Assessment of Cybersecurity Awareness among Students of Majmaah University
Abstract
1. Introduction
- We assessed and explored the cybersecurity awareness level among college students at Majmaah University by concentrating on several safety factors for the use of the Internet.
- We investigated and analyzed the security knowledge and skills of students regarding information security and cybercrime using multiple statistical tests.
- We theoretically constructed approaches to enhance cybersecurity awareness among students and enlighten students about the hazards and challenges prevailing in computer networks.
- We suggest the best security measures and procedures based on the gap observed in the current state-of-the-art methods to handle incidents correctly and efficiently and embed security culture into the college environment.
2. Related Work
3. Methodology
3.1. Research Tools
3.2. Study Setting and Participants
3.3. Inclusion and Exclusion Criteria
3.4. Research Strategy
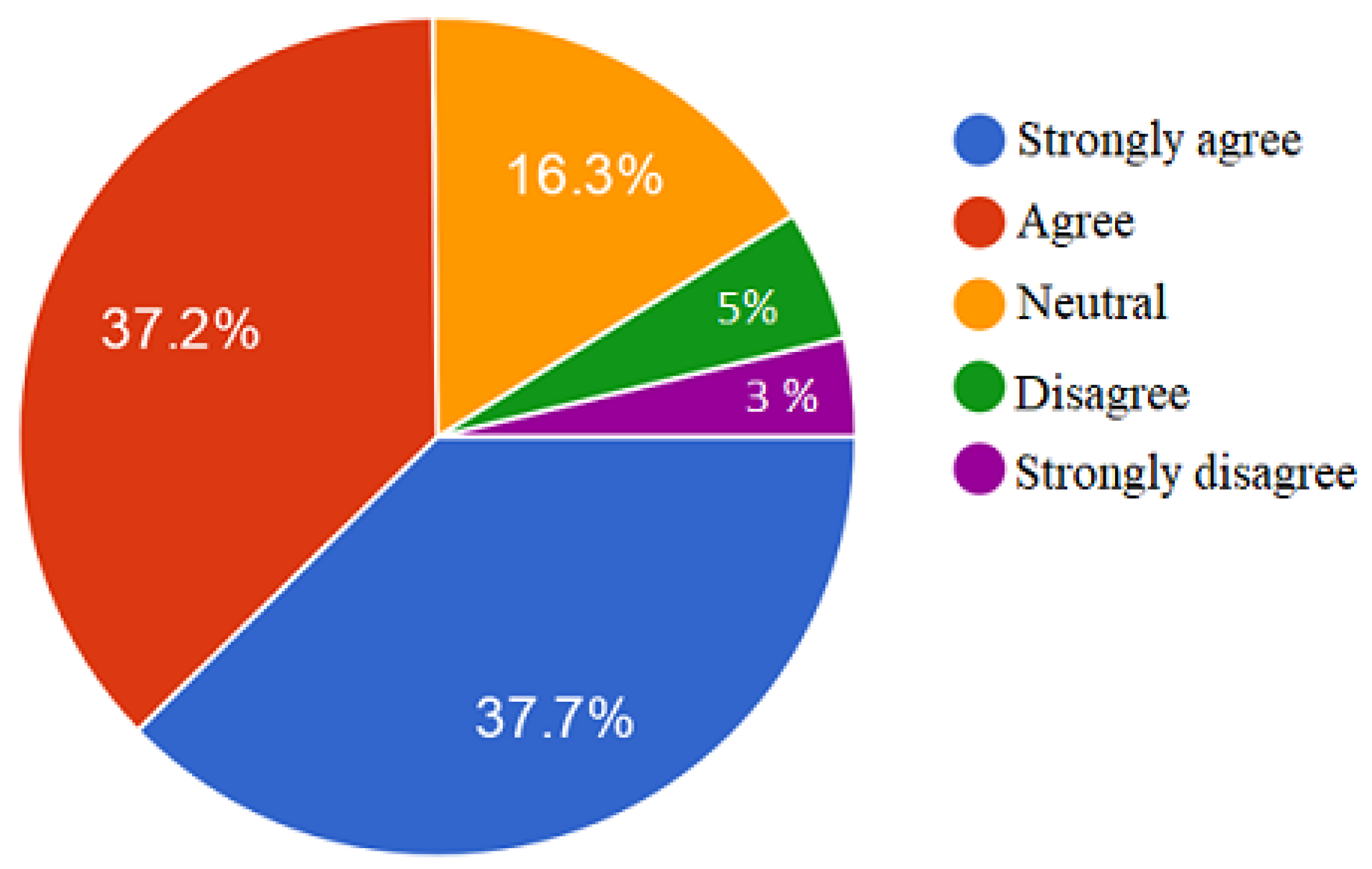
3.5. Respondents’ Impression
4. Results
4.1. Research Distribution
4.2. Knowledge of Main Cybersecurity Concepts
4.3. Knowledge of Cybersecurity Countermeasures
4.4. Knowledge of Password Management
4.5. Knowledge of Browser Security
4.6. Knowledge of Social Network Platforms
5. Discussion and Findings of Tests
5.1. Study Limitations
5.2. Reliability Test
5.3. Factor Analysis
6. Conclusions and Recommendations
- Majmaah University should promote knowledge on common cybersecurity factors, including vulnerabilities, attacks, and incidents, to their students to strengthen their security position.
