An Authenticated Group Shared Key Mechanism Based on a Combiner for Hash Functions over the Industrial Internet of Things
Abstract
1. Introduction
- Secure communication lacking in a predisseminated shared key among a group of IIoT devices.
- Identify compromised IIoT devices and authenticate the identity of the group controller and all members. Moreover, the received data integrity must be verified at each IIoT device.
- The complicated design of the group-shared key mechanism in the resource constraints devices, such as the IIoT, which should consider both security strength and computational time.
- The dynamic supporting for join/leave members of the group.
- The optimal level of self-arrangement of the group shared key.
- The resource is constrained in terms of storage, computation, and communication power.
- The proposed research builds an efficient authenticated group shared key (AGSK) among a set of industrial objects using the IIoT network platform. The common shared key over the IIoT utilizes the combiner for the geolocation hash function and the digital signature of each IIoT device.
- It proposes a key management algorithm to join and leave any group member that allows the IIoT gateway to optimize the number of required steps to dynamically change the old AGSK. Furthermore, the proposed algorithm guarantees to prevent the leaving member from using the IIoT network platform after issuing the leaving request.
- Optimal design of two-handshaking communication messages between the IIoT devices and IIoT gateway to establish the group shared key.
- The random oracle model has been used to prove the security of the AGSK and the adversary model for IIoT network that has been analyzed. In addition, countermeasures against adversary attacks have been investigated.
- Finally, the proposed method has been implemented in an emulation system, assessed (i.e., computation time, power, and storage costs), and compared with the recent baseline group shared key mechanisms.
2. Related Work on Group Shared Key
- The group-shared key was established in the proposed system using two-way handshaking, which reduced communication costs between the IIoT devices and the gateway.
- The combiner for the hash function and digital signature in the proposed system can resist the most effective key attacks, such as the related key, and the key that compromises impersonation attacks.
3. System Design of AGSK Algorithm
3.1. Group Key Management Algorithm
- The IIoT gateway is connected at all times, which means it cannot leave the group. Furthermore, it has a strong security system that can resist any attack.
- During a programming session, the domain parameters are embedded and uploaded to all IIoT devices.
- Every IioT device has two secret keys: a public key that is accessible to all other IioT devices and a private key that is kept secret from the public.
3.1.1. Group Shared Key Generation
- Any IIoT device has data to be sent and it calculates the private key and the public key. The random generator function is used to select the private key d between 1, and n − 1. The scalar multiplication of d and G (e.g., Q = d × G) is used to calculate the public key Q.
- Using unicast forwarding, all public keys for the involved IIoT devices should be sent to the IIoT gateway to calculate the preshared key (PSK) for each of the IIoT devices, as follows:
- The preshared group point for the device number j () can be calculated at the gateway as follows:
- The gateway unicasts the to the device number j, which will calculate the group shared point (), while the x coordinate of will be selected as the group shared key at the device number j (), as follows:
- Finally, the gateway can calculate the GSK for the device number j, as follows:

3.1.2. Authentication Based on ECDH and Combiner for Hash Function
- Step 1: Digital Signature for the Digest of Public Key.
- (1)
- Each IIoT device selects the private key d and calculates the public key Q.
- (2)
- The message authentication code (MAC) is calculated for Q using the hash function-based GPS location for the IIoT device.
- (3)
- (4)
- The digital signature and the Q are sent to the IIoT gateway in the same message.
- Step 2: Digital Signature Verification and Sender Authentication.
- Upon receiving the unicast messages from all IIoT groups, the gateway performs the following verification and authentication:
- (1)
- Three steps of curve-point inspection should be employed to confirm the real identity of the sender who used their signature to sign the Q: 1. Verify that Q lies on the curve. (2) Verify that Q is not equivalent to the identity element O. 3. Verify that n × Q = O.
- (2)
- Verify the sender signature using the received Q. This means that the gateway uses the Q to inverse the digital signature and it uses the stored geolocation of the sender to implement the hash function and to compare the received digest with the calculated one. If they match, the sender is legitimate, and the data are valid. Otherwise, the sender or the data are invalid, and the message is discarded.
- Step 3: Gateway Digital Signature for PGP.
- (1)
- Upon verifying and authenticating all the IIoT devices in the group, the IIoT gateway will calculate the PGP and GSK for each device.
- (2)
- The IIoT gateway creates a MAC for each PGP using GSK, and it signs the MACs using its private key.
- (3)
- The digital signature of the gateway (SG) and the PGP are sent to the corresponding IIoT device.
- Step 4: Verifying Gateway Digital Signature.
- (1)
- Upon receiving the gateway message at the IIoT sender, the true identity of the gateway is verified using three steps of curve-point inspection of PGP.
