A Review of Blockchain Technology in Knowledge-Defined Networking, Its Application, Benefits, and Challenges
Abstract
:1. Introduction
1.1. Objectives and Scope
1.2. Contributions to the Existing Literature
- As this is the first review of how blockchain technology has been applied in Knowledge-Defined Networking, this work will serve as a beneficial resource for other scholars who pursue more study in this domain;
- Survey analysis, with respect to blockchain-based parameters and intelligent networking parameters, provides insight into the distribution and statistics of existing solutions for the considered parameters;
- Advantages of and difficulties in applying blockchain in KDN are discussed while deriving recommendations to overcome the challenges.
1.3. Survey Methodology
2. Overview of Blockchain Technology
2.1. Blockchain Architecture
2.1.1. Block
Linear Blockchain
DAG Blockchain
2.1.2. Merkle Tree
2.1.3. Transaction Process
2.1.4. Blockchain Cryptography
2.2. Blockchain Consensus Algorithms
2.2.1. Proof Based Consensus
2.2.2. Vote Based Consensus
2.2.3. Hybrid Proof- and Vote-Based Consensus
2.3. Blockchain Framework
2.3.1. Data Layer
2.3.2. Network Layer
2.3.3. Application Layer
Cryptocurrency
Smart Contracts
Supply Chains
Networking
Healthcare
Insurance
Voting
Intellectual Property
2.4. Blockchain Characteristics
2.5. Blockchain Vulnerabilities
- Network attacks—Attacks related to the blockchain network, such as denial of service attacks that submit more transactions than the blockchain’s capacity, routing attacks, domain name service attacks, eclipse attacks, etc., fall under this category [142];
- Endpoint attacks—Endpoint attacks target endpoints (nodes) in the network of a blockchain. In the 51% vulnerability, malicious nodes, consisting of greater than 50% of the network endpoints, can manipulate the blockchain in a malicious manner, compromising the security. Another endpoint attack is the cryptojacking attack, where an attacker uses a node’s computational resources to mine cryptocurrencies [143];
- Intentional misuse—Intentional misuse refers to individuals exploiting vulnerabilities in the blockchain network for personal gain. In a double-spending attack, the individuals trick the blockchain network into performing two transactions simultaneously by using the cryptocurrency sufficient for one transaction [144]. In selfish mining, miners intentionally delay the broadcasting of mined blocks to obtain a knowledge advantage over other nodes [145];
- Code vulnerabilities—Code vulnerabilities refer to the misconfiguration or poor use of software code. For example, broken access control refers to misconfiguration or poorly implemented access control such that unauthorized users may obtain access to sensitive data on the blockchain [146]. Criminal smart contracts are smart contracts implementing contractual actions to deceive or harm blockchain users in order to steal cryptocurrency, promote illegal transactions, etc. [147];
- Data exposure—This refers to sensitive data exposure and privacy leakage, which can occur when private data are stored on the blockchain with poor encryption. Furthermore, as blockchain transactions are traceable, some of an individual’s activities can be identified [138];
- Human negligence—The security of the blockchain node may be misconfigured by humans due to negligence. If humans do not properly monitor the security logs, security breaches will not be identified in a timely manner [148].
2.6. Different Forms of Blockchain
2.6.1. Private Blockchain
2.6.2. Public Blockchain
2.6.3. Consortium Blockchain
3. Synopsis of KDN Paradigm
3.1. Introduction to Knowledge Concept
3.2. Detailed KDN Architecture
3.2.1. Knowledge/Cognitive Layer
3.2.2. Management/Administration/Measurement Layer
3.2.3. Data/Infrastructure Layer
3.2.4. Control Layer
3.2.5. Application Layer
3.3. A Glimpse Comparison of KDN with Existing Networks
4. Application of Blockchain Technology in Knowledge-Based Networks
4.1. Service Provisioning
4.1.1. Financial Services
4.1.2. Resource Sharing
4.2. Trustworthiness
4.2.1. Knowledge Sharing
4.2.2. Data Sharing
4.2.3. Trusted Machine Learning
4.3. Traffic Optimization
4.3.1. Packet Forwarding
4.3.2. Load Optimization
4.3.3. QoS Offering
4.4. Network Administration
4.4.1. User Administration
4.4.2. Mobility Administration
4.4.3. Spectrum Administration
4.4.4. Fault Administration
4.4.5. Network Address Translation (NAT) Administration
4.4.6. Energy Administration
4.5. Security and Privacy
4.5.1. Privacy
4.5.2. Authentication, Access Control, and Encryption
4.5.3. Virtual Private Networks (VPN)
4.5.4. Firewall
4.5.5. Anomaly or Intrusion Diagnosis and Suppression
4.6. Virtualization of Networks
4.7. Analysis of Big Data
4.8. Cloud Computing and Edge Computing
4.9. Networking in Data Center
5. Review Analysis
5.1. Classification of Frameworks Based on Application Category
5.2. Detailed Comparison and Performance Analysis of each Blockchain Application in Knowledge-Defined Networks
5.3. Overall Analysis
6. Discussion
6.1. Benefits
6.1.1. Better Data and Machine Learning Model Sharing
6.1.2. Better Data Storage and Data Interoperability
6.1.3. High Security and Privacy
6.1.4. Decentralized Intelligence
6.1.5. Reliable Decision Making
6.1.6. Boosted Automation
6.1.7. Better Resource Sharing
6.1.8. Better Network Administration
6.2. Challenges
6.2.1. Processing of Large Volumes of Data
6.2.2. High Energy Consumption
6.2.3. Difficulties in Resource Management
6.2.4. Lack of Standardization and Interoperability of Blockchains
6.2.5. Scalability of Blockchain
6.2.6. Increased Latency and Limited Throughput
6.2.7. Security Vulnerabilities of Blockchain
6.2.8. Requirement of Extra Resources
7. Final Thoughts, Propositions, and Prospects for the Future
- In blockchain systems integrated with KDN, as the handling and processing of big data were identified as challenges, alternative techniques for improving the handling and processing of big data in blockchain are recommended. These include sharding [394], compression, fragmentation of data, parallel processing [4], and using off-chain storage of data while storing metadata in the blockchain for verification [397];
- As resource management is challenging in blockchain systems, it is recommended to use appropriate optimization [398] techniques to optimize resource management for efficient performance of tasks such as consensus;
- It is advised to use a directed acyclic network to build blockchain with the aim of increasing its capacity for a growth-based approach having parallel processing capability [4]. Furthermore, lightweight and low-energy-consuming blockchain frameworks such as Sensor-Chain [393] can be utilized in KDN systems to improve scalability. Not only that, but off-chain storage [397] is also recommended to improve scalability;
- With the goal of reducing the extra latency imposed by blockchains, which makes the operation of the KDN system challenging, sharding and pruning [394] techniques are recommended;
- As conventional linear blockchains are well known for low transaction throughput, if such blockchains are employed in a KDN, it can limit the performance of the KDN system. Therefore, to obtain maximum performance from the KDN, high-throughput blockchain frameworks such as Conflux [396], which are based on the DAG blockchain, are recommended;
- To overcome the known security vulnerabilities of blockchain, different techniques can be recommended. First, in order to mitigate security attacks such as DDoS attack detection, ML algorithms can be utilized [401]. For preventing privacy exposure in sensitive data, strong encryption such as post-quantum cryptography with robust error detection and masking techniques is recommended, while to detect code vulnerabilities, the employment of AI and human experts is recommended;
- As blockchains cause additional resource expenditure in KDN systems, it is recommended to utilize intelligent networking with resource-efficient blockchain systems [13].
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Kim, S. Blockchain for a trust network among intelligent vehicles. In Advances in Computers; Elsevier: Amsterdam, The Netherlands, 2018; Volume 111, pp. 43–68. [Google Scholar]
- Giungato, P.; Rana, R.; Tarabella, A.; Tricase, C. Current trends in sustainability of bitcoins and related blockchain technology. Sustainability 2017, 9, 2214. [Google Scholar] [CrossRef]
- Park, J.; Park, K. A lightweight blockchain scheme for a secure smart dust IoT environment. Appl. Sci. 2020, 10, 8925. [Google Scholar] [CrossRef]
- Lee, S.W.; Sim, K.B. Design and hardware implementation of a simplified DAG-based blockchain and new AES-CBC algorithm for IoT security. Electronics 2021, 10, 1127. [Google Scholar] [CrossRef]
- Oyinloye, D.P.; Teh, J.S.; Jamil, N.; Alawida, M. Blockchain consensus: An overview of alternative protocols. Symmetry 2021, 13, 1363. [Google Scholar] [CrossRef]
- Panarello, A.; Tapas, N.; Merlino, G.; Longo, F.; Puliafito, A. Blockchain and iot integration: A systematic survey. Sensors 2018, 18, 2575. [Google Scholar] [CrossRef] [PubMed]
- Yang, G.; Lee, K.; Lee, K.; Yoo, Y.; Lee, H.; Yoo, C. Resource Analysis of Blockchain Consensus Algorithms in Hyperledger Fabric. IEEE Access 2022, 10, 74902–74920. [Google Scholar] [CrossRef]
- Singh, S.; Sharma, P.K.; Yoon, B.; Shojafar, M.; Cho, G.H.; Ra, I.H. Convergence of blockchain and artificial intelligence in IoT network for the sustainable smart city. Sustain. Cities Soc. 2020, 63, 102364. [Google Scholar] [CrossRef]
- Singh, J.; Sajid, M.; Gupta, S.K.; Haidri, R.A. Artificial Intelligence and Blockchain Technologies for Smart City. In Intelligent Green Technologies for Sustainable Smart Cities; John Wiley & Sons: Hoboken, NJ, USA, 2022; pp. 317–330. [Google Scholar]
- Marwala, T.; Xing, B. Blockchain and artificial intelligence. arXiv 2018, arXiv:1802.04451. [Google Scholar]
- Tagde, P.; Tagde, S.; Bhattacharya, T.; Tagde, P.; Chopra, H.; Akter, R.; Kaushik, D.; Rahman, M.H. Blockchain and artificial intelligence technology in e-Health. Environ. Sci. Pollut. Res. 2021, 28, 52810–52831. [Google Scholar] [CrossRef]
- Fu, Y.; Li, C.; Yu, F.R.; Luan, T.H.; Zhao, P.; Liu, S. A survey of blockchain and intelligent networking for the metaverse. IEEE Internet Things J. 2022, 10, 3587–3610. [Google Scholar] [CrossRef]
- Khan, M.A.; Abbas, S.; Rehman, A.; Saeed, Y.; Zeb, A.; Uddin, M.I.; Nasser, N.; Ali, A. A machine learning approach for blockchain-based smart home networks security. IEEE Netw. 2020, 35, 223–229. [Google Scholar] [CrossRef]
- Latif, S.A.; Wen, F.B.X.; Iwendi, C.; Li-li, F.W.; Mohsin, S.M.; Han, Z.; Band, S.S. AI-empowered, blockchain and SDN integrated security architecture for IoT network of cyber physical systems. Comput. Commun. 2022, 181, 274–283. [Google Scholar] [CrossRef]
- Mishra, S.; AlShehri, M.A.R. Software defined networking: Research issues, challenges and opportunities. Indian J. Sci. Technol. 2017, 10, 1–9. [Google Scholar] [CrossRef]
- Haji, S.H.; Zeebaree, S.R.; Saeed, R.H.; Ameen, S.Y.; Shukur, H.M.; Omar, N.; Sadeeq, M.A.; Ageed, Z.S.; Ibrahim, I.M.; Yasin, H.M. Comparison of software defined networking with traditional networking. Asian J. Res. Comput. Sci. 2021, 9, 1–18. [Google Scholar] [CrossRef]
- Bhatia, J.; Modi, Y.; Tanwar, S.; Bhavsar, M. Software defined vehicular networks: A comprehensive review. Int. J. Commun. Syst. 2019, 32, e4005. [Google Scholar] [CrossRef]
- Zhu, M.; Cai, Z.P.; Xu, M.; Cao, J.N. Software-defined vehicular networks: Opportunities and challenges. In Energy Science and Applied Technology; CRC Press: Boca Raton, FL, USA, 2015; pp. 247–251. [Google Scholar]
- Nunes, B.A.A.; Mendonca, M.; Nguyen, X.N.; Obraczka, K.; Turletti, T. A survey of software-defined networking: Past, present, and future of programmable networks. IEEE Commun. Surv. Tutor. 2014, 16, 1617–1634. [Google Scholar] [CrossRef]
- Islam, M.M.; Khan, M.T.R.; Saad, M.M.; Kim, D. Software-defined vehicular network (SDVN): A survey on architecture and routing. J. Syst. Archit. 2021, 114, 101961. [Google Scholar] [CrossRef]
- Adbeb, T.; Wu, D.; Ibrar, M. Software-defined networking (SDN) based VANET architecture: Mitigation of traffic congestion. Int. J. Adv. Comput. Sci. Appl. 2020, 11, 706–714. [Google Scholar] [CrossRef]
- Liu, K.; Xu, X.; Chen, M.; Liu, B.; Wu, L.; Lee, V.C. A hierarchical architecture for the future internet of vehicles. IEEE Commun. Mag. 2019, 57, 41–47. [Google Scholar] [CrossRef]
- Toufga, S.; Abdellatif, S.; Assouane, H.T.; Owezarski, P.; Villemur, T. Towards dynamic controller placement in software defined vehicular networks. Sensors 2020, 20, 1701. [Google Scholar] [CrossRef]
- Tselios, C.; Politis, I.; Kotsopoulos, S. Enhancing SDN security for IoT-related deployments through blockchain. In Proceedings of the 2017 IEEE Conference on Network Function Virtualization and Software Defined Networks (NFV-SDN), Berlin, Germany, 6–8 November 2017; pp. 303–308. [Google Scholar]
- Fonseca, P.C.; Mota, E.S. A survey on fault management in software-defined networks. IEEE Commun. Surv. Tutor. 2017, 19, 2284–2321. [Google Scholar] [CrossRef]
- Akhunzada, A.; Khan, M.K. Toward secure software defined vehicular networks: Taxonomy, requirements, and open issues. IEEE Commun. Mag. 2017, 55, 110–118. [Google Scholar] [CrossRef]
- Zhao, L.; Li, J.; Al-Dubai, A.; Zomaya, A.Y.; Min, G.; Hawbani, A. Routing schemes in software-defined vehicular networks: Design, open issues and challenges. IEEE Intell. Transp. Syst. Mag. 2020, 13, 217–226. [Google Scholar] [CrossRef]
- Quan, W.; Cheng, N.; Qin, M.; Zhang, H.; Chan, H.A.; Shen, X. Adaptive transmission control for software defined vehicular networks. IEEE Wirel. Commun. Lett. 2018, 8, 653–656. [Google Scholar] [CrossRef]
- Nisar, K.; Jimson, E.R.; Hijazi, M.H.A.; Welch, I.; Hassan, R.; Aman, A.H.M.; Sodhro, A.H.; Pirbhulal, S.; Khan, S. A survey on the architecture, application, and security of software defined networking: Challenges and open issues. Internet Things 2020, 12, 100289. [Google Scholar] [CrossRef]
- Deveaux, D.; Higuchi, T.; Uçar, S.; Härri, J.; Altintas, O. A definition and framework for vehicular knowledge networking: An application of knowledge-centric networking. IEEE Veh. Technol. Mag. 2021, 16, 57–67. [Google Scholar] [CrossRef]
- Ucar, S.; Higuchi, T.; Wang, C.H.; Deveaux, D.; Härri, J.; Altintas, O. Vehicular knowledge networking and application to risk reasoning. In Proceedings of the Twenty-First International Symposium on Theory, Algorithmic Foundations, and Protocol Design for Mobile Networks and Mobile Computing, New York, NY, USA, 11–14 October 2020; pp. 351–356. [Google Scholar]
- Ucar, S.; Higuchi, T.; Wang, C.H.; Deveaux, D.; Altintas, O.; Härri, J. Vehicular Knowledge Networking and Mobility-Aware Smart Knowledge Placement. In Proceedings of the 2022 IEEE 19th Annual Consumer Communications & Networking Conference (CCNC), Las Vegas, NV, USA, 8–11 January 2022; pp. 593–598. [Google Scholar]
- Ruta, M.; Scioscia, F.; Gramegna, F.; Ieva, S.; Di Sciascio, E.; De Vera, R.P. A knowledge fusion approach for context awareness in vehicular networks. IEEE Internet Things J. 2018, 5, 2407–2419. [Google Scholar] [CrossRef]
- Wu, D.; Li, Z.; Wang, J.; Zheng, Y.; Li, M.; Huang, Q. Vision and challenges for knowledge centric networking. IEEE Wirel. Commun. 2019, 6, 117–123. [Google Scholar] [CrossRef]
- Liu, J.; Xu, Q. Machine learning in software defined network. In Proceedings of the 2019 IEEE 3rd Information Technology, Networking, Electronic and Automation Control Conference (ITNEC), Chengdu, China, 15–17 March 2019; pp. 1114–1120. [Google Scholar]
- Wijesekara, P.A.D.S.N. An Accurate Mathematical Epidemiological Model (SEQIJRDS) to Recommend Public Health Interventions Related to COVID-19 in Sri Lanka. Res. Sq. 2021, Preprint. [Google Scholar] [CrossRef]
- Clark, D.D.; Partridge, C.; Ramming, J.C.; Wroclawski, J.T. A knowledge plane for the internet. In Proceedings of the 2003 Conference on Applications, Technologies, Architectures, and Protocols for Computer Communications, Karlsruhe, Germany, 5–29 August 2003; pp. 3–10. [Google Scholar]
- Alzahrani, A.O.; Alenazi, M.J. Designing a network intrusion detection system based on machine learning for software defined networks. Future Internet 2021, 13, 111. [Google Scholar] [CrossRef]
- Polat, H.; Polat, O.; Cetin, A. Detecting DDoS attacks in software-defined networks through feature selection methods and machine learning models. Sustainability 2020, 12, 1035. [Google Scholar] [CrossRef]
- Dey, S.K.; Rahman, M.M. Effects of machine learning approach in flow-based anomaly detection on software-defined networking. Symmetry 2019, 12, 7. [Google Scholar] [CrossRef]
- Yoo, Y.; Yang, G.; Shin, C.; Lee, J.; Yoo, C. Control Channel Isolation in SDN Virtualization: A Machine Learning Approach. In Proceedings of the 2023 IEEE/ACM 23rd International Symposium on Cluster, Cloud and Internet Computing (CCGrid), Bangalore, India, 1–4 May 2023; pp. 273–285. [Google Scholar]
- Khan, M.I.; Aubet, F.X.; Pahl, M.O.; Härri, J. Deep learning-aided resource orchestration for vehicular safety communication. In Proceedings of the 2019 Wireless Days (WD), Manchester, UK, 24–26 April 2019; pp. 1–8. [Google Scholar]
- Mohammed, A.R.; Mohammed, S.A.; Shirmohammadi, S. Machine learning and deep learning based traffic classification and prediction in software defined networking. In Proceedings of the 2019 IEEE International Symposium on Measurements & Networking (M&N), Catania, Italy, 8–10 July 2019; pp. 1–6. [Google Scholar]
- Indira, B.; Valarmathi, K.; Devaraj, D. An approach to enhance packet classification performance of software-defined network using deep learning. Soft Comput. 2019, 23, 8609–8619. [Google Scholar] [CrossRef]
- Wijesekara, P.A.D.S.N.; Sudheera, K.L.K.; Sandamali, G.G.N.; Chong, P.H.J. Machine Learning Based Link Stability Prediction for Routing in Software Defined Vehicular Networks. In Proceedings of the 20th Academic Sessions, Matara, Sri Lanka, 7 June 2023; p. 60. [Google Scholar]
- Wijesekara, P.A.D.S.N.; Gunawardena, S. A Machine Learning-Aided Network Contention-Aware Link Lifetime- and Delay-Based Hybrid Routing Framework for Software-Defined Vehicular Networks. Telecom 2023, 4, 393–458. [Google Scholar] [CrossRef]
- Toufga, S.; Abdellatif, S.; Owezarski, P.; Villemur, T.; Relizani, D. Effective prediction of V2I link lifetime and vehicle’s next cell for software defined vehicular networks: A machine learning approach. In Proceedings of the 2019 IEEE Vehicular Networking Conference (VNC), Los Angeles, NV, USA, 4–6 December 2019; pp. 1–8. [Google Scholar]
- Amari, H.; Louati, W.; Khoukhi, L.; Belguith, L.H. Securing software-defined vehicular network architecture against ddos attack. In Proceedings of the 2021 IEEE 46th Conference on Local Computer Networks (LCN), Edmonton, AB, Canada, 4–7 October 2021; pp. 653–656. [Google Scholar]
