Towards a Universal Privacy Model for Electronic Health Record Systems: An Ontology and Machine Learning Approach
Abstract
1. Introduction
- We presented a privacy ontology and analyzed EHR use cases to establish a standardized framework for data management, access control, and sensitive health information categorization, promoting interoperability and efficiency for healthcare stakeholders.
- We proposed an ML-based model to identify PII from privacy policies, integrated it with the ontology for a robust medical records protection framework, and demonstrated its effectiveness in distinguishing valid and illegitimate EHR privacy policies, enhancing patient care and privacy.
- For future research directions, we recommended conducting thorough assessments, concentrating on adaptive frameworks, ethical considerations, and implementation strategies to create a widely embraced solution for healthcare information privacy.
2. Related Work
2.1. Personally-Controlled EHR Systems
2.2. Ensuring Privacy through Smart Contract—Healthcare Blockchain Systems
2.3. Context-Sensitive Privacy Policies
2.4. Homomorphic Encryption in EHR Systems
2.5. Comparison with Our Study
- ✔
- An Attempt at Comprehensive Privacy Protection: Our approach endeavored to create a privacy protection solution that is more robust and specific to healthcare information systems by combining ontology and ML. While we believe it can offer improved protection, further studies and real-world testing are necessary to validate this claim.
- ✔
- Consideration of Legal Requirements: We made an effort to incorporate the breadth of GDPR and other privacy regulations into our proposed solution, aiming to ensure compliance with the necessary legal requirements. However, adapting to evolving legal landscapes will require continuous updates and adjustments.
- ✔
- Exploration of Balancing Privacy and Accessibility: Our proposed solution attempts to balance the preservation of patients’ health information privacy with the necessity of access for authorized healthcare providers. Future studies should focus on how well we have achieved this balance in various real-world scenarios.
- ✔
- Aim for User-friendly and Accessible Systems: We acknowledged the complex nature of health information and the diverse range of devices and platforms used to access EHR systems. Our study aimed for a more inclusive approach to healthcare information management, although the user-friendliness of our solution remains to be evaluated in diverse patient groups.
- ✔
- Emphasis on Real-world Implementation and Evaluation: We strove to provide solutions that can be implemented and evaluated in real-world healthcare settings. Our approach takes a practical perspective, though extensive empirical evidence to support its effectiveness is yet to be collected.
- ✔
- Acknowledgment of Cultural and Social Context: We considered the cultural and social context of EHR system development and implementation in our study, aiming for a solution that can cater to diverse needs. However, further research is required to confirm the adaptability of our solution to different cultural and social contexts.
3. Research Motivation
3.1. Use Case Scenarios
3.1.1. Scenario 1: Primary Care Physician
- Stakeholders: PCP, patient, patient’s son, and mental health professional.
- Health Information: Private (address, location), Personal (demographic details), Sensitive (medical and psychological history), Historical (previous health assessments).
3.1.2. Scenario 2: Emergency Care
- Stakeholders: Nurse, patient, medical team, and Medicare.
- Health Information: Private (address, location), Personal (demographic details, Medicare details), Sensitive (medical history, accident details).
3.1.3. Scenario 3: Clinical Research
- Stakeholders: Researcher, GP, patient, clinical trials team.
- Health Information: Private (address, location), Personal (demographic details), Sensitive (medical history, family history), Historical (previous treatment records).
3.1.4. Scenario 4: Multi-Disciplinary Consultation
- Stakeholders: Primary care physicians, specialists, therapists, social workers, patient.
- Health Information: Private (address, location), Personal (demographic details), Sensitive (medical and genetic history), Historical (treatment and therapy records).
3.1.5. Scenario 5: Telehealth
- Stakeholders: Patient, healthcare providers, telehealth platform provider.
- Health Information: Private (address, location), Personal (demographic details), Sensitive (medical history), Historical (previous consultation records).
3.1.6. Scenario 6: Data Breach
- Stakeholders: Patients, healthcare organization, IT department, potentially unauthorized third parties.
- Health Information: Private (address, location), Personal (demographic details), Sensitive (medical history), Historical (previous treatment records).
3.2. Research Challenges
- Sharing personal information with relevant stakeholders: According to APP 6 [21], personal information should only be shared with pertinent stakeholders for a specified purpose, such as treatment or daily care with GPS or nurses. Personal health information may also be shared for secondary purposes under certain conditions. However, discerning these secondary purposes within the existing EHR literature proves to be a substantial research challenge. This difficulty extends to sensitive health information as well. While the APP principles are generic and can be applied to any domain, implementing these principles within the health information domain is particularly challenging. As a result, the development of a privacy ontology for EHR systems is necessary.
- Identifying relevant stakeholders: One of the detailed challenges involved in building the privacy ontology includes identifying the relevant stakeholders associated with different EHR systems. These stakeholders can range from healthcare providers, insurance companies, and government agencies to patients themselves. A privacy ontology should be able to accommodate these various stakeholder groups and their respective access levels, ensuring that sensitive patient information is only accessible to those with appropriate authorization.