- (2)
- If the PGP is verified, it will be used to calculate the GSK using Equation (3). Furthermore, the sign−1 (QG,SG) is applied to obtain the received digest (MAC for PGP), which will be compared using the calculated digest of the IIoT device. If they matched, the gateway is legitimate, and the PGP is authenticated. Otherwise, the message will be discarded.
| Algorithm 1. AGSK pseudocode | |
| Input: Secp192r1 domain parameters p, a, b, G, n, h. | |
| Output: S, SG, GSK. | |
| Start Algorithm (AGSK) | |
| 1 | | While (new session start) do |
| 2 | | For (each IIoT device in the group) do |
| 3 | | Pick private key (dS);//1 ≤ dS ≤ n |
| 4 | | Q = (d × G); |
| Step 1: Digital Signature for the Digest of Public Key. | |
| 5 | | MAC(Q) = H(GLoc,Q); //Calculate MAC (Q) based on a hash function and key Gloc |
| 6 | | S = Sign (d,MAC);// Apply digital signature based on private key d for MAC |
| 7 | | Send_to_Gateway(S,Q);//Send public key with IIoT device signature to gateway |
| Step 2: Digital Signature Verification and Sender Authentication. | |
| 8 | | Verify_Public_key(Q);//Gateway will verify Q using the three steps of point |
| 9 | | Retrieve_Gloc(IIoT_ID); //Gateway retrieves Gloc from its database using IIoT ID |
| 10 | | if (H(Gloc,Q)==Sign−1(Q,S));/*Gateway can inverse S and obtain the received digest using Q. Furthermore, it compares calculated digest with received */ |
| 11 | | The IIoT sender is legitimate, and Q is valid. |
| 12 | | else |
| 13 | | The IIoT sender or Q is invalid; Discard_message(); |
| 14 | | End;//For loop |
| Step 3: Gateway Digital Signature for PGP. | |
| 15 | | Calculate (PGP);// Gateway calculates PGP for all IIoT devices as in Equation (2). |
| 16 | | MAC(PGP) = H(GSK,PGP); //Calculate MAC (PGP) based on a hash function and GSK |
| 17 | | SG = Sign (dG,MAC);// Apply digital signature based on private key d for MAC |
| 18 | | Send_to_IIoT(SG,PGP,QG);//Gateway sends SG,PGP,QG to the corresponding IIoT |
| Step 4: Verifying Gateway Digital Signature. | |
| 19 | | Verify_PGP();//Corresponding IIoT verifies PGP using the three steps of point |
| 20 | | Calculate (GSK); //it calculates the GSK as in Equation (3). |
| 21 | | if (H(GSK,PGP)==Sign−1(QG,SG));/*IIoT device can inverse SG and obtain received digest using QG. Moreover, it compares calculated digest with received */ |
| 22 | | The Gateway is legitimate, and PGP is valid. |
| 23 | | else |
| 24 | | The gateway or PGP is invalid; Discard_message(); |
| 25 | | End;//While loop |
| 26 | End;//Algorithm |

3.1.3. Dynamic Join and Leave in the Proposed AGSK
- (1)
- The new device(s) will send an authenticated unicast message that includes the public key, a digital signature, and a request to join/leave.
- (2)
- Upon the gateway receiving the join/leave request, it authenticates the sender and message data (e.g., geolocation data), recalculates the PGP, creates the digest (MAC) for the new PGP based on the new GSK, and signs the digest with its private key.
- (3)
- The gateway will specifically unicast a reply message to all IIoT devices. The reply message contents include the new PGP, the gateway digital signature, and the public key of the gateway.
- (4)
- If the IIoT node leaves the group, it will inform the gateway, which will create a new PSK between the gateway and the remaining IIoT devices. This means that the PGP will not function in the leaving node. However, if the node wants to join, it will receive the reply message and implement the four steps for the AGSK algorithm.
4. Cybersecurity Analysis
4.1. IIoT Adversary Model
- Spoofing attack: The attacker intercepts or eavesdrops on the exchange messages among the IIoT devices to determine the AGSK vulnerability and obtain access to the IIoT system information.
- A man-in-the-middle attack (MITM): The attacker eavesdrops on the traffic among the IIoT devices or between the IIoT devices and the gateway. The active MITM can manipulate or modify the packets sent to all those devices.
- A brute-force attack: The attacker attempts every available combination of letters, numbers, and symbols in the hash algorithm to obtain the hash key, which could produce the same output. This means the attacker can successfully break the AGSK even if both sides employ exceedingly difficult-to-crack domain parameters for the ECDH technique.
