Distributing Secret Keys with Quantum Continuous Variables: Principle, Security and Implementations
Abstract
:1. Introduction
2. Principle of CVQKD with Coherent States
3. Security Analysis
- Composable security against arbitrary attacks, if one can bound the trace distance of Equation (3), without any restriction on the input state of the protocol.
- Composable security against collective attacks, if one can bound the trace distance of Equation (3) under the restriction that the input state is identically and independently distributed, i.e., .
- Security against collective attacks in the asymptotic limit of infinitely many uses of the channel, if one can compute an upper bound on the Holevo information, from Equation (1), between the raw key and the adversary, assuming that the quantum state shared by Alice and Bob is known. In the case of CV protocols, one only needs to assume that the covariance matrix of the state is known.
| Protocol | (PM) State Preparation | (PM) Modulation | Bob’s Measurement | Best Currently-Available Security Proofs |
|---|---|---|---|---|
| [41] | squeezed | Gaussian | homodyne | Finite-size [38,39] |
| for practical N | ||||
| [23] | coherent | Gaussian | heterodyne | Finite-size [24] |
| for practical N | ||||
| for practical N [37] | ||||
| [22] | coherent | Gaussian | homodyne | asymptotic collective [30,31,42] |
| [43] | coherent | Gaussian 1D | homodyne | asymptotic collective [43] |
| [44] | squeezed | Gaussian | heterodyne | asymptotic collective [45] |
| [46] | thermal | Gaussian | homo/heterodyne | asymptotic collective [47,48,49] |
| [50] | squeezed | Gaussian + additional Gaussian | homodyne | asymptotic collective [50] |
| [51,52] | coherent | Gaussian | homo/heterodyne + Gaussian post-selection | asymptotic collective [51,52] |
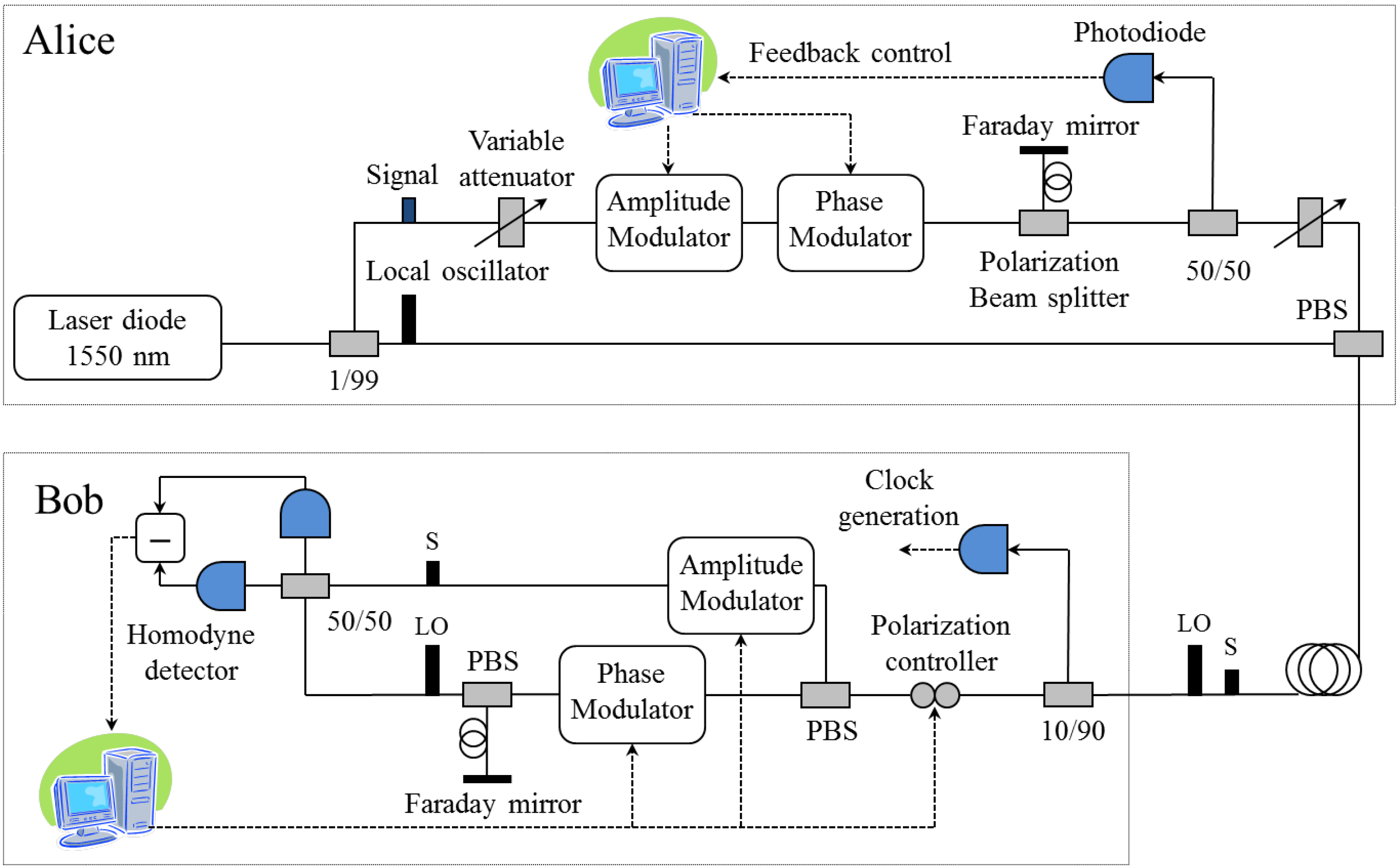
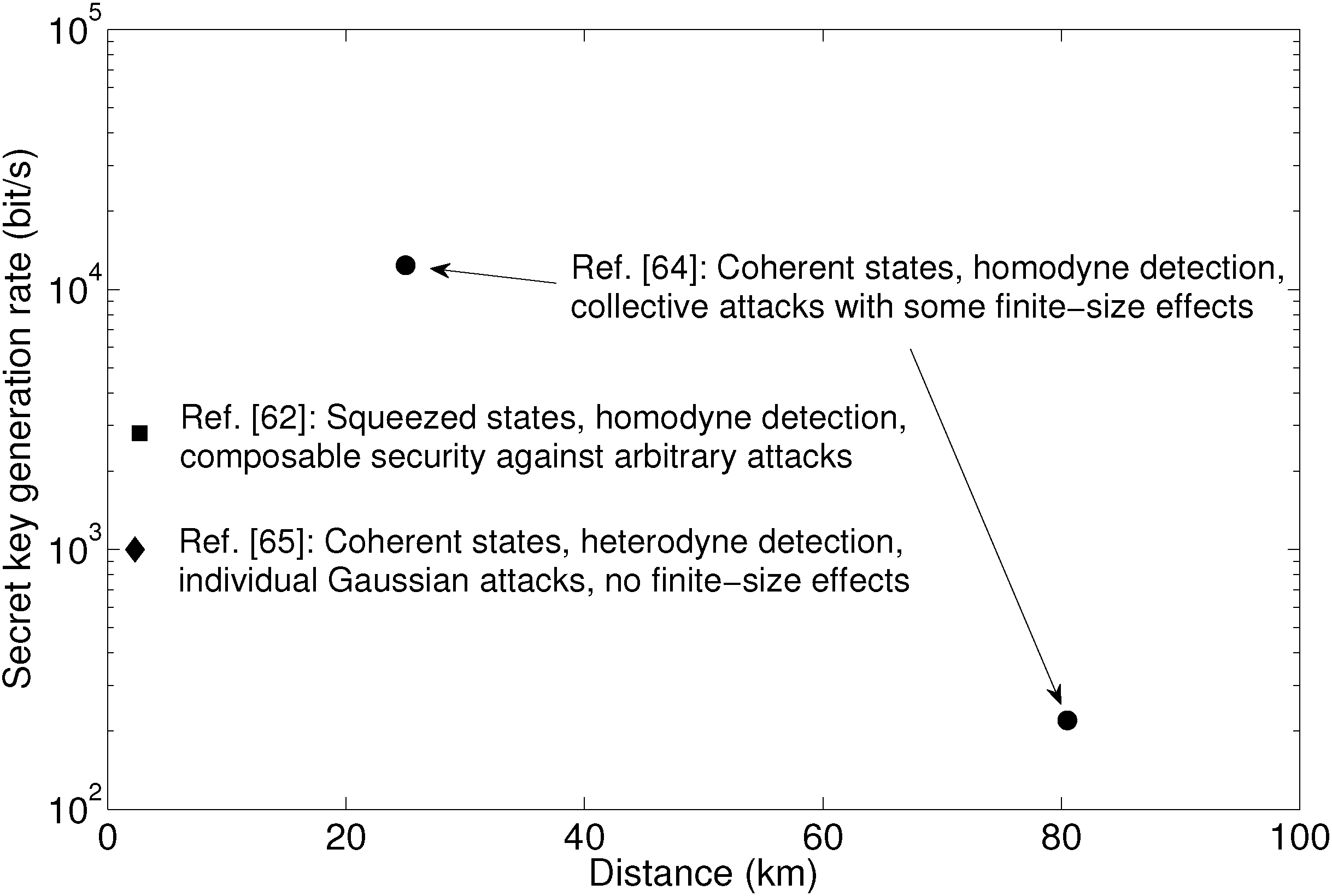
4. Experimental Implementations
5. Imperfections and Side Channels in Practical CVQKD
5.1. State Preparation
5.2. Local Oscillator Manipulation
5.3. Detection
6. Conclusions and Perspectives
Acknowledgments
Conflicts of Interest
References
- Bennett, C.H.; Brassard, G. Quantum cryptography: Public key distribution and coin tossing. In Proceedings of the IEEE International Conference on Computers, Systems, and Signal Processing, Bangalore, India, 10–19 December 1984; Volume 175.
