1. Introduction
Drones were considered for several applications and case studies because of their flexible flight capabilities, which include flying at low altitudes, at high elevation angles, and over urban, suburban, and rural areas [
1]. The typical drone is outfitted with all of the electronic components required to carry out its mission in an efficient manner. These components include a communication module for transmitting data to the ground station (GS), sensors for gathering data, memory for storing the information collected by the sensors, as well as computational and power resources to process information and maintain flight for a predetermined amount of time, respectively [
2,
3,
4,
5]. In addition, recent advancements in fifth-generation (5G) wireless communications made possible the concept of cellular networks beyond 5G (B5G), which may fully unlock the promise of autonomous services and provide wide coverage for drones. Drones outfitted with AI systems in flight would be possible with the faster data transfer rates made possible by a B5G network. The most important development in B5G is satellite integration, which allows drones to deliver centimeter-level precise positioning, global coverage, and heterogeneous QoS provisioning [
6,
7]. If legal provisions permit drone integration with B5G and autonomous flying, the sky will be filled with drones performing activities such as mail and package delivery, traffic monitoring, event filming, surveillance, search and rescue, and marine monitoring [
8].
Drones are typically not designed with security and privacy concerns in mind, leaving them vulnerable to both cyber and physical attacks [
9,
10,
11]. Intruders who wish to compromise the security and privacy of a drone have a variety of options. They could, for instance, send out numerous reservation requests, eavesdrop on control communications, and/or forge data exchange [
12]. Due to unreliable connections and insufficient security protocols, anyone with the proper transmitter can attach to a drone and embed commands into an ongoing session, making them readily interceptable [
13]. If drones fly over a hostile environment, they could become an enticing target for physical attacks. This is another security and privacy concern. In these situations, an intruder can deceive captured drones to gain access to their internal data via standard interfaces or terminals.
Many drone systems depend on the GNSS (global navigation satellite system) for precise location, navigation, and timing for safe and efficient operation. GLONASS, Galileo, BeiDou, and NavIC are also used in drones, although global positioning system (GPS) is the most common. All GNSS systems are subject to cyber-physical attacks [
14,
15]. For example, GPS spoofing [
16] is another significant security threat that occurs when an adversary manipulates the drone’s GPS signals. In this attack, an adversary transmits fake GPS signals to an intended drone at a slightly higher frequency than the real GPS signals, so that the drone believes it is located elsewhere. In B5G networks, however, drones can be linked to new wireless technologies such as visible light communications and quantum communications, which could introduce new security threats [
