Advancement of Routing Protocols and Applications of Underwater Wireless Sensor Network (UWSN)—A Survey
Abstract
1. Introduction
2. Applications and Background of UWSN
2.1. Applications of UWSN
2.1.1. Natural Hazard Detection
2.1.2. Underwater Mapping and Locating Mineral Mines
2.1.3. Environmental Monitoring
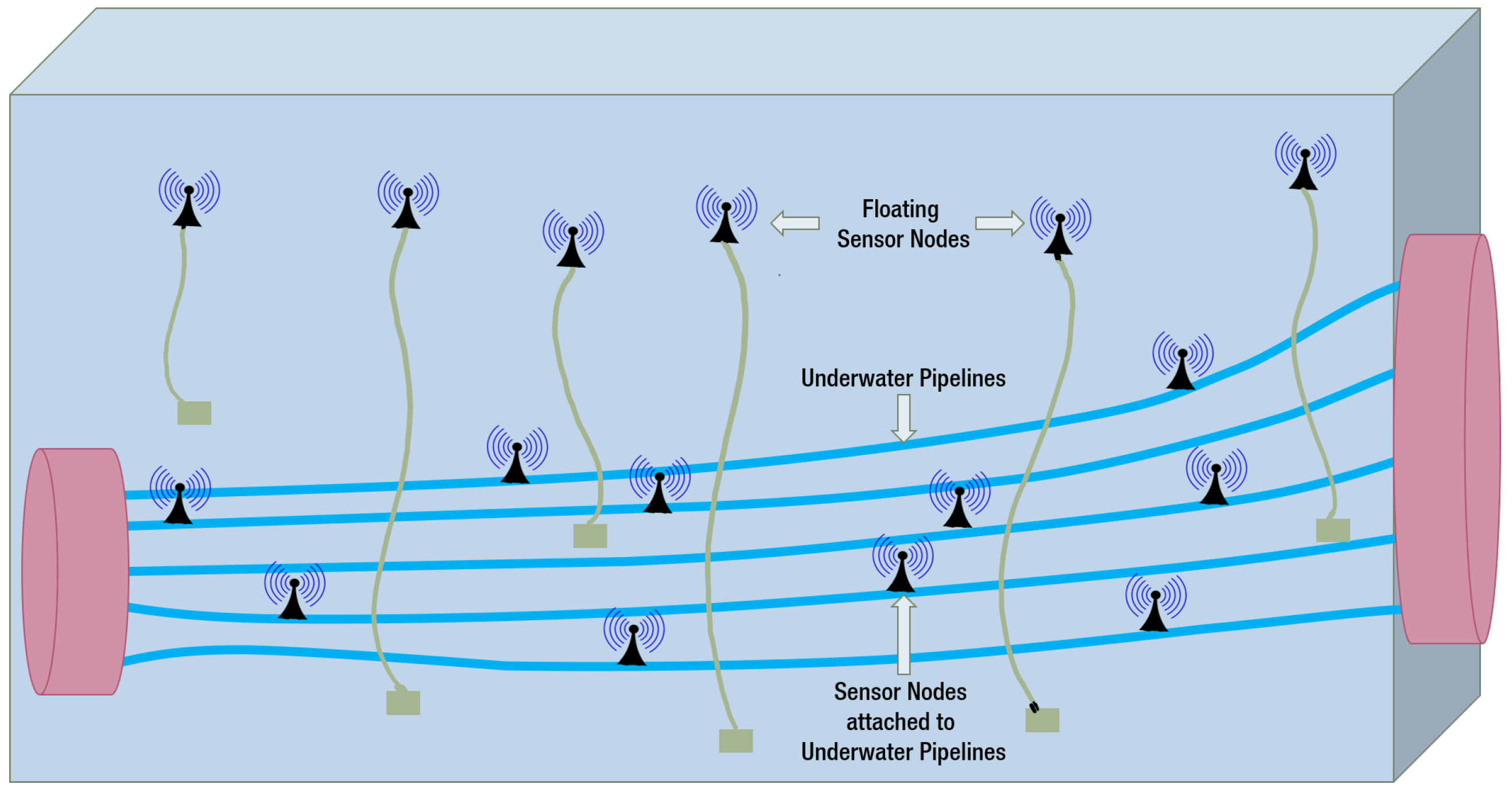
2.1.4. Underwater Pipeline Monitoring
2.1.5. Military Operations
2.2. Background of UWSN
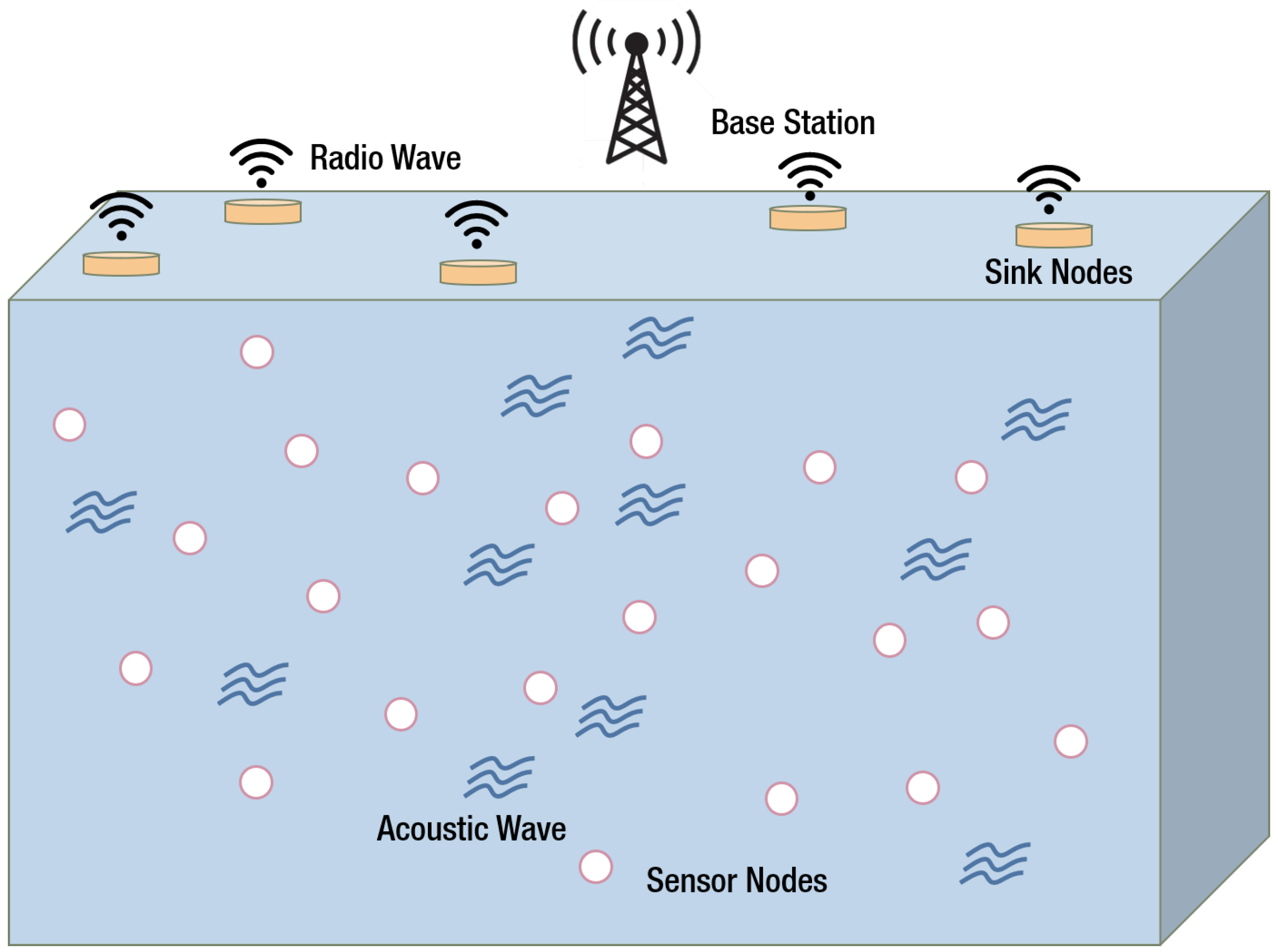
2.2.1. Underwater Acoustic Communication
2.2.2. Deployment of Network Architecture
2.2.3. Localization
2.2.4. Reliability
- Noise of the Communication Medium,
- Attenuation of the Channel,
- Channel Bandwidth Limitation, and
- Low Speed of the Acoustic Transmission.
