Developing a New Collision-Resistant Hashing Algorithm
Abstract
:1. Introduction
- −
- Study the theory of modern hashing algorithms and collision attacks;
- −
- Build a mathematical model of a hash function resistant to collision attacks;
- −
- Perform an analysis of the developed hash function based on statistical methods;
- −
- Implement a data integrity system that is resistant to collision attacks and based on the developed hash function.
2. Materials and Methods
2.1. Description of Hash Function and Collision Attack
2.2. Review of Modern Hashing Algorithms and Collision Attacks
2.3. Related Works
3. Results
3.1. Development of the Collision-Resistant Hashing Algorithm
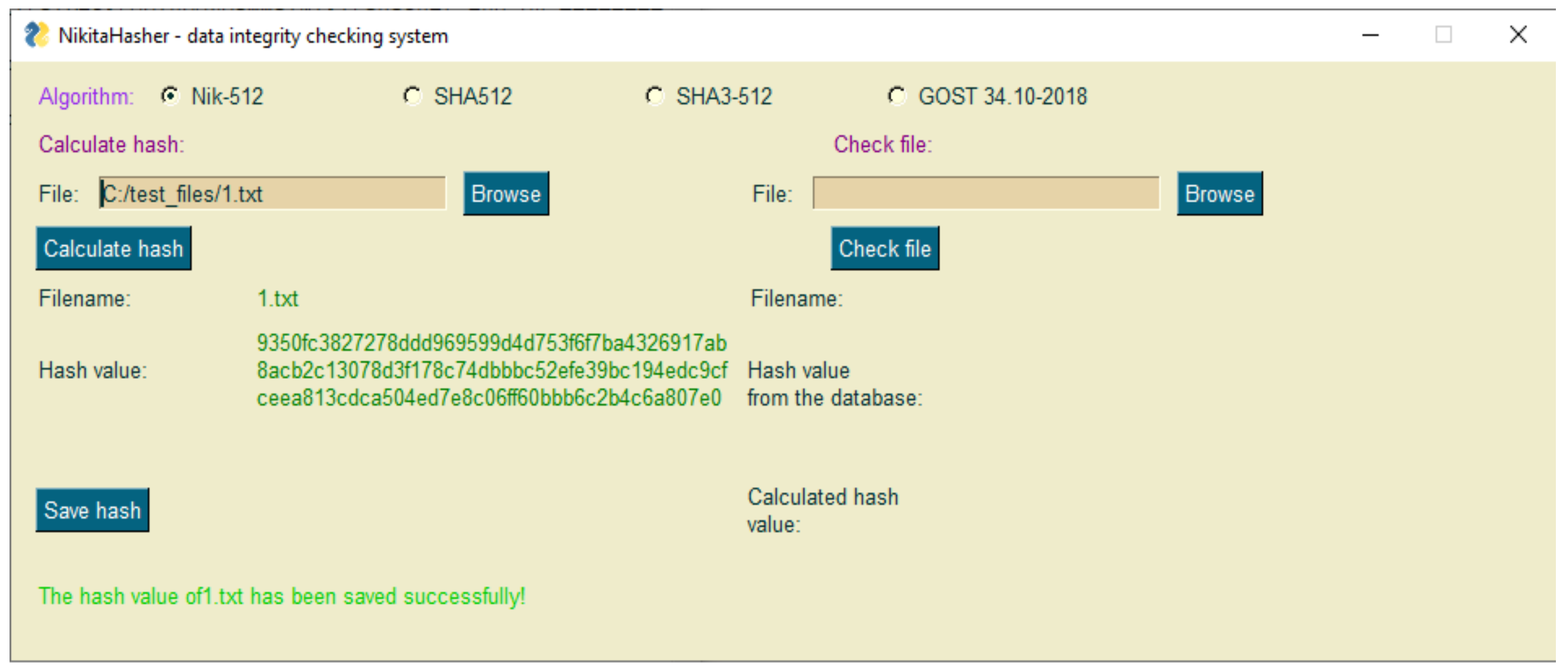
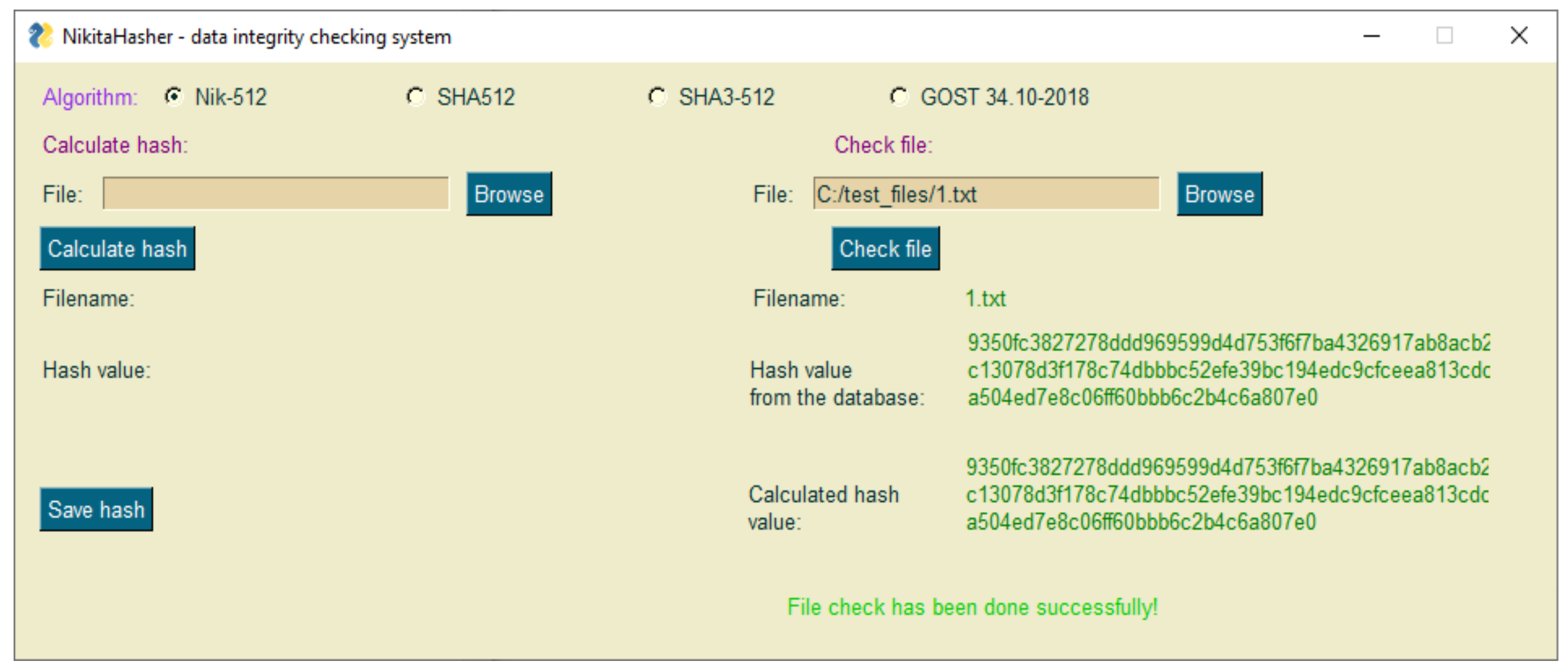
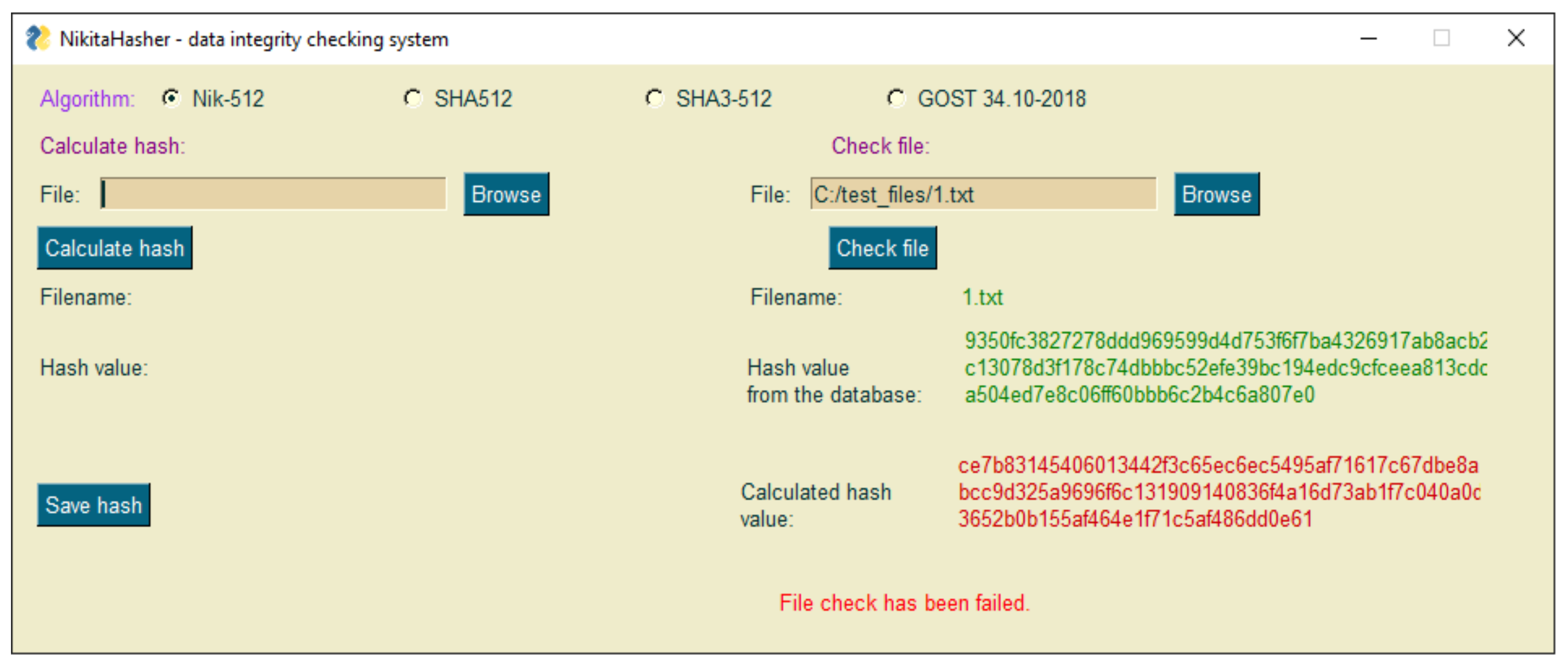
3.2. Demonstration of the Implemented Data Integrity Checking System
4. Discussion
5. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- El-Meligy, N.E.; Diab, T.O.; Mohra, A.S.; Hassan, A.Y.; El-Sobky, W.I. A Novel Dynamic Mathematical Model Applied in Hash Function Based on DNA Algorithm and Chaotic Maps. Mathematics 2022, 10, 1333. [Google Scholar] [CrossRef]
- Torres-Alvarado, A.; Morales-Rosales, L.A.; Algredo-Badillo, I.; López-Huerta, F.; Lobato-Báez, M.; López-Pimentel, J.C. An SHA-3 Hardware Architecture against Failures Based on Hamming Codes and Triple Modular Redundancy. Sensors 2022, 22, 2985. [Google Scholar] [CrossRef] [PubMed]
