A Methodological Framework for the Risk Assessment of Drone Intrusions in Airports
Abstract
1. Introduction
- support the assessment of the risks related to unauthorized drones;
- mitigate risks from unauthorized drone use;
- implement counter-drone measures from a global safety perspective.
- a vulnerability index to quantitatively assess the susceptibility of the airport to drone intrusions, based on reference datasets;
- a set of event trees to quantitatively assess the risks of the different threat scenarios related to drone intrusions, based on the airport’s vulnerability index.
2. Related Work
3. Risk Assessment Framework for Drone Intrusions in Airports
3.1. Problem Statement
- a methodological framework, in the sense of a sequence of steps to complete the assessment procedure;
- unified, in the sense of a safety–security-integrated approach.
- It shall be applicable to a great variety of airports, considering their characteristics;
- It shall support at least a semi-quantitative evaluation of risks, integrating the evaluation with mitigation actions and information about degraded performances in threat scenarios;
- It shall use formalisms that may be easily understood by stakeholders;
- It shall support (possibly automated) what-if analyses for the computation of qualitative/quantitative values of interest about risk-related figures and performance metrics;
- It shall allow a reuse across multiple systems and objects (e.g., different airports, different airport assets, different drone models, etc.);
- It shall effectively consider possible historical or statistical data (if available) about drone intrusions at a local level (i.e., for the specific airport) or at an aggregated level (i.e., for a specific region or State).
3.2. Approach
- model-based, since it applies modelling techniques for the specification of the reference aspects of the target system, e.g., failure-oriented behaviors, success-oriented behaviors;
- data-driven, since it exploits available datasets for the characterization of the susceptibility of an airport with respect to the phenomenon of drone intrusions.
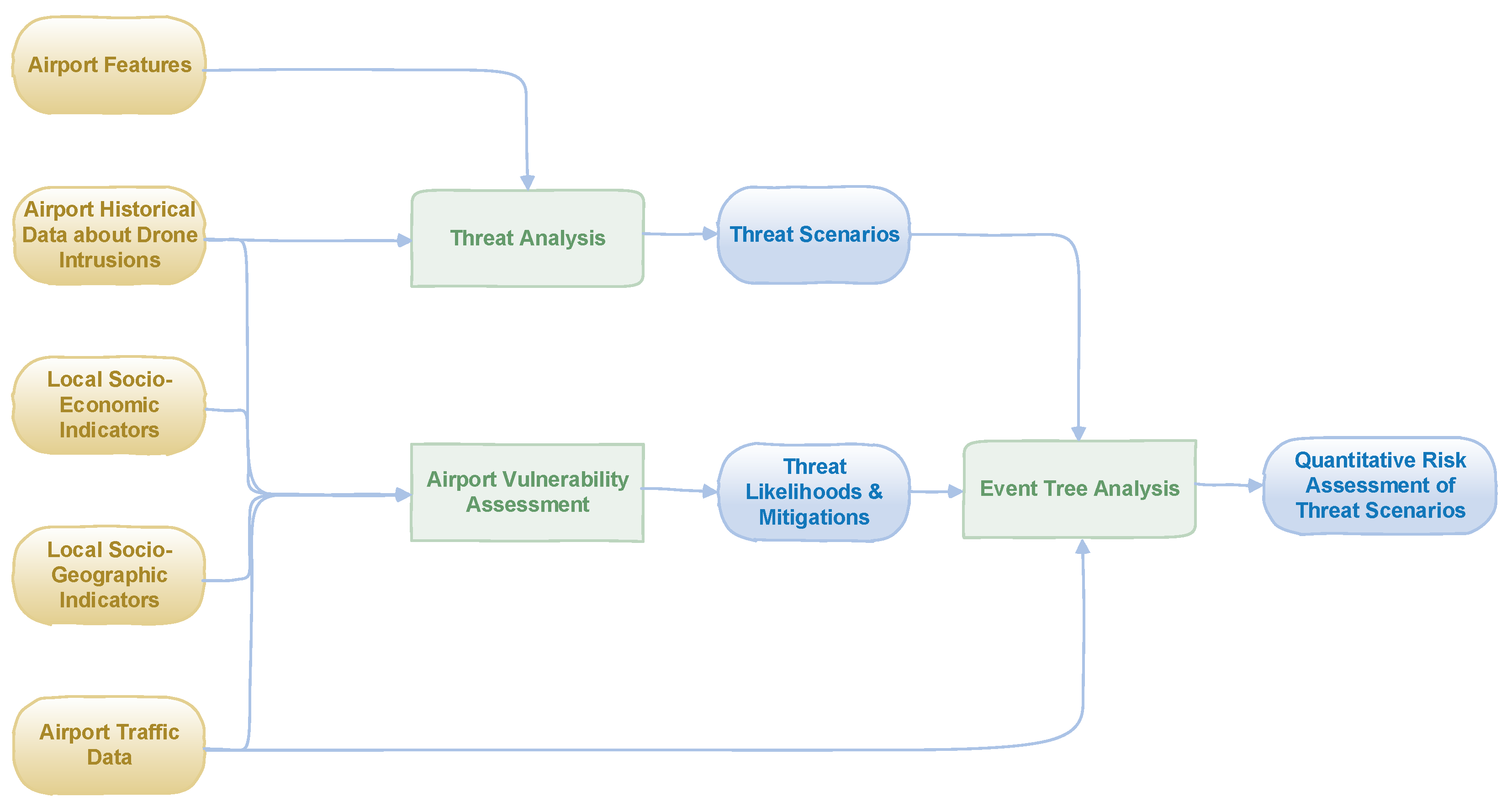
- input data (yellow blocks);
- activities (green blocks);
- outcomes (blue blocks), in terms of both intermediate and final outcomes.
