Advancing Drone Operations through Lightweight Blockchain and Fog Computing Integration: A Systematic Review
Abstract
1. Introduction
2. Selection of Papers by PRISMA
3. Literature Survey
3.1. Key Research on Blockchain Applications and Innovations
3.2. Fog Computing
3.3. Key Research on Fog Computing Applications and Innovations
3.3.1. Case Study on Environmental Monitoring
3.3.2. Support for Autonomous Drone Navigation
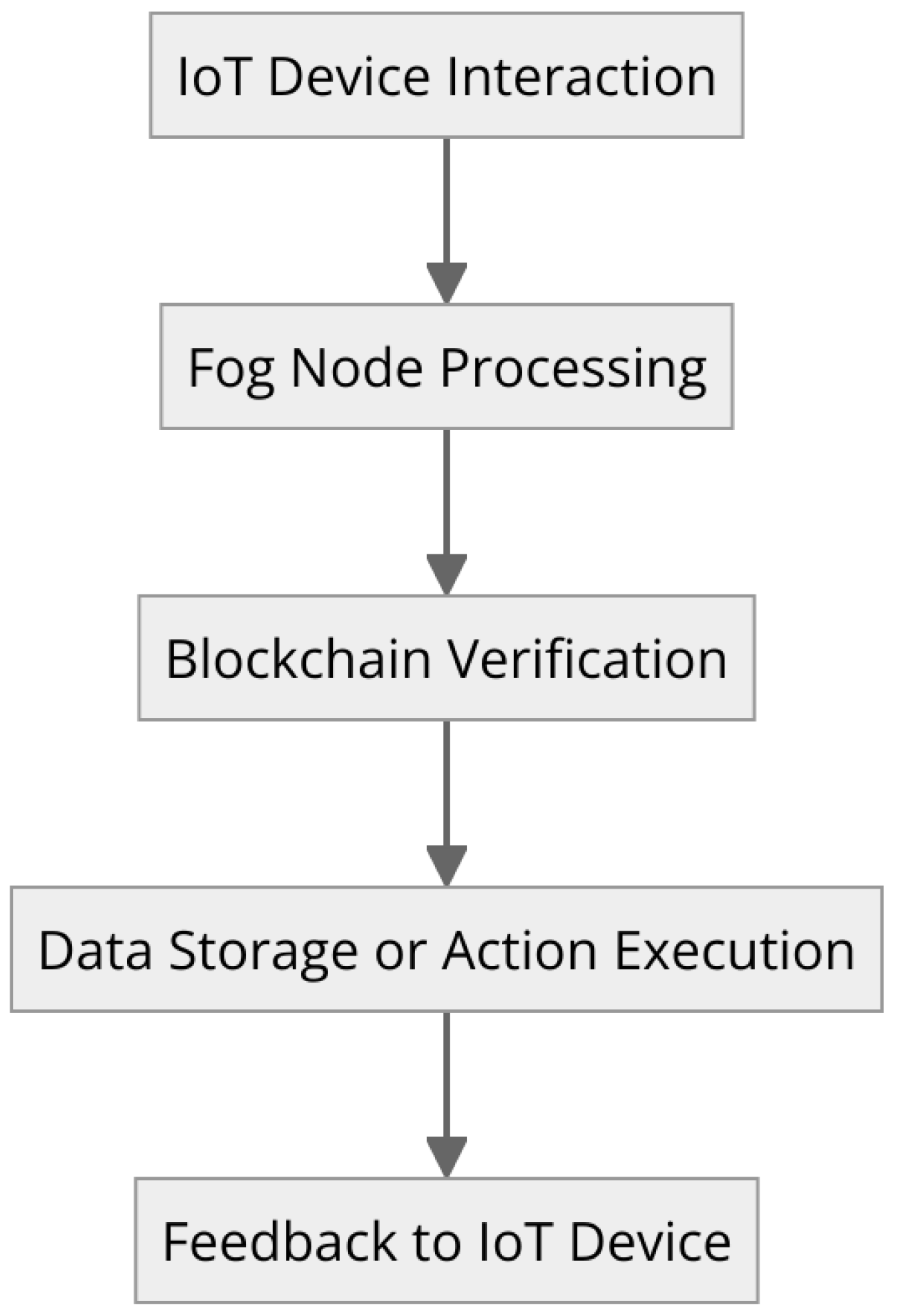
3.3.3. Fog-Assisted IoT Framework
3.4. Lightweight Blockchain Framework with Fog Computing
3.5. Key Research on Lightweight Blockchain Framework with Fog Computing
3.5.1. Theoretical Models and Synergistic Potential
3.5.2. Monitoring Land Surface Changes with Khan et al.’s Framework
3.5.3. Implications for Future Drone Operations
3.6. Elevating Drone Operations with Blockchain and Fog Computing
Advancements through Integration
3.7. Strategies for Latency Minimization in Drone Operations
3.7.1. Real-Time Data Processing Capabilities
3.7.2. Optimization of Communication Protocols
4. Overview of the Existing Literature
4.1. Blockchain and Fog Computing in Vehicular Networks
4.2. Enhancement of Cyberphysical Systems (CPSs)
4.3. Drone Operations’ Security and Efficiency
4.4. Identification of Gaps
- Synthesize and critique existing applications of the blockchain and fog computing in related domains, with a specific lens on their potential applicability to drones.