3. Routing Protocols for UWSN
3.1. Protocols Featuring Node Mobility
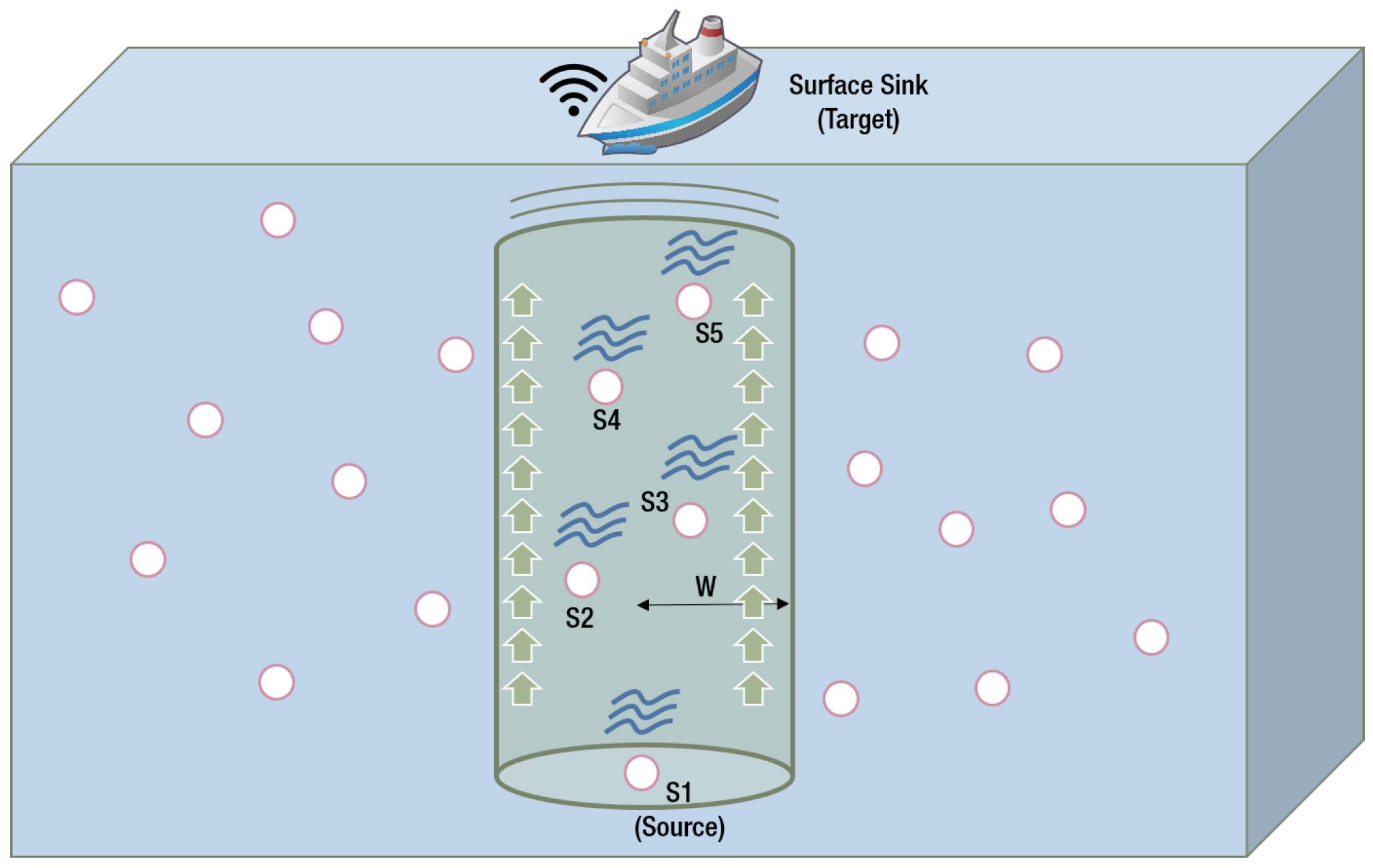
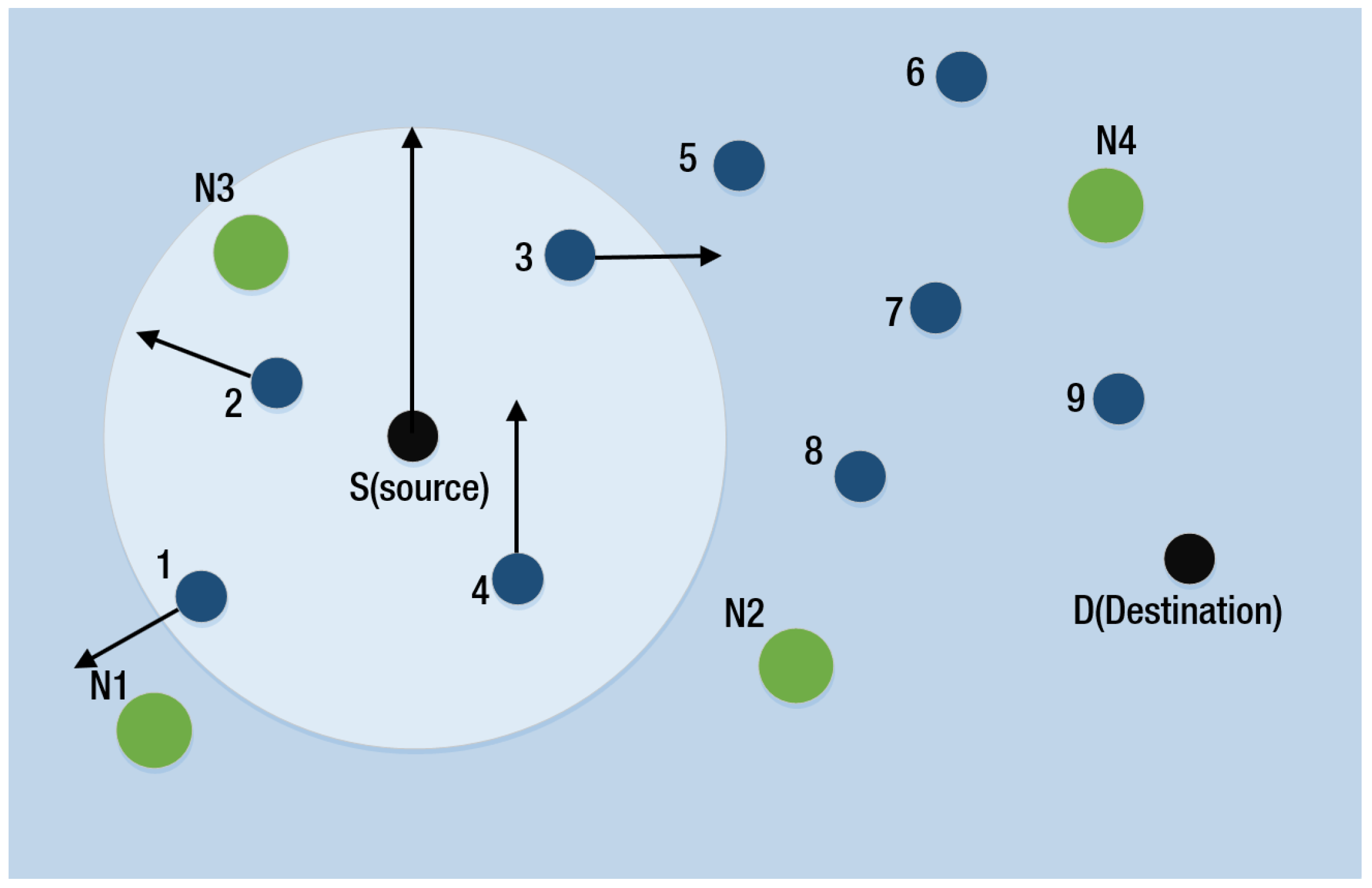
3.1.1. Vector Based Forwarding (VBF) and Hop-by-Hop VBF (HH-VBF)
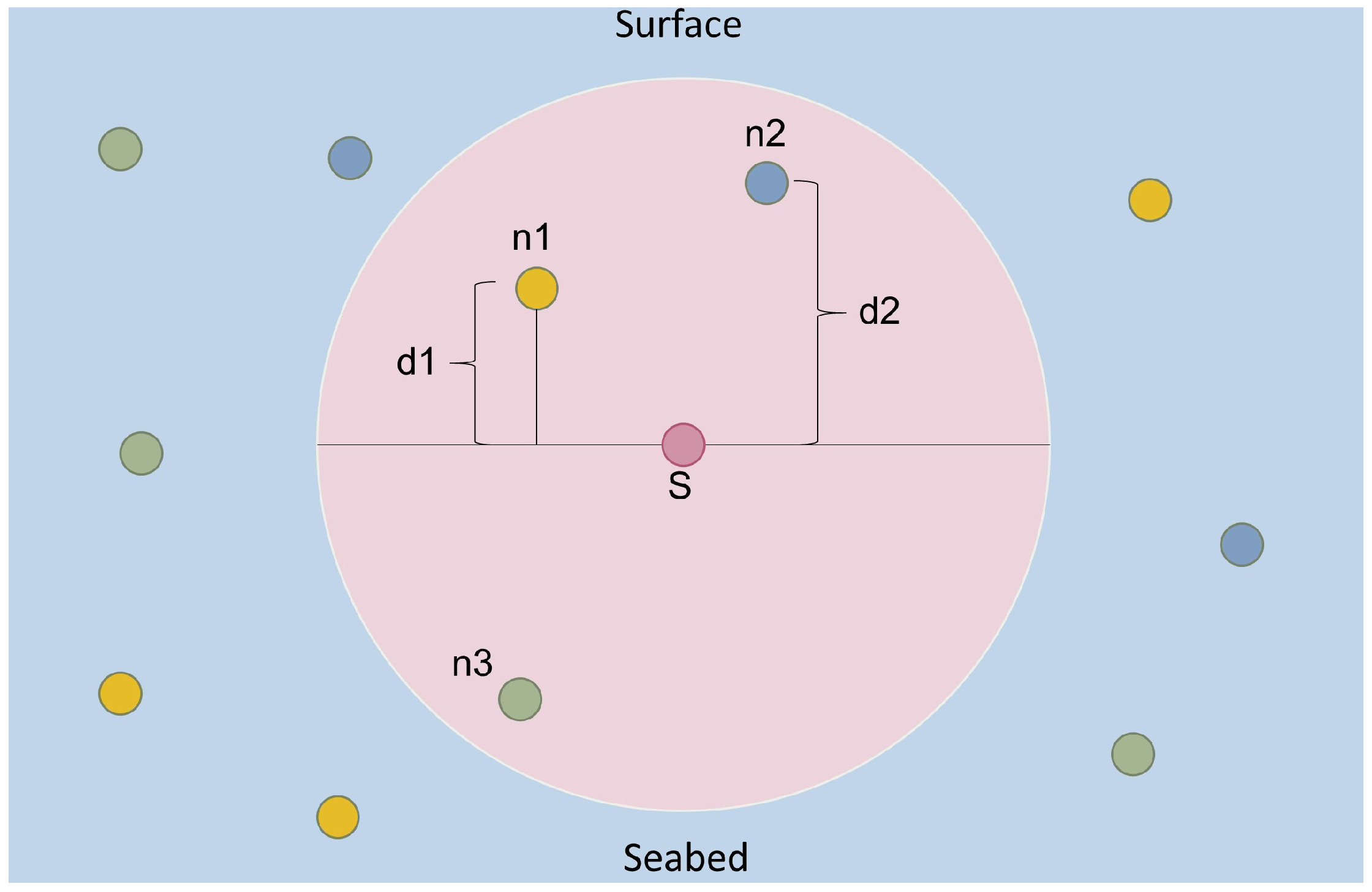
3.1.2. Depth Based Routing (DBR), Depth Based Multi-Hop Routing (DMBR) and Energy-Efficient DBR (EEDBR)
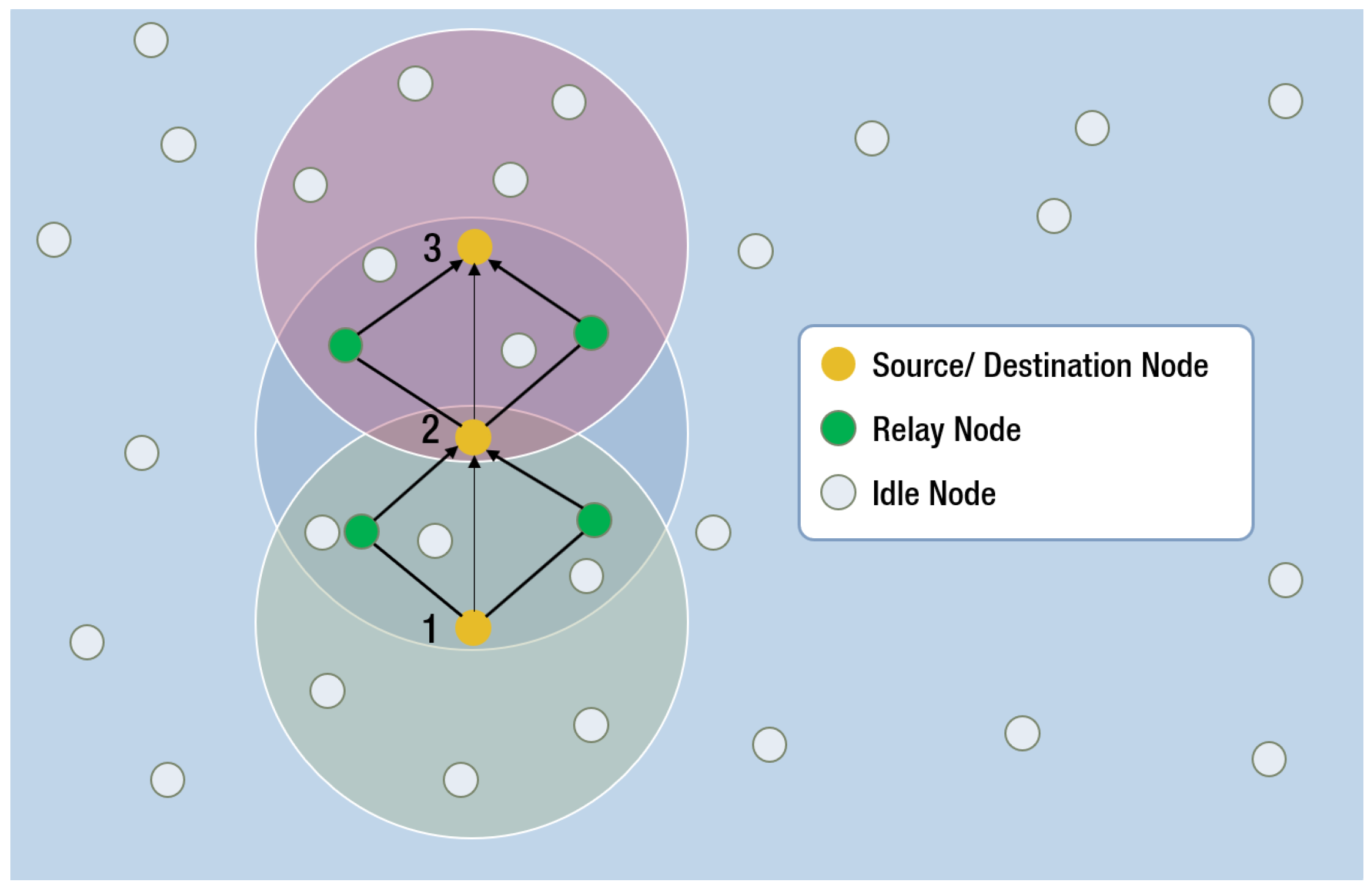
3.1.3. Cooperative Depth Based Routing (CoDBR)
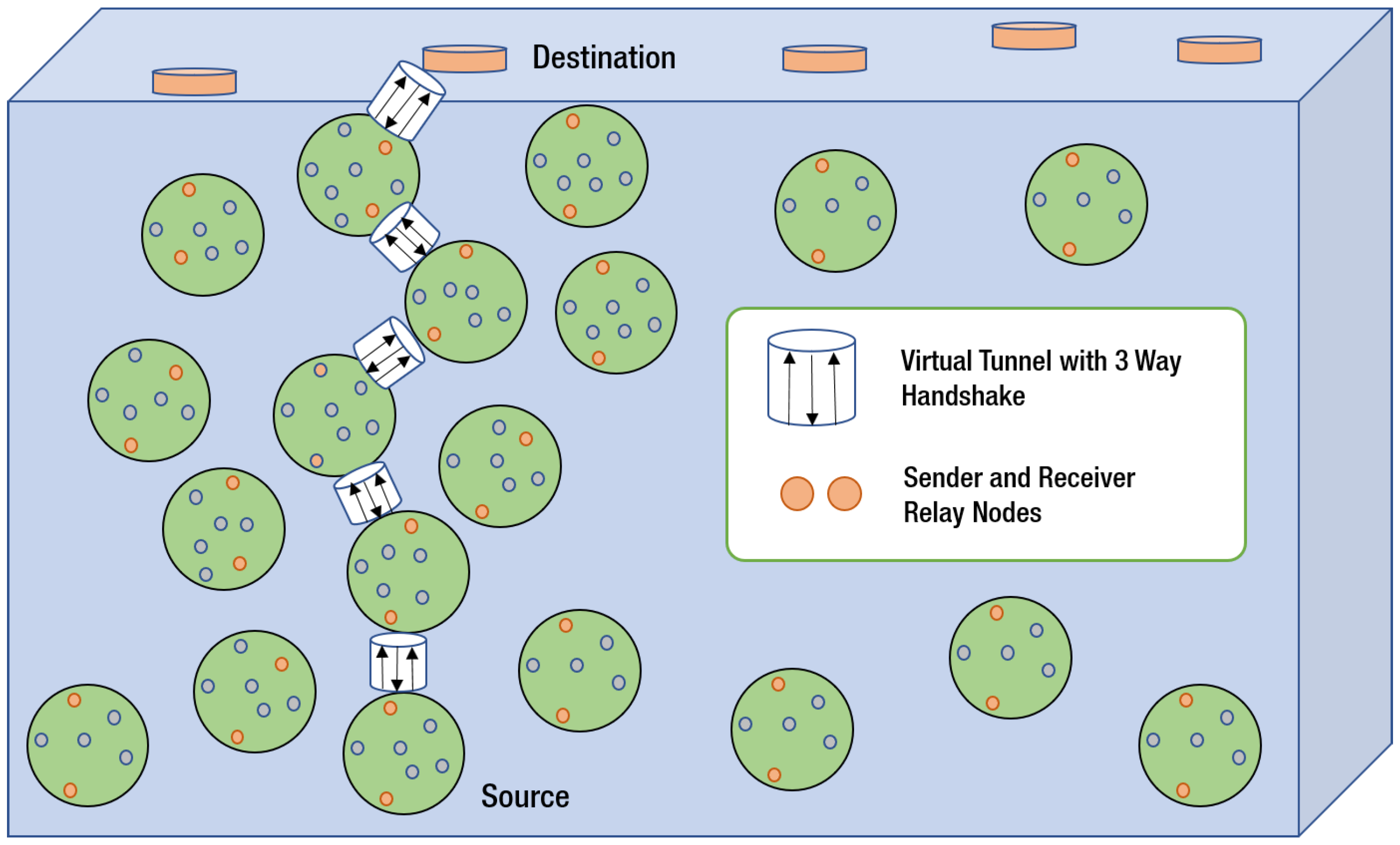
3.1.4. Virtual Tunneling Protocol (VTP)
3.2. Protocols Featuring Energy Balancing
Reliable Energy Efficient Pressure Based Routing (RE-PBR)
3.3. Protocols Featuring Channel Properties
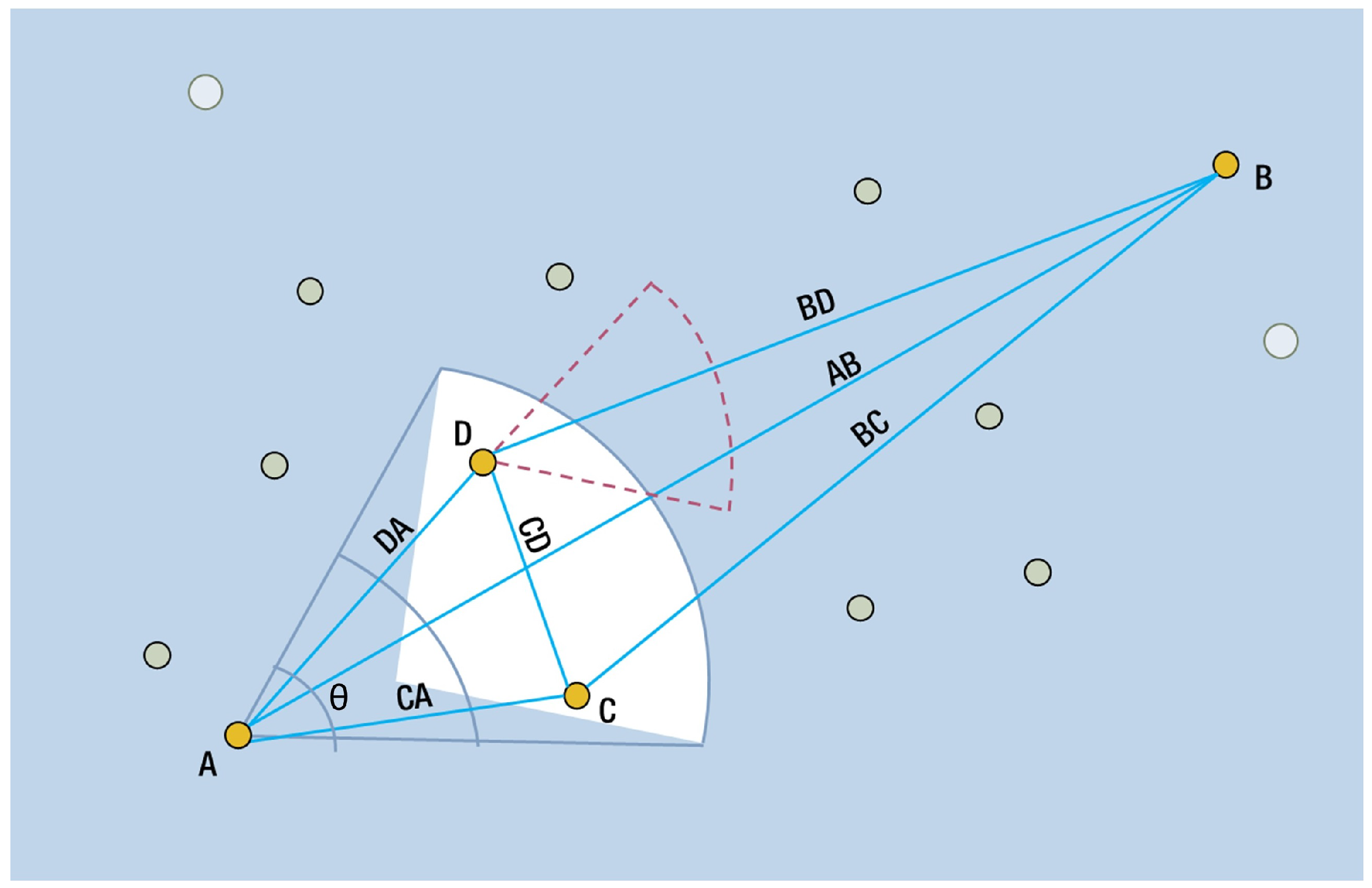
3.3.1. Directional Flooding-Based Routing (DFR)
3.3.2. Location-Aware Routing Protocol (LARP)
3.4. Protocols Featuring Energy Efficiency
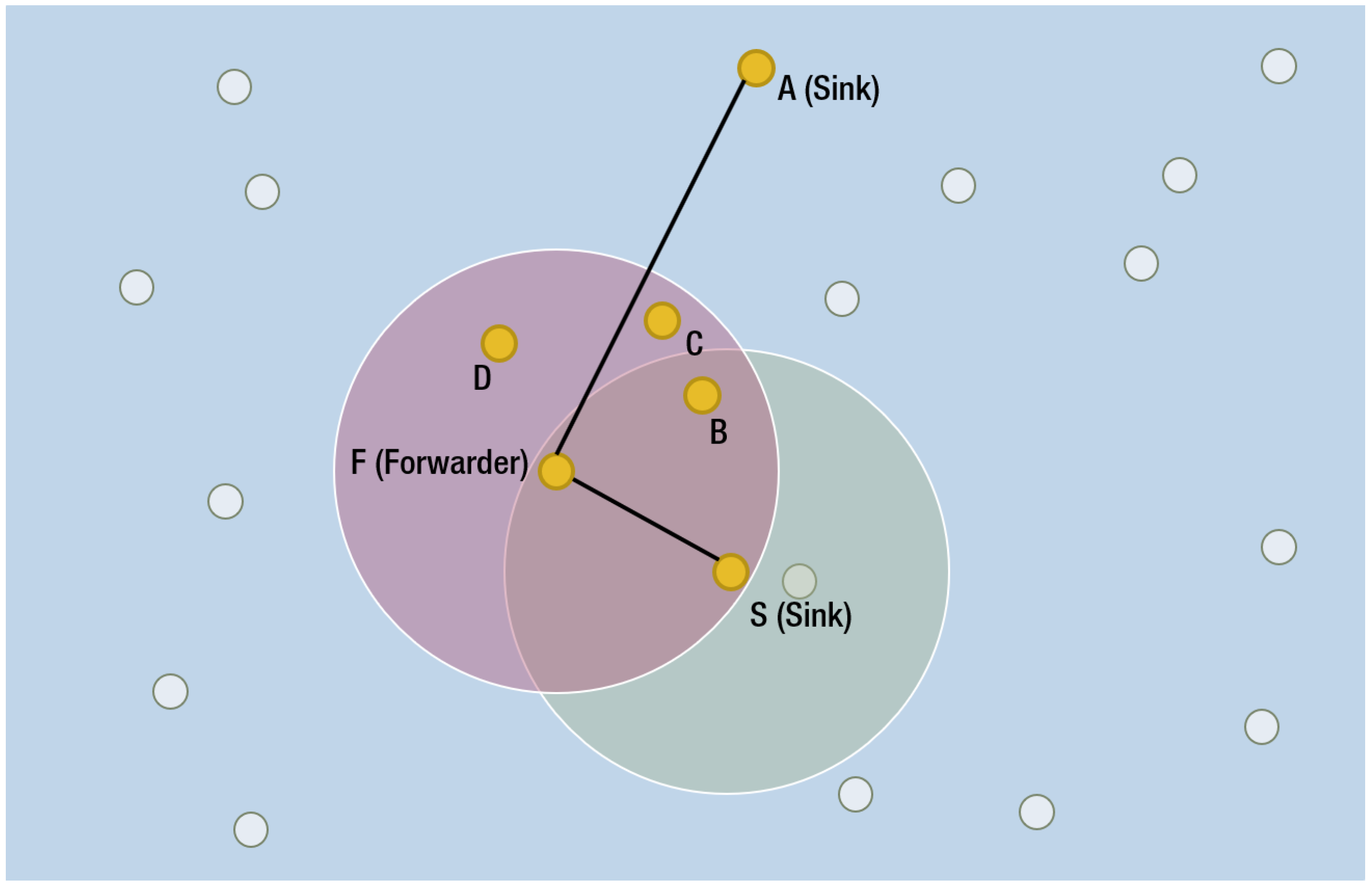
3.4.1. Focused Beam Routing (FBR)
3.4.2. Distributed Underwater Clustering Scheme (DUCS)
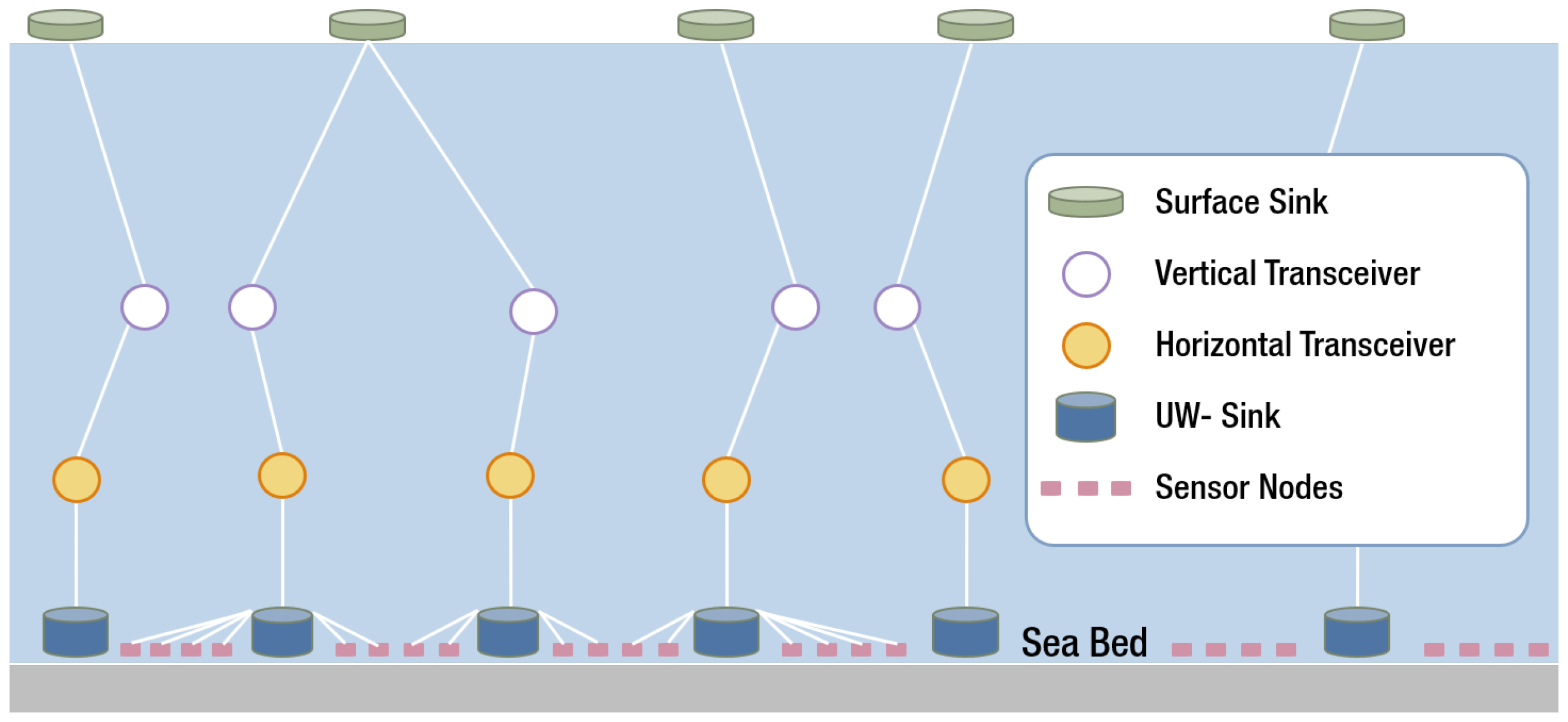
3.4.3. Sparsity-Aware Energy efficient clustering (SEEC)
3.5. Protocols Featuring Network Void Hole Avoidance
3.6. An Energy Balanced Efficient and Reliable Routing Protocol (EBER2) and Weighting Depth and Forwarding Area Division DBR (WDFAD-DBR)
3.7. Regional Sink Mobility (RSM) and Vertical sink Mobility (VSM)
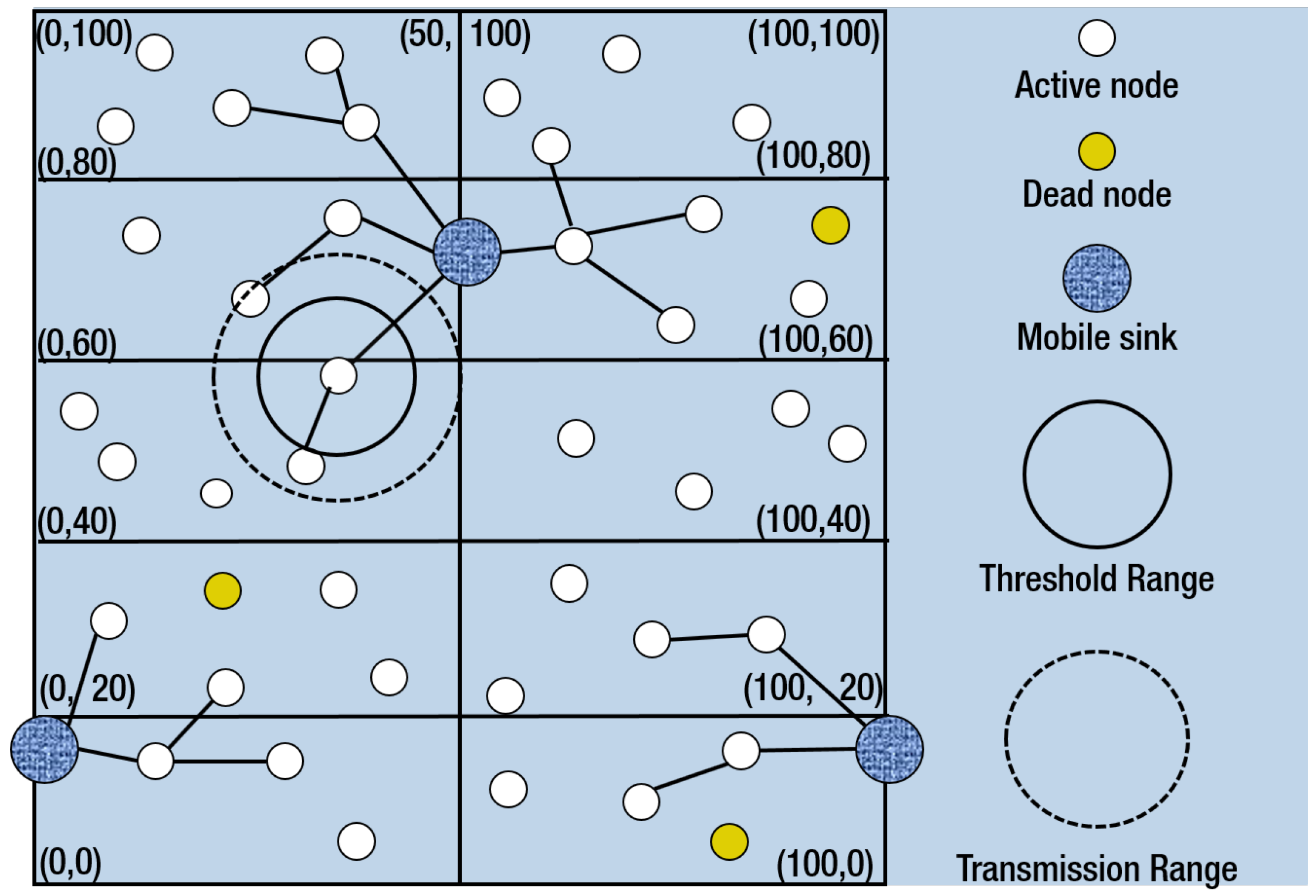
3.7.1. Regional Sink Mobility (RSM)
3.7.2. Vertical Sink Mobility (VSM)
4. Evaluation of the Routing Protocols
5. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Immas, A.; Saadat, M.; Navarro, J.; Drake, M.; Shen, J.; Alam, M.R. High-bandwidth underwater wireless communication using a swarm of autonomous underwater vehicles. In Proceedings of the ASME 2019 38th International Conference on Ocean, Offshore and Arctic Engineering, Glasgow, UK, 9–14 June 2019; American Society of Mechanical Engineers Digital Collection: New York, NY, USA. [Google Scholar]
- Akyildiz, I.F.; Pompili, D.; Melodia, T. Underwater acoustic sensor networks: Research challenges. Ad Hoc Netw. 2005, 3, 257–279. [Google Scholar] [CrossRef]
- Heidemann, J.; Ye, W.; Wills, J.; Syed, A.; Li, Y. Research challenges and applications for underwater sensor networking. In Proceedings of the IEEE Wireless Communications and Networking Conference, WCNC 2006, Las Vegas, NV, USA, 3–6 April 2006; IEEE: Piscataway, NJ, USA, 2006; Volume 1, pp. 228–235. [Google Scholar]
- Goyal, N.; Dave, M.; Verma, A.K. Protocol stack of underwater wireless sensor network: Classical approaches and new trends. Wirel. Pers. Commun. 2019, 104, 995–1022. [Google Scholar] [CrossRef]
- Li, S.; Qu, W.; Liu, C.; Qiu, T.; Zhao, Z. Survey on high reliability wireless communication for underwater sensor networks. J. Netw. Comput. Appl. 2019, 148, 102446. [Google Scholar] [CrossRef]
- Sun, Y.; Yuan, Y.; Xu, Q.; Hua, C.; Guan, X. A Mobile Anchor Node Assisted RSSI Localization Scheme in Underwater Wireless Sensor Networks. Sensors 2019, 19, 4369. [Google Scholar] [CrossRef] [PubMed]
- Yan, J.; Xu, Z.; Wan, Y.; Chen, C.; Luo, X. Consensus estimation-based target localization in underwater acoustic sensor networks. Int. J. Robust Nonlinear Control 2017, 27, 1607–1627. [Google Scholar] [CrossRef]
- Murad, M.; Sheikh, A.A.; Manzoor, M.A.; Felemban, E.; Qaisar, S. A Survey on Current Underwater Acoustic Sensor Network Applications. Int. J. Comput. Theory Eng. 2015, 7, 51. [Google Scholar] [CrossRef]
- Kumar, P.; Kumar, P.; Priyadarshini, P. Underwater acoustic sensor network for early warning generation. In Proceedings of the 2012 Oceans, Hampton Roads, VA, USA, 14–19 October 2012; IEEE: Piscataway, NJ, USA, 2012; pp. 1–6. [Google Scholar]
- Casey, K.; Lim, A.; Dozier, G. A sensor network architecture for tsunami detection and response. Int. J. Distrib. Sens. Netw. 2008, 4, 27–42. [Google Scholar] [CrossRef]
- Handziski, V.; Koepke, A.; Karl, H.; Frank, C.; Drytkiewicz, W. Improving the energy efficiency of directed diffusion using passive clustering. In Proceedings of the European Workshop on Wireless Sensor Networks, Berlin, Germany, 19–21 January 2004; Springer: Berlin/Heidelberg, Germany, 2004; pp. 172–187. [Google Scholar]