- Threat analysis. This activity aims at identifying the possible threats and the related threat scenarios about airport drone intrusions, considering both safety-related (i.e., accidental) and security-related (i.e., malicious) intrusions. It is possibly fed by historical data about intrusions. It is performed by exploiting a detailed analysis of the reference airport, for example, considering the configuration of the following assets: runways, terminals (both passenger and cargo), taxiways, traffic control tower, aircraft hangars, aprons, communication, navigation and surveillance (CNS) systems, etc. Clearly, general features of possible intruding drones (e.g., maximum speed, mass, endurance, radio coverage, etc.) should be used as a reference for the analysis. For the purposes of the methodological framework, a threat is any unauthorized flight activity of a drone in the airspace or in the vicinity of an airport. Note that this choice is in line with EASA guidelines [7]. Then, threat scenarios are inferred by considering the possible physical interference of an intruder drone with respect to a given airport’s asset. In principle, such behavior may be traced to two main classes of drone’s interference: (i) fly-by and (ii) collision. In detail, given an airport’s asset: (i) the fly-by refers to the proximal presence of a drone, wherein proximal means at a distance less than a specific threshold or inside an airspace (typically centered on the asset) with an agreed shape; (ii) the collision refers to the crash of the drone with the asset, usually implying a damage to the asset according to the kinetic energy of the drone itself. Note that these main classes may be further split in sub-classes, for example: different proximity thresholds for the fly-by, which can lead to different interferences of the drone; different categories of collision according to its kinetic energy, which can lead to different damage levels; etc. All these sub-classes are associated with specific threat scenarios. In the case of fly-by, examples of threat scenarios are: unauthorized operations of a drone in the arrival path of a runway; unauthorized operations of a drone in the departure path of a runway; unauthorized operations of a drone in proximity of boarding/de-boarding passengers; unauthorized operations of a drone affecting an aircraft on the ground; unauthorized operations of a drone affecting the air traffic tower; etc.
- Airport vulnerability assessment. This activity aims at evaluating an Airport Vulnerability Index (AVI) to quantify the exposure or susceptibility of an airport with respect to drone intrusions [10]. Such index may be assessed by explicitly considering the influence of different dimensions of the airport’s context (e.g., social, economic, etc.). Thus, the AVI may be used to provide estimations and predictions about drone intrusions in an airport, based on the exposure of the airport itself.
- Event Tree Analysis (ETA). This activity aims at providing a quantitative assessment of the risk associated with each threat scenario by means of event trees. Indeed, event trees help to assess the acceptability of a risk related with a threat scenario fired by a drone interference (fly-by or collision) with an airport’s asset.
- may implicitly manage different airports or different airport aggregations (i.e., at a region level or State level), considering their specific features by means of the input data (yellow blocks in Figure 1);
- delivers a qualitative and quantitative assessment of risk levels for each threat scenario (considering the possible presence of mitigation means in both AVI and ETA), whereas threat analysis is on a qualitative basis (i.e., it is performed by means of the experience of human assessors);
- exploits event trees, which are commonly used for risk analysis;
- may provide what-if analyses, based on the tuning of input data (yellow blocks in Figure 1);
- effectively considers different airports, assets, drone models, etc., based on the identified threat scenarios;
- considers the airport’s historical data about drone intrusions as an essential input for the risk assessment.
4. Airport Vulnerability Assessment
- compare the vulnerability of different systems and communities;
- compare different policies or options of the same system;
- evaluate potential complications for recovery planning in case of occurrence of the feared event.
- the drone-intrusion likelihood;
- the drone-intrusion mitigation.
- is the likelihood function of a drone intrusion in the reference airport;
- is the mitigation function of a drone intrusion in the reference airport;
- is the combination function of the likelihood and the mitigation, and quantifies the exposure of the airport in regard to drone intrusions.
- is the reference State;
- is the estimator of the number of drone intrusions for the airports in the reference State ;
- is the population of the reference State ;
- is the number of officially registered drones in the reference State .
- is the reference year;
- , , and , respectively, represent the yearly estimated number of airport drone intrusions, the population and the number of registered drones in the State for the year .
- the correlation fitting between the population and the number of drone sightings in 2020 for each FAA’s State;
- the correlation fitting between the number of registered drones and the number of drone sightings in 2020 for each FAA’s State.
- ;
- ;
- .
- an estimator according to the population is reasonable and effective to assess the yearly number of a drone intrusions in the airports of a given State;
- the population may be considered as a proper influence variable in regard to the drone-intrusion likelihood and the drone-intrusion exposure.
