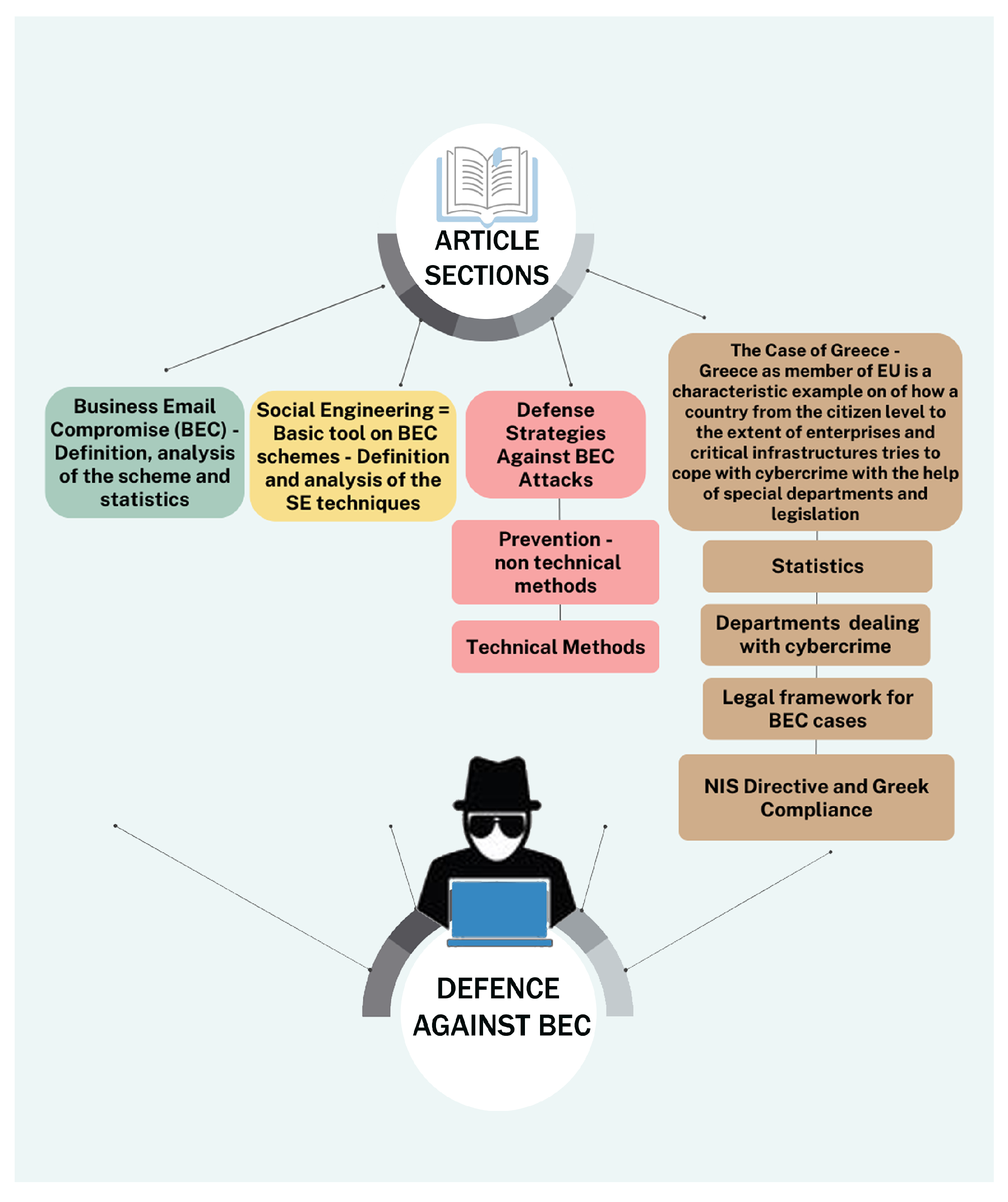
Business Email Compromise (BEC) Attacks: Threats, Vulnerabilities and Countermeasures—A Perspective on the Greek Landscape
Abstract
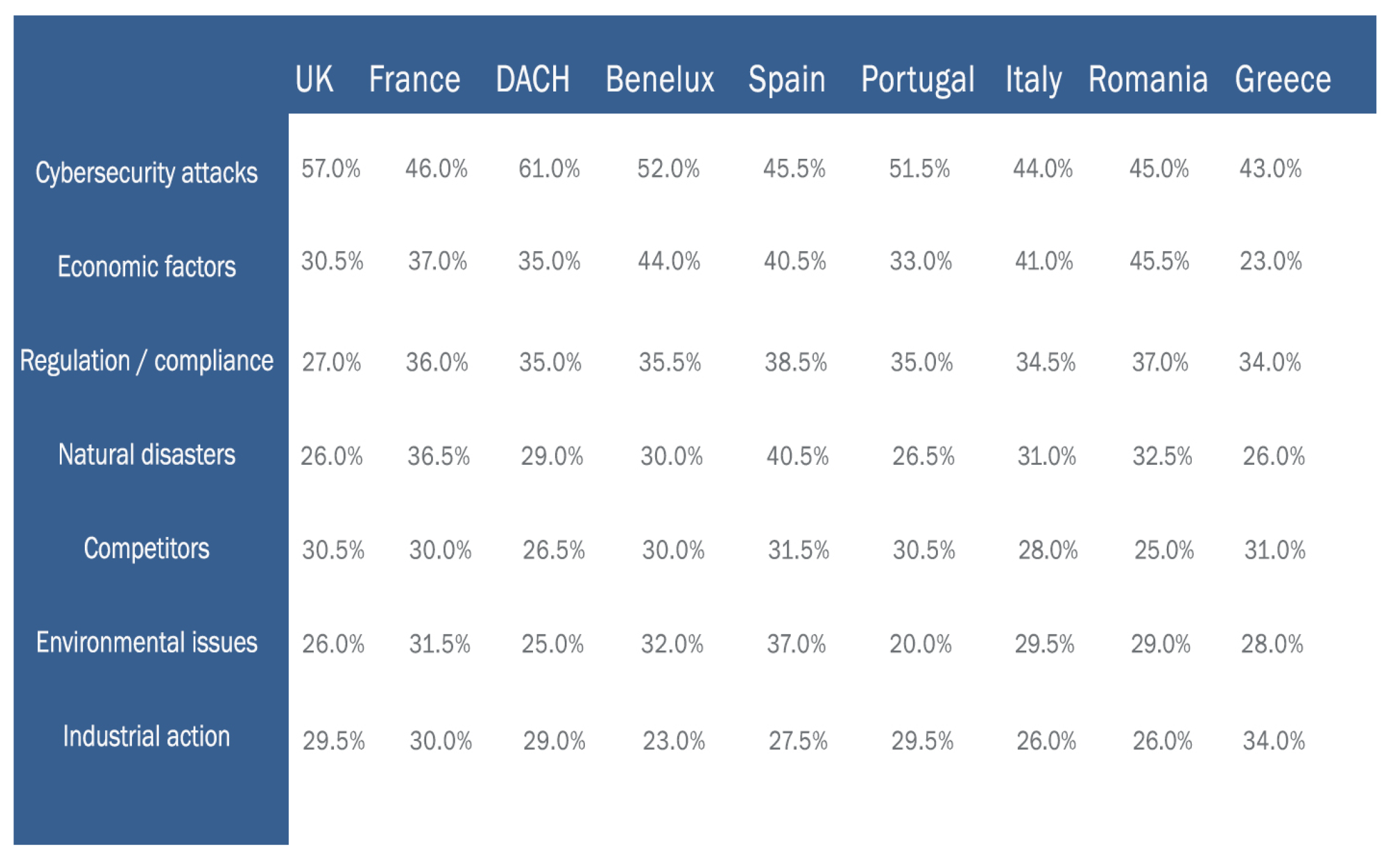
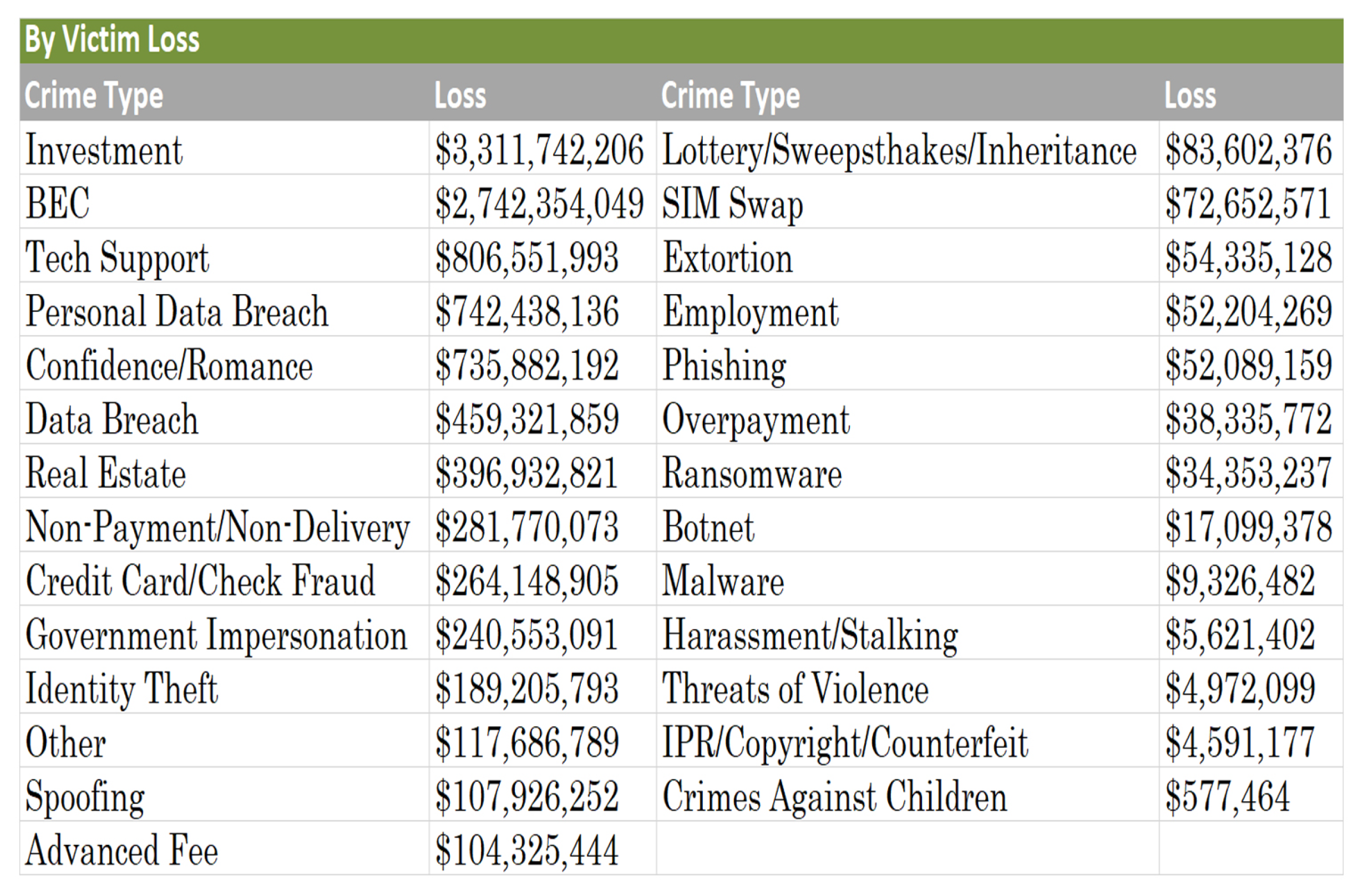
1. Introduction
- Information Gathering (nmap, legion, maltego etc.);
- Vulnerability Analysis (nmap, legion, nikto etc.);
- Web Application Analysis (sqlmap, wpscan, ZAP etc.);
- Database Assessment (sqlmap, SQLite etc.);
- Passwords Attacks (ncrack, medusa, hashcat etc.);
- Wireless Attacks (wifite, aircarck, reaver etc.);
- Reverse Engineering (clang, radare2, NASM shell etc.);
- Exploitation Tools (Metasploit framework, msf payload creator, social engineering toolkit etc.);
- Sniffing and Spoofing (macchanger, wireshark, responder etc.);
- Post Exploitation (mimikatz, weevely, powesploit etc.);
- Social Engineering Tools (maltego, msf payload creator, social engineering toolkit etc.);
Contribution
2. Research Methodology
3. Literary Review
- Spear Phishing attack: in which a hacker targets a specific individual or organization, undergoing a thorough research of the target’s information to increase the chances of the scam attempt being successful.
- Whaling attack: a type of spear phishing attack, but in this case, the target is usually a high-profile executive such as a CEO or CFO [6].
- Phishing-related techniques: A typical phishing attack involves the use of email containing a malicious URL link, PDF attachments containing malicious code or pointing to URLs, HTML files, and file-hosting service sites.
- Malware-related technique: The use of malware for BEC attacks such as keyloggers and remote access tools (RATs) have proven extremely useful due to their effectiveness and low cost. This kind of malware is commonly available in hacking forums or in the dark web and has evolved to use crypto services to evade detection from antivirus programs.
- Social engineering-based technique: This is the most common technique, where a well-crafted email is sent from the attacker who, through extensive research, is impersonating a entity known to the victim, usually a friend, associate, client, etc.
- Subject: Email subjects that contain the words “request”, “payment”, “urgent” and “wire transfer” are a red flag for a BEC attack.
- Reply-To: Due to the fact that most email clients do not display the reply-to addresses, actors insert their email address on the reply-to portion of the mail.
- From: A legitimate-looking email address is crafted to impersonate a person of trust.
- Frequency: The attack is more likely to succeed if BEC actors have checked the location and the time zone of the target. In the case of an attacker impersonating a CEO requesting a wire transfer, sending a BEC email during working hours on Friday and demanding that the request has to be resolved before the weekend has proven particularly successful.
