Multivariable Heuristic Approach to Intrusion Detection in Network Environments
Abstract
1. Introduction
2. Related Work
3. Intrusion Detection
3.1. Intrusion Detection Systems
3.2. Detection Methods
4. Multivariable Heuristic Approach
4.1. Flags
- dangerous—This flag identifies the severity of the threat associated with an IP address (Table 1). The value of this flag is subjective and depends on the environment/federation. In some cases, the attack may not be especially harmful. For example, a phishing attack on medical wristband infrastructure is not especially dangerous; on the other hand, the same type of attack on corporate infrastructure can be critical. The value of this flag and the decision of which flag to assign to the given IP address can be based on an analysis of other flags.
- attack—This flag specifies the type of attack in which the IP address was recently involved. The value of this flag may differ from its environment because the effectiveness of an attack also depends on the network’s purpose and users. Table 2 shows descriptions and default values for attack flags.
- range—This flag describes the impact of an attack by an IP address on other network components such as the server, switch, or router. In this case, a given attack may affect only a single attacked network component or spread over a part or all of the infrastructure. Table 3 shows description and default values for range flags.
- access—Some attacks (e.g., phishing, malware) require user action within the network, while others (e.g., DDoS, DoS) do not require user response. This type of flag describes the need for user response within the network. Table 4 shows two possible flags: none and user. The first describes a situation when the attack does not require a user response. The second flag describes a situation when the attack requires a user response (e.g., opening an attachment in an email).
- availability—Some attacks, such as ransomware, cause a partial or complete loss of access to the unit and data on it. This type of flag describes the impact on the availability of the attacked component. Table 5 shows three levels of impact on the functionality of a given component in the network.
4.2. Entropy
4.3. Shared Data
4.4. Detection Algorithm
- packet_value—Initial value of the received packet immediately after the packet is captured. This value is the same for each analysed packet.