- An IIoT capture attack: To launch cyberattacks against the IIoT network, the attacker kidnaps an IIoT device and obtains the domain parameters and all its other credentials.
- A stolen-verifier attack: The attacker who has taken the AGSK from an IIoT device can pose for authorized access to all messages that are being exchanged among the IIoT devices. Moreover, the attacker who stole the AGSK can launch cyberattacks against the other IIoT devices to steal data or bypass the access rules.
4.2. Cryptanalysis of AGSK
- Ciphertext-only attack: The adversary makes an effort to decipher the plaintext that was encrypted by knowing one or more ciphertexts. It is the simplest to execute in practice because all the adversary needs to do is eavesdrop on the open communication line being used to send the encrypted communications.
- Known-plaintext attack: The adversary knows some of the pairs of the ciphertext and corresponding plaintexts that share the same key. The adversary’s goal is to ascertain the encrypted plaintext to produce a different ciphertext for which the corresponding plaintext is unknown.
- Chosen plaintext attack (CPA): The ciphertexts for whatever plaintext the adversary chooses are assumed to be obtained by the adversary. The adversary can also choose the new input for encryption using the adaptive CPA (CPA2) based on an inspection of the plaintext queries that they have formerly chosen and their accompanying ciphertexts [31].
- Chosen ciphertext attack (CCA): The adversary is expected to be able to crack any ciphertext(s) of their choosing. In addition, the adaptive CCA (CCA2) enables the adversary to change the input they select for the decryption depending on an analysis of the queries they originally chose [32].
- Related-key attacks. The attacker creates a mathematical relationship between various keys, and after a session is established with those connected keys, the adversary is given access to the oracle function of the AGSK. The goal of this adversary is to obtain the genuine shared key from the AGSK. The permutation Pm (K, S(GSK)) is defined as the assortment of all the authenticated group shared keys S(GSKs) with the domain and keys pace K. Furthermore, let be a collection of functions that map K to the output of the associated key . The permitted to relate-key-deriving functions are denoted by the acronym RKD (i.e., allowed a key transformation). We can express the oracle of the related key RK(.) on the S(GSK), as an oracle that accepts two parameters ϕ ∈ and a message M ∈ S(GSK), and it returns Sϕ(k)(M). This can be written in pseudocode as:
