3.4. Cipher Procedure
The high-level description of the ICLEBF cryptosystem consists of a 14-round symmetric encryption algorithm [
42]. In this algorithm, both the permutations, the
S-box, and the schedule keys are dynamic, i.e., in each encryption procedure, they are different. Furthermore, the size of permutations and the schedule keys are the same as the image size. Below, we present the steps of the algorithm in each round.
(I) The encryption algorithm applies a permutation
, on the pixel positions of the original image. This is done before the rounds start. Next, the xor operation is performed between the string that results from the permutation and the first schedule key. Subsequently, the string that results from the xor operation is divided into 8-bit substrings, i.e., a byte. Finally, the substitution operation is applied to each of these bytes, using the first
S-box. The criteria used in the substitution operation are the same as in FIPS 197 [
43]. Later, the permutation
, boxes, and schedule keys are generated.
(II) From rounds two to thirteen, the algorithm executes the following steps: it starts with an xor between the output of the previous round and the corresponding schedule key. Then, the substitution operation is performed with the corresponding S-box.
(III) In round 14, the following steps are executed: first, the xor operation is applied between schedule key 14 and the output of round 13. Next, the result of the previous operation is subdivided into blocks of 8 bits, and the substitution process is then carried out with the last box. It is terminated with an xor operation with schedule key 15. This last result provides the encrypted image.
Regarding the construction of the permutation, the schedule keys and the boxes are shown in the next section.
3.5. Generation of the S-Boxes, Permutation, and Schedule Keys
The procedure for generating the 8 × 8 S-boxes is shown below:
(a) An integer is randomly obtained that satisfies . Subsequently, the point is calculated, where is the primitive number. Let us denote the result = .
(b) In this investigation, the constant
of Equation (
25) is proposed. It has a value associated with the binary string
. Afterward, the operations
are performed.
(c) According to the result of section (b), the bits from the decimal point to the right are divided into blocks of 8 bits. Furthermore, it is clarified that an
S-box is a permutation of the 256 elements of the set
. The constants
of Equation (
42) are computed, and then the permutation is obtained. In this order of ideas, the calculation of
is done as follows: the first 8 bits after the decimal point are taken, and the integer associated with this string of bits is called
. Then, the following calculation is carried out:
=
256, such that
holds.
is related to the
i-th block of 8 bits to the right of the decimal point. This block has an associated integer value which we denote as
. So,
=
256 -
i with
, considering that
= 0.
(d) Once the
has been obtained, the algorithm outlined in
Section 3.3 is used to generate the permutation. To get the other boxes, i.e., from two to fourteen, continue to shift to the right of the 8-bit decimal point and then perform the modular operation.
Regarding the generation of the permutation, the procedure is shown below.
(a) In the same way as before, an integer is randomly generated, that is in a range of .
(b) Once the value
is obtained, the point
is calculated, considering that
is the primitive number. Let us write the result of
as
. Then, the concatenation of the coordinates of
is performed; that is,
. The integer value associated with the binary string
is assigned to the constant
of the Equation (
25).
(c) According to the previous step, the calculation
is carried out. So, in this investigation, it is proposed to divide the binary string formed from the decimal point to the right into blocks of three bytes; that is, it starts with bytes 0, 1, 2. Let us refer to the non-negative integer associated with the binary string of the first three bytes as
; furthermore, let us denote the number of pixels in the image as
l. With this information, the first constant,
, of Equation (
42) is calculated as follows:
. To obtain the constant
with
, we will proceed as follows:
i shifts one byte to the right of the decimal point, and the bytes
are taken. In the same way as before, this 24-bit block has a non-negative integer, which is written as
. From here, the
i-th constant is obtained as follows:
=
.
(d) When the constants indicated in Equation (
42) are calculated, it is possible to generate a permutation as mentioned in
Section 3.3.