5. Event Tree Analysis
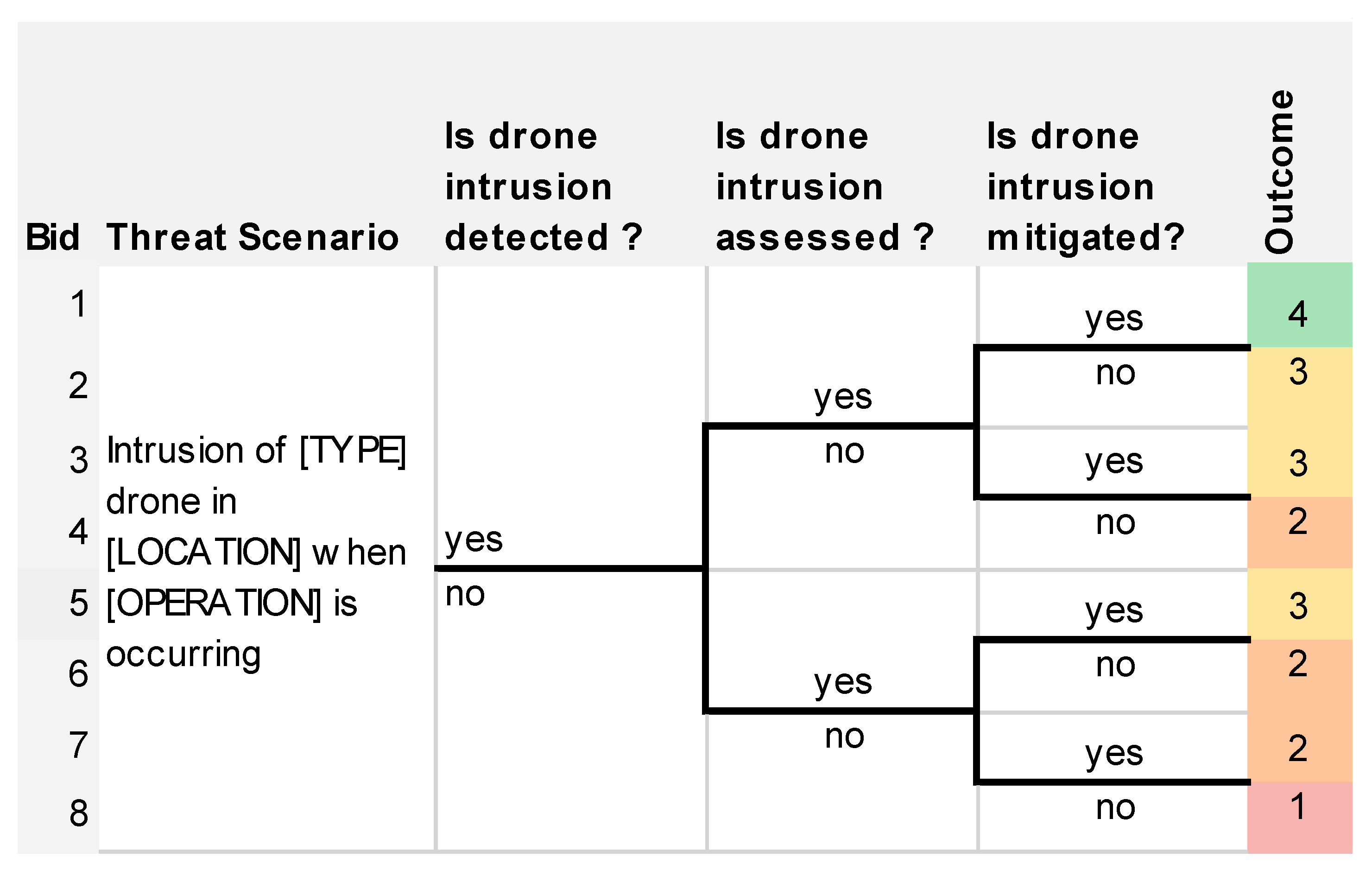
- “Threat scenario”. The second column of the table describes the threat scenario that is analyzed: the TYPE of drones refers to authorized, off-nominal, or unauthorized drone operations; LOCATION refers to a specific place in or near the airport such as the runway, the taxiway, the departure, or arrival paths; and OPERATION refers to the affected airport operation by the intrusion such as aircraft landing, aircraft taxi, aircraft passenger boarding, etc.
- “Is drone intrusion detected?”, “Is drone intrusion assessed?”, “Is drone intrusion mitigated?”. The three following columns describe the answers to questions about the efficiency of the three main technical capabilities of a system protecting airport against drones: the capability to detect, identify, and track a drone; the capability to assess whether a detected drone could cause a risk and decide the best mitigations to be undertaken; and the capability to mitigate a drone threat.