- Felemban, E.; Shaikh, F.K.; Qureshi, U.M.; Sheikh, A.A.; Qaisar, S.B. Underwater sensor network applications: A comprehensive survey. Int. J. Distrib. Sens. Netw. 2015, 2015, 5. [Google Scholar] [CrossRef]
- Thornton, B.; Bodenmann, A.; Asada, A.; Sato, T.; Ura, T. Acoustic and visual instrumentation for survey of manganese crusts using an underwater vehicle. In Proceedings of the 2012 Oceans, Hampton Roads, VA, USA, 14–19 October 2012; IEEE: Piscataway, NJ, USA, 2012; pp. 1–10. [Google Scholar]
- Srinivas, S.; Ranjitha, P.; Ramya, R.; Narendra, G.K. Investigation of oceanic environment using large-scale uwsn and uanets. In Proceedings of the 2012 8th International Conference on Wireless Communications, Networking and Mobile Computing (WiCOM), Shanghai, China, 21–23 September 2012; pp. 1–5. [Google Scholar]
- Khan, A.; Jenkins, L. Undersea wireless sensor network for ocean pollution prevention. In Proceedings of the 2008 3rd International Conference on Communication Systems Software and Middleware and Workshops (COMSWARE’08), Bangalore, India, 6–10 January 2008; IEEE: Piscataway, NJ, USA, 2008; pp. 2–8. [Google Scholar]
- Du, X.; Liu, X.; Su, Y. Underwater acoustic networks testbed for ecological monitoring of Qinghai Lake. In Proceedings of the OCEANS 2016, Shanghai, China, 10–13 April 2016; IEEE: Piscataway, NJ, USA, 2016; pp. 1–4. [Google Scholar]
- Lloret, J.; Sendra, S.; Garcia, M.; Lloret, G. Group-based underwater wireless sensor network for marine fish farms. In Proceedings of the 2011 IEEE GLOBECOM Workshops (GC Wkshps), Houston, TX, USA, 5–9 December 2011; IEEE: Piscataway, NJ, USA, 2011; pp. 115–119. [Google Scholar]
- Mohamed, N.; Jawhar, I.; Al-Jaroodi, J.; Zhang, L. Sensor network architectures for monitoring underwater pipelines. Sensors 2011, 11, 10738–10764. [Google Scholar] [CrossRef]
- Henry, N.F.; Henry, O.N. Wireless sensor networks based pipeline vandalisation and oil spillage monitoring and detection: Main benefits for nigeria oil and gas sectors. SIJ Trans. Comput. Sci. Eng. Its Appl. (CSEA) 2015, 3, 1–6. [Google Scholar]
- Allen, C. Wireless sensor network nodes: Security and deployment in the niger-delta oil and gas sector. Int. J. Netw. Security & Its Appl. (IJNSA) 2011, 3, 68–79. [Google Scholar]
- Freitag, L.; Grund, M.; Von Alt, C.; Stokey, R.; Austin, T. A shallow water acoustic network for mine countermeasures operations with autonomous underwater vehicles. In Proceedings of the Underwater Defense Technology (UDT), Amsterdam, The Netherlands, 21–23 June 2005; pp. 1–6. [Google Scholar]
- Jouhari, M.; Ibrahimi, K.; Tembine, H.; Ben-Othman, J. Underwater wireless sensor networks: A survey on enabling technologies, localization protocols, and internet of underwater things. IEEE Access 2019, 7, 96879–96899. [Google Scholar] [CrossRef]
- Khan, A.; Ahmedy, I.; Anisi, M.H.; Javaid, N.; Ali, I.; Khan, N.; Alsaqer, M.; Mahmood, H. A localization-free interference and energy holes minimization routing for underwater wireless sensor networks. Sensors 2018, 18, 165. [Google Scholar] [CrossRef] [PubMed]
- Ayaz, M.; Baig, I.; Abdullah, A.; Faye, I. A survey on routing techniques in underwater wireless sensor networks. J. Netw. Comput. Appl. 2011, 34, 1908–1927. [Google Scholar] [CrossRef]
- Kremer, K. Advanced underwater technology with emphasis on acoustic modeling and systems. Hydroacoustics 1997, 1. [Google Scholar] [CrossRef]
- Stojanovic, M. Acoustic (underwater) communications. In Encyclopedia of Telecommunications; John Wiley & Sons, Inc.: Hoboken, NJ, USA, 2003. [Google Scholar]
- Li, B.; Huang, J.; Zhou, S.; Ball, K.; Stojanovic, M.; Freitag, L.; Willett, P. MIMO-OFDM for high-rate underwater acoustic communications. IEEE J. Ocean. Eng. 2009, 34, 634–644. [Google Scholar]
- Amruta, M.K.; Satish, M.T. Solar powered water quality monitoring system using wireless sensor network. In Proceedings of the 2013 International Mutli-Conference on Automation, Computing, Communication, Control and Compressed Sensing (iMac4s), Kottayam, India, 22–23 March 2013; IEEE: Piscataway, NJ, USA; pp. 281–285. [Google Scholar]
- Pule, M.; Yahya, A.; Chuma, J. Wireless sensor networks: A survey on monitoring water quality. J. Appl. Res. Technol. 2017, 15, 562–570. [Google Scholar] [CrossRef]