- sensitivity—Lower limit of the packet value. When this limit is exceeded (following analysis), the packet is reported to the console.
- entropy—Upper limit of the packet entropy value above which the packet is reported to the console.
5. Verification
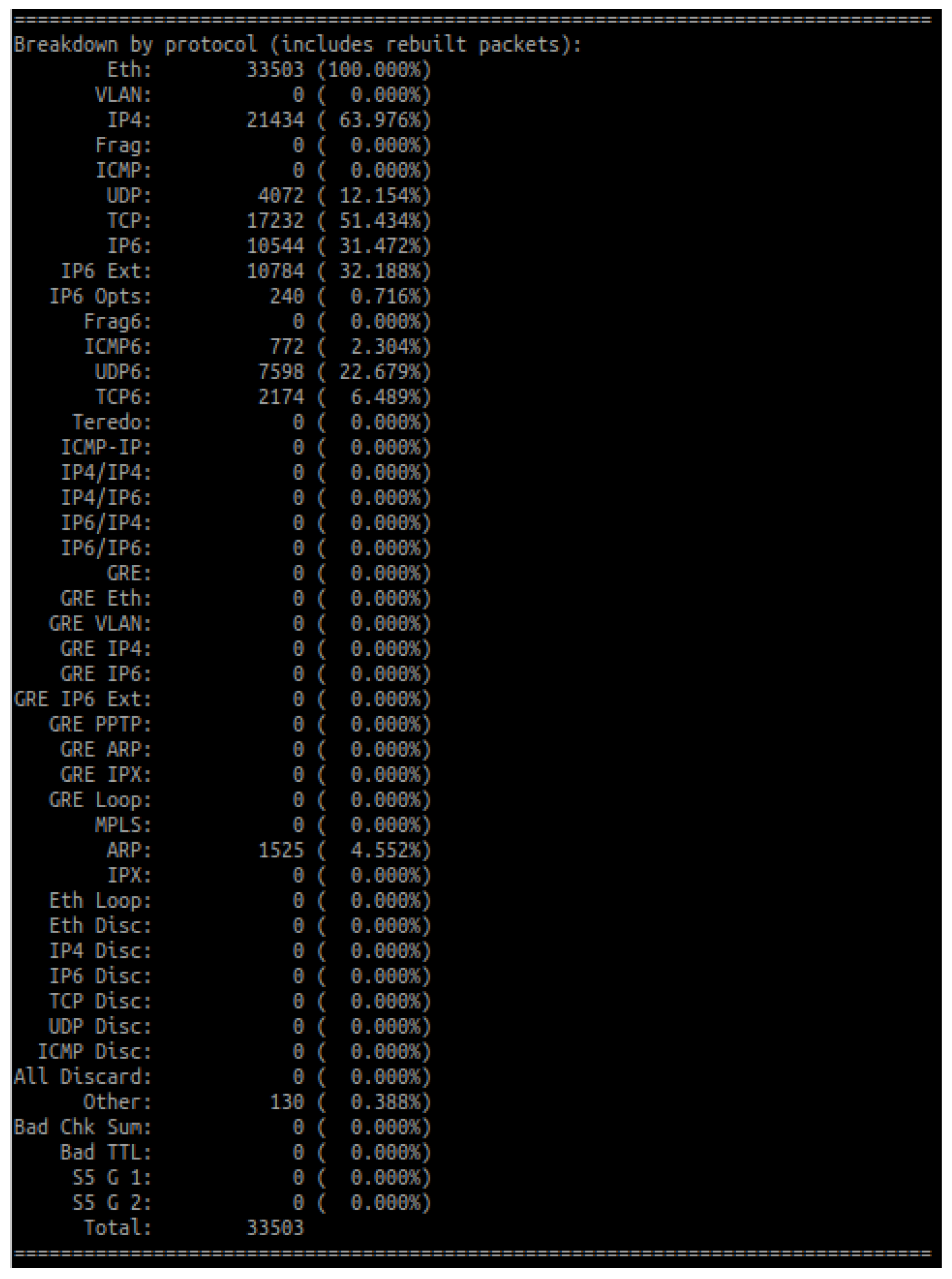
5.1. Methodology and Test Environment
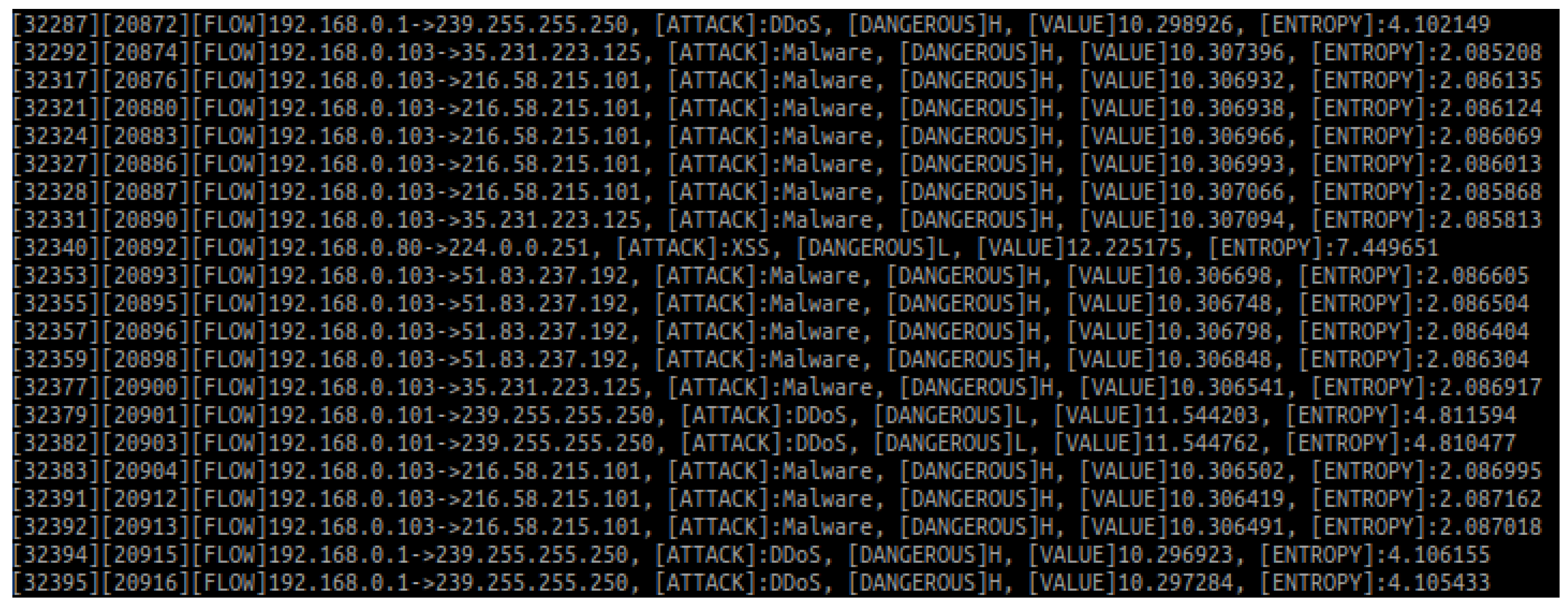
5.2. Validation of the Algorithm
| Listing 1. The content of a shared file (before test). |
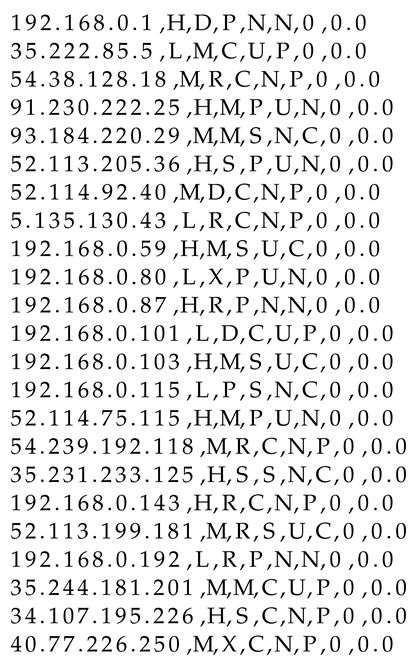 |
| Listing 2. The content of a shared file (after the test). |
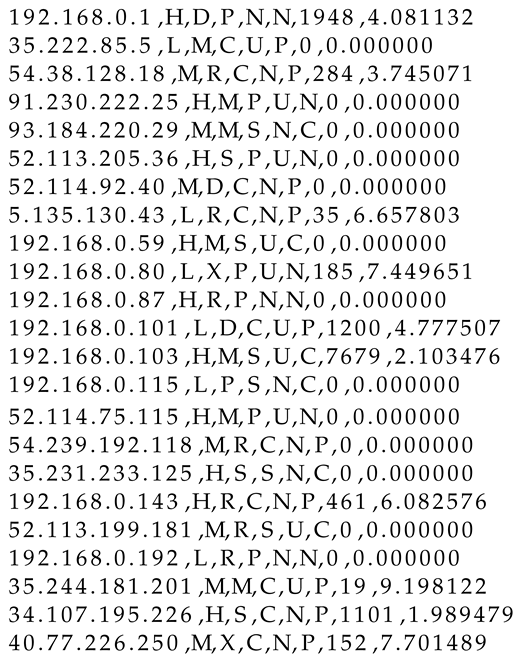 |
5.3. Updating of Variables
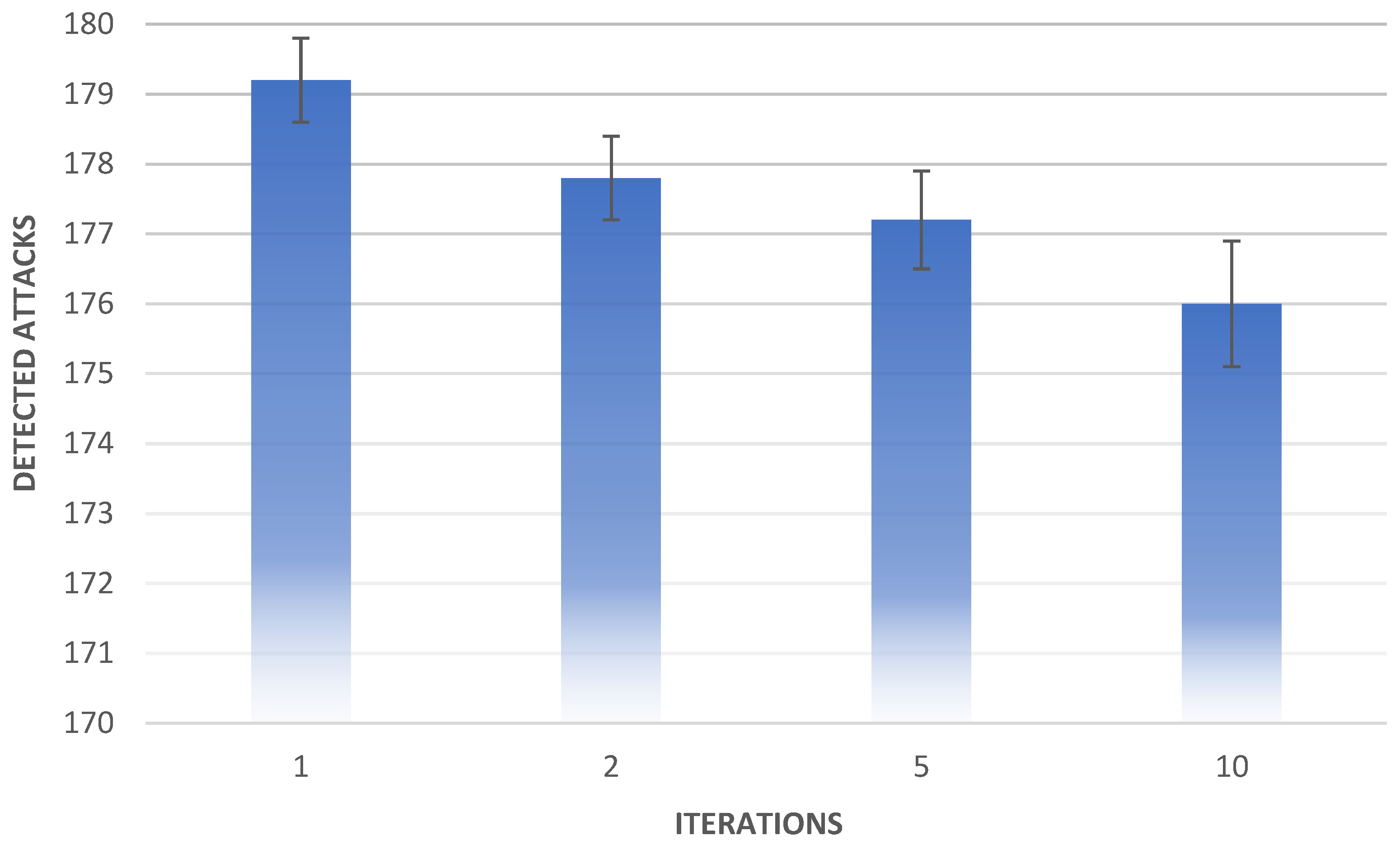
- In most cases, the algorithm cases perform better with a lower number of iterations. Its effectiveness is higher in one-iteration scenarios than in two-, five-, and ten-iteration scenarios. The two-iteration test’s effectiveness is also higher than that of the ten-iteration tests.
- The standard deviation of the tests is lower than 1 in each scenario. This means that the algorithm regularly detects attacks, and anomalies such as the minimum number of attacks detected by the ten-iteration test (174 attacks) are rare throughout its operation.
6. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Conflicts of Interest