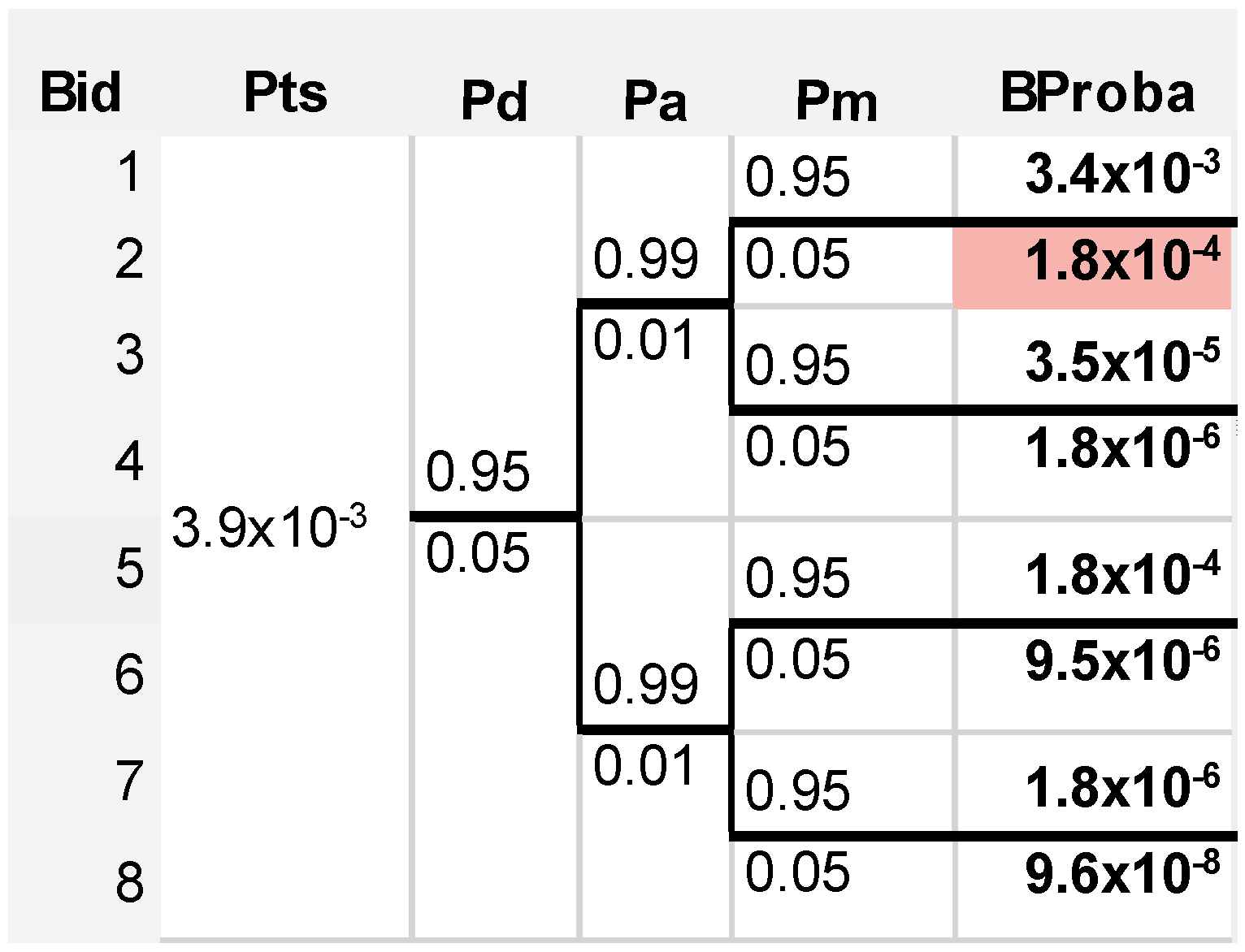
- “Bid”. The first column provides branch identifiers. Branch 1 describes a best-case situation where all three technical capabilities efficiently manage the drone intrusion whereas branch 8 is the worst-case situation where none of three technical capabilities are working efficiently. In the latter case, only non-technical means could be used to protect the airport against drones.
- “Outcome”. The last column describes the safety and operational outcome of the branch.
- Outcome 1. The threat scenario causes a catastrophic safety effect or a severe interruption to airport operations.
- Outcome 2. The threat scenario causes a hazardous safety effect as severe injuries or a major interruption to airport operations.
- Outcome 3. The threat scenario causes a major safety effect as light injuries or a moderate interruption to airport operations.