- Jin, N.; Ma, R.; Lv, Y.; Lou, X.; Wei, Q. A novel design of water environment monitoring system based on wsn. In Proceedings of the 2010 International Conference on Computer Design and Applications, Qinhuangdao, China, 25–27 June 2010; IEEE: Piscataway, NJ, USA; Volume 2, pp. V2–V593. [Google Scholar]
- Verma, S. Wireless Sensor Network application for water quality monitoring in India. In Proceedings of the 2012 National Conference on Computing and Communication Systems, Durgapur, India, 21–22 November 2012; IEEE: Piscataway, NJ, USA; pp. 1–5. [Google Scholar]
- Shi, B.; Sreeram, V.; Zhao, D.; Duan, S.; Jiang, J. A wireless sensor network-based monitoring system for freshwater fishpond aquaculture. Biosyst. Eng. 2018, 172, 57–66. [Google Scholar] [CrossRef]
- Hiremath, V. Design and development of wireless sensor network system to monitor parameters influencing freshwater fishes. Int. J. Comput. Sci. Eng. 2012, 4, 1096. [Google Scholar]
- Sutar, K.G.; Patil, R.T. Wireless sensor network system to monitor the fish farm. Int. J. Eng. Res. Appl. 2013, 3, 194–197. [Google Scholar]
- Abdulameer, D.N.; Ahmad, R. Underwater Acoustic Communications Using Direct-Sequence Spread Spectrum. Int. J. Comput. Sci. Issues (IJCSI) 2014, 11, 76. [Google Scholar]
- Akyildiz, I.F.; Pompili, D.; Melodia, T. State-of-the-art in protocol research for underwater acoustic sensor networks. In Proceedings of the 1st ACM International Workshop on Underwater Networks, Los Angeles, CA, USA, September 2006; ACM: New York, NY, USA, 2006; pp. 7–16. [Google Scholar]
- Cañete, F.J.; López-Fernández, J.; García-Corrales, C.; Sánchez, A.; Robles, E.; Rodrigo, F.J.; Paris, J.F. Measurement and modeling of narrowband channels for ultrasonic underwater communications. Sensors 2016, 16, 256. [Google Scholar] [CrossRef] [PubMed]
- Xie, P.; Cui, J.H.; Lao, L. VBF: Vector-based forwarding protocol for underwater sensor networks. In Proceedings of the International Conference on Research in Networking, Coimbra, Portugal, 15–19 May 2006; Springer: Berlin/Heidelberg, Germany; pp. 1216–1221. [Google Scholar]
- Beniwal, M.; Singh, R.P.; Sangwan, A. A localization scheme for underwater sensor networks without Time Synchronization. Wirel. Pers. Commun. 2016, 88, 537–552. [Google Scholar] [CrossRef]
- Luo, J.; Fan, L.; Wu, S.; Yan, X. Research on localization algorithms based on acoustic communication for underwater sensor networks. Sensors 2018, 18, 67. [Google Scholar] [CrossRef]
- Ahmed, M.; Salleh, M. Localization schemes in underwater sensor network (UWSN): A survey. Indones. J. Electr. Eng. Comput. Sci. 2016, 1, 119–125. [Google Scholar] [CrossRef]
- Su, X.; Ullah, I.; Liu, X.; Choi, D. A Review of Underwater Localization Techniques, Algorithms, and Challenges. J. Sensors 2020, 2020, 6403161. [Google Scholar] [CrossRef]
- Erol, M.; Vieira, L.F.; Gerla, M. Localization with Dive’N’Rise (DNR) beacons for underwater acoustic sensor networks. In Proceedings of the Second Workshop on Underwater Networks, Montreal, QC, Canada, September 2007; ACM: New York, NY, USA; pp. 97–100. [Google Scholar]
- Chen, K.; Zhou, Y.; He, J. A localization scheme for underwater wireless sensor networks. Int. J. Adv. Sci. Technol. 2009, 4, 9–16. [Google Scholar]
- Ayaz, M.; Jung, L.T.; Abdullah, A.; Ahmad, I. Reliable data deliveries using packet optimization in multi-hop underwater sensor networks. J. King Saud Univ.-Comput. Inf. Sci. 2012, 24, 41–48. [Google Scholar] [CrossRef]
- Khan, A.; Ali, I.; Ghani, A.; Khan, N.; Alsaqer, M.; Rahman, A.U.; Mahmood, H. Routing protocols for underwater wireless sensor networks: Taxonomy, research challenges, routing strategies and future directions. Sensors 2018, 18, 1619. [Google Scholar] [CrossRef]
- Xiao, Y. Underwater Scoustic Sensor Networks; CRC Press: Boca Raton, FL, USA, 2010. [Google Scholar]
- Mackenzie, K.V. Nine-term equation for sound speed in the oceans. J. Acoust. Soc. Am. 1981, 70, 807–812. [Google Scholar] [CrossRef]
- Khalid, M.; Ullah, Z.; Ahmad, N.; Arshad, M.; Jan, B.; Cao, Y.; Adnan, A. A survey of routing issues and associated protocols in underwater wireless sensor networks. J. Sensors 2017, 2017, 7539751. [Google Scholar] [CrossRef]
- Islam, T.; Lee, Y.K. A Comprehensive Survey of Recent Routing Protocols for Underwater Acoustic Sensor Networks. Sensors 2019, 19, 4256. [Google Scholar] [CrossRef] [PubMed]