References
- Sajal, S.Z.; Jahan, I.; Nygard, K.E. A Survey on Cyber Security Threats and Challenges in Modem Society. In Proceedings of the 2019 IEEE International Conference on Electro Information Technology (EIT), Brookings, SD, USA, 20–22 May 2019; pp. 525–528. [Google Scholar]
- Hussain, A.; Mohamed, A.; Razali, S. A Review on Cybersecurity: Challenges & Emerging Threats. In Proceedings of the 3rd International Conference on Networking, Information Systems & Security, NISS2020, Marrakech, Morocco, 31 March–2 April 2019; Association for Computing Machinery: New York, NY, USA, 2020. [Google Scholar]
- Kettani, H.; Wainwright, P. On the Top Threats to Cyber Systems. In Proceedings of the 2019 IEEE 2nd International Conference on Information and Computer Technologies (ICICT), Kahului, HI, USA, 14–17 March 2019; pp. 175–179. [Google Scholar]
- Aiyanyo, I.D.; Samuel, H.; Lim, H. A Systematic Review of Defensive and Offensive Cybersecurity with Machine Learning. Appl. Sci. 2020, 10, 5811. [Google Scholar] [CrossRef]
- Cyber Security Statistics. The Ultimate List Of Stats, Data & Trends. 2021. Available online: https://purplesec.us/resources/cyber-security-statistics/ (accessed on 15 April 2021).
