Deceptive Waypoint Sequencing Based UAV–UAV Interception Control Using DBSCAN Learning Strategy
Abstract
1. Introduction
- 1.
- This is the first research to integrate a multi-target grouping scheme based on DBSCAN for coordinating defenses against UAV attackers that are spatially distributed with sliding-mode control and backstepping for an UAV–UAV attacker–defender interception strategy and robust trajectory tracking for interception.
- 2.
- In contrast to the research in [13], in this work a novel deceptive route point strategy is incorporated for defender paths that deceive attacking UAVs. The attackers are non-reactive and do not have access to the defender’s internal reference-switching and waypoint sequencing logic.
- 3.
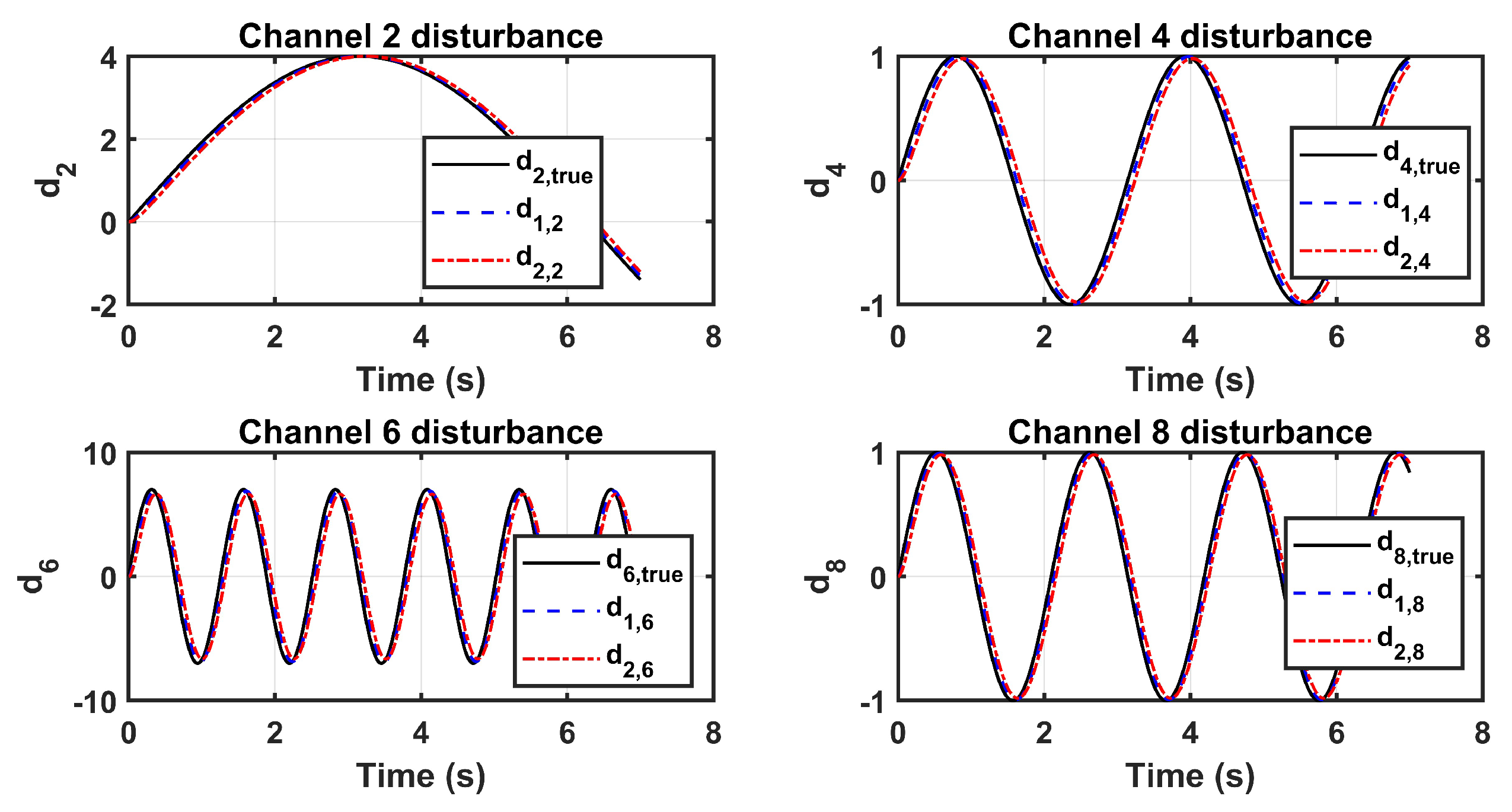
- A robust sliding-mode backstepping controller with an extended state observer (ESO) is incorporated for defender UAVs to accurately intercept cluster centroids under time-varying disturbances.