- Shannon, C.E. A mathematical theory of communication. Bell Syst. Tech. J. 1948, 27, 379–423 and 623–656. [Google Scholar] [CrossRef]
- Portmann, C. Key recycling in authentication. IEEE Trans. Inf. Theory 2014, 60, 4383–4396. [Google Scholar] [CrossRef]
- Peev, M.; Pacher, C.; Alléaume, R.; Barreiro, C.; Bouda, J.; Boxleitner, W.; Debuisschert, T.; Diamanti, E.; Dianati, M.; Dynes, J.F.; et al. The SECOQC quantum key distribution in Vienna. New J. Phys. 2009, 11, 075001. [Google Scholar] [CrossRef]
- Sasaki, M.; Fujiwara, M.; Ishizuka, H.; Klaus, W.; Wakui, K.; Takeoka, M.; Tanaka, A.; Yoshino, K.; Nambu, Y.; Takahashi, S.; et al. Field test of quantum key distribution in the Tokyo QKD Network. Opt. Express 2011, 19, 10387–10409. [Google Scholar] [CrossRef] [PubMed]
- ID Quantique. Available online: http://www.idquantique.com (accessed on 31 August 2015).
- Scarani, V.; Bechmann-Pasquinucci, H.; Cerf, N.J.; Dušek, M.; Lütkenhaus, N.; Peev, M. The security of practical quantum key distribution. Rev. Modern Phys. 2009, 81, 1301. [Google Scholar] [CrossRef]
- Takesue, H.; Nam, S.W.; Zhang, Q.; Hadfield, R.H.; Honjo, T.; Tamaki, K.; Yamamoto, Y. Quantum key distribution over a 40-dB channel loss using superconducting single-photon detectors. Nat. Photonics 2007, 1, 343–348. [Google Scholar] [CrossRef]
- Rosenberg, D.; Peterson, C.G.; Harrington, J.W.; Rice, P.R.; Dallmann, N.; Tyagi, K.T.; McCabe, K.P.; Nam, S.; Baek, B.; Hadfield, R.H.; et al. Practical long-distance quantum key distribution system using decoy levels. New J. Phys. 2009, 11, 045009. [Google Scholar] [CrossRef]
- Dixon, A.R.; Yuan, Z.L.; Dynes, J.F.; Sharpe, A.W.; Shields, A.J. Continuous operation of high bit rate quantum key distribution. Appl. Phys. Lett. 2010, 96, 161102. [Google Scholar] [CrossRef]
- Korzh, B.; Lim, C.C.W.; Houlmann, R.; Gisin, N.; Li, M.J.; Nolan, D.; Sanguinetti, B.; Thew, R.; Zbinden, H. Provably Secure and Practical Quantum Key Distribution over 307 km of Optical Fibre. Nat. Photonics 2015, 9, 163–168. [Google Scholar] [CrossRef]
- Weedbrook, C.; Pirandola, S.; García-Patrón, R.; Cerf, N.J.; Ralph, T.; Shapiro, J.; Lloyd, S. Gaussian quantum information. Rev. Modern Phys. 2012, 84, 621. [Google Scholar] [CrossRef]
- Pirandola, S.; Mancini, S.; Lloyd, S.; Braunstein, S.L. Continuous-variable quantum cryptography using two-way quantum communication. Nat. Phys. 2008, 4, 726–730. [Google Scholar] [CrossRef]
- Weedbrook, C.; Ottaviani, C.; Pirandola, S. Two-way quantum cryptography at different wavelengths. Phys. Rev. A 2014, 89, 012309. [Google Scholar] [CrossRef]
- Lorenz, S.; Korolkova, N.; Leuchs, G. Continuous-variable quantum key distribution using polarization encoding and post-selection. Appl. Phys. B 2004, 79, 273–277. [Google Scholar] [CrossRef] [Green Version]
- Heid, M.; Lütkenhaus, N. Efficiency of coherent-state quantum cryptography in the presence of loss: Influence of realistic error correction. Phys. Rev. A 2006, 73, 052316. [Google Scholar] [CrossRef]
