Reliability of LEON3 Processor’s Program Counter Against SEU, MBU, and SET Fault Injection
Abstract
1. Introduction
2. Fault Injection Studies and Fault Tolerance in LEON3
2.1. Fault Injection Techniques Applied to the LEON3 Processor
2.2. Overview of Built-In Fault Tolerance Mechanisms
- Triple modular redundancy (TMR): Selected critical flip-flops, particularly those associated with control flow, are implemented using TMR. A majority-voting mechanism masks single-bit upsets in these registers at runtime, thereby improving resilience against SEU-induced control flow disruptions [60,61].
- Error detection and correction (EDAC): On-chip EDAC mechanisms provide protection for embedded RAM structures, including the instruction cache (icache), data cache (dcache), and internal memory blocks. These components typically employ single-error correction and double-error detection (SEC/DED) codes to enable runtime correction of soft errors [62]. Pipeline registers and certain internal control buses are safeguarded using parity bits. Although parity protection does not support error correction, it facilitates the detection of single-bit faults and enables error recovery mechanisms to be triggered [63].
- Pipeline restart and resynchronization logic: To recover from detected transient errors, LEON3-FT includes mechanisms such as pipeline flushing, instruction replay, and trap redirection. These techniques allow the processor to recover gracefully without requiring a complete system reset [64].
- Forced cache miss and watchdog monitoring: To mitigate undetected errors in cache tags or lines, forced cache miss logic is used. Additionally, watchdog timers and bus monitoring logic are used to identify faults in peripheral interfaces or interconnects that might otherwise lead to system lockups [64].
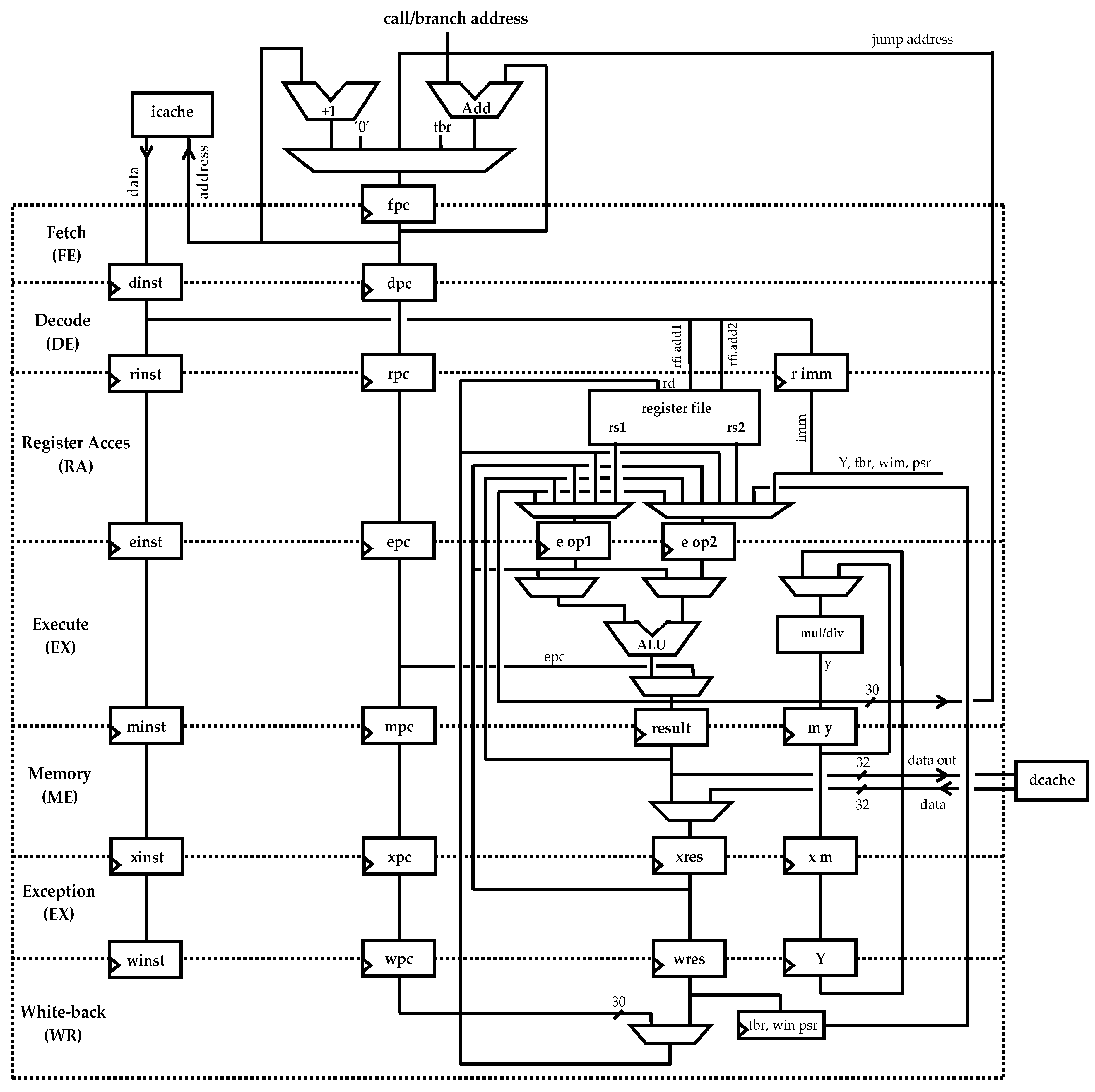
3. Architectural Overview of the LEON3 Integer Unit
- –
- FE stage fetches the instruction at the address stored in ‘fpc’, the local copy of the global PC;
- –
- DE stage decodes the instruction and computes potential branch or jump targets using ‘dpc’ and ‘dnpc’, which are local representations of the PC and the nPC;
- –
- RA may perform PC-relative address calculations, particularly for branch or trap-related instructions;
- –
- EX executes conditional logic that may change control flow, potentially updating ‘epc’/‘enpc’;
- –
- ME and WR do not typically modify the PC directly; however, faults in these stages can still corrupt status flags or trigger exceptions that result in control flow deviations.