- Ransomware Statistics. Trends and Facts for 2020 and Beyond. 2020. Available online: https://www.cloudwards.net/ransomware-statistics/ (accessed on 15 April 2021).
- Whitman, M.E.; Mattord, H.J. Principles of Information Security; Cengage Learning: Boston, MA, USA, 2011. [Google Scholar]
- Ramapantulu, L.; Teo, Y.M.; Chang, E. A conceptural framework to federate testbeds for cybersecurity. In Proceedings of the 2017 Winter Simulation Conference (WSC), Las Vegas, NV, USA, 3–6 December 2017; pp. 457–468. [Google Scholar]
- Shaked, A.; Tabansky, L.; Reich, Y. Incorporating systems thinking into a cyber resilience maturity model. IEEE Eng. Manag. Rev. 2020. [Google Scholar] [CrossRef]
- Cybersecurity Competence Network. Available online: https://cybercompetencenetwork.eu (accessed on 15 April 2021).
- ECHO Project Portal. Available online: https://echonetwork.eu/project-summary/ (accessed on 15 April 2021).
- Al-Asli, M.; Ghaleb, T.A. Review of Signature-based Techniques in Antivirus Products. In Proceedings of the 2019 International Conference on Computer and Information Sciences (ICCIS), Las Vegas, NV, USA, 3–6 December 2019; pp. 1–6. [Google Scholar]
- Samrin, R.; Vasumathi, D. Review on anomaly based network intrusion detection system. In Proceedings of the 2017 International Conference on Electrical, Electronics, Communication, Computer, and Optimization Techniques (ICEECCOT), Mysuru, India, 15–16 December 2017. [Google Scholar]
- Paulauskas, N.; Baskys, A. Application of Histogram-Based Outlier Scores to Detect Computer Network Anomalies. Electronics 2019, 8, 1251. [Google Scholar] [CrossRef]
- Kenny, V.; Nathal, M.; Saldana, S. Northwestern University Open Text Book on Process Optimization— Heuristic Algorithms. 2014. Available online: https://optimization.mccormick.northwestern.edu/index.php/Heuristic_algorithms (accessed on 15 April 2021).
- Ali, W.; Malebary, S. Particle Swarm Optimization-Based Feature Weighting for Improving Intelligent Phishing Website Detection. IEEE Access 2020, 8, 116766–116780. [Google Scholar] [CrossRef]
- Jacob, B. Automatic XSS Detection and Snort Signatures/ACLs Generation by the Means of a Cloud-Based Honeypot System. Master’s Thesis, Edinburgh Napier University, Edinburgh, UK, 2011. [Google Scholar]
- Yerong, T.; Sai, S.; Ke, X.; Zhe, L. Intrusion Detection Based on Support Vector Machine Using Heuristic Genetic Algorithm. In Proceedings of the 2014 Fourth International Conference on Communication Systems and Network Technologies, Washington, DC, USA, 7–9 April 2014; pp. 681–684. [Google Scholar]
- Jothi, K.R.; Balaji B, S.; Pandey, N.; Beriwal, P.; Amarajan, A. An Efficient SQL Injection Detection System Using Deep Learning. In Proceedings of the 2021 International Conference on Computational Intelligence and Knowledge Economy (ICCIKE), Dubai, United Arab Emirates, 17–18 March 2021; pp. 442–445. [Google Scholar]
- Rajesh, M. Intensive analysis of intrusion detection methodology over Mobile Adhoc Network using machine learning strategies. Mater. Today Proc. 2021. [Google Scholar] [CrossRef]
- Bangui, H.; Buhnova, B. Recent Advances in Machine-Learning Driven Intrusion Detection in Transportation: Survey. Procedia Comput. Sci. 2021, 184, 877–886. [Google Scholar] [CrossRef]
- Saravanan, L.; Himanshu, S.; Sreenivasulu, K.; Deivakani, M. Detection of software intrusion based on machine learning techniques for IOT systems. Mater. Today Proc. 2021. [Google Scholar] [CrossRef]
- Kalimuthan, C.; Arokia Renjit, J. Review on intrusion detection using feature selection with machine learning techniques. Mater. Today Proc. 2020, 33, 3794–3802. [Google Scholar] [CrossRef]
- Kilincer, I.F.; Ertam, F.; Sengur, A. Machine learning methods for cyber security intrusion detection: Datasets and comparative study. Comput. Netw. 2021, 188, 107840. [Google Scholar] [CrossRef]