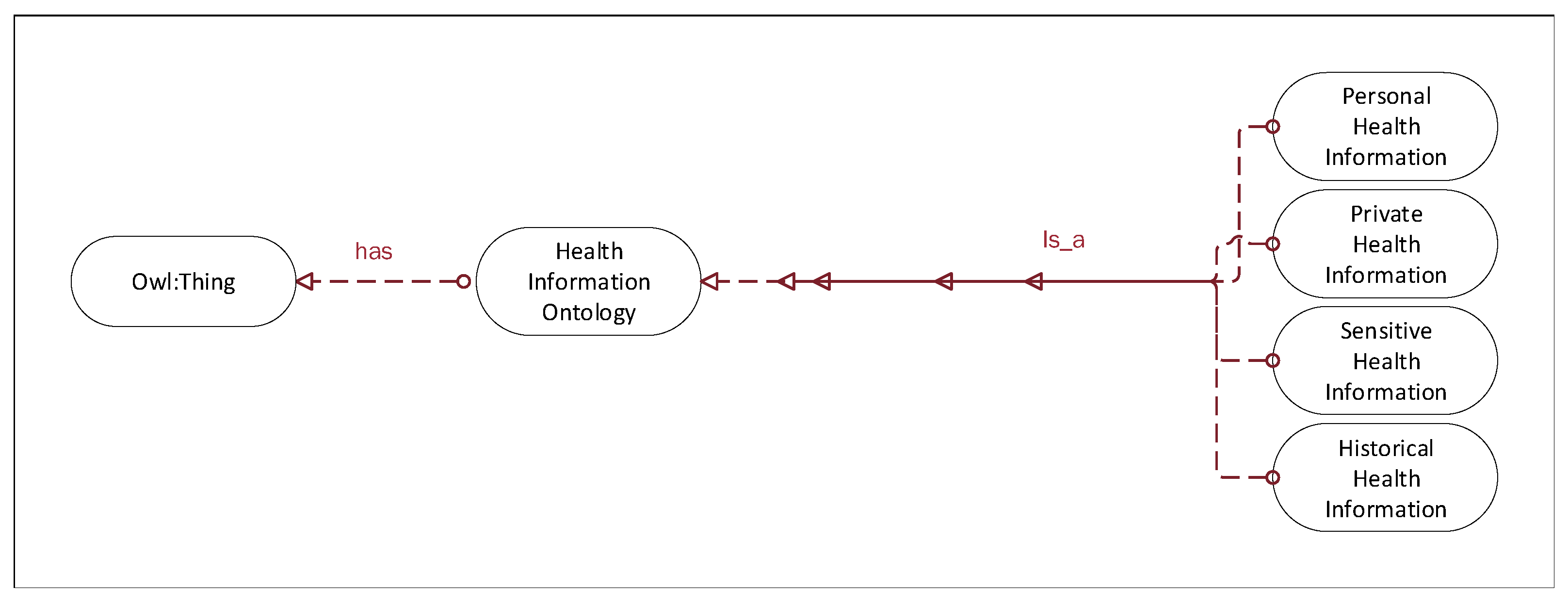
- Categorizing different levels of health-related patient information: Another challenge is to categorize different levels of health-related patient information, which may range from general health indicators to highly sensitive data, such as genetic test results or mental health records. Creating a privacy ontology that can effectively classify this information is essential for implementing appropriate access controls and maintaining patient confidentiality.
- Defining privacy rules and policies: The privacy ontology should also define privacy rules and policies for relevant health-related stakeholders, allowing them to share patient health records across different EHR platforms securely. These rules and policies should be robust, flexible, and adaptable to accommodate the diverse and evolving needs of different healthcare systems and their stakeholders.
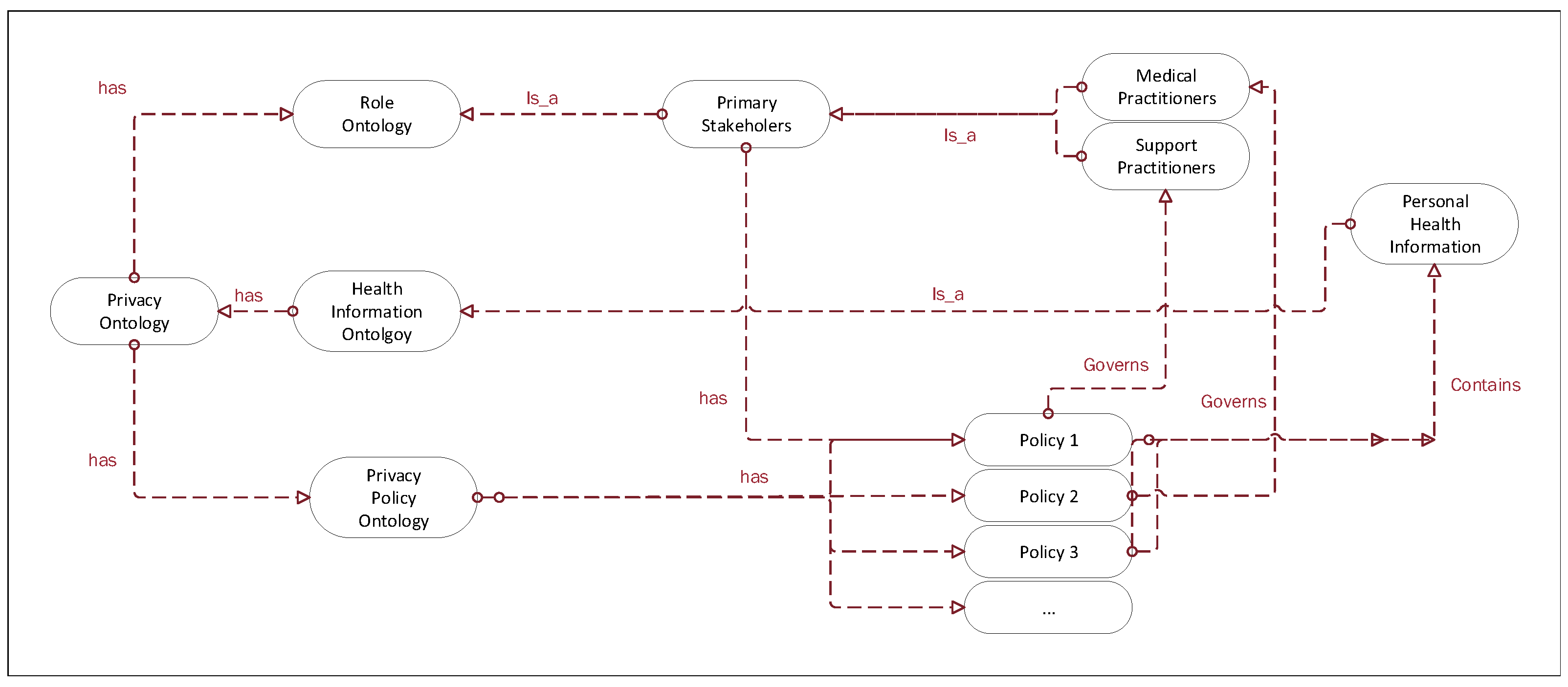
4. A Privacy Model for EHR Systems
4.1. Leveraging Ontology and ML for Enhanced e-Healthcare Privacy
4.1.1. Intrusion Detection and Prevention
4.1.2. Confidentiality and Privacy of EHR
4.1.3. Improved Indexing and Retrieval Performance
4.1.4. Secure Data Access and Privacy Preservation
4.1.5. Privacy Disclosure Measurement
4.1.6. Efficiency and Accuracy in Clinical Information Extraction
4.1.7. Structured Approach to Organizing Clinical Data
4.2. Conceptual Privacy Models
- Identify stakeholders: the relevant stakeholders need to be identified from the application scenarios.
