New Family of Stream Ciphers as Physically Clone-Resistant VLSI-Structures
Abstract
:1. Introduction
2. Proposed Digital Clone-Resistant Physical VLSI Structure
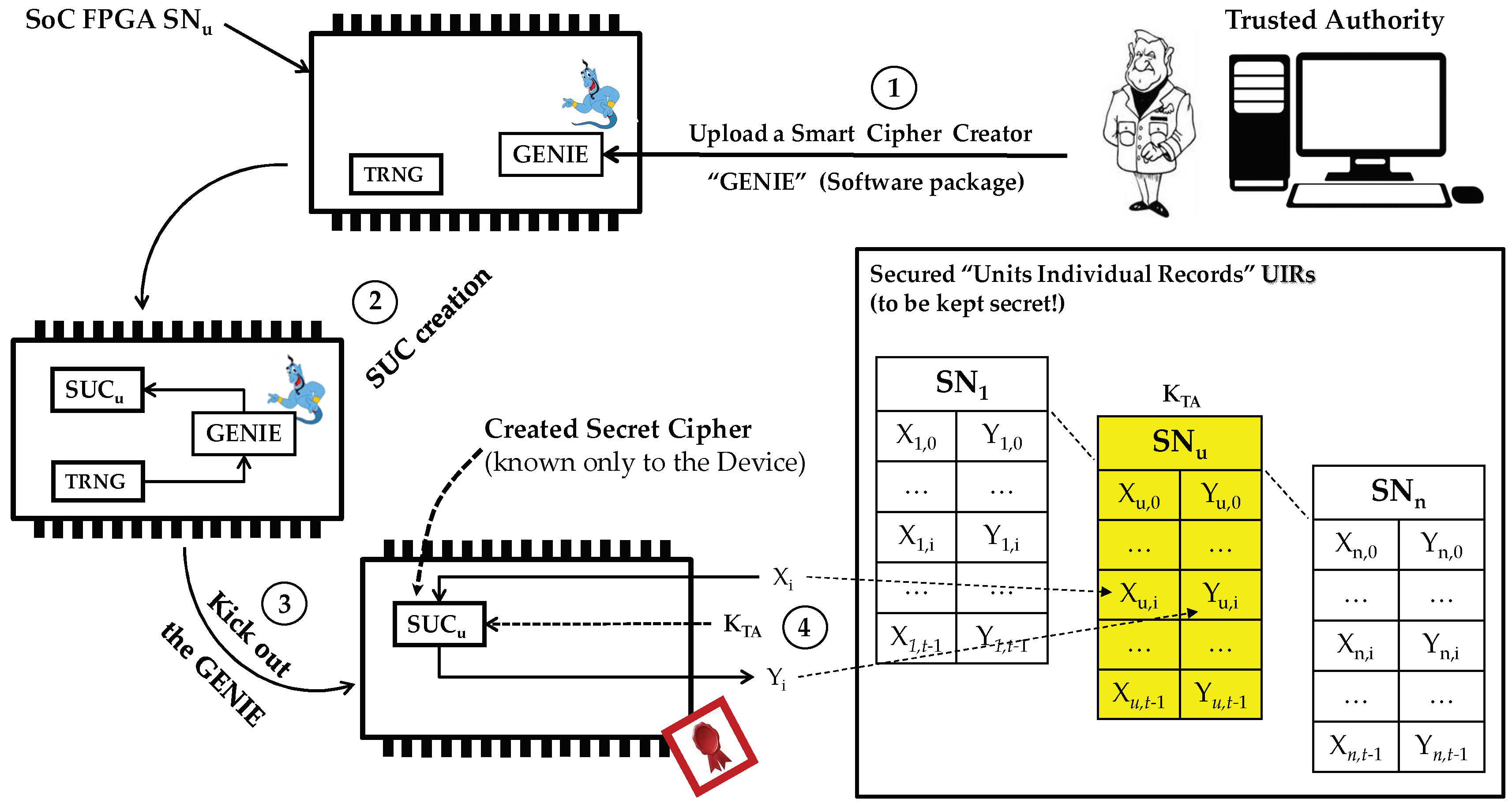
2.1. The Concept of Secret Unknown Ciphers SUCs
- The Trusted Authority (TA) uploads a software package as a smart cipher designer called “GENIE”. “The GENIE concept is taken from 1001-night miracles as a powerful, honest and obedient creature which can realize any wishes after getting out of Aladdin’s lamp”.
- The GENIE is then ordered to create a non-predictable cipher (SUC) with the help of the True Random Number Generator (TRNG) located within the SoC to assure randomized, unpredictable and unknown results. The GENIE stores the created SUC permanently at unknown location/s within the FPGA fabric and makes it usable for encrypting and decrypting data.
- The GENIE is then kicked-out (that is, deleted as a program and ordered to leave the device forever). The end result is a usable cipher which nobody knows. Notice that the created ciphers are basically different, even when having an unknown individual structure and unknown locations for each individual device.
- In this enrollment step, the TA (or any other TA’) challenges each SUCu by a set of t-cleartext patterns to generate the corresponding t-ciphertext set where . Then, the TA stores the X/Y pairs on the corresponding area in its Units Individual Records (UIR) labeled by the serial number of the device . The Xi/Yi pairs are to be used later by the TA/TA’ to identify and authenticate devices. Notice that multiple TA’s can operate completely independently for their own individual application by using the same SUC.
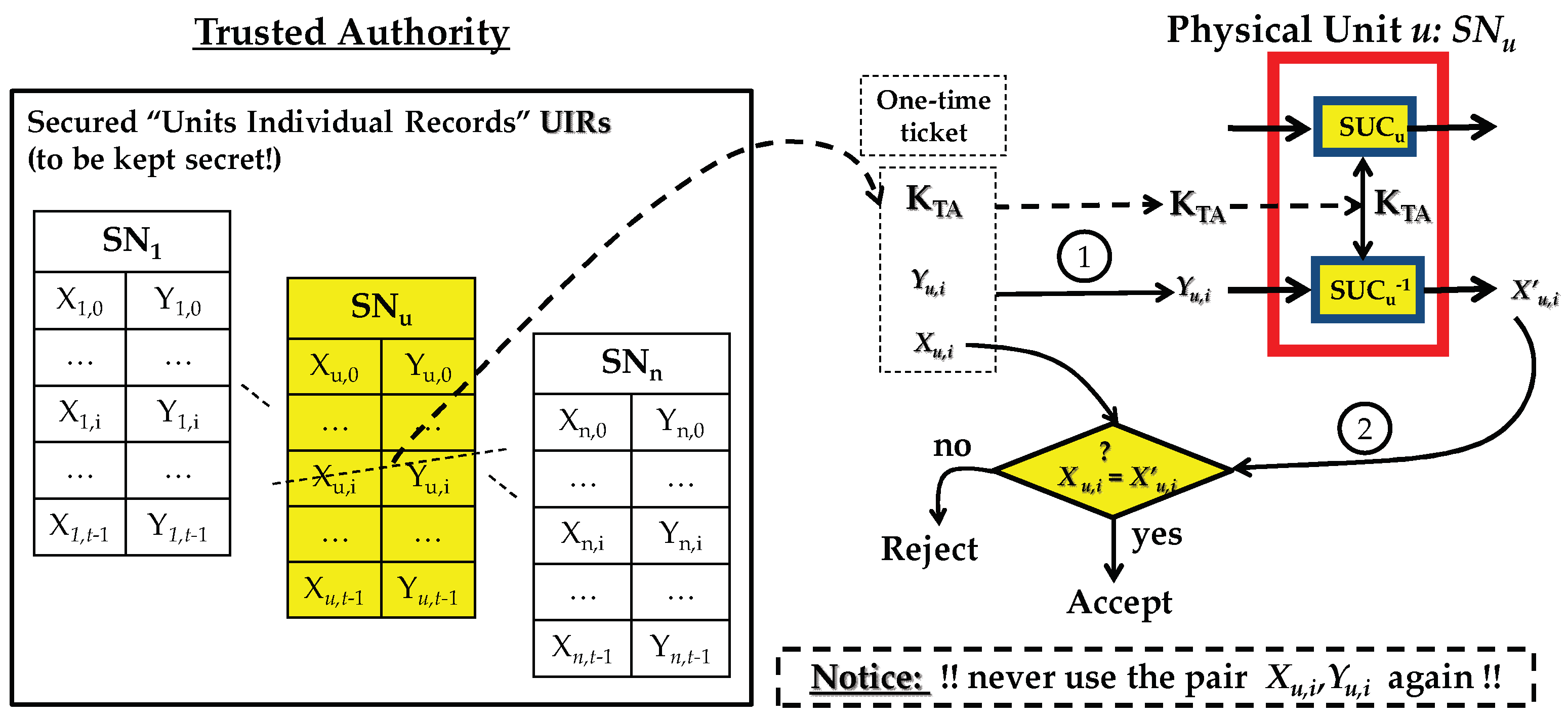
2.2. SUC Generic Use Protocol as Provable Physical Identity
- Path-1: TA randomly selects one of the pairs and challenges unit u with by asking for Xu,i.