- Highlight the operational, security, and efficiency challenges unique to drone operations that are not fully addressed by existing reviews.
- Propose new research directions focused on leveraging the blockchain and fog computing to enhance drone operations, thereby contributing significantly to the field.
4.5. Integrated Insights and Implications
- Enhanced security and efficiency: It has been demonstrated that combining blockchain technology and fog computing dramatically improves the security and effectiveness of IoT systems. The combination of fog computing’s proximity to data sources and the blockchain’s decentralized structure provides a solid answer to latency and data integrity issues.
- Various uses in various industries: The combined capabilities of the blockchain and fog computing have demonstrated various applications, from Industrial IoT and smart cities to environmental monitoring and transportation. This flexibility highlights how these technologies have the power to transform several industries completely.
- Addressing IoT challenges: The integration addresses several critical IoT challenges, including data privacy, efficient resource utilization, and real-time data processing demands.
4.6. Discussion of Research Implications
- -
- IoT cybersecurity: An enhanced cybersecurity framework is provided by the integrated approach. This is essential when cybercriminals are increasingly focusing on IoT devices.
- -
- Future of smart cities and industries: The capacity for real-time data processing and enhanced security opens new possibilities for developing smart cities and industrial automation.
- -
- Scalability and sustainability: Without sacrificing security or performance, the integration offers a scalable and sustainable model for IoT deployments in the future.
5. Performance Metrics and Evaluation Methods in Blockchain and Fog Computing for Drone Operations
5.1. Overview of Performance Metrics
5.2. Evaluation Methods
6. Challenges and Limitations
- Complexity in Implementation: For implementation and maintenance, fog computing with the blockchain brings an additional layer of complexity. This problem arises from the necessity to align two complex technologies requiring a thorough comprehension of fog computing and blockchain specifics [35].
- Storage capacity and scalability constraints: The underlying challenge lies in the fact that most existing blockchains are not inherently designed to handle massive amounts of data storage. With the underlying blockchain continuously expanding, each node must maintain the entire chain to validate new blocks. This necessity introduces a bottleneck, as conventional blockchains are limited in their transaction-handling capabilities and are not optimized for extensive data storage. Attempting to store vast amounts of data results in significant latency, impacting the performance of fog computing’s limited resources [40].
- Innovative approaches for real-time processing: To address these challenges, there is a pressing need for innovative approaches that simplify real-time processing and storage. Techniques such as data compression and data lightning are proposed to alleviate the strain on the system [24]. A comprehensive understanding of projected network performance and scalability is crucial for the development of these innovative solutions.
- Trade-offs for decreasing latency: Various techniques, including off-chain transactions and sharding, have been introduced to decrease latency and optimize storage in blockchains with fog computing integration. However, these innovations imply trade-offs that require further research to strike the right balance between scalability, security, and decentralization. Additionally, the environmental impact, especially in energy consumption, remains a critical concern, particularly in Proof of Work (PoW)-based blockchain systems. Exploring alternative algorithms while maintaining security and dependability is a key avenue for future research [41].
- Quality of service (QoS) metrics: The current consensus models often fall short in delivering satisfactory quality of service (QoS) metrics, including latency, energy use, and operating costs. Notably, throughput and latency for real-world applications frequently do not meet the desired QoS levels. As an example, Bitcoin, while processing a limited number of transactions per second, experiences considerable consensus execution delays. Novel resource scheduling strategies are required to decrease energy consumption without compromising QoS metrics, ensuring a balance between system efficiency and quality of service [42].
- Privacy challenges in the blockchain: The inherent nature of the BC, where information is stored on a public ledger, poses challenges to privacy and confidentiality. The transparency of the ledger makes it challenging to ensure the privacy of sensitive data. Several anonymization or encryption-based techniques may be employed to safeguard data confidentiality. However, these methods are not foolproof and are contingent on the specific implementation and environment [43].