- Identify technologies: the relevant health technologies and platforms need to be identified to gather health related information.
- Identify health information: the health information and records need to be identified and labelled in different categories, such as private record, sensitive record, and so on.
4.3. Identifying Stakeholders
4.4. Redefining Health Information and Privacy Rules
- Identifiable Health Information: This includes any data that can be used to identify an individual, such as name, address, and location. This is akin to what was previously described as ’private health information’ and ’personal information’. Under the GDPR and similar laws, all health information is considered sensitive, hence our shift towards a unified category.
- Health Record Information: This encompasses the clinical details of a patient’s health condition and medical history. It includes past diagnoses, treatment records, and other medical reports. This category is more compatible with current legislation and consolidates what we previously classified as ’sensitive information’ and ’historical information’. The important distinction here is that this information is sensitive by its very nature and is treated as such under GDPR and similar laws.
4.5. Role Ontology
4.6. Health Information Ontology
4.7. Privacy Policy Ontology
4.8. Disclosing Emergency Health Information for Patients in Car Accident Case Study
- Patient Location: Somewhere, a suburb of Melbourne.
- Primary Stakeholders: Patient, GP, Paramedics, Emergency Room Nurse.
- Secondary Stakeholders: Family members, Insurance provider.
- Patient Health Situation: A man with Type 2 diabetes living at 5 Somewhere Street in a Melbourne suburb regularly sees his GP for health monitoring and treatment. His insurance provider and primary stakeholders have access to his health records, but not his specific home address. One night, he experiences a car accident and suffers from severe chest pain, difficulty breathing, and dizziness. A witness calls 000 for emergency help and the operator dispatches paramedics after learning the accident occurred in a Melbourne suburb.
5. Evaluation of Privacy Ontology and Experiments
- ✔
- Data Collection and Preprocessing: We collected a large dataset of health-related privacy policies from various online sources, such as hospitals, clinics, health insurance providers, and health-related mobile applications. These policies were then preprocessed to remove any irrelevant information, formatting inconsistencies, and to convert them into a machine-readable format.
- ✔
- Annotation and Labeling: After preprocessing the data, we manually annotated and labeled the privacy policies based on their adherence to our privacy ontology. The annotation process involved experts in privacy and health domains, who categorized the policies into two classes: valid (policies that comply with the privacy ontology) and illegitimate (policies that do not comply with the privacy ontology).
- ✔
- Feature Extraction: We extracted relevant features from the preprocessed privacy policies, such as the presence of specific keywords or phrases, using NLP techniques. These features were critical for training the BERT model, which was then used to classify the policies into valid and illegitimate categories.
- ✔
- Training and Evaluation of the BERT Model: We used the annotated and labeled dataset to train the BERT model. During the training process, the model learns to identify patterns and relationships between the extracted features and the corresponding labels (valid or illegitimate). After training, we evaluated the model’s performance using standard evaluation metrics such as precision, recall, and F1-score [73].
- ✔
- Analyzing and Interpreting Results: We analyzed the results obtained from the BERT model to identify common patterns and trends in the classification of health-related privacy policies. This analysis provides valuable insights into the effectiveness of the privacy ontology and helps identify potential areas for improvement
5.1. Experiment Setup and Dataset Preparation
5.2. Clarifying Privacy Policy Classification
- First, it is essential to note that, while healthcare institutions in the U.S. must follow HIPAA guidelines, not all institutions worldwide must adhere to the same guidelines. Different countries have different privacy regulations, and the level of privacy protection can vary significantly across countries and even across different institutions within the same country. This variability increases the importance of having a tool that can automatically assess the validity of privacy policies across a broad range of contexts.
- Second, even within the U.S., not all healthcare entities are required to follow HIPAA regulations. HIPAA applies primarily to healthcare providers, health plans, and healthcare clearinghouses, but it does not extend to entities such as life insurers, employers, or schools. Some of these entities might have access to sensitive health-related information and might formulate their privacy policies, necessitating a mechanism to evaluate their policies’ validity.
- Third, even when healthcare entities are required to follow HIPAA guidelines, there may still be differences in how these guidelines are interpreted and implemented. Privacy policies can be complex and nuanced, and different entities might have different interpretations of what constitutes a ‘valid’ policy under HIPAA guidelines. An ML model that classifies privacy policies can serve as an additional check on these entities’ interpretations, highlighting potential areas of concern.
- Finally, while we used the example of HIPAA in our study, the principles of our privacy ontology and our ML-based privacy model are not limited to HIPAA. Our approach was designed to be adaptable to various privacy regulations, not just HIPAA. This adaptability makes our approach potentially useful in a wide range of contexts, even in situations where the applicable privacy regulations differ from HIPAA.
5.3. Development of ML-Based Privacy Model
- BERT: BERT is a powerful pre-trained language model that has achieved state-of-the-art results in various NLP tasks. Its bidirectional nature enables it to understand the context from both left and right sides of a word, resulting in improved understanding and classification accuracy.
- DistilBERT: DistilBERT is a distilled version of BERT, offering a smaller and faster alternative while maintaining most of the original model’s performance. This model is particularly useful in cases where computational resources or model size is a concern.
- ALBERT (A Lite BERT): ALBERT is another variant of BERT that reduces model size and improves training efficiency by sharing parameters across layers. Despite its reduced size, ALBERT maintains competitive performance, making it a suitable choice for our privacy model.
- RoBERTa (Robustly Optimized BERT Pretraining Approach): RoBERTa is a modified version of BERT that has been optimized for increased training efficiency and performance. It uses dynamic masking, larger batch sizes, and other training optimizations to achieve superior results in text classification tasks.
5.4. Application of Privacy Ontology in the Machine Learning Experiment
- Annotation and Labeling: The privacy ontology serves as a guidance for annotating and labeling the collected privacy policies. The experts involved in the annotation process utilize the ontology’s principles to identify the class of each policy. As such, the ontology enables a more reliable and consistent labeling process.
- Feature Extraction: Privacy ontology plays a crucial role in determining the relevant features from the privacy policies. It aids in identifying the specific keywords or phrases that signify valid or illegitimate policies, thereby helping in effective feature extraction.