- Bai, E.; Jiang, X.-Q.; Wu, Y. Memory-Saving and High-Speed Privacy Amplification Algorithm Using LFSR-Based Hash Function for Key Generation. Electronics 2022, 11, 377. [Google Scholar] [CrossRef]
- Gadamsetty, S.; Ch, R.; Ch, A.; Iwendi, C.; Gadekallu, T.R. Hash-Based Deep Learning Approach for Remote Sensing Satellite Imagery Detection. Water 2022, 14, 707. [Google Scholar] [CrossRef]
- Alotaibi, A.S. Biserial Miyaguchi–Preneel Blockchain-Based Ruzicka-Indexed Deep Perceptive Learning for Malware Detection in IoMT. Sensors 2021, 21, 7119. [Google Scholar] [CrossRef] [PubMed]
- Seth, J.N. Practical Cryptography in Python: Learning Correct Cryptography by Example; Apress: Austin, TX, USA, 2019; 380p, ISBN 978-1-4842-4900-0. [Google Scholar]
- Imam, R.; Sumagita, M. Analysis of Secure Hash Algorithm (SHA) 512 for Encryption Process on Web Based Application. Int. J. Cyber-Secur. Digit. Forensics 2018, 7, 373–381. [Google Scholar]
- Stevens, M.; Bursztein, E.; Karpman, P.; Albertini, A.; Markov, Y. The First Collision for Full SHA-1. In Lecture Notes in Computer Science; Springer: Cham, Switzerland, 2017; pp. 570–596. [Google Scholar] [CrossRef] [Green Version]
- Leurent, G.; Peyrin, T. From Collisions to Chosen-Prefix Collisions Application to Full SHA-1. In Advances in Cryptology—EUROCRYPT 2019; Springer: Berlin/Heidelberg, Germany, 2019; pp. 527–555. [Google Scholar] [CrossRef] [Green Version]