- Zhang, D.; Yu, F.R.; Yang, R. A machine learning approach for software-defined vehicular ad hoc networks with trust management. In Proceedings of the 2018 IEEE Global Communications Conference (GLOBECOM), Abu Dhabi, UAE, 9–13 December 2018; pp. 1–6. [Google Scholar]
- Latah, M.; Toker, L. Artificial intelligence enabled software-defined networking: A comprehensive overview. IET Netw. 2019, 8, 79–99. [Google Scholar]
- Lu, W.; Liang, L.; Kong, B.; Li, B.; Zhu, Z. AI-assisted knowledge-defined network orchestration for energy-efficient data center networks. IEEE Commun. Mag. 2020, 58, 86–92. [Google Scholar] [CrossRef]
- Hyun, J.; Van Tu, N.; Hong, J.W.K. Towards knowledge-defined networking using in-band network telemetry. In Proceedings of the NOMS 2018—2018 IEEE/IFIP Network Operations and Management Symposium, Taipei, Taiwan, 23–27 April 2018; pp. 1–7. [Google Scholar]
- Hu, Y.; Li, Z.; Lan, J.; Wu, J.; Yao, L. EARS: Intelligence-driven experiential network architecture for automatic routing in software-defined networking. China Commun. 2020, 17, 149–162. [Google Scholar] [CrossRef]
- Gosh, S.; El Boudani, B.; Dagiuklas, T.; Iqbal, M. SO-KDN: A Self-Organised Knowledge Defined Networks Architecture for Reliable Routing. In Proceedings of the 4th International Conference on Information Science and Systems, Edinburgh, UK, 17–19 March 2021; pp. 160–166. [Google Scholar]
- Rafiq, A.; Rehman, S.; Young, R.; Song, W.C.; Khan, M.A.; Kadry, S.; Srivastava, G. Knowledge defined networks on the edge for service function chaining and reactive traffic steering. Clust. Comput. 2023, 26, 613–634. [Google Scholar] [CrossRef]
- Duque-Torres, A.; Amezquita-Suárez, F.; Caicedo Rendon, O.M.; Ordóñez, A.; Campo, W.Y. An approach based on knowledge-defined networking for identifying heavy-hitter flows in data center networks. Appl. Sci. 2019, 9, 4808. [Google Scholar] [CrossRef]
- Herrera, L.M.C.; Torres, A.D.; Munoz, W.Y.C. An approach based on knowledge-defined networking for identifying video streaming flows in 5G networks. IEEE Lat. Am. Trans. 2021, 19, 1737–1744. [Google Scholar] [CrossRef]
- Gheisari, M.; Ebrahimzadeh, F.; Rahimi, M.; Moazzamigodarzi, M.; Liu, Y.; Dutta Pramanik, P.K.; Heravi, M.A.; Mehbodniya, A.; Ghaderzadeh, M.; Feylizadeh, M.R.; et al. Deep learning: Applications, architectures, models, tools, and frameworks: A comprehensive survey. CAAI Trans. Intell. Technol. 2023, 1–26. [Google Scholar] [CrossRef]
- Sadoughi, F.; Ghaderzadeh, M.; Solimany, M.; Fein, R. An intelligent system based on back propagation neural network and particle swarm optimization for detection of prostate cancer from benign hyperplasia of prostate. J. Health Med. Informat 2014, 5, 1000158. [Google Scholar]
- Ghaderzadeh, M.; Aria, M.; Hosseini, A.; Asadi, F.; Bashash, D.; Abolghasemi, H. A fast and efficient CNN model for B-ALL diagnosis and its subtypes classification using peripheral blood smear images. Int. J. Intell. Syst. 2022, 37, 5113–5133. [Google Scholar] [CrossRef]
- Li, Y.; Su, X.; Ding, A.Y.; Lindgren, A.; Liu, X.; Prehofer, C.; Riekki, J.; Rahmani, R.; Tarkoma, S.; Hui, P. Enhancing the internet of things with knowledge-driven software-defined networking technology: Future perspectives. Sensors 2020, 20, 3459. [Google Scholar] [CrossRef]
- Mestres, A.; Rodriguez-Natal, A.; Carner, J.; Barlet-Ros, P.; Alarcón, E.; Solé, M.; Muntés-Mulero, V.; Meyer, D.; Barkai, S.; Hibbett, M.J.; et al. Knowledge-defined networking. ACM SIGCOMM Comput. Commun. Rev. 2017, 47, 2–10. [Google Scholar] [CrossRef]
- Yao, H.; Mai, T.; Xu, X.; Zhang, P.; Li, M.; Liu, Y. NetworkAI: An intelligent network architecture for self-learning control strategies in software defined networks. IEEE Internet Things J. 2018, 5, 4319–4327. [Google Scholar] [CrossRef]
- Wijesekara, P.A.D.S.N.; Gunawardena, S. A Comprehensive Survey on Knowledge-Defined Networking. Telecom 2023, 4, 477–596. [Google Scholar]
- Alharbi, T. Deployment of blockchain technology in software defined networks: A survey. IEEE Access 2020, 8, 9146–9156. [Google Scholar] [CrossRef]
- Rahman, A.; Montieri, A.; Kundu, D.; Karim, M.R.; Islam, M.J.; Umme, S.; Nascita, A.; Pescapé, A. On the integration of blockchain and sdn: Overview, applications, and future perspectives. J. Netw. Syst. Manag. 2022, 30, 73. [Google Scholar]
- Nam Nguyen, H.; Anh Tran, H.; Fowler, S.; Souihi, S. A survey of Blockchain technologies applied to software-defined networking: Research challenges and solutions. IET Wirel. Sens. Syst. 2021, 11, 233–247. [Google Scholar]
- Miglani, A.; Kumar, N. Blockchain management and machine learning adaptation for IoT environment in 5G and beyond networks: A systematic review. Comput. Commun. 2021, 178, 37–63. [Google Scholar] [CrossRef]
- Ismail, S.; Dawoud, D.W.; Reza, H. Securing Wireless Sensor Networks Using Machine Learning and Blockchain: A Review. Future Internet 2023, 15, 200. [Google Scholar] [CrossRef]
- Mololoth, V.K.; Saguna, S.; Åhlund, C. Blockchain and machine° learning for future smart grids: A review. Energies 2023, 16, 528. [Google Scholar] [CrossRef]
- Mazhar, T.; Irfan, H.M.; Khan, S.; Haq, I.; Ullah, I.; Iqbal, M.; Hamam, H. Analysis of Cyber Security Attacks and Its Solutions for the Smart Grid Using Machine Learning and Blockchain Methods. Future Internet 2023, 15, 83. [Google Scholar] [CrossRef]
- Krichen, M.; Ammi, M.; Mihoub, A.; Almutiq, M. Blockchain for modern applications: A survey. Sensors 2022, 22, 5274. [Google Scholar] [CrossRef]
- Xia, Q.; Sifah, E.B.; Smahi, A.; Amofa, S.; Zhang, X. BBDS: Blockchain-based data sharing for electronic medical records in cloud environments. Information 2017, 8, 44. [Google Scholar] [CrossRef]
- Ismail, L.; Materwala, H. A review of blockchain architecture and consensus protocols: Use cases, challenges, and solutions. Symmetry 2019, 11, 1198. [Google Scholar] [CrossRef]
- Son, B.; Lee, J.; Jang, H. A scalable IoT protocol via an efficient DAG-based distributed ledger consensus. Sustainability 2020, 12, 1529. [Google Scholar] [CrossRef]
- Hellani, H.; Sliman, L.; Samhat, A.E.; Exposito, E. Computing resource allocation scheme for DAG-based IOTA nodes. Sensors 2021, 21, 4703. [Google Scholar] [CrossRef]
- Gayoso Martinez, V.; Hernández-Álvarez, L.; Hernandez Encinas, L. Analysis of the cryptographic tools for blockchain and bitcoin. Mathematics 2020, 8, 131. [Google Scholar] [CrossRef]
- Castellon, C.; Roy, S.; Kreidl, P.; Dutta, A.; Bölöni, L. Energy efficient merkle trees for blockchains. In Proceedings of the 2021 IEEE 20th International Conference on Trust, Security and Privacy in Computing and Communications (TrustCom), Shenyang, China, 20–22 October 2021; pp. 1093–1099. [Google Scholar]
- Ngabo, D.; Wang, D.; Iwendi, C.; Anajemba, J.H.; Ajao, L.A.; Biamba, C. Blockchain-based security mechanism for the medical data at fog computing architecture of internet of things. Electronics 2021, 10, 2110. [Google Scholar] [CrossRef]
- Fang, W.; Chen, W.; Zhang, W.; Pei, J.; Gao, W.; Wang, G. Digital signature scheme for information non-repudiation in blockchain: A state of the art review. EURASIP J. Wirel. Commun. Netw. 2020, 2020, 56. [Google Scholar] [CrossRef]
- Nawaz, A.; Peña Queralta, J.; Guan, J.; Awais, M.; Gia, T.N.; Bashir, A.K.; Kan, H.; Westerlund, T. Edge computing to secure iot data ownership and trade with the ethereum blockchain. Sensors 2020, 20, 3965. [Google Scholar] [CrossRef] [PubMed]
- Khanal, Y.P.; Alsadoon, A.; Shahzad, K.; Al-Khalil, A.B.; Prasad, P.W.; Rehman, S.U.; Islam, R. Utilizing blockchain for iot privacy through enhanced ECIES with secure hash function. Future Internet 2022, 14, 77. [Google Scholar] [CrossRef]
- Seok, B.; Park, J.; Park, J.H. A lightweight hash-based blockchain architecture for industrial IoT. Appl. Sci. 2019, 9, 3740. [Google Scholar] [CrossRef]
- Pop, C.D.; Antal, M.; Cioara, T.; Anghel, I.; Salomie, I. Blockchain and demand response: Zero-knowledge proofs for energy transactions privacy. Sensors 2020, 20, 5678. [Google Scholar] [CrossRef] [PubMed]
- Gupta, S.; Gupta, K.K.; Shukla, P.K.; Shrivas, M.K. Blockchain-based voting system powered by post-quantum cryptography (BBVSP-pqc). In Proceedings of the 2022 Second International Conference on Power, Control and Computing Technologies (ICPC2T), Raipur, India, 1–3 March 2022; pp. 1–8. [Google Scholar]
- Anastasova, M.; Azarderakhsh, R.; Kermani, M.M.; Beshaj, L. Time-Efficient Finite Field Microarchitecture Design for Curve448 and Ed448 on Cortex-M4. In Proceedings of the International Conference on Information Security and Cryptology, Seoul, Republic of Korea, 30 November 2022–2 December 2022; pp. 292–314. [Google Scholar]
- Anastasova, M.; Azarderakhsh, R.; Kermani, M.M. Fast strategies for the implementation of SIKE round 3 on ARM Cortex-M4. IEEE Trans. Circuits Syst. I: Regul. Pap. 2021, 68, 4129–4141. [Google Scholar] [CrossRef]
- Sanal, P.; Karagoz, E.; Seo, H.; Azarderakhsh, R.; Mozaffari-Kermani, M. Kyber on ARM64: Compact implementations of Kyber on 64-bit ARM Cortex-A processors. In Proceedings of the International Conference on Security and Privacy in Communication Systems, virtual event, 6–9 September 2021; pp. 424–440. [Google Scholar]
- Bisheh-Niasar, M.; Azarderakhsh, R.; Mozaffari-Kermani, M. Cryptographic accelerators for digital signature based on Ed25519. IEEE Trans. Very Large Scale Integr. (VLSI) Syst. 2021, 29, 1297–1305. [Google Scholar] [CrossRef]
- Jalali, A.; Azarderakhsh, R.; Kermani, M.M.; Jao, D. Supersingular isogeny Diffie-Hellman key exchange on 64-bit ARM. IEEE Trans. Dependable Secur. Comput. 2017, 16, 902–912. [Google Scholar] [CrossRef]
- Kaur, J.; Sarker, A.; Kermani, M.M.; Azarderakhsh, R. Hardware Constructions for Error Detection in Lightweight Welch-Gong (WG)-Oriented Streamcipher WAGE Benchmarked on FPGA. IEEE Trans. Emerg. Top. Comput. 2021, 10, 1208–1215. [Google Scholar] [CrossRef]
- Kermani, M.M.; Azarderakhsh, R.; Xie, J. Error detection reliable architectures of Camellia block cipher applicable to different variants of its substitution boxes. In Proceedings of the 2016 IEEE Asian Hardware-Oriented Security and Trust (AsianHOST), Yilan, Taiwan, 19–20 December 2016; pp. 1–6. [Google Scholar]
- Aghaie, A.; Kermani, M.M.; Azarderakhsh, R. Fault diagnosis schemes for low-energy block cipher Midori benchmarked on FPGA. IEEE Trans. Very Large Scale Integr. (VLSI) Syst. 2016, 25, 1528–1536. [Google Scholar] [CrossRef]
- Kaur, J.; Kermani, M.M.; Azarderakhsh, R. Hardware constructions for lightweight cryptographic block cipher QARMA with error detection mechanisms. IEEE Trans. Emerg. Top. Comput. 2020, 10, 514–519. [Google Scholar] [CrossRef]
- Kermani, M.M.; Azarderakhsh, R. Lightweight hardware architectures for fault diagnosis schemes of efficiently-maskable cryptographic substitution boxes. In Proceedings of the 2016 IEEE International Conference on Electronics, Circuits and Systems (ICECS), Monte Carlo, Monaco, 11–14 December 2016; pp. 764–767. [Google Scholar]
- Sapra, N.; Shaikh, I.; Dash, A. Impact of proof of work (PoW)-Based blockchain applications on the environment: A systematic review and research agenda. J. Risk Financ. Manag. 2023, 16, 218. [Google Scholar] [CrossRef]
- Karpinski, M.; Kovalchuk, L.; Kochan, R.; Oliynykov, R.; Rodinko, M.; Wieclaw, L. Blockchain Technologies: Probability of Double-Spend Attack on a Proof-of-Stake Consensus. Sensors 2021, 21, 6408. [Google Scholar] [CrossRef] [PubMed]
- Bentov, I.; Lee, C.; Mizrahi, A.; Rosenfeld, M. Proof of activity: Extending bitcoin’s proof of work via proof of stake [extended abstract] y. ACM SIGMETRICS Perform. Eval. Rev. 2014, 42, 34–37. [Google Scholar] [CrossRef]
- Park, S.; Kwon, A.; Fuchsbauer, G.; Gaži, P.; Alwen, J.; Pietrzak, K. Spacemint: A cryptocurrency based on proofs of space. In Proceedings of the Financial Cryptography and Data Security: 22nd International Conference, FC 2018, Nieuwpoort, Curaçao, 26 February–2 March 2018; pp. 480–499. [Google Scholar]
- Karantias, K.; Kiayias, A.; Zindros, D. Proof-of-burn. In Proceedings of the Financial Cryptography and Data Security: 24th International Conference, FC, Kota Kinabalu, Malaysia, 10–14 February 2020; pp. 523–540. [Google Scholar]
- Manolache, M.A.; Manolache, S.; Tapus, N. Decision making using the blockchain proof of authority consensus. Procedia Comput. Sci. 2022, 199, 580–588. [Google Scholar] [CrossRef]
- Chen, L.; Xu, L.; Shah, N.; Gao, Z.; Lu, Y.; Shi, W. On security analysis of proof-of-elapsed-time (poet). In Proceedings of the Stabilization, Safety, and Security of Distributed Systems: 19th International Symposium, SSS 2017, Boston, MA, USA, 5–8 November 2017; pp. 282–297. [Google Scholar]
- Feng, L.; Zhang, H.; Chen, Y.; Lou, L. Scalable dynamic multi-agent practical byzantine fault-tolerant consensus in permissioned blockchain. Appl. Sci. 2018, 8, 1919. [Google Scholar] [CrossRef]
- Ma, F.Q.; Li, Q.L.; Liu, Y.H.; Chang, Y.X. Stochastic performance modeling for practical byzantine fault tolerance consensus in the blockchain. Peer-to-Peer Netw. Appl. 2022, 15, 2516–2528. [Google Scholar] [CrossRef]
- Zhan, Y.; Wang, B.; Lu, R.; Yu, Y. DRBFT: Delegated randomization Byzantine fault tolerance consensus protocol for blockchains. Inf. Sci. 2021, 559, 8–21. [Google Scholar] [CrossRef]
- Huang, D.; Ma, X.; Zhang, S. Performance analysis of the raft consensus algorithm for private blockchains. IEEE Trans. Syst. Man Cybern. Syst. 2019, 50, 172–181. [Google Scholar] [CrossRef]
- Bachani, V.; Bhattacharjya, A. Preferential Delegated Proof of Stake (PDPoS)—Modified DPoS with Two Layers towards Scalability and Higher TPS. Symmetry 2022, 15, 4. [Google Scholar] [CrossRef]
- Saad, S.M.S.; Radzi, R.Z.R.M. Comparative review of the blockchain consensus algorithm between proof of stake (pos) and delegated proof of stake (dpos). Int. J. Innov. Comput. 2020, 10, 27–32. [Google Scholar] [CrossRef]
- Gao, W.; Hatcher, W.G.; Yu, W. A survey of blockchain: Techniques, applications, and challenges. In Proceedings of the 2018 27th International Conference on Computer Communication and Networks (ICCCN), Hangzhou, China, 30 July 2018–2 August 2018; pp. 1–11. [Google Scholar]
- Rahulamathavan, Y.; Phan, R.C.W.; Rajarajan, M.; Misra, S.; Kondoz, A. Privacy-preserving blockchain based IoT ecosystem using attribute-based encryption. In Proceedings of the 2017 IEEE International Conference on Advanced Networks and Telecommunications Systems (ANTS), Bhubaneswar, India, 17–20 December 2017; pp. 1–6. [Google Scholar]
- Deshpande, V.; Badis, H.; George, L. BTCmap: Mapping bitcoin peer-to-peer network topology. In Proceedings of the 2018 IFIP/IEEE International Conference on Performance Evaluation and Modeling in Wired and Wireless Networks (PEMWN), Toulouse, France, 26–28 September 2018; pp. 1–6. [Google Scholar]
- Gao, Y.; Shi, J.; Wang, X.; Tan, Q.; Zhao, C.; Yin, Z. Topology measurement and analysis on ethereum p2p network. In Proceedings of the 2019 IEEE Symposium on Computers and Communications (ISCC), Barcelona, Spain, 29 June–3 July 2019; pp. 1–7. [Google Scholar]
- Kumar, R.; Tripathi, R. Blockchain-based framework for data storage in peer-to-peer scheme using interplanetary file system. In Handbook of Research on Blockchain Technology; Academic Press: Cambridge, MA, USA, 2020; pp. 35–59. [Google Scholar]
- Zhu, Y.; Qin, Y.; Gan, G.; Shuai, Y.; Chu, W.C.C. TBAC: Transaction-based access control on blockchain for resource sharing with cryptographically decentralized authorization. In Proceedings of the 2018 IEEE 42nd Annual Computer Software and Applications Conference (COMPSAC), Tokyo, Japan, 23–27 July 2018; Volume 1, pp. 535–544. [Google Scholar]
- Hashemi Joo, M.; Nishikawa, Y.; Dandapani, K. Cryptocurrency, a successful application of blockchain technology. Manag. Financ. 2020, 46, 715–733. [Google Scholar] [CrossRef]
- Taherdoost, H. Smart Contracts in Blockchain Technology: A Critical Review. Information 2023, 14, 117. [Google Scholar] [CrossRef]
- Sultana, T.; Almogren, A.; Akbar, M.; Zuair, M.; Ullah, I.; Javaid, N. Data sharing system integrating access control mechanism using blockchain-based smart contracts for IoT devices. Appl. Sci. 2020, 10, 488. [Google Scholar] [CrossRef]
- Krichen, M.; Lahami, M.; Al–Haija, Q.A. Formal methods for the verification of smart contracts: A review. In Proceedings of the 2022 15th International Conference on Security of Information and Networks (SIN), Sousse, Tunisia, 11–13 November 2022; pp. 1–8. [Google Scholar]
- Abdellatif, T.; Brousmiche, K.L. Formal verification of smart contracts based on users and blockchain behaviors models. In Proceedings of the 2018 9th IFIP International Conference on New Technologies, Mobility and Security (NTMS), Paris, France, 26–28 February 2018; pp. 1–5. [Google Scholar]
- Litke, A.; Anagnostopoulos, D.; Varvarigou, T. Blockchains for supply chain management: Architectural elements and challenges towards a global scale deployment. Logistics 2019, 3, 5. [Google Scholar] [CrossRef]
- Bamakan, S.M.H.; Moghaddam, S.G.; Manshadi, S.D. Blockchain-enabled pharmaceutical cold chain: Applications, key challenges, and future trends. J. Clean. Prod. 2021, 302, 127021. [Google Scholar] [CrossRef]
- Srivastava, P.R.; Zhang, J.Z.; Eachempati, P. Blockchain technology and its applications in agriculture and supply chain management: A retrospective overview and analysis. Enterp. Inf. Syst. 2023, 17, 1995783. [Google Scholar] [CrossRef]
- Yuan, M.; Xu, Y.; Zhang, C.; Tan, Y.; Wang, Y.; Ren, J.; Zhang, Y. TRUCON: Blockchain-Based Trusted Data Sharing With Congestion Control in Internet of Vehicles. IEEE Trans. Intell. Transp. Syst. 2022, 24, 3489–3500. [Google Scholar] [CrossRef]
- Alphand, O.; Amoretti, M.; Claeys, T.; Dall’Asta, S.; Duda, A.; Ferrari, G.; Rousseau, F.; Tourancheau, B.; Veltri, L.; Zanichelli, F. IoTChain: A blockchain security architecture for the Internet of Things. In Proceedings of the 2018 IEEE Wireless Communications and Networking Conference (WCNC), Barcelona, Spain, 15–18 April 2018; pp. 1–6. [Google Scholar]
- Keshavarz, M.; Gharib, M.; Afghah, F.; Ashdown, J.D. UASTrustChain: A decentralized blockchain-based trust monitoring framework for autonomous unmanned aerial systems. IEEE Access 2020, 8, 226074–226088. [Google Scholar] [CrossRef]
- Tsang, Y.P.; Wu, C.H.; Ip, W.H.; Shiau, W.L. Exploring the intellectual cores of the blockchain–Internet of Things (BIoT). J. Enterp. Inf. Manag. 2021, 34, 1287–1317. [Google Scholar] [CrossRef]
- Sahoo, M.; Singhar, S.S.; Sahoo, S.S. A blockchain based model to eliminate drug counterfeiting. In Proceedings of the Machine Learning and Information Processing: Proceedings of ICMLIP 2019, Pune, India, 27–28 December 2019; pp. 213–222.