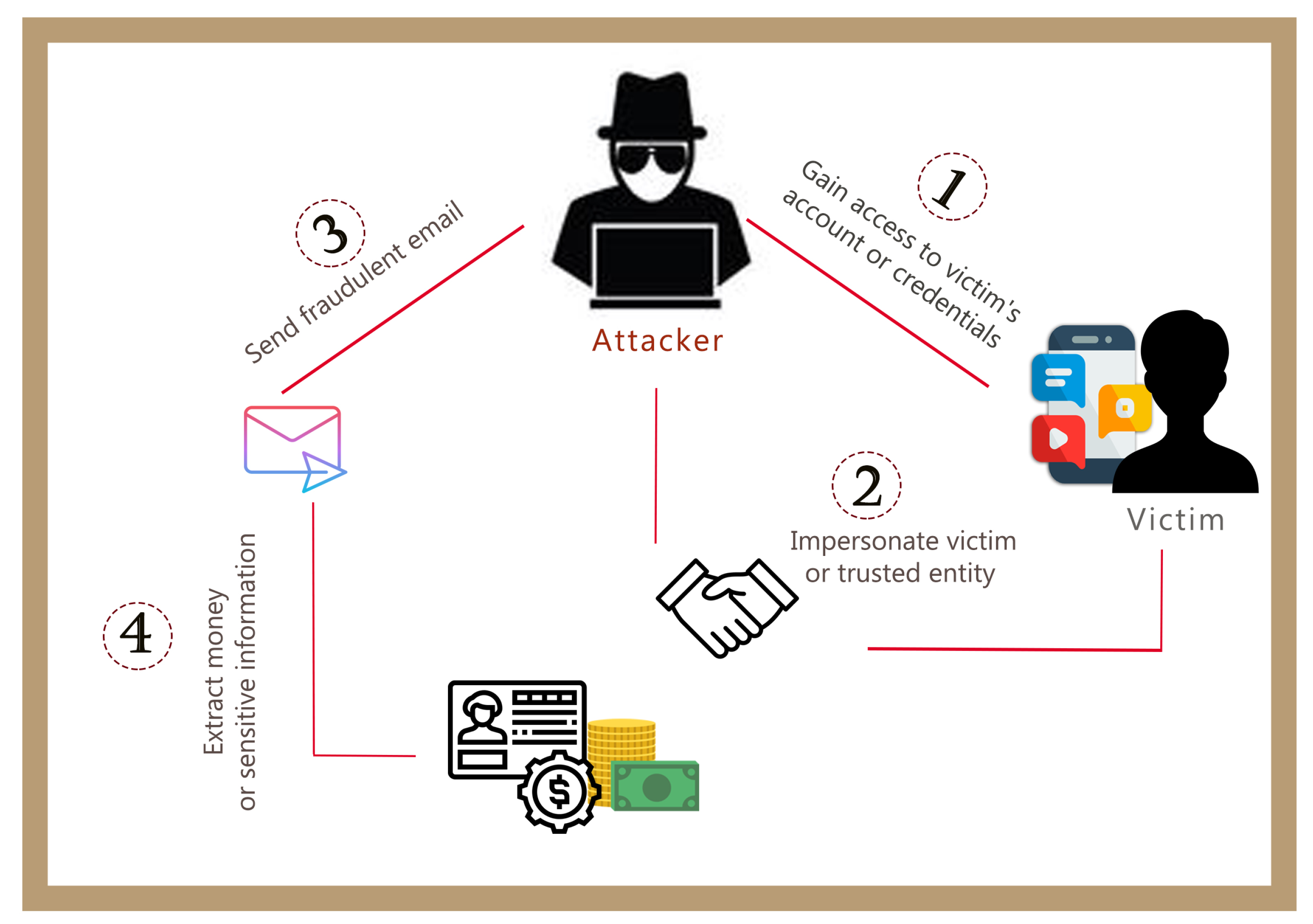
- By gaining access to the victim’s mail account, commonly referred to as Account Take-Over (ATO). Access is usually gained with phishing techniques or malware.
- By spoofing a trusted party. Attackers usually spoof email addresses or reply-to addresses. DMARC has outdated this method, but not all organizations support it.
- Through social engineering techniques and information from social networks like LinkedIn, a scammer can discover relationships between the victim and his/her associates and then register a deceptive domain name or email account. In this case, no spoofing was needed, meaning that DMARC cannot protect the victim from this kind of scam.
The Role of Social Engineering in BEC Attacks
- Social media (LinkeIn, Facebook, Twitter, etc.);
- Search engines;
- Official web sites;
- Forums, blogs etc.;
- Advertisements;
- Services or commands like pipl, WHOIS lookup (Linux or websites), FOCA, Maltego;
- Metadata (documents, photos etc.).
- Authority: This is a particularly effective technique because people are more likely to respond to authority. Attackers can claim authority with various ways like verbal communication, spoofing an email, etc.
- Intimidation: In many cases, intimidation derives from authority. Authority, confidence or even threats of harm can motivate a person to perform actions on an attacker’s behalf.
- Consensus: The act of taking advantage of a person’s natural tendency to mimic what others are doing or are perceived as having done in the past.
- Scarcity: A technique used to convince someone that an object has a higher value based on the object’s scarcity. Scarcity can also be applied to time or information to increase the influence on the target.
- Familiarity, liking, similarity: A principle that exploits a person’s native trust in that which is familiar, meaning that a person is keener to trust someone with common contacts or relationships, also known as a known entity.
- Trust: Trust as a social engineering principle is the effort that an attacker makes to develop a relationship with a victim.
- Distraction: People’s tendency to get distracted can also be exploited by schemers. When someone’s focus is diverted, he or she may ignore other things that are happening.
- Social proof: The use of social proof, meaning convincing the target that he acts in a way that is socially acceptable and has been done by others before, can ease his or her mind to make the decision to take an action they are not comfortable with.
- Urgency: A technique that applies pressure on the victim to act quickly without giving him or her the time to consider their actions.
- Greed-need: Greed and need are powerful motives in and of themselves. In this case, usually, an advance-fee fraud occurs, which involves the promise of wealth, gifts or employment in exchange for a payment.
- Phishing: A form of social engineering attack focused on stealing credentials or identity information from any potential target.
- Spear Phishing: These attacks require collecting information about the victim using available data online (OSINT).
- Whaling Phishing: A spear phishing attack with the difference that it targets high-profile targets.
- Vishing Phishing: This term refers to phone phishing, meaning phishing attempts performed via voice.
- Smishing: The term refers to phishing via SMS communication, usually used to load malware on mobile devices or steal credentials.
- Interactive Voice Response Phishing: These attacks are performed by using an interactive voice response system pretending to be a legitimate business or bank.
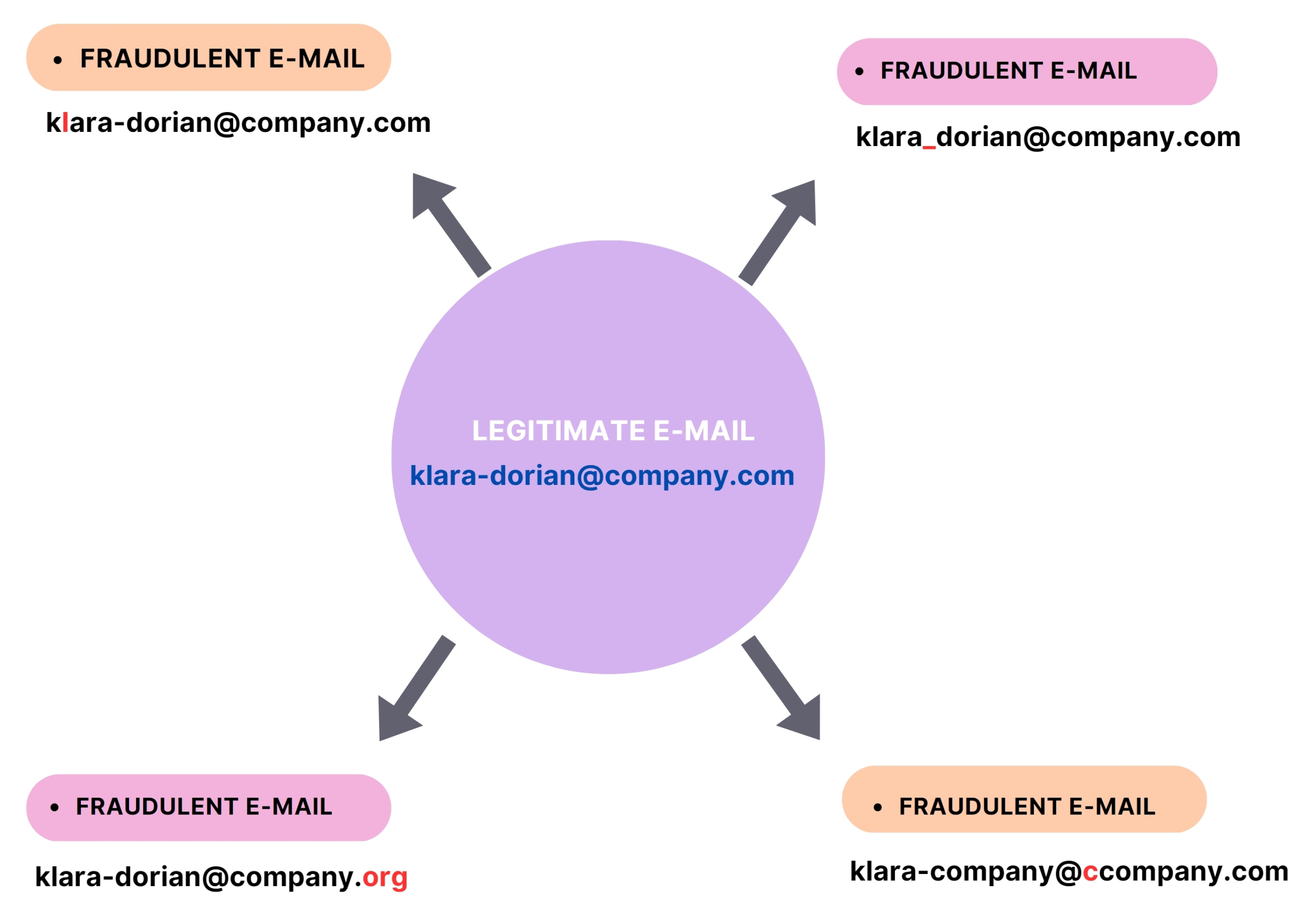
- Business Email Compromise Phishing: This term refers to scams that usually involve the compromise of legitimate business email accounts in order to deceive the victim to conduct unauthorized transfers of funds, giving confidential information [23,24], and in some cases, installing malware (such as keyloggers). An attacker often uses an address that may differ from that of the attacked organization by just one or two letters. For example, a scammer can replace a lowercase L (“l”) with a capital I (“I”), making it extremely difficult to distinguish with the naked eye [25] (Figure 8).