- Al-Odat, Z.; Khan, S. Constructions and Attacks on Hash Functions. In Proceedings of the 2019 International Conference on Computational Science and Computational Intelligence (CSCI), Las Vegas, NV, USA, 5–7 December 2019; pp. 139–144. [Google Scholar] [CrossRef]
- Rasjid, Z.E.; Soewito, B.; Witjaksono, G.; Abdurachman, E. A review of collisions in cryptographic hash function used in digital forensic tools. Procedia Comput. Sci. 2017, 116, 381–392. [Google Scholar] [CrossRef]
- Tiwari, H. Merkle-Damgård Construction Method and Alternatives: A Review. J. Inf. Organ. Sci. 2017, 41, 283–304. [Google Scholar] [CrossRef]
- Aumasson, J.P. Serious Cryptography: A Practical Introduction to Modern Encryption; No Starch Press: San Francisco, CA, USA, 2017; 434p, ISBN 978-1-59327-826-7. [Google Scholar]
- Guo, J.; Liao, G.; Liu, G.; Liu, M.; Qiao, K.; Song, L. Practical Collision Attacks against Round-Reduced SHA-3. J. Cryptol. 2020, 33, 228–270. [Google Scholar] [CrossRef]
- Boissier, R.H.; Noûs, C.; Rotella, Y. Algebraic Collision Attacks on Keccak. IACR Trans. Symmetric Cryptol. 2021, 2021, 239–268. [Google Scholar] [CrossRef]
- Al-Odat, Z.; Ali, M.; Khan, S.U. Mitigation and Improving SHA-1 Standard Using Collision Detection Approach. In Proceedings of the 2018 International Conference on Frontiers of Information Technology (FIT), Islamabad, Pakistan, 17–19 December 2018; pp. 333–338. [Google Scholar] [CrossRef]
- Dobraunig, C. Security of the Suffix Keyed Sponge. IACR Trans. Symmetric Cryptol. 2019, 2019, 223–248. [Google Scholar] [CrossRef]