1]. The best GNSS system for a drone application depends on the use case, precision, and dependability needed, and system risks and vulnerabilities. Drone operators should be aware of GNSS attack threats and take precautions such as employing backup navigation systems or secure communication methods. Additional security mechanisms and countermeasures will be necessary to combat such security hazards.
The deployment of non-terrestrial infrastructures as part of the B5G network, also known as the integrated space and terrestrial drone networks, is regarded as a topic of the long term with the aim of improving coverage rates [
17].
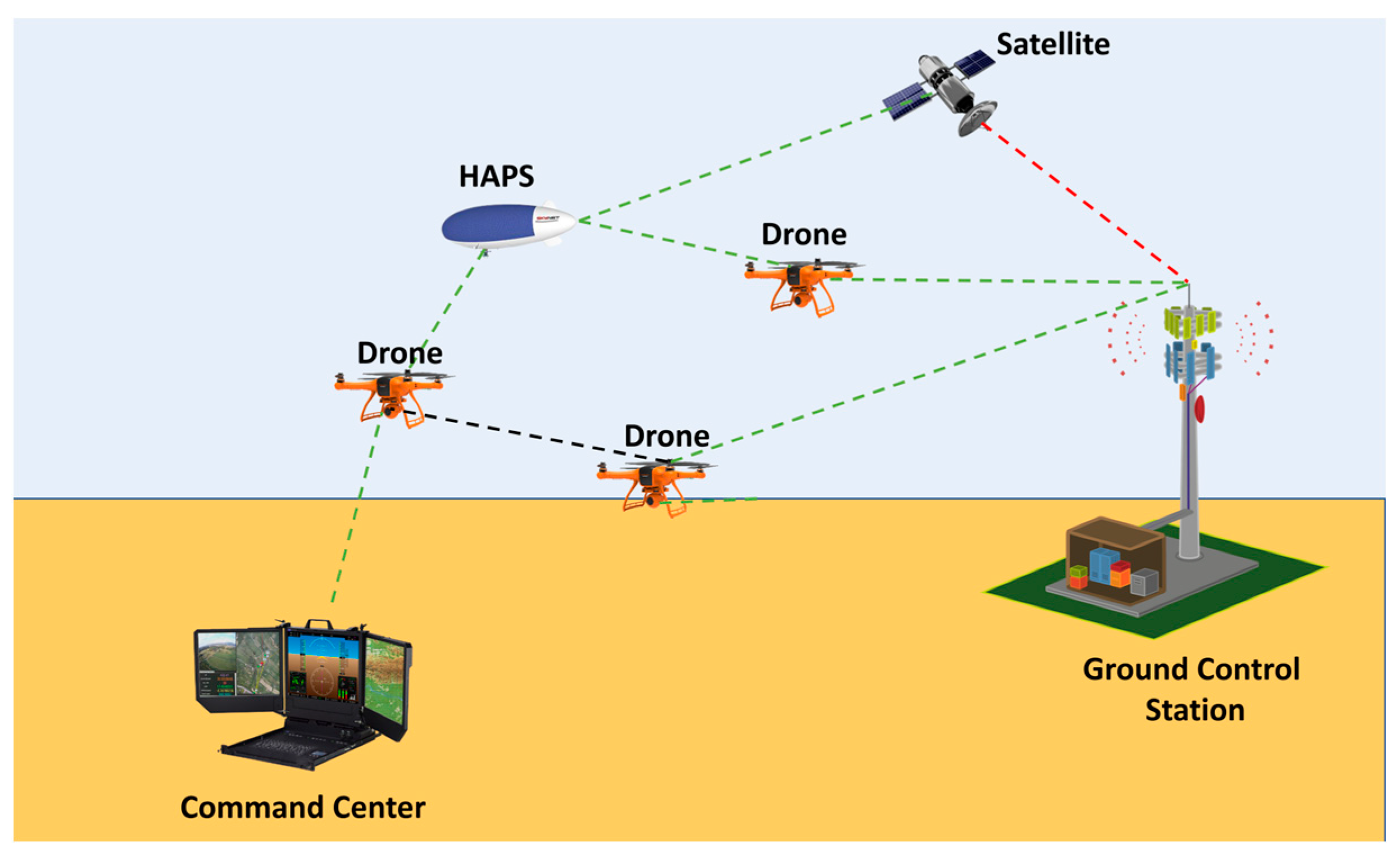
Figure 1 depicts a typical drone architecture for B5G networks, which may include drones, a command center (CC), ground control stations (GCS), and satellites. The stations that can command drones are the CCs, GCSs, and satellites. When a CC intends to issue direct mission commands to drones, digital signcryption ensures the commands’ authenticity, integrity, and confidentiality. However, a drone occasionally performs remote tasks beyond the CC’s range, preventing the CC from communicating directly with the drones. In this scenario, the CC designates a GCS in the drone’s proximity as an agent, and the GCS transmits commands directly to the drone. A proxy signcryption scheme can be used to achieve confidentiality and authentication of the transmitted commands and ensure the drone executes commands in a timely manner.
Using either the public key infrastructure (PKI), a certificateless cryptosystem (CLC), or an identity-based cryptosystem (IBC), the proxy signcryption scheme can be developed. PKI’s primary shortcoming is that its standard application cannot be used with drones. Certificate management overhead, such as certificate storage, distribution, and revocation, is the crucial factor that renders them unsuitable for drone systems [
18]. IBC [
19] is implemented to alleviate the burden on conventional PKI, which uses a publicly recognized string as a public key to reduce the cost of PKI certificate renewal. Being identity-based, the IBC appears to be more vulnerable to external infiltration (key escrow problem). CLC [
20] was developed to address these problems. Key generation center (KGC) generates and distributes partial private keys to network participants. The user will then generate his or her own private and public keys by combining a private key fragment with some arbitrarily generated integers. Therefore, certificateless proxy signcryption scheme is the optimal solution for drones’ system requirements. As a result, we strengthened the proxy signcryption scheme with the following new features, which represent our most significant contributions:
We propose a resource-friendly certificateless proxy signcryption scheme for drones in B5G networks. The proposed scheme is based on the elliptic curve cryptography (ECC) algorithm and enjoys some of its favorable features, such as no key escrow and no secure channel.