- Fang, W.; Tan, X.; Wilbur, D. Application of intrusion detection technology in network safety based on machine learning. Saf. Sci. 2020, 124, 104604. [Google Scholar] [CrossRef]
- Mahboob, A.S.; Moghaddam, M.R.O. An Anomaly-based Intrusion Detection System Using Butterfly Optimization Algorithm. In Proceedings of the 2020 6th Iranian Conference on Signal Processing and Intelligent Systems (ICSPIS), Mashhad, Iran, 23–24 December 2020; pp. 1–6. [Google Scholar]
- Luo, H.; Shi, K.; Qiao, F.; Li, Y. Intrusion Detection Mechanism Based On Modular Neural Network. In Proceedings of the 2020 2nd International Conference on Machine Learning, Big Data and Business Intelligence (MLBDBI), Taiyuan, China, 23–25 October 2020; pp. 419–423. [Google Scholar]
- Lin, Z.; Hongle, D. Research on SDN intrusion detection based on online ensemble learning algorithm. In Proceedings of the 2020 International Conference on Networking and Network Applications (NaNA), Haikou, China, 10–13 December 2020; pp. 114–118. [Google Scholar]
- Jain, V.; Agrawal, M. Applying Genetic Algorithm in Intrusion Detection System of IoT Applications. In Proceedings of the 2020 4th International Conference on Trends in Electronics and Informatics (ICOEI)(48184), Tirunelveli, India, 15–17 June 2020; pp. 284–287. [Google Scholar]
- Saravanan, K.; Subburathinam, K. Packet Score based network security and Traffic Optimization. arXiv 2012, arXiv:1202.2024. [Google Scholar]
- Murtuza, S.; Asawa, K. Mitigation and Detection of DDoS Attacks in Software Defined Networks. In Proceedings of the 2018 Eleventh International Conference on Contemporary Computing (IC3), Noida, India, 2–4 August 2018; pp. 1–3. [Google Scholar]
- Prasath, M.K.; Perumal, B. A meta-heuristic Bayesian network classification for intrusion detection. Int. J. Netw. Manag. 2019, 29, e2047. [Google Scholar] [CrossRef]
- Umbarkar, S.; Shukla, S. Analysis of Heuristic based Feature Reduction method in Intrusion Detection System. In Proceedings of the 2018 5th International Conference on Signal Processing and Integrated Networks (SPIN), Noida, India, 22–23 February 2018; pp. 717–720. [Google Scholar]
- Manzoor, I.; Kumar, N. A feature reduced intrusion detection system using ANN classifier. Expert Syst. Appl. 2017, 88, 249–257. [Google Scholar]
- Mukhopadhyay, I.; Gupta, K.S.; Sen, D.; Gupta, P. Heuristic Intrusion Detection and Prevention System. In Proceedings of the 2015 International Conference and Workshop on Computing and Communication (IEMCON), Vancouver, BC, Canada, 15–17 October 2015; pp. 1–7. [Google Scholar]
- Varma, P.R.K.; Kumari, V.V.; Kumar, S.S. Feature Selection Using Relative Fuzzy Entropy and Ant Colony Optimization Applied to Real-time Intrusion Detection System. Procedia Comput. Sci. 2016, 85, 503–510. [Google Scholar] [CrossRef]
- Xing, H.J.; Ren, H.R. Regularized correntropy criterion based feature extraction for novelty detection. Neurocomputing 2014, 133, 483–490. [Google Scholar] [CrossRef]
- Pivarníková, M.; Sokol, P.; Bajtoš, T. Early-Stage Detection of Cyber Attacks. Information 2020, 11, 560. [Google Scholar] [CrossRef]
- Scarfone, K.; Mell, P. Guide to Intrusion Detection and Prevention Systems (IDPS); Technical Report SP 800-94; National Institute of Standards and Technology: Gaithersburg, ML, USA, 2012. [Google Scholar]
- Stallings, W. Cryptography and Network Security: Principles and Practice, 5th ed.; Prentice Hall: Hoboken, NJ, USA, 2011. [Google Scholar]
- Arshad, J.; Azad, M.A.; Amad, R.; Salah, K.; Alazab, M.; Iqbal, R. A Review of Performance, Energy and Privacy of Intrusion Detection Systems for IoT. Electronics 2020, 9, 629. [Google Scholar] [CrossRef]