- 4.
- This work employs the Lyapunov stability analysis method to guarantee the interception of attackers by UAV defenders and the stability of the system states.
2. Problem Formulation
3. UAV–UAV Deceptive Waypoint Interception Design Using DBSCAN Learning
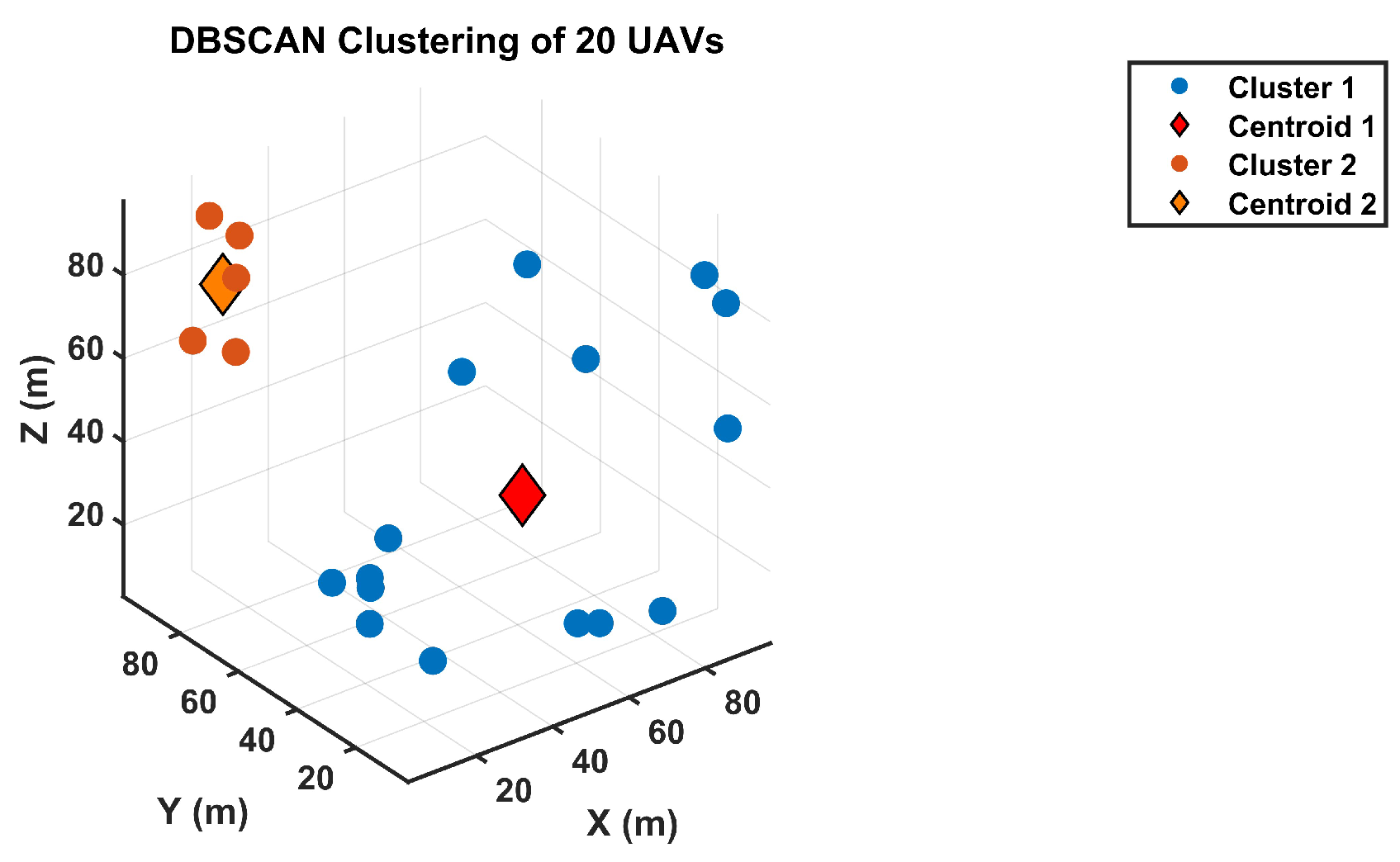
3.1. Clustering Overview
3.2. DBSCAN Clustering
- represents the set of all attacking UAVs;
- denotes the cluster a (i.e., a group of attackers identified as a dense region);
- Clustering is performed based on the attackers’ positions and velocities .