The proposed scheme has a clear distribution of roles: the control center acts as the original signer, the network provider serves as the key generation center (KGC), the ground control station acts as a proxy, and the drones perform the task of un-signcryption.
The proposed protocol guarantees anonymity for both senders and receivers by employing a mechanism wherein participants (), where , send their identities in an encrypted form while requesting a partial private key.
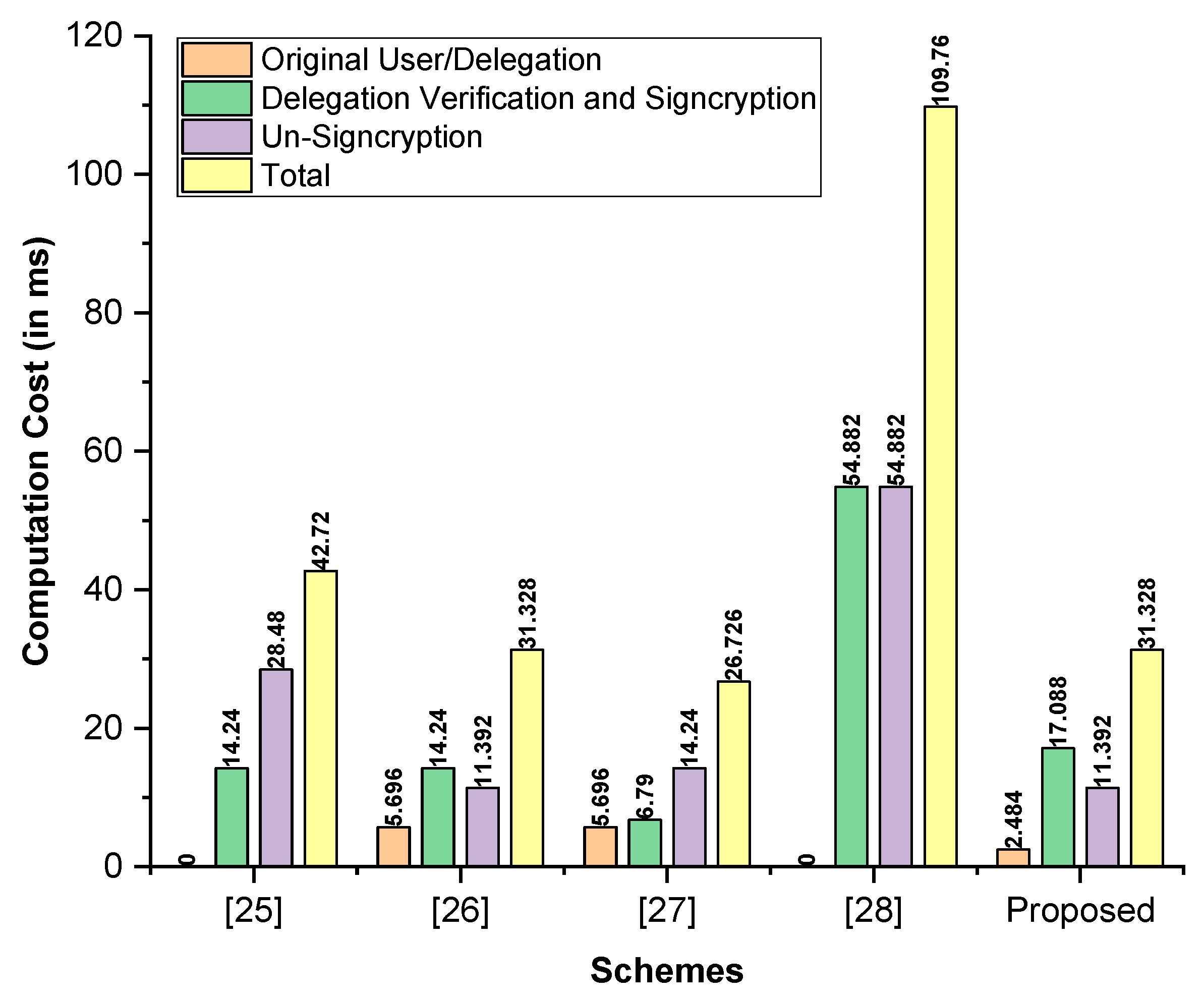
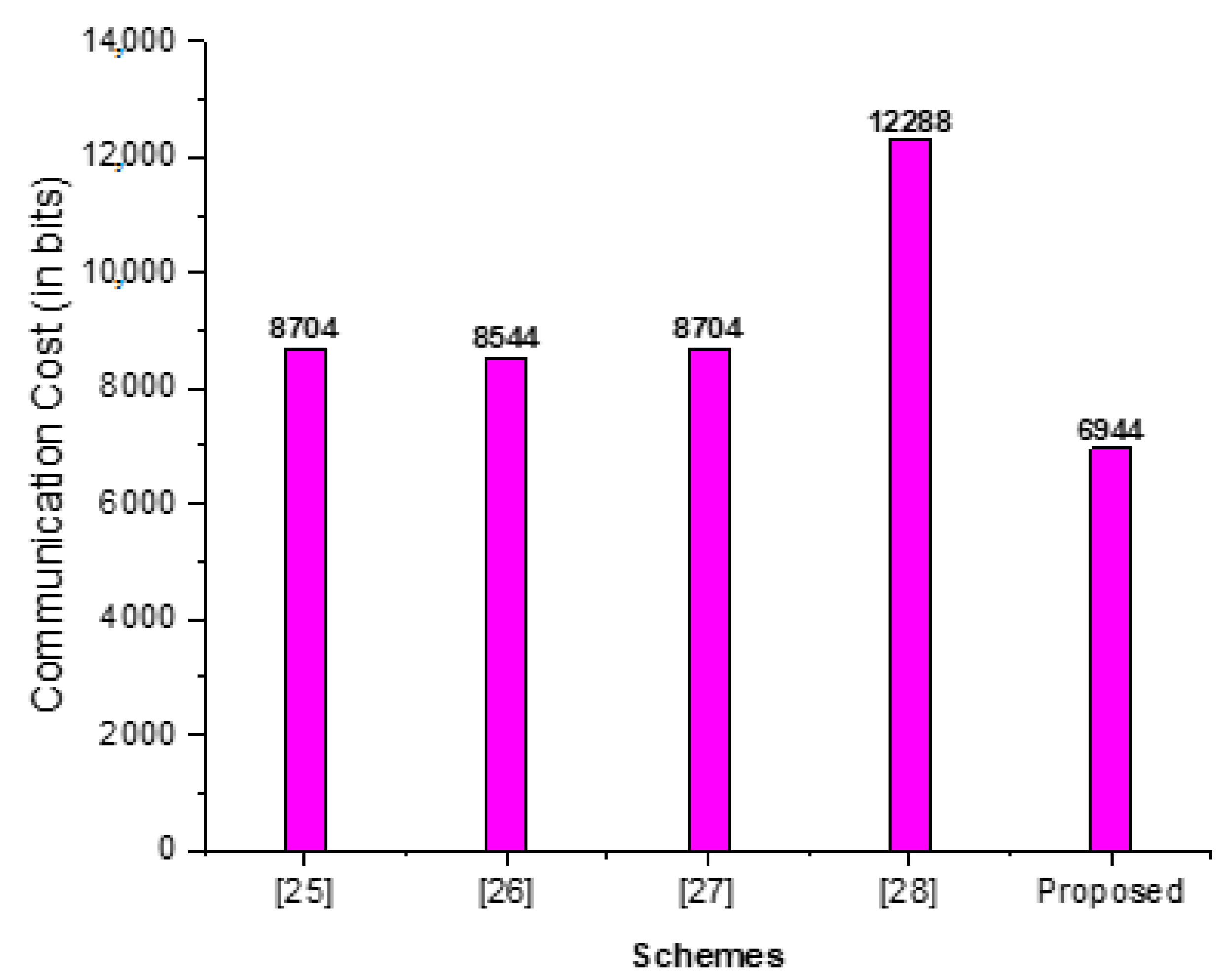
The proposed scheme is capable of withstanding a wide variety of commonly known attacks under ROM. Additionally, it was found that this scheme is efficient in terms of both computation and communication costs when compared to other existing schemes.
The remainder of this article is structured as follows. The literature review is covered in
Section 2.