On the other side, the previous steps are essentially described below. A positive integer
is chosen, that satisfies the condition where it is less than the number of solutions
. This value leads us to a point on the curve
. The previous point generates the integer
. From here, it is possible to execute the operation indicated in Equation (
25). Blocks of one byte are taken to the right of the decimal point. Each byte can be interpreted as an integer and used to obtain the
constants in Equation (
42). Subsequently, a permutation is obtained over an array of 256 positions, which leads us to a box.
Regarding the schedule keys (third aspect), the same calculations in items (a) and (b) are performed to obtain the permutation of bytes of the image. Then, the constant is used.
Subsequently, the decimal point to the right l pixels are obtained from the product ; that is, a binary string of the image size. This paper sets this string as the first schedule key, denoted as . To generate the other schedule keys; that is, ⋯ the following is done:
For with , a one-byte left circular shift of the key is performed.
In order to illustrate the point, the elliptic curve used in this investigation is shown below. Furthermore, it is pointed out that the proposed curve meets the conditions mentioned in Equations (
3)–(
5).
The values of , as well as, the primitive element are expressed next.
p = 988464ba59685284506433ccd3f83450166fda2d2ec7
109a5c0679434e9dfb46b3a447043b406c4115af9a2c7fdc17
bc9b6668f07d80d7142f534a1dc64ef400b9b2100acb691
q = 2621192e965a14a114190cf334fe0d14059bf68b4bb1
c42697019e50d3a77ed1ace911d9c1e6fa9ecb772f44670d2
9e05a69fc249b108ed06114d9e01b7662721ecf151ce2329
a = 31662dbf1d0c1691728e2c47e26720c3d0f760b216aa8
00eb153c54ae3e0c522345eb09
b = 308
k = 870eebe8cf19ece84593dd9deaec2ebab1380c94c240fe
8fc1d45836fff18114c42308e5aafef0ee4d1a643b179415eb
34d8b2118e51ad727b63efc5dba104179bcece5a0d7cb
On the other hand, the generator element is presented below:
= 28b1f61561824dac022aa29d37df70295a2d7f34f696
5e032d85b35b6e4c8403a47922b96753ba338061a05eee5
30f5759043d58aa09d69ae8b2377b640c01e484ac14d27d
693
= 288189d9988f9d839ae797195f3a4b512b36773156af
fd0b64a5ed740c9ea059233eab4765397a0a5de87ea46a20
d208cf8988d433e4d703792e2f950ad6a0a631f0d424e6951
In another order of ideas, it can be seen that the points
and
are important in constructing the symmetric cryptosystem. So, in a secure communication scheme, for example, the PKI [
44], the recipient only needs to know these points to develop the particular symmetric cryptosystem. In this sense, the sender can send the points mentioned above using the recipient’s public key called
Q. Later, the recipient using their private key can get
and
. Furthermore, the sender can sign the message according to the Elliptic Curve Signature Algorithm (ECSA) [
45] standard.
