Vehicle to Everything (V2X) and Edge Computing: A Secure Lifecycle for UAV-Assisted Vehicle Network and Offloading with Blockchain
Abstract
1. Introduction
1.1. Objectives and Contributions
- This paper proposes B-UV2X, a novel and secure distributed UAV-assisted vehicular network infrastructure for IoV interconnectivity. The designed system realizes interoperable communication between devices in the V2X environment with blockchain;
- A blockchain-enabled standardized lifecycle is designed. The main objective is to maintain the process hierarchy throughout transactions acquisition towards deliverance in a secure manner;
- A consortium network with doppler spread is deployed for edge-enabled IoV systems to handle requests related to permissioned or permissionless environments;
- To protect individual transactions of the IoV, B-UV2X uses a proxy re-encryption threshold mechanism. Furthermore, a multi-consensus protocol is created with the predefined method of the digital signature of the hyperledger to schedule the list of node transaction executions, which helps in the management of resources;
- In this paper, three different types (IoV connectivity and data management, record updates, and exchanging) of smart contracts are created and deployed;
- Finally, this paper highlights the implementation challenges faced in the process of B-UV2X deployment, with future open research questions. Possible solutions are discussed.
1.2. Section Distribution
2. Related Work
2.1. Vehicle-to-Everything (V2X) and UAV-Assisted Vehicle Network
2.2. Internet of Vehicles and Mobile Edge Computing with Blockchain
3. Preliminary Knowledge of the Proposed B-UV2X
3.1. Notation, Problem Formulation, and Description
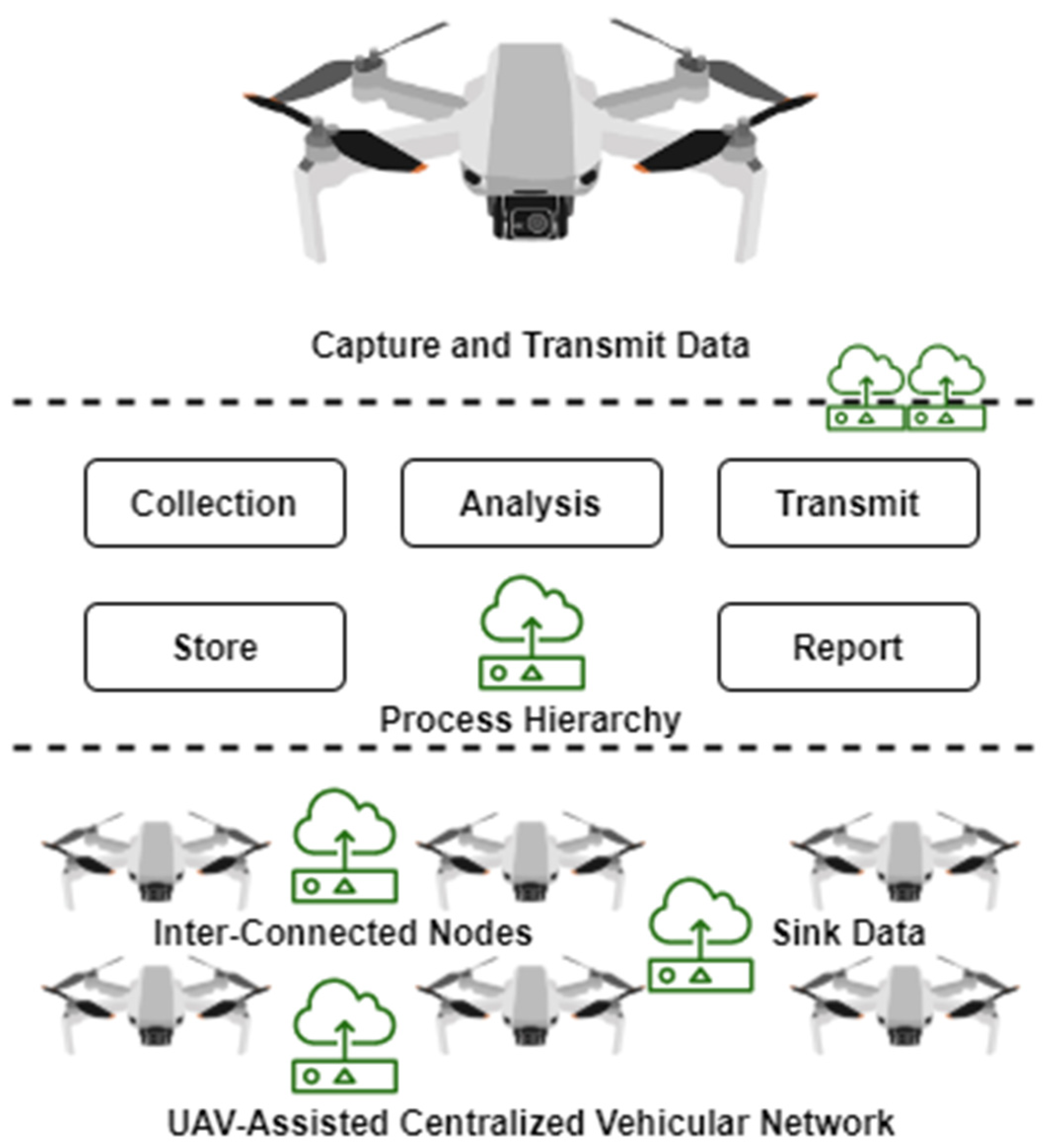
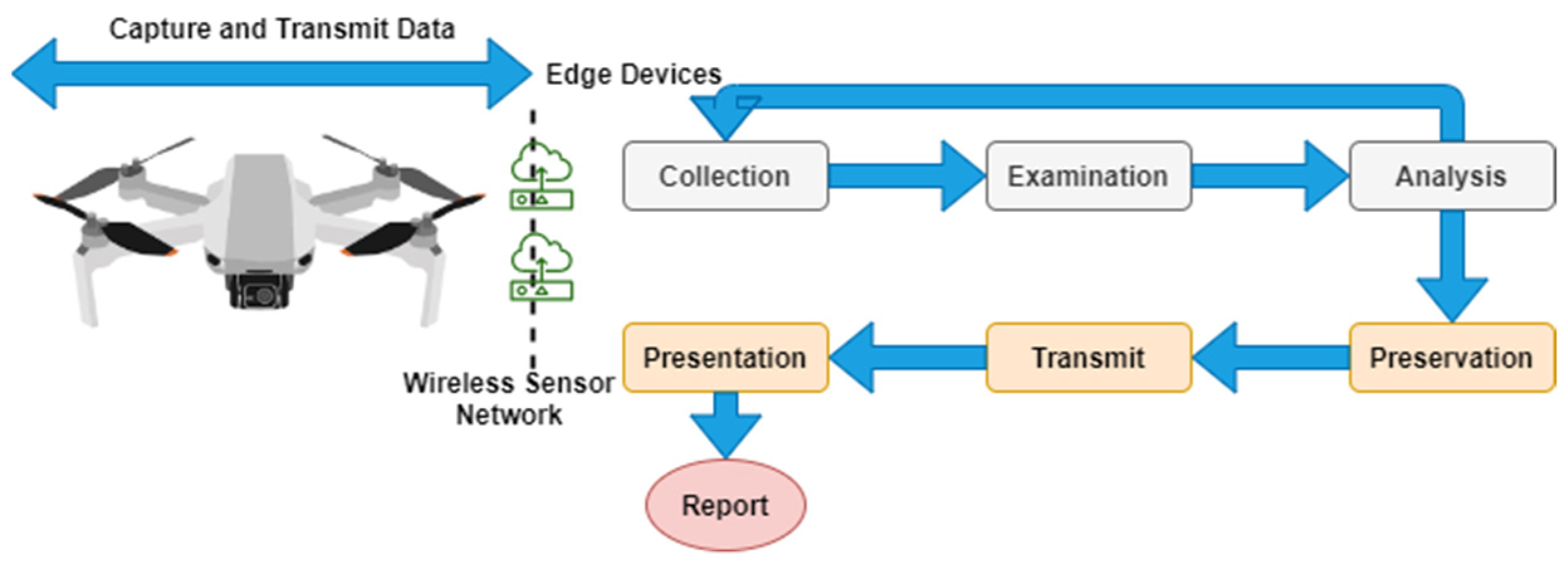
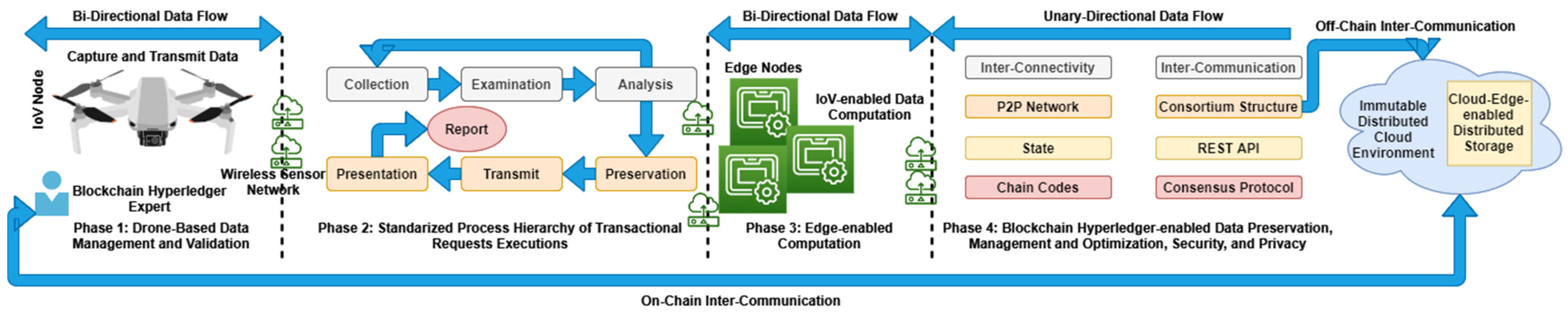
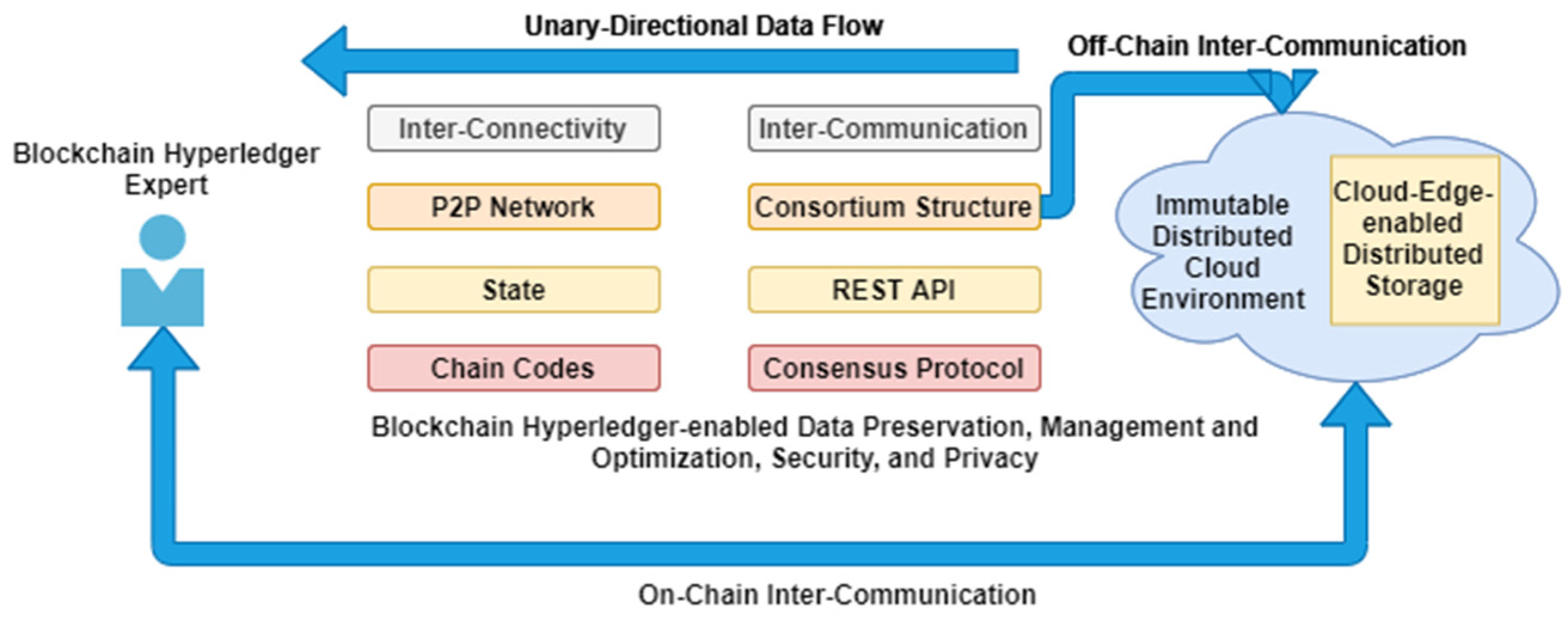
3.2. Proposed Architecture
3.3. Smart Contracts Implementation
4. Simulations, Results, and Discussion
- Heterogeneous node connectivity;
- 4MB size of transactional nodes;
- Single network bandwidth used
- Cloud-edge enabled customized distributed storage deployed;
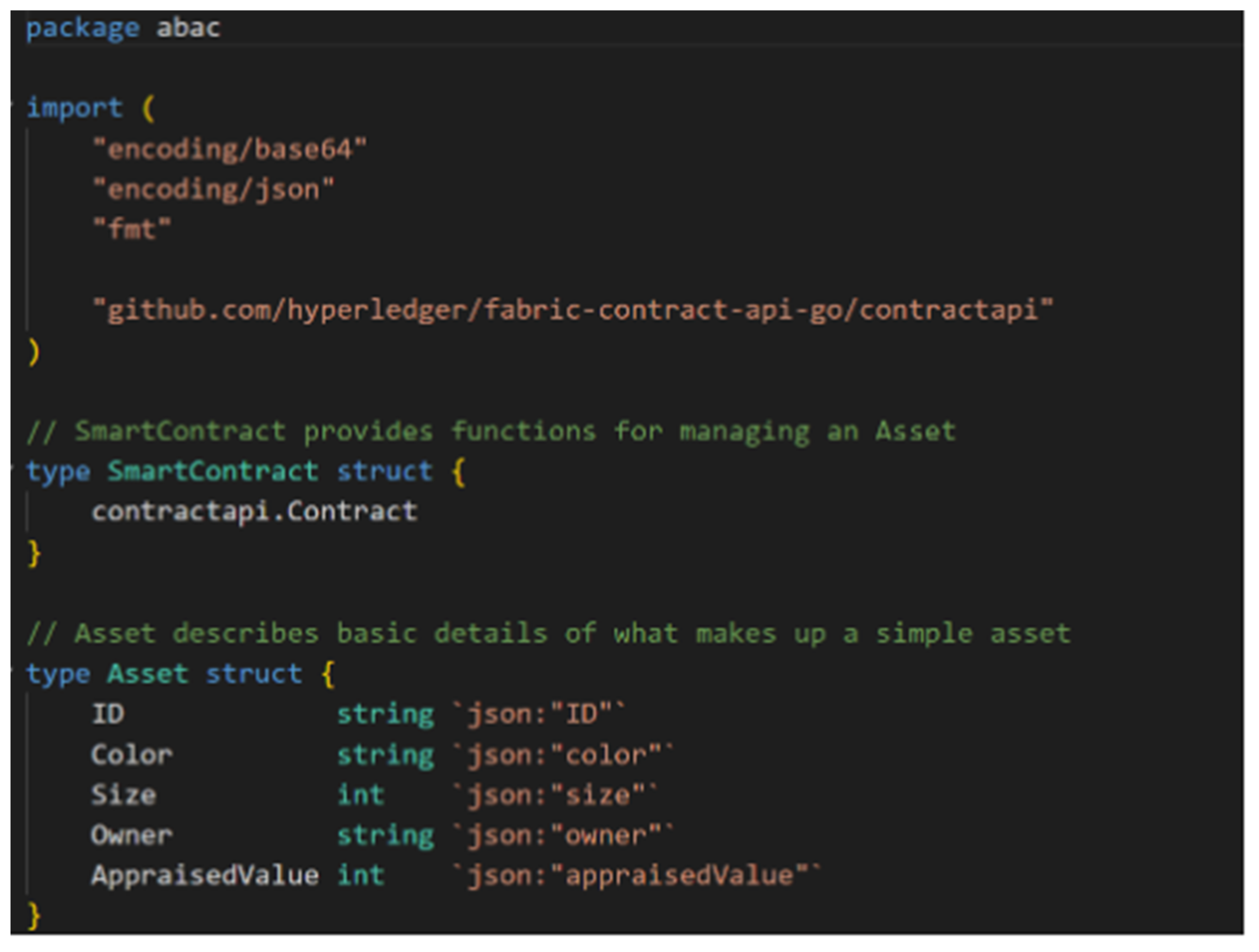
