Abstract
Cloud services offer doctors and data scientists access to medical data from multiple locations using different devices (laptops, desktops, tablets, smartphones, etc.). Therefore, cyber threats to medical data at rest, in transit and when used by applications need to be pinpointed and prevented preemptively through a host of proven cryptographical solutions. The presented work integrates adaptive key generation, neural-based confusion and non-XOR, namely DNA diffusion, which offers a more extensive and unique key, adaptive confusion and unpredictable diffusion algorithm. Only authenticated users can store this encrypted image in cloud storage. The proposed security framework uses logistics, tent maps and adaptive key generation modules. The adaptive key is generated using a multilayer and nonlinear neural network from every input plain image. The Hopfield neural network (HNN) is a recurrent temporal network that updates learning with every plain image. We have taken Amazon Web Services (AWS) and Simple Storage Service (S3) to store encrypted images. Using benchmark evolution metrics, the ability of image encryption is validated against brute force and statistical attacks, and encryption quality analysis is also made. Thus, it is proved that the proposed scheme is well suited for hosting cloud storage for secure images.
Keywords:
chaos key generator; adaptive key generator; DNA encoding; image ciphering; neural networks; cloud storage MSC:
94A60
1. Introduction
In recent decades, the world of computing has grown tremendously. The revolution in modern gadgets is completely rebuilding information sharing and storing in the public sector. In reflection, the security and privacy of information sharing have become a challenge [1]. Additionally, the incremental impact of data storage platforms such as cloud [1], fog [2], edge [3], etc., has led to development in the field of information technology (IT). The rapid increase in Internet of Things-centric engineering applications also demands platforms such as cloud and edge [4,5]. However, information security is a significant concern during transit, and the rest of the multimedia data are shared in the public domain. Confidentiality, integrity, authentication and nonrepudiation are security components that structure the security solutions to share and store multimedia data. The cloud paradigm has recently enabled worldwide organisations to host and run their business applications and IT services in cloud environments (public, private and hybrid). The consistent growth of the cloud paradigm makes it a cornerstone for efficient and affordable multimedia data storage for various applications. Owing to the multitenant nature of the cloud, addressing the security and privacy concerns of multimedia data is essential. Authentication is one solution to ensure the tightest security for confidential and customer data. Images are a significant segment of multimedia data. Multimedia data are captured and transmitted to geographically distributed cloud environments. One such solution is proven and potential image encryption.
Cloud computing plays a commendable role in shaping the IT infrastructure [6]. Cloud computing is the consolidated, centralised/federated, automated and shared computing model representing IT industrialisation. Due to the shared environment, anybody can access cloud services globally to host their data. The pay-per-usage model has created a string of newer possibilities and opportunities for business houses, IT service providers, governments and other establishments across the globe.
The cloud environment offers infrastructure, a platform and storage as a service. Storage is the superior service and backbone for e-commerce and online finance applications (e.g., Salesforce CRM and Netflix) [7]. However, security and privacy are unbeatable challenges for the cloud storage environment, particularly for images as multimedia data. In addition, tamper resistance and data protection are significant challenges [8]. The new shape for image encryption schemes is vital in this concern. Ciphering images is the solution to protect the images in the public cloud storage area. The art of the image encryption approach is to make the image unreadable by unauthorised users. Due to the uniqueness of the image, such as high correlation among neighbouring pixels, conventional crypto solutions cannot be advised for image ciphering [9].
Chaos theory supports image encryption to break neighbouring pixels’ correlation after encryption. Chaotic maps [10], attractors [11], etc. have specific properties such as periodicity, greater keyspace, sensitivity to initial parameters, etc. [12], which played a commendable role in the substitution and transposition process of image encryption [13]. Ponuma et al. proposed compressive sensing-based image encryption with the key matrix generated from the chaotic measurement approach [14].
2. Related Works
The confusion process using a chaotic Arnold’s cat map (ACM) has a flaw: the specific number of rotations fetches the original image again [15]. Along with ACM, the diffusion process using chaotic nature keys increases impulsiveness [16]. Belazi et al. proposed a new 1D map for a permutation-substitution network attained through chaotic linear fractional transformation (LFT) along with the interleaved diffusion process [17]. Huang et al. suggested plain image-dependent encryption through N-dimensional chaotic maps [18]. Broumandnia experimented with image ciphering using multidimensional nonlinear chaos equations to enhance the keyspace [19]. Finally, Chen et al. proposed an image ciphering technique which tolerates brute-force attacks. Nonlinear fractional Tchebyshev moments are used to achieve the fractal permutation to enrich the security level of a colour image [20].
DNA blended image encryption has become a remarkable strategy for data privacy [21]. Substitution rules of DNA coding agree that chaos offers better diffusion in image encryption, which increases the keyspace and entropy, and the correlation results are meagre [22]. Hu et al. suggested a spatiotemporal chaos system constructed using a logistic-sine system (LSS) in the coupled map lattice (CML) for diffusion and DNA-based shuffling in the encryption process and obtained good entropy [23]. Chai et al. experimented with the DNA blended chaos-based grey image encryption where 1D chaotic maps and cipher block chaining approaches are used to obtain near-zero correlation and maximum entropy [24]. Enayatifar et al. proposed DNA XORing for diffusing the image followed by confusion through three-dimensional logistic maps. Still, the diagonal correlation of the encrypted image is near zero compared to the vertical and horizontal correlation of the same. Additionally, the entropy value needs to be improved [25]. A multidimensional hyperchaotic system generates the random key for colour image encryption blended with a DNA-based diffusion process at block and bit levels [26,27]. Wenjie et al. experimented with plaintext-specific key generation for image encryption. The SHA-512 hash value is generated for every plain image as a random key for bit-level scrambling and diffusion [28]. Pavithran et al. suggested DNA-based image encryption using a hyperchaotic key generator [29]. Yousif et al. experimented with an image encryption algorithm comprising bit-level permutation and diffusion using DNA addition to improve the resistivity against known attacks in the cryptosystem [30].
Qin et al. suggested a fully homomorphic encryption (FHE) scheme for image encryption linked with cloud storage where complexity and overhead are very high, even for small images [31]. Chidambaram et al. proposed the DNA blended chaos-based image encryption to offer a secure image repository in the public cloud. Due to coupled chaos and cipher block chaining approaches, the image entropy after encryption was increased, but the keyspace was small, which may not be entertained [32].
Zhang et al. proposed an image encryption algorithm for the Internet of Multimedia Things (IoMT), a combination of Arnold transform-based scrambling followed by XOR-based diffusion using the key generated through cascade chaotic maps [33]. The neural-based works have concluded that it is well suited for all images, namely grey, colour and medical images, which are more feasible for cloud-based storage. In cloud storage, the user is not restricted from uploading these types of images. In addition, neural-based works contribute metrics equivalent to the chaos and attractors [34,35,36,37].
It is observed from the literature that the image encryption approaches [38,39,40,41,42,43,44,45,46,47,48,49,50,51,52,53] linked with cloud storage have become essential, and there are few such algorithms in the literature. Utility-specific algorithms to offer multimedia security to cloud storage demand cloud computing. This proposed algorithm can be a solution for secure image storage in the public cloud network. This security framework experimented with DNA coding blended with chaotic maps to cipher grey images before storing them in a public repository. Any authenticated user can download the decrypted image from the cloud. Later, with the valid keys, the image is decrypted to attain the original image, with confidentiality and authentication. The proposed algorithm is an enhanced approach for managing cloud repositories with utmost image security.
From the survey, offering security for sharing information in the public domain is essential. The uniqueness of the proposed encryption scheme has been enriched with adaptive key generation and chaos key generation for image encryption. As all multimedia data are unique, including their dimensions, value range, nature of the value, properties of the data, randomness and redundancy, at the same time, the key should be random, and it should not be predicted easily. With consideration, the proposed scheme has been inaugurated with adaptive key generation using the back propagation neural (BPN) model, which should be a supervised learning model. As the input of the neural network should be extracted from the features of the multimedia data, such as images and outputs, the initial seed has limited chaotic range. Future prediction is an inherent property of the artificial neural network. The BPN model includes precise selection for the adaptive key generation; during the training, BPN can learn about the randomness and redundancy nature of the image from the extracted image features. After the training, BPN can adapt to any image, producing the adaptive key. The proposed security framework mainly focuses on securely sharing and storing images in the cloud. The significant contributions of the proposed solution are:
- Neural–DNA–chaos permutation-based image encryption.
- Adaptive key generation based on plain image.
- Neural-based confusion of grey image.
- Establishment of a public cloud interface with the security framework.
- Validation of user authenticity to access the cloud-ciphered image.
- Improved protection for image sharing in multimedia communication.
3. Pre-Requisites
3.1. DNA Approach
Nucleic acid bases A (adenine), C (cytosine), G (guanine) and T (thymine) form a DNA sequence. It produces a DNA-coded value for every two-bit binary value, i.e., 00, 01, 10, 11. Based on Watson and Crick’s complementary rule, A complements T and G complements C. Thus, the possible combinations of DNA coding and operations result in 24 DNA rules in which only 8 rules are appropriate for image encryption, as shown in Table 1.