Section 3 explains the network model and construction of the proposed scheme. The security analysis is discussed in
Section 4.
Section 5 discusses performance analysis. The conclusion of the proposed work is discussed in
Section 6.
3. Preliminaries
This section explains the random oracle model (ROM), adversarial or threat model, syntax, and network model of the proposed certificateless proxy signcryption scheme.
3.1. Random Oracle Model
In 1993, Bellare and Rogaway created the random oracle model (ROM). By considering hash functions as random oracles, this model makes it simple to verify the security of cryptographic algorithms that use hash functions. In this paradigm, any input will result in an output of a predetermined length. If the input was requested previously, the oracle returns the same value as it did previously. If the input is not one that the oracle previously received, the oracle returns a randomly chosen output. You can substitute a hash function with an accessible random function (the “random oracle”). Therefore, an adversary must consult the random number generator to determine what the hash function will do.
3.2. Adversarial or Threat Model
This section will outline potential security vulnerabilities that could compromise the confidentiality of the security parameter utilized in the generation of ciphertext and signatures. Two types of adversaries, namely Type 1 Type 1 () and Type 2 (), are defined. The first type of attacker, denoted as Type 1 (), is an external threat actor who aims to compromise the confidentiality of the proposed scheme and engage in signature forgery. It should be noted that the entity denoted as () lacks the capability to access the private keys of the user, yet possesses the ability to replace the public key of said user.
Type 2 () is the insider attacker (malicious ) who desires to violate confidentiality and falsify the signature of the proposed scheme. It should be noted that the entity denoted as possesses the capability to access the private key of , yet lacks the ability to substitute the public key of the user. The primary objective for both adversaries is to reveal the parameters utilized in the creation of the secret key and ciphertext. The subsequent objective entails the construction or retrieval of parameters utilized in the computation of a signature, followed by the generation of a forge signature.
3.3. Syntax of Certificateless Proxy Signcryption
The syntax of the proposed scheme contains the following steps.
Setup: Here, the network provider () assumes the role of KGC; when it receives the security parameter , generates his private key (), his public key (), and public parameters set
Partial Key Generation (PCGU): The participant () desires a partial private key () from , first, it sends through insecure network to . Alternatively, when receives , it generates and sends as an encrypted partial private and public key to over an insecure network.
Public and Private Key Generation (PBCGU): When receives , it sets () to his public key and sets ( to his private key.
Delegation Generation (DG): This phase is run by the CC and when it receives (), where and are the identities of CC and GCS, respectively, is CC’s private key pair, and () is GCS’s public key pair. After that, CC generates and sends the triple as a delegation to the GCS through an open network.
Delegation Verification (DV): When is received by the GCS, then it can perform verification procedures, to check whether the signature is valid or not.
CL-Proxy Signcryption Generation (CL-PSG): This phase is executed by the GCS, which generates and sends the triple ( as a proxy signcryption to drone via an open network.
CL-Proxy Un-Signcryption (CL-PU-S): When is received by the drone, it performs the verifications steps, to check whether the signature is valid or not, if the signature is valid, it performs decryption process to recover plaintext from ciphertext.
3.4. Network Model
The command center (CC), ground control stations (GCS), high altitude platform system (HAPS), drones, and satellites comprise the network architecture for the proposed scheme. Each drone is equipped with a variety of useful components, including cameras, a global positioning system (GPS), an inertial measurement unit (IMU), and sensors, which can be utilized in a variety of application scenarios. In contrast to terrestrial communication systems, satellite services depend on geostationary satellites to transmit and receive signals in out-of-range regions. Additionally, HAPS provides greater coverage/relay and interacts with satellites, enabling more reliable drone communication networks, particularly when satellite communications are disrupted by inclement weather. HAPS may utilize B5G, and the drones require no additional equipment.
The networks depicted in
Figure 1 comprise of several stations, namely the CCs, GCSs, HAPs, and satellites, which possess the capability to command drones. Digital signcryption ensures the authenticity, confidentiality, and integrity of direct mission commands issued by a CC to drones. Occasionally, a drone conducts remote duties beyond the CC’s range, preventing direct communication between the CC and the drones. In this scenario, the CC identifies a nearby GCS as an agent, and the GCS transmits commands directly to the drone. The proposed scheme operates under the assumption that HAPs function as the Key Generation Center (KGC).