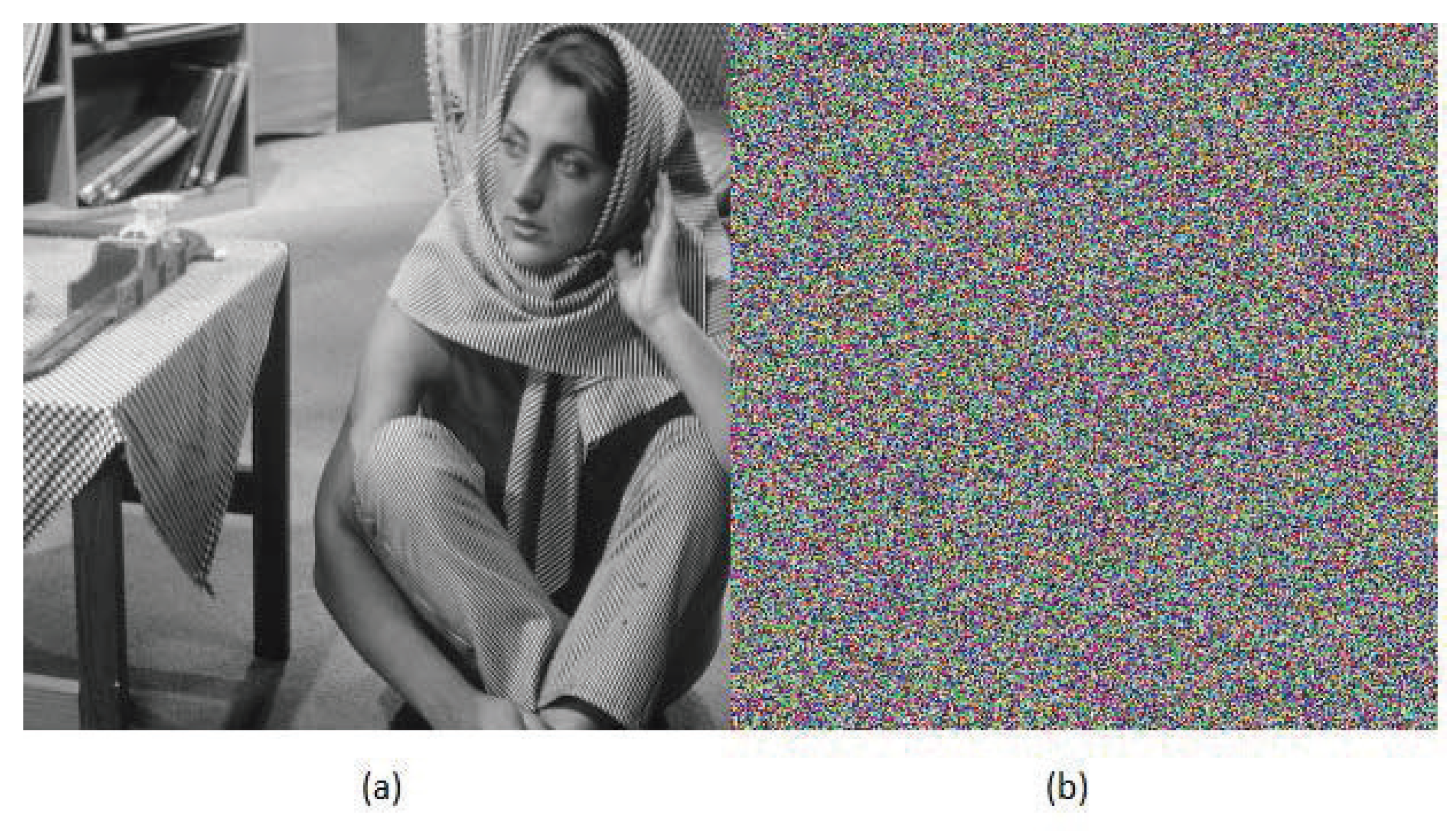
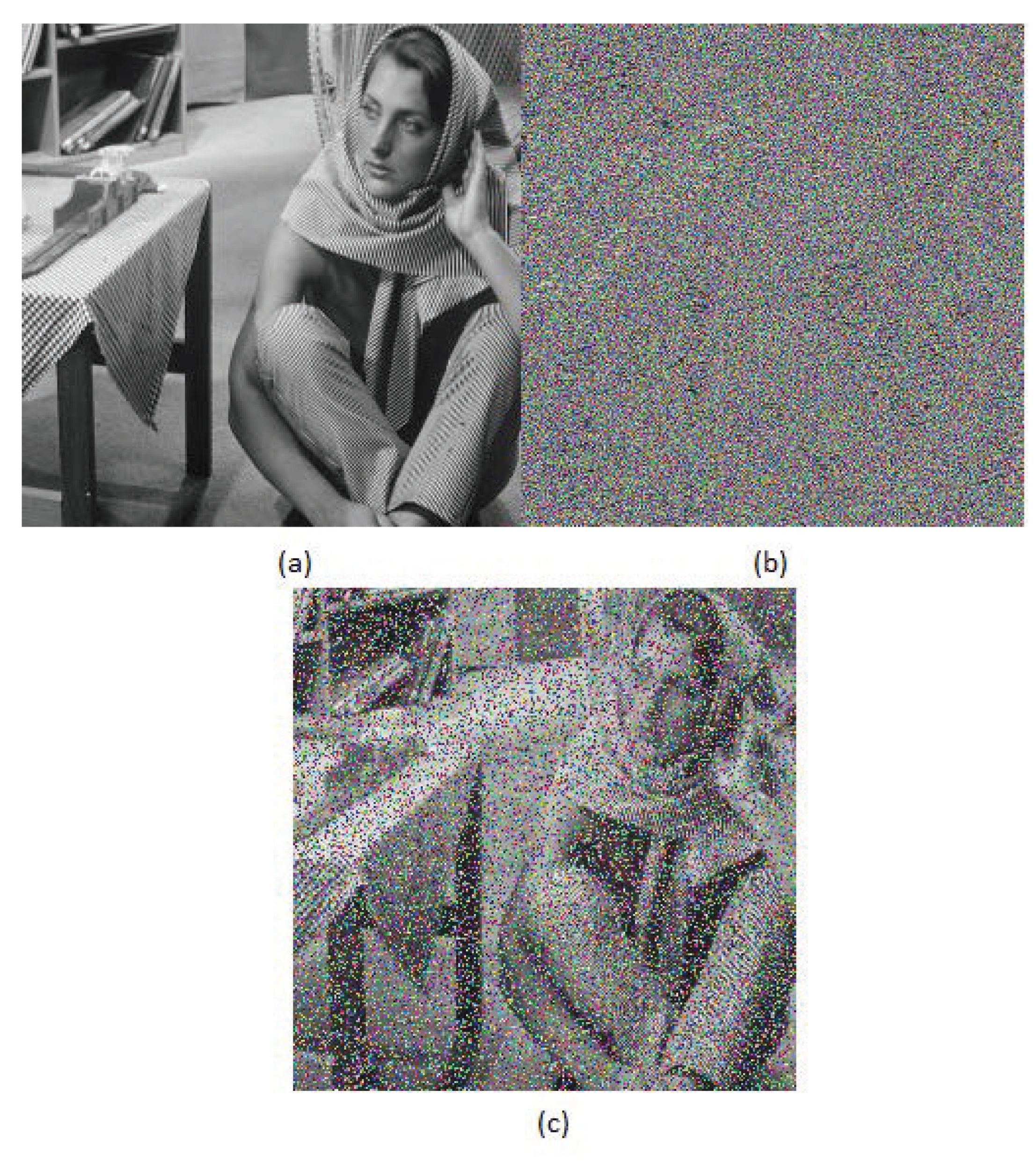
3.6. Images Used to Evaluate ICLEBF
Figure 1 shows the images used in this research to evaluate the encryption quality of the proposed cryptosystem. The size of the images is 512 × 512 pixels, according to the convention used in this kind of research work [
46], although they can be of different dimensions.
The Barbara and Cameraman images (
Figure 1b and
Figure 1d, respectively) are used to test the proposed encryption algorithm because, when using 256-gray-level images, there is a risk of poor-quality encryption if a secret-key cryptosystem is used. In fact, this is why AES is not used as a standard in image encryption, and the AES–CBC [
47] cryptosystem is instead employed. Furthermore, in those images, parts are entirely white, and in the other image, parts are completely black.