- Beale, J. Snort 2.1 Intrusion Detection, 2nd ed.; Syngress: Rockland, MA, USA, 2004. [Google Scholar]
- Papadogiannaki, E.; Ioannidis, S. Acceleration of Intrusion Detection in Encrypted Network Traffic Using Heterogeneous Hardware. Sensors 2021, 21, 1140. [Google Scholar] [CrossRef] [PubMed]
- Soniya, S.S.; Vigila, S.M.C. Intrusion detection system: Classification and techniques. In Proceedings of the 2016 International Conference on Circuit, Power and Computing Technologies (ICCPCT), Nagercoil, India, 18–19 March 2016. [Google Scholar]
- Aryachandra, A.A.; Arif, Y.F.; Anggis, S.N. Intrusion Detection System (IDS) server placement analysis in cloud computing. In Proceedings of the 2016 4th International Conference on Information and Communication Technology (ICoICT), Bandung, Indonesia, 25–27 May 2016. [Google Scholar]
- Snort_Team. SNORT® Users Manual 2.9.16. Available online: http://manual-snort-org.s3-website-us-east-1.amazonaws.com (accessed on 15 April 2021).
- Suricata—Open Source IDS/IPS/NSM Engine. Available online: https://suricata-ids.org (accessed on 15 April 2021).
- Cisco Systems Security Products. Available online: www.cisco.com/c/en/us/products/security/firewalls (accessed on 15 April 2021).
- Palo Alto Networks Security Products. Available online: www.paloaltonetworks.com/network-security (accessed on 15 April 2021).
- Oliveira, N.; Praça, I.; Maia, E.; Sousa, O. Intelligent Cyber Attack Detection and Classification for Network-Based Intrusion Detection Systems. Appl. Sci. 2021, 11, 1674. [Google Scholar] [CrossRef]
- Kim, G.; Lee, S.; Kim, S. A novel hybrid intrusion detection method integrating anomaly detection with misuse detection. Expert Syst. Appl. 2014, 41, 1690–1700. [Google Scholar] [CrossRef]
- Li, J.; Li, Q.; Zhou, S.; Yao, Y.; Ou, J. A review on signature-based detection for network threats. In Proceedings of the 2017 IEEE 9th International Conference on Communication Software and Networks (ICCSN), Guangzhou, China, 6–8 May 2017; pp. 1117–1121. [Google Scholar]
- Kim, J.; Park, M.; Kim, H.; Cho, S.; Kang, P. Insider Threat Detection Based on User Behavior Modeling and Anomaly Detection Algorithms. Appl. Sci. 2019, 9, 4018. [Google Scholar] [CrossRef]
- Lyda, R.; Hamrock, J. Using Entropy Analysis to Find Encrypted and Packed Malware. IEEE Secur. Priv. 2007, 5, 40–45. [Google Scholar] [CrossRef]
- Menéndez, H.D.; Clark, D.T.; Barr, E. Getting Ahead of the Arms Race: Hothousing the Coevolution of VirusTotal with a Packer. Entropy 2021, 23, 395. [Google Scholar] [CrossRef] [PubMed]
- Hemalatha, J.; Roseline, S.A.; Geetha, S.; Kadry, S.; Damaševičius, R. An Efficient DenseNet-Based Deep Learning Model for Malware Detection. Entropy 2021, 23, 344. [Google Scholar] [CrossRef] [PubMed]
- Khamphakdee, N.; Benjamas, N.; Saiyod, S. Improving Intrusion Detection System Based on Snort Rules for Network Probe Attacks Detection with Association Rules Technique of Data Mining. J. ICT Res. Appl. 2015, 8, 234–250. [Google Scholar] [CrossRef][Green Version]
- Coşar, M.; Kiran, H.E. Performance Comparison of Open Source IDSs via Raspberry Pi. In Proceedings of the 2018 International Conference on Artificial Intelligence and Data Processing (IDAP), Malatya, Turkey, 28–30 September 2018. [Google Scholar]
- Caswell, B.; Beale, J.; Baker, A. Snort Intrusion Detection and Prevention Toolkit; Syngress: Rockland, MA, USA, 2007. [Google Scholar]
- Jin, S.; Li, M.; Wang, Z. Research and Design of Preprocessor Plugin Based on PCRE under Snort Platform. In Proceedings of the 2011 International Conference on Control, Automation and Systems Engineering (CASE), Singapore, 30–31 July 2011. [Google Scholar]
- Audi-1. GitHub, SQLI Labs. Available online: github.com/Audi-1/sqli-labs (accessed on 15 April 2021).