- Oracle ERK(ϕ, k)(M) // where M ∈ S(GSK) and RK(ϕ,k) →K is a related function.
- ← ϕ (k); σ ← (M);
- return σ;
- the following is the definition of the pseudorandom permutation in relation to related-key attacks (PRP-RKA):
| Adversary |
| Run A, responding to A’s request (K, M), as follows: |
| Return |
| Until A halts returning a bit b; Return b; } |
4.3. Cyberattacks Analysis
4.3.1. Countermeasures against Replay and MITM Attacks
- Three steps must be taken by the replay and MITM attacker before they may resend the intercepted message, which are GSK determination, MAC calculation, and digital signature implementation, and these are very difficult to compromise without violating the hash function.
- The sender is authenticated based on the geolocation hash function, which is combined with the sender’s digital signature.
- The sender’s private key is used to compute the digital signature, and that key is safeguarded by another hash function.
4.3.2. Countermeasures against Brute Force Attacks
4.3.3. Countermeasures against Device Capture and Stolen-Verifier Attacks
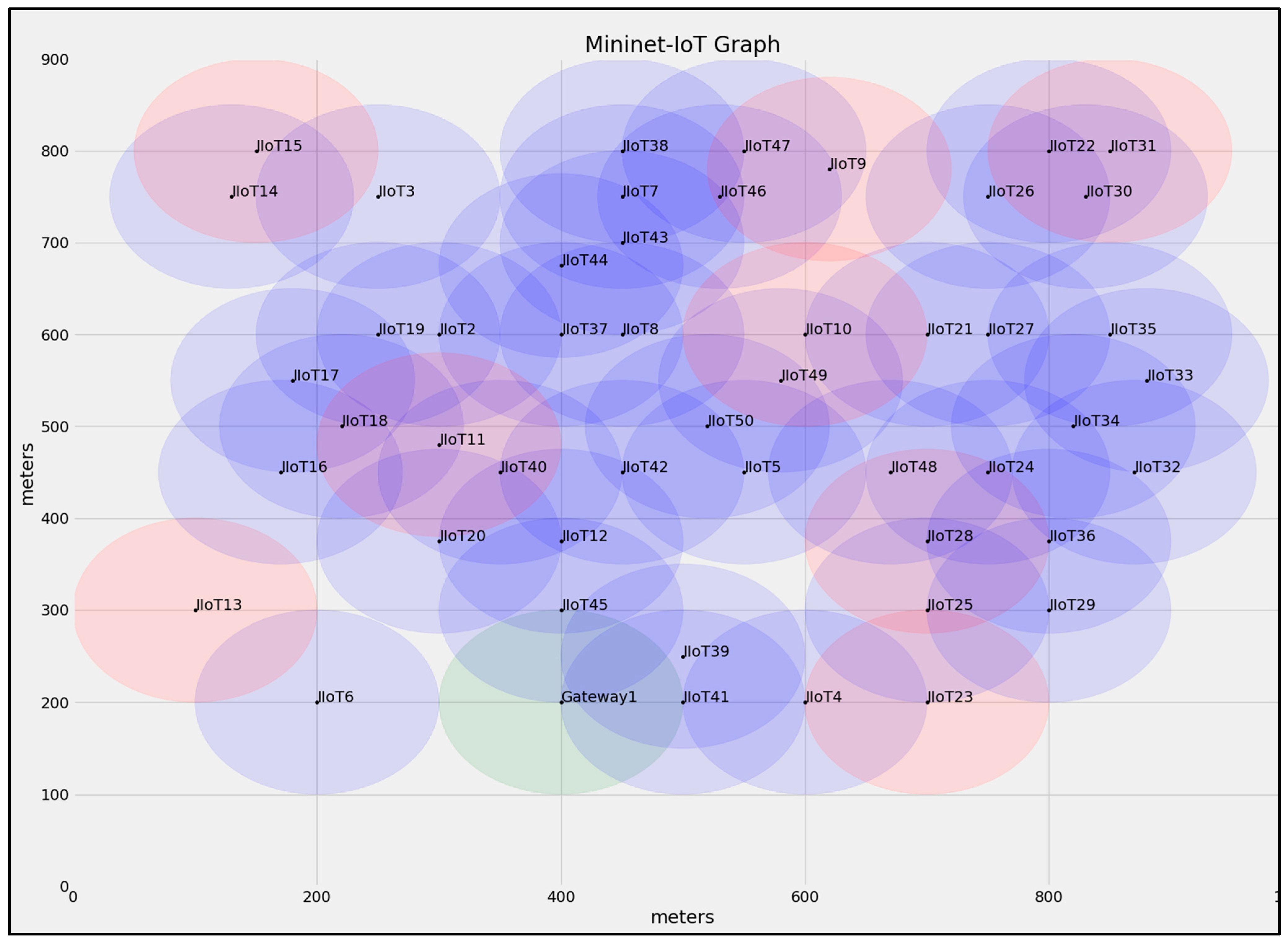
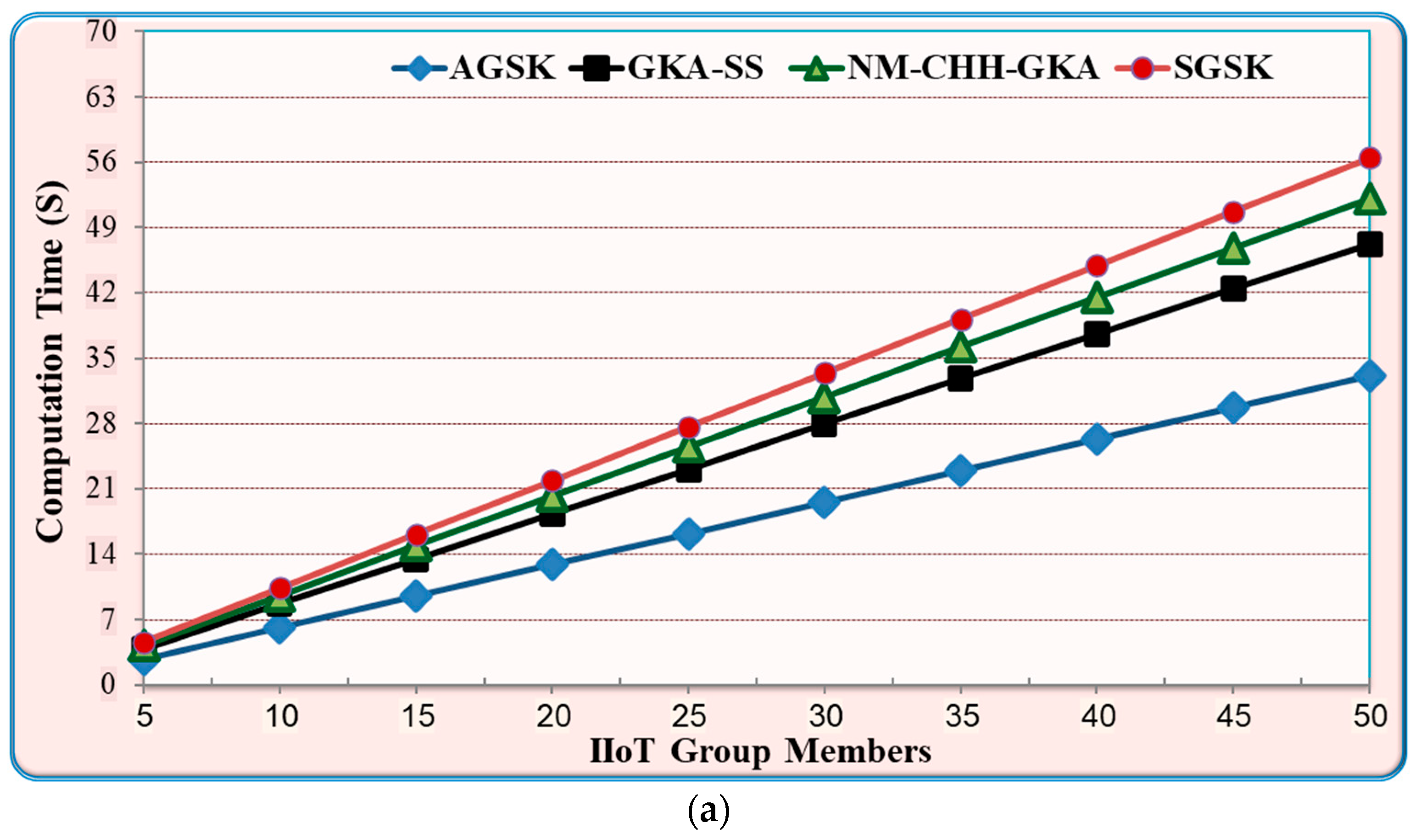
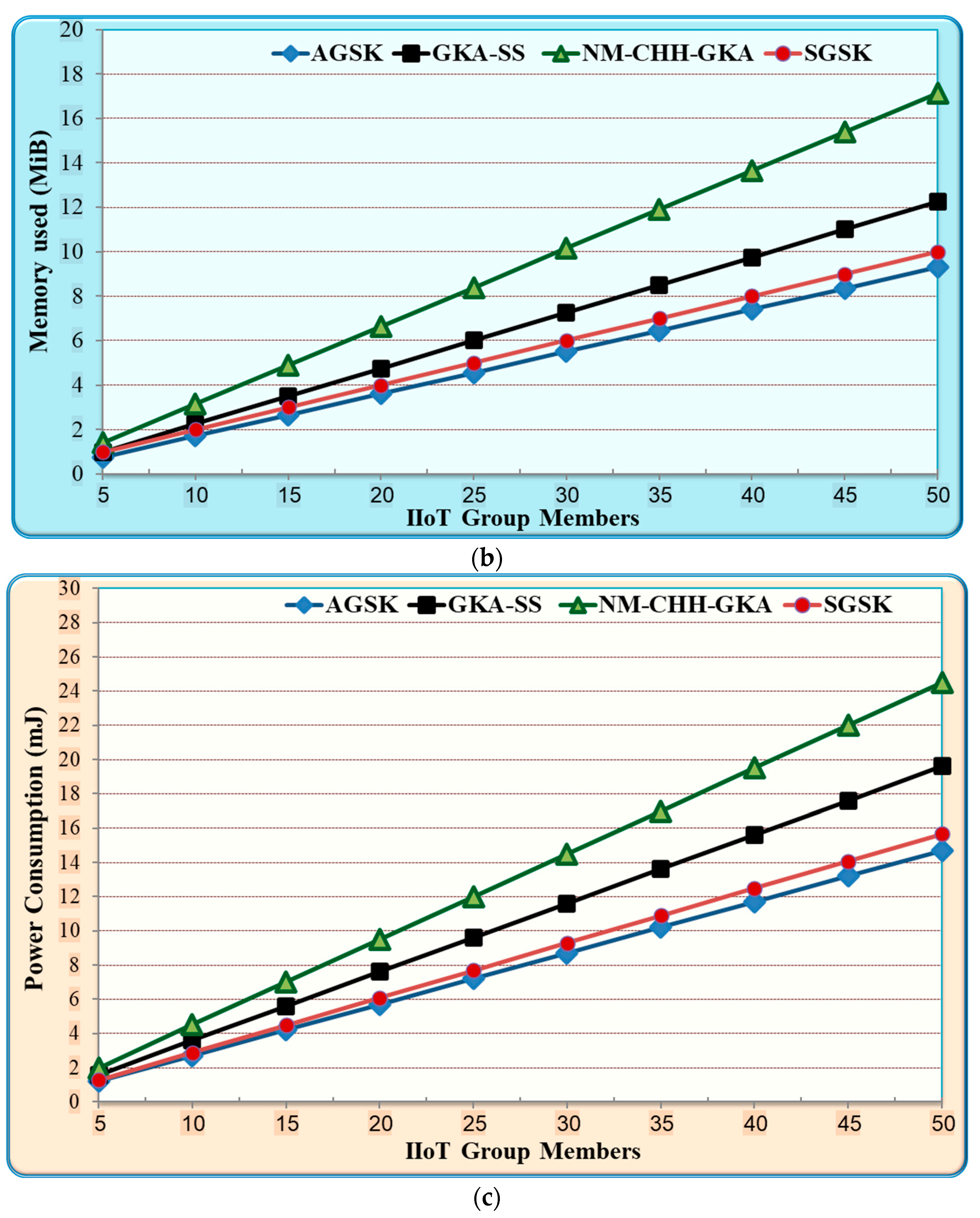
5. Implementation and Performance Evaluation of the AGSK on the IIoT
5.1. Comparison between AGSK and Baseline Mechanisms
5.1.1. Performance Evaluation of the Group Shared Key
- Results and Discussion
5.1.2. Performance Evaluation of Join/Leave Members
- Results and Discussion
6. Conclusions and Future Work
Author Contributions
Funding
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Szymoniak, S.; Kesar, S. Key Agreement and Authentication Protocols in the Internet of Things: A Survey. Appl. Sci. 2023, 13, 404. [Google Scholar] [CrossRef]
- Sarker, I.H.; Khan, A.I.; Abushark, Y.B.; Alsolami, F. Internet of Things (IoT) Security Intelligence: A Comprehensive Overview, Machine Learning Solutions and Research Directions. Mob. Netw. Appl. 2022, 27, 1–17. [Google Scholar] [CrossRef]
- Choo, K.-K.R.; Gritzalis, S.; Park, J.H. Cryptographic Solutions for Industrial Internet-of-Things: Research Challenges and Opportunities. IEEE Trans. Ind. Inform. 2018, 14, 3567–3569. [Google Scholar] [CrossRef]