- Path-2: Unit u deploys its to decrypt as and sends to TA. The TA then checks if , if true, then unit u is deemed as authentic. The used pair is marked as consumed or deleted, and should never be used again.
2.3. Kerckhoffs’s Principle (Shannon’s Maxim) and the SUC Concept
- 1.
- The Case of Published GENIE: In worst case, the GENIE is assumed to be published. That is, the whole cipher design rules are known to the opponent. If the cipher class size = |SUC| is huge, that is:as the cipher is selected randomly, and each cipher is selected randomly equally. If the SUC has a key size equal to k, then the total SUC cloning entropy CE is:|SUC| = N and N is huge, that is N → ∞CE = Log2 N + kAs both the cipher and its key are unknown. Also, it is assumed that if the cipher designer is using state-of-the-art crypto knowledge, then the minimum value is CEmin = k, in the case that the attacker finds the cipher due to the design weakness of the GENIE. Assuming that the GENIE designer is a good up to date cryptographer, then the cloning entropy approaches:CEmax = Log2 N + k
- 2.
- The Case of Unpublished GENIE: To let SUC concept works, TA is not actually required to publish the GENIE. In that case, the minimum CE is:where N0 is some unknown upper bound of the cipher class cardinality under consideration. The security analysis of the proposed family of KSG/stream ciphers is investigated by considering that the cipher design is publicly known. i.e. the NLFSRs’s feedback functions are known.CEmin = Log2 N0 + k