4. Methodology Strategies Preventing BEC Attacks
4.1. Prevention—Non Technical Methods
- Continuous employee training. Employees must be able to detect, report, and respond to a BEC attack. Sensitive departments of a company, such as the financial department, should be trained on a regular basis on social engineering techniques and BEC schemes. Employees must also be suspicious of hyperlinks, attachments, name misspellings, and last-minute directions on wire transfers or changed account details. The verification of the vendor’s info should also be encouraged. All the above should take place, keeping in mind that social engineering and BEC schemes are evolving; that is why continuous and updated training is needed.
- Adopting new and innovative training techniques. Content relevance with technologies can vary in a company, as it does in society in general. Someone should not expect a member of a company’s accounting department to have the same familiarity with computer technologies as an IT member. For that reason, innovative training techniques like thematic and game-based analysis techniques are essential for a better understanding of the dangers lurking in online communication ([26]).
- Formation of blue and red teams is strongly advised, especially for big companies. Blue teams are responsible for evaluating and defending security environments, while red teams are responsible for attacking these environments in order to detect vulnerabilities.
- Defining policies: Establish internal regulations, policies and guidelines requiring special protections for sharing information and for wire transfers or other financial transactions. Make sure that email requests for transferring funds are forbidden and that financial transactions will require the presence of several persons or at least a vocal confirmation. As for communication via phone, setting requirements—like identity verification questions—should be enforced to prevent unwanted data leaks. Establishment of reports when incidents occur should also be encouraged.
- Fraud risk evaluation: Conducting fraud risk evaluation can detect and prevent vulnerabilities that scammers can exploit. An example of the above mentioned is the fraud risk management guide published by the Committee of Sponsoring Organizations for the Treadway Commission (COSO) partnered with the Association of Certified Fraud Examiners (ACFE) and also the ISO 22380:2018.
- Perform regular real world checkups: Given the fact that the employees had undergone a thorough education about social engineering and BEC schemes, and given that those policies had been established, regular real-world checkups should be performed by professional partners like pentesters and social engineers.
- Establishment of a social engineering department: A department with employees trained in social engineering and Open Source Investigations (OSINTs) is a must have, especially for big companies. Employees can utilize OSINT tools to conduct investigations on high-profile targets within their own company. These tools enable them to explore potential data breaches and leaks by leveraging online services such as "Have I Been Pwned," which are offered by Dehashed’s online portal, a reputable organization headquartered on Market Street in San Francisco, CA, USA. All the above gathered information can be used by an attacker to d0x a target, so understanding the gaps and possible compromises in a company’s profile is crucial to prevent/detect future BEC attempts [27].
- Compose safe lists containing email addresses of a company’s employees.
4.2. Technical Methods
- Anti-spam and anti-malware software: Anti-spam software provides protection from spam and phishing attacks, while anti-malware software is able to detect malware. Both of the aforementioned attacks can be part of a BEC scheme.
- Time-of-click protection: This rewrites URLs in email messages and provides point-of-click protection using multiple reputation services [28].
- Executive tracking list: Uses details synched from an Active Directory to automatically detect users’ real names within header and envelope address fields [28].
- Nearby domains: Compares the sender domain to legitimate domain names to identify nearby domains, meaning domains that vary by one or two characters [28].
- Directory harvest attack (DHA) prevention: Drops an email destined for invalid or fake email addresses [28].
- Multi-factor authentication (MFA): MFA provides a valid means for authentication that requires two or more verification factors to gain access to a resource [29].
- Email protocols: confirm that email protocols are updated and ban old email protocols (POP, IMAP, STMP) that can be used to override MFA.
- DKIM: DomainKey Mail (DKIM) is a cryptographic method for email integrity checks and authentication. Emails are signed by the private key of the sending domain, and the receiver domain verifies the signature of the email using the public key of the sender domain available through DNS.
- SPF: Sender Policy Framework (SPF) provides validation of an email’s IP from a list of authorized IP addresses.
- DMARC authentication: Domain-based Message Authentication, Reporting and Conformance (DMARC) combines mechanisms that include DKIM and SPF, and it prevents attackers from spoofing the organization and domain [30]. Its main weakness is that DMARC processes only header information, and it is weak against impersonation.
- Encryption: Encryption can be used to prevent data breaches by requiring both the sender and receiver to have a pair of cryptographic keys.
- Verifiers: Using applications like an invoice verifier, which can scan a QR code on an invoice, provides a verification method that allows users to ensure the authenticity of the invoice attached in an email [31].
- Machine Learning (ML): machine learning technology, as part of the field of artificial intelligence, is composed by algorithms that can analyze email data to construct a model that can classify them and report any anomalies as red flags indicating BEC attempts [32].
- Supervised learning: The operator provides the machine learning algorithm with a known dataset that includes desired inputs and outputs, and the algorithm must find a method to determine how to arrive at those inputs and outputs. The algorithm tries to model relationships between the target output and the input features and match the operator’s results. This process continues until the algorithm achieves a high level of accuracy.
- Semi-supervised learning: Semi-supervised learning is similar to supervised learning in the way that it uses labeled data and is similar to unsupervised learning because it also uses unlabeled data. An operator can use a small amount of data to train a model to classify the rest of the unlabeled data in a dataset.
- Unsupervised learning: In this case, the algorithm studies data to identify patterns without the help of a human operator.
- Reinforcement learning: In reinforcement learning, an algorithm is provided with a set of actions, parameters and end values, but it must find the optimal action through its own experience. This method is based on rewarding desire behaviors and/or punishing undesired ones, meaning that the algorithm obtains the appropriate appraisal value of the environment state and revises its own strategy to adapt to the environment.