- Model Training: During the model training phase, the privacy ontology plays a pivotal role in guiding the learning process of the BERT model. The model learns to identify patterns that align with the principles of our privacy ontology, which helps to classify new privacy policies accurately.
5.5. Evaluation Results
5.5.1. Technical Details
5.5.2. Dataset and Results
5.6. Summary of the Findings
6. Discussion
6.1. The Relationship between the Ontology and the ML Model
6.2. The Complementarity of Ontology and ML Model
6.3. Adoption of Privacy-Preserving Technologies for Health Information Security
6.4. Section Summary
7. Conclusions and Future Research
7.1. Limitation
7.2. Future Research Directions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Wang, H.; Song, Y. Secure cloud-based ehr system using attribute- based cryptosystem and blockchain. J. Med. Syst. 2018, 42, 152. [Google Scholar] [CrossRef]
- Dagher, G.G.; Mohler, J.; Milojkovic, M.; Marella, P.B. Ancile: Privacy-preserving framework for access control and interoperability of electronic health records using blockchain technology. Sustain. Cities Soc. 2018, 39, 283–297. [Google Scholar] [CrossRef]
- Bani Issa, W.; Al Akour, I.; Ibrahim, A.; Almarzouqi, A.; Abbas, S.; Hisham, F.; Griffiths, J. Privacy, confidentiality, security and patient safety concerns about electronic health records. Int. Nurs. Rev. 2020, 67, 218–230. [Google Scholar] [CrossRef]
- Keshta, I.; Odeh, A. Security and privacy of electronic health records: Concerns and challenges. Egypt. Inform. J. 2021, 22, 177–183. [Google Scholar] [CrossRef]
- Ozair, F.F.; Jamshed, N.; Sharma, A.; Aggarwal, P. Ethical issues in electronic health records: A general overview. Perspect. Clin. Res. 2015, 6, 73. [Google Scholar] [PubMed]
- Zaghloul, E.; Li, T.; Ren, J. Security and privacy of electronic health records: Decentralized and hierarchical data sharing using smart contracts. In Proceedings of the 2019 International Conference on Computing, Networking and Communications (ICNC), Honolulu, HI, USA, 18–21 February 2019; pp. 375–379. [Google Scholar] [CrossRef]
- Akarca, D.; Xiu, P.; Ebbitt, D.; Mustafa, B.; Al-Ramadhani, H.; Albey-Atti, A. Blockchain secured electronic health records: Patient rights, privacy and cybersecurity. In Proceedings of the 2019 10th International Conference on Dependable Systems, Services and Technologies (DESSERT), Leeds, UK, 5–7 June 2019; pp. 108–111. [Google Scholar] [CrossRef]
- Omar, A.H.A. The Effect of Electronic Health Records on Undergraduate and Postgraduate Medical Education: A Scoping Review; University of Toronto: Toronto, ON, Canada, 2019. [Google Scholar]
- Rezaeibagha, F.; Mu, Y. Distributed clinical data sharing via dynamic access-control policy transformation. Int. J. Med. Inform. 2016, 89, 25–31. [Google Scholar] [CrossRef]
- Farhadi, M.; Haddad, H.; Shahriar, H. Static analysis of hippa security requirements in electronic health record applications. In Proceedings of the 2018 IEEE 42nd Annual Computer Software and Applications Conference (COMPSAC), Tokyo, Japan, 23–27 June 2018; Volume 2, pp. 474–479. [Google Scholar] [CrossRef]
- Vimalachandran, P.; Zhang, Y.; Cao, J.; Sun, L.; Yong, J. Preserving data privacy and security in australian my health record system: A quality health care implication. In Proceedings of the International Conference on Web Information Systems Engineering, Dubai, United Arab Emirates, 12–15 November 2018; pp. 111–120. [Google Scholar] [CrossRef]
- Budd, J.; Miller, B.S.; Manning, E.M.; Lampos, V.; Zhuang, M.; Edelstein, M.; Rees, G.; Emery, V.C.; Stevens, M.M.; Keegan, N.; et al. Digital technologies in the public-health response to COVID-19. Nat. Med. 2020, 26, 1183–1192. [Google Scholar] [CrossRef] [PubMed]
- Mooney, S.J.; Pejaver, V. Big data in public health: Terminology, machine learning, and privacy. Annu. Rev. Public Health 2018, 39, 95–112. [Google Scholar] [CrossRef] [PubMed]
- Ahmed, Z. Practicing precision medicine with intelligently integrative clinical and multi-omics Data Analysis. Hum. Genom. 2020, 14, 35. [Google Scholar] [CrossRef]
- Kumaar, M.; Samiayya, D.; Vincent, P.M.; Srinivasan, K.; Chang, C.Y.; Ganesh, H. A hybrid framework for intrusion detection in healthcare systems using Deep Learning. Front. Public Health 2021, 9, 824898. [Google Scholar] [CrossRef]
- Alagar, V.; Alsaig, A.; Ormandjiva, O.; Wan, K. Context-based security and privacy for healthcare IoT. In Proceedings of the 2018 IEEE International Conference on Smart Internet of Things (SmartIoT), Xi’an, China, 17–19 August 2018; pp. 122–128. [Google Scholar] [CrossRef]
- Demuro, P.R.; Petersen, C. Managing privacy and data sharing through the use of health care information fiduciaries. In Context Sensitive Health Informatics: Sustainability in Dynamic Ecosystems; IOS Press: Amsterdam, The Netherlands, 2019; pp. 157–162. [Google Scholar] [CrossRef]