- Outcome 4. The threat scenario causes a minor safety effect as passenger discomfort or a small interruption to airport operations.
- Outcome 5. The threat scenario does not affect safety or the airport operations.
- , the probability of the threat scenario;
- , the probability of efficient detection (or , the probability of non-efficient detection);
- , the probability of efficient assessment (or , the probability of non-efficient assessment);
- , the probability of efficient mitigation (or , the probability of non-efficient mitigation).
6. Case Study
6.1. Available Data
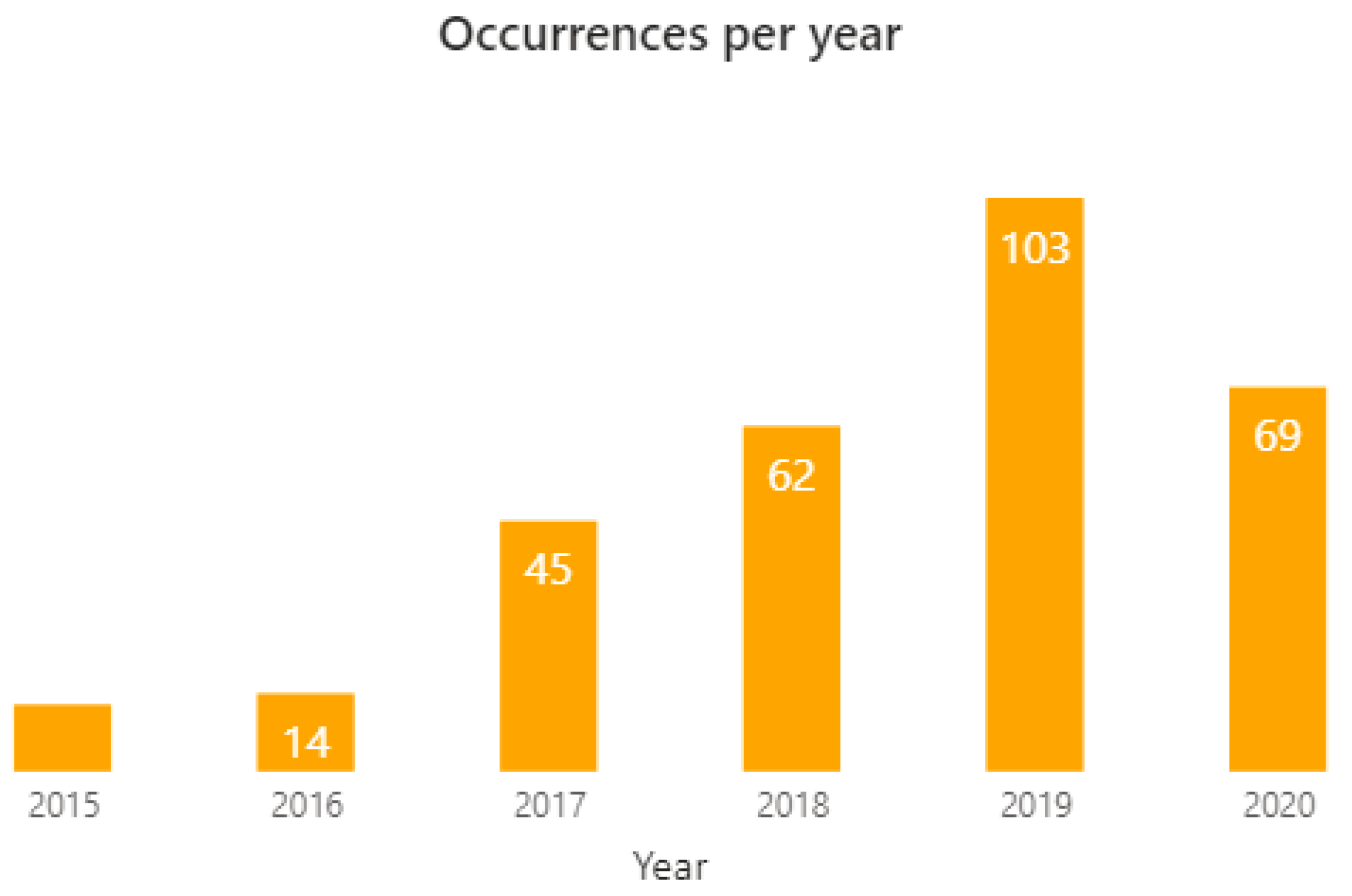
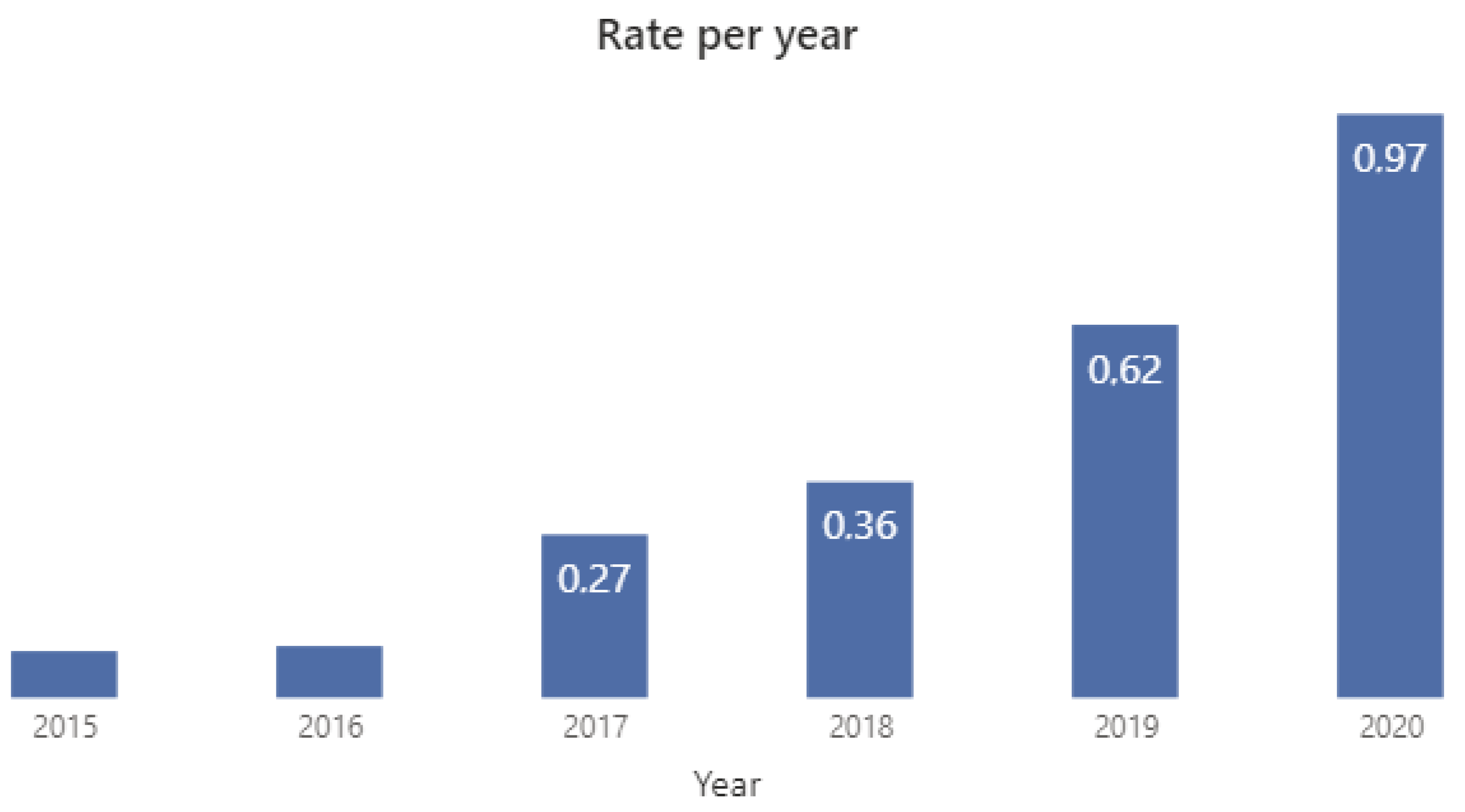
6.1.1. Drone Intrusion Data
6.1.2. Airport Movement Data
6.1.3. Data about the Efficiency of Technical Means
6.2. Results about Airport Vulnerability Index
- is the estimator of the number of drone intrusions in the Italian airports for the year ;
- is the total number of drones in Italy for the year ;
- is the number of airport movements in Italy for the year .