4. Construction of the Proposed Scheme
The proposed scheme is comprised of seven algorithms: Setup, Partial Key Generation (PCGU), Public and Private Key Generation (PBCGU), Delegation Generation (DG), Delegation Verification (DV), CL-Proxy Signcryption Generation (CL-PSG), and CL-Proxy Un-Signcryption (CL-PU-S). The subsequent sub-phases further define the constructions of the seven algorithms listed above. The symbols used in the proposed scheme are listed in
Table 1.
Setup: Here, the network provider () assumes the role of KGC; when it receives the security parameter , executes the steps outlined below.
Selects the group of order and , which will be the generator of ;
Selects four hash functions ;
Sets is the plaintext length and will be the length of selected parameter;
Selects the system private key as and computes the public key ;
can made as the public parameter and distributes it throughout a network.
Partial Key Generation (PCGU): If a participant (), where , desires a partial private key () from , it first selects , computes , computes calculates , and then, sends through insecure network to . Alternatively, when receives , it executes the following calculations: Computes , recovers identity as , and then, selects and computes . In addition, computes , calculates , and sends as an encrypted partial private and public key to over an insecure network.
Public and Private Key Generation (PBCGU): When receives , it computes , sets () to his public key and sets ( to his private key.
Delegation Generation (DG): This phase is run by the CC and when it receives (), where and are the identities of CC and GCS, respectively, is CC’s private key pair, and () is GCS’s public key pair.
Consequently, CC will execute the subsequent steps to generate a delegation signature for warrant .
It selects , computes , and ;
Computes and sends the triple as a delegation to the GCS through an open network.
Delegation Verification (DV): When is received by the GCS, the following verification procedures are carried out.
Computes and ;
If , then accept otherwise, an error message is returned.
CL-Proxy Signcryption Generation (CL-PSG): This phase is executed by the GCS, which generates a certificateless proxy signcryption using the procedures below.
It selects , computes ;
Computes ;
Computes and ;
Computes and ;
Finally, it sends the triple ( as a proxy signcryption to drone via an open network.
CL-Proxy Un-Signcryption (CL-PU-S): When is received by the drone, it performs the following verifications steps.
Computes and ;
Computes and ;
If , then accept otherwise, an error message is returned.
Correctness
The
can compute the secret key
by using the following computations.
The
recovers/ decrypts the user identity by using the following computations.
The
recovers/decrypts the partial public and partial private key by using the following computations.
The
GCS can verify the delegated text
by using the following computations.
The drone can compute the secret key
by using the following computations.
The drone can recover/decrypts the message
by using the following computations.
The drone can verify the proxy signcrypted text
by using the following computations.
5. Security Analysis
In order to carry out the provable security analysis of the proposed scheme, which makes use of a well-known method of formal security analysis called as the random oracle model, the proposed scheme is secured against Type 1 () and Type 2 () adversaries. When these adversaries attempted to violate the confidentiality and forge the original signature, the subsequent sub-steps elucidated the role of (Type 1 () and Type 2 () and the security hard problems upon which our scheme’s security is based.
Elliptic Curve Diffie–Hellman Problem (ECDHP): Given (), finding the values of from is hard and is reported to ECDHP.
Elliptic Curve Discrete Logarithm Problem (ECDLP): Given (), finding the value of from is hard and is reported to ECDLP.
By utilizing the following theorems, we will elucidate how the proposed scheme withstands against Type 1 () and Type 2 ().
Theorem 1. In this theorem, we are going to perform the IND-SFCPS-CCA2 game between and to break the confidentiality of the proposed scheme, in which performs the role helper for to obtain the solution of ECDHP. Suppose wins with the non-ignorable advantage () in the game IND-SFCPS-CCA2 and get the solution for ECDHP with the advantage of . Where, and represent a query for and , and represents a proxy signcryption query.
Proof. Given (), the task of is to extract the value from with the help of . The following is the process in which with the help of could solve the above problem.
Setup: Here, selects computes , makes a param , and sends to Then, can ask for the following queries.
Find Stage: Here, in this section, can ask for the following polynomial bounded queries.
Query: If receives as a query from , checks for in the list , if it is available, it sends to otherwise, choose , here, its probability as . Then, it checks, if , and then chooses sends to and adds into . If , sets , and returns to .