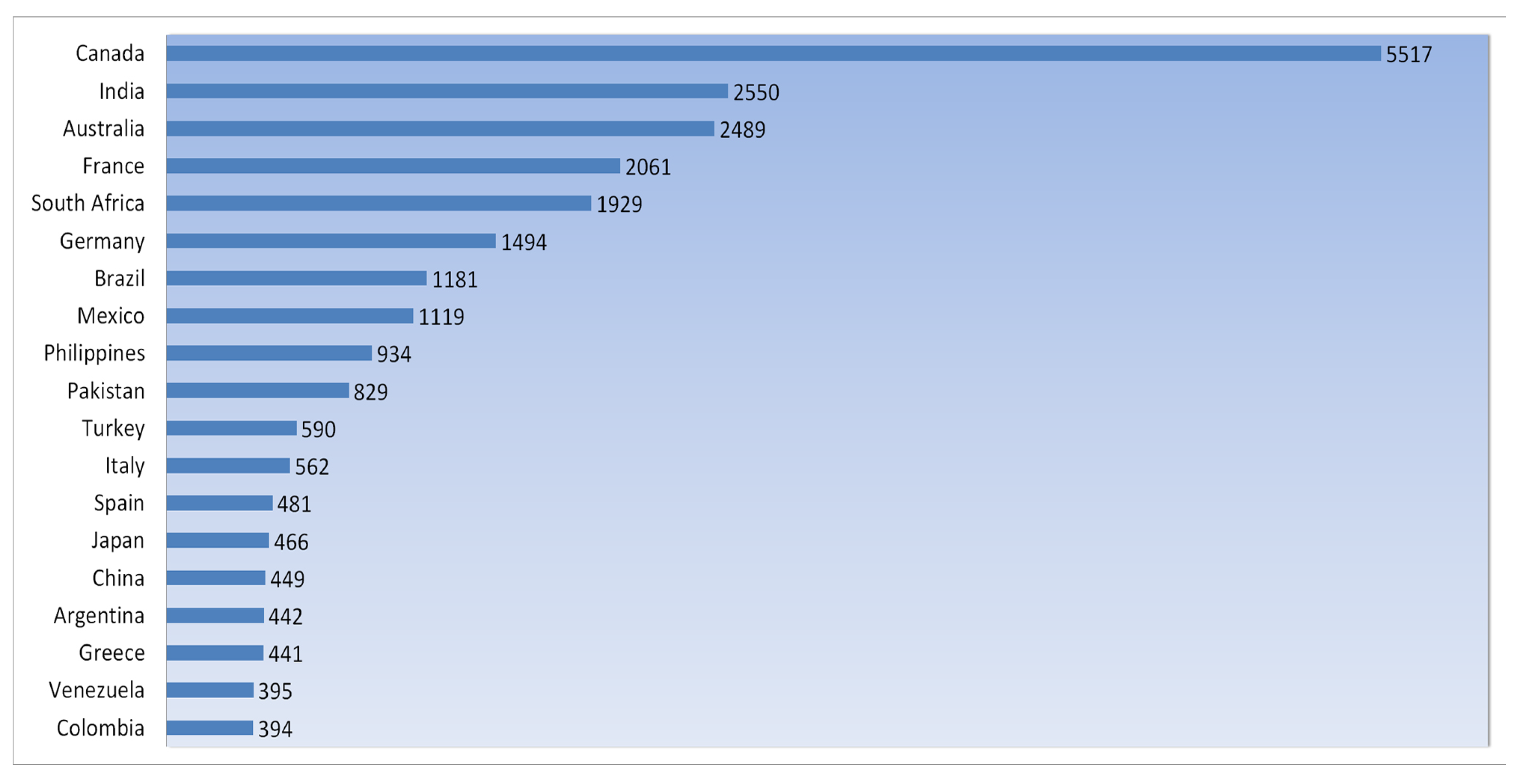
4.3. Detailed Description of BEC Prevention Procedures in Greek Landscape
4.4. Greek Departments Responsible for Cybersecurity and Cybercrime
4.4.1. Department of Administrative Support and Information Management
- Collection, study, analysis, evaluation and processing of information and data related to cases involving cybercrime. This department can also forward any processed data to the competent departments of the directorate for operational use.
- Investigating cases of suicide and cases of suicidal intent or disappearance via the internet.
- Provide assistance to relevant government agencies to prevent suicides reported online.
4.4.2. Department of Innovative Actions and Strategy
- The preparation of information programs for citizens and institutions for internet and electronic crime issues through the implementation of various actions, such as conferences, workshops and videoconferences, as well as the organization of other innovative actions in the field of combating electronic crime;
- Defining strategic planning issues regarding cybercrime;
- The promotion and publication of the social work of the service through the creation and management of profiles on social networking sites (Twitter, Facebook, etc.) for the purposes of citizens’ communication, information and awareness of issues of electronic threats and risks;
- The monitoring of developments in cybercrime issues, both domestically and internationally, the preparation of a relevant annual study with conclusions on the criminality of these offences in the country, and the submission of specific reasoned proposals to address them;
- The recording of actions and statistics regarding cybercrimes and their observance.
4.4.3. Department of Electronic and Telephone Communications Security and Software and Copyright Protection
- Handling cases of illegal infiltration in computer systems and theft, and the destruction or illicit trafficking of hardware, software, digital data and audiovisual works.
- To assist other competent authorities investigating such cases, in accordance with applicable laws.
- The provision of necessary technical assistance to other departments.
- Conducting digital and internet research using modern technological equipment.
- The analysis of digital data, files and other findings in criminal cases.
4.4.4. Department of Online Child Protection
- The detection and prosecution of crimes committed against minors through the use of the internet and other means of electronic or digital communication and storage.
- Investigating cases of online harassment (cyber bullying) in minors.
4.4.5. Department for the Prosecution of Online Financial Crimes
- Combating economic crimes against the financial interests of the state and the national economy, in cooperation with the Directorate of financial police and other competent national, European and foreign services and authorities.
- The investigation of financial cybercrimes, if specialized technical or digital research is required.
- Assisting government agencies in investigating cases involving virtual/digital currencies.
4.4.6. Department of Special Affairs and Digital Investigation
- The handling of serious and organized crime cases as well as conventional crimes committed via the internet, the investigation of which can only be carried out through specialized technical or digital research.
- The continuous investigation of the internet and other means of electronic communication and digital storage for the discovery, detection and prosecution of criminal offenses.
4.4.7. Computer Emergency Response Team (CERT)
- The security of national communication and information technology systems and the evaluation–certification of classified devices and systems concerning communication and IT.
- The evaluation–certification of crypto systems and supporting the Greek Army and the public sector in issues of crypto security.
- The security of national electronic communication devices.
- Preventing, warning and dealing with cyberattacks against the Governance and the Ministries (except for the Defense Ministry).
4.4.8. Hellenic Computer Security Incident Response Team (CSIRT)
4.4.9. National Cyber Security Authority (NCSA)
4.5. Legal Framework and Investigative Tools for Business Email Compromise Cases/Crimes
4.5.1. National Legal and Regulatory Framework for Preventing, Combating and Prosecuting Business Email Compromise Cases/Crimes
4.5.2. Legal Tools for Investigation of Business Email Compromise Cases/Crimes and International Cooperation
Removal of the Confidentiality of Communications/Lawful Interception
Tracing the Money Route
Disclosing Information about Malicious Users in the EU
Join Investigation Teams (JITs) in EU
Disclosing Information about Malicious Users Outside EU
4.6. Procedures after a BEC Attack
- Contacting law enforcement (in the case of Greece, the Unit of Special Cases and Internet Economic Crimes Prosecution) and other competent authorities as soon as possible.
- Immediately informing the banking institute via phone and then through a Transaction Dispute Form.
- Providing the authorities dealing with the case with evidence like:
- –
- Email addresses, email headers, and associated Internet Protocol (IP) addresses with their respective timestamps.
- –
- A description and timing of suspicious email communications.
- –
- Phone numbers.
- –
- Wire transfer details:
- ∗
- Dates and amounts of suspicious transactions.
- ∗
- The sender’s identifying information, account number and financial institution.
- ∗
- The beneficiary’s identifying information, account number and financial institution.
- ∗
- The correspondent and intermediary financial institution’s information, if applicable.
- Obtaining a copy of the emails and performing the following steps:
- –
- Initiating the investigation process by requesting information from the victim’s email provider (if applicable). This entails:
- ∗
- IMAP (Internet Message Access Protocol)—The emails must remain on the server. A copy of the emails should be obtained from the email provider via the legal process or from the victim’s server.