- the number of drones is evaluated by multiplying the number of drone operators by two;
- the number of drones in the previous years is evaluated with the same approach in [10], i.e., by considering a linear incremental factor according to the market trends and by using a trend of +7% per year.
- ;
- .
- The number of drones in Italy in 2021. For this input, the value of has been computing with the previous approach, i.e., by considering a trend of +7% per year.
- The number of movements of Italian airport in 202. This input has been evaluated by using the EUROCONTROL’s measurement of traffic variation between 2020 and 2021 [39]. Such measurement reports a variation of +29% in regard to the traffic level of Italy. Thus, the number of movements in 2021 has been predicted starting from the available data about the number of movements in 2020 (703,751) and by applying a growth factor of 29%.
- The number of drones influencing LIMC in 2021. This input has been evaluated by assuming that the number of drone operators and the number of drones in a region are proportional to the population of the region. Thus, the percentage of the Italian population living in Lombardy (16.3%) has been applied to evaluate the number of drones in Lombardy in 2021, starting from the national number.
- The number of movements of LIMC in 2021. This input has been evaluated by using the ratio between the number of movements of Milan Malpensa and the total number of airport movements in Italy in 2020, which is 13.13%.
6.3. Results about Event Tree Analysis
7. Discussion
- the type of airport;
- the airport’s traffic complexity;
- the unmanned traffic (if any);
- the meteorological conditions and the season;
- the counter-drone solutions in the airport (if any);
- the legal framework for drones in the country of the airport.
- to decrease the probability of the branch by decreasing the probability of its events (this means improving the efficiency of technical means); or
- to reduce the safety and operational outcome of the branch, for instance by introducing specific operational procedures to mitigate the impact of the related risk scenario.
8. Conclusions
Author Contributions
Funding
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- European Commission (EC). Consolidated text: COMMISSION IMPLEMENTING REGULATION (EU) 2019/947 of 24 May 2019 on the rules and procedures for the operation of unmanned aircraft. Off. J. Eur. Union 2019, L152, 45–71. [Google Scholar]
- European Commission (EC). COMMISSION DELEGATED REGULATION (EU) 2019/945 of 12 March 2019 on unmanned aircraft systems and on third-country operators of unmanned aircraft systems. Off. J. Eur. Union 2019, L152, 1–40. [Google Scholar]
- European Commission (EC). COMMISSION IMPLEMENTING REGULATION (EU) 2021/664 of 22 April 2021 on a regulatory framework for the U-space. Off. J. Eur. Union 2021, L139, 161–183. [Google Scholar]
- CORUS Consortium. U-Space Concept of Operations; CORUS Project, EU Contract No 763551, Deliverable D6.3, Edition 03.00.02; SESAR Joint Undertaking: Brussels, Belgium, 2019. [Google Scholar]
- European Union Aviation Safety Agency (EASA). Drone Incident Management at Aerodromes. Part 1: The Challenge of Unauthorised Drones in the Surroundings of Aerodromes; EASA: Cologne, Germany, 2021.
- European Union Aviation Safety Agency (EASA). Drone Incident Management at Aerodromes. Part 2: Guidance and Recommendations; EASA: Cologne, Germany, 2021.
- European Union Aviation Safety Agency (EASA). Drone Incident Management at Aerodromes. Part 3: Resources and Practical Tools; EASA: Cologne, Germany, 2021.
- Shelley, A. Drone Registration Will Not Prevent Another Gatwick. SSRN 2019. [Google Scholar] [CrossRef]
- Wendt, P.; Voltes-Dorta, A.; Suau-Sanchez, P. Estimating the costs for the airport operator and airlines of a drone-related shutdown: An application to Frankfurt international airport. J. Transp. Secur. 2020, 13, 93–116. [Google Scholar] [CrossRef]
- Pascarella, D.; Gigante, G.; Nebula, F.; Vozella, A.; Redondo de la Mata, E.; Jiménez Roncero, F.J.; Martinavarro, E. Historical Data Analysis and Modelling for Drone Intrusions in Airports. In Proceedings of the 2021 13th International Conference on Electronics, Computers and Artificial Intelligence (ECAI), Pitesti, Romania, 1–3 July 2021; pp. 1–8. [Google Scholar] [CrossRef]
- European Union Aviation Safety Agency (EASA). The European Plan for Aviation Safety (EPAS 2021-2025), Volume I: Introduction and Strategy; EASA: Cologne, Germany, 2020.
- ASPRID (Airport System PRotection from Intruding Drones) Project. Available online: https://www.asprid.eu/ (accessed on 9 September 2022).