- Revealing the secret cipher components: An adversary is forced to reveal the randomly selected functions that are used in constructing the SUC.
- Breaking the resulting stream cipher: After revealing the SUC’s secret parameters, this SUC could be considered as a publicly known cipher, and an adversary should apply known cryptanalytical attack to break this SUC.
2.4. State of the Art in Designing SUC Creating GENIEs
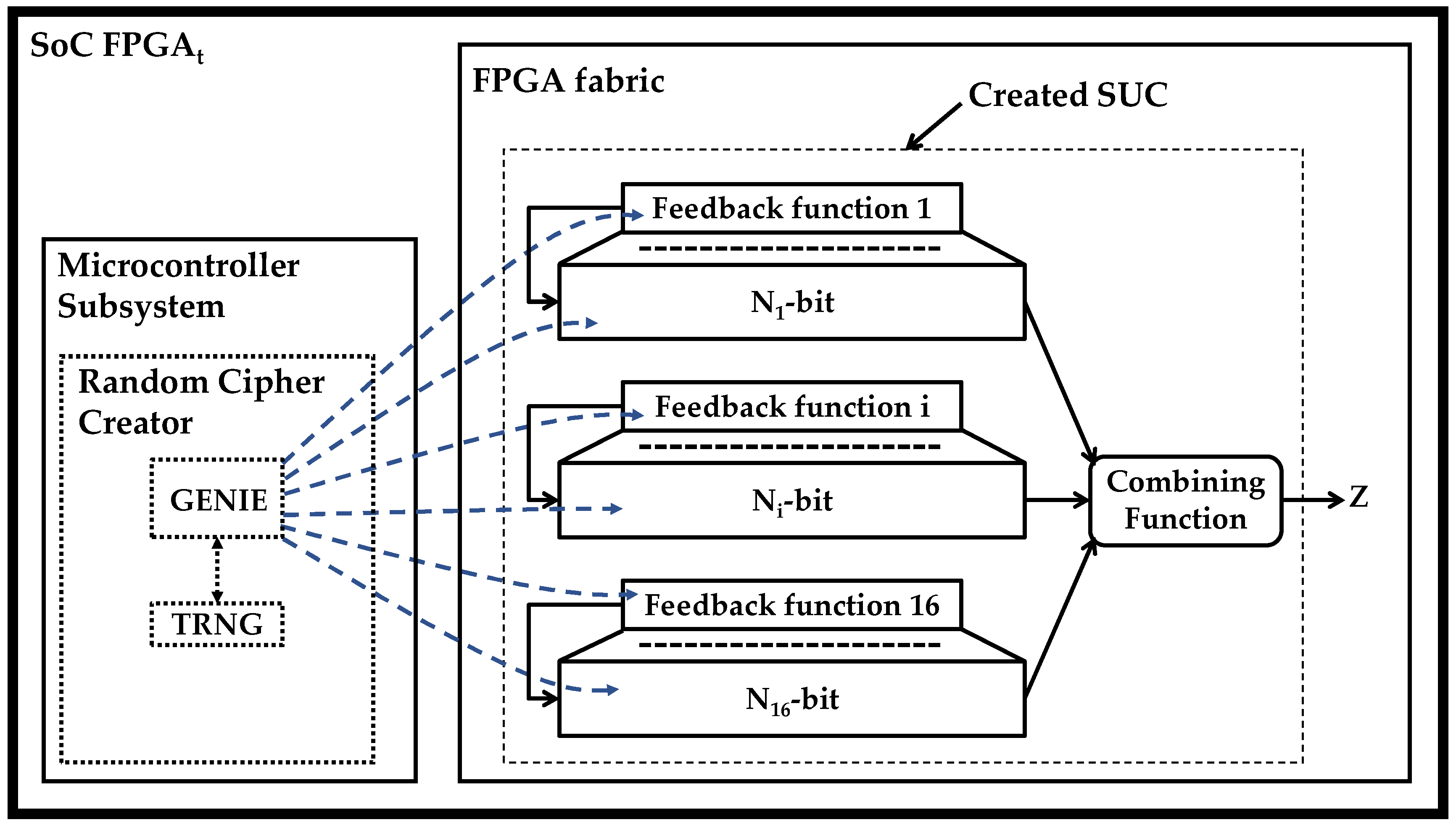
3. Designing a GENIE for Creating Unknown Keystream Generators
3.1. Selected State of the Art on Key Stream Generators
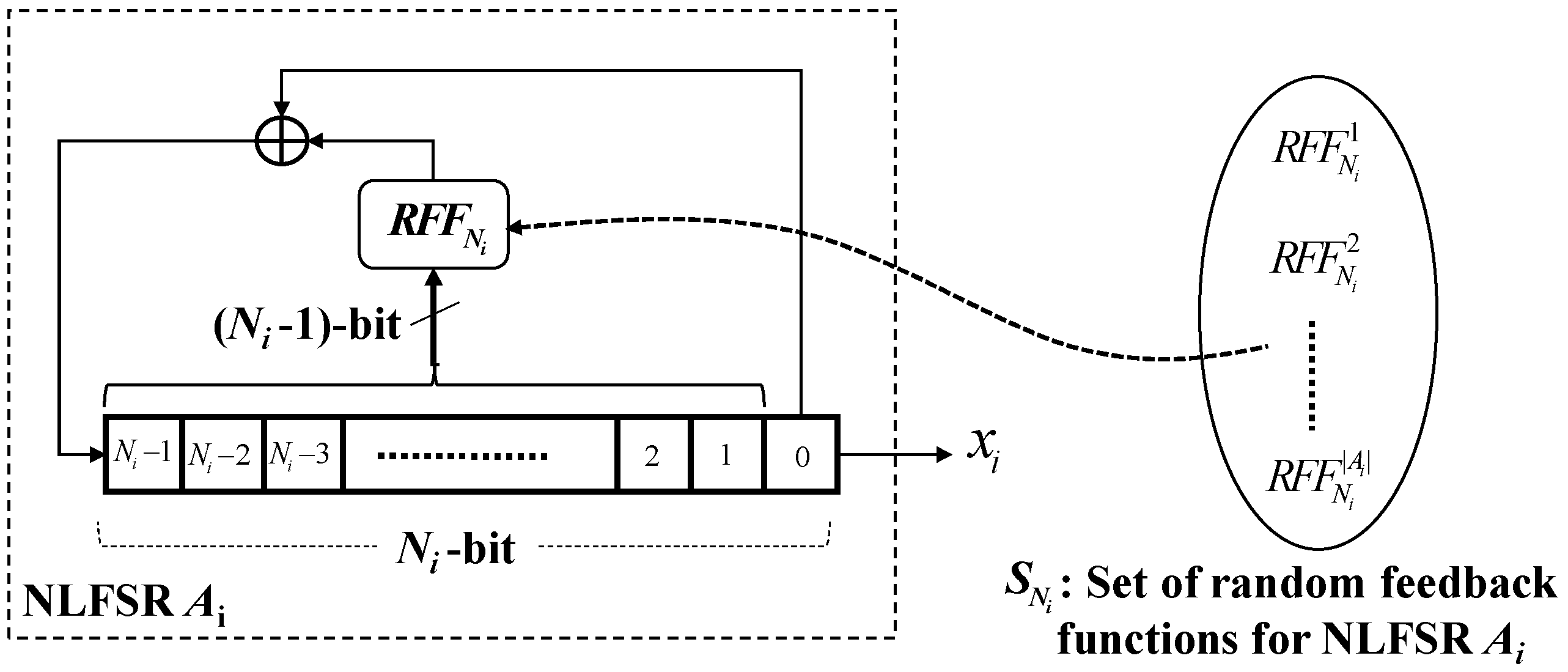
3.2. Creating SUCs Based on Random Keystream Generators
- The GENIE triggers the TRNG and gets random numbers
- The GENIE selects randomly, for each NLFSR, a feedback function from a pre-defined set and loads it to the corresponding area in the FPGA fabric. Also, the GENIE generates a random initial state for each NLFSR.
- Furthermore, the combining function can also be selected randomly by fulfilling some conditions to ensure that the GENIE is going to generate SUCs with an acceptable minimum-security level.
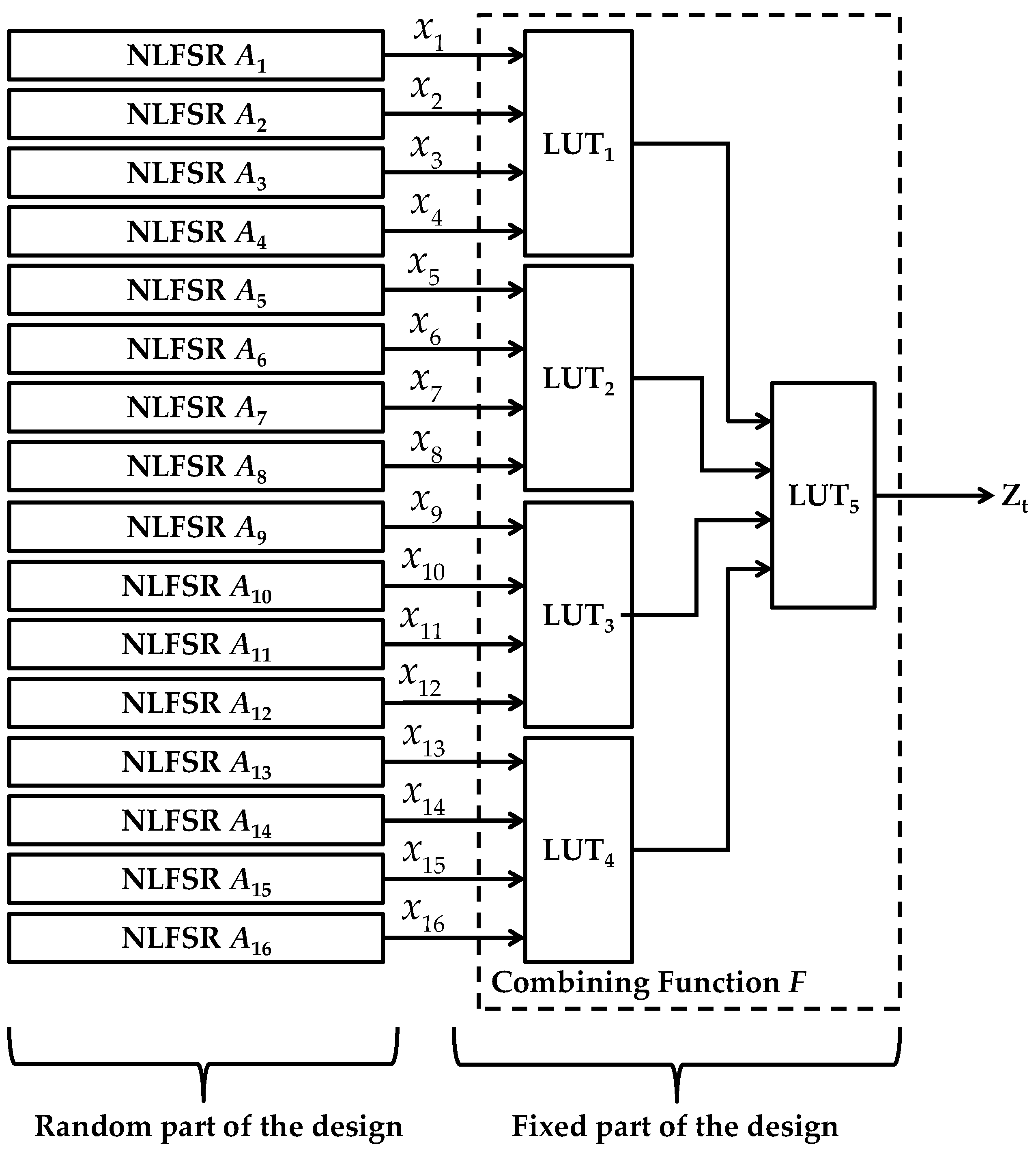
3.3. Description of the Created Random Keystream Generator
3.3.1. Selected Sets of Non-Linear Feedback Shift Registers
- Reverse form:
- Complement form:
- Reverse complement form:
- Berlekamp-Massey (B-M) Algorithm attack: In order to ensure that the attack complexity of B-M Algorithm is over 280; in terms of time complexity. Where the attack complexity is defined as L2, where L is the B-M linear complexity of the total key stream sequence which should exceed 240.
