Abstract
This paper investigates the valuation of vulnerable exchange options with two underlying assets that follow a two-factor volatility model. We employ a reduced-form model incorporating a Poisson process with stochastic intensity. The proposed reduced-form model depends on a stochastic intensity process that is guaranteed to remain positive and includes both systemic and idiosyncratic risks. Using measure change techniques and characteristic functions, we obtain an explicit pricing formula for vulnerable exchange options within the proposed framework. We also provide numerical examples demonstrating the sensitivity of option prices to significant parameters.
MSC:
91G20; 91G40
1. Introduction
The valuation of options that consider counterparty credit risk, termed ‘vulnerable options’, has received significant attention from numerous researchers. Vulnerable options are financial derivatives that incorporate the credit risk associated with the counterparty’s potential default. The adoption of a credit risk model is required to accurately evaluate vulnerable options. In general, two main approaches have been used for modeling credit risk: the structural model and the reduced-form model. The structural model, pioneered by Merton [1] and Black and Cox [2], links credit events to the firm’s value process. A credit event occurs when the firm’s value falls below its liabilities at maturity. In contrast, the reduced-form model, initially developed by Jarrow and Turnbull [3] and Jarrow and Yu [4], separates credit events from the firm’s value. Instead, a credit event is initiated by the first jump of a Poisson process with a predetermined intensity, independent of the firm’s value dynamics. This paper is in line with the development of the reduced-form model.
We employ a reduced-form model to explore the pricing of vulnerable options. Recent studies have focused on vulnerable options within reduced-form model frameworks. Fard [5] developed a pricing formula for vulnerable options under a generalized jump model, utilizing a reduced-form approach to describe counterparty credit risk. Pasricha and Goel [6] investigated a vulnerable power exchange option with two underlying assets within a reduced-form framework. They employed a doubly stochastic Poisson process to model counterparty credit events and incorporated correlations among the three assets in both continuous and jump components. Wang [7] considered basket warrants with default risk under a stochastic volatility model. In addition, Wang [8,9] studied the valuation of European options, Asian options, and fader options with default risk and stochastic volatility in a reduced-form model. More recently, under reduced-form models, Pan et al. [10] provided the pricing formula of European options with default risk in a market where the underlying stocks are not perfectly liquid, and Wang et al. [11] investigated the pricing problem of vulnerable basket options with stochastic liquidity risk. This paper also considers the vulnerable option under a stochastic volatility model. Specifically, vulnerable exchange options, which have two underlying assets, with stochastic volatility are investigated through a reduced-form model.
The aim of this paper is to provide an explicit solution for vulnerable exchange option pricing. In fact, there have been several studies on vulnerable exchange options. Pasricha and Goel [6] developed a vulnerable exchange option pricing model based on correlated dynamics in both the continuous and jump parts. In [12], vulnerable exchange options with early default risk were studied employing dimension reduction, Mellin transform, and the method of images. In addition, the valuation of vulnerable exchange options with the stochastic volatility was investigated in the structural model [13,14]. Unlike prior studies, we apply a reduced-form model in continuous time and two-factor stochastic volatility to demonstrate the credit risk model and the underlying assets, respectively. Furthermore, by dividing the risk into idiosyncratic and systematic components, we complete the reduced-form model. In the proposed model, we derive an explicit pricing formula for vulnerable exchange options.
The remainder of this paper is organized as follows. In Section 2, we introduce the model dynamics, and the pricing problem for vulnerable exchange options is formulated. In Section 3, we derive the explicit solution for option pricing in terms of a characteristic function using the measure change technique. In Section 4, we provide numerical examples to show various characteristics of options with respect to significant parameters. Finally, Section 5 offers concluding remarks.
2. Model
Let be a filtered probability space satisfying the usual conditions, where Q is a risk-neutral measure. We assume that the underlying assets and , which are associated, respectively, with a two-factor stochastic volatility model as described in Christoffersen et al. [15], are governed by the following processes:
where r is the interest rate, , which capture the sensitivities of underlying assets to systematic risk, are constants, are standard Brownian motions, and
where are constants, and are the correlated standard Brownian motions satisfying and , and other Brownian motions are pairwise independent.
In what follows, we model the credit risk of an option issuer using a reduced form model. Following Wang [8], the intensity process is divided into two parts. The first part addresses the systematic risk, while the second part addresses the idiosyncratic risk of option issuers. In more detail, in the work of Wang [8], we can find that means the variance of the market portfolio corresponding to systematic risk, means the variance corresponding to idiosyncratic risk of the underlying asset , and means the variance corresponding to idiosyncratic risk of the underlying asset , respectively. Therefore, we assume that the intensity process is driven by the following process:
where is is a nonnegative constant that captures the correlation between the process and the process . In addition, , which describes the idiosyncratic risk, is given by
where are constants and is a standard Brownian motion that is independent of the other Brownian motions. Given the intensity process , the default is defined as
where and T is the maturity of an option.