- Kisekka, V.; Giboney, J.S. The effectiveness of health care information technologies: Evaluation of trust, security beliefs, and privacy as determinants of health care outcomes. J. Med. Internet Res. 2018, 20, e9014. [Google Scholar] [CrossRef]
- Rieke, N.; Hancox, J.; Li, W.; Milletari, F.; Roth, H.R.; Albarqouni, S.; Bakas, S.; Galtier, M.N.; Landman, B.A.; Maier-Hein, K.; et al. The future of digital health with federated learning. NPJ Digit. Med. 2020, 3, 119. [Google Scholar] [CrossRef] [PubMed]
- Kruse, C.S.; Smith, B.; Vanderlinden, H.; Nealand, A. Security techniques for the electronic health records. J. Med. Syst. 2017, 41, 127. [Google Scholar] [CrossRef]
- Otlowski, M.F.A. Disclosing genetic information to at-risk relatives: New Australian privacy principles, but uniformity still elusive. Med. J. Aust. 2015, 202, 335–337. [Google Scholar] [CrossRef] [PubMed]
- Ahmed, Z.; Mohamed, K.; Zeeshan, S.; Dong, X.Q. Artificial Intelligence with multi-functional machine learning platform development for better healthcare and Precision Medicine. Database 2020, 2020, baaa010. [Google Scholar] [CrossRef]
- Chen, M.; Decary, M. Artificial Intelligence in healthcare: An essential guide for health leaders. Healthc. Manag. Forum 2019, 33, 10–18. [Google Scholar] [CrossRef] [PubMed]
- Koczkodaj, W.W.; Mazurek, M.; Strzałka, D.; Wolny-Dominiak, A.; Woodbury-Smith, M. Electronic health record breaches as social indicators. Soc. Indic. Res. 2019, 141, 861–871. [Google Scholar] [CrossRef]
- Abramson, W.; Hall, A.J.; Papadopoulos, P.; Pitropakis, N.; Buchanan, W.J. A distributed trust framework for privacy-preserving machine learning. In Trust, Privacy and Security in Digital Business; Springer: Cham, Switzerland, 2020; pp. 205–220. [Google Scholar] [CrossRef]
- Islam, T.U.; Ghasemi, R.; Mohammed, N. Privacy-preserving federated learning model for healthcare data. In Proceedings of the 2022 IEEE 12th Annual Computing and Communication Workshop and Conference (CCWC), Las Vegas, NV, USA, 26–29 January 2022. [Google Scholar] [CrossRef]
- Baker, A. Crossing the quality chasm: A new health system for the 21st century. BMJ Clin. Res. 2001, 323, 1192. [Google Scholar] [CrossRef]
- Olive, M.; Rahmouni, H.B.; Solomonides, T.; Breton, V.; Legré, Y.; Blanquer, I.; Hernández, V.; Andoulsi, I.; Herveg, J.A.M.; Wilson, P. Share roadmap 1: Towards a debate. Stud. Health Technol. Inform. 2007, 126, 164–173. [Google Scholar]
- Li, M.; Yu, S.; Ren, K.; Lou, W. Securing personal health records in cloud computing: Patient-centric and fine-grained data access control in multi-owner settings. In Proceedings of the International Conference on Security and Privacy in Communication Systems, Singapore, 7–9 September 2010; pp. 89–106. [Google Scholar] [CrossRef]
- Caine, K.; Hanania, R. Patients want granular privacy control over health information in electronic medical records. J. Am. Med. Inform. Assoc. 2013, 20, 7–15. [Google Scholar] [CrossRef]
- Abouelmehdi, K.; Beni-Hessane, A.; Khaloufi, H. Big healthcare data: Preserving security and privacy. J. Big Data 2018, 5, 1. [Google Scholar] [CrossRef]
- Sun, W.; Cai, Z.; Li, Y.; Liu, F.; Fang, S.; Wang, G. Security and privacy in the medical internet of things: A review. Secur. Commun. Netw. 2018, 2018, 5978636. [Google Scholar] [CrossRef]
- Johnson, C.M.; Grandison, T. Compliance with data protection laws using hippocratic database active enforcement and auditing. IBM Syst. J. 2007, 46, 255–264. [Google Scholar] [CrossRef]
- Fernández-Alemán, J.L.; Señor, I.C.; Lozoya, P.Á.O.; Toval, A. Security and privacy in electronic health records: A systematic literature review. J. Biomed. Inform. 2013, 46, 541–562. [Google Scholar] [CrossRef]
- Eze, E.; Gleasure, R.; Heavin, C. Mobile health solutions in developing countries: A stakeholder perspective. Health Syst. 2020, 9, 179–201. [Google Scholar] [CrossRef]
- Peute, L.W.; Wildenbos, G.A.; Engelsma, T.; Lesselroth, B.J.; Lichtner, V.; Monkman, H.; Neal, D.; Van Velsen, L.; Jaspers, M.W.; Marcilly, R. Overcoming Challenges to Inclusive User-based Testing of Health Information Technology with Vulnerable Older Adults: Recommendations from a Human Factors Engineering Expert Inquiry. Yearb. Med. Inform. 2022, 31, 74–81. [Google Scholar] [CrossRef]
- Mamun, Q. A conceptual framework of personally controlled electronic health record (pcehr) system to enhance security and privacy. In Proceedings of the International Conference on Applications and Techniques in Cyber Security and Intelligence, Barcelona, Spain, 12–16 November 2017; pp. 304–314. [Google Scholar] [CrossRef]
- Samet, S.; Ishraque, M.T.; Sharma, A. Privacy-preserving personal health record (p3hr) a secure android application. In Proceedings of the 7th International Conference on Software and Information Engineering, Cairo, Egypt, 2–4 May 2018. [Google Scholar] [CrossRef]