- Ericson II, C.A. Concise Encyclopedia of System Safety: Definition of Terms and Concepts; John Wiley & Sons, Inc.: Hoboken, NJ, USA, 2011. [Google Scholar]
- Kumpulainen, S. Vulnerability concepts in hazard and risk assessment. Natural and Technological Hazards and Risks Affecting the Spatial Development of European Regions. Geol. Surv. Finl. 2006, 42, 65–74. [Google Scholar]
- Maragakis, I.; Clark, S.; Piers, M.; Prior, D.; Tripaldi, C.; Masson, M.; Audard, C. European Civil Aviation Safety Team (ECAST)—Safety Management System and Safety Culture Working Group (SMS WG)—Guidance on Hazards Identification. March 2009. Available online: https://www.easa.europa.eu/sites/default/files/dfu/WP1-ECASTSMSWG-SafetyCultureframework1.pdf (accessed on 15 October 2022).
- European Union Agency for Cybersecurity (ENISA)—Glossary Published under Risk Management. Available online: https://www.enisa.europa.eu/topics/threat-risk-management/risk-management/current-risk/risk-management-inventory/glossary (accessed on 9 September 2022).
- le Fevre, M.; Gölz, B.; Flohr, R.; Stelkens-Kobsch, T.; Verhoogt, T. SecRAM 2.0 Security Risk Assessment Methodology for SESAR 2020; 02.00.00; SESAR Joint Undertaking: Brussels, Belgium, 2017. [Google Scholar]
- Kriaa, S.; Pietre-Cambacedes, L.; Bouissou, M.; Halgand, Y. A survey of approaches combining safety and security for industrial control systems. Reliab. Eng. Syst. Saf. 2015, 139, 156–178. [Google Scholar] [CrossRef]
- Abdo, H.; Kaouk, M.; Flaus, J.-M.; Masse, F. A safety/security risk analysis approach of industrial control systems: A cyber bowtie—Combining new version of attack tree with bowtie analysis. Comput. Secur. 2017, 72, 175–195. [Google Scholar] [CrossRef]
- ISO 31000:2018; Risk Management—Guidelines. International Organization for Standardization (ISO): Geneva, Switzerland, 2018.
- ISO/IEC 27005:2018; Information Technology—Security Techniques—Information Security Risk Management. International Organization for Standardization (ISO)/International Electrotechnical Commission (IEC): Geneva, Switzerland, 2018.
- International Civil Aviation Organization (ICAO). Doc 9859—Safety Management Manual (SMM), 4th ed.; ICAO: Montreal, QC, Canada, 2018. [Google Scholar]
- International Civil Aviation Organization (ICAO). Doc 8973—Restricted—Aviation Security Manual, 12th ed.; ICAO: Montreal, QC, Canada, 2020. [Google Scholar]
- Rabiller, B.; Fota, N.; Carbo, L. SESAR Safety Reference Material; 00.04.01; EUROCONTROL: Brussels, Belgium, 2018.
- National Safe Skies Alliance. Recommended Security Guidelines for Airport Planning, Design, and Construction; Program for Applied Research in Airport Security (PARAS). PARAS 0004; Transportation Security Administration: Springfield, VA, USA, 2017.
- U.S. Department of Homeland Security. Security Guidelines for General Aviation Airport Operators and Users; U.S. Department of Homeland Security: Washington, DC, USA, 2021.
- SATIE (Security of Air Transport Infrastructure of Europe) Project. Available online: https://satie-h2020.eu/ (accessed on 9 September 2022).
- Borener, S.S.; Guzhva, V.S.; Crook, I.; Fraga, R. Safety Assessment of Implemented NextGen Operational Improvements. Transp. Res. Procedia 2016, 14, 3731–3740. [Google Scholar] [CrossRef]
- Pyrgies, J. The UAVs threat to airport security: Risk analysis and mitigation. J. Airl. Airpt. Manag. 2019, 9, 63–96. [Google Scholar] [CrossRef]
- Lykou, G.; Moustakas, D.; Gritzalis, D. Defending Airports from UAS: A Survey on Cyber-Attacks and Counter-Drone Sensing Technologies. Sensors 2020, 20, 3537. [Google Scholar] [CrossRef] [PubMed]
- Castrillo, V.U.; Manco, A.; Pascarella, D.; Gigante, G. A Review of Counter-UAS Technologies for Cooperative Defensive Teams of Drones. Drones 2022, 6, 65. [Google Scholar] [CrossRef]
- Kang, H.; Joung, J.; Kim, J.; Kang, J.; Cho, Y.S. Protect Your Sky: A Survey of Counter Unmanned Aerial Vehicle Systems. IEEE Access 2020, 8, 168671–168710. [Google Scholar] [CrossRef]
- Sampigethaya, K.; Kopardekar, P.; Davis, J. Cyber security of unmanned aircraft system traffic management (UTM). In Proceedings of the 2018 Integrated Communications, Navigation, Surveillance Conference (ICNS), Herndon, VA, USA, 10–12 April 2018; pp. 1C1-1–1C1-15. [Google Scholar] [CrossRef]
- Federal Aviation Administration (FAA)—UAS Sightings Report. Available online: https://www.faa.gov/uas/resources/public_records/uas_sightings_report (accessed on 9 September 2022).