Table 1.
DNA encoding rules.
In DNA space, addition, subtraction and XORing operations are carried out to offer diffusion. DNA XORing reflects the binary XOR operation rule in DNA space. DNA addition and subtraction are performed as follows:
DNAX(OUT) = mod((DNAX(IN1) + DNAX(IN2)), 4)
DNAX(OUT) = DNAX(IN1) − DNAX(IN2); if DNAX(IN1) − DNAX(IN2)
= (4 + DNAX(IN1)) − DNAX(IN2); else
DNAX(OUT) is the output DNA value in the ruleset X after addition/subtraction.
DNAX(IN1) and DNAX(IN2) are the input values in DNA space at the rule set X.
3.2. Chaotic System
The chaotic system offers a good impact in ciphering the images due to its properties of ergodicity, keyspace and chaotic behaviour. The proposed work used 1D logistic and tent chaotic maps. The initial parameters for the chaotic maps X0 and Y0 vary from 0 to 1. The control parameter for the 1D logistic map is 3.57 ≤ α ≤ 4 and, for the tent map, 2 ≤ µ ≤ 4. The chaotic equations for a 1D logistic map and tent map are expressed through (1) and (2).
The Suitability of Chaotic Sequences for the Image Encryption Algorithm
The chaotic system consistently exhibits disordered behaviour due to chaos properties. In addition, it shows a direct relation with properties expected for cryptographic functions, namely confusion and diffusion [38]. Even if there is a slight change in the initial condition value, the chaos sequences will diverge to the extreme after some iteration. The ergodicity property in the diverged sequences will give uncorrelated neighbouring values, making the chaos system genuinely dynamic. Regarding the property of sensitivity to initial condition value, two very close initial condition values, such as 0.949 and 0.950, have been taken as input and iterated 20 times, as illustrated in Figure 1.
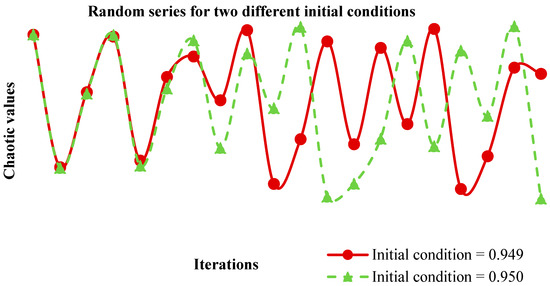
Figure 1.
Random series for two different initial conditions.
3.3. Hyperchaotic HNN
The presented work employed a four-node HNN. All the nodes are interconnected with all others, along with self-connection. Every node produces the output based on its previous state and the external bias input. The connection paths between the nodes are weighted, and the updated weights depend on the Hebb rule with a hyperbolic activation function, which exhibits the desired chaotic behaviour. Since the proposed HNN has four nodes, there are 16 weight values, namely W1–W16 (3).
Converged weight values decide the accuracy of obtained output compared to the actual output. Based on the activation function, the weight values can be integer/floating decimal values. The HNN generates random sequences with chaotic behaviour using Equations (4) and (5).
where Ci is constant and C1 = C2 = C3 = 1; C4 = 100; Xi is the previous state and wij is the weight matrix.
Nonlinearity analysis of HNN
The proposed hyperchaotic HNN weight matrix is given below:
where p is the control parameter.
The weight matrix must be asymmetrical, and the control parameter p = 0.3 is fixed to achieve the chaotic behaviour. With control parameter p = 0.3, the chaotic behaviour is depicted using Figure 2. The chaotic behaviour shown in Figure 2 depends on the initial seed Xi, weight values and the control parameter p.