- ∗
- POP (Post Office Protocol)—Emails are downloaded from the email provider to the victim’s computer. Emails are not located on an external server and must be obtained from the victim’s computer.
- ∗
- An investigation for spear phishing attacks from what appears to be legitimate vendors (slight changes in email address) and for additional communications with the misspelled domain.
- ∗
- An investigation for indications of out-of-band communication changes (e.g., phone number).
- ∗
- An investigation for possible email redirect rule.
- ∗
- Running a PowerShell command across the network looking for forwarding rules because more than one computer may be affected.
- –
- Forensic Analysis of the computer:
- ∗
- Malware may have been used to harvest email credentials (allowing access to the email account). The use of malware may or may not be contemporaneous with the BEC. Often, access to the email account occurs weeks/months prior to the BEC.
- ∗
- An analysis of the victim’s computer/system, even though it does not generally lead to direct information of the transfer of funds (usually provides information on how the email credentials were compromised).
4.7. NIS Directive and Greek Compliance
- Each member state is obliged to participate with representatives in the Cooperation Group and the CSIRT network.
- Each member state is obliged to establish a national strategy for the security of networks and information systems in order to achieve a high level of security that keeps up with the current technological advances and challenges.
- Each member state must designate one or more national competent authorities for the security of networks and information systems.
- Each member state is obliged to appoint one or more CSIRTs responsible for managing risks and handling incidents.
- Member States are obligated to establish regulations regarding penalties for violations of national provisions enacted under this directive and must undertake all necessary actions to ensure their enforcement. The prescribed penalties should be impactful and fair and should serve as a deterrent.
- Member states are required to identify, by November 2018, the entities operating essential services.
- Starting in August 2018, and subsequently on an annual basis, it is mandatory to submit a summary report of the notifications received by the Cooperation Group.
- The National Cyber Security Authority (NCSA) was established by the Presidential Decree of 82/2017, along with the Single Point of Contact under the Ministry of Digital Policy, Telecommunications and Media (now Ministry of Digital Governance).
- The NCSA represents Greece in the Cooperation Group and the National CERT in the CSIRT network of the EU.
- A National Cyber Security Strategy was published in 2018 [45].
- Greek Parliament enacted Law 4577/2018, establishing the national cybersecurity plan and cybersecurity authority in the Ministry of Digital Policy, Telecommunications and Media (now Ministry of Digital Governance) and also setting a range of network and information security requirements for the Operators of Essential Services (OESs) and Digital Service Providers (DSPs).
- Law 4577/2018 also defined the penalties in case of non-compliance.
- The first Annual Report NIS Directive Incidents 2019 was published in December 2020 [46].
- Adding new sectors based on their criticality for the economy and society and introducing a clear size cap—meaning that all medium and large companies in selected sectors will be included.
- The removal of the differentiation between operators of essential services and digital service providers involves classifying entities based on their significance and dividing them into categories of “essential” and “important.” This classification would result in subjecting them to distinct supervisory regimes.
- Enhanced security requirements for companies by implementing a risk management approach that mandates the application of a minimum list of fundamental security elements. This introduces more specific provisions regarding the incident reporting process, including the content of the reports and the required timelines.
- Emphasis of the importance of secure supply chains and supplier relationships by mandating that individual companies address cybersecurity risks within their supply chains and supplier relationships. At the European level, this enhances supply chain cybersecurity measures for important information and communication technologies. In collaboration with the Commission and ENISA, Member States will conduct synchronized risk assessments of critical supply chains.
- Implementation of stricter oversight measures for national authorities, the imposing of more rigorous enforcement requirements, and the aim to standardize sanction regimes among member states.
- The strengthening of the influence of the Cooperation Group in shaping strategic policy decisions concerning emerging technologies. It promotes greater information sharing and cooperation among authorities of member states. Additionally, it improves operational collaboration, particularly in the realm of cyber crisis management.
- The establishment of a fundamental framework to facilitate coordinated vulnerability disclosure for recently identified vulnerabilities throughout the EU. This also establishes an EU registry for this task, which will be operated by the European Union Agency for Cybersecurity (ENISA) [48].
- The requirement that member states must adopt national cybersecurity strategies and designate or establish competent authorities, cyber crisis management authorities, single points of contact for cybersecurity (single points of contact), and computer security incident response teams (CSIRTs).
- Requirements for entities in terms of managing cybersecrurity risks for the following sectors: energy, transportation, banking, financial market infrastructures, health, drinking water, waste water, digital infrastructures, public administration, space, postal and courier services, waste management, manufacture production and distribution of chemicals, manufacture production and distribution of food, manufacturing, digital providers, and research.
- Regulations and responsibilities regarding the sharing of cybersecurity information.
- Obligations for member states in terms of supervision and enforcement.
- The establishment of the European Cyber Crisis Liaison Organization Network (EU-CyCLONe), which aims to facilitate the coordinated handling of significant cybersecurity incidents and crises. This also ensures the consistent exchange of information between member states and various union institutions, bodies, offices, and agencies.
- Specifies the overall criteria for imposing administrative fines on entities classified as essential and important.
- Identify information and cybersecurity risks.
- Establish technical control measures to manage or mitigate the risks of Business Email Compromise, such as employing strong authentication practices, setting up multifactor authentication (MFA) to add an extra layer of security, restricting editing and signing rights, organizing security training for employees, setting up email filters and blocks, verifying all payment requests, monitoring email accounts, using encryption and secure communication channels, and keeping software and security measures up to date.
- Implement procedures for the prompt detection of business email compromise attacks.
- Recover business operations following an incident like Business Email Compromise.
5. Results
6. Future Work
7. Discussion and Conclusions
Author Contributions
Funding
Data Availability Statement
Acknowledgments
Conflicts of Interest
Appendix A
| NIS 2 | ISO 27001:2022 |
|---|---|
| Article 21.2 (a) Policies on risk analysis and information system security | 5.2 Policy |
| 6.1.2 Information security risk assessment | |
| 6.1.3 Information security risk treatment | |
| 8.2 Information security risk assessment | |
| 8.3 Information security risk treatment | |
| Annex A. Information security controls reference: | |
| 5.1 Policies for information security | |
| Article 21.2 (b) Incident handling | Annex A. Information security controls reference: |
| 5.24 Information security incident management planning and preparation | |
| 5.25 Assessment and decision on information security events | |
| 5.26 Response to information security incidents | |
| 5.27 Learning from information security incidents | |
| 5.28 Collection of evidence | |
| 6.8 Information security event reporting | |
| Article 21.2 (c) Business continuity, such as backup management and disaster recovery, and crisis management | Annex A. Information security controls reference: |
| 5.29 Information security during disruption | |
| 5.30 ICT readiness for business continuity | |
| 8.13 Information backup | |
| 8.14 Redundancy of information processing facilities | |
| Article 21.2 (d) Supply chain security, including security related aspects concerning the relationships between each entity and its direct suppliers or service providers | Annex A. Information security controls reference: |
| 5.19 Information security in supplier relationships | |
| 5.20 Addressing information security within supplier agreements | |
| 5.21 Managing information security in the ICT supply chain | |
| 5.22 Monitoring, review and change management of supplier services | |
| 5.23 Information security for use of cloud services | |
| Article 21.2 (e) Security in network and information systems acquisition, development and maintenance, including vulnerability handling and disclosure | Annex A. Information security controls reference: |
| 5.37 Documented operating procedures | |
| 8.8 Management of technical vulnerabilities | |
| 8.9 Configuration management | |
| 8.20 Network security | |
| 8.21 Security of network services | |
| Article 21.2 (f) Policies and procedures to assess the effectiveness of cybersecurity risk management measures | 9.1 Monitoring, measurement, analysis and evaluation |
| 9.2 Internal audit | |
| 9.3 Management review | |
| Annex A. Information security controls reference: | |
| 5.35 Independent review of information security |
References
- Saud Al-Musib, N.; Mohammad Al-Serhani, F.; Humayun, M.; Jhanjhi, N. Business email compromise (BEC) attacks. Mater. Today Proc. 2021, 81, 497–503. [Google Scholar] [CrossRef]
- Europol. Internet Organized Crime Threat Assessment Report. 2020. Available online: https://www.europol.europa.eu/publications-events/main-reports/internet-organised-crime-threat-assessment-iocta-2020 (accessed on 25 April 2023).