- He, D.; Ma, M.; Zeadally, S.; Kumar, N.; Liang, K. Certificateless Public Key Authenticated Encryption with Keyword Search for Industrial Internet of Things. IEEE Trans. Ind. Inform. 2018, 14, 3618–3627. [Google Scholar] [CrossRef]
- Kittur, A.S.; Pais, A.R. A trust model based batch verification of digital signatures in IoT. J. Ambient. Intell. Humaniz. Comput. 2019, 11, 313–327. [Google Scholar] [CrossRef]
- Li, S.; Zhang, T.; Yu, B.; He, K. A Provably Secure and Practical PUF-Based End-to-End Mutual Authentication and Key Exchange Protocol for IoT. IEEE Sens. J. 2021, 21, 5487–5501. [Google Scholar] [CrossRef]
- Khatoon, S.; Rahman, S.M.M.; Tso, R.; Alhamid, M.F. An efficient and secure, ID-based authenticated, asymmetric group key agreement protocol for ubiquitous pay-TV networks. J. Internet. Technol. 2020, 21, 1387–1395. [Google Scholar]
- Diro, A.A.; Chilamkurti, N.; Kumar, N. Lightweight Cybersecurity Schemes Using Elliptic Curve Cryptography in Publish-Subscribe fog Computing. Mob. Netw. Appl. 2017, 22, 848–858. [Google Scholar] [CrossRef]
- Bu, L.; Isakov, M.; Kinsy, M.A. A secure and robust scheme for sharing confidential information in IoT systems. Ad. Hoc. Netw. 2019, 92, 101762. [Google Scholar] [CrossRef]
- Ahmed, A.A.; Barukab, O.M. Unforgeable Digital Signature Integrated into Lightweight Encryption Based on Effective ECDH for Cybersecurity Mechanism in Internet of Things. Processes 2022, 10, 2631. [Google Scholar] [CrossRef]
- Naresh, V.S.; Reddi, S.; Murthy, N.V. A provably secure cluster-based hybrid hierarchical group key agreement for large wireless ad hoc networks. Hum. Cent. Comput. Inf. Sci. 2019, 9, 26. [Google Scholar] [CrossRef]
- Yang, Z.; Wang, Z.; Qiu, F.; Li, F. A group key agreement protocol based on ecdh and short signature. J. Inf. Secur. Appl. 2023, 72, 103388. [Google Scholar] [CrossRef]
- Lo, J.W.; Wu, C.Y.; Chiou, S.F. A lightweight authentication and key agreement scheme for telecare medicine information system. J. Internet. Technol. 2020, 21, 263–272. [Google Scholar]
- Janani, V.S.; Manikandan, M.S. Enhanced security using cluster based certificate management and ECC-CRT key agreement schemes in mobile ad hoc networks. Wirel. Pers. Commun. 2017, 97, 6131–6150. [Google Scholar] [CrossRef]
- Jiang, Y.; Shen, Y.; Zhu, Q. A lightweight key agreement protocol based on Chinese remainder theorem and ECDH for smart homes. Sensors 2020, 20, 1357. [Google Scholar] [CrossRef]