Figure 2.
Chaotic behaviour of HNN with p = 0.3. (a–c) Between nodes X1 and all other three nodes. (d,e) Between nodes X2 with X3 and X4. (f) Between nodes X3 and X4.
4. Proposed Approach
The proposed approach consists of transposition followed by two DNA-based diffusion process stages. For the confusion and diffusion processes, keys are vital. In this proposed framework, two key generator modules are available to generate the keys, which are random sequences. One is to change the pixels’ position in an image, and the other is to change the pixel’s value. A neural attractor-based key is generated specifically for the images, so no two non-identical images have the same key for transposition. A chaotic-based key generation generates the random numbers through which image pixel values are diffused.
First, the adaptive key is generated through neural networks for the confusion process. Second, features extracted from the plain image influence the key generation. Hence, generated keys are image specific. The advantage is that cryptanalysis cannot guess the key without knowing the image features and features unique to the images. Third, the Hopfield neural network confuses the image irrespective of the modality or pixel intensity of the plain image; the knowledge database of the confusion model is updated to the plain image. Hence, image-specific confusion is carried out; as a result, interpixel redundancy is removed, which enhances the resistance against statistical attacks.
Adaptive key generation can be implemented with supervised learning, the BPN model. The model training data set is considered a significant feature of the image and required range of chaotic seeds. The proposed model enhances security using artificial intelligence. Firstly, adaptive key generation using the BPN model and image confusion with the Hopfield neural attractor are carried out. The BPN model is a multilayer feedforward architecture that can be learned through back propagating the error and with the gradient descent method. The Hopfield neural attractor is a recurrent random auto-associator architecture. The Hopfield neural attractor is stimulated with initial inputs, then inputs are removed and the attractor moves towards a stable state. With the initial input, the Hopfield neural attractor has a finite number of pseudo-random states. The pseudo-random states govern the confusion process adaptively. The proposed method is a hybrid technique which creates artificial intelligence-assisted DNA blended security.
Diffusion stages are called cipher block chaining, where pixels are ciphered sequentially. The diffusion operation uses the random keys generated by the chaos key generator. The encrypted image is pushed into a storage area available in the public cloud environment and can be retrieved as the original only with the encryption key(s). The proposed framework establishes secure storage of grey images in the cloud, as shown in Figure 3. The proposed security framework for the cloud-based grey image repository consists of various phases in the image encryption process, namely,
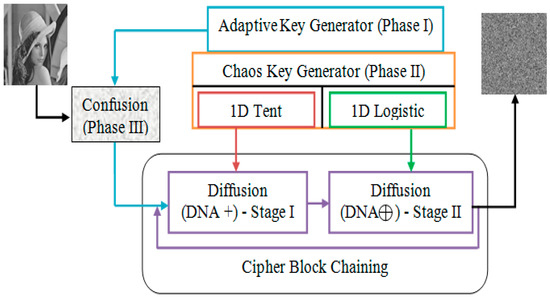
Figure 3.
Proposed Security Framework.
Phase I: Adaptive key generator.
Phase II: Chaos key generator.
Phase III: Hopfield neural network-based confusion process.
Phase IV: Cipher block chaining-based diffusion process.
Phase V: Interfacing cloud and the security framework.
Phase VI: Image decryption—cipher block chaining process.
Phase VII: Image decryption—Hopfield-based reassembling.
4.1. Image Ciphering and Deciphering Process
The various phases incorporated in the image ciphering and deciphering process are given as Algorithms 1–4 below:
| Algorithm 1: Adaptive random sequence generation using discrete Hopfield attractor |
| Input: Multiplicative identity matrix (Β)[4,4], sampling rate Tw, random initiator h[1,4] Output: Nonlinear random sequence Ω Initialise wij ← [w w/2 σ − w; Ψ 2w 3w 0; 3w ϕ w 0; mw 0 0 nw] ← [1 0.5 −5 −1; −0.37 2 3 0; 3 −13 1 0; 100 0 0 170] Update the wij with new σ, Ψ, ϕ Get H(0) ← [h]T Repeat Set r ← r + 1 Until r ≤ (Image size/4) Initialise Ω ← {} for f ← 1 to 16,384 for i ← 1 to 4 Ω ((4 × (f − 1)) + i) = Dh(i) end end Return (Ω) |
| Algorithm 2: Chaos key generator |
| Input: Initial parameters (KLD(0), KT(0)) control parameters (γ, μ) and image size N 3.4 ≤ α2 ≤ 4; 0 ≤ γ ≤ 2; 0 ≤ KLD(0) and KT(0) ≤ 1 Output: Chaos sequence KLDM and KTM as key for size N and DNA rule selectors R1, R2 1D tent map-based sequence as key for Diffusion I Initialise KTM = { }; θ = 1/2 for i ← 1 to N do if KT(i − 1) ≥ θ then Set KT(i) ← (μ × (1 − KT(i − 1))) else Set KT(i) ← (μ × KT(i − 1)) Set KTM(i) ← mod (KT × 1014, 256) end Return (KTM) 1D logistic map-based sequence as key for Diffusion II Set KLD(1) ← (γ × KLD(0)) × (1 − KLD(0)) Initialise KLDM = { } for i ← 2 to N do Set KLD(i) ← (γ × KLD(i −1)) × (1- KLD(i − 1)) Set KLDM(i) ← mod (KLD × 1014, 256) end Return (KLDM) |
| Algorithm 3: Image encryption—Hopfield based permutation |
| Input: Original image I of size (X) [M, N], Nonlinear random sequence Ω Output: Scrambled image matrix C Get where R is the ascending order of key stream ; ∀ is the index of the sorted key stream Repeat Set Set j ← j + 1 Until j < (M × N) Return (C) |
| Algorithm 4: Image encryption—cipher block chaining process |
| Input: Shuffled image C, Key sequences KTM, KLDM, rule for DNA encoding R1, R2 and 8-bit secret key K1 Output: Encrypted image E Set E(1) ← C(1) ⊕ K1 for i← 2 to N do Cd(i) ← C(i) ⊕ E(i − 1) Diffusion Stage I: Set CdDNA(i) DNAEncode (Cd(i)) Set KTMDNA(i) DNAEncode (KTM(i)) Set List ← [0, 2, 4, 6] for j ← 1 to 4 do Set n ← List[j] Set Cd1(i)[n:n + 1] ← mod ((CdDNA(i) [n:n + 1] + KTMDNA (i) [n:n + 1]), 4); end Diffusion Stage II: Set Cd1DNA(i) DNAEncode (Cd1(i)) Set KLDMDNA(i) DNAEncode (KLDM(i)) Set List ← [0, 2, 4, 6] for j ← 1 to 4 do Set n ← List[j] Set E(i)[n:n + 1] ← Cd1DNA (i) [n:n + 1] ⊕ KLDMDNA (i) [n:n + 1] end end Return (E) |
The aim is to store the secure image in a public repository called the cloud. So, the ciphered images are uploaded into the private storage area allotted by Amazon’s public cloud, availed with access privileges and credentials. Algorithm 5 pseudo-code describes the security framework and cloud storage interface. First, the authenticity verification process is carried out with invalid credentials.
| Algorithm 5: Authenticated cloud access process |
| Input: Encrypted image E of size X, login credentials of AWS, identity and access management (IAM) key pairs Output: Uploaded encrypted image E in the cloud storage Set AWS login credentials: username ← “username” and password←“password” Set IAM key pairs: access key ← “AAAAAAA” and secret key ← “SSSSSSS” if (username = “username” && password = “password”) then if (access key = “AAAAAAA” && secret key = “SSSSSSS”) then captcha = randomgen (captcha) and user expect to type it on the screen if captcha matched then Access = “Access Granted” Push S3: Bucket ← Encrypted images else Return (“Invalid CAPTCHA”) else Return (“Invalid Credentials”) else Return (Access = “Access Denied”) |
The cloud is accessed to download the ciphered images with valid credentials. Then, the ciphered images are decrypted using the algorithms described in Algorithms 6 and 7.
| Algorithm 6: Image decryption—cipher block chaining process |
| Input: Encrypted image of size (E) [M, N], key sequences KTM, KLDM, rule for DNA encoding R1, R2 and 8-bit secret key K1 Output: Shuffled image C Diffusion Stage I: Set EDNA(i) DNAEncode (E(i)) Set KLDMDNA(i) DNAEncode (KLDM(i)) Set List ← [0, 2, 4, 6] for j ← 1 to 4 do Set n ← List[j] Set Cd1(i)[n:n + 1] ← EDNA (i) [n:n + 1] ⊕ KLDMDNA (i) [n:n + 1] end Diffusion Stage II: Set Cd1DNA(i) DNAEncode (Cdi(i)) Set KTMDNA(i) DNAEncode (KTM(i)) Set List ← [0, 2, 4, 6] for j ← 1 to 4 do Set n ← List[j] Set Cd(i)[n:n + 1] ← mod ((Cd1DNA (i) [n:n + 1] − KTMDNA (i) [n:n + 1]), 4) end Set C(1) ← Cd(1) ⊕ K1 for i ← 2 to N do Set C(i) ← Cd(i) ⊕ Cd(i − 1) end Return (C) |
| Algorithm 7: Image decryption—Hopfield-based reassembling |
| Input: Scrambled image matrix C of size (X) [M, N], nonlinear random sequence Ω Output: Original image I Get [R, A] ← sort (Ω, “ascend”) where R is the ascending order of key stream ; A is the index of the sorted key stream Repeat Set I (A(j)) ← C(j) Set j ← j + 1 Until j < (M × N) Return (I) |
4.2. Security Framework Interface with Public Cloud
In this proposed approach, the S3 service from Amazon Web Services (AWS) is used as a public repository to store the grey images in encrypted form. The proposed approach offers third-level authentication because one of the contributions of the work is improved protection for image sharing in multimedia communication over public repositories. A user registers with AWS to obtain the S3 service and credentials as a cloud user. Every registered user is provided with a username and password as a level 1 authentication credential. At level 2 authentication, the secret key pairs validate the user’s identity. Third-level authentication employs CAPTCHA verification. During data access, the user’s authenticity is verified. If the credentials fail to be correct at any level of authentication, the user access is denied with the warning “Invalid credentials”. The interface between the proposed framework and the AWS is illustrated in Figure 4a. Figure 4b illustrates the uploading process of cipher images into AWS S3 storage. The view of the S3 bucket with uploaded ciphered images is shown in Figure 5.