- 1.
- The corrupted value may propagate forward through subsequent stages, causing control flow divergence if not masked;
- 2.
- It may trigger traps or exceptions, particularly if the corrupted PC causes misaligned instruction access or illegal operations;
- 3.
- In rare cases, the faulty value may be overwritten or implicitly corrected if a later stage recomputes the control flow path.
- The processor state register (PSR), which monitors the processor’s operational state;
- The window invalid mask (WIM), used to manage register window availability;
- The trap base register (TBR), which defines trap vector base address;
- The multiply/divide register (Y);
- The program counters (PC and nPC).
4. The NETFI+ RTL Fault Injection Framework
5. Reliability Assessment of the LEON3 Program Counter
5.1. Fault Injection Strategy for Program Counter Evaluation
5.2. Benchmark Description and Simulation Workflow
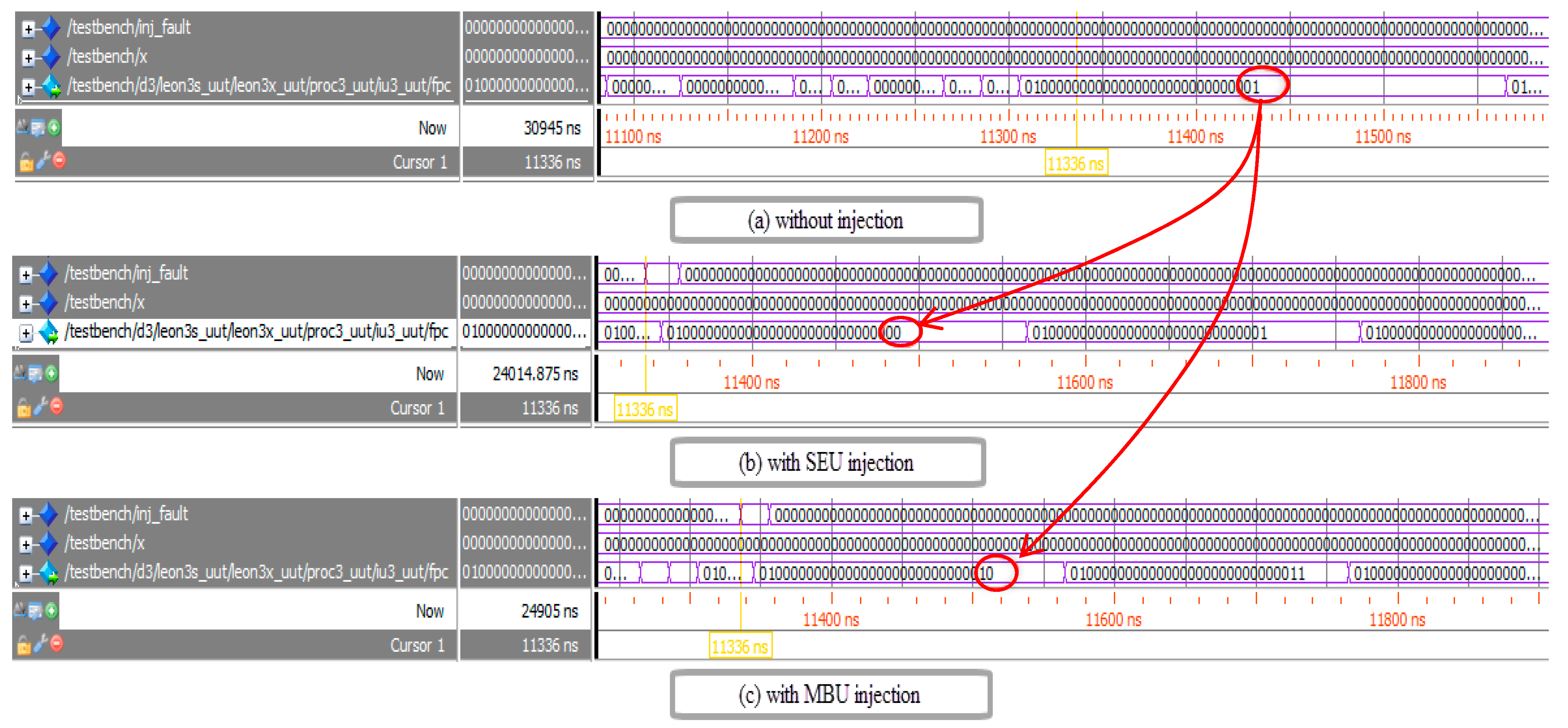
6. SEU Fault Injection Campaign and Analysis
6.1. Pipeline Stage Sensitivity Analysis
- Fault masking: In a subset of injections, the faults were either overwritten or did not affect execution, leaving the final outputs unchanged. Natural faults masking was observed in 6.7% of RA-stage injections, 3.3% of EX-stage injections and 100% in both EX- and ME-stage injections, suggesting some degree of inherent fault containment in the latter stages.
- Silent data corruption: A substantial portion of SEUs led to SDC, where incorrect outputs were produced while the system appeared to execute normally. This behavior was particularly prominent in the RA and EX stages, affecting 48.0% and 50.3% of fault cases, respectively. SDC is particularly dangerous in safety-critical applications due to its undetectable nature, potentially leading to mission-critical failures.
- Halt execution and timeout: In many cases, injected faults triggered severe disruptions, such as premature termination or simulation timeout (beyond the 4365 µs threshold), typically due to deadlocks or unhandled exceptions. This was the sole observed outcome for all SEU injections in the FE and DE stages (100%), and was recorded in 45.3% of RA-stage and 46.3% of EX-stage fault injection.
