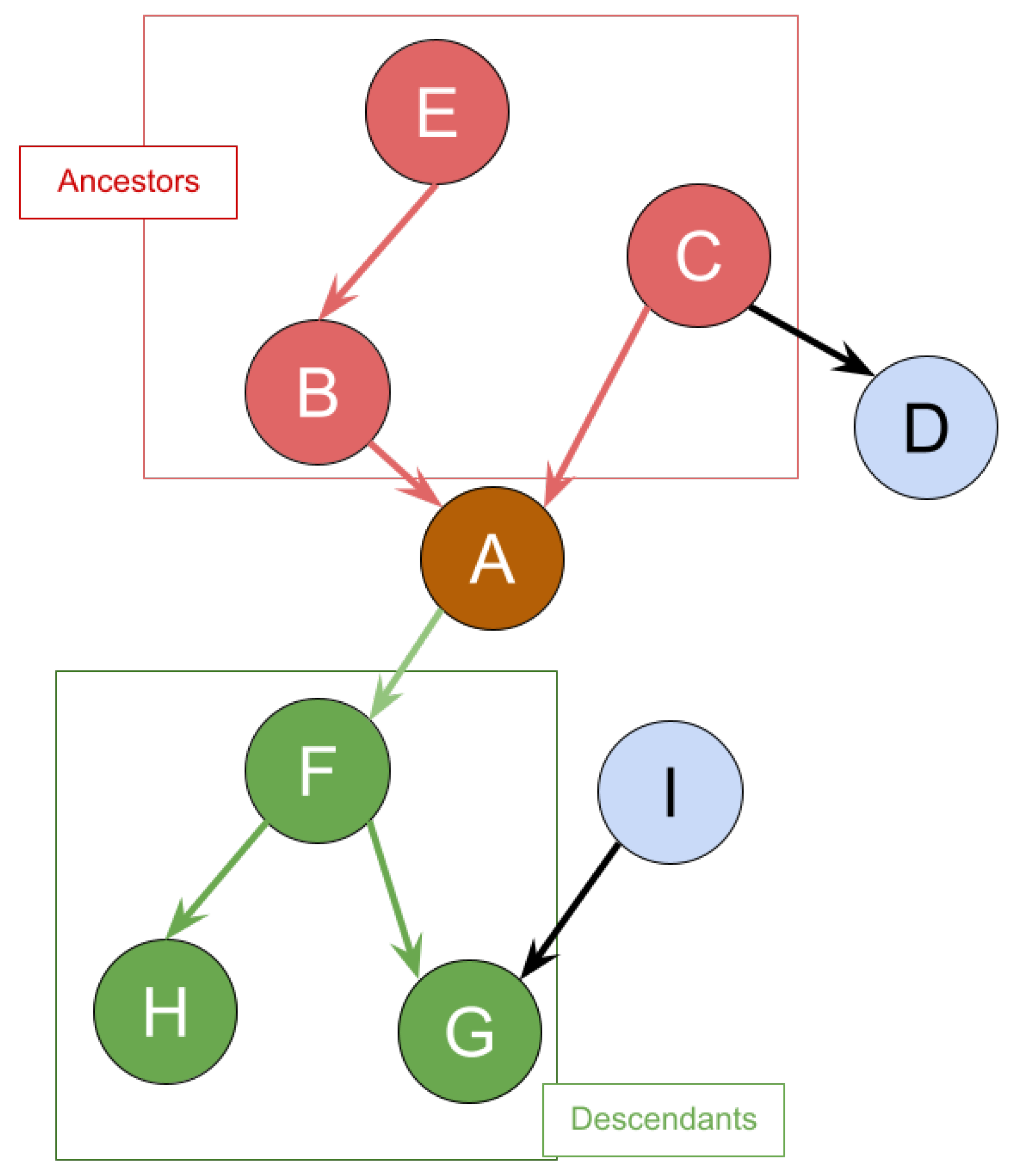
4.2. Iot Identity Ecosystem
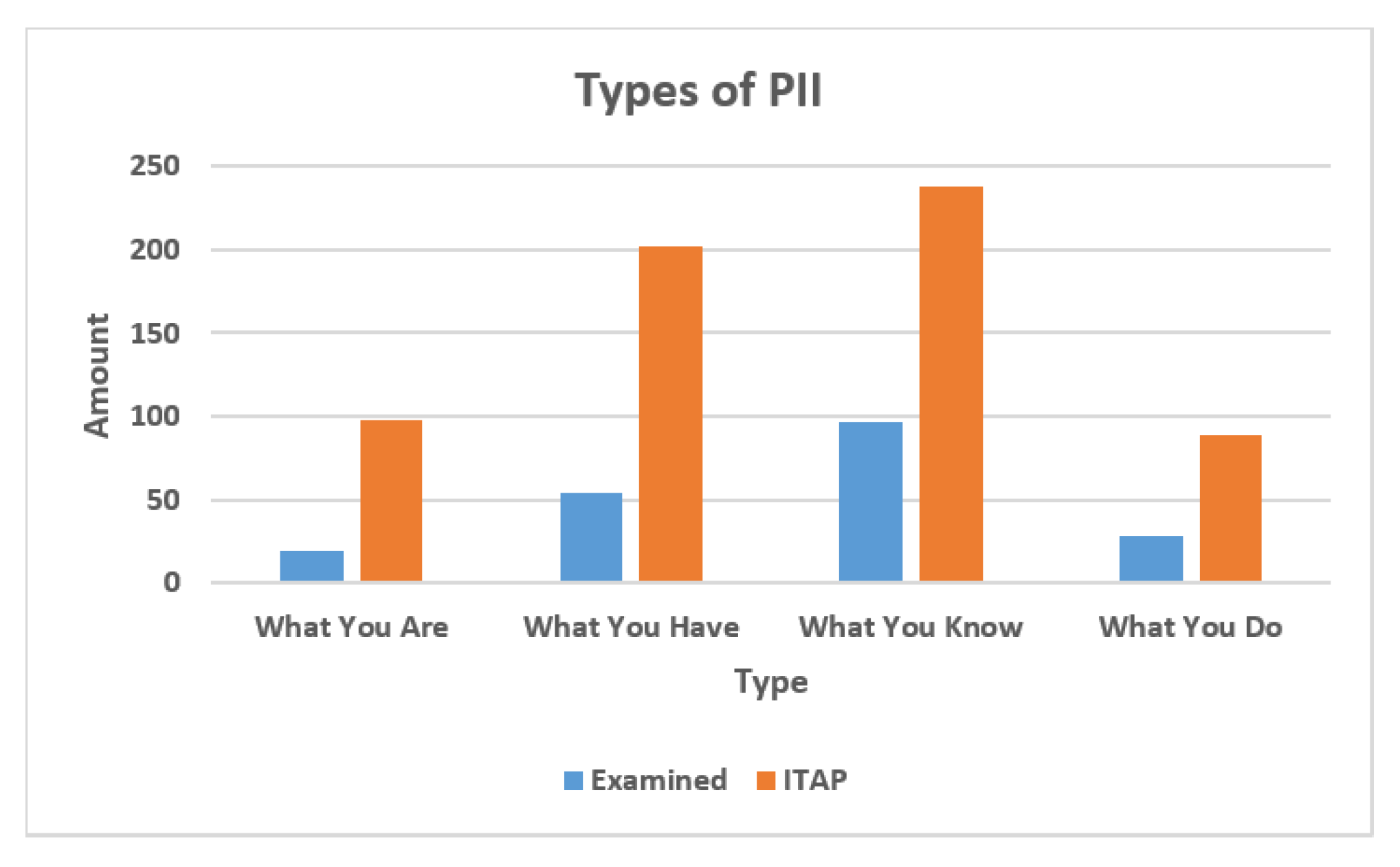
- What You Are: For a person, it means a person’s physical characteristics, such as fingerprints and retinas. For a device, it means the type of a device. It can be a laptop, a smart watch, a sensor, and so on. It is also related to a device’s hardware configuration, such as circuit design and power usage.
- What You Have: For a person, it means credentials and numbers assigned to the person by other entities. For a device, it means identifiers assigned to the device by other entities such as model numbers, serial numbers, and inventory tags.
- What You Know: For a person, it means information known privately to the person, such as passwords. For a device, it means any information that is stored on the device and know only to the device.
- What You Do: For a person, it means a person’s behavior and action patterns, such as GPS location. For a device, it is related to application types, GPS location, behavior patterns.
- Accessibility and Post Effect
- Static Approach
- Risk (shows the risk of exposure): Low, Medium, High.
- Uniqueness (shows how unique the identity attribute is for the individuals, devices or organization who have it): Individual, Small Group, Large Group.