Figure 4.
(a) Block diagram view: Storing ciphered image in S3 bucket. (b) Block diagram view: Retrieving ciphered image from S3 bucket with three-tier authentication.
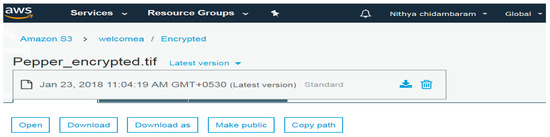
Figure 5.
View of the ciphered image in AWS S3 bucket.
5. Results and Discussion
The performance of the proposed encryption approach was analysed using different grey images of size [256, 256] with the Waterloo image databases (https://links.uwaterloo.ca/Repository.html (accessed on 8 December 2022)). It was implemented using the LabVIEW platform on an Intel Core i5 system configured with a 2.5 GHz CPU, 500 GB of main memory and 4 GB of RAM. The ability of the encryption approach against attacks such as brute force, statistical and chosen plaintext was analysed. The proposed scheme is influenced by adaptive key generation using the BPN model, which generates the adaptive key based on the randomness and redundant nature of the images. Furthermore, the security framework resists known plaintext attacks due to image-specific key generation for transposition. In addition, encryption quality analyses were carried out to prove the fitness of the proposed image encryption algorithm for secure image storage in the cloud.
5.1. Brute Force Attack
5.1.1. Keyspace Analysis
According to Kerckhoff’s cipher principle, the key must be vital and secure even if the encryption algorithm is public access. Keeping a longer key for the encryption process increased the key searching space, increasing the time to find the correct key [25]. In this security framework, six keys were generated adaptively with a precision of 1014. Hence, 10112 is the keyspace for keys generated through the HNN. For the diffusion process, three different keys, K1, K2 and K3, are used of which two keys have chaotic behaviour, requiring four initial parameters, with precision of 1014 and one key is a fixed 8-bit key. Thus, the total keyspace is 102 × 1014 × 1014 × 1014 × 1014 × 10112 = 10170. In our earlier research on DNA blended chaos-based image encryption [24], the keyspace was 1086. Compared to earlier work, this proposed approach exhibits greater keyspace, making the brute force attack even more complex.
5.1.2. Key Sensitivity Analysis
Chaotic sequence generators such as a hyperchaotic HNN and logistic and tent maps are used in the proposed security framework because they are sensitive to the initial conditions. Furthermore, an independent and adaptive key for each image makes the key search complex. Image features used to generate the adaptive keys through the HNN make the search even more complex. For example, a change in one bit out of 256 × 256 × 8 bits in the diffusion stage II key produces an entirely different image due to the chaotic behaviour of the key generated through the 1D logistic map. This is evident for the anti-brute force attack approach of the proposed security algorithm. Figure 6 shows the Lena image before and after encryption with correct and incorrect keys as evidence of the key sensitivity analysis.