- : the neighborhood radius defining spatial proximity;
- MinPts: the minimal quantity of adjacent points necessary to define a dense area.
- A core point if ;
- A border point if it lies within of a core point but has fewer than MinPts neighbors;
- A noise point if it is neither a core nor a border point.
3.2.1. Computational Complexity Analysis of DBSCAN Clustering
- Neighborhood query: For every point, the algorithm retrieves all neighboring points within distance . The computational cost of this step depends on the data structure used:
- -
- Using a naive linear search: ;
- -
- Using an optimized spatial index (e.g., k-d tree or ball tree): .
- Cluster expansion: Once a core point is identified (), DBSCAN recursively expands its cluster by visiting all density-reachable points. This operation, in the worst-case scenario, requires visiting all M points once, resulting in complexity.
3.2.2. Scalability Analysis of DBSCAN
3.2.3. Sensitivity Analysis
3.3. Deceptive Waypoint Sequencing (DWS) for UAV–UAV Interception
3.3.1. Feasibility, Safety, and Smoothness Constraints
- Radial and vertical bounds:
- Inter-waypoint displacement and curvature: for ,
- Safety:where is the free-space set (no-fly zones excluded).
- Timing and derivative bounds: Given waypoint times , the smoothed reference must satisfy
3.3.2. Risk Activation and Switching
3.3.3. Assigning UAV Defenders to Clusters of UAV Attackers Based on DWS
3.4. Defender UAV Model for DWS UAV Interception
- Rotational subsystem : the states correspond to the attitude angles and correspond to the corresponding angular rates . The expressions for , , and include the gyroscopic/cross-inertia coupling terms parameterized by and are driven by the torque inputs , , and .
- Translational subsystem : the states correspond to inertial positions and correspond to the associated linear velocities . The expressions for , , and include drag terms parameterized by and are driven by the total thrust projected via the direction-cosine terms and .
- The coefficients and (as defined in Equation (10) and the inertia-related expressions in Equation (11)) therefore map explicitly to the appropriate rotational/translational states.
3.5. Control
| Algorithm 1: DWS Interception Algorithm using DBSCAN |
 |
- Step (surface )
- Step (surface )
- Step (surface )
- Step (surface )
- Step (surface )
- Step (surface )
4. Simulation Results
5. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Fu, C.H.; Tsao, M.W.; Chi, L.P.; Zhuang, Z.Y. On the dominant factors of Civilian-Use drones: A thorough study and analysis of cross-group opinions using a triple helix model (THM) with the Analytic Hierarchy Process (AHP). Drones 2021, 5, 46. [Google Scholar] [CrossRef]
- Hoseini, S.A.; Hassan, J.; Bokani, A.; Kanhere, S.S. Trajectory optimization of flying energy sources using q-learning to recharge hotspot uavs. In Proceedings of the IEEE INFOCOm 2020—IEEE Conference on Computer Communications Workshops (INFOCOm WKSHPS), Virtual, 6–9 July 2020; IEEE: Piscataway, NJ, USA, 2020; pp. 683–688. [Google Scholar]
- Restas, A. Drone applications for supporting disaster management. World J. Eng. Technol. 2015, 3, 316–321. [Google Scholar] [CrossRef]
- Garg, P.; Chakravarthy, A.S.; Mandal, M.; Narang, P.; Chamola, V.; Guizani, M. Isdnet: Ai-enabled instance segmentation of aerial scenes for smart cities. ACM Trans. Internet Technol. 2021, 21, 1–18. [Google Scholar] [CrossRef]
- Ana-Raluca, S.T.A.N. Drones—A Threat to Security? In Proceedings Strategies XXI-International Scientific Conference the Complex and Dynamic Nature of the Security Environment, 21st ed.; Carol I National Defence University Publishing House: Bucharest, Romania, 2025; pp. 202–213. [Google Scholar]