Query: If receives as a query from , checks for in the list , if it is available, it sends to otherwise, chooses sends to and adds into .
Query: If receives as a query from , checks for in the list , if it is available, it sends to otherwise, chooses sends to and adds into .
Query: If receives as a query from , checks for in the list , if it is available, it sends to otherwise, chooses sends to and adds into .
PCGU Query If receives as a query from checks for in the list , if it is available, it sends to otherwise, chooses computes , sends to , and adds into .
Private Key Query If receives as a query from checks for in the list , if it is available, it sends to Otherwise, chooses obtained from sends to , and add into .
Public Key Query If receives as a query from checks for in the list , if it is available, it sends to Otherwise, searches and finds from and , and then computes , sends to , and adds into .
Replace Public Key Query: sends ( to and can replace on ( for the identity
Delegation Generation Query: sends two identity () and a warrant to it then checks the tuple in . If , it can abort further processing. Otherwise, it extracts from , from , chooses , generates , and sends it to .
CL-Proxy Signcryption Query: sends two identities () and a message to it then checks the tuple in ; if , it can abort further processing. Otherwise, it extracts from , from , chooses , generates ( and sends it to .
CL-Proxy Un-Signcryption Query: sends two identities () and ( to it then checks the tuple in , the response is then provided in the subsequent methods.
If , can obtain from according to identity , from , performs the algorithm and sends to .
If , can get from and computes perform the algorithm. can further obtains from , from , from the list , and can verify the equation . If the condition is met, the output is (m); otherwise, the procedure is repeated with new parameters.
Challenge Stage: Suppose and is adaptively generated two distinct messages by and sends () and two challenged identities () to . Then, checks for the tuple in , if , stop; otherwise, it chooses ( randomly and sends it to as a challenge ciphertext.
Guess Stage: can make sure Query Query, Query Query, PCGU Query, Private Key Query, Public Key Query, Replace Public Key Query, Delegation Generation Query, CL-Proxy Signcryption Query, CL-Proxy Un-Signcryption Query is performed as same as above in Find Stage. So, returns , can made Query with . In this situation, the valid answer for ECDHP is included to . The second situation is that can ignore the randomly selected/guessed value of , then randomly selects from and computes , where already knows the value , and . Otherwise, failed to solve ECDHP.
So, we are going to evaluate the above process with success probability. The success probability will be when made PCGU Query and Private Key Query for The success probability will be when successfully selects from . The success probability will when is not halting this game’s simulation. We can say that can obtain the solution for ECDHP with the advantage as follows: □
Theorem 2. In this theorem, we are going to perform the IND-SFCPS-CCA2 game between and to breaks the confidentiality of the proposed Scheme, in which performs the role of helper for to obtain the solution of ECDHP. Suppose wins with the non-ignorable advantage () in the game IND-SFCPS-CCA2 and gets the solution for ECDHP with the advantage of . Where and represents a query for and , and represents a proxy signcryption query.
Proof. Given (), the task of is to extract the value from with the help of . The following is the process in which with the help of could solve the above problem.
Setup: Here, selects computes , make a param , and sends and to Then, can ask for the following queries.
Find Stage: Here, in this section, can ask for the following polynomial bounded queries.
The queries such as Query, Query, Query, Query are identical to those performed in Theorem 1.
PCGU Query If receives as a query from checks for in the list . If it is available, it sends to Otherwise, chooses computes , sends to , and adds into .
Private Key Query If receives as a query from checks for in the list . If it is available, it sends to Otherwise, chooses obtained from sends to , and adds into .
Public Key Query If receives as a query from checks for in the list , if it is available, it sends to Otherwise, searches and finds from and , and then computes , sends to and adds into .
Delegation Generation Query: sends two identity () and a warrant to it then checks the tuple in ; if , it can abort further processing. Otherwise, it extracts from , from , chooses , generates , and sends it to .
CL-Proxy Signcryption Query: sends two identities () and a message to it then checks the tuple in ; if , it can abort further processing. Otherwise, it extracts from , from , chooses , generates ( and sends it to .
CL-Proxy Un-Signcryption Query: sends two identities () and ( to it then checks the tuple in , and it gives the response in the following ways.
If , can obtain from according to identity , from , perform the algorithm, and sends to .
If , can obtain from , compute , and perform the algorithm. further can get from , from , from the list , and can verify the equation ; if it is satisfied, its output will be otherwise, it repeats this process again with new parameters.