- Leverrier, A.; Grangier, P. Unconditional Security Proof of Long-Distance Continuous-Variable Quantum Key Distribution with Discrete Modulation. Phys. Rev. Lett. 2009, 102, 180504. [Google Scholar] [CrossRef] [PubMed]
- Sych, D.; Leuchs, G. Coherent state quantum key distribution with multi letter phase-shift keying. New J. Phys. 2010, 12, 053019. [Google Scholar] [CrossRef]
- Leverrier, A.; Grangier, P. Continuous-variable quantum-key-distribution protocols with a non-Gaussian modulation. Phys. Rev. A 2011, 83, 042312. [Google Scholar] [CrossRef]
- Silberhorn, C.; Ralph, T.C.; Lütkenhaus, N.; Leuchs, G. Continuous Variable Quantum Cryptography: Beating the 3 dB Loss Limit. Phys. Rev. Lett. 2002, 89, 167901. [Google Scholar] [CrossRef] [PubMed]
- Grosshans, F.; Cerf, N.J.; Wenger, J.; Tualle-Brouri, R.; Grangier, P. Virtual entanglement and reconciliation protocols for quantum cryptography with continuous variables. Quantum Inf. Comput. 2003, 3, 535–552. [Google Scholar]
- Grosshans, F.; Grangier, P. Continuous Variable Quantum Cryptography Using Coherent States. Phys. Rev. Lett. 2002, 88, 057902. [Google Scholar] [CrossRef] [PubMed]
- Weedbrook, C.; Lance, A.M.; Bowen, W.P.; Symul, T.; Ralph, T.C.; Lam, P.K. Quantum cryptography without switching. Phys. Rev. Lett. 2004, 93, 170504. [Google Scholar] [CrossRef] [PubMed]
- Leverrier, A. Composable Security Proof for Continuous-Variable Quantum Key Distribution with Coherent States. Phys. Rev. Lett. 2015, 114, 070501. [Google Scholar] [CrossRef] [PubMed]
- Grosshans, F.; Assche, G.V.; Wenger, J.; Brouri, R.; Cerf, N.J.; Grangier, P. Quantum key distribution using Gaussian-modulated coherent states. Nature 2003, 421, 238. [Google Scholar] [CrossRef] [PubMed]
- Jouguet, P.; Elkouss, D.; Kunz-Jacques, S. High Bit Rate Continuous-Variable Quantum Key Distribution. Phys. Rev. A 2014, 90, 042329. [Google Scholar] [CrossRef]
- Devetak, I.; Winter, A. Distillation of secret key and entanglement from quantum states. Proc. R. Soc. A 2005, 461, 207–235. [Google Scholar] [CrossRef]
- Kraus, B.; Gisin, N.; Renner, R. Lower and upper bounds on the secret-key rate for quantum key distribution protocols using one-way classical communication. Phys. Rev. Lett. 2005, 95, 080501. [Google Scholar] [CrossRef] [PubMed]
- Wolf, M.M.; Giedke, G.; Cirac, J.I. Extremality of Gaussian Quantum States. Phys. Rev. Lett. 2006, 96, 080502. [Google Scholar] [CrossRef] [PubMed]
- García-Patrón, R.; Cerf, N.J. Unconditional Optimality of Gaussian Attacks against Continuous-Variable Quantum Key Distribution. Phys. Rev. Lett. 2006, 97, 190503. [Google Scholar] [CrossRef] [PubMed]
- Navascués, M.; Grosshans, F.; Acín, A. Optimality of Gaussian Attacks in Continuous-Variable Quantum Cryptography. Phys. Rev. Lett. 2006, 97, 190502. [Google Scholar] [CrossRef] [PubMed]
- Renner, R. Security of quantum key distribution. Int. J. Quantum Inf. 2008, 6, 1–127. [Google Scholar] [CrossRef]
- Canetti, R. Universally Composable Security: A New Paradigm for Cryptographic Protocols. In Proceedings of the 42nd IEEE Symposium on Foundations of Computer Science, Las Vegas, NV, USA, 14–17 October 2001; pp. 136–145.