- Fan, K.; Wang, S.; Ren, Y.; Li, H.; Yang, Y. Medblock: Efficient and secure medical data sharing via blockchain. J. Med. Syst. 2018, 42, 136. [Google Scholar] [CrossRef] [PubMed]
- Xia, Q.I.; Sifah, E.B.; Asamoah, K.O.; Gao, J.; Du, X.; Guizani, M. MeDShare: Trust-less medical data sharing among cloud service providers via blockchain. IEEE Access 2017, 5, 14757–14767. [Google Scholar] [CrossRef]
- Bhamidipati, N.R.; Vakkavanthula, V.; Stafford, G.; Dahir, M.; Neupane, R.; Bonnah, E.; Wang, S.; Murthy, J.V.R.; Hoque, K.A.; Calyam, P. Claimchain: Secure blockchain platform for handling insurance claims processing. In Proceedings of the 2021 IEEE International Conference on Blockchain (Blockchain), Melbourne, Australia, 6–8 December 2021; pp. 55–64. [Google Scholar]
- Roriz, R.; Pereira, J.L. Avoiding insurance fraud: A blockchain-based solution for the vehicle sector. Procedia Comput. Sci. 2019, 164, 211–218. [Google Scholar] [CrossRef]
- Johnson, O. Decentralized Reinsurance: Funding blockchain-based parametric bushfire insurance. In Proceedings of the 2022 IEEE International Conference on Blockchain and Cryptocurrency (ICBC), virtual event, 2–5 May 2022; pp. 1–3. [Google Scholar]
- Yang, Y.; Guan, Z.; Wan, Z.; Weng, J.; Pang, H.H.; Deng, R.H. Priscore: Blockchain-based self-tallying election system supporting score voting. IEEE Trans. Inf. Forensics Secur. 2021, 16, 4705–4720. [Google Scholar] [CrossRef]
- Pawlak, M.; Guziur, J.; Poniszewska-Marańda, A. Voting process with blockchain technology: Auditable blockchain voting system. In Proceedings of the Advances in Intelligent Networking and Collaborative Systems: The 10th International Conference on Intelligent Networking and Collaborative Systems (INCoS-2018), Bratislava, Slovakia, 5–7 September 2018; pp. 233–244. [Google Scholar]
- Song, H.; Zhu, N.; Xue, R.; He, J.; Zhang, K.; Wang, J. Proof-of-Contribution consensus mechanism for blockchain and its application in intellectual property protection. Inf. Process. Manag. 2021, 58, 102507. [Google Scholar] [CrossRef]
- Rambhia, V.; Mehta, V.; Mehta, R.; Shah, R.; Patel, D. Intellectual Property Rights Management Using Blockchain. In Proceedings of the Information and Communication Technology for Competitive Strategies (ICTCS 2020): Intelligent Strategies for ICT, Jaipur, India, 11–12 December 2020; pp. 545–552. [Google Scholar]
- Li, Z.; Barenji, A.V.; Huang, G.Q. Toward a blockchain cloud manufacturing system as a peer to peer distributed network platform. Robot. Comput. Integr. Manuf. 2018, 54, 133–144. [Google Scholar] [CrossRef]
- Yu, K.; Tan, L.; Aloqaily, M.; Yang, H.; Jararweh, Y. Blockchain-enhanced data sharing with traceable and direct revocation in IIoT. IEEE Trans. Ind. Inform. 2021, 17, 7669–7678. [Google Scholar] [CrossRef]
- Xu, J.J. Are blockchains immune to all malicious attacks? Financ. Innov. 2016, 2, 1–9. [Google Scholar] [CrossRef]
- Ramachandran, G.S.; Wright, K.L.; Zheng, L.; Navaney, P.; Naveed, M.; Krishnamachari, B.; Dhaliwal, J. Trinity: A byzantine fault-tolerant distributed publish-subscribe system with immutable blockchain-based persistence. In Proceedings of the 2019 IEEE International Conference on Blockchain and Cryptocurrency (ICBC), Seoul, Republic of Korea, 14–17 May 2019; pp. 227–235. [Google Scholar]
- Kanza, Y.; Safra, E. Cryptotransport: Blockchain-powered ride hailing while preserving privacy, pseudonymity and trust. In Proceedings of the 26th ACM SIGSPATIAL International Conference on Advances in Geographic Information Systems, Seattle, WA, USA, 6–9 November 2018; pp. 540–543. [Google Scholar]
- Aggarwal, S.; Kumar, N. Attacks on blockchain. In Advances in Computers; Elsevier: Amsterdam, The Netherlands, 2021; Volume 121, pp. 399–410. [Google Scholar]
- Coppolino, L.; D’Antonio, S.; Mazzeo, G.; Romano, L.; Campegiani, P. Facing the Blockchain Endpoint Vulnerability, an SGX-based Solution for Secure eHealth Auditing. In Proceedings of the ITASEC, virtual event, 7–9 April 2021; pp. 298–308. [Google Scholar]
- Jang, J.; Lee, H.N. Profitable double-spending attacks. Appl. Sci. 2020, 10, 8477. [Google Scholar] [CrossRef]
- Bai, Q.; Zhou, X.; Wang, X.; Xu, Y.; Wang, X.; Kong, Q. A deep dive into blockchain selfish mining. In Proceedings of the ICC 2019—2019 IEEE International Conference on Communications (ICC), Shanghai, China, 20–24 May 2019; pp. 1–6. [Google Scholar]
- Poston, H. Mapping the OWASP top ten to blockchain. Procedia Comput. Sci. 2020, 177, 613–617. [Google Scholar] [CrossRef]
- Juels, A.; Kosba, A.; Shi, E. The ring of gyges: Investigating the future of criminal smart contracts. In Proceedings of the 2016 ACM SIGSAC Conference on Computer and Communications Security, New York, NY, USA, 24–28 October 2016; pp. 283–295. [Google Scholar]
- Ruf, P.; Stodt, J.; Reich, C. Security threats of a blockchain-based platform for industry ecosystems in the cloud. In Proceedings of the 2021 Fifth World Conference on Smart Trends in Systems Security and Sustainability (WorldS4), London, UK, 29–30 July 2021; pp. 192–199. [Google Scholar]
- Pahlajani, S.; Kshirsagar, A.; Pachghare, V. Survey on private blockchain consensus algorithms. In Proceedings of the 2019 1st International Conference on Innovations in Information and Communication Technology (ICIICT), Chennai, India, 25–26 April 2019; pp. 1–6. [Google Scholar]
- Ferdous, M.S.; Chowdhury, M.J.M.; Hoque, M.A. A survey of consensus algorithms in public blockchain systems for crypto-currencies. J. Netw. Comput. Appl. 2021, 182, 103035. [Google Scholar] [CrossRef]
- Jidong, L.; Xueqiang, L.; Yang, J.; Guolin, L. Consensus Mechanisms of Consortium Blockchain: A Survey. Data Anal. Knowl. Discov. 2021, 5, 56–65. [Google Scholar]
- Herath, H.M.D.P.M.; Weraniyagoda, W.A.S.A.; Rajapaksha, R.T.M.; Wijesekara, P.A.D.S.N.; Sudheera, K.L.K.; Chong, P.H.J. Automatic Assessment of Aphasic Speech Sensed by Audio Sensors for Classification into Aphasia Severity Levels to Recommend Speech Therapies. Sensors 2022, 22, 6966. [Google Scholar] [CrossRef]
- Wijesekara, P.A.D.S.N. Deep 3D Dynamic Object Detection towards Successful and Safe Navigation for Full Autonomous Driving. Open Transp. J. 2022, 16, e187444782208191. [Google Scholar] [CrossRef]
- Zins, C. Conceptual approaches for defining data, information, and knowledge. J. Am. Soc. Inf. Sci. Technol. 2007, 58, 479–493. [Google Scholar] [CrossRef]
- Sieber, C.; Blenk, A.; Basta, A.; Hock, D.; Kellerer, W. Towards a programmable management plane for SDN and legacy networks. In Proceedings of the 2016 IEEE NetSoft Conference and Workshops (NetSoft), Seoul, Republic of Korea, 6–10 June 2016; pp. 319–327. [Google Scholar]
- Sezer, S.; Scott-Hayward, S.; Chouhan, P.K.; Fraser, B.; Lake, D.; Finnegan, J.; Viljoen, N.; Miller, M.; Rao, N. Are we ready for SDN? Implementation challenges for software-defined networks. IEEE Commun. Mag. 2013, 51, 36–43. [Google Scholar] [CrossRef]
- da Costa Cordeiro, W.L.; Marques, J.A.; Gaspary, L.P. Data plane programmability beyond openflow: Opportunities and challenges for network and service operations and management. J. Netw. Syst. Manag. 2017, 25, 784–818. [Google Scholar] [CrossRef]
- Li, T.; Chen, J.; Fu, H. Application scenarios based on SDN: An overview. J. Phys. Conf. Ser. 2019, 1187, 052067. [Google Scholar] [CrossRef]
- Trammell, B.; Casas, P.; Rossi, D.; Bär, A.; Houidi, Z.B.; Leontiadis, I.; Szemethy, T.; Mellia, M. mPlane: An intelligent measurement plane for the internet. IEEE Commun. Mag. 2014, 52, 148–156. [Google Scholar] [CrossRef]
- David, L.; Keeney, J.; O’Sullivan, D.; Guo, S. Towards a managed extensible control plane for knowledge-based networking. In Proceedings of the Large Scale Management of Distributed Systems: 17th IFIP/IEEE International Workshop on Distributed Systems: Operations and Management, DSOM, Dublin, Ireland, 23–25 October 2006; pp. 98–111. [Google Scholar]
- Jevsikova, T.; Berniukevičius, A.; Kurilovas, E. Application of resource description framework to personalise learning: Systematic review and methodology. Inform. Educ. 2017, 16, 61–82. [Google Scholar] [CrossRef]
- Wijesekara, P.A.D.S.N.; Wang, Y.K. A Mathematical Epidemiological Model (SEQIJRDS) to Recommend Public Health Interventions Related to COVID-19 in Sri Lanka. COVID 2022, 2, 793–826. [Google Scholar] [CrossRef]
- Wijesekara, P.A.D.S.N. A study in University of Ruhuna for investigating prevalence, risk factors and remedies for psychiatric illnesses among students. Sci. Rep. 2022, 12, 12763. [Google Scholar] [CrossRef]
- Seneviratne, C.; Wijesekara, P.A.D.S.N.; Leung, H. Performance analysis of distributed estimation for data fusion using a statistical approach in smart grid noisy wireless sensor networks. Sensors 2020, 20, 567. [Google Scholar] [CrossRef] [PubMed]
- Tudorache, T.; Nyulas, C.; Noy, N.F.; Musen, M.A. WebProtégé: A collaborative ontology editor and knowledge acquisition tool for the web. Semant. Web 2013, 4, 89–99. [Google Scholar] [CrossRef]
- Hayes, P.; Menzel, C. A semantics for the knowledge interchange format. In Proceedings of the IJCAI 2001 Workshop on the IEEE Standard Upper Ontology, Seattle, WA, USA, 4–6 August 2001; Volume 145, p. 145. [Google Scholar]
- Fensel, D.; Van Harmelen, F.; Horrocks, I.; McGuinness, D.L.; Patel-Schneider, P.F. OIL: An ontology infrastructure for the semantic web. IEEE Intell. Syst. 2001, 16, 38–45. [Google Scholar] [CrossRef]
- McBride, B. The resource description framework (RDF) and its vocabulary description language RDFS. In Handbook on Ontologies; Springer: Berlin/Heidelberg, Germany, 2004; pp. 51–65. [Google Scholar]
- Antoniou, G.; Harmelen, F.V. Web ontology language: Owl. In Handbook on Ontologies; Springer: Berlin/Heidelberg, Germany, 2009; pp. 91–110. [Google Scholar]
- Jarvis, M.P.; Goss, N.-J.; Neil, T.H. Applying machine learning techniques to rule generation in intelligent tutoring systems. In Proceedings of the Intelligent Tutoring Systems: 7th International Conference, ITS 2004, Maceió, Alagoas, Brazil, 30 August–3 September 2004; pp. 541–553. [Google Scholar]
- Boley, H.; Tabet, S.; Wagner, G. Design rationale for RuleML: A markup language for semantic web rules. In Proceedings of the SWWS, Stanford, CA, USA, 30 July–1 August 2001; Volume 1, pp. 381–401. [Google Scholar]
- Kifer, M. Rule interchange format: The framework. In Proceedings of the Web Reasoning and Rule Systems: Second International Conference, RR 2008, Karlsruhe, Germany, 31 October–1 November 2008; pp. 1–11. [Google Scholar]
- Horrocks, I.; Patel-Schneider, P.F.; Boley, H.; Tabet, S.; Grosof, B.; Dean, M. SWRL: A semantic web rule language combining OWL and RuleML. W3C Memb. Submiss. 2004, 21, 1–31. [Google Scholar]
- Liu, D.; Gu, T.; Xue, J.P. Rule engine based on improvement rete algorithm. In Proceedings of the 2010 International Conference on Apperceiving Computing and Intelligence Analysis Proceeding, Chengdu, China, 17–19 December 2010; pp. 346–349. [Google Scholar]
- Jang, M.; Sohn, J.C. Bossam: An extended rule engine for OWL inferencing. In Rules and Rule Markup Languages for the Semantic Web: Third International Workshop, RuleML 2004, Hiroshima, Japan, 8 November 2004; Proceedings 3; Springer: Berlin/Heidelberg, Germany, 2004; pp. 128–138. [Google Scholar]
- Friedman-Hill, E. Jess, the rule engine for the java platform. Available online: http://alvarestech.com/temp/fuzzyjess/Jess60/Jess70b7/docs/index.html (accessed on 6 June 2023).
- Proctor, M. Drools: A rule engine for complex event processing. In Applications of Graph Transformations with Industrial Relevance: 4th International Symposium, AGTIVE 2011, Budapest, Hungary, 4–7 October 2011; Revised Selected and Invited Papers 4; Springer: Berlin/Heidelberg, Germany, 2011; p. 2. [Google Scholar]
- Barbieri, D.F.; Braga, D.; Ceri, S.; VALLE, E.D.; Grossniklaus, M. C-SPARQL: A continuous query language for RDF data streams. Int. J. Semant. Comput. 2010, 4, 3–25. [Google Scholar] [CrossRef]
- Taelman, R.; Vander Sande, M.; Verborgh, R. GraphQL-LD: Linked data querying with GraphQL. In Proceedings of the ISWC2018, 17th International Semantic Web Conference, Monterey, CA, USA, 8–12 October 2018; pp. 1–4. [Google Scholar]
- O’Connor, M.J.; Das, A.K. SQWRL: A query language for OWL. In Proceedings of the OWLED, Chantilly, VA, USA, 23–24 October 2009; Volume 529, pp. 1–8. [Google Scholar]
- Liu, P.; Wang, X.; Fu, Q.; Yang, Y.; Li, Y.F.; Zhang, Q. KGVQL: A knowledge graph visual query language with bidirectional transformations. Knowl.-Based Syst. 2022, 250, 108870. [Google Scholar] [CrossRef]
- Finin, T.; McKay, D.P.; Fritzson, R.; McEntire, R. KQML: An information and knowledge exchange protocol. In Knowledge Building and Knowledge Sharing; IOS Press: Amsterdam, The Netherlands, 1994. [Google Scholar]
- Sieber, C.; Blenk, A.; Hock, D.; Scheib, M.; Höhn, T.; Köhler, S.; Kellerer, W. Network configuration with quality of service abstractions for SDN and legacy networks. In Proceedings of the 2015 IFIP/IEEE International Symposium on Integrated Network Management (IM), Ottawa, ON, Canada, 11–15 May 2015; pp. 1135–1136. [Google Scholar]
- Narisetty, R.; Dane, L.; Malishevskiy, A.; Gurkan, D.; Bailey, S.; Narayan, S.; Mysore, S. OpenFlow configuration protocol: Implementation for the of management plane. In Proceedings of the 2013 Second GENI Research and Educational Experiment Workshop, Salt Lake, UT, USA, 20–22 March 2013; pp. 66–67. [Google Scholar]
- Safrianti, E.; Sari, L.O.; Sari, N.A. Real-Time Network Device Monitoring System with Simple Network Management Protocol (SNMP) Model. In Proceedings of the 2021 3rd International Conference on Research and Academic Community Services (ICRACOS), Surabaya, Indonesia, 9–10 October 2021; pp. 122–127. [Google Scholar]
- Ballani, H.; Francis, P. Conman: A step towards network manageability. ACM SIGCOMM Comput. Commun. Rev. 2007, 37, 205–216. [Google Scholar] [CrossRef]
- Chen, X.; Mao, Z.M.; Van der Merwe, J. PACMAN: A platform for automated and controlled network operations and configuration management. In Proceedings of the 5th International Conference on Emerging Networking Experiments and Technologies, Rome, Italy, 1–4 December 2009; pp. 277–288. [Google Scholar]
- Chowdhury, S.R.; Bari, M.F.; Ahmed, R.; Boutaba, R. Payless: A low cost network monitoring framework for software defined networks. In Proceedings of the 2014 IEEE Network Operations and Management Symposium (NOMS), Krakow, Poland, 5–9 May 2014; pp. 1–9. [Google Scholar]
- Sun, P.; Yu, M.; Freedman, M.J.; Rexford, J.; Walker, D. Hone: Joint host-network traffic management in software-defined networks. J. Netw. Syst. Manag. 2015, 23, 374–399. [Google Scholar] [CrossRef]
- Van Adrichem, N.L.; Doerr, C.; Kuipers, F.A. Opennetmon: Network monitoring in openflow software-defined networks. In Proceedings of the 2014 IEEE Network Operations and Management Symposium (NOMS), Krakow, Poland, 5–9 May 2014; pp. 1–8. [Google Scholar]
- Suh, J.; Kwon, T.T.; Dixon, C.; Felter, W.; Carter, J. Opensample: A low-latency, sampling-based measurement platform for commodity sdn. In Proceedings of the 2014 IEEE 34th International Conference on Distributed Computing Systems, Madrid, Spain, 30 June–3 July 2014; pp. 228–237. [Google Scholar]
- Wijesekara, P.A.D.S.N.; Sudheera, K.L.K.; Sandamali, G.G.N.; Chong, P.H.J. An Optimization Framework for Data Collection in Software Defined Vehicular Networks. Sensors 2023, 23, 1600. [Google Scholar] [CrossRef] [PubMed]
- Wette, P.; Karl, H. Which flows are hiding behind my wildcard rule? adding packet sampling to OpenFlow. In Proceedings of the ACM SIGCOMM 2013 Conference on SIGCOMM, Hong Kong, China, 12–16 August 2013; pp. 541–542. [Google Scholar]
- Zhou, D.; Yan, Z.; Liu, G.; Atiquzzaman, M. An adaptive network data collection system in sdn. IEEE Trans. Cogn. Commun. Netw. 2019, 6, 562–574. [Google Scholar] [CrossRef]
- Liao, W.H.; Kuai, S.C. An energy-efficient sdn-based data collection strategy for wireless sensor networks. In Proceedings of the 2017 IEEE 7th International Symposium on Cloud and Service Computing (SC2), Kanazawa, Japan, 22–25 November 2017; pp. 91–97. [Google Scholar]
- Bjorklund, M. YANG-a data modeling language for the network configuration protocol (NETCONF). Available online: https://www.rfc-editor.org/rfc/rfc6020 (accessed on 5 June 2023).