- Stevens, M.; Karpman, P.; Peyrin, T. Freestart Collision for Full SHA-1. In Advances in Cryptology—EUROCRYPT 2016; Springer: Berlin/Heidelberg, Germany, 2016; pp. 459–483. [Google Scholar] [CrossRef] [Green Version]
- Stevens, M. Speeding up detection of SHA-1 collision attacks using unavoidable attack conditions. In Proceedings of the 26th USENIX Security Symposium; Vancouver, BC, Canada, 16–18 August 2017, USENIX: Berkeley, CA, USA, 2017; 19p, ISBN 978-1-931971-40-9. [Google Scholar]
- Hosoyamada, A.; Sasaki, Y. Finding Hash Collisions with Quantum Computers by Using Differential Trails with Smaller Probability than Birthday Bound. In Advances in Cryptology—EUROCRYPT 2020; Springer: Cham, Switzerland, 2020; Volume 12106, pp. 249–279. [Google Scholar] [CrossRef]
- Hosoyamada, A.; Sasaki, Y.; Xagawa, K. Quantum Multicollision-Finding Algorithm. In Advances in Cryptology—ASIACRYPT 2017; Springer: Cham, Switzerland, 2017; pp. 179–210. [Google Scholar] [CrossRef]
- Mittelbach, A. The Theory of Hash Functions and Random Oracles; Springer Nature Switzerland: Cham, Switzerland, 2021; 780p, ISBN 978-3-030-63287-8. [Google Scholar]
- Chailloux, A.; Naya-Plasencia, M.; Schrottenloher, A. An Efficient Quantum Collision Search Algorithm and Implications on Symmetric Cryptography. In Advances in Cryptology—ASIACRYPT 2017; Springer: Cham, Switzerland, 2017; pp. 211–240. [Google Scholar] [CrossRef]