- Liu, L.; Wang, Y.; Zhang, J.; Yang, Q. A secure and efficient group key agreement scheme for VANET. Sensors 2019, 19, 482. [Google Scholar] [CrossRef]
- Rawat, A.; Deshmukh, M. Tree and elliptic curve based efficient and secure group key agreement protocol. J. Inform. Secur. Appl. 2020, 55, 102599. [Google Scholar] [CrossRef]
- Wang, Y.; Ramamurthy, B.; Zou, X. The performance of elliptic curve based group Diffie–Hellman protocols for secure group communication over ad hoc networks. In Proceedings of the 2006 IEEE International Conference on Communications, Istanbul, Turkey, 11–15 June 2006; pp. 2243–2248. [Google Scholar]
- Zhang, Q.; Zhu, L.; Li, Y.; Ma, Z.; Yuan, J.; Zheng, J.; Ai, S. A group key agreement protocol for intelligent internet of things system. Int. J. Intell. Syst. 2022, 37, 699–722. [Google Scholar] [CrossRef]
- Naresh, V.S.; Allavarpu, V.V.L.D.; Reddi, S.; Murty, P.S.R.; Raju, N.V.S.L.; Mohan, R.N.V.J. A provably secure sharding based blockchain smart contract centric hierarchical group key agreement for large wireless ad-hoc networks. Concurr. Comput. Pract. Exper. 2022, 34, e6553. [Google Scholar] [CrossRef]
- Li, X.; Yin, X. Blockchain-based group key agreement protocol for vehicular ad hoc networks. Comput. Commun. 2022, 183, 107–120. [Google Scholar] [CrossRef]
- Wu, Y.; Feng, T. An Anonymous Authentication and Key Update Mechanism for IoT Devices Based on EnOcean Protocol. Sensors 2022, 22, 6713. [Google Scholar] [CrossRef] [PubMed]
- Songshen, H.A.N.; Kaiyong, X.U.; Zhiqiang, Z.H.U.; Songhui, G.U.O.; Haidong, L.I.U.; Zuohui, L.I. Hash-Based Signature for Flexibility Authentication of IoT Devices. Wuhan Univ. J. Nat. Sci. 2022, 27, 1–10. [Google Scholar]
- Zhang, F.; Wang, H.; Zhou, L.; Xu, D.; Liu, L. A blockchain-based security and trust mechanism for AI-enabled IIoT systems. Future Gener. Comput. Syst. 2023, 147, 78–85. [Google Scholar] [CrossRef]
- Uppuluri, S.; Lakshmeeswari, G. Secure user authentication and key agreement scheme for IoT device access control based smart home communications. Wirel. Netw. 2023, 29, 1333–1354. [Google Scholar] [CrossRef]
- Rahman, H.; Haghighat, A.; Hossein, E.S. A Secure Anonymous D2D Mutual Authentication and Key Agreement Protocol for IoT. Internet Things 2022, 18, 100493. [Google Scholar]