- Uslar, M.; Specht, M.; Rohjans, S.; Trefke, J.; González, J.M. The Common Information Model CIM: IEC 61968/61970 and 62325-A Practical Introduction to the CIM; Springer Science & Business Media: Berlin/Heidelberg, Germany, 2012. [Google Scholar]
- Atutxa, A.; Franco, D.; Sasiain, J.; Astorga, J.; Jacob, E. Achieving low latency communications in smart industrial networks with programmable data planes. Sensors 2021, 21, 5199. [Google Scholar] [CrossRef] [PubMed]
- Wijesekara, P.A.D.S.N.; Sangeeth, W.M.A.K.; Perera, H.S.C.; Jayasundere, N.D. Underwater Acoustic Digital Communication Channel for an UROV. In Proceedings of the 5th Annual Research Symposium (ARS2018), Hapugala, Sri Lanka, 4 January 2018; p. E17. [Google Scholar]
- Paliwal, M.; Shrimankar, D.; Tembhurne, O. Controllers in SDN: A review report. IEEE Access 2018, 6, 36256–36270. [Google Scholar] [CrossRef]
- Haleplidis, E.; Salim, J.H.; Halpern, J.M.; Hares, S.; Pentikousis, K.; Ogawa, K.; Wang, W.; Denazis, S.; Koufopavlou, O. Network programmability with ForCES. IEEE Commun. Surv. Tutor. 2015, 17, 1423–1440. [Google Scholar] [CrossRef]
- Shalimov, A.; Zuikov, D.; Zimarina, D.; Pashkov, V.; Smeliansky, R. Advanced study of SDN/OpenFlow controllers. In Proceedings of the 9th Central & Eastern European Software Engineering Conference in Russia, Moscow, Russia, 24–25 October 2013; pp. 1–6. [Google Scholar]
- Li, S.; Hu, D.; Fang, W.; Ma, S.; Chen, C.; Huang, H.; Zhu, Z. Protocol oblivious forwarding (POF): Software-defined networking with enhanced programmability. IEEE Netw. 2017, 31, 58–66. [Google Scholar] [CrossRef]
- Eadala, S.Y.; Nagarajan, V. A review on deployment architectures of path computation element using software defined networking paradigm. Indian J. Sci. Technol. 2016, 9, 1–10. [Google Scholar] [CrossRef]
- Bianchi, G.; Bonola, M.; Capone, A.; Cascone, C. Openstate: Programming platform-independent stateful openflow applications inside the switch. ACM SIGCOMM Comput. Commun. Rev. 2014, 44, 44–51. [Google Scholar] [CrossRef]
- Ijari, P. Comparison between Cisco ACI and VMWARE NSX. IOSR J. Comput. Eng. (IOSR-JCE) 2017, 19, 70–72. [Google Scholar] [CrossRef]
- Hasan, K.; Ahmed, K.; Biswas, K.; Islam, M.S.; Kayes, A.S.M.; Islam, S.R. Control plane optimisation for an SDN-based WBAN framework to support healthcare applications. Sensors 2020, 20, 4200. [Google Scholar] [CrossRef] [PubMed]
- Gude, N.; Koponen, T.; Pettit, J.; Pfaff, B.; Casado, M.; McKeown, N.; Shenker, S. NOX: Towards an operating system for networks. ACM SIGCOMM Comput. Commun. Rev. 2008, 38, 105–110. [Google Scholar] [CrossRef]
- Rowshanrad, S.; Abdi, V.; Keshtgari, M. Performance evaluation of SDN controllers: Floodlight and OpenDaylight. IIUM Eng. J. 2016, 17, 47–57. [Google Scholar] [CrossRef]
- Sanvito, D.; Moro, D.; Gulli, M.; Filippini, I.; Capone, A.; Campanella, A. ONOS Intent Monitor and Reroute service: Enabling plug&play routing logic. In Proceedings of the 2018 4th IEEE Conference on Network Softwarization and Workshops (NetSoft), Montreal, QC, Canada, 25–29 June 2018; pp. 272–276. [Google Scholar]
- Voellmy, A.; Kim, H.; Feamster, N. Procera: A language for high-level reactive network control. In Proceedings of the First Workshop on Hot Topics in Software Defined Networks, Helsinki, Finland, 13 August 2012; pp. 43–48. [Google Scholar]
- Rotsos, C.; King, D.; Farshad, A.; Bird, J.; Fawcett, L.; Georgalas, N.; Gunkel, M.; Shiomoto, K.; Wang, A.; Mauthe, A.; et al. Network service orchestration standardization: A technology survey. Comput. Stand. Interfaces 2017, 54, 203–215. [Google Scholar] [CrossRef]
- Bannour, F.; Souihi, S.; Mellouk, A. Distributed SDN control: Survey, taxonomy, and challenges. IEEE Commun. Surv. Tutor. 2017, 20, 333–354. [Google Scholar] [CrossRef]
- Koponen, T.; Casado, M.; Gude, N.; Stribling, J.; Poutievski, L.; Zhu, M.; Ramanathan, R.; Iwata, Y.; Inoue, H.; Hama, T.; et al. Onix: A distributed control platform for large-scale production networks. In Proceedings of the OSDI, Vancouver, BC, Canada, 4–6 October 2010; Volume 10, p. 6. [Google Scholar]
- Vahlenkamp, M.; Schneider, F.; Kutscher, D.; Seedorf, J. Enabling information centric networking in IP networks using SDN. In Proceedings of the 2013 IEEE SDN for Future Networks and Services (SDN4FNS), Trento, Italy, 11–13 November 2013; pp. 1–6. [Google Scholar]
- Sheikh, M.N.A.; Halder, M. SDN-Based approach to evaluate the best controller: Internal controller NOX and external controllers POX, ONOS, RYU. Glob. J. Comput. Sci. Technol. 2019, 19, 21–32. [Google Scholar] [CrossRef]
- Banikazemi, M.; Olshefski, D.; Shaikh, A.; Tracey, J.; Wang, G. Meridian: An SDN platform for cloud network services. IEEE Commun. Mag. 2013, 51, 120–127. [Google Scholar] [CrossRef]
- Botelho, F.; Bessani, A.; Ramos, F.M.; Ferreira, P. On the design of practical fault-tolerant SDN controllers. In Proceedings of the 2014 Third EUROPEAN Workshop on Software Defined Networks, Budapest, Hungary, 1–3 September 2014; pp. 73–78. [Google Scholar]
- Hassas Yeganeh, S.; Ganjali, Y. Kandoo: A framework for efficient and scalable offloading of control applications. In Proceedings of the First Workshop on Hot Topics in Software Defined Networks, Helsinki, Finland, 13 August 2012; pp. 19–24. [Google Scholar]
- Fu, Y.; Bi, J.; Gao, K.; Chen, Z.; Wu, J.; Hao, B. Orion: A hybrid hierarchical control plane of software-defined networking for large-scale networks. In Proceedings of the 2014 IEEE 22nd International Conference on Network Protocols, Raleigh, NC, USA, 21–24 October 2014; pp. 569–576. [Google Scholar]
- Curtis, A.R.; Mogul, J.C.; Tourrilhes, J.; Yalagandula, P.; Sharma, P.; Banerjee, S. DevoFlow: Scaling flow management for high-performance networks. In Proceedings of the ACM SIGCOMM 2011 Conference, Toronto, ON, Canada, 15–19 August 2011; pp. 254–265. [Google Scholar]
- Vissicchio, S.; Vanbever, L.; Rexford, J. Sweet little lies: Fake topologies for flexible routing. In Proceedings of the ACM Workshop on Hot Topics in Networks, Los Angeles, CA, USA, 27–28 October 2014; pp. 1–7. [Google Scholar]
- Huang, S.; Zhao, J.; Wang, X. HybridFlow: A lightweight control plane for hybrid SDN in enterprise networks. In Proceedings of the 2016 IEEE/ACM 24th International Symposium on Quality of Service (IWQoS), Beijing, China, 20–21 June 2016; pp. 1–2. [Google Scholar]
- Phemius, K.; Bouet, M.; Leguay, J. DISCO: Distributed SDN controllers in a multi-domain environment. In Proceedings of the 2014 IEEE Network Operations and Management Symposium (NOMS), Krakow, Poland, 5–9 May 2014; pp. 1–2. [Google Scholar]
- Santos, M.A.; Nunes, B.A.; Obraczka, K.; Turletti, T.; De Oliveira, B.T.; Margi, C.B. Decentralizing SDN’s control plane. In Proceedings of the 39th Annual IEEE Conference on Local Computer Networks, Edmonton, AB, Canada, 8–11 September 2014; pp. 402–405. [Google Scholar]
- Stringer, J.; Pemberton, D.; Fu, Q.; Lorier, C.; Nelson, R.; Bailey, J.; Corrêa, C.N.; Rothenberg, C.E. Cardigan: SDN distributed routing fabric going live at an Internet exchange. In Proceedings of the 2014 IEEE Symposium on Computers and Communications (ISCC), Funchal, Portugal, 23–26 June 2014; pp. 1–7. [Google Scholar]
- Zhu, M.; Cao, J.; Pang, D.; He, Z.; Xu, M. SDN-based routing for efficient message propagation in VANET. In Wireless Algorithms, Systems, and Applications: 10th International Conference 2015, WASA 2015, Qufu, China, 10–12 August 2015; Proceedings 10; Springer International Publishing: Cham, Switzerland, 2015; pp. 788–797. [Google Scholar]
- Moghaddam, F.F.; Wieder, P.; Yahyapour, R. Policy Engine as a Service (PEaaS): An approach to a reliable policy management framework in cloud computing environments. In Proceedings of the 2016 IEEE 4th International Conference on Future Internet of Things and Cloud (FiCloud), Vienna, Austria, 22–24 August 2016; pp. 137–144. [Google Scholar]
- Chen, Y.J.; Wang, L.C.; Lin, F.Y.; Lin, B.S.P. Deterministic quality of service guarantee for dynamic service chaining in software defined networking. IEEE Trans. Netw. Serv. Manag. 2017, 14, 991–1002. [Google Scholar] [CrossRef]
- Yang, G.; Jin, H.; Kang, M.; Moon, G.J.; Yoo, C. Network monitoring for SDN virtual networks. In Proceedings of the IEEE INFOCOM 2020-IEEE Conference on Computer Communications, virtual event, 6–9 July 2020; pp. 1261–1270. [Google Scholar]
- Ahvar, E.; Ahvar, S.; Raza, S.M.; Manuel Sanchez Vilchez, J.; Lee, G.M. Next generation of SDN in cloud-fog for 5G and beyond-enabled applications: Opportunities and challenges. Network 2021, 1, 28–49. [Google Scholar] [CrossRef]
- Voellmy, A.; Agarwal, A.; Hudak, P. Nettle: Functional Reactive Programming for Openflow Networks; Yale University Computer Science: New Haven, CT, USA, 2010. [Google Scholar]
- Foster, N.; Freedman, M.J.; Harrison, R.; Rexford, J.; Meola, M.L.; Walker, D. Frenetic: A high-level language for OpenFlow networks. In Proceedings of the Workshop on Programmable Routers for Extensible Services of Tomorrow, Philadelphia, PA, USA, 30 November 2010; pp. 1–6. [Google Scholar]
- Kim, H.; Reich, J.; Gupta, A.; Shahbaz, M.; Feamster, N.; Clark, R. Kinetic: Verifiable dynamic network control. In Proceedings of the 12th USENIX Symposium on Networked Systems Design and Implementation (NSDI 15), Oakland, CA, USA, 4–6 May 2015; pp. 59–72. [Google Scholar]
- Wijesekara, P.A.D.S.N.; Sudheera, K.L.K.; Sandamali, G.G.N.; Chong, P.H.J. Data Gathering Optimization in Hybrid Software Defined Vehicular Networks. In Proceedings of the 20th Academic Sessions, Matara, Sri Lanka, 7 June 2023; p. 59. [Google Scholar]
- Dibaei, M.; Zheng, X.; Xia, Y.; Xu, X.; Jolfaei, A.; Bashir, A.K.; Tariq, U.; Yu, D.; Vasilakos, A.V. Investigating the prospect of leveraging blockchain and machine learning to secure vehicular networks: A survey. IEEE Transactions on Intelligent Transportation Systems 2021, 23, 683–700. [Google Scholar] [CrossRef]
- Alam, T. Blockchain-Enabled Deep Reinforcement Learning Approach for Performance Optimization on the Internet of Things. Wirel. Pers. Commun. 2022, 126, 995–1011. [Google Scholar] [CrossRef]
- Saba, T.; Haseeb, K.; Rehman, A.; Jeon, G. Blockchain-Enabled Intelligent IoT Protocol for High-Performance and Secured Big Financial Data Transaction. IEEE Trans. Comput. Soc. Syst. 2023. [Google Scholar] [CrossRef]
- Dai, Y.; Xu, D.; Maharjan, S.; Chen, Z.; He, Q.; Zhang, Y. Blockchain and deep reinforcement learning empowered intelligent 5G beyond. IEEE Netw. 2019, 33, 10–17. [Google Scholar] [CrossRef]
- Guo, S.; Qi, Y.; Yu, P.; Xu, S.; Qi, F. When network operation meets blockchain: An artificial-intelligence-driven customization service for trusted virtual resources of IoT. IEEE Netw. 2020, 34, 46–53. [Google Scholar] [CrossRef]
- Hu, S.; Liang, Y.C.; Xiong, Z.; Niyato, D. Blockchain and artificial intelligence for dynamic resource sharing in 6G and beyond. IEEE Wirel. Commun. 2021, 28, 145–151. [Google Scholar] [CrossRef]
- Ayaz, F.; Sheng, Z.; Tian, D.; Nekovee, M.; Saeed, N. Blockchain-empowered AI for 6G-enabled Internet of Vehicles. Electronics 2022, 11, 3339. [Google Scholar] [CrossRef]
- Mohammed, A.; Nahom, H.; Tewodros, A.; Habtamu, Y.; Hayelom, G. Deep reinforcement learning for computation offloading and resource allocation in blockchain-based multi-UAV-enabled mobile edge computing. In Proceedings of the 2020 17th International Computer Conference on Wavelet Active Media Technology and Information Processing (ICCWAMTIP), Chengdu, China, 18–20 December 2020; pp. 295–299. [Google Scholar]
- Leng, J.; Yan, D.; Liu, Q.; Xu, K.; Zhao, J.L.; Shi, R.; Wei, L.; Zhang, D.; Chen, X. ManuChain: Combining permissioned blockchain with a holistic optimization model as bi-level intelligence for smart manufacturing. IEEE Trans. Syst. Man Cybern. Syst. 2019, 50, 182–192. [Google Scholar] [CrossRef]
- Chang, F.; Zhou, G.; Zhang, C.; Ding, K.; Cheng, W.; Chang, F. A maintenance decision-making oriented collaborative cross-organization knowledge sharing blockchain network for complex multi-component systems. J. Clean. Prod. 2021, 282, 124541. [Google Scholar] [CrossRef]
- Li, G.; Dong, M.; Yang, L.T.; Ota, K.; Wu, J.; Li, J. Preserving edge knowledge sharing among IoT services: A blockchain-based approach. IEEE Trans. Emerg. Top. Comput. Intell. 2020, 4, 653–665. [Google Scholar] [CrossRef]
- Chai, H.; Leng, S.; Chen, Y.; Zhang, K. A hierarchical blockchain-enabled federated learning algorithm for knowledge sharing in internet of vehicles. IEEE Trans. Intell. Transp. Syst. 2020, 22, 3975–3986. [Google Scholar] [CrossRef]
- Li, Z.; Liu, X.; Wang, W.M.; Vatankhah Barenji, A.; Huang, G.Q. CKshare: Secured cloud-based knowledge-sharing blockchain for injection mold redesign. Enterp. Inf. Syst. 2019, 13, 1–33. [Google Scholar] [CrossRef]
- Chai, H.; Leng, S.; Wu, F.; He, J. Secure and Efficient Blockchain-Based Knowledge Sharing for Intelligent Connected Vehicles. IEEE Trans. Intell. Transp. Syst. 2021, 23, 14620–14631. [Google Scholar] [CrossRef]
- Balasubramaniam, A.; Gul, M.J.J.; Menon, V.G.; Paul, A. Blockchain for intelligent transport system. IETE Tech. Rev. 2021, 38, 438–449. [Google Scholar] [CrossRef]
- Lu, Y.; Huang, X.; Dai, Y.; Maharjan, S.; Zhang, Y. Blockchain and federated learning for privacy-preserved data sharing in industrial IoT. IEEE Trans. Ind. Inform. 2019, 16, 4177–4186. [Google Scholar] [CrossRef]
- Feng, C.; Liu, B.; Yu, K.; Goudos, S.K.; Wan, S. Blockchain-empowered decentralized horizontal federated learning for 5G-enabled UAVs. IEEE Trans. Ind. Inform. 2021, 18, 3582–3592. [Google Scholar] [CrossRef]
- Kumar, R.; Kumar, P.; Tripathi, R.; Gupta, G.P.; Islam, A.N.; Shorfuzzaman, M. Permissioned blockchain and deep learning for secure and efficient data sharing in industrial healthcare systems. IEEE Trans. Ind. Inform. 2022, 18, 8065–8073. [Google Scholar] [CrossRef]
- Li, C.; Huang, Y.; Wu, Y.; Wang, X.; Tian, Y.; Wu, R.; Qu, F.; Wang, Z. Intelligent data sharing strategy supported by artificial intelligence and blockchain technology: Based on medical data. Ann. Oper. Res. 2023, 1–25. [Google Scholar] [CrossRef]
- Kumar, P.; Kumar, R.; Kumar, A.; Franklin, A.A.; Jolfaei, A. Blockchain and deep learning empowered secure data sharing framework for softwarized uavs. In Proceedings of the 2022 IEEE International Conference on Communications Workshops (ICC Workshops), Seoul, Republic of Korea, 16–20 May 2022; pp. 770–775. [Google Scholar]
- Su, X.; Ullah, I.; Wang, M.; Choi, C. Blockchain-based system and methods for sensitive data transactions. IEEE Consum. Electron. Mag. 2021. [Google Scholar] [CrossRef]
- Zhang, H.; Li, G.; Zhang, Y.; Gai, K.; Qiu, M. Blockchain-based privacy-preserving medical data sharing scheme using federated learning. In Proceedings of the Knowledge Science, Engineering and Management: 14th International Conference, KSEM 2021, Tokyo, Japan, 14–16 August 2021; pp. 634–646. [Google Scholar]
- Zhang, G.; Li, T.; Li, Y.; Hui, P.; Jin, D. Blockchain-based data sharing system for ai-powered network operations. J. Commun. Inf. Netw. 2018, 3, 1–8. [Google Scholar] [CrossRef]
- Anita, N.; Vijayalakshmi, M.; and Shalinie, S.M. A Lightweight Scalable and Secure Blockchain Based IoT Using Fuzzy Logic. Wirel. Pers. Commun. 2022, 125, 2129–2146. [Google Scholar] [CrossRef]
- Alam, I.; Kumar, S.; Kumar, M.; Kashyap, P.K. Blockchain Based Intelligent Incentive Enabled Information Sharing Scheme in Future Generation IoV Networks. Res. Squ. 2021, Preprint. [Google Scholar] [CrossRef]