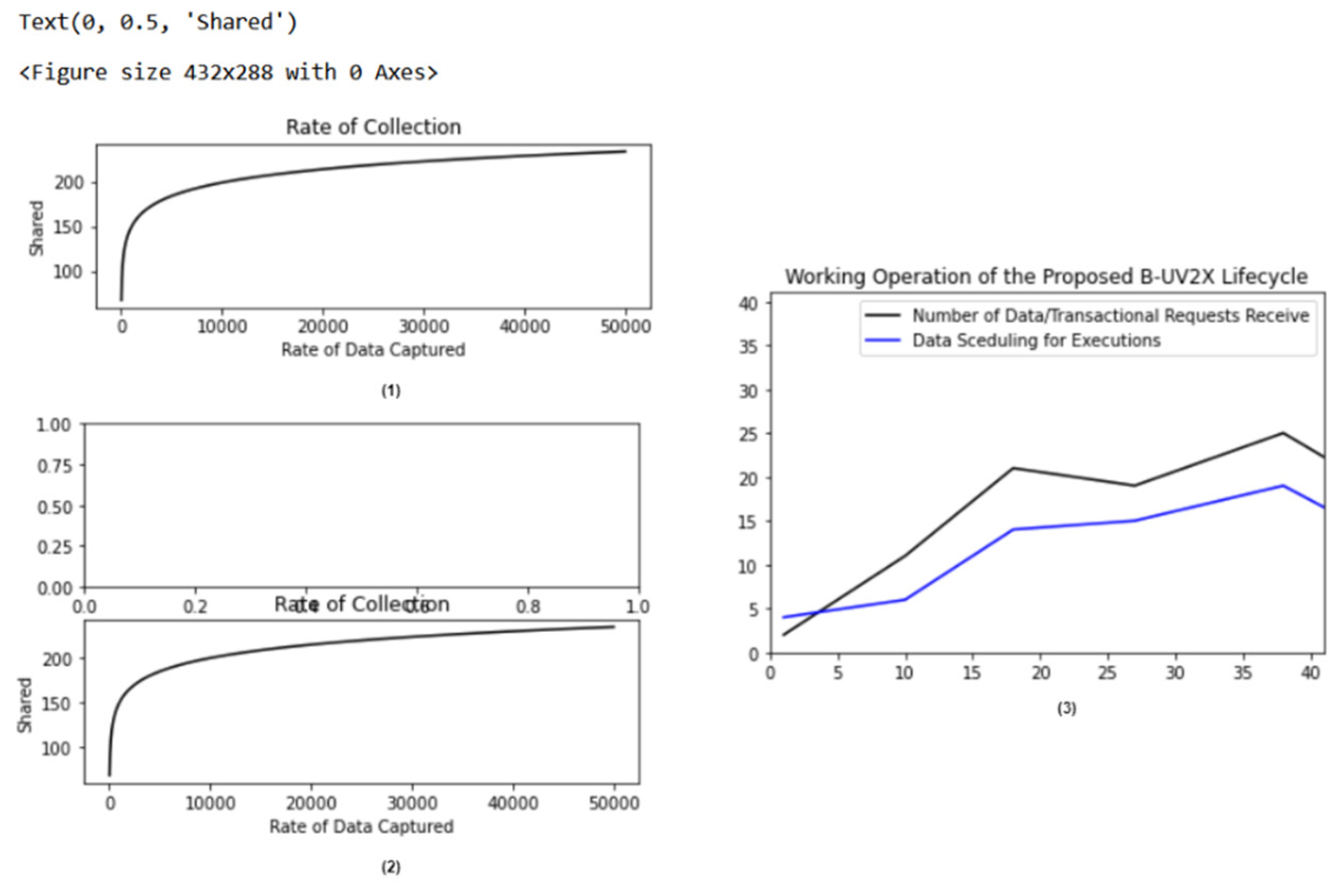
- Blockchain hyperledger expert initiates a chain of the transactional requests of IoVs, as shown in Figure 5 (the test code of smart contract/chain codes with MPoS consensus is presented, along with the parameters of simulations executions).
5. Current Status of Edge Computing and Related Implementation Issues
5.1. Edge Computing Integrated with Outsourced Computation
5.2. Vehicle to Everything-Enabled Distributed Node Interconnectivity
5.3. Role of Blockchain Hyperledger Technology in Edge Computing Environment
5.4. Drone-Based Data Management and Monitoring
6. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Lv, Z.; Qiao, L.; Hossain, M.S.; Choi, B.J. Analysis of Using Blockchain to Protect the Privacy of Drone Big Data. IEEE Netw. 2021, 35, 44–49. [Google Scholar] [CrossRef]
- Gumaei, A.; Al-Rakhami, M.; Hassan, M.M.; Pace, P.; Alai, G.; Lin, K.; Fortino, G. Deep Learning and Blockchain with Edge Computing for 5G-Enabled Drone Identification and Flight Mode Detection. IEEE Netw. 2021, 35, 94–100. [Google Scholar] [CrossRef]
- Cheema, M.A.; Ansari, R.I.; Ashraf, N.; Hassan, S.A.; Qureshi, H.K.; Bashir, A.K.; Politis, C. Blockchain-based secure delivery of medical supplies using drones. Comput. Netw. 2022, 204, 108706. [Google Scholar] [CrossRef]
- Hasan, M.K.; Islam, S.; Shafiq, M.; Ahmed, F.R.A.; Ataelmanan, S.K.M.; Babiker, N.B.M.; Abu Bakar, K.A. Communication Delay Modeling for Wide Area Measurement System in Smart Grid Internet of Things Networks. Wirel. Commun. Mob. Comput. 2021, 2021, 9958003. [Google Scholar] [CrossRef]
- Khan, A.A.; Laghari, A.A.; Awan, S.; Jumani, A.K. Fourth Industrial Revolution Application: Network Forensics Cloud Security Issues. In Security Issues and Privacy Concerns in Industry 4.0 Applications; John Wiley & Sons, Inc.: Hoboken, NJ, USA, 2021; pp. 15–33. [Google Scholar] [CrossRef]
- Feng, C.; Yu, K.; Bashir, A.K.; Al-Otaibi, Y.D.; Lu, Y.; Chen, S.; Zhang, D. Efficient and Secure Data Sharing for 5G Flying Drones: A Blockchain-Enabled Approach. IEEE Netw. 2021, 35, 130–137. [Google Scholar] [CrossRef]