- Correlation immunity: If an adversary succeeds to recover the randomly selected feedback functions, a correlation attack may be launched. As the designed correlation immunity of the combining function is 8, the total size of the shortest 9 (8+1) NLFSRs should be larger than 80. In that case the correlation attack complexity would become 280, which is considered as sufficiently secure for contemporary non-post-quantum cryptography.
3.3.2. Cardinality of the Designed KSG Class
3.3.3. Keystream Boolean Combining Function F
- The linear part, which contains the monomials of degree one to , which can be realized with two 4-LUTs,
- The non-linear part containing monomials of degree two and three, related to the terms to which can also be realized with another two 4-LUTs. The outputs of all four 4-LUTs are combined using one 4-LUT to generate the keystream .
4. Security Analysis
4.1. Brute Force Attack
4.1.1. Exhaustive Search Attack on the NLFSRs Initial States as Secret Key Seeds
4.1.2. Stream Ciphers Linear Complexity and Berlekamp-Massey Algorithm
- 1.
- The algebraic normal form (ANF) of F(x1,…,xt) contains a monomialof degree d for which the corresponding shift register lengthsare pairwise relatively prime.
- 2.
- For all monomials of degree d, which have the form, the following holds:.
- The monomial satisfies condition 1 in the previous lemma: The lengths of the corresponding shift registers contributing in a monomial having d = 4 are which are pairwise relatively prime.
- The other monomials in the ANF of the Boolean combining function are of degree less than the degree 4 of the monomial . therefore, condition 2 holds.
4.2. Correlation Attacks
4.3. Algebraic Attacks
4.4. Parity Check Attack
4.5. Side Channel Attacks
- Timing analysis: It exploits dependencies between the execution time of an algorithm and the secret key bits. The proposed stream cipher design template does not include conditional branches, and hence any randomly generated stream cipher inside the FPGA will provide the response time for any key. Therefore, timing attacks are not feasible.
- Power analysis: Two major categories are discussed; Simple power analysis (SPA) uses a single measurement to reveal a secret key by searching for key dependent patterns in the power trace, while Differential Power Analysis (DPA) uses many power measurements that are evaluated by statistical analysis to reveal the secret key. In [31], a power analysis of stream ciphers which requires frequent resynchronization is investigated. Since, in SUC case, the internal state is selected randomly and unpredictably just once during the personalization of the SoC FPGA, there is no initial vector or key to manipulate from outside to allow such attacks.
5. Generic Use-Case of the Created Random KSG Structures for Authentication
5.1. Protocol’s Enrollment Phase
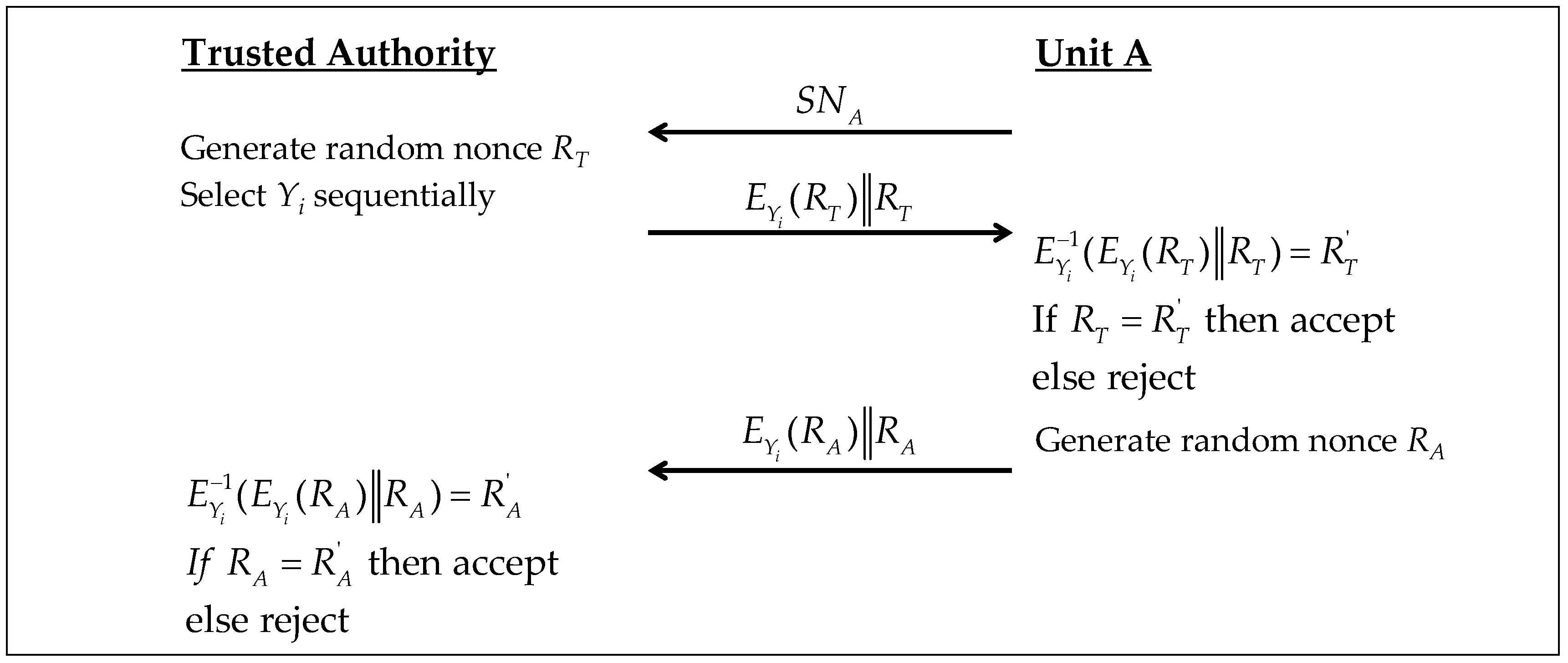
5.2. Identification Protocol
- Unit A sends its serial number to the TA that checks for its existence in the TA unit’s identification records (UIR). If , then TA accepts and continues otherwise it rejects and aborts the communication.