- Wachter, S. The GDPR and the Internet of Things: A three-step transparency model. Law Innov. Technol. 2018, 10, 266–294. [Google Scholar] [CrossRef]
- Cavoukian, A. Privacy by design: The definitive workshop. A foreword by Ann Cavoukian, Ph. D. Identity Inf. Soc. 2010, 3, 247–251. [Google Scholar] [CrossRef]
- Zhang, A.; Lin, X. Towards secure and privacy-preserving data shar- ing in e-health systems via consortium blockchain. J. Med. Syst. 2018, 42, 140. [Google Scholar] [CrossRef]
- Kuo, T.T.; Kim, H.E.; Ohno-Machado, L. Blockchain distributed ledger technologies for biomedical and health care applications. J. Am. Med. Inform. Assoc. 2017, 24, 1211–1220. [Google Scholar] [CrossRef]
- Esposito, C.; Santis, A.; Tortora, G.; Chang, H.; Choo, K.K.R. Blockchain: A panacea for healthcare cloud-based data security and privacy? IEEE Cloud Comput. 2018, 5, 31–37. [Google Scholar] [CrossRef]
- Wang, J.; Li, M.; He, Y.; Li, H.; Xiao, K.; Wang, C. A blockchain based privacy-preserving incentive mechanism in crowdsensing applications. IEEE Access 2018, 6, 17545–17556. [Google Scholar] [CrossRef]
- Fan, K.; Wang, S.; Ren, Y.; Li, H.; Yang, Y. Medblock: Efficient and secure medical data sharing via blockchain. J. Med. Syst. 2018, 42, 136. [Google Scholar] [CrossRef] [PubMed]
- Griggs, K.N.; Ossipova, O.; Kohlios, C.P.; Baccarini, A.N.; Howson, E.A.; Hayajneh, T. Healthcare blockchain system using smart contracts for secure automated remote patient monitoring. J. Med. Syst. 2018, 42, 130. [Google Scholar] [CrossRef] [PubMed]
- Kayes, A.; Rahayu, W.; Dillon, T.; Chang, E.; Han, J. Context-aware access control with imprecise context characterization for cloud-based data resources. Future Gener. Comput. Syst. 2019, 93, 237–255. [Google Scholar] [CrossRef]
- Kayes, A.; Han, J.; Rahayu, W.; Dillon, T.; Islam, M.S.; Colman, A. A policy model and framework for context-aware access control to information resources. Comput. J. 2019, 62, 670–705. [Google Scholar] [CrossRef]
- Kayes, A.; Rahayu, W.; Watters, P.; Alazab, M.; Dillon, T.; Chang, E. Achieving security scalability and flexibility using fog-based context-aware access control. Future Gener. Comput. Syst. 2020, 107, 307–323. [Google Scholar] [CrossRef]
- Kayes, A.; Rahayu, W.; Dillon, T. An ontology-based approach to dynamic contextual role for pervasive access control. In Proceedings of the 2018 IEEE 32nd International Conference on Advanced Information Networking and Applications (AINA), Krakow, Poland, 16–18 May 2018; pp. 601–608. [Google Scholar] [CrossRef]
- Paul, J.; Annamalai, M.S.M.S.; Ming, W.; Al Badawi, A.; Veeravalli, B.; Aung, K.M.M. Privacy-preserving collective learning with homomorphic encryption. IEEE Access 2021, 9, 132084–132096. [Google Scholar] [CrossRef]
- Ikuomola, A.J.; Arowolo, O.O. Securing patient privacy in e-health cloud using homomorphic encryption and access control. Int. J. Comput. Netw. Commun. Secur. 2014, 2, 15–21. [Google Scholar]
- Vengadapurvaja, A.; Nisha, G.; Aarthy, R.; Sasikaladevi, N. An efficient homomorphic medical image encryption algorithm for cloud storage security. Procedia Comput. Sci. 2017, 115, 643–650. [Google Scholar] [CrossRef]
- Alzubi, J.A.; Alzubi, O.A.; Beseiso, M.; Budati, A.K.; Shankar, K. Optimal multiple key-based homomorphic encryption with deep neural networks to secure medical data transmission and diagnosis. Expert Syst. 2022, 39, e12879. [Google Scholar] [CrossRef]
- Subramaniyaswamy, V.; Jagadeeswari, V.; Indragandhi, V.; Jhaveri, R.H.; Vijayakumar, V.; Kotecha, K.; Ravi, L. Somewhat homomorphic encryption: Ring learning with error algorithm for faster encryption of iot sensor signal-based edge devices. Secur. Commun. Netw. 2022, 2022, 2793998. [Google Scholar] [CrossRef]
- Vamsi, D.; Reddy, P. Electronic health record security in cloud: Medical data protection using homomorphic encryption schemes. In Research Anthology on Securing Medical Systems and Records; IGI Global: Hershey, PA, USA, 2022; pp. 853–877. [Google Scholar]
- Spencer, A.; Patel, S. Applying the data protection act 2018 and general data protection regulation principles in healthcare settings. Nurs. Manag. 2019, 26, 34–40. [Google Scholar] [CrossRef] [PubMed]
- Mills, J.L.; Harclerode, K. Privacy, mass intrusion, and the modern data breach. Fla. Law Rev. 2017, 69, 771. [Google Scholar]
- Alghrani, A.; Brazier, M.; Farrell, A.M.; Griffiths, D.; Allen, N. Healthcare scandals in the NHS: Crime and punishment. J. Med. Ethics 2011, 37, 230–232. [Google Scholar] [CrossRef]
- Schaar, P. Privacy by design. Identity Inf. Soc. 2010, 3, 267–274. [Google Scholar] [CrossRef]
- Malamed, S.F. Sedation-e-Book: A Guide to Patient Management; Elsevier Health Sciences: Amsterdam, The Netherlands, 2017. [Google Scholar]