Figure 6.
Key sensitivity analysis through various images: (a) Plain; (b) ciphered (E1); (c) ciphered (one-bit change in original key) (E2); (d) E1 XOR E2; (e) decrypted E1 with correct key; (f) decrypted E1 with an incorrect key.
5.2. Statistical Attack Analysis
Images with statistical properties are subject to vulnerability when stored in public environments such as the cloud. The images before their storage are expected to have zero correlation to avoid such a security breach. The resistivity of the encryption algorithm against statistical attacks is tested through histogram, correlation and entropy analysis.
5.2.1. Histogram Analysis
The intensity of pixels in the greyscale must be distributed uniformly over the image plane for any encrypted image. However, due to the proposed DNA diffusion process, the histogram obtained for the test images is flat in response. Thus, an image’s unpredictability is proved. The histogram analysis for the test images of the proposed method is illustrated in Figure 7. Figure 7 shows that the pixels are uniformly distributed after encryption, and histograms of plain and cipher images are completely different.

Figure 7.
Representation of Histogram for Plain and Cipher images.
5.2.2. Neighbouring Pixel Correlation Analysis
The co-located pixels in the original image are extremely correlated. Ideally, the correlation is zero for an encrypted image, i.e., a near-zero correlation [25]. After employing the proposed encryption algorithm on the images, the randomness of co-occurring pixels is high. Randomness in the encrypted images is calculated using a relation among co-located pixels. The dependency among the pixels is measured using the following expressions ((6)–(8)):
where standard deviation is obtained by
Co-variance of an image is computed by
where Yi and Yj are two nearby pixel values of the ciphered image. The correlation among neighbouring pixels in all three directions of plain and encrypted images is illustrated in Figure 8. Figure 8 reveals that the correlation with the adjacent pixel values of the ciphered image is very low. Thus, the proposed neural-based adaptive key generation used for confusion offers near-zero correlation among the neighbouring pixels compared to other state of the art works shown in Table 2, which proves the ability of attack mitigation in the spatial domain.

Figure 8.
Pixel distribution in horizontal, vertical and diagonal directions.

Table 2.
Correlation analysis of Proposed versus Existing methods.
The neighbouring correlation values in Table 2 prove that the neural-based confusion model breaks the correlation between the adjacent pixels and the desired level. Due to neural-based adaptive confusion, all the images are equally confused, and pixels are dislocated repeatedly until the expected correlation is achieved.
5.2.3. Information Entropy
After encryption of an image, robustness and randomness are analysed using information entropy [25]. Global Shannon entropy E(s) is obtained using the following expression (9):
where I(Si) is the probability of symbol (Si). The pixel bit depths for grey images are always 8, so the entropy exists in the range [0 to 8]. For an ideally encrypted image, the entropy is always 8 [25]. This proposed neural-assisted DNA-based image encryption algorithm makes the pixel distribution over an image plane highly random. Therefore, the entropy value of an encrypted image is very close to 8. If the entropy value is less than 8 or close to 0 then the randomness effect in the encrypted image is significantly less and the vulnerability to attack is high. Table 3 shows that the proposed neural-based image encryption algorithm results in an entropy of almost eight, irrespective of the input image. The entropy value of the proposed encryption is compared with other state of the art works and exhibits the maximum unpredictability of the plain image.

Table 3.
Entropy Analysis of Proposed versus Existing methods.
5.3. Encryption Quality Analysis
5.3.1. Chi-Square Test
The chi-square test measures pixel distribution in ciphered images [18]. The variation in the histogram is quantitatively obtained using a statistical metric called chi squared (), which is expressed as follows:
where PI is the pixel intensity value in the interval of 0 to 255. “i” is the intensity value in the encrypted pixels. The chi-square values that were found for encrypted images are verified with the distribution probability for 1% and 5% significance levels. The critical values for the 1% and 5% significance level with a degree of freedom of 255 are 310.457 and 293.2478, respectively. Therefore, the χ2 value must be lower than the critical values for the ideally encrypted image. Table 4 reveals the uniform distributions of pixels in an encrypted image through low chi-square values compared to essential values.

Table 4.
Chi-square test: Pixel distribution test.
5.3.2. Histogram Maximum Deviation
The histogram maximum deviation is a measure of diffusion efficiency and encryption quality. Histogram maximum deviation is the difference in histogram values between the ciphered and plain image at every pixel intensity [17]. For an ideally encrypted image, the value must be close to the total size of the image. A histogram maximum deviation value close to the size of an image proves the randomness of pixel distribution through the encryption process. Histogram maximum deviation (HM) is obtained using the following Equation (11):
where dif(j) is the difference between the plain and cipher image histogram at the jth index. After encryption, the histogram deviation between the plain and cipher image is high, as shown in Table 5. From Table 5, it is proven that the strength of the encryption algorithm is well suited for secure image sharing and storing compared to other state of the art works. This is because, after ciphering the image, its statistical properties do not reveal any significant detail about the plain image.

Table 5.
Histogram Maximum Deviation.
5.3.3. Irregular Deviation
Encryption quality is analysed using irregular deviation. The linearity of the pixel distribution may be reflected in a differential attack. In any image encryption algorithm, the pixel intensities are expected to be uniformly distributed in the cipher image [17]. The irregular deviation is calculated through Equations (12)–(14), given below:
The mean for the histogram of the difference in pixel intensities between the plain and cipher images (d) is calculated through the following expression:
where di is the ith element in the array d.
Irregular deviation (HI) is obtained using Equation (14).
Table 6 reveals that the proposed encryption algorithm distributes the pixel intensities uniformly without bias in the plain image.

Table 6.
Irregular Deviation.
5.3.4. Deviation from Ideality
Deviation from ideality must be minimal after encryption to prove the algorithm is promising for attacks [17]. Deviation of the originally encrypted image histogram from ideally encrypted images is estimated by the following Equation (15):
where M × N is the total size of the image.
Near-zero HDI proves the quality of the encryption algorithm. Table 7 depicts the existence of a very low deviation from ideality between plain and ciphered images. Thus, the proposed encryption algorithm produces low deviation from ideality compared to the existing literature, as shown in Table 7.