- Rinkish. GitHub, Sqli_Edited_Version. Available online: github.com/Rinkish/Sqli_Edited_Version (accessed on 15 April 2021).
- Ani, U.P.D.; He, H.M.; Tiwari, A. Review of cybersecurity issues in industrial critical infrastructure: Manufacturing in perspective. J. Cyber Secur. Technol. 2017, 1, 32–74. [Google Scholar] [CrossRef]
- Mohamed, N.; Al-Jaroodi, J.; Jawhar, I. Opportunities and Challenges of Data-Driven Cybersecurity for Smart Cities. In Proceedings of the 2020 IEEE Systems Security Symposium (SSS), Crystal City, VA, USA, 1 July–1 August 2020; pp. 1–7. [Google Scholar]

| Flag Type | Flag | Description | Default Value |
|---|---|---|---|
| dangerous | H (High) | High threat | −6 |
| dangerous | M (Medium) | Medium threat | −5 |
| dangerous | L (Low) | Low threat | −2 |
| Flag Type | Flag | Description | Default Value |
|---|---|---|---|
| attack | D | DDoS | −5 |
| attack | P | Phishing | −5 |
| attack | M | Malware | −5 |
| attack | R | Ransomware | −5 |
| attack | S | DoS | −5 |
| attack | X | XSS | −5 |
| Flag Type | Flag | Description | Default Value |
|---|---|---|---|
| range | S (Single) | Attack targeting the attacked station only | −1 |
| range | P (Partial) | Attack on stations affecting adjacent components | −2 |
| range | C (Complete) | Attack on stations affecting the entire network | −3 |
| Flag Type | Flag | Description | Default Value |
|---|---|---|---|
| access | N (None) | Attack does not require user response inside the network | −2 |
| access | U (User) | Attack requires user response inside the network | −1 |
| Flag Type | Flag | Description | Default Value |
|---|---|---|---|
| availability | N (None) | Attack does not affect the functionality of the station | −1 |
| availability | P (Partial) | Attack causes the loss of several functionalities and a decrease in performance | −2 |
| availability | C (Complete) | Attack causes a complete loss of control of the unit | −4 |
| Parameter | Default Value |
|---|---|
| 0.65 | |
| 0.35 | |
| 1 | |
| 1 | |
| 1 | |
| 0.5 |
| Parameter | Default Value |
|---|---|
| packet_value | 23 |
| sensitivity | 15 |
| entropy | 5 |
| Number of Iterations | Maximum Attacks Detected | Minimum Attacks Detected | Average Attacks Detected | Effectiveness | Standard Deviation |
|---|---|---|---|---|---|
| 1 | 180 | 178 | 179.2 | 99.6% | 0.6 |
| 2 | 179 | 177 | 177.8 | 98.8% | 0.6 |
| 5 | 179 | 176 | 177.2 | 98.4% | 0.7 |
| 10 | 177 | 174 | 176.0 | 97.8% | 0.9 |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Niemiec, M.; Kościej, R.; Gdowski, B. Multivariable Heuristic Approach to Intrusion Detection in Network Environments. Entropy 2021, 23, 776. https://doi.org/10.3390/e23060776
Niemiec M, Kościej R, Gdowski B. Multivariable Heuristic Approach to Intrusion Detection in Network Environments. Entropy. 2021; 23(6):776. https://doi.org/10.3390/e23060776
Chicago/Turabian StyleNiemiec, Marcin, Rafał Kościej, and Bartłomiej Gdowski. 2021. "Multivariable Heuristic Approach to Intrusion Detection in Network Environments" Entropy 23, no. 6: 776. https://doi.org/10.3390/e23060776
APA StyleNiemiec, M., Kościej, R., & Gdowski, B. (2021). Multivariable Heuristic Approach to Intrusion Detection in Network Environments. Entropy, 23(6), 776. https://doi.org/10.3390/e23060776