- Zhou, S.; Huang, H.; Chen, W.; Zhou, P.; Zheng, Z.; Guo, S. Pirate: A blockchain-based secure framework of distributed machine learning in 5g networks. IEEE Netw. 2020, 34, 84–91. [Google Scholar] [CrossRef]
- Otoum, S.; Al Ridhawi, I.; Mouftah, H.T. Blockchain-supported federated learning for trustworthy vehicular networks. In Proceedings of the GLOBECOM 2020–2020 IEEE Global Communications Conference, Taipei, Taiwan, 7–11 December 2020; pp. 1–6. [Google Scholar]
- Rathore, S.; Pan, Y.; Park, J.H. BlockDeepNet: A blockchain-based secure deep learning for IoT network. Sustainability 2019, 11, 3974. [Google Scholar] [CrossRef]
- Singh, M.; Aujla, G.S.; Singh, A.; Kumar, N.; Garg, S. Deep-learning-based blockchain framework for secure software-defined industrial networks. IEEE Trans. Ind. Inform. 2020, 17, 606–616. [Google Scholar] [CrossRef]
- Arachchige, P.C.M.; Bertok, P.; Khalil, I.; Liu, D.; Camtepe, S.; Atiquzzaman, M. A trustworthy privacy preserving framework for machine learning in industrial IoT systems. IEEE Trans. Ind. Inform. 2020, 16, 6092–6102. [Google Scholar] [CrossRef]
- Ma, Z.; Yuan, X.; Liang, K.; Feng, J.; Zhu, L.; Zhang, D.; Yu, F.R. Blockchain-escorted distributed deep learning with collaborative model aggregation towards 6G networks. Future Gener. Comput. Syst. 2023, 141, 555–566. [Google Scholar] [CrossRef]
- Nassar, M.; Salah, K.; ur Rehman, M.H.; Svetinovic, D. Blockchain for explainable and trustworthy artificial intelligence. Wiley Interdiscip. Rev. Data Min. Knowl. Discov. 2020, 10, e1340. [Google Scholar] [CrossRef]
- Zeng, Z.; Zhang, X.; Xia, Z. Intelligent blockchain-based secure routing for multidomain SDN-enabled IoT networks. Wirel. Commun. Mob. Comput. 2022, 2022, 5693962. [Google Scholar] [CrossRef]
- Abbas, S.; Javaid, N.; Almogren, A.; Gulfam, S.M.; Ahmed, A.; Radwan, A. Securing genetic algorithm enabled SDN routing for blockchain based Internet of Things. IEEE Access 2021, 9, 139739–139754. [Google Scholar] [CrossRef]
- Yang, J.; He, S.; Xu, Y.; Chen, L.; Ren, J. A trusted routing scheme using blockchain and reinforcement learning for wireless sensor networks. Sensors 2019, 19, 970. [Google Scholar] [CrossRef]
- Guo, Y.; Wang, Y.; Qian, Q. Intelligent edge network routing architecture with blockchain for the IoT. China Commun. 2023. [Google Scholar] [CrossRef]
- Li, Z.; Su, W.; Xu, M.; Yu, R.; Niyato, D.; Xie, S. Compact Learning Model for Dynamic Off-Chain Routing in Blockchain-Based IoT. IEEE J. Sel. Areas Commun. 2022, 40, 3615–3630. [Google Scholar] [CrossRef]
- Mehbodniya, A.; Webber, J.L.; Rani, R.; Ahmad, S.S.; Wattar, I.; Ali, L.; Nuagah, S.J. Energy-aware routing protocol with fuzzy logic in industrial internet of things with blockchain technology. Wirel. Commun. Mob. Comput. 2022, 2022, 7665931. [Google Scholar] [CrossRef]
- Kim, H.Y.; Lee, J.H. A load balancing scheme based on deep learning in blockchain network. In Proceedings of the 2021 International Conference on Computational Science and Computational Intelligence (CSCI), Las Vegas, NV, USA, 15–17 December 2021; pp. 1821–1823. [Google Scholar]
- Tiba, K.; Parizi, R.M.; Zhang, Q.; Dehghantanha, A.; Karimipour, H.; Choo, K.K.R. Secure blockchain-based traffic load balancing using edge computing and reinforcement learning. In Blockchain Cybersecurity, Trust and Privacy; Springer: Berlin/Heidelberg, Germany, 2020; pp. 99–128. [Google Scholar]
- She, H.; Zhu, X.; Guo, Y.; Cao, H.; Garg, S.; Kaddoum, G. BCLB: Blockchain-based Controller Load Balance for Safe and Reliable Resource Optimization. In Proceedings of the 2022 IEEE Globecom Workshops (GC Wkshps), Rio de Janeiro, Brazil, 4–8 December 2022; pp. 668–673. [Google Scholar]
- Alouache, L.; Sylla, T.; Mendiboure, L.; Aniss, H. A Fuzzy approach for load balancing in Blockchain-based Software Defined Vehicular Networks. In Proceedings of the 2022 18th International Conference on Wireless and Mobile Computing, Networking and Communications (WiMob), Thessaloniki, Greece, 10–12 October 2022; pp. 235–242. [Google Scholar]
- Islam, S.; Badsha, S.; Sengupta, S.; La, H.; Khalil, I.; Atiquzzaman, M. Blockchain-enabled intelligent vehicular edge computing. IEEE Netw. 2021, 35, 125–131. [Google Scholar] [CrossRef]
- Al-Jawad, A.; Comşa, I.S.; Shah, P.; Gemikonakli, O.; Trestian, R. An innovative reinforcement learning-based framework for quality of service provisioning over multimedia-based sdn environments. IEEE Trans. Broadcast. 2021, 67, 851–867. [Google Scholar] [CrossRef]
- Choudhary, S.; Dorle, S. A quality of service-aware high-security architecture design for software-defined network powered vehicular ad-hoc network s using machine learning-based blockchain routing. Concurr. Comput. Pract. Exp. 2022, 34, e6993. [Google Scholar] [CrossRef]
- Agrawal, S.; Kumar, S. MLSMBQS: Design of a machine learning based split & merge blockchain model for QoS-aware secure IoT deployments. Int. J. Image Graph. Signal Process 2022, 14, 58–71. [Google Scholar]
- Vairagade, R.S.; SH, B. Enabling machine learning-based side-chaining for improving QoS in blockchain-powered IoT networks. Trans. Emerg. Telecommun. Technol. 2022, 33, e4433. [Google Scholar] [CrossRef]
- Lanjewar, A.; Kumar, S.; Malik, L. ATQMB: Design of an augmented trust enabled QoS aware MAC model with intelligent blockchain sharding. In Proceedings of the 2022 10th International Conference on Emerging Trends in Engineering and Technology-Signal and Information Processing (ICETET-SIP-22), Nagpur, India, 29–30 April 2022; pp. 1–6. [Google Scholar]
- Khan, A.A.; Shaikh, Z.A.; Baitenova, L.; Mutaliyeva, L.; Moiseev, N.; Mikhaylov, A.; Laghari, A.A.; Idris, S.A.; Alshazly, H. QoS-ledger: Smart contracts and metaheuristic for secure quality-of-service and cost-efficient scheduling of medical-data processing. Electronics 2021, 10, 3083. [Google Scholar] [CrossRef]
- Maksymyuk, T.; Gazda, J.; Han, L.; Jo, M. Blockchain-based intelligent network management for 5G and beyond. In Proceedings of the 2019 3rd International Conference on Advanced Information and Communications Technologies (AICT), Lviv, Ukraine, 2–6 July 2019; pp. 36–39. [Google Scholar]
- Seid, A.M.; Erbad, A.; Abishu, H.N.; Albaseer, A.; Abdallah, M.; Guizani, M. Blockchain-Empowered Resource Allocation in Multi-UAV-Enabled 5G-RAN: A Multi-agent Deep Reinforcement Learning Approach. IEEE Trans. Cogn. Commun. Netw. 2023, 9, 991–1011. [Google Scholar] [CrossRef]
- Zhang, H.; Wang, R.; Sun, W.; Zhao, H. Mobility management for blockchain-based ultra-dense edge computing: A deep reinforcement learning approach. IEEE Trans. Wirel. Commun. 2021, 20, 7346–7359. [Google Scholar] [CrossRef]
- Jung, Y.; Peradilla, M.; Agulto, R. Blockchain-based NAT management for smart mobility. In Proceedings of the 2018 International Conference on Computational Science and Computational Intelligence (CSCI), Las Vegas, NV, USA, 12–14 December 2018; pp. 495–500. [Google Scholar]
- Yu, S.; Chen, X.; Zhou, Z.; Gong, X.; Wu, D. When deep reinforcement learning meets federated learning: Intelligent multitimescale resource management for multiaccess edge computing in 5G ultradense network. IEEE Internet Things J. 2020, 8, 2238–2251. [Google Scholar] [CrossRef]
- Ahmed, I.; Zhang, Y.; Jeon, G.; Lin, W.; Khosravi, M.R.; Qi, L. A blockchain-and artificial intelligence-enabled smart IoT framework for sustainable city. Int. J. Intell. Syst. 2022, 37, 6493–6507. [Google Scholar] [CrossRef]
- Salim, M.M.; Shanmuganathan, V.; Loia, V.; Park, J.H. Deep learning enabled secure IoT handover authentication for blockchain networks. Hum. Cent. Comput. Inf. Sci. 2021, 11, 21. [Google Scholar]
- Manjaragi, S.V.; Saboji, S.V. Fast user authentication in 5G heterogeneous networks using RLAC-FNN and blockchain technology for handoff delay reduction. Wirel. Netw. 2023, 1–19. [Google Scholar] [CrossRef]
- Sharmila, A.H.; Jaisankar, N. Edge intelligent agent assisted hybrid hierarchical blockchain for continuous healthcare monitoring & recommendation system in 5G WBAN-IoT. Comput. Netw. 2021, 200, 108508. [Google Scholar]
- Wang, X.; Garg, S.; Lin, H.; Piran, M.J.; Hu, J.; Hossain, M.S. Enabling secure authentication in industrial iot with transfer learning empowered blockchain. IEEE Trans. Ind. Inform. 2021, 17, 7725–7733. [Google Scholar] [CrossRef]
- Luong, N.C.; Anh, T.T.; Xiong, Z.; Niyato, D.; Kim, D.I. Joint time scheduling and transaction fee selection in blockchain-based RF-powered backscatter cognitive radio network. Comput. Netw. 2022, 214, 109135. [Google Scholar] [CrossRef]
- Sellami, B.; Hakiri, A.; Yahia, S.B. Deep Reinforcement Learning for energy-aware task offloading in join SDN-Blockchain 5G massive IoT edge network. Future Gener. Comput. Syst. 2022, 137, 363–379. [Google Scholar] [CrossRef]
- Ren, Y.; Chen, X.; Guo, S.; Guo, S.; Xiong, A. Blockchain-based VEC network trust management: A DRL algorithm for vehicular service offloading and migration. IEEE Trans. Veh. Technol. 2021, 70, 8148–8160. [Google Scholar] [CrossRef]
- Alam, T.; Ullah, A.; Benaida, M. Deep reinforcement learning approach for computation offloading in blockchain-enabled communications systems. J. Ambient. Intell. Humaniz. Comput. 2023, 14, 9959–9972. [Google Scholar] [CrossRef]
- He, Q.; Feng, Z.; Fang, H.; Wang, X.; Zhao, L.; Yao, Y.; Yu, K. A Blockchain-Based Scheme for Secure Data Offloading in Healthcare With Deep Reinforcement Learning. IEEE/ACM Trans. Netw. 2023. [Google Scholar] [CrossRef]
- Nguyen, D.C.; Pathirana, P.N.; Ding, M.; Seneviratne, A. Secure computation offloading in blockchain based IoT networks with deep reinforcement learning. IEEE Trans. Netw. Sci. Eng. 2021, 8, 3192–3208. [Google Scholar] [CrossRef]
- Wang, D.; Zhao, N.; Song, B.; Lin, P.; Yu, F.R. Resource management for secure computation offloading in softwarized cyber–physical systems. IEEE Internet Things J. 2021, 8, 9294–9304. [Google Scholar] [CrossRef]
- Liang, Y.C. Dynamic Spectrum Management: From Cognitive Radio to Blockchain and Artificial Intelligence; Springer Nature: Berlin/Heidelberg, Germany, 2020; p. 166. [Google Scholar]
- Maksymyuk, T.; Gazda, J.; Liyanage, M.; Han, L.; Shubyn, B.; Strykhaliuk, B.; Yaremko, O.; Jo, M.; Dohler, M. Ai-enabled blockchain framework for dynamic spectrum management in multi-operator 6g networks. In Future Intent-Based Networking: On the QoS Robust and Energy Efficient Heterogeneous Software Defined Networks; Springer International Publishing: Cham, Switzerland, 2021; pp. 322–338. [Google Scholar]
- Miah, M.S.; Hossain, M.S.; Armada, A.G. Machine Learning-based Malicious Users Detection in Blockchain-Enabled CR-IoT Network for Secured Spectrum Access. In Proceedings of the 2022 IEEE International Symposium on Broadband Multimedia Systems and Broadcasting (BMSB), Bilbao, Spain, 15–17 June 2022; pp. 1–6. [Google Scholar]
- Lu, Y.; Huang, X.; Zhang, K.; Maharjan, S.; Zhang, Y. Communication-efficient federated learning and permissioned blockchain for digital twin edge networks. IEEE Internet Things J. 2020, 8, 2276–2288. [Google Scholar] [CrossRef]
- Maksymyuk, T.; Gazda, J.; Volosin, M.; Bugar, G.; Horvath, D.; Klymash, M.; Dohler, M. Blockchain-empowered framework for decentralized network management in 6G. IEEE Commun. Mag. 2020, 58, 86–92. [Google Scholar] [CrossRef]
- Rajesh Babu, C.; Amutha, B. Blockchain and extreme learning machine based spectrum management in cognitive radio networks. Trans. Emerg. Telecommun. Technol. 2022, 33, e4174. [Google Scholar] [CrossRef]
- Liu, Y.; Gu, Y.; Yang, D.; Wang, J. Fault identification and relay protection of hybrid microgrid using blockchain and machine learning. IETE J. Res. 2022, 1–11. [Google Scholar] [CrossRef]
- Belhadi, A.; Djenouri, Y.; Srivastava, G.; Jolfaei, A.; Lin, J.C.W. Privacy reinforcement learning for faults detection in the smart grid. Ad Hoc Netw. 2021, 119, 102541. [Google Scholar] [CrossRef]
- Calo, J.; Lo, B. IoT Federated Blockchain Learning at the Edge. arXiv 2023, arXiv:2304.03006. [Google Scholar]
- Aloqaily, M.; Al Ridhawi, I.; Guizani, M. Energy-aware blockchain and federated learning-supported vehicular networks. IEEE Trans. Intell. Transp. Syst. 2021, 23, 22641–22652. [Google Scholar] [CrossRef]
- Xu, C.; Wang, K.; Guo, M. Intelligent resource management in blockchain-based cloud datacenters. IEEE Cloud Comput. 2017, 4, 50–59. [Google Scholar] [CrossRef]
- Luo, J.; Chen, Q.; Yu, F.R.; Tang, L. Blockchain-enabled software-defined industrial internet of things with deep reinforcement learning. IEEE Internet Things J. 2020, 7, 5466–5480. [Google Scholar] [CrossRef]
- Chen, G.; Wu, J.; Yang, W.; Bashir, A.K.; Li, G.; Hammoudeh, M. Leveraging graph convolutional-LSTM for energy-efficient caching in blockchain-based green IoT. IEEE Trans. Green Commun. Netw. 2021, 5, 1154–1164. [Google Scholar] [CrossRef]
- El Azzaoui, A.; Singh, S.K.; Pan, Y.; Park, J.H. Block5GIntell: Blockchain for AI-enabled 5G networks. IEEE Access 2020, 8, 145918–145935. [Google Scholar] [CrossRef]
- Ashfaq, T.; Khalid, M.I.; Ali, G.; Affendi, M.E.; Iqbal, J.; Hussain, S.; Ullah, S.S.; Yahaya, A.S.; Khalid, R.; Mateen, A. An efficient and secure energy trading approach with machine learning technique and consortium blockchain. Sensors 2022, 22, 7263. [Google Scholar] [CrossRef] [PubMed]
- Said, D. A decentralized electricity trading framework (DETF) for connected EVs: A blockchain and machine learning for profit margin optimization. IEEE Trans. Ind. Inform. 2020, 17, 6594–6602. [Google Scholar] [CrossRef]
- Cao, Y.; Ren, X.; Qiu, C.; Wang, X. Hierarchical reinforcement learning for blockchain-assisted software defined industrial energy market. IEEE Trans. Ind. Inform. 2022, 18, 6100–6108. [Google Scholar] [CrossRef]
- Jamil, F.; Iqbal, N.; Ahmad, S.; Kim, D. Peer-to-peer energy trading mechanism based on blockchain and machine learning for sustainable electrical power supply in smart grid. IEEE Access 2021, 9, 39193–39217. [Google Scholar] [CrossRef]
- Hossain, M.S.; Rahman, M.H.; Rahman, M.S.; Hosen, A.S.; Seo, C.; Cho, G.H. Intellectual property theft protection in IoT based precision agriculture using SDN. Electronics 2021, 10, 1987. [Google Scholar] [CrossRef]
- Kumar, P.; Kumar, R.; Srivastava, G.; Gupta, G.P.; Tripathi, R.; Gadekallu, T.R.; Xiong, N.N. PPSF: A privacy-preserving and secure framework using blockchain-based machine-learning for IoT-driven smart cities. IEEE Trans. Netw. Sci. Eng. 2021, 8, 2326–2341. [Google Scholar] [CrossRef]
- Nawaz, A.; Gia, T.N.; Queralta, J.P.; Westerlund, T. Edge AI and blockchain for privacy-critical and data-sensitive applications. In Proceedings of the 2019 Twelfth International Conference on Mobile Computing and Ubiquitous Network (ICMU), Kathmandu, Nepal, 4–6 November 2019; pp. 1–2. [Google Scholar]
- Elhoseny, M.; Haseeb, K.; Shah, A.A.; Ahmad, I.; Jan, Z.; Alghamdi, M.I. IoT solution for AI-enabled PRIVACY-PREServing with big data transferring: An application for healthcare using blockchain. Energies 2021, 14, 5364. [Google Scholar] [CrossRef]
- Aliyu, I.; Feliciano, M.C.; Van Engelenburg, S.; Kim, D.O.; Lim, C.G. A blockchain-based federated forest for SDN-enabled in-vehicle network intrusion detection system. IEEE Access 2021, 9, 102593–102608. [Google Scholar] [CrossRef]
- Munir, M.S.; Bajwa, I.S.; Cheema, S.M. An intelligent and secure smart watering system using fuzzy logic and blockchain. Comput. Electr. Eng. 2019, 77, 109–119. [Google Scholar] [CrossRef]