- Passive awareness methods, such as email, oral presentation, newsletters, and SMS messages, are insufficient for educating users. There is a need to integrate more proactive methods, such as training and interviews. A combination of both methods is more effective and highly recommended.
- The delivery methods for cybersecurity awareness and training programs can be video-based, text-based, or game-based, as the target here is adult students. Security awareness must be taught at an early age to develop a sustainable cybersecurity behavior among users.
- Different datasets should be obtained from different universities and the findings should be systematically compared with those presented in this paper. Further questions should be added to cover all the important aspects of cybersecurity behavior.
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Gamreklidze, E. Cyber security in developing countries, a digital divide issue: The case of Georgia. J. Int. Commun. 2014, 20, 200–217. [Google Scholar] [CrossRef]
- Garg, A.; Curtis, J.; Halper, H. Quantifying the financial impact of IT security breaches. Inf. Manag. Comput. Secur. 2003, 11, 74–83. [Google Scholar] [CrossRef]
- Green, M.J.S. Cyber Security: An Introduction for Non-Technical Managers; Ashgate Publishing, Ltd.: Farnham, UK, 2015. [Google Scholar]
- Whitman, M.E.; Mattord, H.J. Principles of Information Security; Cengage Learning: Boston, MA, USA, 2011. [Google Scholar]
- Willard, N.E. Cyber-Safe Kids, Cyber-Savvy Teens: Helping Young People Learn to Use the Internet Safely and Responsibly; John Wiley & Sons: Hoboken, NJ, USA, 2007. [Google Scholar]
- Simsim, M.T. Internet usage and user preferences in Saudi Arabia. J. King Saud Univ. Eng. Sci. 2011, 23, 101–107. [Google Scholar] [CrossRef]
- Internet Usage in the Kingdom of Saudi Arabia. Available online: www.citc.gov.sa/en/reportsandstudies/studies/Pages/Computer-and-Internet-Usage-in-KSA-Study.aspx (accessed on 20 February 2021).
- Aboul Enein, S. Cybersecurity Challenges in the Middle East. Available online: https://www.gcsp.ch/publications/cybersecurity-challenges-middle-east (accessed on 30 April 2021).
- Sait, S.M.; Al-Tawil, K.M.; Ali, S.; Hussain, A. Use and effect of Internet in Saudi Arabia. 2003. Available online: https://core.ac.uk/download/pdf/242401013.pdf (accessed on 30 April 2021).
- Katz, F.H. The effect of a university information security survey on instruction methods in information security. In Proceedings of the 2nd Annual Conference on Information Security Curriculum Development, Kennesaw, GA, USA, 23–24 September 2005; pp. 43–48. [Google Scholar]
- Alshankity, Z.; Alshawi, A. Gender differences in internet usage among faculty members: The case of Saudi Arabia. In Proceedings of the 2008 Conference on Human System Interactions, Krakow, Poland, 25–27 May 2008. [Google Scholar]
- CITC Roles and Responsibilities. Available online: www.citc.gov.sa/en/RulesandSystems/RegulatoryDocuments/Pages/default.aspx (accessed on 20 February 2021).