6.2. Trap Analysis and Error Propagation Insights
6.2.1. Illegal Instruction Trap
6.2.2. Privileged Instruction Trap
6.2.3. Window Overflow Trap
6.2.4. Window Underflow Trap
6.2.5. Summary of Trap Behavior
7. MBU Fault Injection Campaign and Analysis
7.1. Fault Impact and Error Rate Classification
- Fault masking: A small percentage of MBU injections did not result in any functional error. For example, when an MBU was injected at the ME stage, corrupting two adjacent bits of the PC, the altered address still referenced a valid instruction within the same code block. Consequently, the processor continued execution without any observable malfunction, effectively masking the injected fault at runtime.
- Silent data corruption: SDCs were observed when the system completed execution but produced incorrect outputs. For instance, an MBU in the DE stage modified the PC value, causing the program to skip a loop iteration during matrix multiplication. As no exception was triggered, the output deviated from the reference without detection, silently compromising correctness.
- Simulation timeout: In certain cases, MBUs disrupted control flow or instruction decoding to such an extent that program termination was not achieved. A representative scenario involved an MBU in the EX stage, which redirected the PC to an address outside the valid instruction memory range. This fault caused the processor to enter an undefined loop, leading to non-termination and ultimately exceeding the maximum simulation duration.
- Halt execution: This was the most frequently observed failure mode. In one illustrative case, an MBU in the FE stage caused the PC to point to an invalid or non-executable address. As a result, the LEON3 processor triggered a trap, halting execution prematurely. This behavior demonstrates the role of the built-in exception mechanism in preserving system integrity under fault conditions.
7.2. Trap Analysis in MBU Fault Injection
7.2.1. Memory Address Misalignment Trap
7.2.2. Floating-Point (FP) Exception Trap
7.2.3. Interrupt and Control Path Traps
7.3. Comparative Analysis: SEU vs. MBU Effects
8. SET Fault Injection Campaign and Analysis
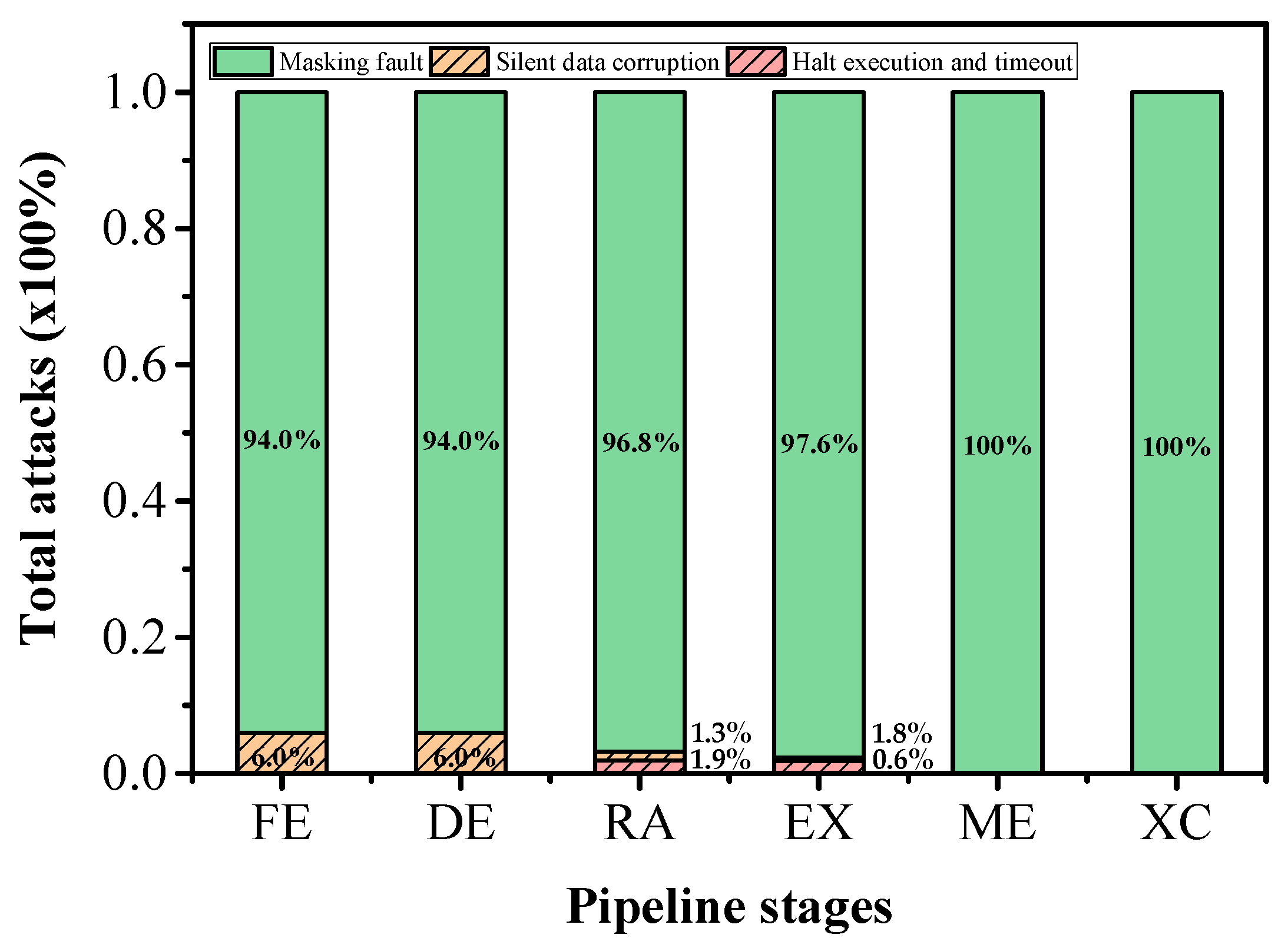
8.1. Sensitivity and Error Manifestation Analysis
- Fault masking: The majority of SET injections had no observable effects. For example, when a transient pulse was injected into the combinational logic driving the PC during the RA stage, the glitch either failed to reach a latch or was overwritten in the subsequent cycle. This allowed the processor to restore nominal behavior. This effect was particularly common in early pipeline stages, such as FE, where greater timing slack and shallower logic depth inherently suppressed transient propagation.