- Amer, E.; Zelinka, I.; El-Sappagh, S. A Multi-Perspective malware detection approach through behavioral fusion of API call sequence. Comput. Secur. 2021, 110, 102449. [Google Scholar] [CrossRef]
- Europol. Internet Organized Crime Threat Assessment Report. 2021. Available online: https://www.europol.europa.eu/publications-events/main-reports/internet-organised-crime-threat-assessment-iocta-2021 (accessed on 25 April 2023).
- Kaspersky. Separated by a Common Language: Is the C-Suite Able to Truly Decipher and Act upon the Real Threat of Cyber-Attacks? 2022. Available online: https://go.kaspersky.com/rs/802-IJN-240/images/Kaspersky-Speaks-your-Language-1122.pdf (accessed on 25 April 2023).
- Maleki, N. A Behavioral Based Detection Approach for Business Email Compromises. 2019. Available online: https://unbscholar.lib.unb.ca/islandora/object/unbscholar%3A10122 (accessed on 25 April 2023).
- FBI. Business Email Compromise and Real Estate Wire Fraud. 2022. Available online: https://www.fbi.gov/file-repository/fy-2022-fbi-congressional-report-business-email-compromise-and-real-estate-wire-fraud-111422.pdf/view (accessed on 25 April 2023).
- FBI. Internet Crime Report. 2022. Available online: https://www.ic3.gov/Media/PDF/AnnualReport/2022IC3Report.pdf (accessed on 25 April 2023).
- European Union Agency for Cybersecurity. ENISA Threat Landscape 2022: July 2021 to July 2022; Publications Office: Luxembourg, 2022. [Google Scholar] [CrossRef]
- 2022 Data Breach Investigations Report. 2022. Available online: https://www.verizon.com/business/resources/reports/dbir/ (accessed on 25 April 2023).
- Cloudflare. Cloudflare Security Report. 2021. Available online: https://www.cloudflare.com/resources/assets/slt3lc6tev37/1vmmNMaaktXDk5iHxxDdCj/ebe40635588eaafa15ab89944ff9a36b/Cloudflare_Impact_Report_2021.pdf (accessed on 25 April 2023).
- Cloudflare. Cloudflare Security Report. 2022. Available online: https://cf-assets.www.cloudflare.com/slt3lc6tev37/4sivQSVRKbmDGL6VqSLLmM/3f62dd0c9dd7534ca9b43d012ddd8635/CloudflareArea1Whitepaper-HowtoStopBusinessEmailCompromiseMay2022.pdf (accessed on 25 April 2023).
- Remorin, L.; Flores, R.; Matsukawa, B. Tracking Trends in Business Email Compromise (BEC) Schemes. 2018. Available online: https://documents.trendmicro.com/assets/TrackingTrendsinBusinessEmailCompromise.pdf (accessed on 25 April 2023).
- Jakobbson, M. (Ed.) Understanding Social Engineering Based Scams; Springer: New York, NY, USA, 2016. [Google Scholar]
- Krombholz, K.; Hobel, H.; Huber, M.; Weippl, E. Advanced social engineering attacks. J. Inf. Secur. Appl. 2015, 22, 113–122. [Google Scholar] [CrossRef]
- Hadnagy, C. Social Engineering: The Science of Human Hacking, 2nd ed.; John Wiley & Sons, Inc.: Indianapolis, IN, USA, 2018. [Google Scholar]
- Chapple, M.; Stewart, J.M.; Gibson, D. (ISC)² CISSP Certified Information Systems Security Professional Official Study Guide, 9th ed.; John Wiley and Sons: Indianapolis, IN, USA, 2021. [Google Scholar]
- Edwards, M.; Peersman, C.; Rashid, A. Scamming the Scammers: Towards Automatic Detection of Persuasion in Advance Fee Frauds. In Proceedings of the 26th International Conference on World Wide Web Companion—WWW ’17 Companion, Perth, Australia, 3–7 April 2017; pp. 1291–1299. [Google Scholar] [CrossRef]
- Abraham, S.; Chengalur-Smith, I. An overview of social engineering malware: Trends, tactics, and implications. Technol. Soc. 2010, 32, 183–196. [Google Scholar] [CrossRef]
- Mitnick, K.D.; Simon, W.L. The art of Deception: Controlling the Human Element of Security; Wiley: Indianapolis, IN, USA, 2002. [Google Scholar]
- Peltier, T.R. Social Engineering: Concepts and Solutions. Inf. Syst. Secur. 2006, 15, 13–21. [Google Scholar] [CrossRef]
- Salahdine, F.; Kaabouch, N. Social Engineering Attacks: A Survey. Future Internet 2019, 11, 89. [Google Scholar] [CrossRef]
- Opazo, B.; Whitteker, D.; Shing, C.C. Email trouble: Secrets of spoofing, the dangers of social engineering, and how we can help. In Proceedings of the 2017 13th International Conference on Natural Computation, Fuzzy Systems and Knowledge Discovery (ICNC-FSKD), Guilin, China, 29–31 July 2017; pp. 2812–2817. [Google Scholar] [CrossRef]
- Bakarich, K.M.; Baranek, D. Something Phish-y is Going On Here: A Teaching Case on Business Email Compromise. Curr. Issues Audit. 2020, 14, A1–A9. [Google Scholar] [CrossRef]
- Kaspersky. Fighting Business Email Compromise with Kaspersky Security for Microsoft Office 365. 2020. Available online: https://www.kaspersky.com/office365-security (accessed on 25 April 2023).
- Yasin, A.; Fatima, R.; Liu, L.; Yasin, A.; Wang, J. Contemplating social engineering studies and attack scenarios: A review study. Secur. Priv. 2019, 2, e73. [Google Scholar] [CrossRef]
- Bazzell, M. Open Source Intelligence Techniques: Resources for Searching and Analyzying Online Information, 9th ed.; Amazon Digital Services: London, UK, 2022. [Google Scholar]
- Bitdefender. GravityZone Email Security Repor. 2019. Available online: https://www.bitdefender.com/content/dam/business/b2b/white-papers/Bitdefender-GravityZone-Email-Security-Report.pdf (accessed on 25 April 2023).
- Ometov, A.; Bezzateev, S.; Mäkitalo, N.; Andreev, S.; Mikkonen, T.; Koucheryavy, Y. Multi-Factor Authentication: A Survey. Cryptography 2018, 2, 1. [Google Scholar] [CrossRef]
- Derouet, E. Fighting phishing and securing data with email authentication. Comput. Fraud. Secur. 2016, 2016, 5–8. [Google Scholar] [CrossRef]
- Teerakanok, S.; Yasuki, H.; Uehara, T. A Practical Solution Against Business Email Compromise (BEC) Attack using Invoice Checksum. In Proceedings of the 2020 IEEE 20th International Conference on Software Quality, Reliability and Security Companion (QRS-C), Macau, China, 11–14 December 2020; pp. 160–167. [Google Scholar] [CrossRef]
- Awad, W. Machine Learning Methods for Spam E-Mail Classification. Int. J. Comput. Sci. Inf. Technol. 2011, 3, 173–184. [Google Scholar] [CrossRef]
- Choi, R.Y.; Coyner, A.S.; Kalpathy-Cramer, J.; Chiang, M.F.; Campbell, J.P. Introduction to Machine Learning, Neural Networks, and Deep Learning. Transl. Vis. Sci. Technol. 2020, 9, 14. [Google Scholar] [CrossRef]
- Atlam, H.F.; Oluwatimilehin, O. Business Email Compromise Phishing Detection Based on Machine Learning: A Systematic Literature Review. Electronics 2023, 12, 42. [Google Scholar] [CrossRef]
- Cidon, A.; Gavish, L.; Bleier, I.; Korshun, N.; Schweighauser, M.; Tsitkin, A. High Precision Detection of Business Email Compromise. In Proceedings of the 28th USENIX Security Symposium (USENIX Security 19), Santa Clara, CA, USA, 14–16 August 2019; pp. 1291–1307. [Google Scholar]
- Police, H. Cyber Crime Division. Available online: https://www.astynomia.gr/hellenic-police/special-services/cyber-crime-division/?lang=en (accessed on 25 April 2023).