- Kamalov, F.; Gheisari, M.; Liu, Y.; Feylizadeh, M.R.; Moussa, S. Critical Controlling for the Network Security and Privacy Based on Blockchain Technology: A Fuzzy DEMATEL Approach. Sustainability 2023, 15, 10068. [Google Scholar] [CrossRef]
- Outchakoucht, A.; Hamza, E.S.; Leroy, J.P. Dynamic access control policy based on blockchain and machine learning for the internet of things. Int. J. Adv. Comput. Sci. Appl. 2017, 8, 417–424. [Google Scholar] [CrossRef]
- Mrabet, H.; Alhomoud, A.; Jemai, A.; Trentesaux, D. A secured industrial Internet-of-things architecture based on blockchain technology and machine learning for sensor access control systems in smart manufacturing. Appl. Sci. 2022, 12, 4641. [Google Scholar] [CrossRef]
- Akbarfam, A.J.; Barazandeh, S.; Maleki, H.; Gupta, D. DLACB: Deep Learning Based Access Control Using Blockchain. arXiv 2023, arXiv:2303.14758. [Google Scholar]
- Rana, S.K.; Rana, S.K.; Nisar, K.; Ag Ibrahim, A.A.; Rana, A.K.; Goyal, N.; Chawla, P. Blockchain technology and Artificial Intelligence based decentralized access control model to enable secure interoperability for healthcare. Sustainability 2022, 14, 9471. [Google Scholar] [CrossRef]
- Xiong, W.; Xiong, L. Smart contract based data trading mode using blockchain and machine learning. IEEE Access 2019, 7, 102331–102344. [Google Scholar] [CrossRef]
- Truong, V.; Le, L.B. Security for the Metaverse: Blockchain and Machine Learning Techniques for Intrusion Detection. TechrXiv 2023, Preprint. [Google Scholar] [CrossRef]
- Philip, A.O.; Saravanaguru, R.K. Secure incident & evidence management framework (SIEMF) for internet of vehicles using deep learning and blockchain. Open Comput. Sci. 2020, 10, 408–421. [Google Scholar]
- Gaur, R.; Prakash, S.; Kumar, S.; Abhishek, K.; Msahli, M.; Wahid, A. A Machine-Learning–Blockchain-Based Authentication Using Smart Contracts for an IoHT System. Sensors 2022, 22, 9074. [Google Scholar] [CrossRef] [PubMed]
- Zulkifl, Z.; Khan, F.; Tahir, S.; Afzal, M.; Iqbal, W.; Rehman, A.; Saeed, S.; Almuhaideb, A.M. FBASHI: Fuzzy and blockchain-based adaptive security for healthcare IoTs. IEEE Access 2022, 10, 15644–15656. [Google Scholar] [CrossRef]
- Ogundoyin, S.O.; Kamil, I.A. An efficient authentication scheme with strong privacy preservation for fog-assisted vehicular ad hoc networks based on blockchain and neuro-fuzzy. Veh. Commun. 2021, 31, 100384. [Google Scholar] [CrossRef]
- Sammeta, N.; and Parthiban, L. Hyperledger blockchain enabled secure medical record management with deep learning-based diagnosis model. Complex Intell. Syst. 2022, 8, 625–640. [Google Scholar] [CrossRef]
- Cristina, C.; Moro, E.P.; Maple, C.; Epiphaniou, G. I-Trace: Protecting cyber-physical infrastructure through enhanced gateways, DLT and machine learning. In Proceedings of the Competitive Advantage in the Digital Economy (CADE 2021), Online, 2–3 June 2021. [Google Scholar]
- Finogeev, A.; Deev, M.; Parygin, D.; Finogeev, A. Intelligent SDN Architecture With Fuzzy Neural Network and Blockchain for Monitoring Critical Events. Appl. Artif. Intell. 2022, 36, 2145634. [Google Scholar] [CrossRef]
- Qi, Y.; Hossain, M.S.; Nie, J.; Li, X. Privacy-preserving blockchain-based federated learning for traffic flow prediction. Future Gener. Comput. Syst. 2021, 117, 328–337. [Google Scholar] [CrossRef]
- Rahman, Z.; Yi, X.; Khalil, I.; Anwar, A.; Pal, S. Blockchain-Based and Fuzzy Logic-Enabled False Data Discovery for the Intelligent Autonomous Vehicular System. In Proceedings of the Third International Symposium on Advanced Security on Software and Systems, Melbourne, Australia, 10–14 July 2023; pp. 1–11. [Google Scholar]
- Wijesekara, P.A.D.S.N. Prevalence, Risk Factors and Remedies for Psychiatric Illnesses among Students in Higher Education: A Comprehensive Study in University of Ruhuna. Res. Sq. 2022, Preprint. [Google Scholar] [CrossRef]
- Cheema, M.A.; Qureshi, H.K.; Chrysostomou, C.; Lestas, M. Utilizing blockchain for distributed machine learning based intrusion detection in internet of things. In Proceedings of the 2020 16th International Conference on Distributed Computing in Sensor Systems (DCOSS), Marina del Rey, CA, USA, 25–27 May 2020; pp. 429–435. [Google Scholar]
- Saveetha, D.; Maragatham, G. Design of Blockchain enabled intrusion detection model for detecting security attacks using deep learning. Pattern Recognit. Lett. 2022, 153, 24–28. [Google Scholar] [CrossRef]
- Mansour, R.F. Artificial intelligence based optimization with deep learning model for blockchain enabled intrusion detection in CPS environment. Sci. Rep. 2022, 12, 12937. [Google Scholar] [CrossRef] [PubMed]
- Alkadi, O.; Moustafa, N.; Turnbull, B.; Choo, K.K.R. A deep blockchain framework-enabled collaborative intrusion detection for protecting IoT and cloud networks. IEEE Internet Things J. 2020, 8, 9463–9472. [Google Scholar] [CrossRef]
- Khan, A.A.; Khan, M.M.; Khan, K.M.; Arshad, J.; Ahmad, F. A blockchain-based decentralized machine learning framework for collaborative intrusion detection within UAVs. Comput. Netw. 2021, 196, 108217. [Google Scholar] [CrossRef]
- Vargas, H.; Lozano-Garzon, C.; Montoya, G.A.; Donoso, Y. Detection of security attacks in industrial IoT networks: A blockchain and machine learning approach. Electronics 2021, 10, 2662. [Google Scholar] [CrossRef]
- Ferrag, M.A.; Maglaras, L. DeepCoin: A novel deep learning and blockchain-based energy exchange framework for smart grids. IEEE Trans. Eng. Manag. 2019, 67, 1285–1297. [Google Scholar] [CrossRef]
- Farooq, M.S.; Khan, S.; Rehman, A.; Abbas, S.; Khan, M.A.; Hwang, S.O. Blockchain-Based Smart Home Networks Security Empowered with Fused Machine Learning. Sensors 2022, 22, 4522. [Google Scholar] [CrossRef]
- Abdel-Basset, M.; Moustafa, N.; Hawash, H.; Razzak, I.; Sallam, K.M.; Elkomy, O.M. Federated intrusion detection in blockchain-based smart transportation systems. IEEE Trans. Intell. Transp. Syst. 2021, 23, 2523–2537. [Google Scholar] [CrossRef]
- Liu, H.; Zhang, S.; Zhang, P.; Zhou, X.; Shao, X.; Pu, G.; Zhang, Y. Blockchain and federated learning for collaborative intrusion detection in vehicular edge computing. IEEE Trans. Veh. Technol. 2021, 70, 6073–6084. [Google Scholar] [CrossRef]
- Derhab, A.; Guerroumi, M.; Gumaei, A.; Maglaras, L.; Ferrag, M.A.; Mukherjee, M.; Khan, F.A. Blockchain and random subspace learning-based IDS for SDN-enabled industrial IoT security. Sensors 2019, 19, 3119. [Google Scholar] [CrossRef]
- He, X.; Chen, Q.; Tang, L.; Wang, W.; Liu, T. Cgan-based collaborative intrusion detection for uav networks: A blockchain-empowered distributed federated learning approach. IEEE Internet Things J. 2022, 10, 120–132. [Google Scholar] [CrossRef]
- Jmal, R.; Ghabri, W.; Guesmi, R.; Alshammari, B.M.; Alshammari, A.S.; Alsaif, H. Distributed Blockchain-SDN Secure IoT System Based on ANN to Mitigate DDoS Attacks. Appl. Sci. 2023, 13, 4953. [Google Scholar] [CrossRef]
- Yazdinejad, A.; Dehghantanha, A.; Parizi, R.M.; Srivastava, G.; Karimipour, H. Secure intelligent fuzzy blockchain framework: Effective threat detection in iot networks. Comput. Ind. 2023, 144, 103801. [Google Scholar] [CrossRef]
- Ghazal, T.M.; Hasan, M.K.; Abdallah, S.N.H.; Abubakkar, K.A. Secure IoMT pattern recognition and exploitation for multimedia information processing using private blockchain and fuzzy logic. Trans. Asian Low-Resour. Lang. Inf. Process. 2022. [Google Scholar] [CrossRef]
- Ali, S.E.; Tariq, N.; Khan, F.A.; Ashraf, M.; Abdul, W.; Saleem, K. BFT-IoMT: A Blockchain-Based Trust Mechanism to Mitigate Sybil Attack Using Fuzzy Logic in the Internet of Medical Things. Sensors 2023, 23, 4265. [Google Scholar] [CrossRef] [PubMed]
- Abdulqadder, I.H.; Zou, D.; Aziz, I.T. The DAG blockchain: A secure edge assisted honeypot for attack detection and multi-controller based load balancing in SDN 5G. Future Gener. Comput. Syst. 2023, 141, 339–354. [Google Scholar] [CrossRef]
- Abou El Houda, Z.; Hafid, A.; Khoukhi, L. Brainchain-a machine learning approach for protecting blockchain applications using sdn. In Proceedings of the ICC 2020–2020 IEEE International Conference on Communications (ICC), virtual event, 7–11 June 2020; pp. 1–6. [Google Scholar]
- Preuveneers, D.; Rimmer, V.; Tsingenopoulos, I.; Spooren, J.; Joosen, W.; Ilie-Zudor, E. Chained anomaly detection models for federated learning: An intrusion detection case study. Appl. Sci. 2018, 8, 2663. [Google Scholar] [CrossRef]
- Wang, J.; Jin, H.; Chen, J.; Tan, J.; Zhong, K. Anomaly detection in Internet of medical Things with Blockchain from the perspective of deep neural network. Inf. Sci. 2022, 617, 133–149. [Google Scholar] [CrossRef]
- Alkhamisi, A.; Katib, I.; Buhari, S.M. Blockchain-Assisted Hybrid Deep Learning-Based Secure Mechanism for Software Defined Networks. In Proceedings of the 2023 IEEE International Conference on Consumer Electronics (ICCE), Las Vegas, NV, USA, 6–8 January 2023; pp. 1–8. [Google Scholar]
- Yang, G.; Shin, C.; Yoo, Y.; Yoo, C. A case for SDN-based network virtualization. In Proceedings of the 2021 29th International Symposium on Modeling, Analysis, and Simulation of Computer and Telecommunication Systems (MASCOTS), Houston, TX, USA, 3–5 November 2021; pp. 1–8. [Google Scholar]
- Adhikari, A.; Rawat, D.B.; Song, M. Wireless network virtualization by leveraging blockchain technology and machine learning. In Proceedings of the ACM Workshop on Wireless Security and Machine Learning, Miami, FL, USA, 15–17 May 2019; pp. 61–66. [Google Scholar]
- Qiu, C.; Yu, F.R.; Xu, F.; Yao, H.; Zhao, C. Blockchain-based distributed software-defined vehicular networks via deep q-learning. In Proceedings of the 8th ACM Symposium on Design and Analysis of Intelligent Vehicular Networks and Applications, Montreal, QC, Canada, 28 October–2 November 2018; pp. 8–14. [Google Scholar]
- Fu, X.; Yu, F.R.; Wang, J.; Qi, Q.; Liao, J. Performance optimization for blockchain-enabled distributed network function virtualization management and orchestration. IEEE Trans. Veh. Technol. 2020, 69, 6670–6679. [Google Scholar] [CrossRef]
- Boateng, G.O.; Sun, G.; Mensah, D.A.; Doe, D.M.; Ou, R.; Liu, G. Consortium blockchain-based spectrum trading for network slicing in 5G RAN: A multi-agent deep reinforcement learning approach. IEEE Trans. Mob. Comput. 2022. [Google Scholar] [CrossRef]
- Abdulqadder, I.H.; Zhou, S. SliceBlock: Context-aware authentication handover and secure network slicing using DAG-blockchain in edge-assisted SDN/NFV-6G environment. IEEE Internet Things J. 2022, 9, 18079–18097. [Google Scholar] [CrossRef]
- Gong, Y.; Sun, S.; Wei, Y.; Song, M. Deep reinforcement learning for edge computing resource allocation in blockchain network slicing broker framework. In Proceedings of the 2021 IEEE 93rd Vehicular Technology Conference (VTC2021-Spring), virtual event, 25 April–19 May 2021; pp. 1–6. [Google Scholar]
- Bandara, E.; Liang, X.; Shetty, S.; Mukkamala, R.; Rahman, A.; Keong, N.W. Skunk—A blockchain and zero trust security enabled federated learning platform for 5G/6G network slicing. In Proceedings of the 2022 19th Annual IEEE International Conference on Sensing, Communication, and Networking (SECON), virtual event, 20–23 September 2022; pp. 109–117. [Google Scholar]
- Boateng, G.O.; Ayepah-Mensah, D.; Doe, D.M.; Mohammed, A.; Sun, G.; Liu, G. Blockchain-enabled resource trading and deep reinforcement learning-based autonomous RAN slicing in 5G. IEEE Trans. Netw. Serv. Manag. 2021, 19, 216–227. [Google Scholar] [CrossRef]
- Ou, R.; Sun, G.; Ayepah-Mensah, D.; Boateng, G.O.; Liu, G. Two-Tier Resource Allocation for Multi-Tenant Network Slicing: A Federated Deep Reinforcement Learning Approach. IEEE Internet Things J. 2023. [Google Scholar] [CrossRef]
- Singh, S.K.; Rathore, S.; Park, J.H. Blockiotintelligence: A blockchain-enabled intelligent IoT architecture with artificial intelligence. Future Gener. Comput. Syst. 2020, 110, 721–743. [Google Scholar] [CrossRef]
- Unal, D.; Hammoudeh, M.; Khan, M.A.; Abuarqoub, A.; Epiphaniou, G.; Hamila, R. Integration of federated machine learning and blockchain for the provision of secure big data analytics for Internet of Things. Comput. Secur. 2021, 109, 102393. [Google Scholar] [CrossRef]
- Lv, Z.; Xiu, W. Interaction of edge-cloud computing based on SDN and NFV for next generation IoT. IEEE Internet Things J. 2019, 7, 5706–5712. [Google Scholar] [CrossRef]
- Zhang, K.; Zhu, Y.; Maharjan, S.; Zhang, Y. Edge intelligence and blockchain empowered 5G beyond for the industrial Internet of Things. IEEE Netw. 2019, 33, 12–19. [Google Scholar] [CrossRef]
- He, Y.; Wang, Y.; Qiu, C.; Lin, Q.; Li, J.; Ming, Z. Blockchain-based edge computing resource allocation in IoT: A deep reinforcement learning approach. IEEE Internet Things J. 2020, 8, 2226–2237. [Google Scholar] [CrossRef]
- Tian, Y.; Li, T.; Xiong, J.; Bhuiyan, M.Z.A.; Ma, J.; Peng, C. A blockchain-based machine learning framework for edge services in IIoT. IEEE Trans. Ind. Inform. 2021, 18, 1918–1929. [Google Scholar] [CrossRef]
- Shahbazi, Z.; Byun, Y.C. Improving transactional data system based on an edge computing–blockchain–machine learning integrated framework. Processes 2021, 9, 92. [Google Scholar] [CrossRef]
- Gardas, B.B.; Heidari, A.; Navimipour, N.J.; Unal, M. A fuzzy-based method for objects selection in blockchain-enabled edge-IoT platforms using a hybrid multi-criteria decision-making model. Appl. Sci. 2022, 12, 8906. [Google Scholar] [CrossRef]
- Lakhan, A.; Mohammed, M.A.; Kozlov, S.; Rodrigues, J.J. Mobile-fog-cloud assisted deep reinforcement learning and blockchain-enable IoMT system for healthcare workflows. Trans. Emerg. Telecommun. Technol. 2021, e4363. [Google Scholar] [CrossRef]
- Zhang, S.; Wang, Z.; Zhou, Z.; Wang, Y.; Zhang, H.; Zhang, G.; Ding, H.; Mumtaz, S.; Guizani, M. Blockchain and federated deep reinforcement learning based secure cloud-edge-end collaboration in power IoT. IEEE Wirel. Commun. 2022, 29, 84–91. [Google Scholar] [CrossRef]
- Qu, G.; Cui, N.; Wu, H.; Li, R.; Ding, Y. ChainFL: A simulation platform for joint federated learning and blockchain in edge/cloud computing environments. IEEE Trans. Ind. Inform. 2021, 18, 3572–3581. [Google Scholar] [CrossRef]
- Guo, S.; Dai, Y.; Xu, S.; Qiu, X.; Qi, F. Trusted cloud-edge network resource management: DRL-driven service function chain orchestration for IoT. IEEE Internet Things J. 2019, 7, 6010–6022. [Google Scholar] [CrossRef]
- Maaroufi, S.; Pierre, S. BCOOL: A novel blockchain congestion control architecture using dynamic service function chaining and machine learning for next generation vehicular networks. IEEE Access 2021, 9, 53096–53122. [Google Scholar] [CrossRef]
- Li, M.; Pei, P.; Yu, F.R.; Si, P.; Li, Y.; Sun, E.; Zhang, Y. Cloud–Edge Collaborative Resource Allocation for Blockchain-Enabled Internet of Things: A Collective Reinforcement Learning Approach. IEEE Internet Things J. 2022, 9, 23115–23129. [Google Scholar] [CrossRef]
- Singh, S.; Rathore, S.; Alfarraj, O.; Tolba, A.; Yoon, B. A framework for privacy-preservation of IoT healthcare data using Federated Learning and blockchain technology. Future Gener. Comput. Syst. 2022, 129, 380–388. [Google Scholar] [CrossRef]
- Yin, B.; Yin, H.; Wu, Y.; Jiang, Z. FDC: A secure federated deep learning mechanism for data collaborations in the Internet of Things. IEEE Internet Things J. 2020, 7, 6348–6359. [Google Scholar] [CrossRef]