- Li, T.; Liu, W.; Liu, A.; Dong, M.; Ota, K.; Xiong, N.N.; Li, Q. BTS: A Blockchain-Based Trust System to Deter Malicious Data Reporting in Intelligent Internet of Things. IEEE Internet Things J. 2021, 9, 22327–22342. [Google Scholar] [CrossRef]
- Khan, A.A.; Laghari, A.A.; Shaikh, A.A.; Dootio, M.A.; Estrela, V.V.; Lopes, R.T. A blockchain security module for brain-computer interface (BCI) with Multimedia Life Cycle Framework (MLCF). Neurosci. Inform. 2021, 2, 100030. [Google Scholar] [CrossRef]
- Alsamhi, S.H.; Almalki, F.A.; Afghah, F.; Hawbani, A.; Shvetsov, A.V.; Lee, B.; Song, H. Drones’ Edge Intelligence Over Smart Environments in B5G: Blockchain and Federated Learning Synergy. IEEE Trans. Green Commun. Netw. 2021, 6, 295–312. [Google Scholar] [CrossRef]
- Aloqaily, M.; Bouachir, O.; Boukerche, A.; Al Ridhawi, I. Design Guidelines for Blockchain-Assisted 5G-UAV Networks. IEEE Netw. 2021, 35, 64–71. [Google Scholar] [CrossRef]
- Shafiq, M.; Tian, Z.; Bashir, A.K.; Cengiz, K.; Tahir, A. SoftSystem: Smart Edge Computing Device Selection Method for IoT Based on Soft Set Technique. Wirel. Commun. Mob. Comput. 2020, 2020, 8864301. [Google Scholar] [CrossRef]
- Khan, A.A.; Wagan, A.A.; Laghari, A.A.; Gilal, A.R.; Aziz, I.A.; Talpur, B.A. BIoMT: A State-of-the-Art Consortium Serverless Network Architecture for Healthcare System Using Blockchain Smart Contracts. IEEE Access 2022, 10, 78887–78898. [Google Scholar] [CrossRef]
- Luo, S.; Li, H.; Wen, Z.; Qian, B.; Morgan, G.; Longo, A.; Rana, O.; Ranjan, R. Blockchain-Based Task Offloading in Drone-Aided Mobile Edge Computing. IEEE Netw. 2021, 35, 124–129. [Google Scholar] [CrossRef]
- Khan, A.A.; Shaikh, A.A.; Shaikh, Z.A.; Laghari, A.A.; Karim, S. IPM-Model: AI and metaheuristic-enabled face recognition using image partial matching for multimedia forensics investigation with genetic algorithm. Multimedia Tools Appl. 2022, 81, 23533–23549. [Google Scholar] [CrossRef]
- Abualigah, L.; Diabat, A.; Sumari, P.; Gandomi, A.H. Applications, Deployments, and Integration of Internet of Drones (IoD): A Review. IEEE Sens. J. 2021, 21, 25532–25546. [Google Scholar] [CrossRef]
- Khan, A.A.; Shaikh, Z.A.; Belinskaja, L.; Baitenova, L.; Vlasova, Y.; Gerzelieva, Z.; Laghari, A.A.; Abro, A.A.; Barykin, S. A Blockchain and Metaheuristic-Enabled Distributed Architecture for Smart Agricultural Analysis and Ledger Preservation Solution: A Collaborative Approach. Appl. Sci. 2022, 12, 1487. [Google Scholar] [CrossRef]