- Silent data corruption: In some cases, SETs introduced subtle control flow perturbations that were not detected during program execution. For instance, an SET affecting the PC computation logic in the DE stage caused the processor to skip a single instruction. The program completed normally, but the output matrix from the multiplication benchmark was incorrect. This kind of latent error is especially concerning in real-time or safety-critical systems.
- Halt execution and timeout: Although less frequent than in MBU scenarios, halted execution still occurred. In one example, a transient injected into the PC logic during the EX stage caused the processor to branch to an invalid memory address, triggering a trap and prematurely halting execution. This highlights the processor’s ability to detect some control flow anomalies, even those originating from transient events. In rare cases, SETs caused simulation timeouts. One notable instance involved an SET during the RA stage, which corrupted the PC and caused the processor to enter a non-terminating loop, thereby preventing the simulation from completing within the allotted time window. This indicates a serious disruption of sequential control.
8.2. Comparative Insights and Trap Analysis
9. Cross-Fault Comparison and Discussion
10. Conclusions and Future Work
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
Abbreviations
| API | Application Programming Interface |
| ARM | Advanced RISC Machine |
| ASIL | Automotive Safety Integrity Level |
| CI | Continuous Integration |
| CWP | Window Invalid Mask |
| DE | Decode |
| DED | Double-Error Detection |
| ECC | Error Correcting Code |
| EDAC | Error Detection and Correction |
| EX | Execute |
| FE | Fetch |
| FF | Flip-Flops |
| FP | Floating Point |
| FPGA | Field Programmable Gate Array |
| FPO | Floating-Point Operations |
| FPU | Floating-Point Unit |
| HDLs | Hardware Description Languages |
| HwIFI | Hardware-Implemented Fault Injection |
| IC | Integrated Circuit |
| IU | Integer Unit |
| JMPL | Jump and link |
| LDSB | Load Signed Byte |
| LSB | Least Significant Bits |
| MBT | Model-Based Testing |
| MBU | Multiple Bit Upsets |
| ME | Memory |
| MODNET | MODify NETlist |
| MSB | Most Significant Bits |
| NETFI | NETlist Fault Injection |
| nPC | Next Program Counter |
| PC | Program Counter |
| PSR | Processor State Register |
| RA | Register Access |
| RETT | Return from Trap |
| RTL | Register Transfer Level |
| RTOS | Real-Time Operating System |
| SDC | Silent Data Corruption |
| SEC | Single-Error Correction |
| SET | Single Event Transients |
| SEU | Single Event Upsets |
| SPARC | Scalable Processor Architecture |
| SRAM | Static Random Access Memory |
| SwIFI | Software-Implemented Fault Injection |
| TBR | Trap Base Register |
| TLM | Transaction-Level Modeling |
| TMR | Triple Modular Redundancy |
| ViP | Virtual Platform |
| WIM | Window Invalid Mask |
| WR | Write-back |
| XC | Exception |
References
- Baumann, R.C. Radiation-induced soft errors in advanced semiconductor technologies. IEEE Trans. Device Mater. Reliab. 2005, 5, 305–316. [Google Scholar] [CrossRef]
- Salih, N.K.; Satyanarayana, D.; Alkalbani, A.S.; Gopal, R. A survey on software/hardware fault injection tools and techniques. In Proceedings of the 2022 IEEE Symposium on Industrial Electronics & Applications (ISIEA), Langkawi Island, Malaysia, 16–17 July 2022; pp. 1–7. [Google Scholar]
- Breier, J.; Hou, X. How practical are fault injection attacks, really? IEEE Access 2022, 10, 113122–113130. [Google Scholar] [CrossRef]
- Benot, O. Fault attack. In Encyclopedia of Cryptography, Security and Privacy; Springer Nature: Cham, Switzerland, 2025; pp. 882–884. [Google Scholar]
- Sini, J.; Scialabba, K.; Violante, M.; Cosimi, F.; Arena, A. A Novel Approach to Address Random Hardware Failures for Automotive Application Within the ISO26262 and AUTOSAR Frameworks. IEEE Access 2024, 12, 165845–165860. [Google Scholar] [CrossRef]
- Birch, J.; Rivett, R.; Habli, I.; Bradshaw, B.; Botham, J.; Higham, D.; Jesty, P.; Monkhouse, H.; Palin, R. Safety cases and their role in ISO 26262 functional safety assessment. In Computer Safety, Reliability, and Security, Proceedings of the 32nd International Conference, SAFECOMP 2013, Toulouse, France, 24–27 September 2013, Proceedings; Springer: Berlin/Heidelberg, Germany, 2013; pp. 154–165. [Google Scholar]
- Ismail, A.; Liu, Q. ISO 26262 automotive functional safety: Issues and challenges. Int. J. Reliab. Appl. 2014, 15, 151–161. [Google Scholar]
- Plappert, C.; Zelle, D.; Gadacz, H.; Rieke, R.; Scheuermann, D.; Krauß, C. Attack surface assessment for cybersecurity engineering in the automotive domain. In Proceedings of the 29th IEEE Euromicro International Conference on Parallel, Distributed and Network-Based Processing (PDP), Valladolid, Spain, 10–12 March 2021; pp. 266–275. [Google Scholar]
- Ziade, H.; Ayoubi, R.A.; Velazco, R. A survey on fault injection techniques. Int. Arab J. Inf. Technol. 2004, 1, 171–186. [Google Scholar]