Challenge Stage: Suppose and adaptively generated two distinct messages by and send () and two challenged identities () to . Then, checks for the tuple in , if , stop; otherwise, it chooses ( randomly and sends it to as a challenge ciphertext.
Guess Stage: can ensure Query Query, Query Query, PCGU Query, Private Key Query, Delegation Generation Query, CL-Proxy Signcryption Query, CL-Proxy Un-Signcryption Query is performed as same as above in Find Stage of Theorem 1 and Public Key Query of Theorem 2. So, returns , can make Query with ; in this situation, the valid answer for ECDHP includes . The second situation is that can ignore the randomly selected/guessed value of , then randomly selects from and computes , where already knows the value , and . Otherwise, failed to solve ECDHP.
Therefore, we will evaluate the preceding procedure based on its success probability. The success probability will be when made PCGU Query and Private Key Query for The success probability will be when successfully selects from . The success probability will when is not stopped in the simulation of this game. So, we can say that can obtain the solution for ECDHP with the following advantages: □
Theorem 3. In this theorem, we are going to perform the EUF-SFCPS-CMA game between and to forge the signature of the proposed scheme, in which perform the role helper for to get the solution of ECDLP. Suppose wins with the non-ignorable advantage () in the game EUF-SFCPS-CMA and get the solution for ECDLP with the advantage of . Where and represents a query for and , and represents a proxy Signcryption query.
Proof. Given (, the task of is to extract the value from with the help of . The following are the processes in which with the help of , could solve the above problem.
Setup: Here, selects computes , makes a param , and sends to Then, can ask for the following queries.
Find Stage: Here, in this section, can ask for the following polynomial bounded queries.
Query Query, Query Query, PCGU Query, Private Key Query, Public Key Query, Replace Public Key Query, Delegation Generation Query, CL-Proxy Signcryption Query, CL-Proxy Un-Signcryption Query is performed in the same way as above in Find Stage of Theorem 1.
Forgery: As can ask for the following polynomial-bounded queries: Query Query, Query Query, PCGU Query, Private Key Query, Public Key Query, Replace Public Key Query, Delegation Generation Query, CL-Proxy Signcryption Query, CL-Proxy Un-Signcryption Query is performed as same as above in Find Stage of Theorem 1 and generates a forged proxy signcryption triple ( with the help of . Note that can only solve the ECDLP if it accessed the actual value for and from .
So, we are going to evaluate the above process with success probability. The success probability will be when made PCGU Query and Private Key Query for The success probability will be when successfully selects from . The success probability will when does not stop the simulation of this game. So, we can say that can obtain solution for ECDHP with the followed advantages: . □
Theorem 4. In this theorem, we are going to perform the EUF-SFCPS-CMA game between and to forge the signature of the proposed scheme, in which performs the role helper for to get the solution of ECDHP. Suppose wins with the non-ignorable advantage () in the game EUF-SFCPS-CMA and get the solution for ECDLP with the advantage of , where and represents a query for and , and represents a proxy signcryption query.
Proof. Given (, the task of is to extract the value from with the help of . The following are the processes in which with the help of , could solve the above problem.
Setup: Here, selects computes , makes a param , and sends and to Then, can ask for the following queries.
Find Stage: Here, in this section, can ask for the following polynomial-bounded queries: Query Query, Query Query, PCGU Query, Private Key Query, Delegation Generation Query, CL-Proxy Signcryption Query, CL-Proxy Un-Signcryption Query is performed in the same way as above in Find Stage of Theorem 1 and Public Key Query of Theorem 2.
Forgery: As can ask for the following polynomial-bounded queries: Query Query, Query Query, PCGU Query, Private Key Query, Delegation Generation Query, CL-Proxy Signcryption Query, CL-Proxy Un-Signcryption Query is performed as same as above in Find Stage of Theorem 1 and Public Key Query of Theorem 2. Furthermore, it generates a forged proxy signcryption triple ( with the help of . Note that can only solve the ECDLP if it accessed the actual value for and from .
So, we are going to evaluate the above process with success probability. The success probability will be when made PCGU Query and Private Key Query for The success probability will be when successfully selects from . The success probability will when does not stop the simulation of this game. So, we can say that can obtain solution for ECDHP with the following advantages: □