- Furrer, F.; Åberg, J.; Renner, R. Min-and max-entropy in infinite dimensions. Commun. Math. Phys. 2011, 306, 165–186. [Google Scholar] [CrossRef]
- Berta, M.; Furrer, F.; Scholz, V.B. The smooth entropy formalism on von Neumann algebras. 2011; >arXiv:1107.5460. [Google Scholar]
- Renner, R.; Cirac, J.I. De Finetti Representation Theorem for Infinite-Dimensional Quantum Systems and Applications to Quantum Cryptography. Phys. Rev. Lett. 2009, 102, 110504. [Google Scholar] [CrossRef] [PubMed]
- Leverrier, A.; García-Patrón, R.; Renner, R.; Cerf, N.J. Security of Continuous-Variable Quantum Key Distribution Against General Attacks. Phys. Rev. Lett. 2013, 110, 030502. [Google Scholar] [CrossRef] [PubMed]
- Furrer, F.; Franz, T.; Berta, M.; Leverrier, A.; Scholz, V.B.; Tomamichel, M.; Werner, R.F. Continuous variable quantum key distribution: Finite-key analysis of composable security against coherent attacks. Phys. Rev. Lett. 2012, 109, 100502. [Google Scholar] [CrossRef] [PubMed]
- Furrer, F. Reverse-reconciliation continuous-variable quantum key distribution based on the uncertainty principle. Phys. Rev. A 2014, 90, 042325. [Google Scholar] [CrossRef]
- Furrer, F.; Berta, M.; Tomamichel, M.; Scholz, V.B.; Christandl, M. Position-momentum uncertainty relations in the presence of quantum memory. J. Math. Phys. 2014, 55, 122205. [Google Scholar] [CrossRef]
- Cerf, N.J.; Levy, M.; Assche, G.V. Quantum distribution of Gaussian keys using squeezed states. Phys. Rev. A 2001, 63, 052311. [Google Scholar] [CrossRef]
- Pirandola, S.; Braunstein, S.L.; Lloyd, S. Characterization of collective Gaussian attacks and security of coherent-state quantum cryptography. Phys. Rev. Lett. 2008, 101, 200504. [Google Scholar] [CrossRef] [PubMed]
- Usenko, V.C.; Grosshans, F. Unidimensional continuous-variable quantum key distribution. 2015; >arXiv:1504.07093. [Google Scholar]
- García-Patrón, R.; Cerf, N.J. Continuous-variable quantum key distribution protocols over noisy channels. Phys. Rev. Lett. 2009, 102, 130501. [Google Scholar] [CrossRef] [PubMed]
- Pirandola, S.; García-Patrón, R.; Braunstein, S.L.; Lloyd, S. Direct and reverse secret-key capacities of a quantum channel. Phys. Rev. Lett. 2009, 102, 050503. [Google Scholar] [CrossRef] [PubMed]
- Filip, R. Continuous-variable quantum key distribution with noisy coherent states. Phys. Rev. A 2008, 77, 022310. [Google Scholar] [CrossRef]
- Usenko, V.C.; Filip, R. Feasibility of continuous-variable quantum key distribution with noisy coherent states. Phys. Rev. A 2010, 81, 022318. [Google Scholar] [CrossRef]
- Weedbrook, C.; Pirandola, S.; Lloyd, S.; Ralph, T.C. Quantum cryptography approaching the classical limit. Phys. Rev. Lett. 2010, 105, 110501. [Google Scholar] [CrossRef] [PubMed]
- Weedbrook, C.; Pirandola, S.; Ralph, T.C. Continuous-variable quantum key distribution using thermal states. Phys. Rev. A 2012, 86, 022318. [Google Scholar] [CrossRef]
- Madsen, L.S.; Usenko, V.C.; Lassen, M.; Filip, R.; Andersen, U.L. Continuous variable quantum key distribution with modulated entangled states. Nat. Commun. 2012, 3, 1083. [Google Scholar] [CrossRef] [PubMed]
- Fiurášek, J.; Cerf, N.J. Gaussian post-selection and virtual noiseless amplification in continuous-variable quantum key distribution. Phys. Rev. A 2012, 86, 060302. [Google Scholar] [CrossRef]
- Walk, N.; Ralph, T.C.; Symul, T.; Lam, P.K. Security of continuous-variable quantum cryptography with Gaussian post-selection. Phys. Rev. A 2013, 87, 020303(R). [Google Scholar] [CrossRef]
- Silberhorn, C.; Korolkova, N.; Leuchs, G. Quantum Key Distribution with Bright Entangled Beams. Phys. Rev. Lett. 2002, 88, 167902. [Google Scholar] [CrossRef] [PubMed]
- Fossier, S.; Diamanti, E.; Debuisschert, T.; Villing, A.; Tualle-Brouri, R.; Grangier, P. Field test of a continuous-variable quantum key distribution prototype. New J. Phys. 2009, 11, 045023. [Google Scholar] [CrossRef]
- Jouguet, P.; Kunz-Jacques, S.; Debuisschert, T.; Fossier, S.; Diamanti, E.; Alléaume, R.; Tualle-Brouri, R.; Grangier, P.; Leverrier, A.; Pache, P.; et al. Field test of classical symmetric encryption with continuous variables quantum key distribution. Opt. Express 2012, 20, 14030–14041. [Google Scholar] [CrossRef] [PubMed]