- Miele, A. A fault-injection methodology for the system-level dependability analysis of multiprocessor embedded systems. Microprocess. Microsyst. 2014, 38, 567–580. [Google Scholar] [CrossRef]
- Velazco, R.; Fouillat, P.; Reis, R. (Eds.) Radiation Effects on Embedded Systems; Springer Science & Business Media: Berlin/Heidelberg, Germany, 2007. [Google Scholar]
- Nicolaidis, M. Time redundancy based soft-error tolerance to rescue nanometer technologies. In Proceedings of the 17th IEEE VLSI Test Symposium, Dana Point, CA, USA, 25–29 April 1999; Cat. No. PR00146. pp. 86–94. [Google Scholar]
- Cha, H.; Rudnick, E.M.; Choi, G.S.; Patel, J.H.; Iyer, R.K. A fast and accurate gate-level transient fault simulation environment. In Proceedings of the FTCS-23 The Twenty-Third International Symposium on Fault-Tolerant Computing, Toulouse, France, 22–24 June 1993; pp. 310–319. [Google Scholar]
- Pulli, A.; Lupi, M. A simulation methodology for verification of transient fault tolerance of ASICs designed for high-energy physics experiments. J. Instrum. 2023, 18, C01038. [Google Scholar] [CrossRef]
- Solouki, M.A.; Angizi, S.; Violante, M. Dependability in embedded systems: A survey of fault tolerance methods and software-based mitigation techniques. IEEE Access 2024, 12, 180939–180967. [Google Scholar] [CrossRef]
- Boulifa, R.; Di Natale, G.; Maistri, P. Countermeasures Against Fault Injection Attacks in Processors: A Review. Information 2025, 16, 293. [Google Scholar] [CrossRef]
- Gil, P.; Blanc, S.; Serrano, J.J. Pin-Level Hardware Fault Injection Techniques. In Fault Injection Techniques and Tools for Embedded Systems Reliability Evaluation. Frontiers in Electronic Testing; Benso, A., Prinetto, P., Eds.; Springer: Boston, MA, USA, 2023; Volume 23, pp. 63–79. [Google Scholar]
- Zussa, L.; Dutertre, J.M.; Clédière, J.; Robisson, B. Analysis of the fault injection mechanism related to negative and positive power supply glitches using an on-chip voltmeter. In Proceedings of the 2014 IEEE International Symposium on Hardware-Oriented Security and Trust (HOST), Arlington, VA, USA, 6–7 May 2014; pp. 130–135. [Google Scholar]
- Bozzato, C.; Focardi, R.; Palmarini, F. Shaping the glitch: Optimizing voltage fault injection attacks. IACR Trans. Cryptogr. Hardw. Embed. Syst. 2019, 2019, 199–224. [Google Scholar] [CrossRef]
- Endo, S.; Sugawara, T.; Homma, N.; Aoki, T.; Satoh, A. An on-chip glitchy-clock generator for testing fault injection attacks. J. Cryptogr. Eng. 2011, 1, 265–270. [Google Scholar] [CrossRef]
- Khuat, V.; Danger, J.L.; Dutertre, J.M. Laser fault injection in a 32-bit microcontroller: From the flash interface to the execution pipeline. In Proceedings of the 2021 Workshop on Fault Detection and Tolerance in Cryptography (FDTC), Milan, Italy, 17 September 2021; pp. 74–85. [Google Scholar]
- Ebrahimabadi, M.; Mehjabin, S.S.; Viera, R.; Guilley, S.; Danger, J.L.; Dutertre, J.M.; Karimi, N. DELFINES: Detecting laser fault injection attacks via digital sensors. IEEE Trans. Comput.-Aided Des. Integr. Circuits Syst. 2023, 43, 774–787. [Google Scholar] [CrossRef]
- Alexandrescu, D.; Sterpone, L.; López-Ongil, C. Fault injection and fault tolerance methodologies for assessing device robustness and mitigating against ionizing radiation. In Proceedings of the 2014 19th IEEE European Test Symposium (ETS), Paderborn, Germany, 26–30 May 2014; pp. 1–6. [Google Scholar]
- Foucard, G.; Peronnard, P.; Velazco, R. Reliability Limits of TMR Implemented in a SRAM-based FPGA: Heavy Ion Measures vs. Fault Injection Predictions. J. Electron. Test. 2021, 27, 627–633. [Google Scholar] [CrossRef]
- Zhang, Y.; Cai, L.; Ye, B.; Chen, Q.; Yan, X.; Jin, Y.; Chen, T.; Liu, Y.; Jiao, Y.; Zhao, S.; et al. Evaluating single event effects on 28 nm FPGAs under multi conditions: High-LET ion irradiation and fault injection. Radiat. Eff. Defects Solids 2025, 1–14. [Google Scholar] [CrossRef]
- Gangolli, A.; Mahmoud, Q.H.; Azim, A. A systematic review of fault injection attacks on IoT systems. Electronics 2022, 11, 2023. [Google Scholar] [CrossRef]
- Natella, R.; Cotroneo, D.; Madeira, H.S. Assessing dependability with software fault injection: A survey. ACM Comput Surv. CSUR 2016, 48, 1–55. [Google Scholar] [CrossRef]
- Ruano, Ó.; García-Herrero, F.; Aranda, L.A.; Sánchez-Macián, A.; Rodriguez, L.; Maestro, J.A. Fault injection emulation for systems in FPGAs: Tools, techniques and methodology, a tutorial. Sensors 2021, 21, 1392. [Google Scholar] [CrossRef]
- Moradi, M.; Van Acker, B.; Vanherpen, K.; Denil, J. Model-implemented hybrid fault injection for Simulink (tool demonstrations). In Cyber Physical Systems. Model-Based Design, Proceedings of the 8th International Workshop, CyPhy 2018, and 14th International Workshop, WESE 2018, Turin, Italy, 4–5 October 2018, Revised Selected Papers 8; Springer International Publishing: Berlin/Heidelberg, Germany, 2019; pp. 71–90. [Google Scholar]