- Dynamic Approach
4.3. Privacy Risk Score Estimation
4.3.1. Basic Measurement
4.3.2. Dynamic Measurement
4.4. Scoring for Iot Devices
4.5. UTCID Personalized Privacy Assistant for Iot
5. Experimental Results
5.1. Comparison of Target Set to Dataset Collected by Popular Open-Source Apps
5.2. Comparison between Personalized Privacy Assistants
- Multiple Recommendations Sources: Users are aware of potential biases and agendas influencing recommendations from PPA. A good design for this functionality would allow users to pick the types of recommendation sources that they would prefer.
- Crowd-sourced: Recommendations based on real users’ opinions and social cues.
- Authoritative source: Recommendations based on expert opinions, manufacturers and independent organizations.
- Trusted Location: Remove unnecessary notifications by incorporating a “trusted location” feature, such that users would not be notified about devices in those locations.
- Setting Configuration: PPA could list devices once and request a decision, revisiting that decision periodically if new devices were added or the user’s preferences changed. Another way to avoid unnecessary notifications is let the PPA learn the user’s preference setting or to specify data collection situations where users are always opposed to or always in favor of sharing.
- Explanations of risks and benefits: Users sometimes may feel nothing from privacy-concerning contexts because the risks did not seem to be dangerous to them or could do any harm to them. To mitigate this, recommendations from PPA should offer users detailed and transparent explanations of risks, benefits, and consequences. This can help users understand what the collection and use of these identity attributes have to do with them and why they need to care, and make them more comfortable and decisive when making judgments and decisions.
6. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Data Availability Statement
Conflicts of Interest
Abbreviations
| UTCID | University of Texas at Austin, Center for Identity |
| ITAP | The Identity Threat Assessment and Prediction |
| PII | Personally Identifiable Information |
| PPA | Personal Privacy Assistant |
| IoT | Internet of Things |
| OSN | Online Social Networks |
| DNS | Domain Name System |
| NLP | Natural Language Processing |
References
- Deloitte. Shiny new devices may be bringing joy, but who’s protecting consumer data? Deloitte Insights 2023. Available online: https://www2.deloitte.com/us/en/insights/industry/technology/consumer-data-privacy.html. (accessed on 12 April 2023).
- IBM. Cost of a Data Breach Report 2022; IBM: Armonk, NY, USA, 2022. [Google Scholar]
- Landi, H. Fitbit, apple user data exposed in breach impacting 61M fitness tracker records. Fierce Healthc. 2021. Available online: https://www.fiercehealthcare.com/digital-health/fitbit-apple-user-data-exposed-breach-impacting-61m-fitness-tracker-records. (accessed on 12 April 2023).
- University of Texas at Austin. About the Center for Identity. Available online: https://identity.utexas.edu/about-center-identity. (accessed on 12 April 2023).
- Zaiss, J.; Nokhbeh Zaeem, R.; Barber, K.S. Identity Threat Assessment and Prediction. J. Consum. Aff. 2019, 53, 58–70. [Google Scholar] [CrossRef]
- Zaeem, R.N.; Manoharan, M.; Yang, Y.; Barber, K.S. Modeling and analysis of identity threat behaviors through text mining of identity theft stories. Comput. Secur. 2017, 65, 50–63. [Google Scholar] [CrossRef]
- Zaiss, J.; Anderson, R.; Zaeem, R.N.; Barber, K.S. ITAP Report 2019. 2019. Available online: https://identity.utexas.edu/2019-itap-report-0 (accessed on 1 February 2023).