In the reduced form model, we investigate a vulnerable exchange option with maturity T. Basically, the price of the option is determined by whether default occurs or not before maturity. In other words, if , there is no default before the maturity, and if , the price is determined by the recover rate w. Then, we can find that the pricing expression includes two parts. From the assumptions, the price of the vulnerable exchange option at time 0 under the risk neutral measure Q can be presented as
where w is the recovery rate satisfying , and is the expectation under the risk neutral measure Q.
3. Valuation of Vulnerable Exchange Option
In this section, we provide an analytic pricing formula of a vulnerable exchange option in the proposed framework. To derive the pricing formula of the option in (4), we need to define the joint characteristic function of under the measure Q. That is, the function is defined as
where are complex numbers. To provide the explicit solution of the function , we should introduce the following lemma. For more details, one can refer to Cox et al. [16].
Lemma 1.
For any complex numbers and , the joint characteristic function of is given by
where is defined in (3), and
Applying the result in Lemma 1, we can find the explicit solution of the function in the following Theorem.
Theorem 1.
Under the risk-neutral measure Q, the joint characteristic function defined in (5) is given by
where
Proof.
We consider the dynamics of underlying asset s and in (1). Then, and are presented as
Based on the above expression, we rewrite and as
where and are the standard Brownian motions, and are independent of other Brownian motions. These have the following forms:
respectively. Adding (8) in (5), the function is represented as
We deal with the first expectation in (9). To obtain the explicit solution, we apply the law of iterated expectation. Then, we have that
Other terms are also calculated similar to (10). Therefore, we obtain the following result:
By using Lemma 1 with each term in (11), the characteristic function is completed. □
By using the characteristic function and the measure change technique, we can derive a vulnerable European option under the proposed model. The pricing formula of vulnerable options in (4) is provided in the following Theorem.
Theorem 2.
The price of a vulnerable exchange option under the proposed model at time 0 is given by
where
Proof.
Recall the price of vulnerable exchange option in (4). Then, the option price C can be decomposed as follows.
where
We first consider the calculation of . To obtain the explicit solution of , we employ a new probability measure , which is equivalent to Q, defined by the Radon–Nikodým derivative
Then, the characteristic function of under the measure is given by
By applying standard probability theory described in [17], we derive from the characteristic function .
Following an analogous approach, we can derive . For in (13), we adopt a new probability measure defined by
Under the measure , the characteristic function of has the form of
Using the characteristic function , we obtain
In a similar manner, is calculated and takes a form similar to . This completes the proof of Theorem 2. □
In Theorem 2, we present the explicit solution of a vulnerable exchange option price under a two-factor stochastic volatility model. In the next section, through numerical experiments, we show how default risk impacts option prices.
4. Numerical Examples
This section provides several numerical examples to illustrate the effects of the option issuer’s credit risk on option prices, and to verify the accuracy of proposed formula. The numerical examples present the prices of exchange options, including the prices without credit risk for sensitivity analysis. Table 1 lists a base set of parameters for the base case experiments, based on Pasricha and Goel [6] and Wang [8].

Table 1.
The baseline parameter values.
Table 2 demonstrates computational examples for exchange options under the proposed model. Specifically, we compare option prices using the Monte Carlo simulation method and the derived pricing formula. Table 2 provides ‘Price’ values generated from our formula in Theorem 2 and ‘MC’ values generated from Monte Carlo simulations with 1000 time steps and 100,000 trials. In Table 2, ‘R-Err’ values represent the relative error between values obtained using our formula and values obtained using the Monte Carlo simulations, defined by

Table 2.
Comparison of prices using Theorem 2 and Monte Carlo prices for different T and w.
The results in Table 2 demonstrate that our analytic approach is accurate. Concretely, ‘R-Err’ values are less than 0.31% in all experiments.
Figure 1 presents the prices of vulnerable exchange options for three different recovery rate cases, including a no-default case, under the proposed stochastic volatility model. From Figure 1, we observe that option prices increase as the maturity T increases. This shows the fact that option prices are an increasing function of maturity. Additionally, we observe that option prices are higher when the recovery rate w has a high value because the expected value at maturity T increases as the recovery rate increases. Intuitively, it makes sense that the prices of options with credit risk decrease as w decreases.