- Das, S.R.; Li, J.F.; Nayak, A.R.; Assaf, M.H.; Petriu, E.M.; Biswas, S.N. Circuit architecture test verification based on hardware software co-design with ModelSim. IETE J. Res. 2013, 59, 132–140. [Google Scholar] [CrossRef]
- Panda, P.R. SystemC: A modeling platform supporting multiple design abstractions. In Proceedings of the 14th international symposium on Systems synthesis, Montréal, PQ, Canada, 30 September–4 October 2001; pp. 75–80. [Google Scholar]
- Stoppe, J.; Drechsler, R. Analyzing SystemC designs: SystemC analysis approaches for varying applications. Sensors 2015, 15, 10399–10421. [Google Scholar] [CrossRef]
- Bellard, F. QEMU, a fast and portable dynamic translator. In Proceedings of the USENIX Annual Technical Conference, FREENIX Track, Anaheim, CA, USA, 10–15 April 2005; Volume 41, pp. 10–55. [Google Scholar]
- Saraoğlu, M.; Morozov, A.; Söylemez, M.T.; Janschek, K. ErrorSim: A tool for error propagation analysis of simulink models. In Computer Safety, Reliability, and Security, Proceedings of the 36th International Conference, SAFECOMP 2017, Trento, Italy, 13–15 September 2017, Proceedings; Springer International Publishing: Cham, Switzerland, 2017; pp. 245–254. [Google Scholar]
- Abdelmoez, W.; Nassar, D.M.; Shereshevsky, M.; Gradetsky, N.; Gunnalan, R.; Ammar, H.H.; Yu, B.; Mili, A. Error propagation in software architectures. In Proceedings of the 10th International Symposium on Software Metrics, 2004. Proceedings, Chicago, IL, USA, 11–17 September 2004; pp. 384–393. [Google Scholar]
- Sturesson, F.; Gaisler, J.; Ginosar, R.; Liran, T. Radiation characterization of a dual core LEON3-FT processor. In Proceedings of the 12th European Conference on Radiation and Its Effects on Components and Systems, Seville, Spain, 19–23 September 2011; pp. 938–944. [Google Scholar]
- Luo, F.; Zhang, X.; Yang, Z.; Jiang, Y.; Wang, J.; Wu, M.; Feng, W. Cybersecurity testing for automotive domain: A survey. Sensors 2022, 22, 9211. [Google Scholar] [CrossRef] [PubMed]
- Wang, Y.; Jia, P.; Liu, L.; Huang, C.; Liu, Z. A systematic review of fuzzing based on machine learning techniques. PLoS ONE 2020, 15, e0237749. [Google Scholar] [CrossRef]
- Eceiza, M.; Flores, J.L.; Iturbe, M. Fuzzing the internet of things: A review on the techniques and challenges for efficient vulnerability discovery in embedded systems. IEEE Internet Things J. 2021, 8, 10390–10411. [Google Scholar] [CrossRef]
- Zhang, Z.; Zhang, H.; Zhao, J.; Yin, Y. A survey on the development of network protocol fuzzing techniques. Electronics 2023, 12, 2904. [Google Scholar] [CrossRef]
- Zhou, X.; Wang, P.; Zhou, L.; Xun, P.; Lu, K. A survey of the security analysis of embedded devices. Sensors 2023, 23, 9221. [Google Scholar] [CrossRef] [PubMed]
- Schieferdecker, I.; Grossmann, J.; Schneider, M. Model-based security testing. arXiv 2012, arXiv:1202.6118. [Google Scholar] [CrossRef]
- Hambarde, P.; Varma, R.; Jha, S. The survey of real time operating system: RTOS. In Proceedings of the International Conference on Electronic Systems, Signal Processing and Computing Technologies, Nagpur, India, 9–11 January 2014; pp. 34–39. [Google Scholar]
- Gay, M.; Paxian, T.; Upadhyaya, D.; Becker, B.; Polian, I. Hardware-oriented algebraic fault attack framework with multiple fault injection support. In Proceedings of the IEEE Workshop on Fault Diagnosis and Tolerance in Cryptography (FDTC), Atlanta, GA, USA, 24 August 2019; pp. 25–32. [Google Scholar]
- Rangnau, T.; Buijtenen, R.V.; Fransen, F.; Turkmen, F. Continuous security testing: A case study on integrating dynamic security testing tools in ci/cd pipelines. In Proceedings of the 2020 IEEE 24th International Enterprise Distributed Object Computing Conference (EDOC), Eindhoven, The Netherlands, 5–8 October 2020; pp. 145–154. [Google Scholar]
- Gheraibia, Y.; Kabir, S.; Djafri, K.; Krimou, H. An overview of the approaches for automotive safety integrity levels allocation. J. Fail. Anal. Prev. 2018, 18, 707–720. [Google Scholar] [CrossRef]
- Török, Á.; Szalay, Z.; Sághi, B. New aspects of integrity levels in automotive industry-cybersecurity of automated vehicles. IEEE Trans. Intell. Transp. Sys. 2020, 23, 383–391. [Google Scholar] [CrossRef]
- SPARC International, Inc.; Weaver, D.L. The SPARC Architecture Manual; Prentice-Hall: Englewood Cliffs, NJ, USA, 1994; pp. 61–82. [Google Scholar]
- Bekker, D.L.; Tran, M.Q.P. Performance analysis of standalone and in-fpga LEON3 processors for use in deep space missions. In Proceedings of the IEEE Aerospace Conference, Big Sky, MT, USA, 2–9 March 2019; pp. 1–17. [Google Scholar]
- Sari, A.; Psarakis, M. A fault injection platform for the analysis of soft error effects in FPGA soft processors. In Proceedings of the IEEE 19th International Symposium on Design and Diagnostics of Electronic Circuits & Systems (DDECS), Kosice, Slovakia, 20–22 April 2016; pp. 1–6. [Google Scholar]