- Qi, B.; Huang, L.; Qian, L.; Lo, H.K. Experimental study on the Gaussian-modulated coherent-state quantum key distribution over standard telecommunication fibers. Phys. Rev. A 2007, 76, 052323. [Google Scholar] [CrossRef]
- Lodewyck, J.; Bloch, M.; García-Patrón, R.; Fossier, S.; Karpov, E.; Diamanti, E.; Cerf, N.J.; Debuisschert, T.; Tualle-Brouri, R.; McLaughlin, S.W.; et al. Quantum key distribution over 25 km with an all-fiber continuous-variable system. Phys. Rev. A 2007, 76, 042305. [Google Scholar] [CrossRef]
- Xuan, Q.D.; Zhang, Z.; Voss, P.L. A 24 km fiber-based discretely signaled continuous variable quantum key distribution system. Opt. Express 2009, 17, 24244. [Google Scholar] [CrossRef] [PubMed]
- Shen, Y.; Zou, H.; Tian, L.; Chen, P.; Yuan, J. Experimental study on discretely modulated continuous-variable quantum key distribution. Phys. Rev. A 2010, 82, 022317. [Google Scholar] [CrossRef]
- Leverrier, A.; Alléaume, R.; Boutros, J.; Zémor, G.; Grangier, P. Multidimensional reconciliation for a continuous-variable quantum key distribution. Phys. Rev. A 2008, 77, 042325. [Google Scholar] [CrossRef]
- Jouguet, P.; Kunz-Jacques, S.; Leverrier, A. Long-distance continuous-variable quantum key distribution with a Gaussian modulation. Phys. Rev. A 2011, 84, 062317. [Google Scholar] [CrossRef]
- Gehring, T.; Händchen, V.; Duhme, J.; Furrer, F.; Franz, T.; Pacher, C.; Werner, R.F.; Schnabel, R. Implementation of Quantum Key Distribution with Composable Security against Coherent Attacks Using Einstein-Podolsky-Rosen Entanglement. 2014; arXiv:1406.6174. [Google Scholar]
- Jouguet, P.; Kunz-Jacques, S.; Diamanti, E.; Leverrier, A. Analysis of Imperfections in Practical Continuous-Variable Quantum Key Distribution. Phys. Rev. A 2012, 86, 032309. [Google Scholar] [CrossRef]
- Jouguet, P.; Kunz-Jacques, S.; Leverrier, A.; Grangier, P.; Diamanti, E. Experimental demonstration of long-distance continuous-variable quantum key distribution. Nat. Photonics 2013, 7, 378–381. [Google Scholar] [CrossRef]
- Lance, A.M.; Symul, T.; Sharma, V.; Weedbrook, C.; Ralph, T.C.; Lam, P.K. No-Switching Quantum Key Distribution Using Broadband Modulated Coherent Light. Phys. Rev. Lett. 2005, 95, 180503. [Google Scholar] [CrossRef] [PubMed]
- Symul, T.; Alton, D.J.; Assad, S.M.; Lance, A.M.; Weedbrook, C.; Ralph, T.C.; Lam, P.K. Experimental demonstration of post-selection-based continuous-variable quantum key distribution in the presence of Gaussian noise. Phys. Rev. A 2007, 76, 030303. [Google Scholar] [CrossRef]
- Blandino, R.; Leverrier, A.; Barbieri, M.; Etesse, J.; Grangier, P.; Tualle-Brouri, R. Improving the maximum transmission distance of continuous-variable quantum key distribution using a noiseless amplifier. Phys. Rev. A 2012, 86, 012327. [Google Scholar] [CrossRef]
- Fiurasek, J.; Cerf, N.J. Gaussian post-selection and virtual noiseless amplification in continuous-variable quantum key distribution. Phys. Rev. A 2012, 86, 060302(R). [Google Scholar] [CrossRef]
- Huang, D.; Fang, J.; Wang, C.; Huang, P.; Zeng, G. A 300-MHz Bandwidth Balanced Homodyne Detector for Continuous Variable Quantum Key Distribution. Chin. Phys. Lett. 2013, 30, 114209. [Google Scholar] [CrossRef]
- Zhao, Y.; Fung, C.H.F.; Qi, B.; Chen, C.; Lo, H.K. Quantum hacking: Experimental demonstration of time-shift attack against practical quantum-key-distribution systems. Phys. Rev. A 2008, 78, 042333. [Google Scholar] [CrossRef]
- Xu, F.; Qi, B.; Lo, H.K. Experimental demonstration of phase-remapping attack in a practical quantum key distribution system. New J. Phys. 2010, 12, 113026. [Google Scholar] [CrossRef]
- Lydersen, L.; Wiechers, C.; Wittmann, C.; Elser, D.; Skaar, J.; Makarov, V. Hacking commercial quantum cryptography systems by tailored bright illumination. Nat. Photonics 2010, 4, 686–689. [Google Scholar] [CrossRef]
- Gisin, N.; Fasel, S.; Kraus, B.; Zbinden, H.; Ribordy, G. Trojan-horse attacks on quantum-key-distribution systems. Phys. Rev. A 2006, 73, 022320. [Google Scholar] [CrossRef]
- Khan, I.; Jain, N.; Stiller, B.; Jouguet, P.; Kunz-Jacques, S.; Diamanti, E.; Marquardt, C.; Leuchs, G. Trojan horse attacks on practical continuous-variable quantum key distribution systems. In Proceedings of Conference on Quantum Cryptography (QCRYPT), Paris, France, 1–5 September 2014.