- Chang, K.C.; Nokhbeh Zaeem, R.; Barber, K.S. Is Your Phone You? How Privacy Policies of Mobile Apps Allow the Use of Your Personally Identifiable Information. In Proceedings of the 2020 Second IEEE International Conference on Trust, Privacy and Security in Intelligent Systems and Applications (TPS-ISA), Atlanta, GA, USA, 28–31 October 2020; pp. 256–262. [Google Scholar] [CrossRef]
- Feng, Y.; Yao, Y.; Sadeh, N. A Design Space for Privacy Choices: Towards Meaningful Privacy Control in the Internet of Things. In Proceedings of the 2021 CHI Conference on Human Factors in Computing Systems, Yokohama, Japan, 8–13 May 2021; Association for Computing Machinery: New York, NY, USA, 2021. [Google Scholar] [CrossRef]
- Carrez, F.; Elsaleh, T.; Gómez, D.; Sánchez, L.; Lanza, J.; Grace, P. A Reference Architecture for federating IoT infrastructures supporting semantic interoperability. In Proceedings of the 2017 European Conference on Networks and Communications (EuCNC), Oulu, Finland, 12–15 June 2017; pp. 1–6. [Google Scholar] [CrossRef]
- Das, A.; Degeling, M.; Smullen, D.; Sadeh, N. Personalized privacy assistants for the internet of things: Providing users with notice and choice. IEEE Pervasive Comput. 2018, 17, 35–46. [Google Scholar] [CrossRef]
- Krishnamurthy, B.; Wills, C.E. On the Leakage of Personally Identifiable Information via Online Social Networks. In Proceedings of the 2nd ACM Workshop on Online Social Networks, Barcelona, Spain, 17 August 2009; ACM: New York, NY, USA, 2009; pp. 7–12. [Google Scholar] [CrossRef]
- Humphreys, L.; Gill, P.; Krishnamurthy, B. Twitter: A content analysis of personal information. Inf. Commun. Soc. 2014, 17, 843–857. [Google Scholar] [CrossRef]
- Aura, T.; Kuhn, T.A.; Roe, M. Scanning Electronic Documents for Personally Identifiable Information. In Proceedings of the 5th ACM Workshop on Privacy in Electronic Society, Alexandria, VA, USA, 30 October 2006; ACM: New York, NY, USA, 2006; pp. 41–50. [Google Scholar] [CrossRef]
- Ranchal, R.; Bhargava, B.; Othmane, L.B.; Lilien, L.; Kim, A.; Kang, M.; Linderman, M. Protection of Identity Information in Cloud Computing without Trusted Third Party. In Proceedings of the 2010 29th IEEE Symposium on Reliable Distributed Systems, New Delhi, India, 31 October–3 November 2010; pp. 368–372. [Google Scholar] [CrossRef]
- Weingärtner, R.; Westphall, C.M. A Design Towards Personally Identifiable Information Control and Awareness in OpenID Connect Identity Providers. In Proceedings of the 2017 IEEE International Conference on Computer and Information Technology (CIT), Helsinki, Finland, 21–23 August 2017; pp. 37–46. [Google Scholar] [CrossRef]
- Arefi, M.N.; Alexander, G.; Crandall, J.R. PIITracker: Automatic Tracking of Personally Identifiable Information in Windows. In Proceedings of the 11th European Workshop on Systems Security, Porto, Portugal, 23–26 April 2018; ACM: New York, NY, USA, 2018; pp. 3:1–3:6. [Google Scholar] [CrossRef]
- Canbay, Y.; Ulker, M.; Sagiroglu, S. Detection of mobile applications leaking sensitive data. In Proceedings of the 2017 5th International Symposium on Digital Forensic and Security (ISDFS), Tirgu Mures, Romania, 26–28 April 2017; pp. 1–5. [Google Scholar] [CrossRef]
- Reardon, J.; Feal, Á.; Wijesekera, P.; On, A.E.B.; Vallina-Rodriguez, N.; Egelman, S. 50 ways to leak your data: An exploration of apps’ circumvention of the android permissions system. In Proceedings of the 28th USENIX Security Symposium (USENIX Security 19), Santa Clara, CA, USA, 14–16 August 2019; pp. 603–620. [Google Scholar]
- Liu, X.; Liu, J.; Zhu, S.; Wang, W.; Zhang, X. Privacy risk analysis and mitigation of analytics libraries in the android ecosystem. IEEE Trans. Mob. Comput. 2019, 19, 1184–1199. [Google Scholar] [CrossRef]
- Alazab, M.; Alazab, M.; Shalaginov, A.; Mesleh, A.; Awajan, A. Intelligent mobile malware detection using permission requests and API calls. Future Gener. Comput. Syst. 2020, 107, 509–521. [Google Scholar] [CrossRef]
- Grundy, Q.; Chiu, K.; Held, F.; Continella, A.; Bero, L.; Holz, R. Data sharing practices of medicines related apps and the mobile ecosystem: Traffic, content, and network analysis. BMJ 2019, 364, l920. [Google Scholar] [CrossRef] [PubMed]