- Kreps, S.E.; Rogers, J.P. Drones: What Everyone Needs to Know®; Oxford University Press: Oxford, UK, 2025. [Google Scholar]
- da Cruz, J.D.A. Criminal Drone Evolution: Cartel Weaponization of Aerial IEDs ed. by Robert J. Bunker & John P. Sullivan. J. Glob. South Stud. 2022, 39, 436–440. [Google Scholar] [CrossRef]
- Ivascu, L.N.; Jahankhani, H. An Investigation into Counter Drones Digital Forensics Aided by Remote Identification. In Space Governance: Challenges, Threats and Countermeasures; Springer Nature: Cham, Switzerland, 2024; pp. 195–227. [Google Scholar]
- Khawaja, W.; Semkin, V.; Ratyal, N.I.; Yaqoob, Q.; Gul, J.; Guvenc, I. Threats from and Countermeasures for UAVs and UUVs. Sensors 2022, 22, 3896. [Google Scholar] [CrossRef]
- Coluccia, A.; Parisi, G.; Fascista, A. Detection and Classification of Multirotor Drones in Radar Sensor Networks: A Review. Sensors 2020, 20, 4172. [Google Scholar] [CrossRef]
- Aouladhadj, D.; Kpre, E.; Deniau, V.; Kharchouf, A.; Gransart, C.; Gaquière, C. Drone Detection and Tracking Using RF Identification Signals. Sensors 2023, 23, 7650. [Google Scholar] [CrossRef]
- Castrillo, V.U.; Manco, A.; Pascarella, D.; Gigante, G. A Review of Counter-UAS Technologies for Cooperative Defensive Teams of Drones. Drones 2022, 6, 65. [Google Scholar] [CrossRef]
- Abubakar, A.N.; Nasir, A.; Saif, A.W.A. Sliding Mode Based Backstepping Control for UAV-UAV Interception Strategy with K-Mean Clustering. Int. J. Intell. Robot. Appl. 2025. [Google Scholar] [CrossRef]
- Zhang, Z.; Wang, F.; Guo, Y.; Hua, C. Multivariable Sliding Mode Backstepping Controller for Quadrotor UAV Based on Disturbance Observer. Sci. China Inf. Sci. 2018, 61, 112207. [Google Scholar] [CrossRef]
- Ram, A.; Jalal, S.; Jalal, A.S.; Kumar, M. A density based algorithm for discovering density varied clusters in large spatial databases. Int. J. Comput. Appl. 2010, 3, 1–4. [Google Scholar] [CrossRef]
- Chen, Y.; Wang, Y. Group Target Tracking for Highly Maneuverable UAV Swarms: A Perspective. Sensors 2023, 23, 4465. [Google Scholar] [CrossRef]
- Abir, T.A.; Le, V.; Kuantama, E.; Gupta, P.S.; Copley, A.; Dawes, J.; Islam, M.; Han, R.; Nguyen, P. Detection and Tracking of Drone Swarms using LiDAR. In Proceedings of the 23rd Annual International Conference on Mobile Systems, Applications and Services, Anaheim, CA, USA, 23–27 June 2025; pp. 500–514. [Google Scholar]
- Rahman, M.H.; Sejan, M.A.S.; Aziz, M.A.; Tabassum, R.; Baik, J.I.; Song, H.K. A comprehensive survey of unmanned aerial vehicles detection and classification using machine learning approach: Challenges, solutions, and future directions. Remote Sens. 2024, 16, 879. [Google Scholar] [CrossRef]
- Chi, Y.; Dong, Y.; Zhang, L.; Qiu, Z.; Zheng, X.; Li, Z. Collaborative Control of UAV Swarms for Target Capture Based on Intelligent Control Theory. Mathematics 2025, 13, 413. [Google Scholar] [CrossRef]
- Wang, J.; Zhao, L.; Xia, K.; Wang, C. Discrete-Time Net Capture Against an Intruder Using Multiple UAVs. IEEE Trans. Aerosp. Electron. Syst. 2024, 61, 2094–2105. [Google Scholar] [CrossRef]
- Xu, R.; Peng, Q.; Wu, H. Optimization Design of Flexible Net Capture System for Low, Slow, and Small Unmanned Aerial Vehicles Based on Improved Multi-Objective Wolf Pack Algorithm. Drones 2025, 9, 190. [Google Scholar] [CrossRef]
- Pradhan, A. Increasing the Range & Effectiveness of Air-to-Air Missiles using Directed Energy Weapons (Lasers) Integrated with Missiles. In Proceedings of the Regional Student Conferences, Multiple Locations, 1 January 2025; p. 98250. [Google Scholar]
- Gupta, T. The Role of High Energy Laser as a U.S. Army Counter-Small Unmanned Aircraft System (UAS) Weapon; Technical Report; U.S. Army: Washington, DC, USA, 2023. Available online: https://apps.dtic.mil/sti/html/trecms/AD1230685/ (accessed on 17 February 2026).