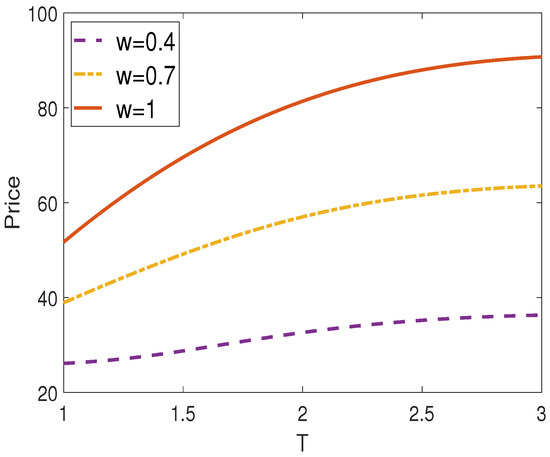
Figure 1.
Vulnerable exchange option prices against maturity time T for different values w.
Figure 2 and Figure 3 illustrate the effects of the initial values of the two underlying assets. The results in Figure 2 indicate that option prices incorporating the issuer’s credit risk increase monotonically with the initial value of the first underlying asset . That is, option prices are proportional to . On the other hand, option prices are inversely proportional to the initial value of the second underlying asset . In fact, the value of serves a similar role to the strike price of a standard European call option. Therefore, option prices decrease as increases.
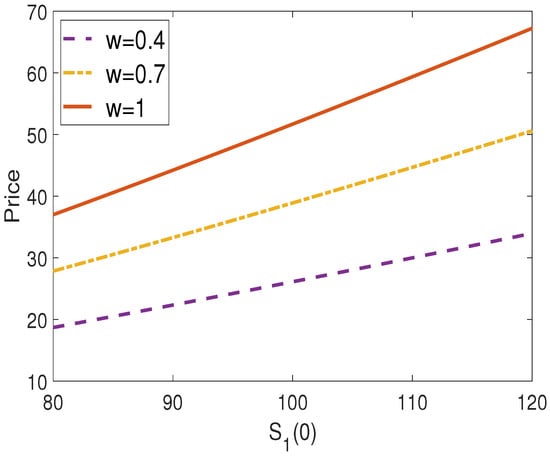
Figure 2.
Vulnerable exchange option prices against initial price of underlying asset for different values w.
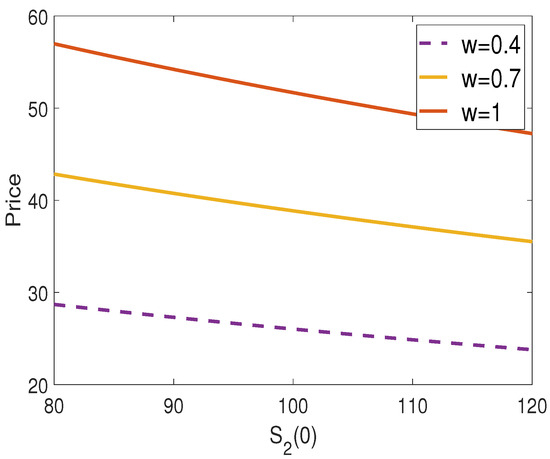
Figure 3.
Vulnerable exchange option prices against initial price of underlying asset for different values w.
From Figure 4, we observe differences in option prices when the first underlying asset has varying proportions of systematic risk . It can be seen that option prices increase slightly with an increase in systematic risk . Figure 5 presents the effects of different values of in the intensity process. The higher the value of the intensity process , the higher the probability of a credit event. Therefore, higher values of result in lower option prices. However, if the recovery rate is equal to one, the value of has no effect.
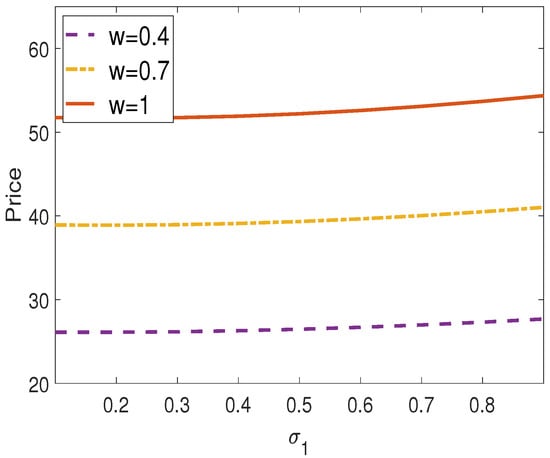
Figure 4.
Vulnerable exchange option prices against for different values w.
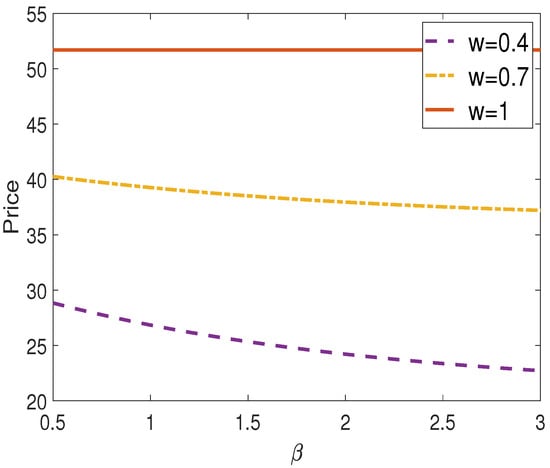
Figure 5.