- Kasap, S.; Wächter, E.W.; Zhai, X.; Ehsan, S.; Mcdonald-Maier, K. Survey of soft error mitigation techniques applied to LEON3 soft processors on SRAM-based FPGAs. IEEE Access 2020, 8, 28646–28658. [Google Scholar] [CrossRef]
- Lindoso, A.; Entrena, L.; García-Valderas, M.; Parra, L. A hybrid fault-tolerant LEON3 soft core processor implemented in low-end SRAM FPGA. IEEE Trans. Nucl. Sci. 2016, 64, 374–381. [Google Scholar] [CrossRef]
- Deepanjali, S.; Sk, N.M. Fault tolerant micro-programmed control unit for SEU and MBU mitigation in space based digital systems. Microelectron. Reliab. 2024, 155, 115360. [Google Scholar] [CrossRef]
- Da Silva, A.; Sanchez, S. LEON3 ViP: A virtual platform with fault injection capabilities. In Proceedings of the 13th IEEE Euromicro Conference on Digital System Design: Architectures, Methods and Tools, Lille, France, 1–3 September 2010; pp. 813–816. [Google Scholar]
- Bonnoit, T.; Coelho, A.; Zergainoh, N.E.; Velazco, R. SEU impact in processor’s control-unit: Preliminary results obtained for LEON3 soft-core. In Proceedings of the 18th IEEE Latin American Test Symposium (LATS), Bogota, Colombia, 13–15 March 2017; pp. 1–4. [Google Scholar]
- Mirkhani, S.; Cho, H.; Mitra, S.; Abraham, J.A. Rethinking error injection for effective resilience. In Proceedings of the 2014 19th Asia and South Pacific Design Automation Conference (ASP-DAC), Singapore, 20–23 January 2014; pp. 390–393. [Google Scholar]
- Keller, A.M.; Wirthlin, M.J. Benefits of complementary SEU mitigation for the LEON3 soft processor on SRAM-based FPGAs. IEEE Trans. Nucl. Sci. 2016, 64, 519–528. [Google Scholar] [CrossRef]
- Houssany, S.; Guibbaud, N.; Bougerol, A.; Leveugle, R.; Miller, F.; Buard, N. Microprocessor soft error rate prediction based on cache memory analysis. IEEE Trans. Nucl. Sci. 2012, 59, 980–987. [Google Scholar] [CrossRef]
- Van der Horst, J.G. Radiation Tolerant Implementation of a soft-Core Processor for Space Applications. Ph.D. Thesis, University of Stellenbosch, Stellenbosch, South Africa, 2007. [Google Scholar]
- Wirthlin, M.J.; Keller, A.M.; McCloskey, C.; Ridd, P.; Lee, D.; Draper, J. SEU mitigation and validation of the LEON3 soft processor using triple modular redundancy for space processing. In Proceedings of the 2016 ACM/SIGDA International Symposium on Field-Programmable Gate Arrays, Monterey, CA, USA, 21–23 February 2016; pp. 205–214. [Google Scholar]
- Pham, H.M.; Pillement, S.; Piestrak, S.J. Low-overhead fault-tolerance technique for a dynamically reconfigurable softcore processor. IEEE Trans. Comput. 2012, 62, 1179–1192. [Google Scholar] [CrossRef]
- Goerl, R.C.; Villa, P.R.; Poehls, L.B.; Bezerra, E.A.; Vargas, F.L. An efficient EDAC approach for handling multiple bit upsets in memory array. Microelectron. Reliab. 2018, 88, 214–218. [Google Scholar] [CrossRef]
- Learn, M.W. Evaluation of the Leon3 Soft-Core Processor Within a Xilinx Radiation-Hardened Field-Programmable Gate Array (No. SAND2012-0454); Sandia National Laboratories (SNL): Albuquerque, NM, USA; Livermore, CA, USA, 2012. [Google Scholar]
- Bin, B.; Min, W.; Wang, Y. SEU Tolerance Design and Implementation of a Space High Reliability Microprocessor. Procedia Eng. 2011, 23, 525–530. [Google Scholar] [CrossRef][Green Version]
- Yuce, B.; Ghalaty, N.F.; Schaumont, P. Improving fault attacks on embedded software using RISC pipeline characterization. In Proceedings of the IEEE Workshop on Fault Diagnosis and Tolerance in Cryptography (FDTC), Saint-Malo, France, 13 September 2015; pp. 97–108. [Google Scholar]
- Mansour, W.; Velazco, R. SEU fault-injection in VHDL-based processors: A case study. J. Electron. Test. 2013, 29, 87–94. [Google Scholar] [CrossRef]
- Mansour, W.; Velazco, R. An automated SEU fault-injection method and tool for HDL-based designs. IEEE Trans. Nucl. Sci. 2013, 60, 2728–2733. [Google Scholar] [CrossRef]
- Solinas, M.; Coelho, A.; Fraire, J.A.; Zergainoh, N.E.; Ferreyra, P.A.; Velazco, R. Preliminary results of NETFI-2: An automatic method for fault injection on HDL-based designs. In Proceedings of the 2017 18th IEEE Latin American Test Symposium (LATS), Bogota, Colombia, 13–15 March 2017; pp. 1–4. [Google Scholar]
- Kchaou, A.; Youssef, W.E.H.; Tourki, R. SEUs Mitigation on Program Counter of the LEON3 Soft Processor. Int. J. Adv. Comput. Sci. Appl. 2017, 8, 278–285. [Google Scholar] [CrossRef]
- Abbasitabar, H.; Zarandi, H.R.; Salamat, R. Susceptibility analysis of LEON3 embedded processor against multiple event transients and upsets. In Proceedings of the IEEE 15th International Conference on Computational Science and Engineering, Paphos, Cyprus, 5–7 December 2012; pp. 548–553. [Google Scholar]
- Timmers, N.; Spruyt, A.; Witteman, M. Controlling PC on ARM using fault injection. In Proceedings of the IEEE 2016 Workshop on Fault Diagnosis and Tolerance in Cryptography (FDTC), Santa Barbara, CA, USA, 16 August 2016; pp. 25–35. [Google Scholar]
- Mansour, W.; Velazco, R.; Hubert, G. Error-rate estimation combining SEE static cross-section predictions and fault-injections performed on HDL-based designs. IEEE Trans. Nucl. Sci. 2013, 60, 4238–4242. [Google Scholar] [CrossRef]