- Hathaway, M.; Spidalieri, F.; Alsowailm, F. Kingdom of Saudi Arabia Cyber Readiness at a Glance; Potomac Institute for Policy Studies: Arlington, VA, USA, 2017. [Google Scholar]
- Nurunnabi, M. Transformation from an oil-based economy to a knowledge-based economy in Saudi Arabia: The Direction of Saudi Vision 2030. J. Knowl. Econ. 2017, 8, 536–564. [Google Scholar] [CrossRef]
- ALArifi, A.; Tootell, H.; Hyland, P. Information Security Awareness in Saudi Arabia. In Proceedings of the CONF-IRM, Vienna, Austria, 21–23 May 2012; Volume 57, pp. 1–11. [Google Scholar]
- Aloul, F.A. The need for effective information security awareness. J. Adv. Inf. Technol. 2012, 3, 176–183. [Google Scholar] [CrossRef]
- Boneh, D.; Lynn, B.; Shacham, H. Short signatures from the Weil pairing. In International Conference on the Theory and Application of Cryptology and Information Security; Springer: Berlin/Heidelberg, Germany, 2001; pp. 514–532. [Google Scholar]
- Liu, X.; Zhang, Y.; Wang, B.; Yan, J. Mona: Secure multi-owner data sharing for dynamic groups in the cloud. IEEE Trans. Parallel Distrib. Syst. 2012, 24, 1182–1191. [Google Scholar] [CrossRef]
- Kamara, S.; Lauter, K. Cryptographic cloud storage. In International Conference on Financial Cryptography and Data Security; Springer: Berlin/Heidelberg, Germany, 2010; pp. 136–149. [Google Scholar]
- Al-Janabi, S.; Al-Shourbaji, I. A study of cyber security awareness in educational environment in the middle east. J. Inf. Knowl. Manag. 2016, 15, 1650007. [Google Scholar] [CrossRef]
- Ahmed, N.; Kulsum, U.; Azad, I.B.; Momtaz, A.Z.; Haque, M.E.; Rahman, M.S. Cybersecurity awareness survey: An analysis from Bangladesh perspective. In Proceedings of the 2017 IEEE Region 10 Humanitarian Technology Conference (R10-HTC), Dhaka, Bangladesh, 21–23 December 2017. [Google Scholar]
- Plackett, R.L. Karl Pearson and the chi-squared test. Int. Stat. Rev. Int. Stat. 1983, 51, 59–72. [Google Scholar] [CrossRef]
- Slusky, L.; Partow-Navid, P. Students information security practices and awareness. J. Inf. Priv. Secur. 2012, 8, 3–26. [Google Scholar] [CrossRef]
- Alotaibi, F.; Furnell, S.; Stengel, I.; Papadaki, M. A survey of cyber-security awareness in Saudi Arabia. In Proceedings of the 2016 11th International Conference for Internet Technology and Secured Transactions (ICITST), Barcelona, Spain, 5–7 December 2016. [Google Scholar]
- Senthilkumar, K.; Easwaramoorthy, S. A Survey on Cyber Security awareness among college students in Tamil Nadu. In IOP Conference Series: Materials Science and Engineering; IOP Publishing: Bristol, UK, 2017; Volume 263, p. 042043. [Google Scholar]
- Moallem, A. Cyber Security Awareness Among College Students. In International Conference on Applied Human Factors and Ergonomics; Springer: Berlin/Heidelberg, Germany, 2018; pp. 79–87. [Google Scholar]
- Taha, N.; Dahabiyeh, L. College students information security awareness: A comparison between smartphones and computers. Educ. Inf. Technol. 2020, 26, 1–16. [Google Scholar] [CrossRef]
- Moallem, A. Cybersecurity Awareness Among Students and Faculty; CRC Press: Boca Raton, FL, USA, 2019. [Google Scholar]
- Zwilling, M.; Klien, G.; Lesjak, D.; Wiechetek, Ł.; Cetin, F.; Basim, H.N. Cyber security awareness, knowledge and behavior: A comparative study. J. Comput. Inf. Syst. 2020. [Google Scholar] [CrossRef]
- Garba, A.; Sirat, M.B.; Hajar, S.; Dauda, I.B. Cyber Security Awareness Among University Students: A Case Study. Sci. Proc. Ser. 2020, 2, 82–86. [Google Scholar] [CrossRef]
- Aljeaid, D.; Alzhrani, A.; Alrougi, M.; Almalki, O. Assessment of End-User Susceptibility to Cybersecurity Threats in Saudi Arabia by Simulating Phishing Attacks. Information 2020, 11, 547. [Google Scholar] [CrossRef]
- Ahram, T.Z.; Nicholson, D. Advances in Human Factors in Cybersecurity. In Proceedings of the AHFE 2018 International Conference on Human Factors in Cybersecurity, Orlando, FL, USA, 21–25 July 2018; Springer: Berlin/Heidelberg, Germany, 2018. [Google Scholar]
- Al-Khater, W.A.; Al-Maadeed, S.; Ahmed, A.A.; Sadiq, A.S.; Khan, M.K. Comprehensive Review of Cybercrime Detection Techniques. IEEE Access 2020, 8, 137293–137311. [Google Scholar] [CrossRef]
- Garba, A.A.; Siraj, M.M.; Othman, S.H.; Musa, M. A Study on Cybersecurity Awareness among Students in Yobe State University, Nigeria: A Quantitative Approach. Available online: https://www.researchgate.net/publication/343600853_A_Study_on_Cybersecurity_Awareness_Among_Students_in_Yobe_A_Quantitative_Approach (accessed on 30 April 2021).