- Li, W.; Su, Z.; Li, R.; Zhang, K.; Wang, Y. Blockchain-based data security for artificial intelligence applications in 6G networks. IEEE Netw. 2020, 34, 31–37. [Google Scholar] [CrossRef]
- Hitaj, B.; Ateniese, G.; Perez-Cruz, F. Deep models under the GAN: Information leakage from collaborative deep learning. In Proceedings of the 2017 ACM SIGSAC Conference on Computer and Communications Security, Dallas, TX, USA, 30 October–3 November 2017; pp. 603–618. [Google Scholar]
- Liu, Y.; Yu, F.R.; Li, X.; Ji, H.; Leung, V.C. Blockchain and machine learning for communications and networking systems. IEEE Commun. Surv. Tutor. 2020, 22, 1392–1431. [Google Scholar] [CrossRef]
- Shahid, A.R.; Niki, P.; Corey, S.; Rain, K. Sensor-chain: A lightweight scalable blockchain framework for internet of things. In Proceedings of the 2019 International Conference on Internet of Things (iThings) and IEEE Green Computing and Communications (GreenCom) and IEEE Cyber, Physical and Social Computing (CPSCom) and IEEE Smart Data (SmartData), Atlanta, GA, USA, 14–17 July 2019; pp. 1154–1161. [Google Scholar]
- Zhang, P.; Guo, W.; Liu, Z.; Zhou, M.; Huang, B.; Sedraoui, K. Optimized Blockchain Sharding Model Based on Node Trust and Allocation. IEEE Trans. Netw. Serv. Manag. 2023. [Google Scholar] [CrossRef]
- Spain, M.; Foley, S.; Gramoli, V. The impact of ethereum throughput and fees on transaction latency during icos. In Proceedings of the International Conference on Blockchain Economics, Security and Protocols (Tokenomics 2019), Paris, France, 6–7 May 2019; pp. 9:1–9:15. [Google Scholar]
- Li, C.; Li, P.; Zhou, D.; Yang, Z.; Wu, M.; Yang, G.; Xu, W.; Long, F.; Yao, A.C.C. A decentralized blockchain with high throughput and fast confirmation. In Proceedings of the 2020 USENIX Annual Technical Conference (USENIXATC 20), virtual event, 15–17 July 2020; pp. 515–528. [Google Scholar]
- Xu, C.; Zhang, C.; Xu, J.; Pei, J. Slimchain: Scaling blockchain transactions through off-chain storage and parallel processing. Proc. Vldb Endow. 2021, 14, 2314–2326. [Google Scholar] [CrossRef]
- Yang, L.; Li, M.; Si, P.; Yang, R.; Sun, E.; Zhang, Y. Energy-efficient resource allocation for blockchain-enabled industrial Internet of Things with deep reinforcement learning. IEEE Internet Things J. 2020, 8, 2318–2329. [Google Scholar] [CrossRef]
- Reijsbergen, D.; Maw, A.; Zhang, J.; Dinh, T.T.A.; Datta, A. PIEChain–A Practical Blockchain Interoperability Framework. arXiv 2023, arXiv:2306.09735. [Google Scholar]
- Ding, D.; Duan, T.; Jia, L.; Li, K.; Li, Z.; Sun, Y. Interchain: A framework to support blockchain interoperability. In Proceedings of the Second Asia-Pacific Workshop on Networking, Beijing, China, 1–3 August 2018. [Google Scholar]
- Baek, U.J.; Ji, S.H.; Park, J.T.; Lee, M.S.; Park, J.S.; Kim, M.S. DDoS attack detection on bitcoin ecosystem using deep-learning. In Proceedings of the 2019 20th Asia-Pacific Network Operations and Management Symposium (APNOMS), Matsue, Japan, 18–20 September 2019; pp. 1–4. [Google Scholar]
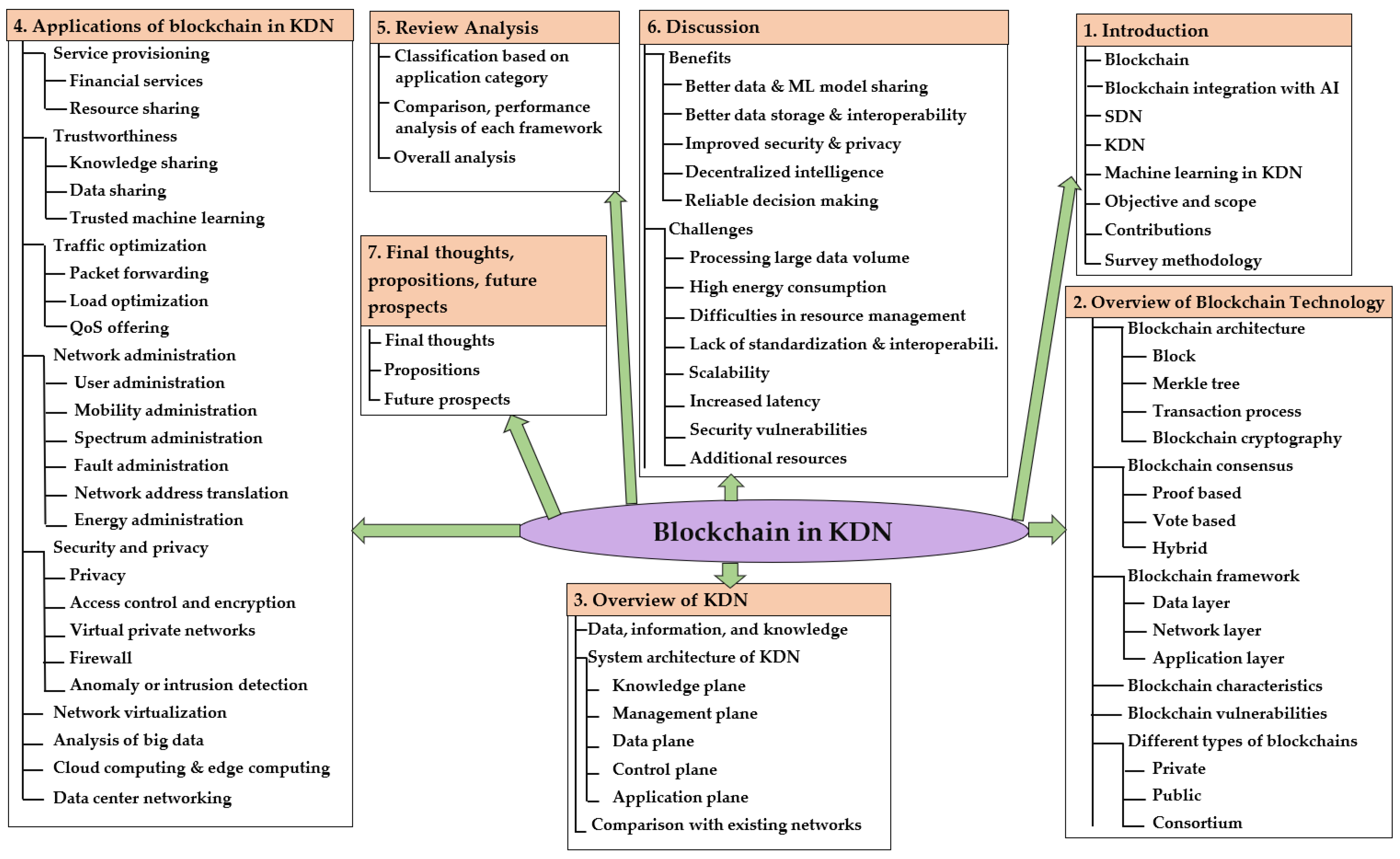
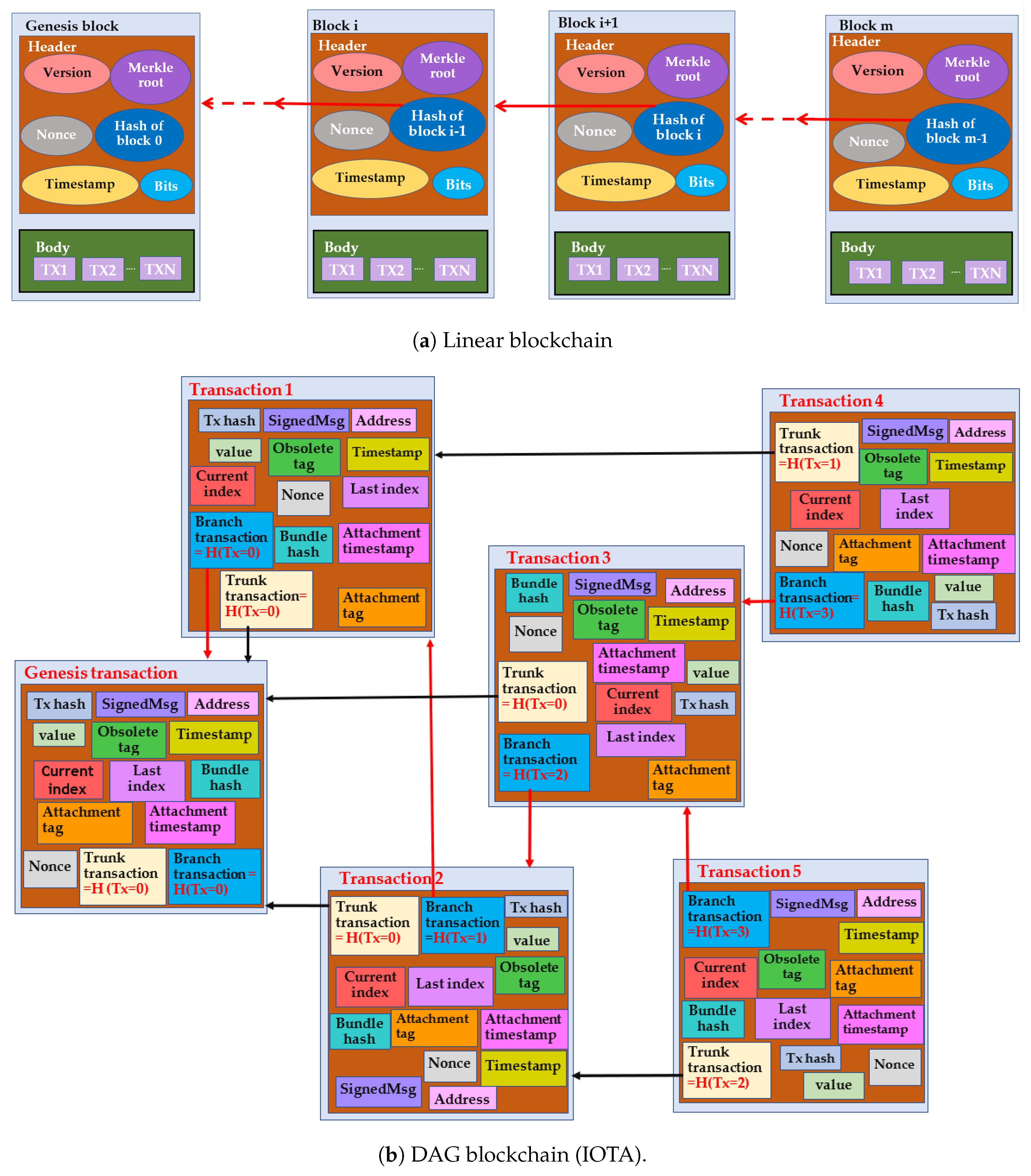
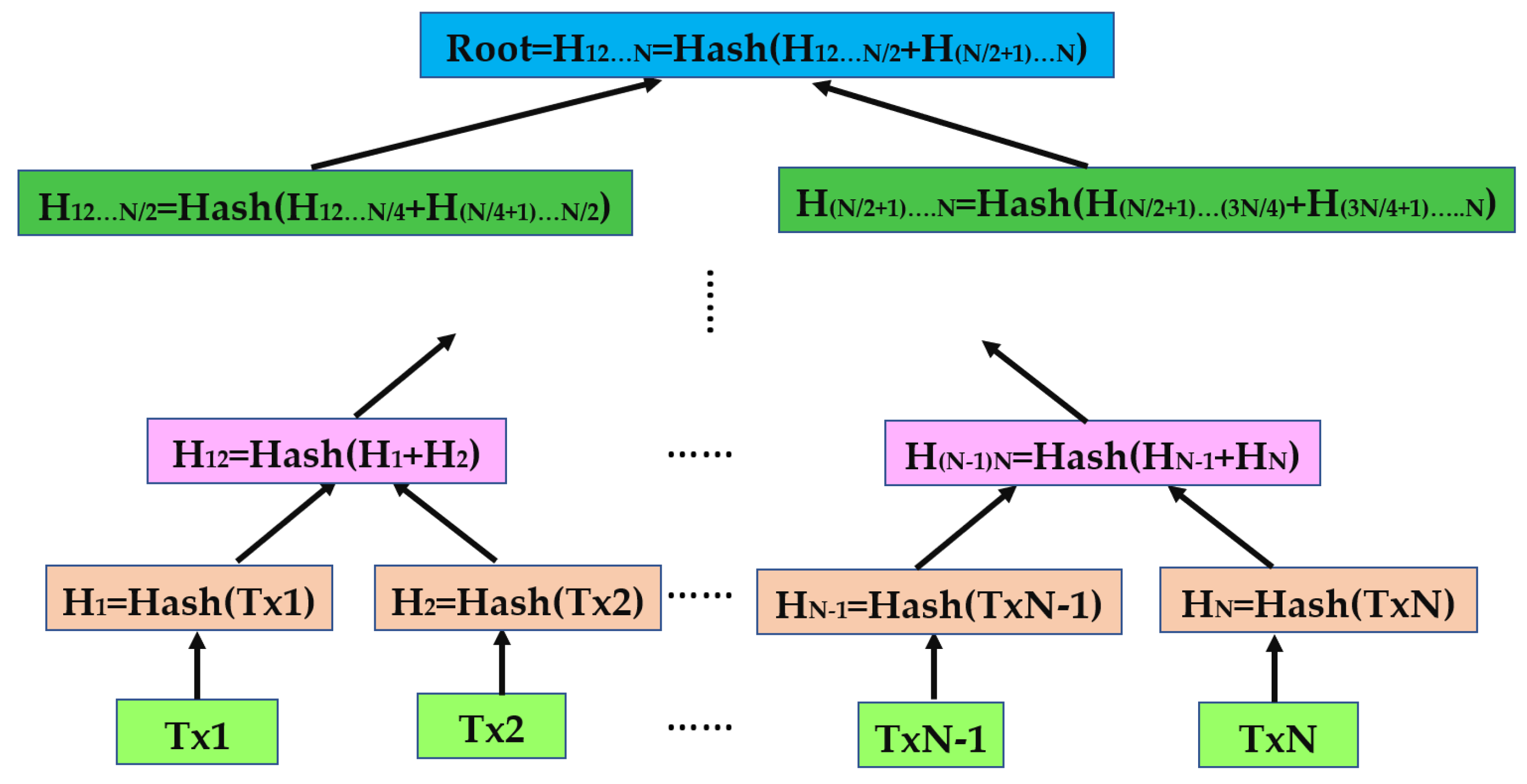

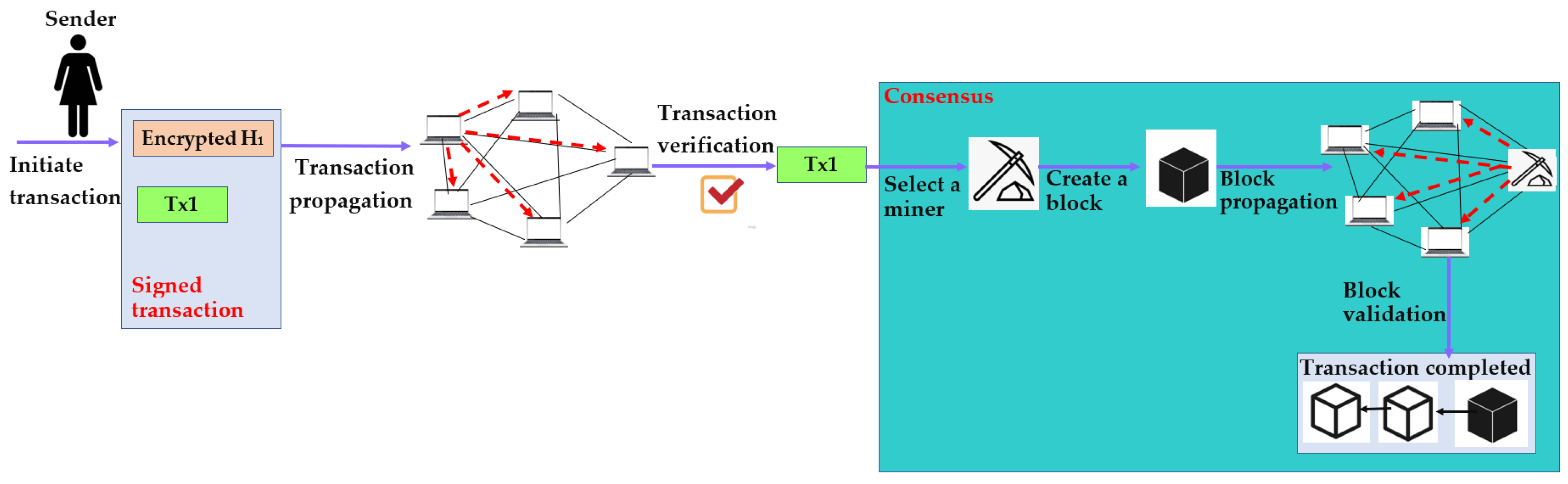
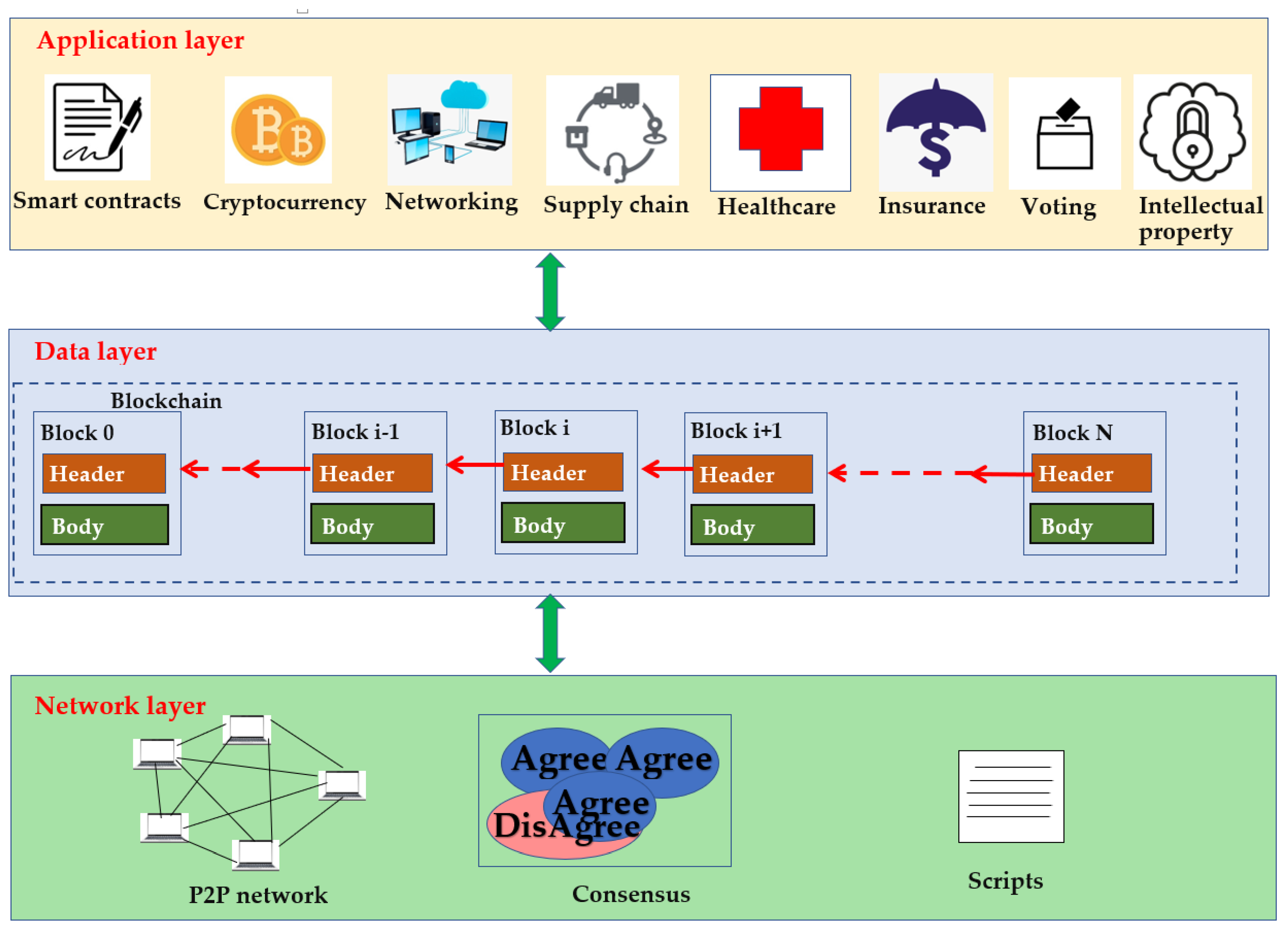

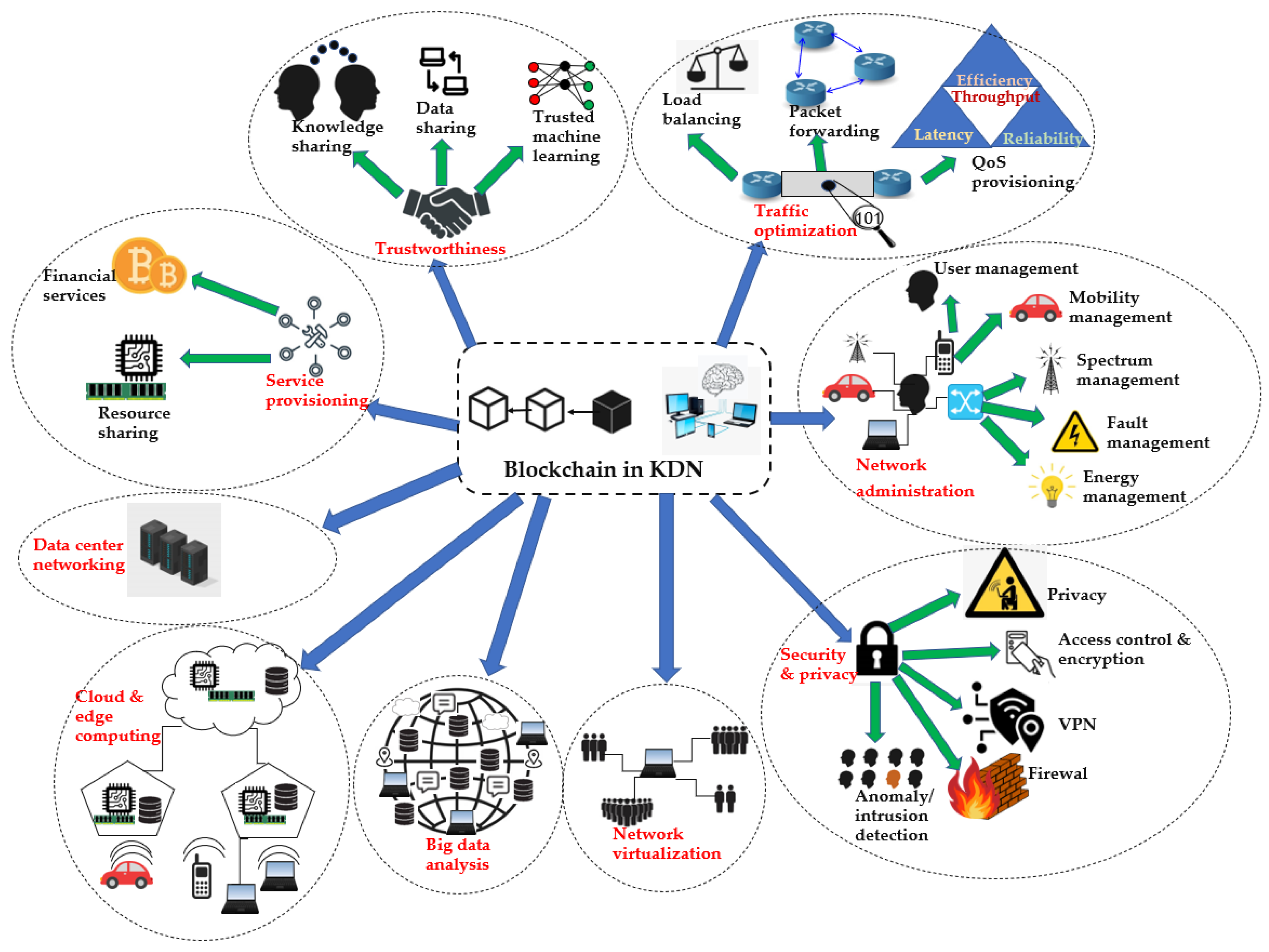
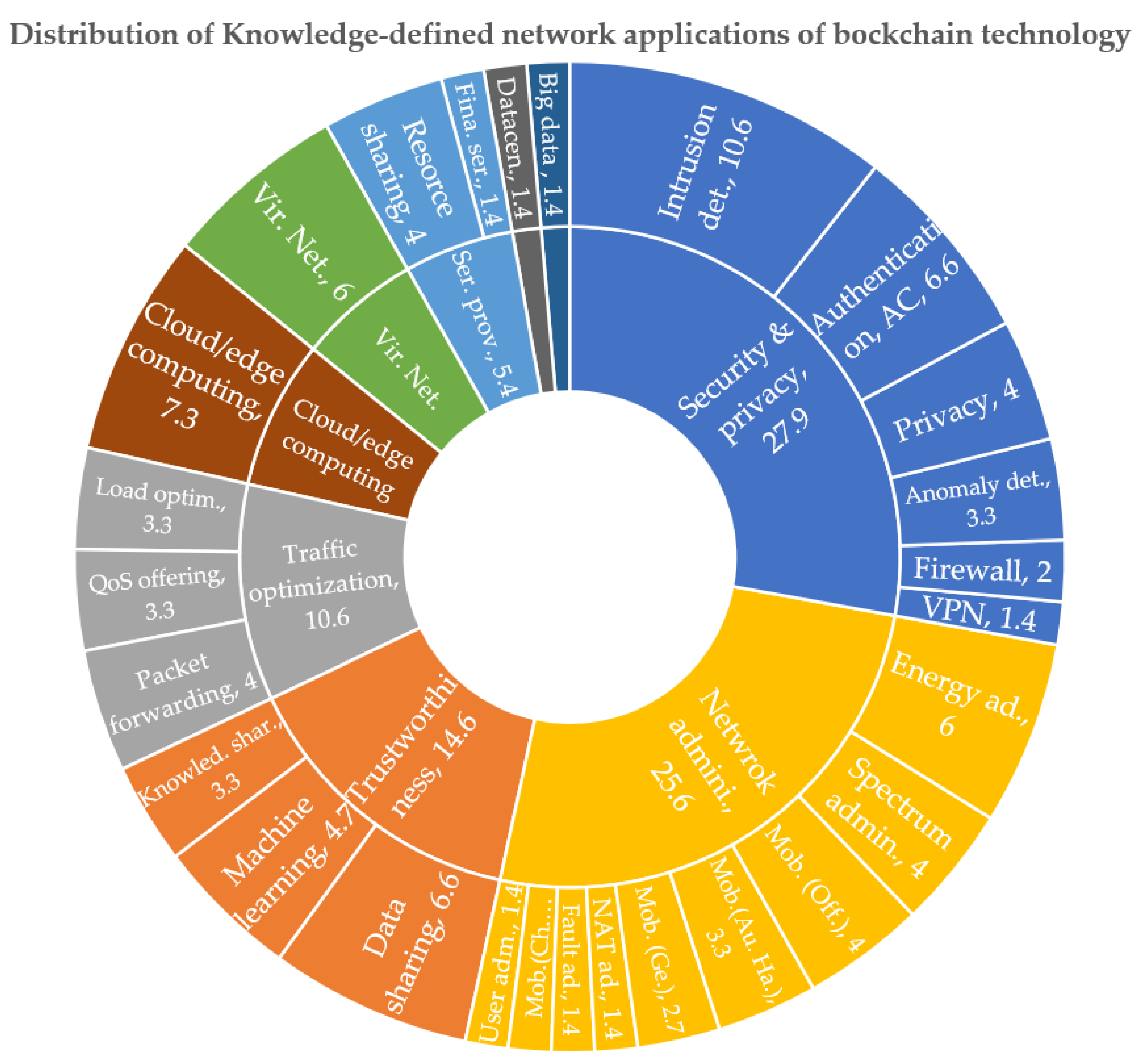

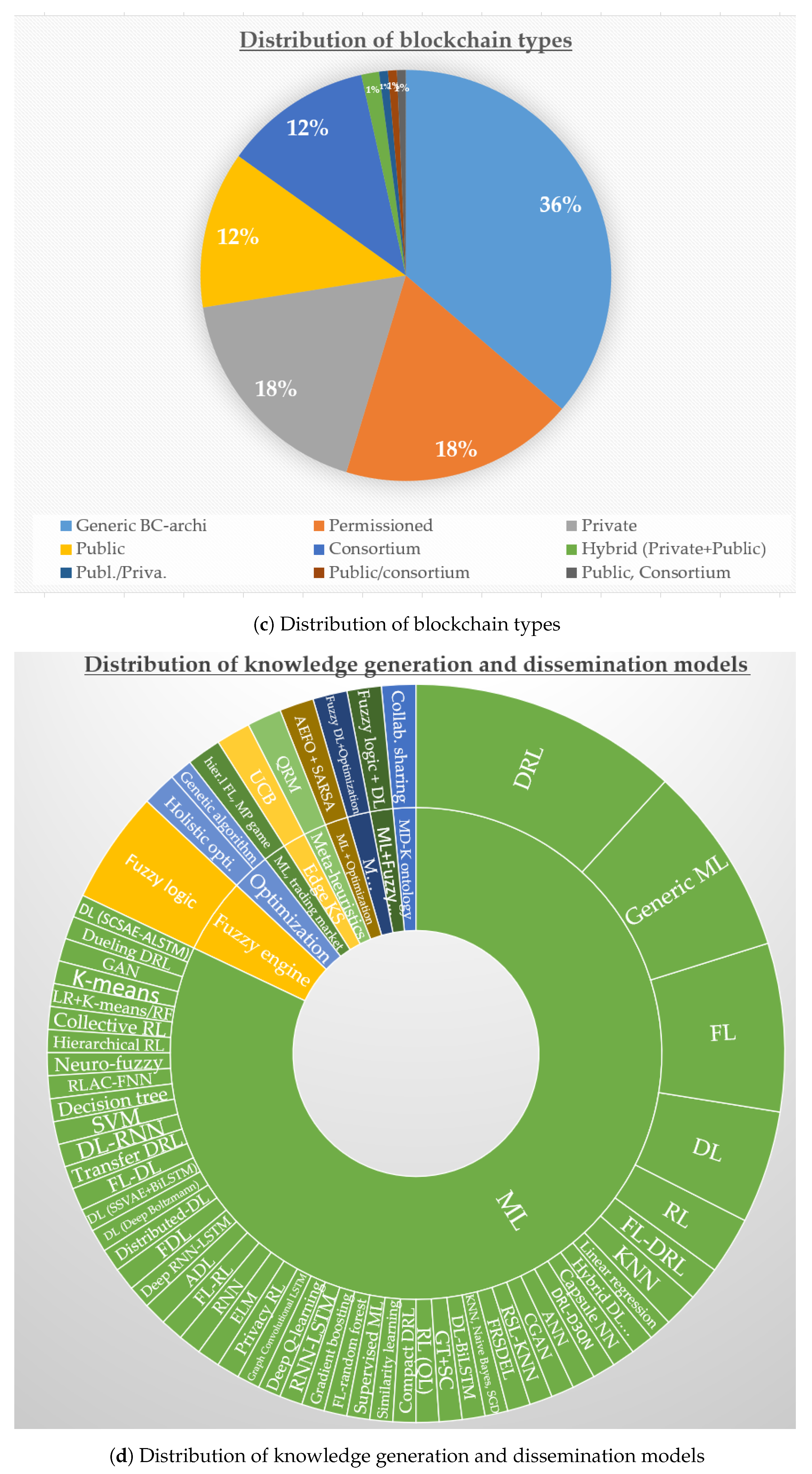

| Plane | Function/Purpose | Protocols/Models/Approaches/Frameworks/Examples |
|---|---|---|
| Network | Proof-based consensus | PoW [96], PoS [97], PoA [98], PoSp [99], PoB [100], PoAu [101], PoET [102] |
| Vote-based consensus | PBFT [103], DBFT [105], Raft [106] | |
| Hybrid consensus | DPoS [107] | |
| Scripts | TBAC [114] | |
| P2P communication | Bitcoin protocol [111], Ethereum wire protocol [112], IPFS [113] | |
| Network attacks | DoS attacks, routing attacks, domain name service attacks, eclipse attacks [142] | |
| Data | Architectures | Linear [3], Directed acyclic graph [4] |
| Types | Private [149], Public [150], Consortium [151] | |
| Cryptography | Hashing [82], Public key cryptography [80], Zero-knowledge proofs [84], Post-quantum cryptography [87,88,90], Hybrid cryptography [86,89], fault-tolerant ciphers [91,92,93,94,95] | |
| Endpoint attacks | 51% vulnerability, cryptojacking [143] | |
| Application | Smart contracts | Contractual automation [116], access control [117] |
| Cryptocurrency | Bitcoin [2], Ethereum [81] | |
| Supply chain | Cold chain management [121] | |
| Networking | TRUCON [123], IoTChain [124], UASTrustChain [125] | |
| Healthcare | Drug counterfeiting [127], Medblock [128], MedShare [129] | |
| Insurance | ClaimChain [130], Insurance fraud protection [131], Decentralized reinsurance [132] | |
| Voting | PriScore [133], Auditable voting [134] | |
| Intellectual property | IP protection [135], IP rights management [136] |
| Plane | Function | Protocols/Models/Languages |
|---|---|---|
| Knowledge | Store knowledge | KIF [166], OIL [167], OWL [169], RDFS [168], RDF [161] |
| Rule modeling and dissemination | RuleML [171], RIF [172], SWRL [173] | |
| Knowledge querying only | KGQL [181], KQML [182], SQWRL [180] | |
| Knowledge querying and modifying | SPARQL [178], GraphQL [179] | |
| Rule/knowledge assessment | RETE [174], Bossam [175], Jess [176], Drools [177] | |
| Management | Network management | OF-CONFIG [184], SNMP [185], PACMAN [187], CONMan [186] |
| Network monitoring | Payless [188], HONE [189], OpenNetMon [190], OpenSample [191] | |
| Data collection | IQP [192,235], packet sampling [193], adaptive data collection [194], sensor measurement collection [195] | |
| Data storage | YANG [196], CIM [197] | |
| Data | Forwarding models | OpenFlow [202], ForCES [201], OpFlex [200], POF [203], PCE-PCC [204], OpenState [205] |
| Control | Northbound API | Adhoc [208], RESTful [209], intent-based [210], language-based API [211] |
| East–Westbound API | ALTO [212], Hyperflow [213], ONOS [210], Onix [214] | |
| Southbound API | OpenFlow [202], ForCES [201], OpFlex [200], POF [203], PCE-PCC [204], OpenState [205] | |
| Logically and physically centralized control | NOX [208], Trema [215], Ryu [216], Meridian [217] | |
| Logically centralized and physically distributed control | SMaRtLight [218], HyperFlow [213], ONOS [210], Onix [214], Kandoo [219], Orion [220] | |
| Hybrid control | DevoFlow [221], Fibbing [222], HybridFlow [223] | |
| Logically and physically distributed control | DISCO [224], D-SDN [225], Cardigan [226] | |
| Application | Policy definition and update | Procera [211], Nettle [232], Frenetic [233], Kinetic [234] |
| Group | Sub-Group | Blockchain Based Frameworks |
|---|---|---|
| Service Provisioning | Financial services | DRL [237], BEIIP [238] |
| Resource sharing | Dai et al. [239], Guo et al. [240], DRS [241], 6G-IoV [242], Mohammed et al. [243], ManuChain [244] | |
| Trustworthiness | Knowledge sharing | MKShareNet [245], Li et al. [246], HBEFL [247], CKShare [248], Chai et.al. [249] |
| Data sharing | FL [251], Feng et al. [252], PBDL [253], MDS [254], Kumar et al. [255], MPBC [257], Zhang et al. [258], fuzzy engine [259], ANFPB [260] | |
| Machine learning | PiRATE [261], DFL [262], BlockDeepNet [263], Singh et al. [264], PriModChain [265], BBDDL [266], explainable AI [267] | |
| Traffic optimization | Packet forwarding | Secure routing [268], GAR [269], trusted routing [270], ENIR [271], CDRL [272], FLEA-RPL [273] |
| Load optimization | LB-DRL [274], ECRL [275], BCLB [276], Fuzzy [277], IVEC [278] | |
| QoS offering | MLBQR [280], MLSMBQS [281], side chaining [282], ATQMB [283], QoS-ledger [284] | |
| Network administration | User administration | CGT [285] |
| Mobility (Generic) | MADRL [286], DRL [287], QRM [288], DMM [289] | |
| Mobility (Authentication handover) | IoTAH [290], deep learning [291], RLAC-FNN [292], AEFO [293], ATLB [294] | |
| Mobility (Channel scheduling) | BBAIoT [295] | |
| Mobility (Offloading) | ACDRL [296], SOM [297], DRL-CO [298], SCRDO [299], Edge-cloud CO [300], DCRM [301] | |
| Spectrum administration | SMS [302], 6GSH [303], CR-IOT [304], DITEN [305], spectrum trading [306], SSA [307] | |
| Fault administration | FIRP [308], PRLB [309] | |
| NAT administration | QRM [288], IoMT [310] | |
| Energy administration | UAGV [311], RM [312], EE [313], pre-caching [314], Block5GIntell [315], VEN [316], DETF [317], DET [318], SDEM [319] | |
| Security and privacy | Privacy | PPSF [321], EAI [322], PPBD [323], FFIDS [324], SWS [325], FDEMATEL [326] |
| Authentication, access control, and encryption | Dynamic AC [327], SC [328], DLACB [329], DAC [330], SC-DT [331], MSecureChain [332], SIEMF [333], SVM [334], FBASHI [335], NF-VANET [336] | |
| VPN | VAE [337], I-Trace [338] | |
| Firewall | Fuzzy NN [339], FL-FW [340], fuzzy-IVN [341] | |
| Intrusion detection | SVM-AL [343], DL [344], PRO-DLBIDCPS [345], DBF [346], CID [347], KNN [348], DeepCoin [349], FRSDEL [350], FED-IDS [351], CIDS [352], RSL–KNN [353], CGAN [354], ANN [355], Fuzzy-IDS [356], PBFL-ADS [357], BFT-IoMT [358] | |
| Anomaly detection | DAG blockchain [359], Brain-chain [360], PBFLAD [361], IoMTBC-AD [362], HDL [363] | |
| Virtual network | ———— | BTNV [365], DQL-KDVN [366], DLT [367], CBDST [368], SliceBlock [369], BNSB [370], Skunk [371], SRT-DDQ [372], TTRAS [373] |
| Big data analysis | ———— | BlockIoTIntelligence [374], DFL-B [375] |
| Cloud/edge compu. | ———— | ERSS [377], Edge-RA [378], Tian et al. [379], Shahbazi et al. [380], NS-IoT [381], OSS [382], DSF [383], ChainFL [384], CBDRL [385], BCOOL [386], IC-ECRA [387] |
| Data center | ———— | PDC [388], FDC [389] |
| Framework | Blockchain Architecture | Blockchain Consensus | Blockchain Type | Knowledge Generation/Dissemination Model | Knowledge Generation/Dissemination Technique | Network Type | Performance | Publication Year |
|---|---|---|---|---|---|---|---|---|
| DRL [237] | Linear | PoW | Public | ML | DRL | IoT | Offload dumping service to obtain performance up to 85% | 2022 |
| BEIIP [238] | Linear | Generic | Permissioned | ML | DL | IoT | Better compared to TORM and RouteChain | 2023 |
| Dai et al. [239] | Linear | PBFT | Consortium | ML | DRL | 5G, 6G | Better convergence performance for resource management | 2019 |
| Guo et al. [240] | Linear | PoContribution | Consortium | ML | DL | IoT | Service response time increases with number of nodes | 2020 |
| DRS [241] | Linear | PoW+PoS | Public/Private | ML | DRL | 6G | High throughput and profit ratio compared to Q-learning | 2021 |
| 6G-IoV [242] | Linear | PoFL | Public | ML | FDL | 6G-IoV | Failure rate is 5% lower with 30% malicious nodes | 2022 |
| Mohammed et al. [243] | Linear | PoW | Public | ML | DRL | UAV | No performance analysis presented | 2020 |
| ManuChain [244] | Linear | Custom-XFT | Private | Optimization | Holistic | IIoT | Improves efficiency of manufacturing planning and execution | 2019 |
| MKShareNet [245] | Linear | PoW | Consortium | MD-K ontology | Collaborative sharing | Generic | Peak throughput—1900 tps, latency—300 ms | 2021 |
| Li et al. [246] | Linear | PoP | Private | Edge KS | UCB | IoT | Low delay and latency for block generating | 2020 |
| HBEFL [247] | Hierarchical | PoL | Consortium | ML, trading market | Hierarchical FL, multiplayer game | IoV | 10% more accuracy than traditional FL | 2020 |
| CKShare [248] | Linear | Generic | Public | ML | KNN | Manufacture | Gurantee confidentiality, improves ownership, avoid copyright problems | 2019 |
| Chai et al. [249] | DAG | TSA | Consortium | ML | ADL | ICV | Secure and resist malicious attacks | 2021 |
| FL [251] | Linear | PoQ | Private | ML | FL | IIoT | Good accuracy, efficiency, and security | 2019 |
| Feng et al. [252] | Linear | PoW | Public | ML | FL | 5G-Drone | High efficiency for authentication and good accuracy | 2021 |
| PBDL [253] | Linear | Smart contract | Private | ML | DL (SSVAE+BiLSTM) | Industrial healthcare | Better data sharing performance compared to existing studies | 2022 |
| MDS [254] | Linear | Generic | Permissioned | ML | DL | IoMT | Throughput—1, overhead—600 B, low latency and packet loss rate | 2023 |
| Kumar et al. [255] | Linear | PoAuthentication | Private | ML | DL (SCSAE-ALSTM) | UAV | Good performance in detecting illegitimate transactions | 2022 |
| MPBC [257] | Linear | Committee-based | Private | ML | FL-DL | Medical | Safe and effective for sharing medical data | 2021 |
| Zhang et al. [258] | Linear | PBFT | Permissioned | ML | Generic | Generic | Secure and trustless data sharing | 2018 |
| fuzzy engine [259] | Linear | PoW | Public | Fuzzy engine | Fuzzy logic | IoT | High block reliability and data integrity | 2022 |
| ANFPB [260] | Linear | PoS | Private | ML | Neuro-fuzzy | IoV | Efficient in preserving privacy and computational costs | 2021 |
| PiRATE [261] | Linear | PBFT | Permissioned | ML | Generic | 5G | More efficient than LearningChain in storage complexity and communication time | 2020 |
| DFL [262] | Linear | PBFT | Private | ML | FL | Vehicle | 0.97 accuracy, good throughput, low latency, good energy efficiency | 2020 |
| BlockDeepNet [263] | Linear | PBFT | Private | ML | DL | 5G-IoT | High accuracy with considerable overhead, latency | 2019 |
| Singh et al. [264] | Linear | Vote-based | Permissioned | ML | DL (Deep Boltzmann) | SD-Industrial | Scalable, better accuracy, low computation time and overhead | 2020 |
| PriModChain [265] | Linear | PoW | Public | ML | FL | IIoT | Good privacy, security, resilience, safety, and reliability | 2020 |
| BBDDL [266] | Linear | Dual-driven | Generic | ML | Distributed-DL | 6G-IoE | Better accuracy and latency | 2023 |
| explainable AI [267] | Linear | Vote-based | Public | ML | Generic | Generic | Trustworthy and explainable predictions | 2020 |
| Secure routing [268] | Linear | Vote-based | Permissioned | ML | Generic | SD-IoT | High trust and secure in multi-domains | 2022 |
| GAR [269] | Linear | PoW | Public | Optimization | Genetic algorithm | SD-IoT | Optimized resource utilization for routing | 2021 |
| trusted routing [270] | Linear | PoAu | Consortium | ML | RL | WSN | Low delay even at 51% vulnerability, good throughput, energy consumption | 2019 |
| ENIR [271] | Linear | Generic | Permissioned | ML | DRL | IoT | Better utilization of links and low transmission delay | 2023 |
| CDRL [272] | Linear | Generic | Permissioned | ML | Compact DRL | IoT | Require only 10% of resources, good transaction efficiency | 2022 |
| FLEA-RPL [273] | Generic | Generic | Generic | Fuzzy engine | Fuzzy logic | IIoT | Improves packet delivery ratio by reducing route interruptions | 2022 |
| LB-DRL [274] | Generic | Generic | Generic | ML | DRL | Generic | Scalable and reliable load balancing | 2021 |
| ECRL [275] | Linear | Generic | Permissioned | ML | RL | Vehicle | Good accuracy and throughput, high computational time | 2020 |
| BCLB [276] | Linear | Generic | Permissioned | ML | DRL | Generic | Prevent leakage of domain info, low migration cost | 2022 |
| Fuzzy [277] | Linear | Generic | Permissioned | Fuzzy engine | Fuzzy logic | SDVN | Good throughput, low latency and computation usage | 2022 |
| IVEC [278] | Linear | PoVS | Permissioned | ML | RL | VEC | Efficiently manage unbalanced load | 2021 |
| MLBQR [280] | Linear | PoW | Generic | ML | RL (QL) | SDVN | 15% low delay, 18% low energy consumption, 38% high throughput | 2022 |
| MLSMBQS [281] | Linear | PoW + EHO | Generic | ML | Generic | IoT | 8.5% high throughput, 15.3% low delay, 4.9% low energy consumption, better security | 2022 |