Table 7.
Deviation from Ideality.
5.4. Chosen Plaintext Attack
Diffusion employed in the encryption through XOR alone as an operation is subject to a chosen plaintext attack. The chosen plaintext attack results in the key used for diffusion; the encryption algorithm is compromised. Any encryption algorithms against the chosen plaintext attack need to satisfy the following condition:
P1 ⊕ P2 ≠ E1 ⊕ E2
Any two plain grey images, as P1 and P2, are XORed. Similarly, the encrypted versions of P1 and P2 as E1 and E2 are XORed. If both the XORed values are equal, it is vulnerable to chosen plaintext attack. Otherwise, breaking the image encryption algorithm is impossible, and its fitness against the chosen plaintext attack is proved. The ability of this security algorithm is analysed and it is shown that the DNA diffusion approach acts against the chosen plaintext attack. Figure 9a shows the XORed result of two plain images; the encrypted version of the same plain images is XORed, as shown in Figure 9b. Figure 9a,b are not identical, which indicates that the proposed diffusion process is not vulnerable to the chosen plaintext attack. A known plaintext attack becomes unviable in the proposed security framework due to the image-specific adaptive key generation using a neural network.

Figure 9.
(a) P1 ⊕ P2; (b) E1 ⊕ E2.
5.5. Bit Distribution Analysis at Plane Level
The potency of the diffusion process is further analysed using the equality test over every bit plane. For any encrypted image, the distribution of zeros and ones in each bit plane must be equal, i.e., 50% of zeros and ones must be present in each plane to prove the unpredictability of the plain image after encryption. The diffusion strategy proposed in the algorithm outfit for the image encryption are shown, where the bits 1 and 0 of an encrypted image are equally distributed and tabulated in Table 8. Table 8 shows the bit “1” percentage in each plain and encrypted test image’s bit plane. Table 8 shows that each plane’s bit “1” in an encrypted image is equally distributed. So, the proposed DNA-based diffusion offers strong enough image encryption.

Table 8.
Bit distribution analysis at plane level.
5.6. Computational Complexity
The overhead of the proposed security framework includes significant operations called key generation, confusion and DNA-based diffusions. The greyscale image used in this research is of size [M, N], where M = N = 256. The random number generated using the HNN takes the complexity of O {n(M × N)}. The transposition process complexity is O {M × N}. The proposed algorithm contains two DNA-based diffusion stages, which take O {4(M × N)}. So, the total computational complexity of the proposed framework takes O {(n + 5)(M × N)}. Table 9 compares the proposed system and other state of the art works with various aspects such as system configuration, tool used for implementation, the approach suggested and execution time. This proposed work has been implemented using the LabVIEW platform on an Intel Core i5 system configured with a 2.5 GHz CPU, 500 GB of main memory and 4 GB of RAM. Total execution time taken by this proposed approach, including key generation and cipher block chaining encryption, is calculated as 219.5 ms, comparable with Ref. [32]. The file is pushed into the AWS S3 bucket via a Wi-Fi network with 144.4 Mbps speed, which takes an uploading time of 0.4056 sec. Network speed influences propagation delay, which means they are inversely proportional.