- Nicolaou, N.; See, A.; Xie, P.; Cui, J.H.; Maggiorini, D. Improving the robustness of location-based routing for underwater sensor networks. In Proceedings of the OCEANS 2007-Europe, Aberdeen, UK, 18–21 June 2007; IEEE: Piscataway, NJ, USA, 2007; pp. 1–6. [Google Scholar]
- Yan, H.; Shi, Z.J.; Cui, J.H. DBR: Depth-based routing for underwater sensor networks. In Proceedings of the International Conference on Research in Networking, Singapore, 5–9 May 2008; Springer: Berlin/Heidelberg, Germany; pp. 72–86. [Google Scholar]
- Bharathy, A.V.; Chandrasekar, V. A Novel Virtual Tunneling Protocol for Underwater Wireless Sensor Networks. In Soft Computing and Signal Processing; Springer: Berlin/Heidelberg, Germany, 2019; pp. 281–289. [Google Scholar]
- Nasir, H.; Javaid, N.; Ashraf, H.; Manzoor, S.; Khan, Z.A.; Qasim, U.; Sher, M. CoDBR: Cooperative depth based routing for underwater wireless sensor networks. In Proceedings of the 2014 Ninth International Conference on Broadband and Wireless Computing, Communication and Applications, Guangdong, China, 8–10 November 2014; IEEE: Piscataway, NJ, USA, 2014; pp. 52–57. [Google Scholar]
- Wahid, A.; Lee, S.; Jeong, H.J.; Kim, D. Eedbr: Energy-efficient depth-based routing protocol for underwater wireless sensor networks. In Advanced Computer Science and Information Technology; Springer: Berlin/Heidelberg, Germany, 2011; pp. 223–234. [Google Scholar]
- Khasawneh, A.; Latiff, M.S.B.A.; Kaiwartya, O.; Chizari, H. A reliable energy-efficient pressure-based routing protocol for underwater wireless sensor network. Wirel. Netw. 2018, 24, 2061–2075. [Google Scholar] [CrossRef]
- Shin, D.; Hwang, D.; Kim, D. DFR: An efficient directional flooding-based routing protocol in underwater sensor networks. Wirel. Commun. Mob. Comput. 2012, 12, 1517–1527. [Google Scholar] [CrossRef]
- Shen, J.; Tan, H.W.; Wang, J.; Wang, J.W.; Lee, S.Y. A novel routing protocol providing good transmission reliability in underwater sensor networks. J. Internet Technol. 2015, 16, 171–178. [Google Scholar]
- Jornet, J.M.; Stojanovic, M.; Zorzi, M. Focused beam routing protocol for underwater acoustic networks. In Proceedings of the Third ACM International Workshop on Underwater Networks, San Francisco, CA, USA, September 2008; ACM: New York, NY, USA; pp. 75–82. [Google Scholar]
- Domingo, M.C.; Prior, R. A distributed clustering scheme for underwater wireless sensor networks. In Proceedings of the 2007 IEEE 18th International Symposium on Personal, Indoor and Mobile Radio Communications, Athens, Greece, 3–7 September 2007; IEEE: Piscataway, NJ, USA, 2007; pp. 1–5. [Google Scholar]
- Azam, I.; Majid, A.; Ahmad, I.; Shakeel, U.; Maqsood, H.; Khan, Z.A.; Qasim, U.; Javaid, N. SEEC: Sparsity-aware energy efficient clustering protocol for underwater wireless sensor networks. In Proceedings of the 2016 IEEE 30th International Conference on Advanced Information Networking and Applications (AINA), Crans-Montana, Switzerland, 23–25 March 2016; IEEE: Piscataway, NJ, USA, 2016; pp. 352–361. [Google Scholar]
- Guangzhong, L.; Zhibin, L. Depth-based multi-hop routing protocol for underwater sensor network. In Proceedings of the 2010 The 2nd International Conference on Industrial Mechatronics and Automation (ICIMA), Wuhan, China, 30–31 May 2010; Volume 2, pp. 268–270. [Google Scholar]
- Wadud, Z.; Ismail, M.; Qazi, A.B.; Khan, F.A.; Derhab, A.; Ahmad, I.; Ahmad, A.M. An Energy Balanced Efficient and Reliable Routing Protocol for Underwater Wireless Sensor Networks. IEEE Access 2019, 7, 175980–175999. [Google Scholar] [CrossRef]
- Ali, B.; Javaid, N.; Islam, S.U.; Ahmed, G.; Qasim, U.; Khan, Z.A. RSM and VSM: Two New Routing Protocols for Underwater WSNs. In Proceedings of the 2016 International Conference on Intelligent Networking and Collaborative Systems (INCoS), Ostrawva, Czech Republic, 7–9 September 2016; IEEE: Piscataway, NJ, USA, 2016; pp. 173–179. [Google Scholar]
- Yu, H.; Yao, N.; Wang, T.; Li, G.; Gao, Z.; Tan, G. WDFAD-DBR: Weighting depth and forwarding area division DBR routing protocol for UASNs. Ad Hoc Netw. 2016, 37, 256–282. [Google Scholar] [CrossRef]