- Shaikh, Z.A.; Khan, A.A.; Teng, L.; Wagan, A.A.; Laghari, A.A. BIoMT Modular Infrastructure: The Recent Challenges, Issues, and Limitations in Blockchain Hyperledger-Enabled E-Healthcare Application. Wirel. Commun. Mob. Comput. 2022, 2022, 813841. [Google Scholar] [CrossRef]
- Wang, D.; Wu, M.; He, Y.; Pang, L.; Xu, Q.; Zhang, R. An HAP and UAVs Collaboration Framework for Uplink Secure Rate Maximization in NOMA-Enabled IoT Networks. Remote. Sens. 2022, 14, 4501. [Google Scholar] [CrossRef]
- Wang, D.; Zhou, F.; Lin, W.; Ding, Z.; Al-Dhahir, N. Cooperative Hybrid Non-Orthogonal Multiple Access Based Mobile-Edge Computing in Cognitive Radio Networks. IEEE Trans. Cogn. Commun. Netw. 2022, 8, 1104–1117. [Google Scholar] [CrossRef]
- Singh, M.P.; Aujla, G.S.; Bali, R.S. Blockchain for the Internet of Drones: Applications, Challenges, and Future Directions. IEEE Internet Things Mag. 2021, 4, 47–53. [Google Scholar] [CrossRef]
- Khan, A.A.; Khan, M.M.; Khan, K.M.; Arshad, J.; Ahmad, F. A blockchain-based decentralized machine learning framework for collaborative intrusion detection within UAVs. Comput. Netw. 2021, 196, 108217. [Google Scholar] [CrossRef]
- Gupta, R.; Bhattacharya, P.; Tanwar, S.; Kumar, N.; Zeadally, S. GaRuDa: A Blockchain-Based Delivery Scheme Using Drones for Healthcare 5.0 Applications. IEEE Internet Things Mag. 2021, 4, 60–66. [Google Scholar] [CrossRef]
- Aujla, G.S.; Vashisht, S.; Garg, S.; Kumar, N.; Kaddoum, G. Leveraging Blockchain for Secure Drone-to-Everything Communications. IEEE Commun. Stand. Mag. 2021, 5, 80–87. [Google Scholar] [CrossRef]
- Yahuza, M.; Idris, M.Y.I.; Bin Ahmedy, I.; Wahab, A.W.A.; Nandy, T.; Noor, N.M.; Bala, A. Internet of Drones Security and Privacy Issues: Taxonomy and Open Challenges. IEEE Access 2021, 9, 57243–57270. [Google Scholar] [CrossRef]
- Wang, J.; Liu, Y.; Niu, S.; Song, H. Lightweight blockchain assisted secure routing of swarm UAS networking. Comput. Commun. 2021, 165, 131–140. [Google Scholar] [CrossRef]