- Zidane, Y.; Silva, J.S.; Tavares, G. Jamming and spoofing techniques for drone neutralization: An experimental study. Drones 2024, 8, 743. [Google Scholar] [CrossRef]
- Joeaneke, P.; Obioha, V.O.; Olaniyi, O.O.; Ogungbemi, O.S.; Olisa, A.O.; Akinola, O.I. Protecting Autonomous UAVs from GPS Spoofing and Jamming: A Comparative Analysis of Detection and Mitigation Techniques. J. Eng. Res. Rep. 2024, 26, 71–92. [Google Scholar] [CrossRef]
- Meheretu, S.E.; Nigussie, E.; Gebremeskel, G.B.; Hailesilassie, S.Y. A Systematic Literature Review on Spoofing and Jamming Approaches in Unmanned Aerial Vehicles Navigation. J. Aerosp. Technol. Manag. 2025, 17, e3425. [Google Scholar] [CrossRef]
- Ratnoo, T. Shima, Line-of-sight interceptor guidance for defending an aircraft. J. Guid. Control Dyn. 2011, 34, 522–532. [Google Scholar] [CrossRef]
- Pliska, M.; Vrba, M.; Báča, T.; Saska, M. Towards safe mid-air drone interception: Strategies for tracking & capture. IEEE Robot. Autom. Lett. 2024, 9, 8810–8817. [Google Scholar] [CrossRef]
- Lee, H.; Radzicki, V.R.; Rajagopal, A. Near-field homing and guidance planning for autonomous navigation systems. In Proceedings of the International Telemetering Conference (ITC), Las Vegas, NV, USA, 23–26 October 2017; Volume 53, pp. 677–684. [Google Scholar]
- Pastrick, H.L.; Seltzer, S.M.; Warren, M.E. Guidance laws for short-range tactical missiles. J. Guid. Control 1981, 4, 98–108. [Google Scholar] [CrossRef]
- Pal, A. Impact Angle Constrained Guidance for Nonstationary Maneuvering and Nonmaneuvering Targets. Master’s Thesis, Jadavpur University, Kolkata, India, 2023. Available online: http://20.198.91.3:8080/jspui/handle/123456789/8943 (accessed on 17 February 2026).
- Barišić, A.; Petric, F.; Bogdan, S. Brain over brawn: Using a stereo camera to detect, track, and intercept a faster UAV by reconstructing the intruder’s trajectory. Field Robot. 2022, 2, 222–240. [Google Scholar] [CrossRef]
- Nguyen, T.; Shivakumar, S.S.; Miller, I.D.; Keller, J.; Lee, E.S.; Zhou, A.; Özaslan, T.; Loianno, G.; Harwood, J.H.; Wozencraft, J.; et al. Mavnet: An effective semantic segmentation micro-network for mav-based tasks. IEEE Robot. Autom. Lett. 2019, 4, 3908–3915. [Google Scholar] [CrossRef]
- Vrba, M.; Saska, M. Marker-less micro aerial vehicle detection and localization using convolutional neural networks. IEEE Robot. Autom. Lett. 2020, 5, 2459–2466. [Google Scholar] [CrossRef]
- Vrba, M.; Heřt, D.; Saska, M. Onboard marker-less detection and localization of non-cooperating drones for their safe interception by an autonomous aerial system. IEEE Robot. Autom. Lett. 2019, 4, 3402–3409. [Google Scholar] [CrossRef]
- Carrio, A.; Vemprala, S.; Ripoll, A.; Saripalli, S.; Campoy, P. Drone detection using depth maps. In 2018 IEEE/RSJ International Conference on Intelligent Robots and Systems (IROS); IEEE: Piscataway, NJ, USA, 2018. [Google Scholar] [CrossRef]
- Xiao, J.; Feroskhan, M. Learning multipursuit evasion for safe targeted navigation of drones. IEEE Trans. Artif. Intell. 2024, 5, 6210–6224. [Google Scholar] [CrossRef]
- Xiong, S.; Liu, H.H.T. Low-altitude fixed-wing robust and optimal control using a barrier penalty function method. J. Guid. Control Dyn. 2023, 46, 2218–2223. [Google Scholar] [CrossRef]