- Sreejith, R.; Senthil, S. Dynamic Data Infrastructure Security for interoperable e-healthcare systems: A semantic feature-driven NoSQL intrusion attack detection model. BioMed Res. Int. 2022, 2022, 4080199. [Google Scholar] [CrossRef]
- Deebak, B.D.; Memon, F.H.; Cheng, X.; Dev, K.; Hu, J.; Khowaja, S.A.; Qureshi, N.M.; Choi, K.H. Seamless privacy-preservation and Authentication Framework for IOT-enabled Smart eHealth Systems. Sustain. Cities Soc. 2022, 80, 103661. [Google Scholar] [CrossRef]
- Sharma, A.; Kumar, S. Machine learning and ontology-based novel semantic document indexing for information retrieval. Comput. Ind. Eng. 2023, 176, 108940. [Google Scholar] [CrossRef]
- Fries, J.A.; Steinberg, E.; Khattar, S.; Fleming, S.L.; Posada, J.; Callahan, A.; Shah, N.H. Ontology-driven weak supervision for clinical entity classification in Electronic Health Records. Nat. Commun. 2021, 12, 2017. [Google Scholar] [CrossRef]
- Sahoo, S.S.; Kobow, K.; Zhang, J.; Buchhalter, J.; Dayyani, M.; Upadhyaya, D.P.; Prantzalos, K.; Bhattacharjee, M.; Blumcke, I.; Wiebe, S.; et al. Ontology-based feature engineering in machine learning workflows for Heterogeneous Epilepsy Patient Records. Sci. Rep. 2022, 12, 19430. [Google Scholar] [CrossRef] [PubMed]
- Zhu, N.; Chen, B.; Wang, S.; Teng, D.; He, J. Ontology-based approach for the measurement of privacy disclosure. Inf. Syst. Front. 2021, 24, 1689–1707. [Google Scholar] [CrossRef]
- Yehia, E.; Boshnak, H.; Abdelgaber, S.; Abdo, A.; Elzanfaly, D.S. Ontology-based clinical information extraction from physician’s free-text notes. J. Biomed. Inform. 2019, 98, 103276. [Google Scholar] [CrossRef] [PubMed]
- Bosco, A.D.; Vieira, R.; Zanotto, B.; Etges, A.P.D.S. Ontology based classification of electronic health records to support value-based health care. In Proceedings of the Brazilian Conference on Intelligent Systems, Virtual, 29 November–3 December 2021; pp. 359–371. [Google Scholar] [CrossRef]
- Kayes, A.S.M.; Han, J.; Colman, A. An ontology-based approach to context-aware access control for software services. In Proceedings of the International Conference on Web Information Systems Engineering, Nanjing, China, 13–15 October 2013; pp. 410–420. [Google Scholar] [CrossRef]
- McGuinness, D.L.; Van Harmelen, F. OWL web ontology language overview. W3C Recomm. 2004, 10, 2004. [Google Scholar]
- Wang, A.; Cho, K. BERT has a mouth, and it must speak: BERT as a Markov random field language model. arXiv 2019, arXiv:1902.04094. [Google Scholar] [CrossRef]
- Bisong, E. Google colaboratory. In Building Machine Learning and Deep Learning Models on Google Cloud Platform: A Comprehensive Guide for Beginners; Springer: Berlin/Heidelberg, Germany, 2019; pp. 59–64. [Google Scholar] [CrossRef]
- Schweitzer, E.J. Reconciliation of the cloud computing model with US federal electronic health record regulations. J. Am. Med. Inform. Assoc. 2012, 19, 161–165. [Google Scholar] [CrossRef]
- Adel, E.; El-Sappagh, S.; Barakat, S.; Hu, J.W.; Elmogy, M. An extended semantic interoperability model for distributed electronic health record based on fuzzy ontology semantics. Electronics 2021, 10, 1733. [Google Scholar] [CrossRef]
- Afzal, Z.; Schuemie, M.J.; van Blijderveen, J.C.; Sen, E.F.; Sturkenboom, M.C.; Kors, J.A. Improving sensitivity of machine learning methods for automated case identification from free-text electronic medical records. BMC Med. Inform. Decis. Mak. 2013, 13, 30. [Google Scholar] [CrossRef]
- Gu, T.; Wang, X.H.; Pung, H.K.; Zhang, D.Q. An ontology-based context model in intelligent environments. arXiv 2020, arXiv:2003.05055. [Google Scholar] [CrossRef]
- Puri, C.A.; Gomadam, K.; Jain, P.; Yeh, P.Z.; Verma, K. Multiple Ontologies in Healthcare Information Technology: Motivations and Recommendation for Ontology Mapping and Alignment. In Proceedings of the ICBO, Buffalo, NY, USA, 26–30 July 2011. [Google Scholar]
- Quamar, A.; Özcan, F.; Miller, D.; Moore, R.J.; Niehus, R.; Kreulen, J. Conversational BI: An ontology-driven conversation system for business intelligence applications. Proc. VLDB Endow. 2020, 13, 3369–3381. [Google Scholar] [CrossRef]
- Tsymbal, A.; Zillner, S.; Huber, M. Ontology–supported machine learning and decision support in biomedicine. In Proceedings of the Data Integration in the Life Sciences: 4th International Workshop, DILS 2007, Philadelphia, PA, USA, 27–29 June 2007; pp. 156–171. [Google Scholar] [CrossRef]
- Zhang, L.; Qi, F.; Wang, Z.; Wang, E.; Liu, Z. Integrating Semantic Knowledge to Tackle Zero-shot Text Classification. arXiv 2019, arXiv:1911.04841. [Google Scholar] [CrossRef]
- Hitzler, P.; Krisnadhi, A.A.; Janowicz, K. Ontology Engineering with Ontology Design Patterns: Foundations and Applications; IOS Press: Amsterdam, The Netherlands, 2016. [Google Scholar]