- 2015 Cyber Security Survey: Major Australian Business. Available online: www.cyber-securityhub.gov.za/cyberawareness/images/pdfs/2015-ACSC-Cyber-Security-Survey-Major-Australian-Businesses.pdf/ (accessed on 20 February 2021).
- Shen, L. The NIST cybersecurity framework: Overview and potential impacts. Scitech Lawyer 2014, 10, 16. [Google Scholar]
- Baskerville, R.; Rowe, F.; Wolff, F.C. Integration of information systems and cybersecurity countermeasures: An exposure to risk perspective. ACM SIGMIS Database Database Adv. Inf. Syst. 2018, 49, 33–52. [Google Scholar] [CrossRef]
- Colnago, J.; Devlin, S.; Oates, M.; Swoopes, C.; Bauer, L.; Cranor, L.; Christin, N. “It’s not actually that horrible” Exploring Adoption of Two-Factor Authentication at a University. In Proceedings of the 2018 CHI Conference on Human Factors in Computing Systems, Montreal, QC, Canada, 21–26 April 2018; pp. 1–11. [Google Scholar]
- Fennell, C.; Wash, R. Do Stories Help People Adopt Two-Factor Authentication? Available online: https://www.rickwash.com/papers/SOUPS2019_LBW_Submission.pdf (accessed on 30 April 2021).
- Kruger, H.; Steyn, T.; Dawn Medlin, B.; Drevin, L. An empirical assessment of factors impeding effective password management. J. Inf. Priv. Secur. 2008, 4, 45–59. [Google Scholar] [CrossRef]
- Ter Louw, M.; Lim, J.S.; Venkatakrishnan, V.N. Enhancing web browser security against malware extensions. J. Comput. Virol. 2008, 4, 179–195. [Google Scholar] [CrossRef]
- Alwagait, E.; Shahzad, B.; Alim, S. Impact of social media usage on students academic performance in Saudi Arabia. Comput. Hum. Behav. 2015, 51, 1092–1097. [Google Scholar] [CrossRef]
- Mesch, G.S. Is online trust and trust in social institutions associated with online disclosure of identifiable information online? Comput. Hum. Behav. 2012, 28, 1471–1477. [Google Scholar] [CrossRef]
- Taber, K.S. The use of Cronbach’s alpha when developing and reporting research instruments in science education. Res. Sci. Educ. 2018, 48, 1273–1296. [Google Scholar] [CrossRef]
- Cavana, R.; Delahaye, B.; Sekeran, U. Applied Business Research: Qualitative and Quantitative Methods; John Wiley & Sons: Hoboken, NJ, USA, 2001. [Google Scholar]
- Cerny, B.A.; Kaiser, H.F. A study of a measure of sampling adequacy for factor-analytic correlation matrices. Multivar. Behav. Res. 1977, 12, 43–47. [Google Scholar] [CrossRef] [PubMed]
- Kaiser, H.F.; Rice, J. Little jiffy, mark IV. Educ. Psychol. Meas. 1974, 34, 111–117. [Google Scholar] [CrossRef]
- Abawajy, J. User preference of cyber security awareness delivery methods. Behav. Inf. Technol. 2014, 33, 237–248. [Google Scholar] [CrossRef]

| Variables | Number # | Percentage % | |
|---|---|---|---|
| Sex | Male | 353 | 61.3 |
| Female | 223 | 38.7 | |
| Age (years) | 18–25 | 536 | 93.1 |
| 26–34 | 28 | 4.9 | |
| Above 34 | 12 | 2.1 | |
| Type of College | College of Computer and Information Sciences (Number of IT/Cybersecurity = 7) | 89 | 15.4 |
| College of Science (Number of IT/Cybersecurity = 3) | 39 | 6.8 | |
| College of Science and Humanities (Number of IT/Cybersecurity = 1) | 94 | 16.3 | |