- Hou, Y.; Chen, D.; Yang, S. Adaptive robust trajectory tracking controller for a quadrotor UAV with uncertain environment parameters based on backstepping sliding mode method. IEEE Trans. Autom. Sci. Eng. 2023, 22, 4446–4456. [Google Scholar] [CrossRef]
- Abdullah, M.; Zulfiqar, A.; Arman, J.H. An integral backstepping and nonlinear disturbance observer-based sliding mode control for active fault-tolerant quadcopter UAVs with simulation as well as hardware-in-the-loop experiments. Int. J. Dyn. Control 2025, 13, 159. [Google Scholar] [CrossRef]
- Kulkarni, O.; Burhanpurwala, A. A survey of advancements in DBSCAN clustering algorithms for big data. In Proceedings of the 2024 3rd International Conference on Power Electronics and IoT Applications in Renewable Energy and Its Control (PARC), Mathura, India, 23–24 February 2024; IEEE: Piscataway, NJ, USA, 2024; pp. 106–111. [Google Scholar]
- Raja, M.; Hasan, P.; Mahmudunnobe, M.; Saifuddin, M.; Hasan, S.N. Membership determination in open clusters using the DBSCAN Clustering Algorithm. Astron. Comput. 2024, 47, 100826. [Google Scholar] [CrossRef]
- Kremers, B.J.; Citrin, J.; Ho, A.; van de Plassche, K.L. Two-step clustering for data reduction combining DBSCAN and k-means clustering. Contrib. Plasma Phys. 2023, 63, e202200177. [Google Scholar] [CrossRef]
- Li, J.; Zheng, A.; Guo, W.; Bandyopadhyay, N.; Zhang, Y.; Wang, Q. Urban flood risk assessment based on DBSCAN and K-means clustering algorithm. Geomat. Nat. Hazards Risk 2023, 14, 2250527. [Google Scholar] [CrossRef]
- Ceviz, O.; Sen, S.; Sadioglu, P. A survey of security in uavs and fanets: Issues, threats, analysis of attacks, and solutions. IEEE Commun. Surv. Tutor. 2024, 27, 3227–3265. [Google Scholar] [CrossRef]
- Wang, X.; Zhao, Z.; Yi, L.; Ning, Z.; Guo, L.; Yu, F.R.; Guo, S. A survey on security of UAV swarm networks: Attacks and countermeasures. ACM Comput. Surv. 2024, 57, 1–37. [Google Scholar] [CrossRef]
- Harshil, J.; Goti, H.; Mahida, N.; Gupta, R.; Tanwar, S.; Bhardwaj, G.; Jhanjhi, N.Z.; Ray, S.K. AI-based Approach for Radio Frequency Jamming Attack Detection in Unmanned Aerial Vehicles. In Proceedings of the 2024 IEEE 29th Asia Pacific Conference on Communications (APCC), Bali, Indonesia, 5–7 November 2024; IEEE: Piscataway, NJ, USA, 2024; pp. 266–271. [Google Scholar]
- Xia, B.; Mantegh, I.; Xie, W. Decentralized UAV Swarm Control: A Multi-Layered Architecture for Integrated Flight Mode Management and Dynamic Target Interception. Drones 2024, 8, 350. [Google Scholar] [CrossRef]
- Maaruf, M.; Abubakar, A.N.; Gulzar, M.M. Adaptive backstepping and sliding mode control of a quadrotor. J. Braz. Soc. Mech. Sci. Eng. 2024, 46, 630. [Google Scholar] [CrossRef]
- Maaruf, M.; Abubakar, A.N.; Gulzar, M.M.; Bali, A. Finite-Time Adaptive Dynamic Surface Control of a Quadrotor with Input Delay. Arab. J. Sci. Eng. 2025, 1–17. [Google Scholar] [CrossRef]
- Shayea, G.G.; Zabil, M.H.M.; Habeeb, M.A.; Khaleel, Y.L.; Albahri, A.S. Strategies for protection against adversarial attacks in AI models: An in-depth review. J. Intell. Syst. 2025, 34, 20240277. [Google Scholar] [CrossRef]