- Ferenczi, A.; Grangier, P.; Grosshans, F. Calibration Attack and Defense in Continuous Variable Quantum Key Distribution. In Proceedings of the European Conference on Lasers and Electro-Optics/International Quantum Electronics Conference (CLEO/Europe-IQEC), Munich, Germany, 17–22 June 2007.
- Ma, X.C.; Sun, S.H.; Jiang, M.S.; Liang, L.M. Local oscillator fluctuation opens a loophole for Eve in practical continuous-variable quantum-key-distribution systems. Phys. Rev. A 2013, 88, 022339. [Google Scholar] [CrossRef]
- Jouguet, P.; Kunz-Jacques, S.; Diamanti, E. Preventing calibration attacks on the local oscillator in continuous-variable quantum key distribution. Phys. Rev. A 2013, 87, 062313. [Google Scholar] [CrossRef]
- Jouguet, P.; Kunz-Jacques, S. Robust Shot Noise Measurement for Continuous Variable Quantum Key Distribution. Phys. Rev. A 2015, 91, 022307. [Google Scholar]
- Qi, B.; Lougovski, P.; Pooser, R.; Grice, W.; Bobrek, M. Generating the local oscillator “locally” in continuous-variable quantum key distribution based on coherent detection. 2015; >arXiv:1503.00662. [Google Scholar]
- Soh, D.B.S.; Brif, C.; Coles, P.J.; Lütkenhaus, N.; Camacho, R.M.; Urayama, J.; Sarovar, M. Self-referenced continuous-variable quantum key distribution. 2015; >arXiv:1503.04763. [Google Scholar]
- Qin, H.; Kumar, R.; Alléaume, R. Saturation attack on continuous-variable quantum key distribution system. Proc. SPIE 2013, 8899. [Google Scholar] [CrossRef]
- Ma, X.C.; Sun, S.H.; Jiang, M.S.; Liang, L.M. Wavelength attack on practical continuous-variable quantum-key-distribution system with a heterodyne protocol. Phys. Rev. A 2013, 87, 052309. [Google Scholar] [CrossRef]
- Huang, J.Z.; Kunz-Jacques, S.; Jouguet, P.; Weedbrook, C.; Yin, Z.Q.; Wang, S.; Chen, W.; Guo, G.C.; Han, Z.F. Quantum Hacking on Quantum Key Distribution Using Homodyne Detection. Phys. Rev. A 2014, 89, 032304. [Google Scholar] [CrossRef]
- Acín, A.; Brunner, N.; Gisin, N.; Massar, S.; Pironio, S.; Scarani, V. Device-independent security of quantum cryptography against collective attacks. Phys. Rev. Lett. 2007, 98, 230501. [Google Scholar] [CrossRef] [PubMed]
- Vazirani, U.; Vidick, T. Fully device-independent quantum key distribution. Phys. Rev. Lett. 2014, 113, 140501. [Google Scholar] [CrossRef] [PubMed]
- Clauser, J.F.; Horne, M.A.; Shimony, A.; Holt, R.A. Proposed experiment to test local hidden-variable theories. Phys. Rev. Lett. 1969, 23, 880. [Google Scholar] [CrossRef]
- Lo, H.K.; Curty, M.; Qi, B. Measurement-device-independent quantum key distribution. Phys. Rev. Lett. 2012, 108, 130503. [Google Scholar] [CrossRef] [PubMed]
- Braunstein, S.L.; Pirandola, S. Side-channel-free quantum key distribution. Phys. Rev. Lett. 2012, 108, 130502. [Google Scholar] [CrossRef] [PubMed]
- Pirandola, S.; Ottaviani, C.; Spedalieri, G.; Weedbrook, C.; Braunstein, S.L.; Lloyd, S.; Gehring, T.; Jacobsen, C.S.; Andersen, U.L. High-rate measurement-device-independent quantum cryptography. Nat. Photonics 2015, 9, 397–402. [Google Scholar] [CrossRef]
- Ottaviani, C.; Spedalieri, G.; Braunstein, S.L.; Pirandola, S. Continuous-variable quantum cryptography with an untrusted relay: Detailed security analysis of the symmetric configuration. Phys. Rev. A 2015, 91, 022320. [Google Scholar] [CrossRef]
- Ma, X.C.; Sun, S.H.; Jiang, M.S.; Gui, M.; Liang, L.M. Gaussian-modulated coherent-state measurement-device-independent quantum key distribution. Phys. Rev. A 2014, 89, 042335. [Google Scholar] [CrossRef]