- Hu, T.; Fei, Y. MURAO: A multi-level routing protocol for acoustic-optical hybrid underwater wireless sensor networks. In Proceedings of the 2012 9th Annual IEEE Communications Society Conference on Sensor, Mesh and Ad Hoc Communications and Networks (SECON), Seoul, South Korea, 18–21 June 2012; IEEE: Piscataway, NJ, USA, 2012; pp. 218–226. [Google Scholar]
- Basagni, S.; Petrioli, C.; Petroccia, R.; Spaccini, D. CARP: A channel-aware routing protocol for underwater acoustic wireless networks. Ad Hoc Netw. 2015, 34, 92–104. [Google Scholar] [CrossRef]
- Noh, Y.; Lee, U.; Wang, P.; Choi, B.S.C.; Gerla, M. VAPR: Void-aware pressure routing for underwater sensor networks. IEEE Trans. Mob. Comput. 2013, 12, 895–908. [Google Scholar] [CrossRef]
- Hussain, S.N.; Hussain, M.M.; Aslam, M.G. Flooding based routing techniques for efficient communication in underwater wsns1. Eur. J. Comput. Sci. Inf. Technol. 2015, 3, 52–60. [Google Scholar]
- De Morais Cordeiro, C.; Agrawal, D.P. Ad Hoc and Sensor Networks: Theory and Applications; World Scientific: Singapore, 2011. [Google Scholar]
- Zhangjie, F.; Xingming, S.; Qi, L.; Lu, Z.; Jiangang, S. Achieving efficient cloud search services: Multi-keyword ranked search over encrypted cloud data supporting parallel computing. IEICE Trans. Commun. 2015, 98, 190–200. [Google Scholar]
- Jornet, J.M.; Stojanovic, M. Distributed power control for underwater acoustic networks. In Proceedings of the OCEANS 2008, Quebec City, QC, Canada, 15–18 September 2008; IEEE: Piscataway, NJ, USA, 2008; pp. 1–7. [Google Scholar]
- Hu, K.; Song, X.; Sun, Z.; Luo, H.; Guo, Z. Localization based on map and pso for drifting-restricted underwater acoustic sensor networks. Sensors 2019, 19, 71. [Google Scholar] [CrossRef] [PubMed]
- Li, H.; He, Y.; Cheng, X.; Zhu, H.; Sun, L. Security and privacy in localization for underwater sensor networks. IEEE Commun. Mag. 2015, 53, 56–62. [Google Scholar] [CrossRef]


| Operating Frequency Bands (kHz) | Direct Transmission Range with no hopping (km) | Bandwidth (kHz) | Applications |
|---|---|---|---|
| 0.01–1 | 1000 (Very Long) | <1 (Very Low) | For Very Long Range and Very Low Bandwidth Applications: Ocean Monitoring, Marine Life Monitoring [15,16,17]. |
| 1–5 | 10–100 (Long) | 2–5 (Low) | For Long Range and Low Bandwidth Applications: Underwater Pipeline Monitoring and Natural Hazard Detection [8,9,10,11,18,19,20]. |
| 5–10 | 1–10 (Medium) | ≈10 (Medium) | For Medium Range and Medium Bandwidth Applications: Underwater Mapping, Locating Mineral Mines and Military Applications [2,13,14,21]. |
| 10–100 | 0.1–1 (Short) | 20–50 (High) | For Short Range and High Bandwidth Applications: Lake / River Water Quality monitoring [28,29,30,31]. |
| 100–1000 | <1 (Very Short) | >100 (Very High) | For Very Short Range and Very High Bandwidth Applications: Fresh Water Fish Farm [32,33,34]. |
| Sl. No. | Name of the Routing Protocols | Feature Based Classification | Classification Based on Localization |
|---|---|---|---|
| 1 | Vector Based Forwarding (VBF) [38] | Node Mobility | Location Based |
| 2 | Hop-by-Hop VBF (HH-VBF) [51] | Node Mobility | Location Based |
| 3 | Depth Based Routing (DBR) [52] | Node Mobility | Location Free |
| 4 | Virtual Tunneling Protocol (VTP) [53] | Node Mobility | Location Free |
| 5 | Cooperative Depth Based Routing (CoDBR) [54] | Node Mobility | Location Free |
| 6 | Energy-Efficient DBR (EEDBR) [55] | Energy Balancing | Location Free |
| 7 | Reliable Energy Efficient Pressure Based Routing (RE-PBR) [56] | Energy Balancing | Location Free |
| 8 | Directional Flooding-Based Routing (DFR) [57] | Channel Properties | Location Based |
| 9 | Location-Aware Routing Protocol (LARP) [58] | Channel Properties | Location Based |
| 10 | Focused beam routing (FBR) [59] | Energy Efficiency | Location Based |
| 11 | Distributed Underwater Clustering Scheme (DUCS) [60] | Energy Efficiency | Location Free |
| 12 | Sparsity-aware Energy Efficient Clustering Protocol (SEEC) [61] | Energy Efficiency | Location Free |
| 13 | Depth Based Multi-Hop Routing (DMBR) [62] | Energy Efficiency | Location Free |
| 14 | An Energy Balanced Efficient and Reliable Routing Protocol (EBER2) [63] | Network Void Hole Avoidance | Location Free |
| 15 | Regional Sink Mobility (RSM) [64] | Network Void Hole Avoidance | Location Free |
| 16 | Vertical sink Mobility (VSM) [64] | Network Void Hole Avoidance | Location Free |