- Huckvale, K.; Torous, J.; Larsen, M.E. Assessment of the data sharing and privacy practices of smartphone apps for depression and smoking cessation. JAMA Netw. Open 2019, 2, e192542. [Google Scholar] [CrossRef] [PubMed]
- He, Y.; Yang, X.; Hu, B.; Wang, W. Dynamic privacy leakage analysis of Android third-party libraries. J. Inf. Secur. Appl. 2019, 46, 259–270. [Google Scholar] [CrossRef]
- Shipp, L.; Blasco, J. How private is your period?: A systematic analysis of menstrual app privacy policies. Proc. Priv. Enhancing Technol. 2020, 2020, 491–510. [Google Scholar] [CrossRef]
- Salat, L.; Davis, M.; Khan, N. DNS Tunnelling, Exfiltration and Detection over Cloud Environments. Sensors 2023, 23, 2760. [Google Scholar] [CrossRef] [PubMed]
- de Moraes Rossetto, A.G.; Sega, C.; Leithardt, V.R.Q. An Architecture for Managing Data Privacy in Healthcare with Blockchain. Sensors 2022, 22, 8292. [Google Scholar] [CrossRef] [PubMed]
- Babun, L.; Celik, Z.B.; McDaniel, P.; Uluagac, A.S. Real-time analysis of privacy-(un) aware IoT applications. arXiv 2019, arXiv:1911.10461. [Google Scholar] [CrossRef]
- Sharma, K.; Gupta, B.B. Towards privacy risk analysis in android applications using machine learning approaches. Int. J.-Serv. Mob. Appl. 2019, 11, 1–21. [Google Scholar] [CrossRef]
- Han, C.; Reyes, I.; Feal, Á.; Reardon, J.; Wijesekera, P.; Vallina-Rodriguez, N.; Elazar, A.; Bamberger, K.A.; Egelman, S. The price is (not) right: Comparing privacy in free and paid apps. Proc. Priv. Enhancing Technol. 2020, 2020, 222–242. [Google Scholar] [CrossRef]
- Pereira, F.; Crocker, P.; Leithardt, V.R. PADRES: Tool for PrivAcy, Data REgulation and Security. SoftwareX 2022, 17, 100895. [Google Scholar] [CrossRef]
- Barua, A.; Al Alamin, M.A.; Hossain, M.S.; Hossain, E. Security and Privacy Threats for Bluetooth Low Energy in IoT and Wearable Devices: A Comprehensive Survey. IEEE Open J. Commun. Soc. 2022, 3, 251–281. [Google Scholar] [CrossRef]
- Au, K.; Zhou, Y.; Huang, Z.; Gill, P.; Lie, D. Short paper: A look at smartphone permission models. In Proceedings of the 1st ACM Workshop on Security and Privacy in Smartphones and Mobile Devices, Chicago, IL, USA, 17 October 2011. [Google Scholar] [CrossRef]
- Felt, A.P.; Chin, E.; Hanna, S.; Song, D.; Wagner, D. Android Permissions Demystified. In Proceedings of the 18th ACM Conference on Computer and Communications Security, Chicago, IL, USA, 17–21 October 2011; Association for Computing Machinery: New York, NY, USA, 2011; pp. 627–638. [Google Scholar] [CrossRef]
- Zaeem, R.N.; German, R.L.; Barber, K.S. PrivacyCheck: Automatic Summarization of Privacy Policies Using Data Mining. ACM Trans. Internet Technol. 2018, 18, 1–18. [Google Scholar] [CrossRef]
- Nokhbeh Zaeem, R.; Barber, K.S. A study of web privacy policies across industries. J. Inf. Priv. Secur. 2017, 13, 169–185. [Google Scholar] [CrossRef]
- Zaeem, R.N.; Barber, K.S. The Effect of the GDPR on Privacy Policies: Recent Progress and Future Promise. ACM Trans. Manag. Inf. Syst. 2020, 12, 1–20. [Google Scholar] [CrossRef]
- O’Loughlin, K.; Neary, M.; Adkins, E.C.; Schueller, S.M. Reviewing the data security and privacy policies of mobile apps for depression. Internet Interv. 2019, 15, 110–115. [Google Scholar] [CrossRef] [PubMed]
- Harkous, H.; Fawaz, K.; Lebret, R.; Schaub, F.; Shin, K.G.; Aberer, K. Polisis: Automated Analysis and Presentation of Privacy Policies Using Deep Learning. In Proceedings of the 27th USENIX Security Symposium (USENIX Security 18), Baltimore, MD, USA, 15–17 August 2018; USENIX Association: Baltimore, MD, USA, 2018; pp. 531–548. [Google Scholar]
- Zuo, C.; Lin, Z.; Zhang, Y. Why Does Your Data Leak? Uncovering the Data Leakage in Cloud from Mobile Apps. In Proceedings of the 2019 IEEE Symposium on Security and Privacy (SP), San Francisco, CA, USA, 19–23 May 2019; pp. 1296–1310. [Google Scholar]
- Ayci, G.; Sensoy, M.; ÖzgÜr, A.; Yolum, P. A Self-aware Personal Assistant for Making Personalized Privacy Decisions. arXiv 2022, arXiv:2205.06544. [Google Scholar]
- Stöver, A.; Hahn, S.; Kretschmer, F.; Gerber, N. Investigating How Users Imagine Their Personal Privacy Assistant. Proc. Priv. Enhancing Technol. 2023, 2, 384–402. [Google Scholar] [CrossRef]
- Applikey Editorial Team. Most Profitable App Categories; Applikey 2018. Available online: https://applikeysolutions.com/blog/most-profitable-app-categories (accessed on 12 April 2023).