Table 9.
Computational complexity comparison with existing literature.
5.7. Discussion
The proposed algorithm is tested with ten test images of size [256, 256]. The algorithm achieves average entropy of 7.996098 and offers better entropy when compared to Refs. [12,16,39] and is comparable with [40,41,42,43,44,45,46,47,48,49,50,51,52,53]. The near-zero correlation offered by the proposed algorithm is better than the previous works, which is also given in the findings. The obtained average bit distribution at the plane level for the test images is 50.00364 and shows that the encrypted images are highly randomised. Therefore, the proposed image encryption is cryptographically efficient and can withstand statistical and chosen plaintext attacks. Furthermore, the presented work can restore useful images from captured versions of images under various environmental conditions. The suggested methodology is the best for analysing an image across a wireless medium and is sufficiently robust to interference.
6. Conclusions
Cloud storage is trendy and inevitable in many applications. However, data stored in the cloud are always under threat due to their multitenancy. So, it is essential to construct a security solution to ensure the security of cloud-hosted data. The proposed Hopfield attractor-based permutation blended DNA diffusion provides tightened security for grey images hosted in public cloud storage during when at rest, in transit and used by other applications. The proposed security framework exhibits greater potency to defend against various attacks. This proposed work uses a Hopfield attractor and chaotic maps, resulting in the keyspace of 10170. The key generated for the confusion process is adaptive and image specific; hence, attackers cannot find the key using a chosen plaintext attack and a known plaintext attack. The proposed security algorithm yielded an average entropy value of 7.9973 and an average correlation value of 0.0008; hence, attackers cannot find the plain image using a statistical attack. This framework can be enhanced in future by using a reconfigurable hardware platform.
Author Contributions
Conceptualisation, H.M., N.C. and R.A.; methodology, C.L., N.C. and P.V.M.; software, C.L., N.C. and P.V.M.; validation, P.V.M., K.M.M. and K.T.; formal analysis, K.M.M. and P.V.M.; investigation, N.C., P.V.M. and K.M.M.; resources, P.V.M.; data curation, N.C., P.V.M. and K.T.; writing—original draft preparation, H.M., K.T. and R.A.; writing—review and editing, H.M., K.M.M. and R.A.; visualisation, P.V.M.; supervision, R.A. and K.T.; project administration, H.M., K.T. and R.A.; funding acquisition, HM and R.A. All authors have read and agreed to the published version of the manuscript.
Funding
Institutional Fund Projects under grant no. IFPIP: 965-144-1443. Ministry of Education and King Abdulaziz University, DSR, Jeddah, Saudi Arabia.
Data Availability Statement
Not applicable.
Acknowledgments
The authors gratefully acknowledge the technical and financial support provided by the Ministry of Education and King Abdulaziz University, DSR, Jeddah, Saudi Arabia.
Conflicts of Interest
The authors declare no conflict of interest.
References
- Singh, A.; Chatterjee, K. Cloud security issues and challenges: A survey. J. Netw. Comput. Appl. 2017, 79, 88–115. [Google Scholar] [CrossRef]
- Yang, R.; Xu, Q.; Au, M.H.; Yu, Z.; Wang, H.; Zhou, L. Position based cryptography with location privacy: A step for Fog Computing. Future Gener. Comput. Syst. 2018, 78, 799–806. [Google Scholar] [CrossRef]
- Shahzadi, S.; Iqbal, M.; Dagiuklas, T.; Qayyum, Z.U. Multi-access edge computing: Open issues, challenges and future perspectives. J. Cloud Comput. 2017, 6, 30. [Google Scholar] [CrossRef]
- Huh, J.H.; Seo, Y.S. Understanding edge computing: Engineering evolution with artificial intelligence. IEEE Access 2019, 7, 164229–164245. [Google Scholar] [CrossRef]
- Eom, S.; Huh, J.H. The opening capability for security against privacy infringements in the smart grid environment. Mathematics 2018, 6, 202. [Google Scholar] [CrossRef]
- Tao, M.; Ota, K.; Dong, M. Ontology-based data semantic management and application in IoT- and cloud-enabled smart homes. Future Gener. Comput. Syst. 2017, 76, 528–539. [Google Scholar] [CrossRef]
- Asadi, S.; Nilashi, M.; Husin, A.R.C.; Yadegaridehkordi, E. Customers perspectives on adoption of cloud computing in banking sector. Inf. Technol. Manag. 2017, 18, 305–330. [Google Scholar] [CrossRef]
- Singh, S.; Jeong, Y.S.; Park, J.H. A survey on cloud computing security: Issues, threats, and solutions. J. Netw. Comput. Appl. 2016, 75, 200–222. [Google Scholar] [CrossRef]
- Kumari, M.; Gupta, S.; Sardana, P. A Survey of Image Encryption Algorithms. 3D Res. 2017, 8, 37. [Google Scholar] [CrossRef]
- Wang, B.; Xie, Y.; Zhou, C.; Zhou, S.; Zheng, X. Evaluating the permutation and diffusion operations used in image encryption based on chaotic maps. Optik 2016, 127, 3541–3545. [Google Scholar] [CrossRef]
- Alsaedi, M. Colored image encryption and decryption using multi-chaos 2D quadratic strange attractors and matrix transformations. Multimed. Tools Appl. 2017, 76, 24527–24547. [Google Scholar] [CrossRef]
- Hua, Z.; Zhou, Y.; Pun, C.M.; Chen, C.L.P. 2D Sine Logistic modulation map for image encryption. Inf. Sci. 2015, 297, 80–94. [Google Scholar] [CrossRef]
- Diaconu, A.V. Circular inter-intra pixels bit-level permutation and chaos-based image encryption. Inf. Sci. 2016, 355–356, 314–327. [Google Scholar] [CrossRef]
- Ponuma, R.; Amutha, R. Compressive sensing based image compression-encryption using novel 1D-chaotic map. Multimed. Tools Appl. 2018, 77, 19209–19234. [Google Scholar] [CrossRef]
- Abbas, N.A. Image encryption based on Independent Component Analysis and Arnold’s Cat Map. Egypt. Inform. J. 2016, 17, 139–146. [Google Scholar] [CrossRef]
- Wang, X.; Liu, L.; Zhang, Y. A novel chaotic block image encryption algorithm based on dynamic random growth technique. Opt. Lasers Eng. 2015, 66, 10–18. [Google Scholar] [CrossRef]
- Belazi, A.; Abd El-Latif, A.A.; Belghith, S. A novel image encryption scheme based on substitution-permutation network and chaos. Signal Process. 2016, 128, 155–170. [Google Scholar] [CrossRef]
- Huang, X.; Ye, G. An image encryption algorithm based on irregular wave representation. Multimed. Tools Appl. 2018, 77, 2611–2628. [Google Scholar] [CrossRef]
- Broumandnia, A. Designing digital image encryption using 2D and 3D reversible modular chaotic maps. J. Inf. Secur. Appl. 2019, 47, 188–198. [Google Scholar] [CrossRef]
- Duan, C.F.; Zhou, J.; Gong, L.H.; Wu, J.Y.; Zhou, N.R. New color image encryption scheme based on multi-parameter fractional discrete Tchebyshev moments and nonlinear fractal permutation method. Opt. Lasers Eng. 2022, 150, 106881. [Google Scholar] [CrossRef]