- Mei, Q.; Xiong, H.; Zhao, Y.; Yeh, K.-H. Toward Blockchain-Enabled IoV with Edge Computing: Efficient and Privacy-Preserving Vehicular Communication and Dynamic Updating. In Proceedings of the 2021 IEEE Conference on Dependable and Secure Computing (DSC), Aizuwakamatsu, Japan, 30 January–2 February 2021; pp. 1–8. [Google Scholar] [CrossRef]
- Wang, D.; He, T.; Zhou, F.; Cheng, J.; Zhang, R.; Wu, Q. Outage-driven link selection for secure buffer-aided networks. Sci. China Inf. Sci. 2022, 65, 182303. [Google Scholar] [CrossRef]
- Al-Hourani, A.; Kandeepan, S.; Lardner, S. Optimal LAP Altitude for Maximum Coverage. IEEE Wirel. Commun. Lett. 2014, 3, 569–572. [Google Scholar] [CrossRef]
- He, Y.; Wang, D.; Huang, F.; Zhang, R.; Pan, J. Trajectory Optimization and Channel Allocation for Delay Sensitive Secure Transmission in UAV-Relayed VANETs. IEEE Trans. Veh. Technol. 2022, 71, 4512–4517. [Google Scholar] [CrossRef]
- Islam, S.; Badsha, S.; Sengupta, S.; La, H.; Khalil, I.; Atiquzzaman, M. Blockchain-Enabled Intelligent Vehicular Edge Computing. IEEE Netw. 2021, 35, 125–131. [Google Scholar] [CrossRef]
- Jiang, X.; Yu, F.R.; Song, T.; Leung, V.C. Edge Intelligence for Object Detection in Blockchain-Based Internet of Vehicles: Convergence of Symbolic and Connectionist AI. IEEE Wirel. Commun. 2021, 28, 49–55. [Google Scholar] [CrossRef]
- Yang, J.; Liu, J.; Song, H.; Liu, J.; Lei, X. Blockchain-based Conditional Privacy-Preserving Authentication Protocol with Implicit Certificates for Vehicular Edge Computing. In Proceedings of the 2022 7th International Conference on Cloud Computing and Big Data Analytics (ICCCBDA) 2022, Chengdu, China, 22–24 April 2022; pp. 210–216. [Google Scholar] [CrossRef]
- Jing, W.; Fu, X.; Liu, P.; Song, H. Joint resource trading and computation offloading in blockchain enhanced D2D-assisted mobile edge computing. Clust. Comput. 2022, 1–15. [Google Scholar] [CrossRef]
- Xu, L.; Ge, M.; Wu, W. Edge Server Deployment Scheme of Blockchain in IoVs. IEEE Trans. Reliab. 2022, 71, 500–509. [Google Scholar] [CrossRef]
- Zhang, D.; Yu, F.R.; Yang, R. Blockchain-Based Multi-Access Edge Computing for Future Vehicular Networks: A Deep Compressed Neural Network Approach. IEEE Trans. Intell. Transp. Syst. 2021, 23, 12161–12175. [Google Scholar] [CrossRef]