| 17 | Weighting Depth and Forwarding Area Division DBR (WDFAD-DBR) [65] | Network Void Hole Avoidance | Location Free |
| Sl. No. | Name of the Protocols | Key Features | Main Drawbacks |
|---|---|---|---|
| 1 | Vector Based Forwarding (VBF) [38] | 1. End-to-End forwarding. 2. Location based scheme. 3. Only few nodes take part in routing where others sit idle. 4. Doesn’t require any state information. 5. Scalable to the network demand. 6. Energy efficient. 7. In dense network gives descent performance. | 1. In sparse network packet delivery rate degraded drastically. 2. Difficult to find proper routing radius threshold. |
| 2 | Hop-by-Hop VBF (HH-VBF) [51] | 1. The data transmission is done by ho-by-hop technique. 2. In Sparse region, it gives better packet delivery ratio than VBF. | 1. Gives more signal overhead than VBF. |
| 3 | Depth Based Routing (DBR) [52] | 1. Packet forwarding decision by a node is taken depending on its depth and the prior sender. 2. Only the depth information of the node is necessary. 3. Gives good performance in dense network. | 1. It works only in greedy mode. 2. Packet delivery ratio degrades in sparse network. |
| 4 | Virtual Tunneling Protocol (VTP) [53] | 1. It is a cluster based scheme. 2. It forms a virtual tunnel for a strong connection from source to the destination. 3. Three-way handshake is followed for packet data transfer. 4. It gives better packet delivery rate, latency in compared to CARP and MURAO. | 1. It might not be an energy efficient scheme as it follows three-way handshake to transfer single data packet. |
| 5 | Cooperative DBR (CoDBR) [54] | 1. DBR is incorporated with path diversity via multiple path to increase reliability. 2. Localization free protocol. 3. Next hop is selected based on the nodes having minimum depth. 4. Unlike DBR simultaneously same data is transmitted twice. 5. Data packet is dropped if it crosses the maximum allowable bit error rate. 6. It has higher reliability than DBR but it’s energy consumption is also higher than DBR. 7. It offers 83% more throughput and and 90% less packet drop. | 1. Energy consumption is higher than DBR. 2. Network life is shorter than DBR. |
| 6 | Reliable and Energy efficient PBR (RE-PBR) [56] | 1. Depth based and localization free protocol. 2. It measures link quality precisely with triangle metric. 3. Next forwarding node is selected basing on residual energy and triangle metric based link quality. 4. Its network lifetime is longer than DBR and EEDBR. 5. Comparing it to the DBR and EEDBR it gives better delivery ratio. 6. It consumes less energy than DBR and EEDBR but provides higher reliability than these two protocol. | 1. As the node increases, energy consumption increases in compared to DBR and EEDBR. |
| 7 | Directional Flooding-Based Routing (DFR) [57] | 1. Per hop forwarding is followed. 2. Comparing BASE ANGLE with CURRENT ANGLE a node decides whether to forward the data. 3. It gives better delivery ratio than VBF. 4. Shorter end-to-end delay and less communication overhead than VBF. | 1. Network is disrupted when a hole is created due to absence of any node near to the sink. |
| 8 | Location-Aware Routing Protocol (LARP) [58] | 1. Good packet delivery ratio. 2. To know the nodes’ location it uses a technique called RSSI. 3. Provides more reliable transmission than other routing protocols. | 1. To work perfectly it needs very dense network. 2. It has low delay efficiency. |
| 9 | Focused Beam Routing (FBR) [59] | 1. Avoids Unnecessary flooding. 2. It works well with both the steady and moving nodes. 3. A source node has to know only its position and position of the destination. 4. It reduces energy consumption by maintaining different power levels. | 1. This scheme increases the overhead. 2. Network is more restricted as the sink is fixed. |
| 10 | Distributed Underwater Clustering Scheme (DUCS) [60] | 1. It is a self changeable routing protocol which can assemble itself. 2. Distributed algorithm is used to form the clusters. 3. Intra-cluster Communications and inter-cluster communications are controlled by cluster head. 4. Random rotation of cluster head. 5. Energy efficient. 6. Increased throughput. | 1. Water current may reduce cluster life by affecting its structure. 2. Inter-cluster communications depend solely on cluster head. |