- Zhang, Q.; Liu, L.; Wei, X. Improved algorithm for image encryption based on DNA encoding and multi-chaotic maps. AEU Int. J. Electron. Commun. 2014, 68, 186–192. [Google Scholar] [CrossRef]
- Wang, X.Y.; Zhang, Y.Q.; Bao, X.M. A novel chaotic image encryption scheme using DNA sequence operations. Opt. Lasers Eng. 2015, 73, 53–61. [Google Scholar] [CrossRef]
- Hu, T.; Liu, Y.; Gong, L.H.; Guo, S.F.; Yuan, H.M. Chaotic image cryptosystem using DNA deletion and DNA insertion. Signal Process. 2017, 134, 234–243. [Google Scholar] [CrossRef]
- Chai, X.; Chen, Y.; Broyde, L. A novel chaos-based image encryption algorithm using DNA sequence operations. Opt. Lasers Eng. 2017, 88, 197–213. [Google Scholar] [CrossRef]
- Enayatifar, R.; Abdullah, A.H.; Isnin, I.F.; Altameem, A.; Lee, M. Image encryption using a synchronous permutation-diffusion technique. Opt. Lasers Eng. 2017, 90, 146–154. [Google Scholar] [CrossRef]
- Wang, S.; Peng, Q.; Du, B. Chaotic color image encryption based on 4D chaotic maps and DNA sequence. Opt. Laser Technol. 2022, 148, 107753. [Google Scholar] [CrossRef]
- Alarood, A.A.; Alsolami, E.; Al-Khasawneh, M.A.; Ababneh, N.; Elmedany, W. IES: Hyper-chaotic plain image encryption scheme using improved shuffled confusion-diffusion. Ain Shams Eng. J. 2022, 13, 101583. [Google Scholar] [CrossRef]
- Zhou, W.; Wang, X.; Wang, M.; Li, D. A new combination chaotic system and its application in a new Bit-level image encryption scheme. Opt. Lasers Eng. 2022, 149, 106782. [Google Scholar] [CrossRef]
- Pavithran, P.; Mathew, S.; Namasudra, S.; Srivastava, G. A novel cryptosystem based on DNA cryptography, hyperchaotic systems and a randomly generated Moore machine for cyber physical systems. Comput. Commun. 2022, 188, 1–12. [Google Scholar] [CrossRef]
- Yousif, S.F.; Abboud, A.J.; Alhumaima, R.S. A new image encryption based on bit replacing, chaos and DNA coding techniques. Multimed. Tools Appl. 2022, 81, 27453–27493. [Google Scholar] [CrossRef]
- Qin, Z.; Weng, J.; Cui, Y.; Ren, K. Privacy-Preserving Image Processing in the Cloud. IEEE Cloud Comput. 2018, 5, 48–57. [Google Scholar] [CrossRef]
- Chidambaram, N.; Raj, P.; Thenmozhi, K.; Rajagopalan, S.; Amirtharajan, R. A cloud compatible DNA coded security solution for multimedia file sharing & storage. Multimed. Tools Appl. 2019, 78, 33837–33863. [Google Scholar]
- Zhang, Y.; He, Q.; Xiang, Y.; Zhang, L.Y.; Liu, B.; Chen, J.; Xie, Y. Low-Cost and Confidentiality-Preserving Data Acquisition for Internet of Multimedia Things. IEEE Internet Things J. 2018, 5, 3442–3451. [Google Scholar] [CrossRef]
- Bigdeli, N.; Farid, Y.; Afshar, K. A robust hybrid method for image encryption based on Hopfield neural network. Comput. Electr. Eng. 2012, 38, 356–369. [Google Scholar] [CrossRef]
- Lakshmi, C.; Thenmozhi, K.; Rayappan, J.B.B.; Amirtharajan, R. Hopfield attractor-trusted neural network: An attack-resistant image encryption. Neural Comput. Appl. 2020, 32, 11477–11489. [Google Scholar] [CrossRef]
- Lakshmi, C.; Thenmozhi, K.; Venkatesan, C.; Seshadhri, A.; Rayappan, J.B.B.; Amirtharajan, R. Mutated cleavages of images for stealth disclosure: A hopfield neural network attractor (HNNA) approach. Neural Process. Lett. 2021, 53, 907–928. [Google Scholar] [CrossRef]
- Lakshmi, C.; Thenmozhi, K.; Rayappan, J.B.B.; Rajagopalan, S.; Amirtharajan, R.; Chidambaram, N. Neural-assisted image-dependent encryption scheme for medical image cloud storage. Neural Comput. Appl. 2021, 33, 6671–6684. [Google Scholar] [CrossRef]
- Dhall, S.; Pal, S.K.; Sharma, K. A chaos-based probabilistic block cipher for image encryption. J. King Saud Univ. Comput. Inf. Sci. 2022, 34, 1533–1543. [Google Scholar] [CrossRef]
- Patel, S.; Thanikaiselvan, V.; Pelusi, D.; Nagaraj, B.; Arunkumar, R.; Amirtharajan, R. Colour image encryption based on customised neural network and DNA encoding. Neural Comput. 2021, 33, 14533–14550. [Google Scholar] [CrossRef]
- Jiang, Z.; Liu, X. Image Encryption Algorithm Based on Discrete Quantum Baker Map and Chen Hyperchaotic System. Int. J. Theor. Phys. 2023, 62, 22. [Google Scholar] [CrossRef]
- Wang, W.T.; Sun, J.Y.; Zhang, H.; Zhang, J. Quantum cryptosystem and circuit design for color image based on novel 3D Julia-fractal chaos system. Quantum Inf. Process. 2023, 22, 64. [Google Scholar] [CrossRef]
- Wang, H.K.; Xu, G.B.; Jiang, D.H. Quantum grayscale image encryption and secret sharing schemes based on Rubik’s Cube. Physica A Stat. Mech. Its Appl. 2023, 612, 128482. [Google Scholar] [CrossRef]
- Hao, W.; Zhang, T.; Chen, X.; Zhou, X. A hybrid NEQR image encryption cryptosystem using two-dimensional quantum walks and quantum coding. Signal Process. 2023, 205, 108890. [Google Scholar] [CrossRef]
- Mahalingam, H.; Veeramalai, T.; Menon, A.R.; S., S.; Amirtharajan, R. Dual-Domain Image Encryption in Unsecure Medium—A Secure Communication Perspective. Mathematics 2023, 11, 457. [Google Scholar] [CrossRef]
- Zhu, S.; Deng, X.; Zhang, W.; Zhu, C. Image Encryption Scheme Based on Newly Designed Chaotic Map and Parallel DNA Coding. Mathematics 2023, 11, 231. [Google Scholar] [CrossRef]
- Song, X.; Chen, G.; Abd El-Latif, A.A. Quantum Color Image Encryption Scheme Based on Geometric Transformation and Intensity Channel Diffusion. Mathematics 2022, 10, 3038. [Google Scholar] [CrossRef]
- Zhong, H.; Li, G.; Xu, X.; Song, X. Image Encryption Algorithm Based on a Novel Wide-Range Discrete Hyperchaotic Map. Mathematics 2022, 10, 2583. [Google Scholar] [CrossRef]
- Mansoor, S.; Sarosh, P.; Parah, S.A.; Ullah, H.; Hijji, M.; Muhammad, K. Adaptive Color Image Encryption Scheme Based on Multiple Distinct Chaotic Maps and DNA Computing. Mathematics 2022, 10, 2004. [Google Scholar] [CrossRef]
- Mfungo, D.E.; Fu, X.; Wang, X.; Xian, Y. Enhancing Image Encryption with the Kronecker xor Product, the Hill Cipher, and the Sigmoid Logistic Map. Appl. Sci. 2023, 13, 4034. [Google Scholar] [CrossRef]
- Chen, C.; Zhu, D.; Wang, X.; Zeng, L. One-Dimensional Quadratic Chaotic System and Splicing Model for Image Encryption. Electronics 2023, 12, 1325. [Google Scholar] [CrossRef]
- Chen, X.; Wang, Q.; Fan, L.; Yu, S. A Novel Chaotic Image Encryption Scheme Armed with Global Dynamic Selection. Entropy 2023, 25, 476. [Google Scholar] [CrossRef] [PubMed]
- Chang, H.; Wang, E.; Liu, J. Research on Image Encryption Based on Fractional Seed Chaos Generator and Fractal Theory. Fractal Fract. 2023, 7, 221. [Google Scholar] [CrossRef]
- Zhao, J.; Wang, S.; Zhang, L. Block Image Encryption Algorithm Based on Novel Chaos and DNA Encoding. Information 2023, 14, 150. [Google Scholar] [CrossRef]
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).