- The TA selects the next unused and generates a random nonce . Then, encrypts with a standard cipher by using as a key and sends it concatenated to as . Unit A generates the next response and decrypts the received message as . If , unit A rejects TA and keeps its state . this retains system synchronization. Otherwise, and TA is authentic.
- Unit A generates a random nonce , encrypts it by the same and sends it concatenated to as a response back to TA. TA decrypts the received message as . If , then unit A is deemed as authentic. Yi should never be used again.
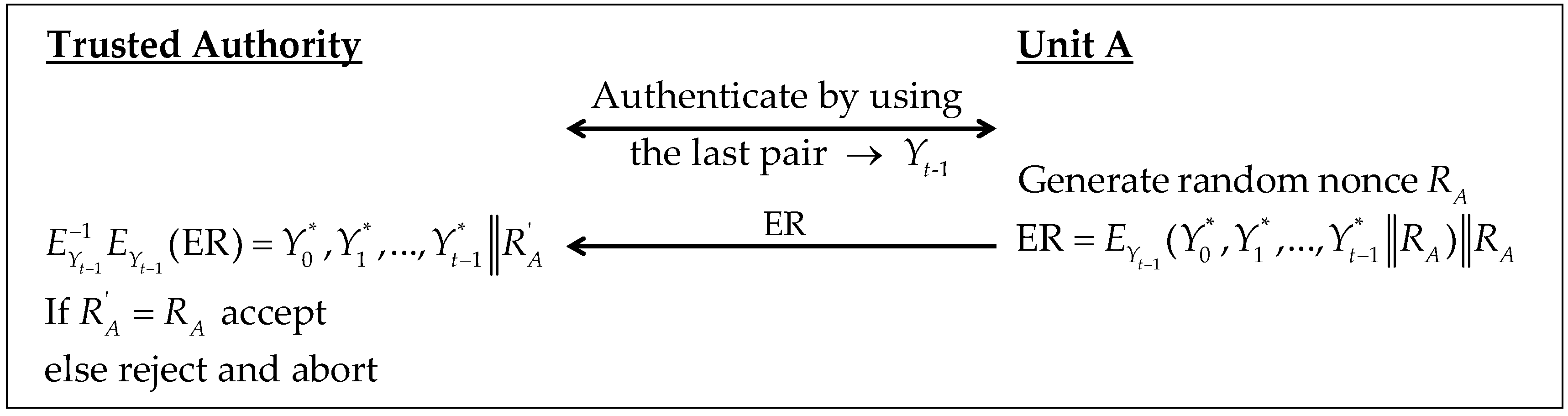
5.3. UIR Update Protocol
- The TA and unit A authenticate each other by using the final response as in the identification protocol above.
- Unit A generates a random nonce RA and a new t-responses set vectors . Then, it sends the encrypted responses (ER) to TA. TA decrypts ER by using as . If , the new response set is accepted.
6. Hardware Complexity
7. Conclusions
Author Contributions
Funding
Conflicts of Interest
Abbreviations
| SoC | System on Chip |
| SUC | Secret Unknown Cipher |
| PUF | Physical(ly) Unclonable Function |
| KSG | Key Stream Generator |
| NLFSR | Nonlinear Feedback Shift Register |
| ANF | Algebraic Normal Form |
| RFF | Random Feedback Function |
| RSC | Random Stream Cipher |
| UIR | Users Individual Records |
| TA | Trusted Authority |
Appendix A
| NLFSR | Length Ni | Set of Random Feedback Functions |
|---|---|---|
| A1 | 6 | 1,2,(1,2); 1,2,(2,4); 1,3,(1,5); 1,4,(1,4); 2,3,(1,3); 2,3,(1,5); 2,3,(2,3); 2,3,(2,4); 1,(1,2),(4,5); 1,(1,3),(3,5); 1,(2,3),(2,5); 2,(1,3),(2,4); 2,(1,3),(3,4); 2,(1,3),(3,5); 2,(1,5),(2,4); 2,(1,5),(4,5); 2,(2,3),(3,5); 2,(3,4),(3,5); 3,(1,4),(2,3); 3,(1,4),(2,4); 3,(1,4),(3,4); |
| A2 | 7 | 1,2,(2,6); 1,4,(1,3); 1,5,(1,5); 1,5,(3,5); 1,5,(4,6); 2,4,(1,2); 2,4,(2,5); 1,(1,2),(5,6); 1,(1,5),(3,4); 1,(1,6),(4,5); 1,(2,3),(3,5); 1,(2,5),(3,5); 1,(2,5),(4,5); 1,(3,4),(4,5); 2,(1,2),(4,6); 2,(1,4),(3,4); 2,(1,5),(2,6); 2,(1,6),(2,4); 2,(1,6),(3,6); 2,(1,6),(5,6); 2,(2,4),(3,5); 2,(2,5),(4,6); 2,(2,6),(4,6); 2,(3,6),(5,6); 3,(1,2),(2,3); 3,(1,3),(1,6); 3,(1,4),(3,6); 3,(1,5),(3,5); 3,(1,6),(3,4); 3,(2,3),(4,5); 3,(2,5),(3,5); 1,2,3,4,(1,6); 1,2,3,4,(2,3); 1,2,3,4,(2,6); 1,2,3,6,(1,3); 1,2,3,6,(1,5); 1,2,3,6,(2,6); 1,2,4,5,(1,2); 1,2,4,5,(1,5); 1,2,4,5,(2,6) |
| A3 | 8 | 1,5,(1,5); 1,6,(1,2); 1,6,(1,7); 1,6,(2,4); 1,6,(4,5); 1,6,(5,6); 2,5,(2,4); 2,5,(3,7); 2,5,(4,5); 3,4,(2,4); 3,4,(2,7); 3,4,(3,4); 3,4,(4,6); 3,4,(4,7); 3,4,(6,7); 1,(1,4),(2,4); 1,(1,6),(2,5); 1,(2,3),(2,4); 1,(2,4),(6,7); 1,(3,4),(4,7); 2,(1,3),(4,6); 2,(1,3),(5,7); 2,(1,5),(6,7); 2,(1,7),(2,3); 2,(3,7),(6,7); 3,(1,2),(2,4); 3,(1,4),(2,4); 3,(1,6),(3,6); 3,(1,6),(4,6); 3,(1,6),(4,7); 3,(2,3),(5,6); 3,(2,4),(6,7); 3,(2,6),(3,7); 1,2,3,5,(2,6); 1,2,3,6,(3,5); 1,2,3,6,(5,7); 1,2,4,5,(2,4); 1,2,4,7,(1,5); 1,2,5,7,(2,4); 1,3,4,7,(1,4); 1,3,4,7,(1,6); 1,3,4,7,(3,7) |
| A4 | 9 | 1,6,(4,6); 1,6,(4,8); 2,4,(4,5); 3,4,(3,7); 1,(1,5),(2,5); 1,(1,6),(6,7); 1,(1,8),(2,7); 1,(1,8),(5,6); 1,(2,3),(3,8); 1,(2,8),(3,7); 1,(3,4),(3,5); 1,(3,7),(5,8); 2,(1,5),(4,6); 2,(1,6),(2,7); 2,(1,8),(3,4); 2,(2,7),(4,6); 2,(4,7),(5,6); 3,(1,2),(4,7); 3,(1,6),(1,7); 3,(1,7),(4,8); 3,(2,3),(4,7); 4,(1,3),(2,8); 4,(1,6),(3,6); 4,(2,3),(5,8); 4,(2,5),(2,8); 4,(2,7),(3,8); 4,(2,8),(6,7); 4,(3,5),(3,7); 1,2,3,4,(3,7); 1,2,3,7,(4,6); 1,2,4,7,(1,6); 1,2,5,6,(1,6); 1,2,5,6,(2,6); 1,2,5,8,(2,6); 1,2,6,7,(3,6); 1,3,4,5,(3,7); 1,3,5,7,(5,6); 1,3,5,8,(3,5); 1,4,6,7,(1,7); 2,3,4,7,(2,8) |
| A5 | 10 | 1,2,(8,9); 1,4,(3,7); 1,8,(6,7); 2,5,(1,5); 4,5,(2,6); 4,5,(4,8); 4,5,(4,9); 1,(1,2),(3,4); 1,(2,4),(2,5); 1,(2,8),(7,9); 1,(3,8),(4,7); 1,(4,8),(6,7); 2,(1,3),(4,7); 2,(1,4),(3,7); 2,(1,5),(3,5); 2,(1,5),(4,9); 2,(1,6),(1,7); 2,(1,7),(4,6); 2,(1,9),(5,9); 2,(3,5),(3,7); 2,(3,9),(8,9); 3,(1,2),(2,8); 3,(1,3),(7,9); 3,(1,6),(3,8); 3,(1,6),(6,9); 3,(2,3),(2,6); 3,(2,7),(8,9); 3,(2,8),(7,9); 3,(6,7),(8,9); 4,(1,3),(1,7); 4,(1,3),(7,8); 4,(1,3),(7,9); 4,(1,5),(1,9); 4,(1,5),(7,9); 4,(7,8),(7,9); 1,2,4,8,(1,5); 1,2,4,8,(2,4); 1,2,5,8,(5,9); 1,3,4,7,(3,6); 1,3,6,7,(1,6); 1,4,5,9,(1,9); 1,4,5,9,(4,9); 1,4,5,9,(5,9); 1,5,6,7,(2,8); 2,3,4,6,(3,6); 2,4,5,8,(2,4); 2,4,6,7,(1,6) |