- Wang, K.; Tu, Z.; Ji, Z.; He, S. Faster Service with Less Resource: A Resource Efficient Blockchain Framework for Edge Computing. 2022. Available online: https://assets.researchsquare.com/files/rs-1719287/v1_covered.pdf?c=1654894162 (accessed on 31 October 2022).
- Shaikh, Z.A.; Khan, A.A.; Baitenova, L.; Zambinova, G.; Yegina, N.; Ivolgina, N.; Laghari, A.A.; Barykin, S.E. Blockchain Hyperledger with Non-Linear Machine Learning: A Novel and Secure Educational Accreditation Registration and Distributed Ledger Preservation Architecture. Appl. Sci. 2022, 12, 2534. [Google Scholar] [CrossRef]
- Ahmed, M.M.; Hasan, M.K.; Shafiq, M.; Qays, O.; Gadekallu, T.R.; Nebhen, J.; Islam, S. A peer-to-peer blockchain based interconnected power system. Energy Rep. 2021, 7, 7890–7905. [Google Scholar] [CrossRef]
- Khan, A.A.; Laghari, A.A.; Gadekallu, T.R.; Shaikh, Z.A.; Javed, A.R.; Rashid, M.; Estrela, V.V.; Mikhaylov, A. A drone-based data management and optimization using metaheuristic algorithms and blockchain smart contracts in a secure fog environment. Comput. Electr. Eng. 2022, 102, 108234. [Google Scholar] [CrossRef]


| Title of the Article | Proposed Method/Procedure | Research Gaps in the Study | Similarities and Differences with the Proposed B-UV2X |
|---|---|---|---|
| Internet of Drones (IoD) applications with blockchain [20] | The authors of this paper discussed the role of blockchain and its integration in the improvement of IoD connectivity and security, as well as the importance of distributed applications for drone-based data management and monitoring in a protected manner, especially in smart-city environments. |
|
|
| A decentralized machine learning framework for intrusion detection in UAV using blockchain distributed ledger modular infrastructure [21] | This paper presents a distributed framework for intrusion detection using integrated machine learning and blockchain technologies. In this design, the system is potentially able to significantly enhance the integrity, transparency, and storage of information for smart decision-making among multiple UAVs. |
|
|