Vulnerable exchange option prices against for different values w.
5. Concluding Remarks
This paper investigates the valuation of vulnerable exchange options by incorporating a reduced-form model. In the proposed model, the processes of underlying assets are governed by a two-factor stochastic volatility model, while a mean-reverting square root process is used for the stochastic intensity process to ensure that it is positive at all times. Finally, in the proposed model, we provide the explicit solution for vulnerable exchange option pricing using the measure change technique, as well as several numerical examples to demonstrate how significant parameters impact option prices and to verify how accurate the derived formula.
Author Contributions
J.J. and G.K. designed the model; J.J. and G.K. contributed to the analysis of the mathematical model; J.J. proved the propositions in the paper; J.J. and G.K. wrote the paper. All authors have read and agreed to the manuscript.
Funding
This research was supported by Seoul National University of Science and Technology.
Data Availability Statement
The original contributions presented in the study are included in the article; further inquiries can be directed to the corresponding author.
Conflicts of Interest
The authors declare no conflicts of interest.
References
- Merton, R.C. On the pricing of corporate debt: The risk structure of interest rates. J. Financ. 1974, 29, 449–470. [Google Scholar]
- Black, F.; Cox, J.C. Valuing corporate securities: Some effects of bond indenture provisions. J. Financ. 1976, 31, 351–367. [Google Scholar] [CrossRef]
- Jarrow, R.; Turnbull, S. Pricing options on financial securities subject to default risk. J. Financ. 1995, 50, 53–86. [Google Scholar] [CrossRef]
- Jarrow, R.A.; Yu, F. Counterparty risk and the pricing of defaultable securities. J. Financ. 2001, 56, 1765–1799. [Google Scholar] [CrossRef]
- Fard, F.A. Analytical pricing of vulnerable options under a generalized jump–diffusion model. Insur. Math. Econ. 2015, 60, 19–28. [Google Scholar] [CrossRef]
- Pasricha, P.; Goel, A. Pricing vulnerable power exchange options in an intensity based framework. J. Comput. Appl. Math. 2019, 355, 106–115. [Google Scholar] [CrossRef]
- Wang, X. Pricing European basket warrants with default risk under stochastic volatility models. Appl. Econ. Lett. 2022, 29, 253–260. [Google Scholar] [CrossRef]
- Wang, X. Analytical valuation of vulnerable European and Asian options in intensity-based models. J. Comput. Appl. Math. 2021, 393, 113412. [Google Scholar] [CrossRef]
- Wang, X. Pricing vulnerable fader options under stochastic volatility models. J. Ind. Manag. Optim. 2023, 19. [Google Scholar] [CrossRef]
- Pan, Y.; Tang, D.; Wang, X. Valuation of vulnerable European options with market liquidity risk. Probab. Eng. Informational Sci. 2024, 38, 65–81. [Google Scholar] [CrossRef]
- Wang, B.; Wang, X.; Zhao, M. Valuing Vulnerable Basket Options with Stochastic Liquidity Risk in Reduced-form Models. Comput. Econ. 2024, 1–17. [Google Scholar] [CrossRef]
- Kim, D.; Kim, G.; Yoon, J.H. Pricing of vulnerable exchange options with early counterparty credit risk. N. Am. J. Econ. Financ. 2022, 59, 101624. [Google Scholar] [CrossRef]
- Jeon, J.; Huh, J.; Kim, G. An analytical approach to the pricing of an exchange option with default risk under a stochastic volatility model. Adv. Contin. Discret. Model. 2023, 2023, 37. [Google Scholar] [CrossRef]
- Yue, S.; Ma, C.; Zhao, X.; Deng, C. Pricing power exchange options with default risk, stochastic volatility and stochastic interest rate. Commun.-Stat.-Theory Methods 2023, 52, 1431–1456. [Google Scholar] [CrossRef]
- Christoffersen, P.; Heston, S.; Jacobs, K. The shape and term structure of the index option smirk: Why multifactor stochastic volatility models work so well. Manag. Sci. 2009, 55, 1914–1932. [Google Scholar] [CrossRef]
- Cox, J.C.; Ingersoll, J.E., Jr.; Ross, S.A. A Theory of the Term Structure of Interest Rates. Econometrica 1985, 53, 385–407. [Google Scholar] [CrossRef]
- Shephard, N.G. From characteristic function to distribution function: A simple framework for the theory. Econom. Theory 1991, 7, 519–529. [Google Scholar] [CrossRef]
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).