| A6 | 11 | 1,9,(1,4); 2,5,(1,9); 2,8,(6,9); 1,(1,7),(2,8); 1,(1,9),(2,7); 1,(2,3),(4,5); 1,(2,5),(3,4); 1,(2,7),(3,10); 1,(3,7),(3,8); 1,(3,7),(7,8); 2,(4,5),(6,10); 2,(4,6),(9,10); 2,(7,9),(8,10); 3,(1,6),(8,9); 3,(1,9),(5,10); 3,(2,7),(5,7); 3,(3,5),(6,9); 3,(3,6),(5,8); 3,(3,7),(7,10); 4,(1,2),(9,10); 4,(2,3),(2,10); 4,(3,7),(4,8); 5,(1,4),(6,9); 5,(2,8),(6,8); 5,(4,7),(6,7); 1,2,3,5,(4,6); 1,2,4,5,(4,6); 1,2,4,7,(2,3); 1,2,4,7,(4,9); 1,2,4,7,(8,9); 1,2,4,10,(1,9); 1,2,4,10,(3,9); 1,2,7,8,(1,9); 1,2,7,8,(9,10); 1,3,4,10,(6,10); 1,3,6,8,(6,8); 1,3,6,10,(7,9); 1,3,7,9,(1,8); 1,4,5,8,(5,7); 1,4,7,10,(1,9); 1,5,6,8,(5,9); 1,5,7,9,(2,8); 1,6,8,9,(2,6); 2,3,7,8,(4,10); 2,3,7,8,(6,10); 2,3,7,8,(7,10); 2,4,5,9,(5,9); 3,4,5,6,(2,10); 3,4,6,7,(2,3); 3,5,6,7,(4,8) |
| A7 | 12 | 3,8,(3,9); 4,7,(1,7); 4,7,(4,7); 1,(2,3),(3,4); 1,(2,5),(3,10); 1,(2,8),(6,10); 1,(7,8),(8,10); 1,(8,11),(9,10); 2,(1,3),(3,6); 2,(1,7),(2,8); 2,(1,10),(1,11); 2,(2,3),(7,9); 2,(3,9),(3,11); 2,(3,9),(5,9); 2,(5,11),(8,11); 2,(7,9),(7,11); 3,(1,8),(7,10); 3,(5,11),(6,10); 1,2,3,5,(5,9); 1,2,5,9,(7,11); 1,2,6,11,(2,6); 1,3,6,7,(4,10); 1,3,6,9,(1,9); 1,3,6,9,(4,10); 1,3,7,10,(4,5); 1,4,8,10,(2,5); 1,5,6,8,(4,6); 1,5,6,8,(6,10); 1,5,6,11,(7,8); 1,5,7,9,(1,11); 1,5,9,10,(6,7); 2,3,4,10,(3,8); 2,3,6,8,(3,6); 2,3,6,10,(2,6); 2,3,6,10,(4,10); 2,5,6,10,(2,10) |
| A8 | 13 | 1,11,(5,9); 4,8,(9,10); 1,(1,7),(3,7); 1,(2,3),(6,11); 1,(2,5),(5,11); 1,(2,6),(6,8); 1,(2,9),(4,5); 2,(1,6),(9,12); 2,(7,10),(10,12); 3,(1,9),(2,11); 3,(4,6),(9,11); 3,(8,9),(9,10); 4,(1,3),(4,6); 4,(1,3),(10,12); 4,(2,9),(8,10); 5,(1,5),(4,9); 5,(1,12),(7,11); 5,(2,9),(4,5); 5,(3,6),(4,9); 5,(3,12),(9,11); 6,(1,5),(2,12); 1,2,4,5,(1,7); 1,2,10,11,(6,12); 1,3,4,6,(6,10); 1,4,5,10,(4,8); 1,5,6,7,(5,9); 1,5,7,9,(8,9); 1,5,7,11,(8,10); 1,7,10,11,(2,6); 1,8,9,10,(8,9); 2,3,8,11,(1,10); 2,5,6,11,(8,11); 2,6,7,10,(8,12); 3,4,5,12,(4,5); 3,5,6,10,(8,11); 3,5,7,10,(2,10) |
| A9 | 14 | 1,2,(7,12); 1,(2,13),(4,12); 1,(5,12),(9,12); 2,(1,5),(3,11); 3,(1,6),(4,12); 3,(2,4),(6,12); 3,(2,12),(6,13); 3,(5,10),(7,12); 5,(2,4),(6,13); 6,(1,13),(5,9); 6,(5,9),(12,13); 1,2,3,5,(1,3); 1,2,4,7,(1,3); 1,4,5,8,(2,8); 1,4,5,13,(1,6); 1,4,7,11,(1,11); 1,6,10,12,(3,7); 1,6,10,12,(7,9); 1,7,9,12,(3,13); 2,3,5,7,(1,5); 2,3,10,12,(9,10); 2,5,6,12,(6,10); 2,7,9,11,(11,12); 4,5,6,8,(1,4); 4,6,7,10,(5,13) |
| A10 | 15 | 5,9,(2,11); 2,(6,8),(12,14); 4,(2,11),(7,10); 4,(5,6),(5,14); 4,(6,10),(9,10); 4,(7,8),(12,14); 6,(8,11),(12,13); 7,(2,11),(10,13); 7,(3,12),(3,13); 1,3,7,11,(9,10); 1,4,5,12,(3,4); 1,4,6,11,(2,14); 1,4,9,10,(7,10); 1,5,11,13,(5,11); 2,3,9,10,(6,10); 2,3,9,13,(3,7); 2,4,10,14,(4,10); 3,4,5,10,(3,7); 3,5,7,8,(3,13); 4,5,7,10,(1,14); 4,8,12,14,(5,6); 4,9,11,14,(1,13); 5,6,11,14,(5,8); 5,6,12,13,(5,9) |
| A11 | 16 | 2,13,(2,3); 3,(1,5),(5,7; 3,(2,13),(7,14); 5,(4,8),(6,12); 5,(4,12),(7,8); 7,(2,6),(10,13); 7,(8,14),(11,12); 1,2,3,9,(6,14); 1,5,13,14,(14,15); 1,11,12,13,(5,15); 2,5,10,14,(6,14); 2,6,11,12,(14,15); 2,7,8,10,(3,6); 2,7,8,13,(3,15); 4,8,9,10,(8,12) |
| A12 | 17 | 1,(7,10),(9,15); 3,(6,9),(13,14); 5,(4,7),(6,13); 6,(2,9),(7,12); 7,(1,8),(9,14); 8,(10,12),(11,16); 1,3,9,12,(7,13); 1,3,12,14,(2,10); 1,5,9,11,(1,13); 1,7,11,13,(6,14); 2,4,9,12,(6,16); 3,6,7,10,(9,15); 3,8,11,12,(3,11); 4,6,10,16,(3,11); 5,6,9,14,(6,14) |
| A13 | 19 | 7,10,(6,18); 9,12,(1,13); 2,(6,8),(8,10); 4,(5,16),(7,14); 6,(4,8),(17,18); 1,4,5,8,(5,15); 1,4,8,17,(1,13); 3,7,9,16,(3,17); 5,6,12,14,(2,18) |
| A14 | 21 | 1,15,17,19,(13,15); 2,7,12,17,(4,10); 3,5,9,13,(15,17); 4,8,9,11,(3,11) |
| A15 | 22 | 1,(4,10),(11,18); 5,(4,12),(7,14); 1,6,8,12,(10,17); 1,10,16,18,(3,21); 5,6,11,15,(9,21) |
| A16 | 23 | 3,(13,19),(18,19); 2,6,10,14,(5,13); 3,11,16,18,(4,19) |
References
- Wael, A.; Ayoub, M. Physical and Mechatronic Security, Technologies and Future Trends for Vehicular Environment. In Proceedings of the VDI-Fachtagung Automotive Security, VDI Berichte, Nürtingen, Germany, 27 September 2017; Volume 2310, pp. 73–95. [Google Scholar]