| Drone-based delivery scheme for industrial healthcare using blockchain technology [22] | This paper highlights the list of current blockchain-based drone-enabled industrial healthcare applicational challenges and limitations. These include harsh environmental conditions, rough terrain, war-prone areas, congested traffic, remote location, etc. |
|
|
| Internet of Drones (IoD): communication leveraging with blockchain [23] | The authors of this paper presented a security approach for drone-to-everything communication, in which the locations of drones are traced by segment divisions of the areas in which they are deployed. |
|
|
| Internet of Vehicles (IoV) security [24] | In this paper, the authors defined the taxonomy of IoD security and privacy along with access to the controlled airspace to provide an inter-location navigation service using AI, machine learning, blockchain, and federated learning. |
|
|
| A lightweight assisted secure routing scheme for the IoV using blockchain Ethereum [25] | A secure routing algorithm for IoT-enabled drone management swarm UAS networking is proposed in this research. The benefits are as follows:
|
|
|
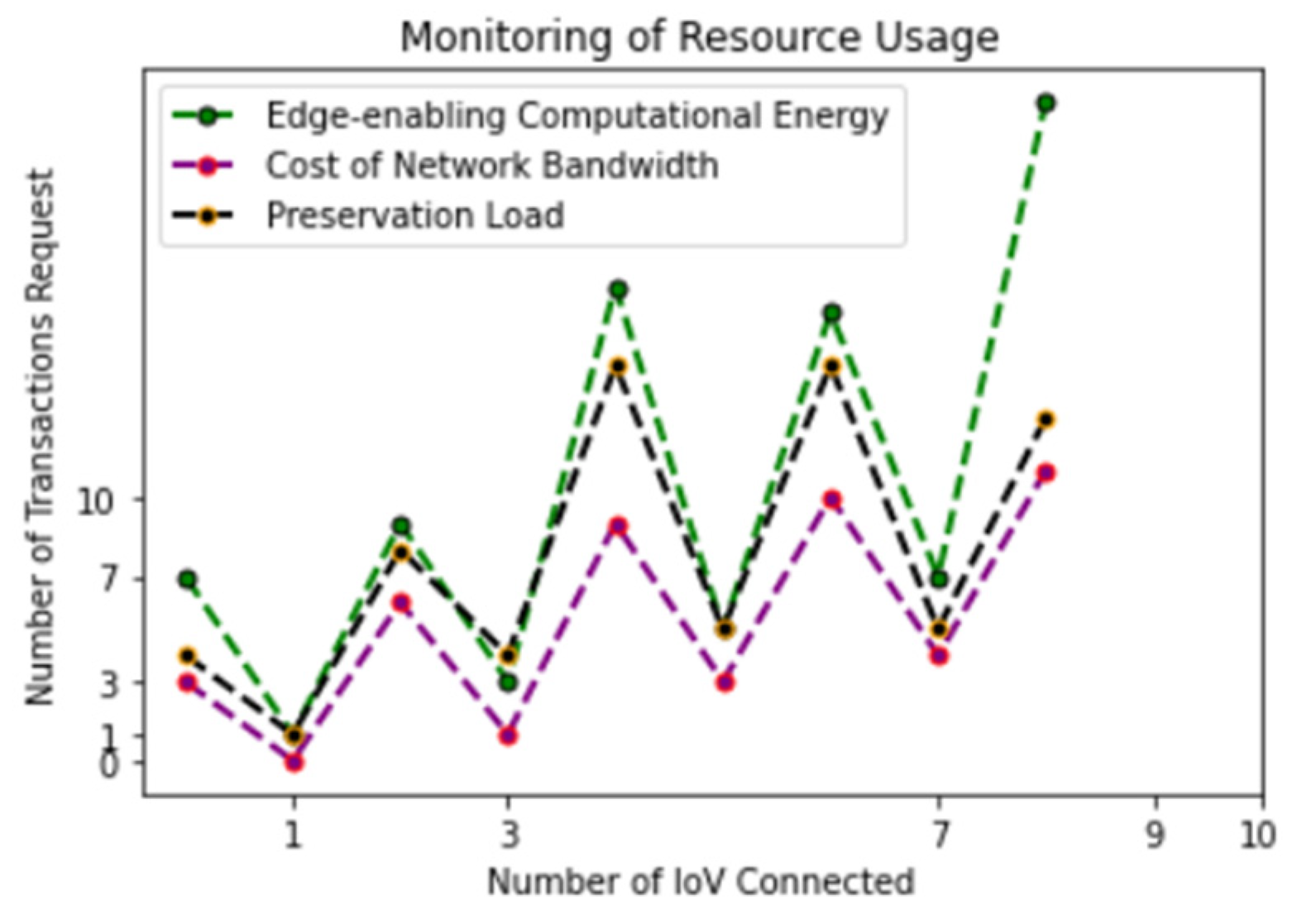
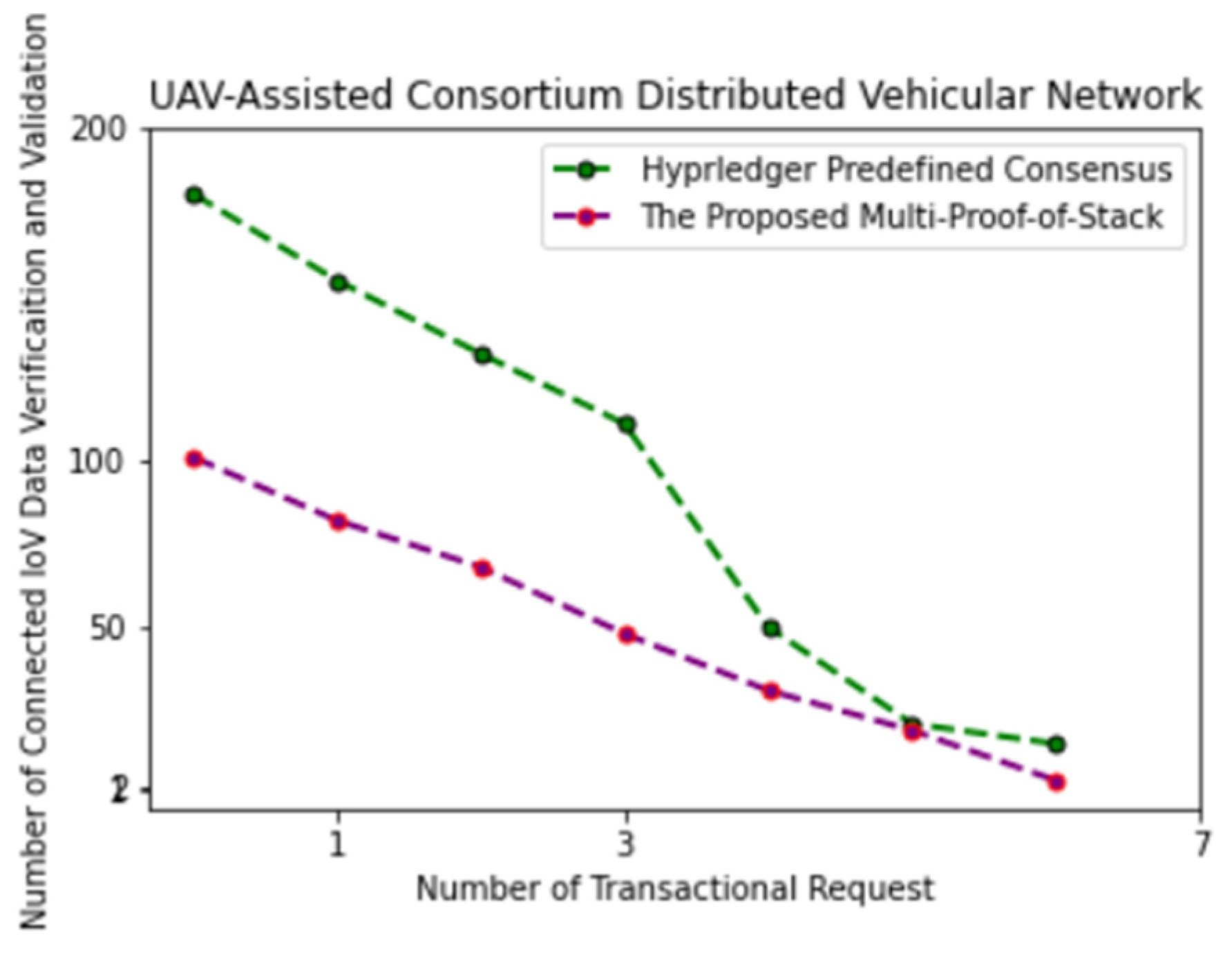
Input Variables: The engineer of the blockchain hyperledger is the person to initiate chain/transactional requests. Manages events of node (IoV) transactions executions and preservation. Stakeholder registration (verification and validation). Exchange information between the participating nodes. Updates logs/records and sharing. Assumptions and Declaration: int main().File[x].X: IoV node/device registration, IoVReg(); Stakeholder registration (smart cities), StkReg(); UAV-assisted vehicular lifecycle, UAVAVLC(); Add new transaction/request details, AddNTD(); Resource management and monitoring, ResMM(); Consortium channels, Ccha(); Update transactions, UpdTr(); Exchange information, ExInfo(); Data/information preservation, InfoPre(); Blockchain fabric timestamp [run]; Blockchain hyperledger expert schedule list of requests and executions, Counter + 1; Count(request/executed); Executions: if IoV is not in IoVReg(), then, AddNTD() and exchange; if transactions initiated/requested passes through