- Sharma, S.; Alebouyeh, A.R.; Perera, S.; Barreto, M.D.; Udgata, S.K. The role of ontologies for sustainable, semantically interoperable and trustworthy EHR solutions. Healthc. Technol. Lett. 2020, 7, 14–22. [Google Scholar]
- Stevens, A.; Dehghan, A. Using machine learning to identify disease-relevant genes. Curr. Opin. Genet. Dev. 2018, 50, 48–53. [Google Scholar]
- Sánchez, D.; Batet, M. C-sanitized: A privacy model for document redaction and sanitization. J. Assoc. Inf. Sci. Technol. 2016, 67, 148–163. [Google Scholar] [CrossRef]
- Kanaan, H.; Mahmood, K.; Sathyan, V. An ontological model for privacy in emerging decentralized healthcare systems. In Proceedings of the 2017 IEEE 13th International Symposium on Autonomous Decentralized System (ISADS), Bangkok, Thailand, 22–24 March 2017; IEEE: Piscataway, NJ, USA; pp. 107–113. [Google Scholar] [CrossRef]


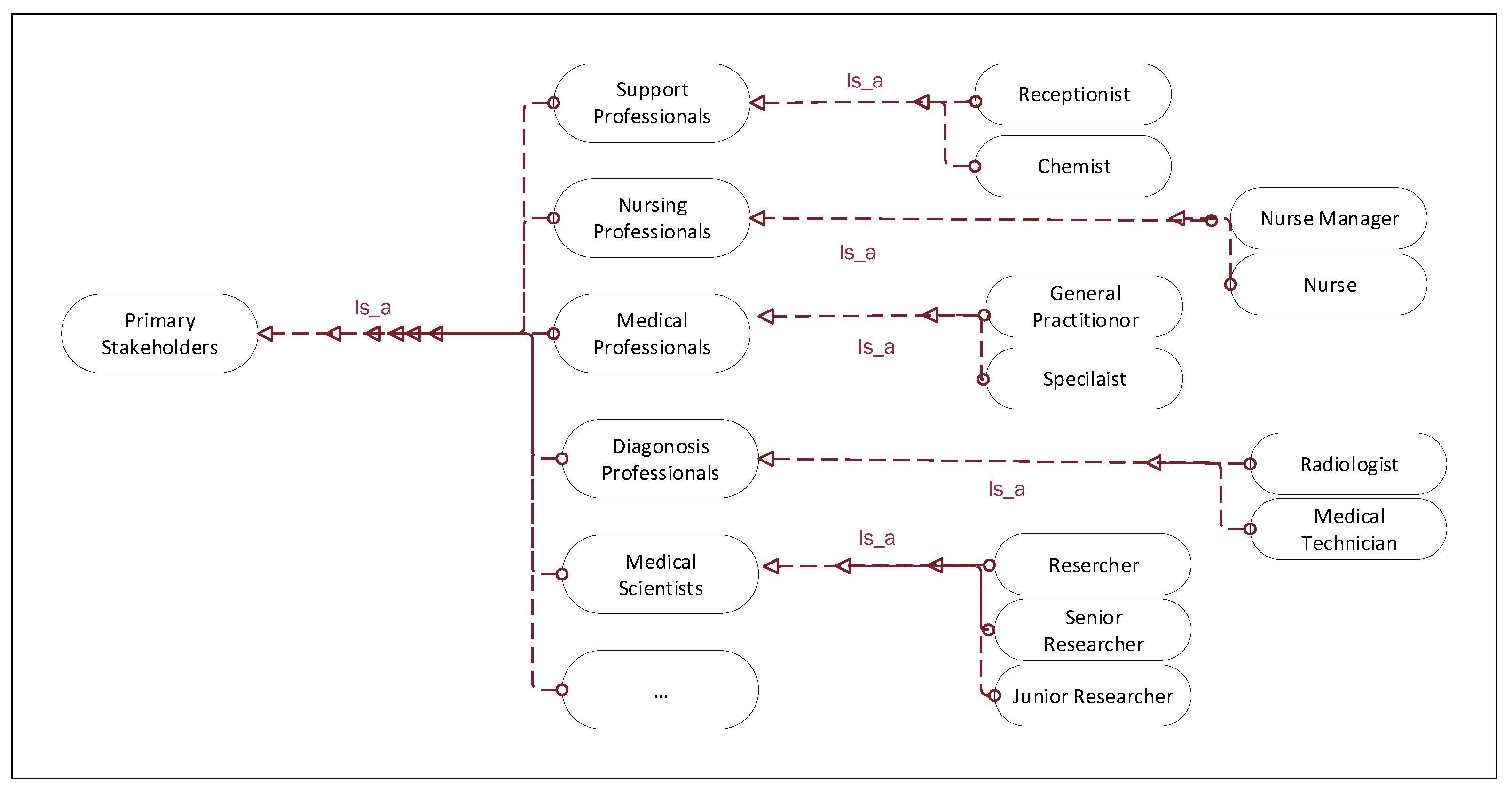
| Stakeholders’ Category | Stakeholders’ Example | Role-Based (Senior/Junior) | Privacy Roles |
|---|---|---|---|
| Support Professionals | Receptionist, Pharmacist | Junior | Policy 1: Support professionals can only deal with personal health information |
| Nursing Professionals | Nurse Manager, Nurse | Junior | Policy 2: Nursing professionals can deal with both personal and private health information |
| Medical Practitioners | General Practitioner, Specialist | Senior | Policy 3: Medical practitioners can deal with personal, private, sensitive, and historical health information |
| Diagnosis Professionals | Radiologist, Medical Technician | Senior | Policy 4: Diagnosis professionals can deal with personal and historical health information |
| Medical Scientists | Researcher, Junior Researcher | Junior | Policy 5: Medical scientists can deal all types of health information with the approval of relevant stakeholders |
| Basic Modeling Criteria | Privacy Ontology Elements |
|---|---|
| Classes | All primary stakeholders are represented as senior roles. |
| Sub classes | All secondary stakeholders are represented as junior roles. |
| Object-type Properties | The relationships between classes to classes are represented as object type properties. |
| Datatype Properties | The relationships between classes to their features are represented as datatype properties. |
| Personal Health Information | Privacy Policy | Emergency Situation |
|---|---|---|
| A primary address, such as “suburb is a suburban area in Melbourne”, will only be released to all stakeholders. However, the patient’s actual address, which is “5 Somewhere Street, a suburban area in Melbourne”, is only released in the event of any emergency. | All primary stakeholders have access to patients’ personal health information. However, they do not have access to private health information. | In an emergency, some primary stakeholders can have access to patients’ private health information. For example, in cases where the patient considered to be in a very critical condition and needs to be admitted to hospital, medical practitioners have access to patients’ exact home address for an emergency treatment/situation. |
| Policy Type | Policy Statement |
|---|---|
| 0] | … Alexa Internet Privacy Policy, based on the last updated version on 7 April 2011. What Personal Information About Users Does Alexa Gather? Information You Give Us—We receive and store any information you enter on our Web site or give us in any other way. Automatic Information We Collect From the Toolbar Service—When you use the Toolbar Service, we collect information about the websites you visit and the advertisements that you see on those websites, the searches you perform using search engines… |
| BERT Techniques | Accuracy | Precision | F1 Score |
|---|---|---|---|
| BERT | 0.92 | 0.86 | 0.90 |
| Distil BERT | 0.94 | 0.94 | 0.94 |
| Albert Tokenizer | 0.76 | 0.87 | 0.76 |
| Roberta Tokenizer | 0.90 | 0.82 | 0.92 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Nowrozy, R.; Ahmed, K.; Wang, H.; Mcintosh, T. Towards a Universal Privacy Model for Electronic Health Record Systems: An Ontology and Machine Learning Approach. Informatics 2023, 10, 60. https://doi.org/10.3390/informatics10030060
Nowrozy R, Ahmed K, Wang H, Mcintosh T. Towards a Universal Privacy Model for Electronic Health Record Systems: An Ontology and Machine Learning Approach. Informatics. 2023; 10(3):60. https://doi.org/10.3390/informatics10030060
Chicago/Turabian StyleNowrozy, Raza, Khandakar Ahmed, Hua Wang, and Timothy Mcintosh. 2023. "Towards a Universal Privacy Model for Electronic Health Record Systems: An Ontology and Machine Learning Approach" Informatics 10, no. 3: 60. https://doi.org/10.3390/informatics10030060
APA StyleNowrozy, R., Ahmed, K., Wang, H., & Mcintosh, T. (2023). Towards a Universal Privacy Model for Electronic Health Record Systems: An Ontology and Machine Learning Approach. Informatics, 10(3), 60. https://doi.org/10.3390/informatics10030060