- Steiner, M.; Deierling, W.; Johnson, D. Lightning safety at airports—Material for thunder. In Proceedings of the 3rd WMO/WWRP International Symposium on Nowcasting and Very Short Range Forecasting, Rio de Janeiro, Brazil, 6–10 August 2012. [Google Scholar]
- EUROCONTROL—Public Airport Corner. Available online: https://ext.eurocontrol.int/airport_corner_public/ (accessed on 9 September 2022).
- Svanström, F.; Englund, C.; Alonso-Fernandez, F. Real-Time Drone Detection and Tracking With Visible, Thermal and Acoustic Sensors. In Proceedings of the 25th International Conference on Pattern Recognition (ICPR), Milan, Italy, 10–15 January 2021; pp. 7265–7272. [Google Scholar] [CrossRef]
- Kouhestani, C.; Woo, B.; Birch, G. Counter unmanned aerial system testing and evaluation methodology. In Proceedings of the SPIE 10184, Sensors, and Command, Control, Communications, and Intelligence (C3I) Technologies for Homeland Security, Defense, and Law Enforcement Applications XVI, Anaheim, CA, USA, 9–13 April 2017; Volume 1018408. [Google Scholar] [CrossRef]
- EUROCONTROL—EUROCONTROL Comprehensive Assessment, COVID 19 Impact on European Aviation. Available online: https://www.eurocontrol.int/sites/default/files/2021-07/covid19-eurocontrol-comprehensive-air-traffic-assessment-08072021.pdf (accessed on 9 September 2022).









| Term | Description | Reference |
|---|---|---|
| Vulnerability | A weakness of a reference system (i.e., an infrastructure, an asset, a group of assets, an organization, etc.) that may result in a temporary or permanent interruption of the system’s operations. Thus, vulnerability is the susceptibility of a system to mishap risks. | [13] |
| Threat or hazard | Anything that might exploit a vulnerability for the temporary or permanent interruption of the system’s operations. In general, a threat may be: (i) accidental, i.e., unintentional; (ii) malicious, i.e., hostile and deliberate. | [13] |
| Vulnerability index | A measure of the susceptibility of people, communities, or regions to natural or technological hazards. A vulnerability index represents a measure of the exposure of the system or the community under study with respect to the reference hazards. | [14] |
| Safety threat | A threat that refers to any accidental cause of the interruption of system’s operations, in the case that such interruption operation exhibits a safety impact for the outcome, i.e., if the reference system is safety-critical. This type of threat is also named just hazard, which is “a dormant potential for harm which is present in one form or another within the aviation system or its environment”. | [15] |
| Security threat | A threat that refers to any malicious (intentional) cause of the interruption of system’s operations. It is often named just threat and it is the equivalent to hazard in safety. According to the European Union Agency for Cybersecurity (ENISA), a threat is “any circumstance or event with the potential to adversely impact an asset through unauthorized access, destruction, disclosure, modification of data, and/or denial of service”. Clearly, a security threat may also have a safety impact if the reference system is safety-critical. | [16] |
| Threat agent or attacker | In case of a security threat, a threat agent or attacker is an entity (i.e., person, organization, system, etc.) that has the power to act, cause, carry, transmit, or support the reference threat. Thus, a threat agent is the entity which has the intention, the capacity, and the opportunity to exploit the vulnerabilities of the system. | [17] |
| Threat scenario or hazard scenario | The description of how a threat or hazard might materialize and represents a logic sequence from a hazard to its consequence | [7] |
| Risk | A vector value combining event likelihood with event outcome related to a threat scenario. | [13] |
| Risk assessment | A process to identify plausible threat scenarios and quantifies their level of risk, i.e., by analyzing their likelihood, reasonable worst-case consequences, the current mitigating measures, and the remaining vulnerabilities. Risk assessment may contain safety elements or security elements, or both. For example, a security-based risk assessment or security risk assessment evaluates the security-related vulnerabilities of the reference system, and the occurrence probability and the potential impact of security incidents. | [5] |
| Security incident | Off-nominal events in the system’s operations that are caused by an attack of a threat agent and that have an actual or potentially adverse effect on the security or performance of the system. | [16] |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Pascarella, D.; Gigante, G.; Vozella, A.; Bieber, P.; Dubot, T.; Martinavarro, E.; Barraco, G.; Li Calzi, G. A Methodological Framework for the Risk Assessment of Drone Intrusions in Airports. Aerospace 2022, 9, 747. https://doi.org/10.3390/aerospace9120747
Pascarella D, Gigante G, Vozella A, Bieber P, Dubot T, Martinavarro E, Barraco G, Li Calzi G. A Methodological Framework for the Risk Assessment of Drone Intrusions in Airports. Aerospace. 2022; 9(12):747. https://doi.org/10.3390/aerospace9120747
Chicago/Turabian StylePascarella, Domenico, Gabriella Gigante, Angela Vozella, Pierre Bieber, Thomas Dubot, Edgar Martinavarro, Giovanni Barraco, and Greta Li Calzi. 2022. "A Methodological Framework for the Risk Assessment of Drone Intrusions in Airports" Aerospace 9, no. 12: 747. https://doi.org/10.3390/aerospace9120747
APA StylePascarella, D., Gigante, G., Vozella, A., Bieber, P., Dubot, T., Martinavarro, E., Barraco, G., & Li Calzi, G. (2022). A Methodological Framework for the Risk Assessment of Drone Intrusions in Airports. Aerospace, 9(12), 747. https://doi.org/10.3390/aerospace9120747