- Ahmed, A.A.; Ahmed, W.A. An Effective Multifactor Authentication Mechanism Based on Combiners of Hash Function over Internet of Things. Sensors 2019, 19, 3663. [Google Scholar] [CrossRef]
- Ahmed, A.A. Lightweight Digital Certificate Management and Efficacious Symmetric Cryptographic Mechanism over Industrial Internet of Things. Sensors 2021, 21, 2810. [Google Scholar] [CrossRef]
- Gong, X.; Feng, T. Lightweight Anonymous Authentication and Key Agreement Protocol Based on CoAP of Internet of Things. Sensors 2022, 22, 7191. [Google Scholar] [CrossRef]
- Saleem, K.; Khalil, M.S.; Fisal, N.; Ahmed, A.A.; Orgun, M.A. Efficient random key based encryption system for data packet confidentiality in WSNs. In Proceedings of the 2013 12th IEEE International Conference on Trust, Security and Privacy in Computing and Communications, Melbourne, VIC, Australia, 16–18 July 2013; pp. 1662–1668. [Google Scholar]
- Biryukov, A. Adaptive Chosen Plaintext Attack. In Encyclopedia of Cryptography and Security; Van Tilborg, H.C.A., Jajodia, S., Eds.; Springer: Boston, MA, USA, 2011. [Google Scholar]
- Biryukov, A. Related Key Attack. In Encyclopedia of Cryptography and Security; Van Tilborg, H.C.A., Jajodia, S., Eds.; Springer: Boston, MA, USA, 2011. [Google Scholar]
- Silverma, J.H. An Introduction to the Theory of Elliptic Curves, Summer School on Computational Number Theory and Applications to Cryptography; Brown University: Providence, RI, USA, 2006. [Google Scholar]
- Vidya, R.; Prema, K.V. Lightweight hashing method for user authentication in Internet-of-Things. Ad. Hoc. Netw. 2019, 89, 97–106. [Google Scholar]
- Chuang, Y.-H.; Lo, N.-W.; Yang, C.-Y.; Tang, S.-W. A Lightweight Continuous Authentication Protocol for the Internet of Things. Sensors 2018, 18, 1104. [Google Scholar] [CrossRef]
- Riad, K.; Huang, T.; Ke, L. A dynamic and hierarchical access control for IoT in multi-authority cloud storage. J. Netw. Comput. Appl. 2020, 160, 102633. [Google Scholar] [CrossRef]
- Alamer, A. An efficient group signcryption scheme supporting batch verification for securing transmitted data in the Internet of Things. J. Ambient. Intell. Humaniz. Comput. 2020, 11, 1–18. [Google Scholar] [CrossRef]
- Lochter, M.; Merkle, J. RFC 5639: Elliptic Curve Cryptography (ECC) Brainpool Standard Curves and Curve Generation; IETF: Fremont, CA, USA, 2010. [Google Scholar]
- Mininet-IoT Emulator of Internet of Things. Available online: https://github.com/ramonfontes/mininet-iot (accessed on 27 November 2022).