- Impact on reliability and data integrity in fog computing: Although the blockchain contributes to fog computing data flexibility and security, questions of its effects on reliability or relatedness/integrity in the case of fog computing appear. The blockchain validates data creators and provides for the immutability of the data, which are not susceptible to changes. On the other hand, corrupted data entering the blockchain may yield problems because corruption is not immediately visible and it can be a case of consistently damaged information. The corruption of data may arise as a result of several factors such as hostile attacks, surroundings, and device failures [44].
- Technological maturity: The relative novelty of both fog computing and the blockchain introduces challenges related to their technological maturity. As emerging technologies, their full potential and long-term implications are still being understood. Navigating this evolving landscape requires a proactive approach to harness their capabilities fully [45].
Addressing Unique Challenges in Drone Operations
- Operational challenges: These include the dynamic and often unpredictable environments in which drones demand advanced decision-making and autonomous navigation capabilities. The integration of blockchains and fog computing must, therefore, not only ensure robust data integrity and decentralized processing but also support the complex algorithms required for drones to adapt in real time to environmental changes and mission parameters.
- Security challenges: Beyond safeguarding data, the security measures for drones must encompass physical device security and operational integrity. Utilizing blockchains for immutable operation logs and leveraging fog computing for localized, real-time security assessments present a novel approach to creating a multi-tiered security framework that addresses both cyber and physical threats.
- Efficiency challenges: The energy efficiency of drones, especially for prolonged missions or in resource-constrained environments, is paramount. Innovations in blockchains and fog computing must focus on minimizing energy consumption without compromising the operational efficacy of drone networks. This includes exploring lightweight blockchain protocols and energy-efficient data processing models tailored to the unique requirements of drone operations [46].
7. Future Research Directions
- Improved integration approaches: New studies should focus on creating simpler and more efficient means of integrating blockchains with fog computing. The simplification of the integration process can thereby contribute to improving the synergy between these technologies, which would make it more convenient and efficient when implementing them collaboratively. Exploring new approaches, frameworks, and protocols can help to develop a more efficient integration of blockchain technology with fog computing by eliminating complexity issues but enhancing performance.
- Scalability solutions: The rapid explosion of data collected from IoT networks demands a focused study on scalability measures. By contrast, future research should concentrate on bold ideas that could address the large quantities of data to be generated by IoT networks in the years ahead. Scalability solutions might include innovations in data processing methods, storage techniques, or network architectures. It is, therefore, essential to investigate how blockchains and fog computing can act in a way that allows them to scale automatically as IoT ecosystems change [24].
- Long-term impact studies: It is necessary to examine long-term in-depth studies so that the enduring impacts of blockchain and fog computing technologies on privacy, security, and IoT evolution can be ascertained. Future studies have to investigate the elaborate relationship between blockchains, fog computing, and IoT technology’s evolution. This entails considering the lasting implications regarding data privacy, integrated systems’ security standing, and the IoT application evolutionary path. These studies will provide priceless knowledge regarding the sustainable and codependent adoption of blockchains and fog computing within the wider technological infrastructure.
8. Conclusions
Author Contributions
Funding
Data Availability Statement
Acknowledgments
Conflicts of Interest
Abbreviations
| UAVs | Unmanned Aerial Vehicles |
| CA | Certificate Authority |
| IoT | Internet of Things |
| FC | fog computing |
| ECC | elliptic curve cryptography |
| SDN | Software-Defined Networking |
References
- Kim, H.; Jung, Y.W.; Zhang, H. Guest Editorial Special Issue on Time-Sensitive Networks for Unmanned Aircraft Systems. Sensors 2021, 21, 6132. [Google Scholar] [CrossRef] [PubMed]
- Clarke, R.; Moses, L.B. The regulation of civilian drones’ impacts on public safety. Comput. Law Secur. Rev. 2014, 30, 263–285. [Google Scholar] [CrossRef]
- Kalatzis, N.; Avgeris, M.; Dechouniotis, D.; Papadakis-Vlachopapadopoulos, K.; Roussaki, I.; Papavassiliou, S. Edge Computing in IoT Ecosystems for UAV-Enabled Early Fire Detection. In Proceedings of the 2018 IEEE International Conference on Smart Computing (SMARTCOMP), Taormina, Italy, 18–20 June 2018; pp. 106–114. [Google Scholar] [CrossRef]
- Wu, D.; Ansari, N. A Cooperative Computing Strategy for Blockchain-Secured Fog Computing. IEEE Internet Things J. 2020, 7, 6603–6609. [Google Scholar] [CrossRef]
- Finlow-Bates, K. A Lightweight Blockchain Consensus Protocol. 2016. Available online: https://www.researchgate.net/publication/339948592_A_Lightweight_Blockchain_Consensus_Protocol (accessed on 8 July 2018).