- Hosoyamada, A.; Sasaki, Y. Quantum Collision Attacks on Reduced SHA-256 and SHA-512. In Advances in Cryptology—CRYPTO 2021; Springer: Cham, Switzerland, 2021; pp. 616–646. [Google Scholar] [CrossRef]
- Sakan, K.; Nyssanbayeva, S.; Kapalova, N.; Algazy, K.; Khompysh, A.; Dyusenbayev, D. Development and analysis of the new hashing algorithm based on block cipher. Eastern-European J. Enterp. Technol. 2022, 2, 60–73. [Google Scholar] [CrossRef]
- Tutueva, A.V.; Karimov, A.I.; Moysis, L.; Volos, C.; Butusov, D.N. Construction of one-way hash functions with increased key space using adaptive chaotic maps. Chaos Solitons Fractals 2020, 141, 110344. [Google Scholar] [CrossRef]
- Wang, Y.; Chen, L.; Wang, X.; Wu, G.; Yu, K.; Lu, T. The design of keyed hash function based on CNN-MD structure. Chaos Solitons Fractals 2021, 152, 111443. [Google Scholar] [CrossRef]
- Da Silva, E.V. Viktoria: A New Architecture for Hash Functions. In Proceedings of the Future Technologies Conference (FTC), Vancouver, BC, Canada, 28–29 November; Springer: Cham, Switzerland, 2021; Volume 3, pp. 251–271. [Google Scholar] [CrossRef]
- Thanalakshmi, P.; Anitha, R.; Anbazhagan, N.; Park, C.; Joshi, G.P.; Seo, C. A Hash-Based Quantum-Resistant Designated Verifier Signature Scheme. Mathematics 2022, 10, 1642. [Google Scholar] [CrossRef]



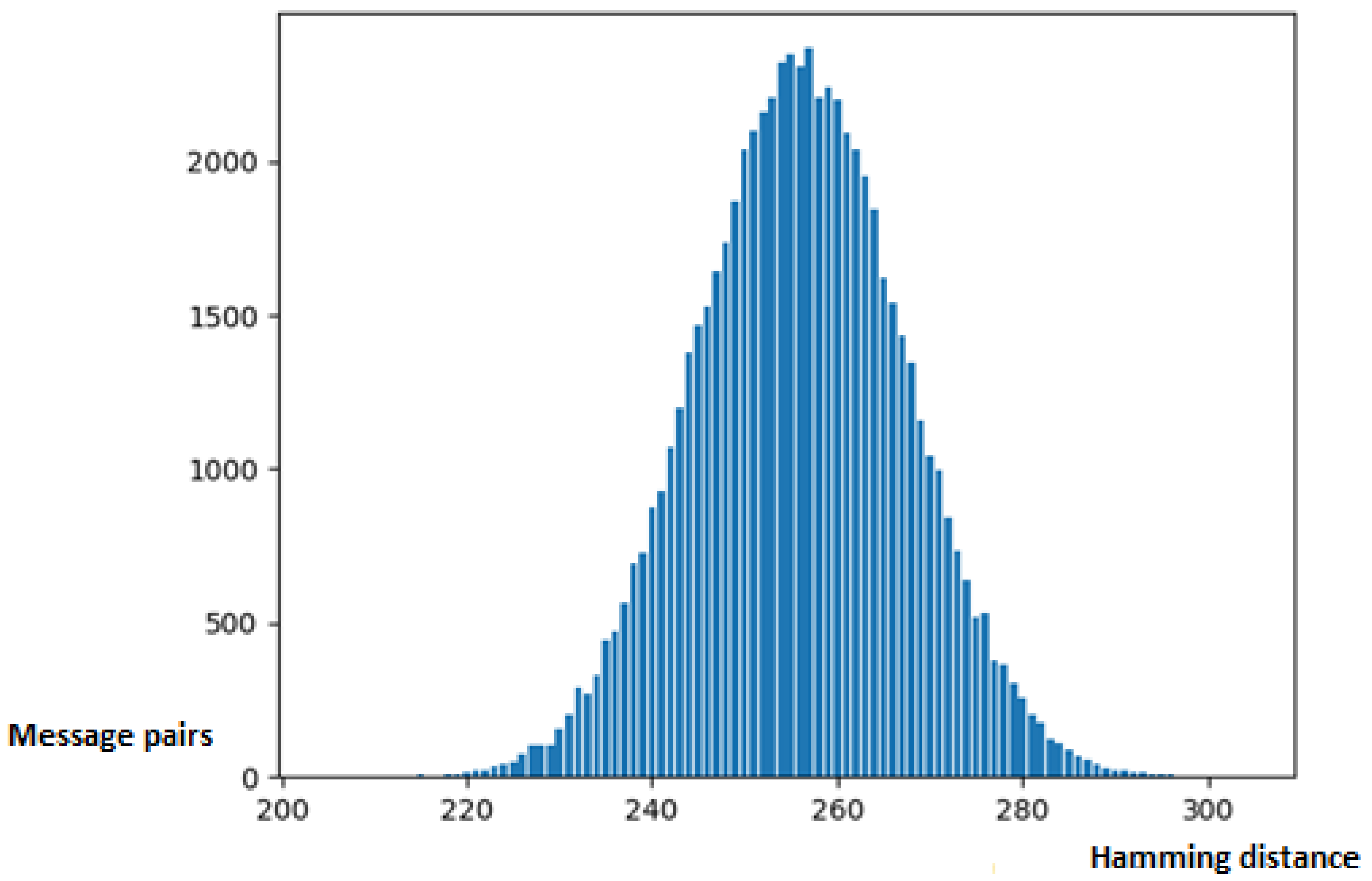
| Hash Function | Absolute Difference between the Expected Value (256) and the Average Hamming Distance | Standard Deviation of the Hamming Distance |