| Side chaining [282] | Linear | DPBFT-DPOS | Generic | ML | Generic | IoT | 15% high throughput and energy efficiency, High accuracy and F1-score, 10% low delay | 2022 |
| ATQMB [283] | Linear | PoS | Generic | ML | Generic | Generic | High security and traceability, moderate scalability | 2022 |
| QoS-ledger [284] | Linear | Smart contract | Public | Meta-heuristics | Genetic algorithm | Medical | Delay of 87–95 ms, 185 byte throughput, 8% duty cycle | 2021 |
| CGT [285] | Linear | Generic | Generic | Meta-heuristics | GT + SC | 5G, 6G | Achieves Nash equilibrium within a short time | 2019 |
| MADRL [286] | Linear | PBFT + PoReputation | Consortium | ML | DRL | 5G-UAV | Better utility optimization satisfaction for QoS | 2023 |
| DRL [287] | Linear | Generic | Generic | ML | DRL | Generic | Low computational delay and handover failure rate | 2021 |
| QRM [288] | Linear | Generic | Generic | Meta-heuristics | QRM | Generic | Improved latency with respect to mobility and security | 2018 |
| DMM [289] | Linear | Generic | Generic | ML | FL-DRL | 5G-UDN | 31.87% task execution time reduction | 2020 |
| IoTAH [290] | Generic | Generic | Generic | ML | Generic | IoT | Various smart applications in smart cities are discussed | 2022 |
| deep learning [291] | Linear | PoW | Private | ML | DL | IoT | Malicious device detection accuracy of 0.91 | 2021 |
| RLAC-FNN [292] | Linear | Custom | Generic | ML | RLAC-FNN | 5G | Reduce handover and consensus delay, authentication frequency | 2023 |
| AEFO [293] | Hierarchical | PoAu | Hybrid (Private + Public) | ML + Optimization | AEFO + SARSA | 5G WBAN-IoT | Low delay, packet loss rate, authentication time, energy consumption | 2021 |
| ATLB [294] | Linear | Generic | Permissioned | ML | Transfer DRL | IIoT | Accurate authentication with high throughput and low latency | 2021 |
| BBAIoT [295] | Linear | PoW | Public/consortium | ML | DRL-D3QN | CRN | Better network throughput and convergence speed | 2022 |
| ACDRL [296] | Linear | PoAu | Private | ML | DRL | SD-5G-IoT | 50% energy efficiency | 2022 |
| SOM [297] | Linear | PBFT | Consortium | ML | DRL | VEC | High throughput, low service execution delay and energy consumption | 2021 |
| DRL-CO [298] | Linear | Generic | Generic | ML | DRL | IoT | Low delay and consume low transmission power | 2022 |
| SCRDO [299] | Linear | Generic | Generic | ML | DRL | Medical | Lower cost than other approaches | 2023 |
| Edge-cloud CO [300] | Linear | PoW | Private | ML | DRL | IoT | High security with minimum smart contract and offloading costs | 2021 |
| DCRM [301] | Linear | PBFT | Generic | ML | DRL | Cyber-physical | Low system delay and good decision making related to self-adaptation | 2021 |
| SMS [302] | Linear | Generic | Generic | ML | DRL | CRN | Minimum experience of disruption and delay in handover | 2020 |
| 6GSH [303] | Linear | Generic | Generic | ML | Deep RNN-LSTM | 6G | Despite of service operators, a stabilized service quality is provided | 2021 |
| CR-IOT [304] | Linear | PoW | Generic | ML | Decision tree | CR-IoT | Effective in malicious user detection for secure spectrum access | 2022 |
| DITEN [305] | Linear | DPoS | Permissioned | ML | FL-RL | IoT | Data security and communication efficiency are improved | 2020 |
| Spectrum trading [306] | Linear | PoW, PoS, DPoS, PBFT | Public, Consortium | ML | RNN | 6G | Good throughput and profit and low overhead | 2020 |
| SSA [307] | Linear | Generic | Generic | ML | ELM | CRN | 0.68 detection rate | 2022 |
| FIRP [308] | Linear | Generic | Generic | ML | Generic | Microgrid | High power supply fault identification rate, improved relay protection success rate | 2022 |
| PRLB [309] | Linear | PoW | Private | ML | Privacy RL | Smartgrid | Better performance in outlier detection and runtime performance | 2021 |
| IoMT [310] | Linear | PoW | Generic | ML | FL | IoMT | Average accuracy around 65% | 2023 |
| UAGV [311] | Linear | Generic | Generic | ML | FL | UAV | Improved connectivity, energy enhancement, and service availability | 2021 |
| RM [312] | Linear | PoW | Public | ML | RL | Generic | Reduced cost and energy | 2017 |
| EE [313] | Linear | BFT | Permissioned | ML | DRL | IIoT | Improved energy efficiency with limited performance reduction | 2020 |
| Pre-caching [314] | Hierarchical | Custom | Private | ML | Graph Convolutional LSTM | IoT | Low energy consumption for caching | 2021 |
| Block5GIntell [315] | Linear | Modified PBFT | Consortium | ML | Generic | 5G | 20% decrease in energy consumption | 2020 |
| VEN [316] | Linear | Generic | Consortium | ML | KNN | VEN | Reduce charging cost and time | 2022 |
| DETF [317] | Linear | Generic | Consortium | ML | Generic | Connected EVs | Improved profitability | 2019 |
| DET [318] | Linear | Generic | Consortium | ML | Hierarchical RL | SD-EI | Total mean reward of 18% | 2022 |
| SDEM [319] | Linear | PBFT | Permissioned | ML | RNN–LSTM | Smart Grid | Low mean absolute percentage error and latency, high throughput, energy crowdsourcing | 2021 |
| PPSF [321] | Linear | PoW | Generic | ML | Gradient boosting | IoT-smart city | Intrusion detection preserving privacy, good classification performance | 2021 |
| EAI [322] | Linear | PoW | Private | ML | Generic | Generic | 300 ms processing time, low resource consumption | 2019 |
| PPBD [323] | Linear | Generic | Generic | ML | Generic | IoT | Maintain privacy, minor computing overhead | 2021 |
| FFIDS [324] | Linear | PoW | Public | ML | FL-random forest | SDVN | Efficient memory and computation resource usage, 0.9 attack detection rate | 2021 |
| SWS [325] | Linear | Generic | Generic | Fuzzy engine | Fuzzy logic | Smart agriculture | Securely and efficiently handle watering | 2019 |
| FDEMATEL [326] | Linear | Generic | Public | Fuzzy engine | Fuzzy logic | IoT | High impact related to authentication and intrusion detection criteria | 2023 |
| Dynamic AC [327] | Linear | Generic | Generic | ML | RL | IoT | Distributed access control with efficient handling | 2017 |
| SC [328] | Linear | Generic | Permissioned | ML | Supervised ML | IIoT | Can effectively reduce different types of threats | 2022 |
| DLACB [329] | Linear | PoAu | Private | ML | DL | Generic | Correct user authentication performance, access control identifying malicious users | 2023 |
| DAC [330] | Linear | PoAu | Public | ML | Generic | Healthcare | Traceable, authorized access control | 2022 |
| SC-DT [331] | Linear | PoW | Public | ML | Similarity learning | Generic | Good confidentiality, reduce replay attacks, good integrity | 2019 |
| MSecureChain [332] | Linear | PBFT | Generic | ML | FL | Metaverse | Enhance security, scalable, prevent single point of failure | 2023 |
| SIEMF [333] | Linear | PoW | Public | ML | DL | Generic | Privacy of vehicles is preserved, low block read and retrieval times | 2020 |
| SVM [334] | Linear | PoW | Private | ML | SVM | IoHT | Trusted, low consumption, improved security | 2022 |
| FBASHI [335] | Linear | PoW | Permissioned | Fuzzy engine | Fuzzy logic | IoHT | Distributed trust, prevent single point of failure, detect malicious behavior | 2022 |
| NF-VANET [336] | Linear | Generic | Generic | ML | Neuro-fuzzy | Vehicle | 91.5% accuracy, improvement in computation cost and overhead | 2021 |
| VAE [337] | Linear | PoW | Permissioned | ML | DL | Medical | High secrecy with good detection performance | 2022 |
| I-Trace [338] | Linear | Generic | Generic | ML | Generic | Cyber-physical | Secure infrastructure of cyber-physical networks | 2021 |
| Fuzzy NN [339] | Linear | PoW | Permissioned | ML + Fuzzy engine | Fuzzy logic + DL | SD-IoT | Fast attack detection, Accuracy of 96%, high throughput | 2022 |
| FL-FW [340] | Linear | delegated PBFT | Consortium | ML | FL | Vehicle | Prevent data poisoning attacks, flow prediction securing privacy | 2021 |
| fuzzy-IVN [341] | Linear | Generic | Generic | Fuzzy engine | Fuzzy logic | Vehicle | Detects false data and preserves reputation | 2023 |
| SVM-AL [343] | Linear | PoW | Private | ML | SVM | IoT | Accuracy, precision, F1-score close to 1 | 2020 |
| DL [344] | Linear | PoW | Public | ML | DL | Generic | High accuracy in detecting attacks | 2022 |
| PRO-DLBIDCPS [345] | Linear | PoW | Private | ML | DL-RNN | Cyber-physical | Enhanced detection and security, high accuracy with low training and testing times | 2022 |
| DBF [346] | Linear | PoW | Private | ML | DL-BiLSTM | IoT | Can securely transmit data in a timely and reliably, good detection rate | 2020 |
| CID [347] | Linear | Ranking algorithm | Generic | ML | KNN, Naive Bayes, SGD | UAV | Good accuracy, precision, and detection rate, low time to train | 2021 |
| KNN [348] | Linear | Generic | Generic | ML | KNN | IIoT | Scalable, detect diverse attacks, low computational usage | 2022 |
| DeepCoin [349] | Linear | PBFT | Private | ML | DL-RNN | Smart grid | 98% detection accuracy, low false alarm rate, preserve privacy | 2019 |
| FRSDEL [350] | Linear | Generic | Private | ML | FRSDEL | Smart home | Good stability and less error rate for intrusion detection | 2022 |
| FED-IDS [351] | Linear | Generic | Generic | ML | FL | Smart transportation | Efficient and credible intrusion detection | 2021 |
| CIDS [352] | Linear | PoW + PoAccuracy | Public | ML | FL | VEC | Low overhead and computational cost with collaborative privacy preserved detection | 2021 |
| RSL–KNN [353] | Linear | Access rights | Permissioned | ML | RSL–KNN | SD-IIoT | 96.73% accuracy, 100% detection rate | 2019 |
| CGAN [354] | Linear | Generic | Generic | ML | CGAN | UAV | Improved intrusion data detection, good generalization capability | 2022 |
| ANN [355] | Linear | Generic | Private | ML | ANN | SD-IoT | Guarantee security with improved threat detection and mitigation | 2023 |
| Fuzzy-IDS [356] | Linear | Generic | Generic | ML + Metaheuristics | Fuzzy DL + Optimization | IoT | Good threat classification performance, high throughput and low latency | 2023 |
| PBFL-ADS [357] | Linear | Generic | Private | Fuzzy engine | Fuzzy logic | IoMT | Diagnose fraudulent nodes with considerable workload, pattern identification ratio—92.1%, server utilization—40% | 2022 |
| BFT-IoMT [358] | Linear | Generic | Generic | Fuzzy engine | Fuzzy logic | IoMT | Better attack detection, low energy consumption, high packet delivery ratio and throughput | 2023 |
| DAG blockchain [359] | DAG | Generic | Generic | ML | Capsule NN | 5G-SDN | Outperforms others in terms of bandwidth, delay, packet loss, and security parameters | 2023 |
| Brain-chain [360] | Linear | Generic | Permissioned | ML | Supervised ML | Generic | Fast and effective in mitigating attacks, high accuracy with low false positive rate | 2020 |
| PBFLAD [361] | Linear | Round robin | Permissioned | ML | FL | Generic | About 10% impact from blockchain to FL | 2018 |
| IoMTBC-AD [362] | Linear | Generic | Generic | ML | DL | IoMT | Detects anomalies effectively | 2022 |
| HDL [363] | Linear | Generic | Generic | ML | Hybrid DL (CNN + LSTM) | Generic | Outperform conventional SDN by 8.6% higher accuracy | 2023 |
| BTNV [365] | Linear | Vote-based | Generic | ML | Linear regression | Wireless | Minimum double spending attacks and delays when selecting radio frequency slices | 2019 |
| DQL-KDVN [366] | Linear | Custom | Permissioned | ML | Deep Q learning | SDVN | Improved throughput, require caching resources | 2018 |
| DLT [367] | Linear | Custom | Permissioned | ML | Dueling DRL | IoV | Converges with high reward | 2020 |
| CBDST [368] | Linear | PBFT | Consortium | ML | DRL | 5G-RAN | Good security, utility of players are maximized | 2022 |
| SliceBlock [369] | DAG | PoSp | Generic | ML | GAN | SD-6G | Slice the network securely and energy efficiently | 2022 |
| BNSB [370] | Linear | Generic | Generic | ML | DRL | 5G | Price and time delay is better, high reward | 2021 |
| Skunk [371] | Linear | Generic | Generic | ML | FL | 5G, 6G | Detect attacks in the sliced network | 2022 |
| SRT-DDQ [372] | Linear | Generic | Consortium | ML | DRL | 5G | 12% reduction in double spending attacks, maximize player utility | 2021 |
| TTRAS [373] | Linear | Generic | Generic | ML | FL-DRL | 5G | Solution converges and maximize utility under various prices | 2023 |
| BlockIoTIntelligence [374] | Linear | Generic | Permissioned | ML | Generic | IoT | High accuracy and low latency in object detection | 2020 |
| DFL-B [375] | Linear | PoW | Private | ML | FL | IoT | Efficient, preserves privacy, low packet overhead and energy consumption | 2021 |
| ERSS [377] | Linear | Credit differentiated | Consortium | ML | Generic | IIoT | Improved edge service cost and service capacities | 2019 |
| Edge-RA [378] | Linear | PoW/PoS | Private | ML | DRL | IoT | Solution convergence with low delay and task drop rate | 2020 |
| Tian et al. [379] | Linear | Generic | Generic | ML | Decision tree | IIoT | Secure and efficient, high edge service accuracy | 2021 |
| Shahbazi et al. [380] | Linear | Generic | Generic | ML | K-means | Smart manufacturing | Improves processing time of manufacturing tasks, low delay and cost of deployment | 2021 |
| NS-IoT [381] | Linear | Custom | Permissioned | Fuzzy engine | Fuzzy logic | IoT | Quick node selection, manage linguistic and numerical data | 2022 |
| OSS [382] | Linear | Custom | Hybrid (Public + Private) | ML | DRL | IoMT | Low communication and computation time for offloading and scheduling | 2022 |
| DSF [383] | Linear | Generic | Generic | ML | DRL | Power IoT | Low queing delay and consensus delay | 2020 |
| ChainFL [384] | Linear | Generic | Generic | ML | FL-DRL | IoT | High convergence under upload and download attacks, scalable | 2021 |
| CBDRL [385] | Linear | Optimized PBFT | Consortium | ML | DRL | IoT | 15.8% and 10.1% cost saving, time saving-22% and 10% for link state routing and deep Q network placement, respectively | 2019 |
| BCOOL [386] | Linear | PoA | Generic | ML | Linear regression + K-means/random forest | Vehicle | High reliability and efficiency, accurate congestion prediction for realtime monitoring | 2021 |
| IC-ECRA [387] | Linear | Generic | Generic | ML | Collective RL | IoT | Effective in collaborative resource allocation | 2022 |
| PDC [388] | Linear | Generic | Generic | ML | FL | IoT-Datacenter | Can train ML models without sending private data | 2022 |
| FDC [389] | Linear | Generic | Generic | ML | FL | IoT-Datacenter | Converge well and have a high training accuracy compared to centralized ML | 2020 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Wijesekara, P.A.D.S.N.; Gunawardena, S. A Review of Blockchain Technology in Knowledge-Defined Networking, Its Application, Benefits, and Challenges. Network 2023, 3, 343-421. https://doi.org/10.3390/network3030017
Wijesekara PADSN, Gunawardena S. A Review of Blockchain Technology in Knowledge-Defined Networking, Its Application, Benefits, and Challenges. Network. 2023; 3(3):343-421. https://doi.org/10.3390/network3030017
Chicago/Turabian StyleWijesekara, Patikiri Arachchige Don Shehan Nilmantha, and Subodha Gunawardena. 2023. "A Review of Blockchain Technology in Knowledge-Defined Networking, Its Application, Benefits, and Challenges" Network 3, no. 3: 343-421. https://doi.org/10.3390/network3030017
APA StyleWijesekara, P. A. D. S. N., & Gunawardena, S. (2023). A Review of Blockchain Technology in Knowledge-Defined Networking, Its Application, Benefits, and Challenges. Network, 3(3), 343-421. https://doi.org/10.3390/network3030017