- Khor, J.H.; Sidorov, M.; Zulqarnain, S.A.B. Scalable Lightweight Protocol for Interoperable Public Blockchain-Based Supply Chain Ownership Management. Sensors 2023, 23, 3433. [Google Scholar] [CrossRef] [PubMed]
- Michailidis, E.T.; Vouyioukas, D. A review on software-based and hardware-based authentication mechanisms for the Internet of Drones. Drones 2022, 6, 41. [Google Scholar] [CrossRef]
- Andola, N.; Raghav; Yadav, V.K.; Venkatesan, S.; Verma, S. SpyChain: A lightweight blockchain for authentication and anonymous authorization in IoD. Wirel. Pers. Commun. 2021, 119, 343–362. [Google Scholar] [CrossRef]
- Ch, R.; Srivastava, G.; Gadekallu, T.R.; Maddikunta, P.K.R.; Bhattacharya, S. Security and privacy of UAV data using blockchain technology. J. Inf. Secur. Appl. 2020, 55, 102670. [Google Scholar] [CrossRef]
- Gupta, R.; Kumari, A.; Tanwar, S. Fusion of blockchain and artificial intelligence for secure drone networking underlying 5G communications. Trans. Emerg. Telecommun. Technol. 2021, 32, e4176. [Google Scholar] [CrossRef]
- Aggarwal, S.; Shojafar, M.; Kumar, N.; Conti, M. A New Secure Data Dissemination Model in Internet of Drones. In Proceedings of the ICC 2019—2019 IEEE International Conference on Communications (ICC), Shanghai, China, 20–24 May 2019; pp. 1–6. [Google Scholar] [CrossRef]
- Alkadi, R.; Alnuaimi, N.; Yeun, C.Y.; Shoufan, A. Blockchain Interoperability in Unmanned Aerial Vehicles Networks: State-of-the-Art and Open Issues. IEEE Access 2022, 10, 14463–14479. [Google Scholar] [CrossRef]
- Javed, S.; Khan, M.A.; Abdullah, A.M.; Alsirhani, A.; Alomari, A.; Noor, F.; Ullah, I. An efficient authentication scheme using blockchain as a certificate authority for the internet of drones. Drones 2022, 6, 264. [Google Scholar] [CrossRef]
- Mershad, K. A taxonomy and review of lightweight blockchain solutions for internet of things networks. arXiv 2022, arXiv:2212.06272. [Google Scholar]
- Hou, X.; Ren, Z.; Wang, J.; Zheng, S.; Cheng, W.; Zhang, H. Distributed Fog Computing for Latency and Reliability Guaranteed Swarm of Drones. IEEE Access 2020, 8, 7117–7130. [Google Scholar] [CrossRef]
- Ometov, A.; Molua, O.L.; Komarov, M.; Nurmi, J. A survey of security in cloud, edge, and fog computing. Sensors 2022, 22, 927. [Google Scholar] [CrossRef] [PubMed]
- Aazam, M.; Zeadally, S.; Harras, K.A. Fog Computing Architecture, Evaluation, and Future Research Directions. IEEE Commun. Mag. 2018, 56, 46–52. [Google Scholar] [CrossRef]
- Haouari, F.; Faraj, R.; AlJa’am, J.M. Fog Computing Potentials, Applications, and Challenges. In Proceedings of the 2018 International Conference on Computer and Applications (ICCA), Beirut, Lebanon, 25–26 August 2018; pp. 399–406. [Google Scholar] [CrossRef]
- Ahanger, T.A.; Tariq, U.; Nusir, M. Mobility of Internet of Things and Fog Computing: Concerns and Future Directions. Int. J. Commun. Netw. Inf. Secur. 2018, 10, 534. [Google Scholar] [CrossRef]
- Brogi, A.; Forti, S.; Guerrero, C.; Lera, I. How to place your apps in the fog: State of the art and open challenges. Softw. Pract. Exp. 2020, 50, 719–740. [Google Scholar] [CrossRef]
- Li, X.; Zhou, L.; Sun, Y.; Ulziinyam, B. Multi-task offloading scheme for UAV-enabled fog computing networks. Eurasip J. Wirel. Commun. Netw. 2020, 2020, 230. [Google Scholar] [CrossRef]
- Aazam, M.; Zeadally, S.; Harras, K.A. Offloading in fog computing for IoT: Review, enabling technologies, and research opportunities. Future Gener. Comput. Syst. 2018, 87, 278–289. [Google Scholar] [CrossRef]
- Abdali, T.A.N.; Hassan, R.; Aman, A.H.M.; Nguyen, Q.N. Fog Computing Advancement: Concept, Architecture, Applications, Advantages, and Open Issues. IEEE Access 2021, 9, 75961–75980. [Google Scholar] [CrossRef]
- Lei, K.; Du, M.; Huang, J.; Jin, T. Groupchain: Towards a Scalable Public Blockchain in Fog Computing of IoT Services Computing. IEEE Trans. Serv. Comput. 2020, 13, 252–262. [Google Scholar] [CrossRef]
- Khan, A.A.; Shaikh, Z.A.; Laghari, A.A.; Bourouis, S.; Wagan, A.A.; Ali, G.A.A.A. Blockchain-aware distributed dynamic monitoring: A smart contract for fog-based drone management in land surface changes. Atmosphere 2021, 12, 1525. [Google Scholar] [CrossRef]