| 11 | Sparsity-aware energy efficient clustering protocol (SEEC) [61] | 1. SEEC is location free routing scheme which features the energy efficiency 2. The whole deployed region is divided into few regions and dense and sparse regions are sorted out. 3. UW-Sinks collect the data from the sparse region whereas clustering scheme is applied in dense network regions. 4. It gives better energy-efficiency, network life-time, delivery ratio in comparison to DBR and EEDBR | 1. SEEC gives lower data throughput in comparison to DBR and EEDBR. |
| 12 | Energy Balanced Efficient and Reliable Routing Protocol (EBER2) [63] | 1. Packet forwarding decision by a node is taken depending on its depth of first two hops. 2. It also considers Probable Forwarder Nodes of the next forwarder. 3. As it considers residual energy of the nodes for forwarding it also does energy optimization and energy distribution throughout the network. 4. It can avoid network void holes and gives better reliability. 5. It gives much better delivery ratio and overall performance than DBR, WDFAD-DBR and EEDBR. | 1. The delay efficiency of the network is average. 2. For the consideration of the PFNs the number of duplicate packet increased. |
| 13 | Regional Sink Mobility (RSM) and Vertical Sink Mobility (VSM) [64] | 1. One node must be aware of the location of its neighboring nodes. 2. In both RSM and VSM sensor nodes are randomly deployed. 3. The whole region is divides into 3 equal parts in RSM and 10 equal parts in VSM. 4. They both have improved throughput, data receive rate and initial network stability than SEEC. | 1. Both the schemes have low residual energy. 2. Their network lifetime is less than SEEC. |
| Sl. No. | Protocol | End-to-End/ Multi-Hop/ Clustering | Delivery Ratio | Energy Efficiency | Delay Efficiency | Localization Requirement | Reliability | Performance |
|---|---|---|---|---|---|---|---|---|
| 1 | VBF [38] | End-to-End | Low | Medium | Low | Not Needed | Low | Low |
| 2 | HH-VBF [51] | Multi-Hop | High | Low | Medium | Not Needed | High | Medium |
| 3 | DBR [52] | Multi-Hop | High | Medium | High | Not Needed | High | High |
| 4 | VTP [53] | Multi-Hop and Clustering | Very High | Low | Very High | Not Needed | High | High |
| 5 | CoDBR [54] | Multi-Hop | Very High | Low | Medium | Not Needed | Very High | High |
| 6 | EEDBR [55] | Multi-Hop | High | High | High | Not Needed | High | High |
| 7 | RE-PBR [56] | Multi-Hop | Very High | High | Very High | Not Needed | Very High | Very High |
| 8 | DFR [57] | Multi-Hop | Medium | Medium | Medium | Needed | High | Medium |
| 9 | LARP [58] | Multi-Hop | High | Medium | Low | Needed | High | High |
| 10 | FBR [59] | Multi-Hop | Medium | Medium | High | Partially Needed | Medium | High |
| 11 | DUCS [60] | Multi-Hop | Medium | High | Low | Not Needed | Low | Low |
| 12 | SEEC [61] | Clustering | Medium | Very High | High | Not Needed | High | High |
| 13 | EBER2 [63] | Multi-Hop | Very High | Very High | Medium | Not Needed | Very High | Very High |
| 14 | RSM and VSM [64] | Multi-Hop and Clustering | High | Medium | High | Not Needed | High | High |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Haque, K.F.; Kabir, K.H.; Abdelgawad, A. Advancement of Routing Protocols and Applications of Underwater Wireless Sensor Network (UWSN)—A Survey. J. Sens. Actuator Netw. 2020, 9, 19. https://doi.org/10.3390/jsan9020019
Haque KF, Kabir KH, Abdelgawad A. Advancement of Routing Protocols and Applications of Underwater Wireless Sensor Network (UWSN)—A Survey. Journal of Sensor and Actuator Networks. 2020; 9(2):19. https://doi.org/10.3390/jsan9020019
Chicago/Turabian StyleHaque, Khandaker Foysal, K. Habibul Kabir, and Ahmed Abdelgawad. 2020. "Advancement of Routing Protocols and Applications of Underwater Wireless Sensor Network (UWSN)—A Survey" Journal of Sensor and Actuator Networks 9, no. 2: 19. https://doi.org/10.3390/jsan9020019
APA StyleHaque, K. F., Kabir, K. H., & Abdelgawad, A. (2020). Advancement of Routing Protocols and Applications of Underwater Wireless Sensor Network (UWSN)—A Survey. Journal of Sensor and Actuator Networks, 9(2), 19. https://doi.org/10.3390/jsan9020019