|---|---|---|
| SHA512 | 0.3786 | 11.3647 |
| SHA3-512 | 0.4921 | 11.3451 |
| ΓOCT 34.11–2018 | 0.4515 | 11.2974 |
| Nik-512 | 0.0467 | 11.2951 |
| SHA-2 | SHA-3 | GOST 34.11-2018 | Whirlpool | Nik-512 | Vulnerable (SHA-1, MD-5) | |
|---|---|---|---|---|---|---|
| HashGenerator | + | + | − | − | − | + |
| HashMyFiles | + | + | − | − | − | + |
| HashTab | + | + | − | + | − | + |
| QuickHash | + | − | − | − | − | + |
| MultiHasher | + | − | − | − | − | + |
| NikitaHasher | + | + | + | − | + | − |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Cherckesova, L.V.; Safaryan, O.A.; Lyashenko, N.G.; Korochentsev, D.A. Developing a New Collision-Resistant Hashing Algorithm. Mathematics 2022, 10, 2769. https://doi.org/10.3390/math10152769
Cherckesova LV, Safaryan OA, Lyashenko NG, Korochentsev DA. Developing a New Collision-Resistant Hashing Algorithm. Mathematics. 2022; 10(15):2769. https://doi.org/10.3390/math10152769
Chicago/Turabian StyleCherckesova, Larissa V., Olga A. Safaryan, Nikita G. Lyashenko, and Denis A. Korochentsev. 2022. "Developing a New Collision-Resistant Hashing Algorithm" Mathematics 10, no. 15: 2769. https://doi.org/10.3390/math10152769
APA StyleCherckesova, L. V., Safaryan, O. A., Lyashenko, N. G., & Korochentsev, D. A. (2022). Developing a New Collision-Resistant Hashing Algorithm. Mathematics, 10(15), 2769. https://doi.org/10.3390/math10152769