| College of Business Administration (Number of IT/Cybersecurity = 1) | 46 | 8 | |
| College of Applied Medical Sciences (Number of IT/Cybersecurity = 1) | 58 | 10.1 | |
| College of Medicine (Number of IT/Cybersecurity = 1) | 37 | 6.4 | |
| College of Dentistry (Number of IT/Cybersecurity = 1) | 47 | 8.1 | |
| College of Engineering (Number of IT/Cybersecurity = 1) | 39 | 6.8 | |
| College of Education (Number of IT/Cybersecurity = 0) | 73 | 12.7 | |
| Community College (Number of IT/Cybersecurity = 0) | 54 | 9.4 | |
| Year of Study | 1st year | 70 | 12.2 |
| 2nd year | 124 | 21.5 | |
| 3rd year | 143 | 24.8 | |
| 4th year | 112 | 19.5 | |
| 5th year | 77 | 13.4 | |
| Internship year | 49 | 8.5 | |
| Daily Used Device | Smart phone | 435 | 75.5 |
| Tablet | 92 | 16 | |
| Desktop | 12 | 2.1 | |
| Laptop | 37 | 4.2 | |
| Variable | Frequency | Percentage (%) |
|---|---|---|
| Automatic update (No intervention from the user) | 231 | 40.1 |
| Manual update (User disables automatic update and updates outdated software when it is needed) | 244 | 42.4 |
| No update (User does not apply required updates) | 32 | 5.6 |
| Neglect update (User does not care about updates at all) | 69 | 12 |
| Variable | Strongly Agree | Agree | Neutral | Disagree | Strongly Disagree |
|---|---|---|---|---|---|
| All my passwords include: 12 upper and lower characters, numbers, and symbols | 42.7% | 30.4% | 14.1% | 9.7% | 3.1% |
| I must change my password periodically | 19.4% | 24.3% | 27.3% | 18.4% | 10.6% |
| I can use previously used passwords | 13.5% | 26.4% | 22.4% | 23.8% | 13.9% |
| I use one strong password for across different websites and accounts | 17.4% | 30.7% | 19.4% | 18.6% | 13.9% |
| It is annoying to have a long and strong password for each website and account | 34.5% | 26.2% | 19.4% | 10.1% | 9.7% |
| I often share my passwords with others | 4.5% | 5% | 6.3% | 19.8% | 64.4% |
| Variable | Strongly Agree | Agree | Neutral | Disagree | Strongly Disagree |
|---|---|---|---|---|---|
| The web browser should be updated regularly | 41% | 38.2% | 17.5% | 2.3% | 1% |
| I should avoid installing extensions from third-party websites | 31.6% | 37.7% | 25.5% | 2.8% | 2.4% |
| I must check the security settings and configurations of the web browser periodically | 29.9% | 29.5% | 27.1% | 10.2% | 3.3% |
| I must check the browser history and find suspicious activities | 35.2% | 37.7% | 18.4% | 6.4% | 2.3% |
| Variable | Strongly Agree | Agree | Neutral | Disagree | Strongly Disagree |
|---|---|---|---|---|---|
| It is acceptable to post personal pictures on social media | 15.6% | 21.9% | 26.7% | 18.8% | 17% |
| It is ok to accept friend requests from strangers | 14.4% | 21.2% | 30.2% | 22.7% | 14.4% |
| There is no problem with sharing my current location publicly on social media | 8.5% | 12% | 23.3% | 26.9% | 29.3% |
| There is no problem with adding all personal information like data of birth, current job, etc. | 9.7% | 14.4% | 23.4% | 24.3% | 28.1% |
| I know how to report any threat or suspicious activity on social media | 33.5% | 38.5% | 15.5% | 9% | 3.5% |