- Maes, R.; Verbauwhede, I. Physically Unclonable Functions: A Study on the State of the Art and Future Research Directions. In Towards Hardware-Intrinsic Security; Springer: Berlin, Germany, 2010; pp. 3–37. ISBN 978-3-642-14451-6, 978-3-642-14452-3. [Google Scholar]
- Sadeghi, A.-R.; Visconti, I.; Wachsmann, C. Enhancing RFID Security and Privacy by Physically Unclonable Functions. In Towards Hardware-Intrinsic Security; Springer: Berlin/Heidelberg, Germany, 2010. [Google Scholar]
- Tuyls, P.; Batina, L. RFID-tags for anti-counterfeiting. In Proceedings of the Cryptographers’ Track at the RSA Conference, San Jose, CA, USA, 13–17 February 2006; pp. 115–131. [Google Scholar]
- Škoric, B.; Tuyls, P.; Ophey, W. Robust key extraction from physical uncloneable functions. In Proceedings of the Applied Cryptography and Network Security, New York, NY, USA, 7–10 June 2005; Volume 3531, pp. 407–422. [Google Scholar]
- Guajardo, J.; Kumar, S.S.; Schrijen, G.-J.; Tuyls, P. FPGA Intrinsic PUFs and Their Use for IP Protection. In Proceedings of the Cryptographic Hardware and Embedded Systems—CHES 2007, Vienna, Austria, 10–13 September 2007; Volume 4727, pp. 63–80. [Google Scholar]
- Bösch, C.; Guajardo, J.; Sadeghi, A.-R.; Shokrollahi, J.; Tuyls, P. Efficient Helper Data Key Extractor on FPGAs. Cryptogr. Hardw. Embed. Syst. 2008, 5154, 181–197. [Google Scholar]
- Dodis, Y.; Ostrovsky, R.; Reyzin, L.; Smith, A. Fuzzy Extractors: How to Generate Strong Keys from Biometrics and Other Noisy Data. In Proceedings of the International Conference on the Theory and Applications of Cryptographic Techniques, St. Petersburg, Russia, 28 May–1 June 2006. [Google Scholar]
- Nedospasov, D.; Seifert, J.-P.; Helfmeier, C.; Boit, C. Invasive PUF Analysis. In Proceedings of the Fault Diagnosis and Tolerance in Cryptography (FDTC), Washington, DC, USA, 20 August 2013; pp. 30–38. [Google Scholar]
- Rührmair, U.; Sölter, J.; Sehnke, F.; Xu, X.; Mahmoud, A.; Stoyanova, V.; Dror, G.; Schmidhuber, J.; Burleson, W.; Devadas, S. PUF modeling attacks on simulated and silicon data. IEEE Trans. Inf. Forensics Secur. 2013, 8, 1876–1891. [Google Scholar] [CrossRef]
- Merli, D.; Schuster, D.; Stumpf, F.; Sigl, G. Side-Channel Analysis of PUFs and Fuzzy Extractors. In Proceedings of the International Conference on Trust and Trustworthy Computing, Pittsburgh, PA, USA, 22–24 June 2011; Springer: Berlin/Heidelberg, Germany, 2011; pp. 33–47. [Google Scholar]
- Mahmoud, A.; Rührmair, U.; Majzoobi, M.; Koushanfar, F. Combined Modeling and Side Channel Attacks on Strong PUFs. IACR Cryptol. ePrint Arch. 2013, 2013, 632. [Google Scholar]
- Adi, W.; Mars, A.; Mulhem, S. Generic identification protocols by deploying Secret Unknown Ciphers (SUCs). In Proceedings of the 2017 IEEE International Conference on Consumer Electronics—Taiwan (ICCE-TW), Taipei, Taiwan, 12–14 June 2017; pp. 255–256. [Google Scholar]
- Mars, A.; Adi, W. Converting NV-FPGAs into Physically Clone-Resistant Units by Digital Mutations. 2019; submitted for publication. [Google Scholar]
- Mars, A.; Adi, W.; Mulhem, S.; Hamadaqa, E. Random stream cipher as a PUF-like identity in FPGA environment. In Proceedings of the Seventh International Conference on Emerging Security Technologies (EST), Canterbury, UK, 6–8 September 2017; pp. 209–214. [Google Scholar]
- Mars, A.; Adi, W. Clone-Resistant Entities for Vehicular Security. In Proceedings of the IEEE 13th International Conference on Innovations in Information Technology (IIT), Al Ain, UAE, 18–19 November 2018. [Google Scholar]
- Mars, A.; Adi, W. New Concept for Physically-Secured E-Coins Circulations. In Proceedings of the 2018 NASA/ESA Conference on Adaptive Hardware and Systems, Edinburgh, UK, 6–9 August 2018. [Google Scholar]
- Kerckhoffs, A. LA CRYPTOGRAPHIE MILITAIRE. Available online: http://www.petitcolas.net/kerckhoffs/la_cryptographie_militaire_i.htm (accessed on 2 April 2019).