- Li, Z.; Zhang, Y.C.; Xu, F.; Peng, X.; Guo, H. Continuous-variable measurement-device-independent quantum key distribution. Phys. Rev. A 2014, 89, 052301. [Google Scholar] [CrossRef]
- Weedbrook, C. Continuous-variable quantum key distribution with entanglement in the middle. Phys. Rev. A 2013, 87, 022308. [Google Scholar] [CrossRef]
- Tang, Y.L.; Yin, H.L.; Chen, S.J.; Liu, Y.; Zhang, W.J.; Jiang, X.; Zhang, L.; Wang, J.; You, L.X.; Guan, J.Y.; et al. Measurement-device-independent quantum key distribution over 200 km. Phys. Rev. Lett. 2014, 113, 190501. [Google Scholar] [CrossRef] [PubMed]
- Takeoka, M.; Guha, S.; Wilde, M.M. Fundamental rate-loss tradeoff for optical quantum key distribution. Nat. Commun. 2014, 5, 5235. [Google Scholar] [CrossRef] [PubMed]
- Ziebell, M.; Persechino, M.; Harris, N.; Galland, C.; Marris-Morini, D.; Vivien, L.; Diamanti, E.; Grangier, P. Towards On-Chip Continuous-Variable Quantum Key Distribution. In Proceedings of the Conference on Lasers and Electo-Optics/European Quantum Electronics Conference (CLEO/Europe-EQEC), Munich, Germany, 21–25 June 2015.
- Qi, B.; Zhu, W.; Qian, L.; Lo, H.K. Feasibility of quantum key distribution through dense wavelength division multiplexing network. New J. Phys. 2010, 12, 103042. [Google Scholar] [CrossRef]
- Kumar, R.; Qin, H.; Alléaume, R. Coexistence of continuous variable QKD with intense DWDM classical channels. New J. Phys. 2015, 17, 043027. [Google Scholar] [CrossRef]
- Heim, B.; Peuntinger, C.; Killoran, N.; Khan, I.; Wittmann, C.; Marquardt, C.; Leuchs, G. Atmospheric continuous-variable quantum communication. New J. Phys. 2014, 16, 113018. [Google Scholar] [CrossRef]
- Vallone, G.; Bacco, D.; Dequal, D.; Gaiarin, S.; Luceri, V.; Bianco, G.; Villoresi, P. Experimental Satellite Quantum Communications. Phys. Rev. Lett. 2015, 115, 040502. [Google Scholar] [CrossRef] [PubMed]
- Magnin, L.; Magniez, F.; Leverrier, A.; Cerf, N.J. Strong no-go theorem for Gaussian quantum bit commitment. Phys. Rev. A 2010, 81, 010302(R). [Google Scholar] [CrossRef]
- Mandilara, A.; Cerf, N.J. Quantum bit commitment under Gaussian constraints. Phys. Rev. A 2012, 85, 062310. [Google Scholar] [CrossRef]
- Furrer, F.; Schaffner, C.; Wehner, S. Continuous-Variable Protocols in the Noisy Quantum Storage Model. In Proceedings of Conference on Quantum Cryptography (QCRYPT), Tokyo, Japan, 28 September–2 October 2015.
- Lau, H.K.; Weedbrook, C. Quantum secret sharing with continuous-variable cluster states. Phys. Rev. A 2013, 88, 042313. [Google Scholar] [CrossRef]
- Qi, B.; Siopsis, G. Loss-tolerant position-based quantum cryptography. Phys. Rev. A 2015, 91, 042337. [Google Scholar] [CrossRef]
© 2015 by the authors; licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Diamanti, E.; Leverrier, A. Distributing Secret Keys with Quantum Continuous Variables: Principle, Security and Implementations. Entropy 2015, 17, 6072-6092. https://doi.org/10.3390/e17096072
Diamanti E, Leverrier A. Distributing Secret Keys with Quantum Continuous Variables: Principle, Security and Implementations. Entropy. 2015; 17(9):6072-6092. https://doi.org/10.3390/e17096072
Chicago/Turabian StyleDiamanti, Eleni, and Anthony Leverrier. 2015. "Distributing Secret Keys with Quantum Continuous Variables: Principle, Security and Implementations" Entropy 17, no. 9: 6072-6092. https://doi.org/10.3390/e17096072
APA StyleDiamanti, E., & Leverrier, A. (2015). Distributing Secret Keys with Quantum Continuous Variables: Principle, Security and Implementations. Entropy, 17(9), 6072-6092. https://doi.org/10.3390/e17096072