UAVAALC(), then, AddNTD(), ResMM(), Ccha(), and ExInfo(); Multi-Proof-of-Stack (MPoS()), Digital signature (after receiving 51% consensus votes), Consensus(); Counter + 1, updTr(), and InfoPre(); else check error, change state, share, exchange, and preserve, terminate; else check error, change state, share, exchange, and preserve, terminate; Outputs: IoVReg(); UAVAVLC(); AddNTD(); UpdTr(); and InfoPre(); |
| Methodology of Other State-of-the-Art Methods | Main Contributions | Analytical Matrices of Other State-of-the-Art Methods | Proposed B-UV2X |
|---|---|---|---|
| A resource trading, computational offloading, and management approach for enhanced drone-to-drone assisted environment using blockchain distributed ledger [33] |
|
| The analytical matrices of the proposed B-UV2X are as follows:
|
| Edge-enabled mobile server deployment scheme for IoVs with blockchain [34] |
|
| |
| A multi-access edge computing for vehicular network using a deep neural approach [35] |
|
| |
| A resource efficient framework for IoVs using blockchain, AI, and edge computing [36] |
|
|
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Khan, A.A.; Laghari, A.A.; Shafiq, M.; Awan, S.A.; Gu, Z. Vehicle to Everything (V2X) and Edge Computing: A Secure Lifecycle for UAV-Assisted Vehicle Network and Offloading with Blockchain. Drones 2022, 6, 377. https://doi.org/10.3390/drones6120377
Khan AA, Laghari AA, Shafiq M, Awan SA, Gu Z. Vehicle to Everything (V2X) and Edge Computing: A Secure Lifecycle for UAV-Assisted Vehicle Network and Offloading with Blockchain. Drones. 2022; 6(12):377. https://doi.org/10.3390/drones6120377
Chicago/Turabian StyleKhan, Abdullah Ayub, Asif Ali Laghari, Muhammad Shafiq, Shafique Ahmed Awan, and Zhaoquan Gu. 2022. "Vehicle to Everything (V2X) and Edge Computing: A Secure Lifecycle for UAV-Assisted Vehicle Network and Offloading with Blockchain" Drones 6, no. 12: 377. https://doi.org/10.3390/drones6120377
APA StyleKhan, A. A., Laghari, A. A., Shafiq, M., Awan, S. A., & Gu, Z. (2022). Vehicle to Everything (V2X) and Edge Computing: A Secure Lifecycle for UAV-Assisted Vehicle Network and Offloading with Blockchain. Drones, 6(12), 377. https://doi.org/10.3390/drones6120377