- eSTREAM, the ECRYPT Stream Cipher Project. Available online: http://www.ecrypt.eu.org/stream/ (accessed on 2 April 2019).
- Gammel, B.M.; Göttfert, R.; Kniffler, O. The Achterbahn stream cipher. eSTREAM 2005. submitted. [Google Scholar]
- Johansson, T.; Meier, W.; Müller, F. Cryptanalysis of Achterbahn. In Proceedings of the International Workshop on Fast Software Encryption, Graz, Austria, 15–17 March 2006; Springer: Berlin/Heidelberg, Germany; Volume 4047, pp. 1–14. [Google Scholar]
- Chan, A.H.; Games, R.A.; Key, E.L. On the complexities of de Bruijn sequences. J. Comb. Theory Ser. A 1982, 33, 233–246. [Google Scholar] [CrossRef]
- Dubrova, E. A List of Maximum Period NLFSRs. IACR Cryptol. ePrint Arch. 2012, 2012, 166. [Google Scholar]
- Courtois, N.T.; Meier, W. Algebraic Attacks on Stream Ciphers with Linear Feedback. In Proceedings of the International Conference on the Theory and Applications of Cryptographic Techniques, Warsaw, Poland, 4–8 May 2003. [Google Scholar]
- Gammel, B.M.; Göttfert, R.; Kniffler, O. Status of Achterbahn and Tweaks. In Proceedings of the SASC 2006-Stream Ciphers Revisited, Leuven, Belgium, 2–3 February 2006. [Google Scholar]
- Siegenthaler, T. Correlation-immunity of nonlinear combining functions for cryptographic applications (Corresp.). IEEE Trans. Inf. Theory 1984, 30, 776–780. [Google Scholar] [CrossRef]
- Meier, W.; Staffelbach, O. Fast correlation attacks on certain stream ciphers. J. Cryptol. 1989, 1, 159–176. [Google Scholar] [CrossRef]
- Courtois, N.T. Fast Algebraic Attacks on Stream Ciphers with Linear Feedback. In Proceedings of the CRYPTO 2003: Advances in Cryptology, Santa Barbara, CA, USA, 17–21 August 2003; Volume 2729, pp. 176–194. [Google Scholar]
- Gammel, B.; Göttfert, R.; Kniffler, O. Achterbahn-128/80: Design and analysis. In Proceedings of the ECRYPT Workshop SASC 2007—The State of the Art of Stream Ciphers, Bochum, Germany, 31 January–1 February 2007. [Google Scholar]
- Gierlichs, B.; Batina, L.; Clavier, C.; Eisenbarth, T.; Gouget, A.; Handschuh, H.; Kasper, T.; Lemke-Rust, K.; Mangard, S.; Moradi, A.; et al. Susceptibility of eSTREAM Candidates towards Side Channel Analysis. In Proceedings of the ECRYPT Workshop SASC 2008–The State of the Art of Stream Ciphers, Lausanne, Switzerland, 13 February 2008. [Google Scholar]
- Lano, J.; Mentens, N.; Preneel, B.; Verbauwhede, I. Power analysis of synchronous stream ciphers with resynchronization mechanism. In Proceedings of the ECRYPT Workshop SASC 2004–The State of the Art of Stream Ciphers, Brugge, Belgium, 14–15 October 2004; pp. 327–333. [Google Scholar]
- Hell, M.; Johansson, T.; Meier, W. Grain-A Stream Cipher for Constrained Environments. Int. J. Wirel. Mob. Comput. 2007, 2, 86–93. [Google Scholar] [CrossRef]
- Babbage, S. The stream cipher MICKEY 2.0. In New Stream Cipher Designs; Springer: Berlin, Germany, 2006. [Google Scholar]
- De Cannìere, C.; Preneel, B. TRIVIUM Specifications. eSTREAM: the ECRYPT Stream Cipher Project. 2006. Available online: http://citeseerx.ist.psu.edu/viewdoc/summary?doi=10.1.1.59.9030 (accessed on 6 April 2019).
- Good, T.; Benaissa, M. Hardware performance of eStream phase-III stream cipher candidates. In Proceedings of the ECRYPT Workshop SASC 2008–The State of the Art of Stream Ciphers, Lausanne, Switzerland, 13 February 2008; pp. 163–173. [Google Scholar]
| Ni | 6 | 7 | 8 | 9 | 10 | 11 | 12 | 13 | 14 | 15 | 16 | 17 | 19 | 21 | 22 | 23 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 84 | 160 | 168 | 160 | 188 | 200 | 144 | 144 | 100 | 96 | 60 | 60 | 36 | 16 | 20 | 12 |
| KSG Components | Resources Usage | % of Usage for M2S005 | % of Usage for M2S150 | ||||
|---|---|---|---|---|---|---|---|
| LUTs | DFFs | LUTs | DFFs | LUTs | DFFs | ||
| NLFSRs | Shift registers | 0 | 223 | 0 | 3.71 | 0 | 0.15 |
| Feedback Functions | 32 | 0 | 0.52 | 0 | 0.02 | 0 | |
| Feedback Functions | 5 | 0 | 0.09 | 0 | 0.005 | 0 | |
| Total | 37 | 223 | 0.61 | 3.71 | 0.025 | 0.15 | |
| Function | DFF | AND2 | XOR2 |
|---|---|---|---|
| Gate Count | 8 | 1.5 | 2.5 |
| Components | Grain | Our KSGs | Trivium | MICKEY2 | ||
|---|---|---|---|---|---|---|
| Best Case | Worst Case | |||||
| Components | DFF (State Size) | 160 | 223 | 223 | 288 | 200 |
| XOR2 | - | 63 | 95 | 11 | - | |
| AND2 | - | 29 | 29 | 3 | - | |
| Gate count | 1294 | 1985 | 2065 | 2580 | 3188 | |
| Total Power | 109.4 | 120 | 120 | 175.1 | 196.5 | |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Mars, A.; Adi, W. New Family of Stream Ciphers as Physically Clone-Resistant VLSI-Structures. Cryptography 2019, 3, 11. https://doi.org/10.3390/cryptography3020011
Mars A, Adi W. New Family of Stream Ciphers as Physically Clone-Resistant VLSI-Structures. Cryptography. 2019; 3(2):11. https://doi.org/10.3390/cryptography3020011
Chicago/Turabian StyleMars, Ayoub, and Wael Adi. 2019. "New Family of Stream Ciphers as Physically Clone-Resistant VLSI-Structures" Cryptography 3, no. 2: 11. https://doi.org/10.3390/cryptography3020011
APA StyleMars, A., & Adi, W. (2019). New Family of Stream Ciphers as Physically Clone-Resistant VLSI-Structures. Cryptography, 3(2), 11. https://doi.org/10.3390/cryptography3020011