- IPv6 over Low-Power Wireless Personal Area Networks (6LoWPANs): Overview, Assumptions, Problem Statement, and Goals. Available online: http://www.ietf.org/rfc/rfc4919.txt (accessed on 27 November 2022).



| Notation | Meaning | Notation | Meaning |
|---|---|---|---|
| AGSK | Authenticated group shared key | MAC | Message authentication code |
| C | Ciphertext | n | order of G |
| CCA | Chosen cipher attack | O | A further point in the curve’s infinite |
| CPA | Chosen plaintext attack | P | Modular prime |
| CPU | Central processing unit | PGP | Preshared group point |
| d | Private key | PSK | Preshared key |
| ECC | Elliptic curve cryptography | PFS | Perfect forward secrecy |
| ECDH | Elliptic Curve Diffie Hellman | Q | Public key |
| G | Base point generator | S | Digital Signature |
| Group shared point at device j | GSK | Group shared key | |
| h | Subgroup cofactor | PSK between the gateway and device i | |
| IIoT | Industrial Internet of Things |
| Parameter | Values |
|---|---|
| ECDH curve domain parameters | Secp192r1 |
| Key size | 192 Bits |
| MAC and PHY | 802.15.14_hmsim and 802.11_hmsim |
| Event area | (1000 m × 900 m) |
| Cover of IIoT device | 150 m |
| Cover range of Gateway1 | 250 m |
| Propagation model | Shadowing |
| Path loss exponent | 3.0 |
| Shadowing deviation (dB) | 3.0 |
| Traffic emulator | TCP client/server socket programming |
| Number of packets | 1000 packets, each packet 127 bytes |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Ali, W.; Ahmed, A.A. An Authenticated Group Shared Key Mechanism Based on a Combiner for Hash Functions over the Industrial Internet of Things. Processes 2023, 11, 1558. https://doi.org/10.3390/pr11051558
Ali W, Ahmed AA. An Authenticated Group Shared Key Mechanism Based on a Combiner for Hash Functions over the Industrial Internet of Things. Processes. 2023; 11(5):1558. https://doi.org/10.3390/pr11051558
Chicago/Turabian StyleAli, Waleed, and Adel Ali Ahmed. 2023. "An Authenticated Group Shared Key Mechanism Based on a Combiner for Hash Functions over the Industrial Internet of Things" Processes 11, no. 5: 1558. https://doi.org/10.3390/pr11051558
APA StyleAli, W., & Ahmed, A. A. (2023). An Authenticated Group Shared Key Mechanism Based on a Combiner for Hash Functions over the Industrial Internet of Things. Processes, 11(5), 1558. https://doi.org/10.3390/pr11051558