- Available online: https://csirt.cd.mil.gr/el/phishing-gr/ (accessed on 25 April 2023).
- Concordia. National Cyber Security Authority – Ministry of Digital Governance (NCSA). Available online: https://www.concordia-h2020.eu/consortium/national-cyber-authority-ncsa/ (accessed on 25 April 2023).
- Papathanasiou, A.; Germanos, G. The phenomenon of crime-as-a-service for the violent crimes in Dark Web. Criminology 2017, 1, 40. [Google Scholar]
- Egmont Group Bulletin. Business Email Compromise Fraud. Available online: https://egmontgroup.org/wp-content/uploads/2021/09/2019_Egmont_Group_Bulletin_Business_Email_Compromise_Fraud.pdf (accessed on 25 April 2023).
- Ali, M.; Kaur, S. Next-Generation Digital Forensic Readiness BYOD Framework. Secur. Commun. Netw. 2021, 2021, 6664426. [Google Scholar] [CrossRef]
- Carvalho, J.A.V.; Carvalho, S.; Rocha, A. European Strategy and Legislation for Cybersecurity: Implications for Portugal. Clust. Comput. 2020, 23, 1845–1854. [Google Scholar] [CrossRef]
- Directive (EU) 2016/1148 of the European Parliament and of the Council of 6 July 2016 Concerning Measures for a High Common Level of Security of Network and Information Systems across the Union. Available online: https://eur-lex.europa.eu/legal-content/EN/TXT/?uri=celex:32016L1148 (accessed on 25 April 2023).
- Maglaras, L.; Drivas, G.; Noou, K.; Rallis, S. NIS directive: The case of Greece. EAI Endorsed Trans. Secur. Saf. 2018, 4, e1. [Google Scholar] [CrossRef][Green Version]
- Greek Government Gazette. Decision No. DIDAD/F.11/36/29542/1390. 2019. Available online: https://diavgeia.gov.gr/doc/%CE%A84%CE%A17465%CE%A7%CE%980-%CE%966%CE%A9?inline=true (accessed on 25 April 2023).
- NIS Cooperation Group. Annual Report NIS Directive Incidents 2019; NIS Cooperation Group, European Commission: Brussels, Belgium, 2020. [Google Scholar]
- Cybersecurity in the EU: Overview of Challenges and State of Play. 2021. Available online: https://www.europarl.europa.eu/RegData/etudes/BRIE/2021/689333/EPRS_BRI(2021)689333_EN.pdf (accessed on 25 April 2023).
- Proposal for a Directive on Measures for a High Common Level of Cybersecurity across the UNION. Available online: https://digital-strategy.ec.europa.eu/en/library/proposal-directive-measures-high-common-level-cybersecurity-across-union (accessed on 25 April 2023).
- Parliament, E. Directive (EU) 2022/2555 of the European Parliament and of the Council of 21 March 2022 laying down measures for a high common level of cybersecurity across the Union. Off. J. Eur. Union 2022, 1–87. Available online: https://eur-lex.europa.eu/legalcontent/136EN/TXT/PDF/?uri=CELEX:32022L2555 (accessed on 25 April 2023).
- Fuster, G.G.; Jasmontaite, L. Cybersecurity Regulation in the European Union: The Digital, the Critical and Fundamental Rights. In The Ethics of Cybersecurity; Christen, M., Gordijn, B., Loi, M., Eds.; Springer International Publishing: Cham, Switzerland, 2020; pp. 97–115. [Google Scholar] [CrossRef]
- Krüger, P.; Brauchle, J.P. The European Union, Cybersecurity, and the Financial Sector: A Primer. Carnegie Endowment for International Peace, March 2021, Massachusetts Avenue NW, Washington, U.S. Available online: https://carnegieendowment.org/files/Krueger_Brauchle_Cybersecurity_legislation.pdf (accessed on 25 April 2023).





| Victim | Loss | Year | What Happened |
|---|---|---|---|
| Facebook and Google | $123 Million | 2019 | A Lithuanian scammer impersonated Quanta Computer, an electronics supplier for Facebook and Google. Facebook and Google paid $123 million in fake invoices to the scammer. |
| Crelan Bank | $75.8 Million | 2016 | Belgian-based Crelan Bank lost over €70 million (roughly $75.8 milllion) to fraudsters who compromised the CEO’s email account. The attack was later discovered in an internal audit. |
| Toyota Subsidiary | $37 Million | 2019 | A European subsidiary of the Toyota Boshoku Corporation(subsidiary of the Toyota Group) was duped into transferring approximately $37 billion in a BEC scam |
| Scoular | $17.2 Million | 2014 | US commodities trading company Scolar wired $17.2 million to a fraudulent offshore account after receiving a fake email from the CEO. |
| Mattel | $ 3 Milllion (recovered) | 2016 | A financial executive at Mattel transferred $3 million to a fraudulent account after receiving a spoofed email appearing to be from the CEO. |
| Departments | Legal Tools |
|---|---|
| Greek Cyber Crime Division (GCCD) | Removal of the confidentiality of communications/lawful interception |
| Tracing the money route | |
| Disclosing information about malicious users in the EU | |
| Join Investigation Teams (JITs) in the EU | |
| Disclosing information about malicious users outside the EU | |
| Computer Emergency Response Team (CERT) | Removal of the confidentiality of communications/lawful interception |
| Disclosing information about malicious users in the EU | |
| Disclosing information about malicious users outside the EU | |
| Hellenic Computer Security Incident Response Team (CSIRT) | Disclosing information about malicious users in the EU |
| Disclosing information about malicious users outside the EU | |
| National Cyber Security Authority (NCSA) | Disclosing information about malicious users in the EU |
| Disclosing information about malicious users outside the EU |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Papathanasiou, A.; Liontos, G.; Liagkou, V.; Glavas, E. Business Email Compromise (BEC) Attacks: Threats, Vulnerabilities and Countermeasures—A Perspective on the Greek Landscape. J. Cybersecur. Priv. 2023, 3, 610-637. https://doi.org/10.3390/jcp3030029
Papathanasiou A, Liontos G, Liagkou V, Glavas E. Business Email Compromise (BEC) Attacks: Threats, Vulnerabilities and Countermeasures—A Perspective on the Greek Landscape. Journal of Cybersecurity and Privacy. 2023; 3(3):610-637. https://doi.org/10.3390/jcp3030029
Chicago/Turabian StylePapathanasiou, Anastasios, George Liontos, Vasiliki Liagkou, and Euripidis Glavas. 2023. "Business Email Compromise (BEC) Attacks: Threats, Vulnerabilities and Countermeasures—A Perspective on the Greek Landscape" Journal of Cybersecurity and Privacy 3, no. 3: 610-637. https://doi.org/10.3390/jcp3030029
APA StylePapathanasiou, A., Liontos, G., Liagkou, V., & Glavas, E. (2023). Business Email Compromise (BEC) Attacks: Threats, Vulnerabilities and Countermeasures—A Perspective on the Greek Landscape. Journal of Cybersecurity and Privacy, 3(3), 610-637. https://doi.org/10.3390/jcp3030029