- Li, X.; Ru, C.; Sun, H. Adversarial generative learning and timed path optimization for real-time visual image prediction to guide robot arm movements. J.-Real-Time Image Process. 2024, 21, 154. [Google Scholar] [CrossRef]
- Xu, R.; Wunsch, D. Survey of clustering algorithms. IEEE Trans. Neural Netw. 2005, 16, 645–678. [Google Scholar] [CrossRef]
- Alqefari, S.; Menai, M.E.B. Multi-UAV task assignment in dynamic environments: Current trends and future directions. Drones 2025, 9, 75. [Google Scholar] [CrossRef]
- Zhang, Y.; Li, M.; Wang, S.; Dai, S.; Luo, L.; Zhu, E.; Xu, H.; Zhu, X.; Yao, C.; Zhou, H. Gaussian mixture model clustering with incomplete data. ACM Trans. Multimed. Comput. Commun. Appl. 2021, 17, 1–14. [Google Scholar] [CrossRef]
- Ikotun, A.M.; Ezugwu, A.E.; Abualigah, L.; Abuhaija, B.; Heming, J. K-means clustering algorithms: A comprehensive review, variants analysis, and advances in the era of big data. Inf. Sci. 2023, 622, 178–210. [Google Scholar] [CrossRef]
- Fuchs, M.; Höpken, W. Clustering: Hierarchical, k-means, DBSCAN. In Applied Data Science in Tourism: Interdisciplinary Approaches, Methodologies, and Applications; Springer International Publishing: Cham, Switzerland, 2022; pp. 129–149. [Google Scholar]
- Fahim, A. An extended DBSCAN clustering algorithm. Int. J. Adv. Comput. Sci. Appl. 2022, 13, 245–258. [Google Scholar] [CrossRef]
- Li, S.; Duan, N.; Min, H. Trajectory tracking control for quadrotor unmanned aerial vehicle with input delay and disturbances. Asian J. Control 2024, 26, 150–161. [Google Scholar] [CrossRef]
- Bouadi, H.; Bouchoucha, M.; Tadjine, M. Sliding mode control based on backstepping approach for an UAV type-quadrotor. World Acad. Sci. Eng. Technol. 2007, 26, 22–27. [Google Scholar]










| Parameter | Value | Parameter | Value |
|---|---|---|---|
| J | |||
| m | |||
| d | b | ||
| Approach (Scenario) | Interception (Yes/No) | Interception Time (s) | Average Interception Error (m) |
|---|---|---|---|
| PID-based (Single UAV) | No | – | High |
| Proposed approach (Single UAV) | Yes | 7 | |
| PID-based (Multiple UAVs) | No | – | High |
| Proposed approach (Multiple UAVs) | Yes | 8 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license.
Share and Cite
Abubakar, A.N.; Nasir, A.; Saif, A.-W.A. Deceptive Waypoint Sequencing Based UAV–UAV Interception Control Using DBSCAN Learning Strategy. Mach. Learn. Knowl. Extr. 2026, 8, 54. https://doi.org/10.3390/make8030054
Abubakar AN, Nasir A, Saif A-WA. Deceptive Waypoint Sequencing Based UAV–UAV Interception Control Using DBSCAN Learning Strategy. Machine Learning and Knowledge Extraction. 2026; 8(3):54. https://doi.org/10.3390/make8030054
Chicago/Turabian StyleAbubakar, Abdulrazaq Nafiu, Ali Nasir, and Abdul-Wahid A. Saif. 2026. "Deceptive Waypoint Sequencing Based UAV–UAV Interception Control Using DBSCAN Learning Strategy" Machine Learning and Knowledge Extraction 8, no. 3: 54. https://doi.org/10.3390/make8030054
APA StyleAbubakar, A. N., Nasir, A., & Saif, A.-W. A. (2026). Deceptive Waypoint Sequencing Based UAV–UAV Interception Control Using DBSCAN Learning Strategy. Machine Learning and Knowledge Extraction, 8(3), 54. https://doi.org/10.3390/make8030054