- Kuklenko, D. The Most Promising App Categories in 2019. Applikey 2019. Available online: https://applikeysolutions.com/blog/the-most-promising-app-categories-in-2019 (accessed on 12 April 2023).
- Anthopoulos, L.G. Understanding the Smart City Domain: A Literature Review. In Transforming City Governments for Successful Smart Cities; Rodríguez-Bolívar, M.P., Ed.; Springer International Publishing: Cham, Switzerland, 2015; pp. 9–21. [Google Scholar] [CrossRef]
- Schaffers, H.; Komninos, N.; Pallot, M.; Trousse, B.; Nilsson, M.; Oliveira, A. Smart cities and the future internet: Towards cooperation frameworks for open innovation. In The Future Internet Assembly; Springer: Berlin/Heidelberg, Germany, 2011; pp. 431–446. [Google Scholar]
- Gubbi, J.; Buyya, R.; Marusic, S.; Palaniswami, M. Internet of Things (IoT): A vision, architectural elements, and future directions. Future Gener. Comput. Syst. 2013, 29, 1645–1660. [Google Scholar] [CrossRef]
- Zaeem, R.N.; Manoharan, M.; Barber, K.S. Risk Kit: Highlighting Vulnerable Identity Assets for Specific Age Groups. In Proceedings of the 2016 European Intelligence and Security Informatics Conference (EISIC), Uppsala, Sweden, 17–19 August 2016; pp. 32–38. [Google Scholar] [CrossRef]
- Cao, Y.; Yang, L. A survey of Identity Management technology. In Proceedings of the 2010 IEEE International Conference on Information Theory and Information Security, Beijing, China, 17–19 December 2010; pp. 287–293. [Google Scholar] [CrossRef]
- Chang, K.C.; Zaeem, R.N.; Barber, K.S. A Framework for Estimating Privacy Risk Scores of Mobile Apps. In International Conference on Information Security; Springer: Berlin/Heidelberg, Germany, 2020; pp. 217–233. [Google Scholar]
- Chang, K.C.; Zaeem, R.N.; Barber, K.S. Enhancing and evaluating identity privacy and authentication strength by utilizing the identity ecosystem. In Proceedings of the 2018 Workshop on Privacy in the Electronic Society, Toronto, ON, Canada, 15 October 2018; pp. 114–120. [Google Scholar]
- Colnago, J.; Feng, Y.; Palanivel, T.; Pearman, S.; Ung, M.; Acquisti, A.; Cranor, L.F.; Sadeh, N. Informing the Design of a Personalized Privacy Assistant for the Internet of Things. In Proceedings of the 2020 CHI Conference on Human Factors in Computing Systems, Honolulu, HI, USA, 25–30 April 2020; Association for Computing Machinery: New York, NY, USA, 2020; pp. 1–13. [Google Scholar] [CrossRef]


| Work | Category | Advantages | Gap |
|---|---|---|---|
| [12,13,14,15,16,17] | Identity Attributes in General | Analyzation for mobile apps to detect identity attributes shared from or generated by the app. | A comprehensive analysis of identity attribute collection, sharing and abuse. A comprehensive analysis of identity attribute occurrences, dependencies, value and risk across multiple cases of sharing and abuse. |
| [18,19,20,21,22,23,24,25,26,27,28,29,30,31,32] | Devices and Privacy | Focuses on the detection of actual mobile app data transmissions to third parties or mobile apps accessing data | Does not allow for user’s run-time preventive solutions. Program analysis requires experts, is conducted off-line, and is time-consuming and expensive. Detection of actual data transmission only allows for reactive solutions. Consequences of personal data transmissions to third parties not identified. |