- Alzoubi, Y.I.; Aljaafreh, A. Blockchain-Fog Computing Integration Applications: A Systematic Review. Cybern. Inf. Technol. 2023, 23, 3–37. [Google Scholar] [CrossRef]
- Eddine, M.S.; Ferrag, M.A.; Friha, O.; Maglaras, L. EASBF: An efficient authentication scheme over blockchain for fog computing-enabled internet of vehicles. J. Inf. Secur. Appl. 2021, 59, 102802. [Google Scholar] [CrossRef]
- Shukla, S.; Thakur, S.; Hussain, S.; Breslin, J.G.; Jameel, S.M. Identification and authentication in healthcare internet-of-things using integrated fog computing based blockchain model. Internet Things 2021, 15, 100422. [Google Scholar] [CrossRef]
- Kamruzzaman, M.; Yan, B.; Sarker, M.N.I.; Alruwaili, O.; Wu, M.; Alrashdi, I. Blockchain and fog computing in IoT-driven healthcare services for smart cities. J. Healthc. Eng. 2022, 2022. [Google Scholar] [CrossRef] [PubMed]
- Bouachir, O.; Aloqaily, M.; Tseng, L.; Boukerche, A. Blockchain and Fog Computing for Cyberphysical Systems: The Case of Smart Industry. Computer 2020, 53, 36–45. [Google Scholar] [CrossRef]
- Liu, Y.; Zhang, J.; Zhan, J. Privacy protection for fog computing and the internet of things data based on blockchain. Clust. Comput. 2021, 24, 1331–1345. [Google Scholar] [CrossRef]
- Muthanna, A.; Ateya, A.A.; Khakimov, A.; Gudkova, I.; Abuarqoub, A.; Samouylov, K.; Koucheryavy, A. Secure and reliable IoT networks using fog computing with software-defined networking and blockchain. J. Sens. Actuator Netw. 2019, 8, 15. [Google Scholar] [CrossRef]
- Ngabo, D.; Wang, D.; Iwendi, C.; Anajemba, J.H.; Ajao, L.A.; Biamba, C. Blockchain-based security mechanism for the medical data at fog computing architecture of internet of things. Electronics 2021, 10, 2110. [Google Scholar] [CrossRef]
- Gumaei, A.; Al-Rakhami, M.; Hassan, M.M.; Pace, P.; Alai, G.; Lin, K.; Fortino, G. Deep Learning and Blockchain with Edge Computing for 5G-Enabled Drone Identification and Flight Mode Detection. IEEE Netw. 2021, 35, 94–100. [Google Scholar] [CrossRef]
- Kaur, K.; Garg, S.; Kaddoum, G.; Gagnon, F.; Ahmed, S.H. Blockchain-Based Lightweight Authentication Mechanism for Vehicular Fog Infrastructure. In Proceedings of the 2019 IEEE International Conference on Communications Workshops (ICC Workshops), Shanghai, China, 20–24 May 2019; pp. 1–6. [Google Scholar] [CrossRef]
- Gomes, E.; Costa, F.; De Rolt, C.; Plentz, P.; Dantas, M. A survey from real-time to near real-time applications in fog computing environments. In Proceedings of the Telecommunications, Alexandria, Egypt, 13–15 July 2021; Volume 2, pp. 489–517. [Google Scholar]
- Badidi, E.; Mahrez, Z.; Sabir, E. Fog computing for smart cities’ big data management and analytics: A review. Future Internet 2020, 12, 190. [Google Scholar] [CrossRef]
- Jalowiczor, J.; Rozhon, J.; Voznak, M. Study of the efficiency of fog computing in an optimized lorawan cloud architecture. Sensors 2021, 21, 3159. [Google Scholar] [CrossRef] [PubMed]
- Balen, J.; Damjanovic, D.; Maric, P.; Vdovjak, K. Optimized Edge, Fog and Cloud Computing Method for Mobile Ad-hoc Networks. In Proceedings of the 2021 International Conference on Computational Science and Computational Intelligence (CSCI), IEEE, Las Vegas, NV, USA, 15–17 December 2021; pp. 1303–1309. [Google Scholar]
- Tariq, N.; Asim, M.; Al-Obeidat, F.; Zubair Farooqi, M.; Baker, T.; Hammoudeh, M.; Ghafir, I. The security of big data in fog-enabled IoT applications including blockchain: A survey. Sensors 2019, 19, 1788. [Google Scholar] [CrossRef] [PubMed]
- Baniata, H.; Kertesz, A. A survey on blockchain-fog integration approaches. IEEE Access 2020, 8, 102657–102668. [Google Scholar] [CrossRef]
- Vairagade, R.S.; Sh, B. Enabling machine learning-based side-chaining for improving QoS in blockchain-powered IoT networks. Trans. Emerg. Telecommun. Technol. 2022, 33, e4433. [Google Scholar] [CrossRef]
- Ferrag, M.A.; Shu, L.; Yang, X.; Derhab, A.; Maglaras, L. Security and privacy for green IoT-based agriculture: Review, blockchain solutions, and challenges. IEEE Access 2020, 8, 32031–32053. [Google Scholar] [CrossRef]
- Rivera, A.V.; Refaey, A.; Hossain, E. A blockchain framework for secure task sharing in multi-access edge computing. IEEE Netw. 2020, 35, 176–183. [Google Scholar] [CrossRef]