On the other hand,
Figure 1a is widely known in the encryption field; the Lena image. Furthermore, in this research, the image of Vicky in
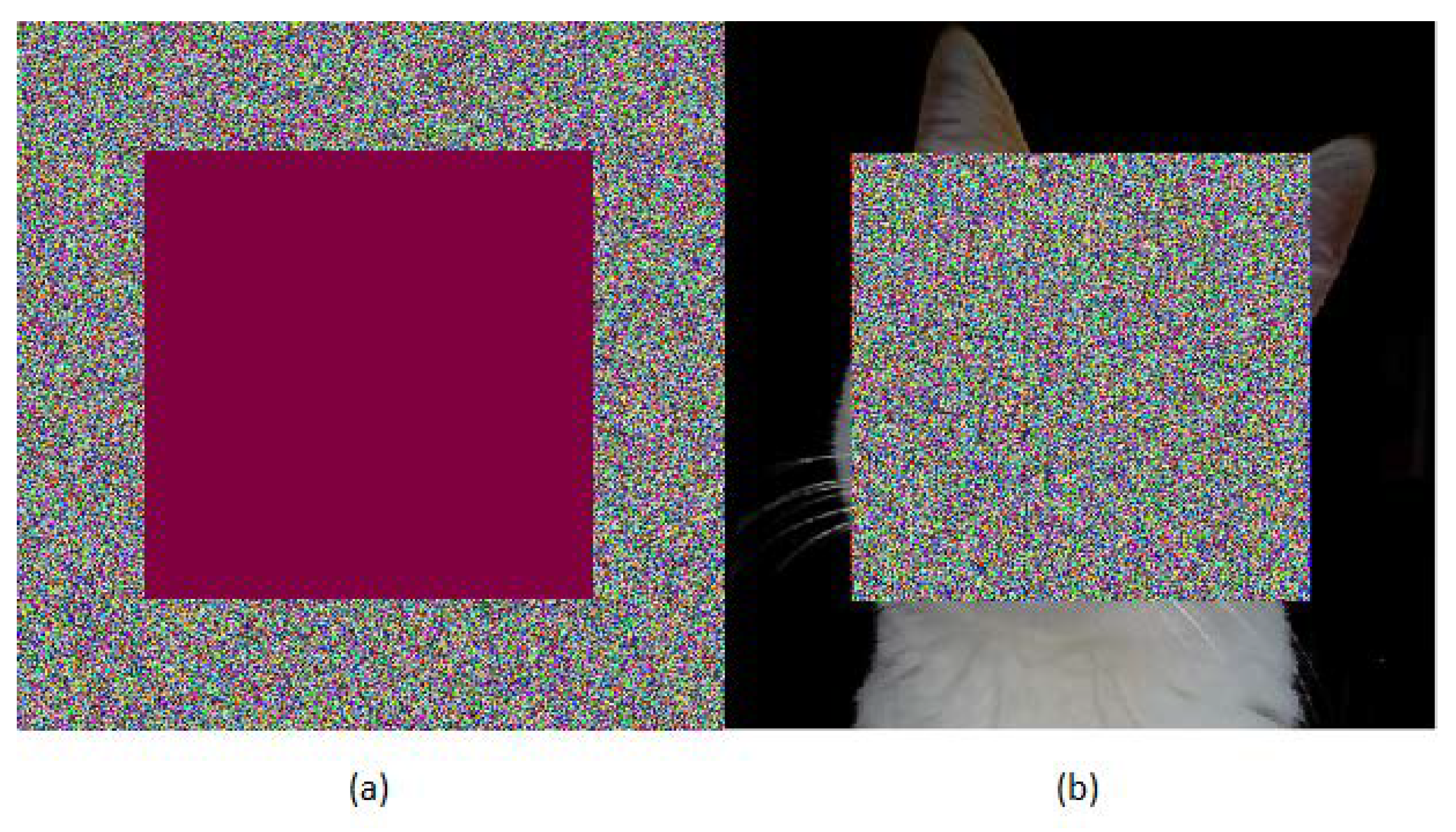
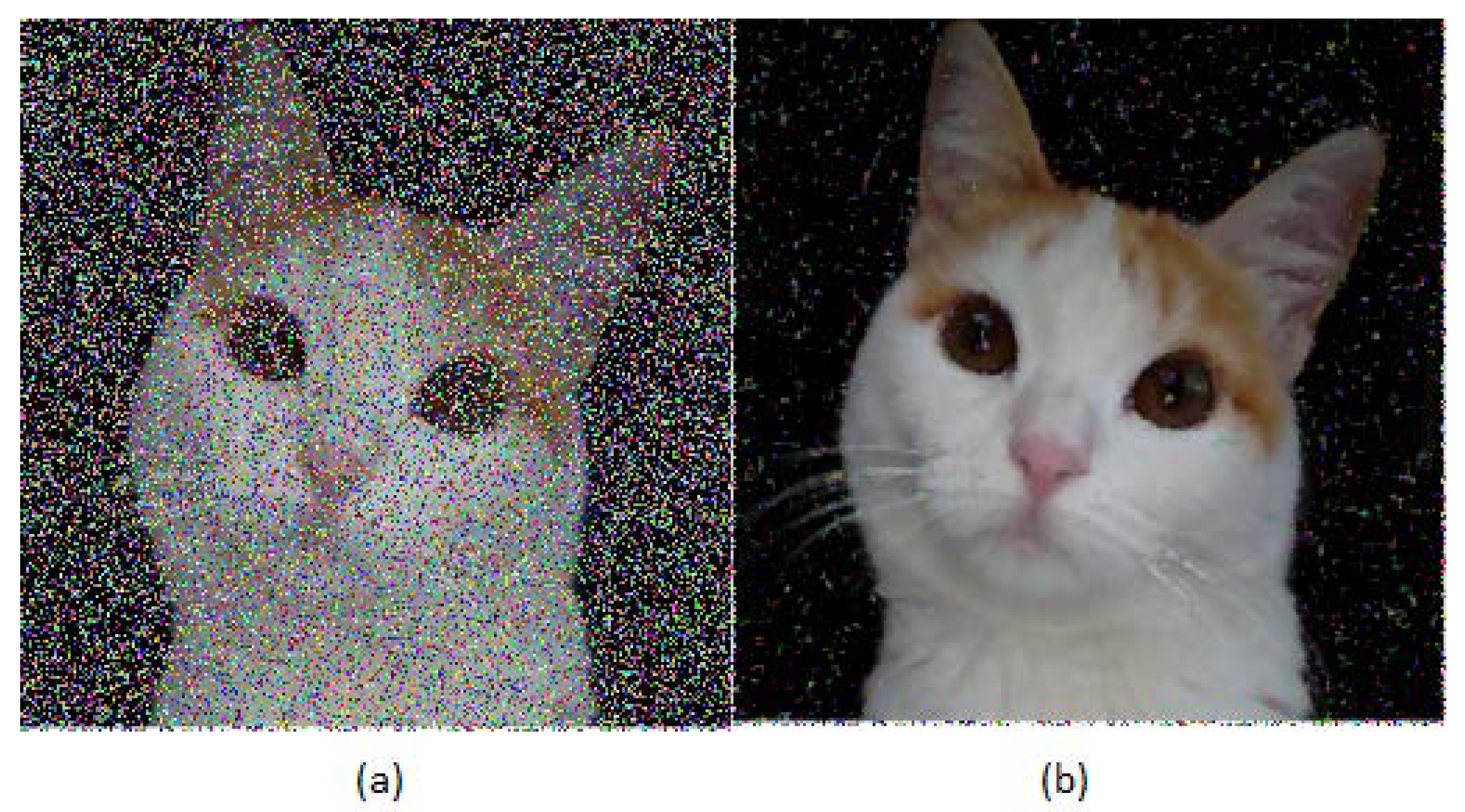
Figure 1c is used, and both images are in color, i.e., the three primary colors appear, red, green, and blue, with 256 levels for each one.
To conclude this section, it is noted that
Figure 1c is encrypted with AES–CBC, and then an occlusion noise damage of 40% of the encrypted figure size is applied. This is later decrypted. The previous result is compared with that obtained when the same procedure is carried out, except that
Figure 1c is now encrypted with the ICLEBF algorithm. Finally, in the “Result” section, the comparison is shown.