| [33,34,35,36,37,38,39,40] | Privacy Risk Estimation | Analyzation for privacy policies to assess governance and regulation compliance. | Does not focus privacy risk posed by mobile apps. Lacks calculation of direct privacy risk to users. |
| [9,11,41,42] | Privacy Assistant | provides users suggestions on their privacy settings based on users’ setting preferences. | Does not suggest settings based on user’s privacy risk. Does not let users know why one identity attribute is more important than another. |
| PortNumbers | PowerFrequency | PowerUsage |
| ProcessorType | Reputation | SerialNo |
| ApplicationType | BusType | Cache |
| CircuitDesign | Color | CookieWipe |
| Symbol | Meaning |
|---|---|
| V | The set of identity attributes in UTCID IoT Identity Ecosystem. |
| E | The set of directed edges. |
| G | The graph the UTCID IoT Identity Ecosystem represents as. |
| The probability of exposure for identity attribute A. | |
| The liability value for identity attribute A. | |
| The set of ancestors for identity attribute A. | |
| The set of descendants for identity attribute A. | |
| The probability of identity attribute A gets exposed on its own after its ancestor was exposed. | |
| The accessibility for identity attribute A. | |
| The post effect for identity attribute A. | |
| The expected loss for identity attribute A. | |
| The privacy risk score for identity attribute A. | |
| The privacy risk score for IoT device S. |
| Password | Username | Name | Login Credentials |
| Phone Number | Account Information | Email Address | Zip Code |
| Security Q&A | Time Stamp | Date | URL |
| User Sign Up Date | Address | Last Login Date | Age |
| Date of Birth | Gender | IP Address | Location |
| 1. Name | 2. Address | 3. Email Address | 4. Phone Number | 5. Dat of Birth |
| 6. Credit Card | 7. Password | 8. Username | 9. Bank Account | 10. Debit Card |
| App | Score (%) |
|---|---|
| Target set | 36.69 |
| N-400 | 26.8 |
| Wiki | 43.63 |
| Firefox Focus | 47.99 |
| Kodi | 48.79 |
| QsmFurthermore, | 54.51 |
| Duckduckgo | 67.39 |
| OpenVPN | 68.92 |
| Signal Private Messenger | 69.32 |
| Ted | 71.82 |
| Blockchain Wallet | 73.67 |
| Telegram | 73.99 |
| Data Set Required at USCIS | |||
|---|---|---|---|
| 1. MilitaryId | 2. Military Service Record | 3. Email | 4. SSN |
| 5. Phone Number | 6. Travel History | 7. Fingerprints | 8. Parents Name |
| 9. Parents Occupation | 10. Spouse Info | 11. Address | 12. Birth Certificate |
| 13. Hometown | 14. School | 15. Organization | 16. Signature |
| 17. Citizenship | 18. Zip Code | 19. Name | 20. Date of Birth |
| 21. Height | 22. Weight | 23. Gender | 24. Eye Color |
| 25. Hair Color | 26. Ethnicity | 27. Crime History | 28. Age |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Chang, K.-C.; Barber, S. Personalized Privacy Assistant: Identity Construction and Privacy in the Internet of Things. Entropy 2023, 25, 717. https://doi.org/10.3390/e25050717
Chang K-C, Barber S. Personalized Privacy Assistant: Identity Construction and Privacy in the Internet of Things. Entropy. 2023; 25(5):717. https://doi.org/10.3390/e25050717
Chicago/Turabian StyleChang, Kai-Chih, and Suzanne Barber. 2023. "Personalized Privacy Assistant: Identity Construction and Privacy in the Internet of Things" Entropy 25, no. 5: 717. https://doi.org/10.3390/e25050717
APA StyleChang, K.-C., & Barber, S. (2023). Personalized Privacy Assistant: Identity Construction and Privacy in the Internet of Things. Entropy, 25(5), 717. https://doi.org/10.3390/e25050717