- Sharma, P.K.; Chen, M.Y.; Park, J.H. A software defined fog node based distributed blockchain cloud architecture for IoT. IEEE Access 2017, 6, 115–124. [Google Scholar] [CrossRef]
- Mairaj, A.; Baba, A.I.; Javaid, A.Y. Application specific drone simulators: Recent advances and challenges. Simul. Model. Pract. Theory 2019, 94, 100–117. [Google Scholar] [CrossRef]
- Sharma, I.; Gupta, S.K. SFL-MDrone: Synchronous federated learning enabled multi drones. J. Intell. Fuzzy Syst. 2024, 1–20. [Google Scholar] [CrossRef]

| Author | Year | Main Focus | Key Findings | Applications/Use Case |
|---|---|---|---|---|
| K. Finlow-Bates [5] | 2017 | Lightweight blockchain protocols | Protocol improving computational overhead by up to 40%. | Supply chain, healthcare, IoT devices |
| Khor et al. [6] | 2023 | Blockchain applications and security | Versatility and cryptographic techniques for security. | Healthcare, supply chain, public records |
| Michailidis et al. [7] | 2022 | AI with blockchains | AI optimizes blockchain operations and security. | Predictive analysis, threat detection |
| Andola et al. [8] | 2021 | Blockchains for the IoD | Methods to hide drone identities using NIZKP. | Internet of Drones (IoD) |
| Rupa, C. et al. [9] | 2020 | 5G network evolution | 5G technical attributes and capabilities. | Smart cities, autonomous vehicles, telemedicine |
| Gupta, R et al. [10] | 2020 | Network technology examination | Evolving network technologies’ impact. | Broad spectrum communication, IoT integration |
| Aggarwal, S et al. [11] | 2019 | Data dissemination in the IoD | Blockchain in IoD for integrity and authentication. | Surveillance, agriculture, military operations |
| Alkadi, R et al. [12] | 2022 | Blockchain in UAV networks | Blockchain applications for UAV safety and security. | Multiple UAV service providers, drone recharging |
| Javed et al. [13] | 2022 | Blockchain for IoD authentication | Blockchain for enhanced IoD network security. | Secure IoD network communication |
| Mershada et al. [14] | 2023 | Lightweight blockchain for networks | Challenges in blockchain integration. | Smart homes, healthcare, Internet of Vehicles |
| Author | Year | Main Focus | Key Findings | Applications/Use Case |
|---|---|---|---|---|
| Ometov et al. [16] | 2022 | Identify ecosystem of cloud, edge, and fog computing. Security threats. Computing paradigms. | Security and privacy challenges. Differences between cloud, edge, and fog computing. Mitigation techniques. | Cloud, edge, and fog computing security and privacy. |
| Aazam et al. [17] | 2018 | Fog computing with cloud computing in the IoT. | "Fog-assisted IoT" framework. Resource management. Latency reduction. Energy efficiency. Challenges. | IoT systems, smart cities, healthcare. |
| Hou et al. [15] | 2019 | Distributed fog computing in drone swarms. | Reliability modeling for drones. Mathematical models for drone swarm reliability. Disturbances in operations. | Drone swarms, robotic communication, IoT systems. |
| Haouari et al. [18] | 2018 | Significance of fog computing in the IoT. | Fog computing as a decentralized approach. Advantages over cloud computing. Latency in real-time applications. | IoT systems, real-time applications, smart devices, wearables. |
| Ahanger et al. [19] | 2018 | IoT and fog computing intersection. | Edge/fog computing for IoT device resource constraints. Augmenting centralized cloud systems. | IoT systems, data handling and delivery, technological advancements. |
| Brogi et al. [20] | 2020 | Application placement in fog computing. | Service quality improvement. Algorithms, prototypes, and test cases. Open challenges in application placement. | IoT systems, application deployment in fog environments, service optimization. |
| Xu jie Li et al. [21] | 2020 | Task offloading in UAV-enabled fog computing networks. | Task offloading as a combinatorial optimization problem. Minimizing task delays. | UAV networks, wireless communication systems. |
| Kalatzis et al. [3] | 2018 | UAV-enabled IoT systems. | Edge computing for task offloading in UAVs. Resource distribution and optimization. Semantic reasoning support. | UAV-based fire detection, IoT networks. |