| Cronbach’s Alpha | Cronbach’s Alpha Based on Standardized Items | No. Items |
|---|---|---|
| 0.795 | 0.811 | 50 |
| KMO and Bartlett’s Test (This Test Is Based on Correlations) | ||
|---|---|---|
| Kaiser–Meyer–Olkin measure of sampling adequacy | 0.795 | |
| Bartlett’s test of sphericity | Approx. chi-square | 7.565 × 10 |
| df | 946 | |
| Sig. | 0.000 | |
| Component | Use of Security Tools | Phishing | Cryptology | Browser Security | Social Networking | Cybersecurity Knowledge | Cybersecurity Awareness |
|---|---|---|---|---|---|---|---|
| Use of security tools | 1 | ||||||
| Phishing | 0.041 | 1 | |||||
| Cryptology | 0.135 | −0.097 | 1 | ||||
| Browser security | 0.203 | 0.032 | 0.115 | 1 | |||
| Social networking | 0.296 | −0.147 | 0.049 | 0.211 | 1 | ||
| Cybersecurity knowledge | 0.093 | 0.106 | 0.091 | 0.112 | 0.028 | 1 | |
| Cybersecurity awareness | 0.094 | 0.034 | −0.081 | 0.095 | 0.076 | 0.09 | 1 |
| Model | Sum of Squares | df | Mean Square | F | Sig. | |
|---|---|---|---|---|---|---|
| 1 | Regression | 93.152 | 6 | 15.525 | 117.158 | 0.000 |
| Residual | 74.341 | 561 | 0.133 | |||
| Total | 167.493 | 567 | ||||
| Model | R | R Square | Adjusted R-Square | Standard Error of the Estimate | Change Statistics | ||||
|---|---|---|---|---|---|---|---|---|---|
| R-Square Change | F Change | df1 | df2 | Sig. F Change | |||||
| 1 | 0.746 | 0.556 | 0.551 | 0.36403 | 0.556 | 117.158 | 6 | 561 | 0.000 |
| Model | Unstandardized Coefficients | Standardized Coefficients | t | Sig. | 95% Confidence Interval for B | |||
|---|---|---|---|---|---|---|---|---|
| B | Standard Error | Beta | Lower Bound | Upper Bound | ||||
| 1 | (Constant) | 1.754 | 0.015 | 114.803 | 0.000 | 1.724 | 1.784 | |
| Use of security tools | 0.155 | 0.016 | 0.286 | 9.493 | 0.000 | 0.123 | 0.187 | |
| Phishing | 0.316 | 0.016 | 0.581 | 19.507 | 0.000 | 0.284 | 0.347 | |
| Cryptology | 0.107 | 0.016 | 0.196 | 6.700 | 0.000 | 0.075 | 0.138 | |
| Browser security | 0.044 | 0.016 | 0.081 | 2.729 | 0.007 | 0.012 | 0.076 | |
| Social networking | 0.077 | 0.016 | 0.142 | 4.674 | 0.000 | 0.045 | 0.109 | |
| Cybersecurity knowledge | 0.007 | 0.016 | 0.013 | 0.464 | 0.643 | −0.023 | 0.038 | |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Alharbi, T.; Tassaddiq, A. Assessment of Cybersecurity Awareness among Students of Majmaah University. Big Data Cogn. Comput. 2021, 5, 23. https://doi.org/10.3390/bdcc5020023
Alharbi T, Tassaddiq A. Assessment of Cybersecurity Awareness among Students of Majmaah University. Big Data and Cognitive Computing. 2021; 5(2):23. https://doi.org/10.3390/bdcc5020023
Chicago/Turabian StyleAlharbi, Talal, and Asifa Tassaddiq. 2021. "Assessment of Cybersecurity Awareness among Students of Majmaah University" Big Data and Cognitive Computing 5, no. 2: 23. https://doi.org/10.3390/bdcc5020023
APA StyleAlharbi, T., & Tassaddiq, A. (2021). Assessment of Cybersecurity Awareness among Students of Majmaah University. Big Data and Cognitive Computing, 5(2), 23. https://doi.org/10.3390/bdcc5020023