- Madeira, H.; Costa, D.; Vieira, M. On the emulation of software faults by software fault injection. In Proceedings of the International Conference on Dependable Systems and Networks. DSN 2000, New York, NY, USA, 25–28 June 2000; pp. 417–426. [Google Scholar]
- Carreira, J.; Madeira, H.; Silva, J.G. Xception: Software fault injection and monitoring in processor functional units. Dependable Comput. Fault Toler. Syst. 1998, 10, 245–266. [Google Scholar]
- Wrobel, F.; Palau, J.M.; Calvet, M.C.; Bersillon, O.; Duarte, H. Simulation of nucleon-induced nuclear reactions in a simplified SRAM structure: Scaling effects on SEU and MBU cross sections. IEEE Trans. Nucl. Sci. 2001, 48, 1946–1952. [Google Scholar] [CrossRef]
- Black, J.D.; Sternberg, A.L.; Alles, M.L.; Witulski, A.F.; Bhuva, B.L.; Massengill, L.W.; Benedetto, J.M.; Baze, M.P.; Wert, J.L.; Hubert, M.G. Multiple-bit upset in 130 nm CMOS technology. IEEE Trans. Nucl. Sci. 2005, 52, 2536–2541. [Google Scholar] [CrossRef]
- Gao, S.; Yang, J.H.; Ye, B.; Cai, C.; He, Z.; Liu, J.; Liu, T.Q.; Yan, X.Y.; Sun, Y.M.; Xiao, G.Q. Differences in MBUs induced by high-energy and medium-energy heavy ions in 28 nm FPGAs. Nucl. Sci. Tech. 2022, 33, 112. [Google Scholar] [CrossRef]
- Rao, N.P.; Sarik, S.; Desai, M.P. On the likelihood of multiple bit upsets in logic circuits. arXiv 2014, arXiv:1401.1003. [Google Scholar] [CrossRef]
- Azimi, S.; De Sio, C.; Rizzieri, D.; Sterpone, L. Analysis of single event effects on embedded processor. Electronics 2021, 10, 3160. [Google Scholar] [CrossRef]
- Aguiar, V.A.; Alberton, S.G.; Pereira, M.S. Radiation-Induced Effects on Semiconductor Devices: A Brief Review on Single-Event Effects, Their Dynamics, and Reliability Impacts. Chips 2025, 4, 12. [Google Scholar] [CrossRef]




| Feature | Fault Injection | Fuzzing |
|---|---|---|
| Goal | Evaluate system resilience to hardware/software faults | Discover software bugs and security vulnerabilities |
| Target level | Hardware/RTL level, firmware, or runtime state (registers, memory, control flow) | Application/Input interface (e.g., files, network, APIs) |
| Fault model | Bit flips, signal glitches, stuck-at faults, timing violations | Malformed or adversarial input data |
| Execution context | Instruction-level, micro-architectural, or gate-level | Application-level |
| Typical use | Reliability analysis, safety certification, system validation | Vulnerability discovery, penetration testing |
| Injection mechanism | Physical (laser, electromagnetic), clock glitching, voltage, or simulation | Input manipulation (e.g., random, mutation-based) |
| Automation & coverage | Moderate to high (in simulation), lower in physical tests | High (via feedback-driven fuzzing) |
| Detection focus | Silent data corruption, trap generation, control flow errors | Crashes, hangs, memory errors |
| Complementarity | Can inform fuzzing by revealing fault-induced execution paths | Can be combined with fault injection to test error propagation from hardware to software |
| Type of Trap | Stages of Pipeline | |||
|---|---|---|---|---|
| FE | DE | RA | EX | |
| Illegal_instructions | 50.79% | 67% | 52.04% | 63.66% |
| Privileged_instructions | 14% | 2.99% | 6.91% | 10.03% |
| Window_overflow | - | - | 34.34% | 23% |
| Window_underflow | 35.2% | 30% | - | - |
| Type of Trap | Stages of Pipeline | |||
|---|---|---|---|---|
| FE | DE | RA | EX | |
| Illegal_instructions | 61.02% | 67.69% | 65.75% | 1.83% |
| Privileged_instructions | 25.22% | 14.28% | 6.85% | 29.74% |
| Window_overflow | 2.29% | 13.06% | 17.25% | 58.51% |
| Window_underflow | 1.83% | 0.22% | - | - |
| Memory_address_misalignment | 1.83% | 0.22% | 4.65% | 0.92% |
| Fp_exception_traps | 0.91% | 0.22% | - | 5.09% |
| Interrupting_traps | 3.5% | 1.51% | - | 0.21% |
| Type of Trap | Stages of Pipeline | |||
|---|---|---|---|---|
| FE | DE | RA | EX | |
| Illegal_instructions | 6% | 6% | 3.2% | - |
| Window_overflow | - | - | - | 2.4% |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Kchaou, A.; Saad, S.; Garrab, H.; Machhout, M. Reliability of LEON3 Processor’s Program Counter Against SEU, MBU, and SET Fault Injection. Cryptography 2025, 9, 54. https://doi.org/10.3390/cryptography9030054
Kchaou A, Saad S, Garrab H, Machhout M. Reliability of LEON3 Processor’s Program Counter Against SEU, MBU, and SET Fault Injection. Cryptography. 2025; 9(3):54. https://doi.org/10.3390/cryptography9030054
Chicago/Turabian StyleKchaou, Afef, Sehmi Saad, Hatem Garrab, and Mohsen Machhout. 2025. "Reliability of LEON3 Processor’s Program Counter Against SEU, MBU, and SET Fault Injection" Cryptography 9, no. 3: 54. https://doi.org/10.3390/cryptography9030054
APA StyleKchaou, A., Saad, S., Garrab, H., & Machhout, M. (2025). Reliability of LEON3 Processor’s Program Counter Against SEU, MBU, and SET Fault Injection. Cryptography, 9(3), 54. https://doi.org/10.3390/cryptography9030054