| Aazam et al. [22] | 2018 | Offloading in fog computing for the IoT. | Importance of offloading. Criteria for offloading tasks. | Smart healthcare, virtual reality, intelligent vehicular communication, smart cities, IoT. |
| Abdali et al. [23] | 2021 | Fog computing in the IoT. | Fog as middleware between the cloud and IoT. Local data processing. Addressing latency and bandwidth limitations. | Environmental monitoring, infrastructure control, home automation. |
| Author | Year | Objective/Research Question | Blockchain and Fog Integration | Key Findings/ Contributions |
|---|---|---|---|---|
| Khan et al. [25] | 2021 | Introduction of a blockchain-aware framework for land surface change monitoring using drones. | Utilizes an SH-256 consortium P2P network with smart contracts. | Efficient, secure, automated monitoring and data management. |
| Alzoubi and Aljaafreh [26] | 2023 | Systematic review of blockchain and fog computing integration in the IoT. | Highlights fog as an IoT–cloud bridge and blockchain’s decentralized attributes. | Guide to blockchain–fog applications in the digital domain. |
| Eddine et al. [27] | 2021 | Exploration of security challenges in the IoV and EASBF authentication scheme. | Blockchains in fog computing-enabled IoV environments. | Robust solution addressing IoV security and latency concerns. |
| Shukla et al. [28] | 2021 | Security challenges in healthcare IoT devices and an integrated solution. | Synergizes fog computing and blockchains for healthcare IoT devices. | ASE algorithm and three-tier FC architecture for secure data transmission. |
| Kamruzzaman et al. [29] | 2022 | Role of the blockchain, IoT, and fog in smart city healthcare. | Blockchains for data security; fog computing for real-time IoT healthcare devices. | Enhanced healthcare infrastructure in smart cities. |
| Bouachir et al. [30] | 2020 | Blockchains and fog computing in cyberphysical systems for smart industries. | Blockchains for data protection in the IIoT and fog computing for data management. | ICPS model integrating blockchains and fog/edge computing. |
| Liu et al. [31] | 2021 | Safeguarding sensitive IoT data. | Blockchains for access control, fog computing for data processing. | Mechanism integrating blockchains, fog computing, and encryption. |
| Muthanna et al. [32] | 2019 | Enhancing security and reliability of IoT networks. | Integration of fog computing, SDN, and blockchains. | Framework for IoT networks with a data offloading algorithm. |
| Ngabo et al. [33] | 2021 | Security in fog computing architecture and CoT. | Public-permissioned blockchain with ECC digital signature. | Robust security solution for data immutability and transparency. |
| Gumaei et al. [34] | 2021 | Enhancing drone security in 5G. | Blockchain with DRNN and edge computing for drone identification. | Framework for data integrity and secure transmission for drones. |
| Kaur et al. [35] | 2019 | Data transmission challenges in vehicular networks. | Vehicular fog computing and authentication using blockchains and ECC. | Secure and efficient data transmission approach for vehicular networks. |
| Metric | Relevance to Drone Operations |
|---|---|
| Latency | Measures the time delay in processing and communicating data, which is crucial for real-time drone applications such as navigation and surveillance, where quick data analysis and decision-making are essential. |
| Throughput | Quantifies the volume of data that can be processed within a given timeframe. It is important to assess the system’s capability to handle the large amounts of data generated by drones, especially in monitoring and mapping tasks. |
| Resource Utilization | Assesses the efficiency of computational and energy resources used by the system. Essential for ensuring the sustainability of drone operations and that the integration of the blockchain and fog computing does not excessively drain the drone’s limited resources. |
| Security | Evaluates the system’s ability to protect data against unauthorized access and breaches. It is paramount in drone operations due to the sensitive nature of the data collected and the implications of potential security lapses. |
| Scalability | Examines the system’s ability to adapt and manage increased loads, which could arise from adding more drones or processing larger datasets. It ensures that the technological solution can grow to meet expanding operational demands without degradation in performance. |
| Reliability | Measures the consistency of system performance over time, including metrics like uptime and error rates. It is critical for maintaining dependable drone operations and ensuring service delivery meets expected standards. |
| Method | Strengths | Limitations |
|---|---|---|
| Theoretical Models |
|
|
| Simulations |
|
|
| Prototype Testing |
|
|
| Practical Implementations |
|
|
| Challenge Category | Description | Key Papers |
|---|---|---|
| Complexity in implementation | Aligning fog computing with blockchain adds complexity due to the need for a comprehensive understanding of both technologies. | [35] |
| Storage Capacity and scalability | Blockchain’s design limitations in handling large data volumes create bottlenecks in performance and scalability, impacting fog computing’s efficiency. | [40] |
| Innovative approaches for real-time processing | The need for simplified real-time processing and storage solutions to alleviate system strain. Techniques such as data compression and data lightning are proposed. | [24] |
| Trade-offs for decreasing latency | Techniques like off-chain transactions and sharding reduce latency but introduce trade-offs requiring further research to balance scalability, security, and decentralization. | [41] |
| Quality of service (QoS) metrics | Existing consensus models often fail to meet desired QoS levels, indicating a need for novel resource scheduling strategies. | [42] |
| Privacy challenges in blockchains | The transparency of the blockchain ledger complicates ensuring data privacy and confidentiality, with techniques being contingent on specific implementations. | [43] |
| Impact on reliability and data integrity | The blockchain enhances data security in fog computing but raises concerns about data reliability and integrity, especially with corrupted data entry. | [44] |
| Technological maturity | The emergent nature of both fog computing and blockchains presents challenges related to their technological maturity and understanding of their long-term implications. | [45] |
| Area | Key Challenges | Future Research Directions |
|---|---|---|
| Scalability | Handling large volumes of data | Explore new algorithms and architectures that improve blockchain scalability without compromising security or decentralization. |
| Security | Enhancing data privacy | Develop advanced encryption methods and privacy-preserving techniques tailored for fog computing environments. |
| Efficiency | Reducing latency | Investigate off-chain solutions and more efficient consensus mechanisms that reduce transaction validation times. |
| Integration | Seamless technology fusion | Study frameworks and standards that facilitate easier integration of blockchains with fog computing and IoT devices. |
| Environmental Impact | Energy consumption of PoW | Research into less energy-intensive consensus algorithms like Proof of Stake (PoS) or Directed Acyclic Graph (DAG) technologies. |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Aldossri, R.; Aljughaiman, A.; Albuali, A. Advancing Drone Operations through Lightweight Blockchain and Fog Computing Integration: A Systematic Review. Drones 2024, 8, 153. https://doi.org/10.3390/drones8040153
Aldossri R, Aljughaiman A, Albuali A. Advancing Drone Operations through Lightweight Blockchain and Fog Computing Integration: A Systematic Review. Drones. 2024; 8(4):153. https://doi.org/10.3390/drones8040153
Chicago/Turabian StyleAldossri, Rawabi, Ahmed Aljughaiman, and Abdullah Albuali. 2024. "Advancing Drone Operations through Lightweight Blockchain and Fog Computing Integration: A Systematic Review" Drones 8, no. 4: 153. https://doi.org/10.3390/drones8040153
APA StyleAldossri, R., Aljughaiman, A., & Albuali, A. (2024). Advancing Drone Operations through Lightweight Blockchain and Fog Computing Integration: A Systematic Review. Drones, 8(4), 153. https://doi.org/10.3390/drones8040153






