A Mechanism for Securing IoT-enabled Applications at the Fog Layer
Abstract
:1. Introduction
1.1. Problem Statement
1.2. Contributions
- A Fog Security Service (FSS) to provide identity-based authentication, the integrity of data, and non-repudiation of connected nodes.
- A Private Key Generator (PKG) at fog layer to enhance end-to-end security between IoT and fog layer.
- Implementation and evaluation of the proposed FSS to demonstrate the appropriateness of the proposed mechanism.
1.3. Paper Structure
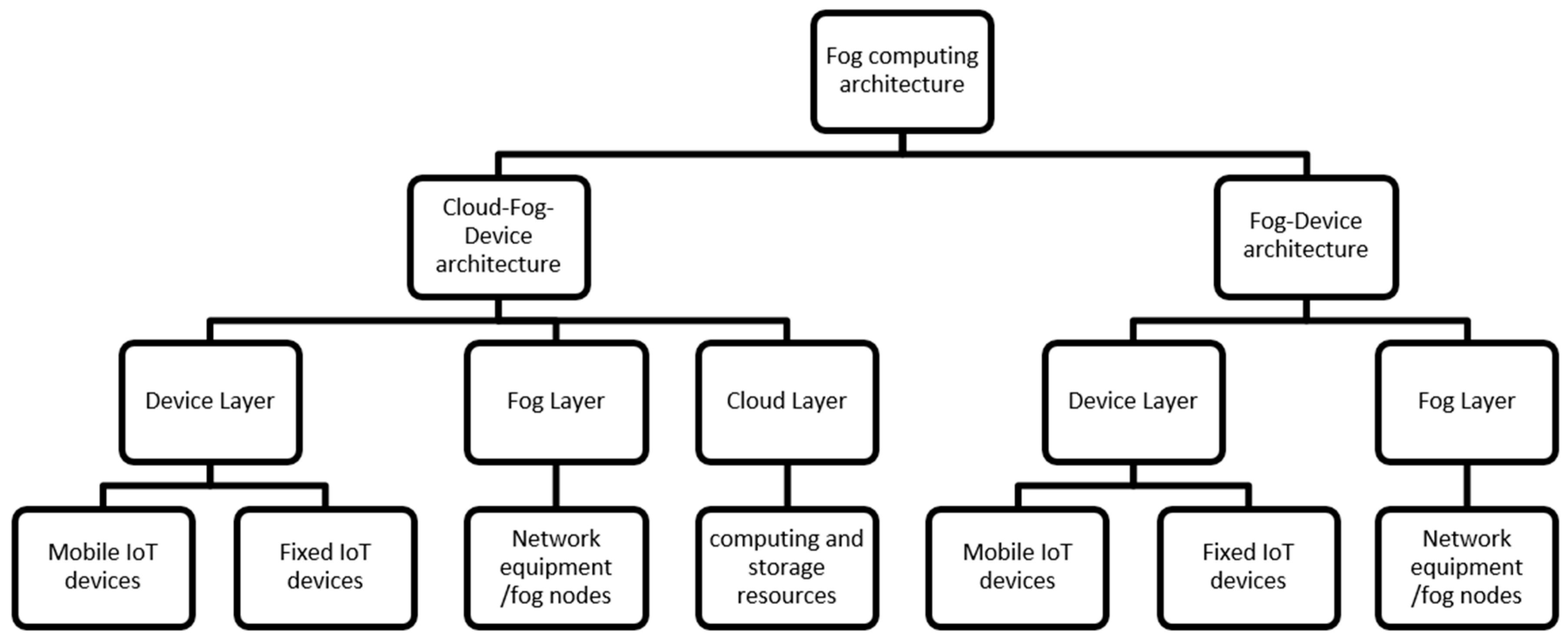
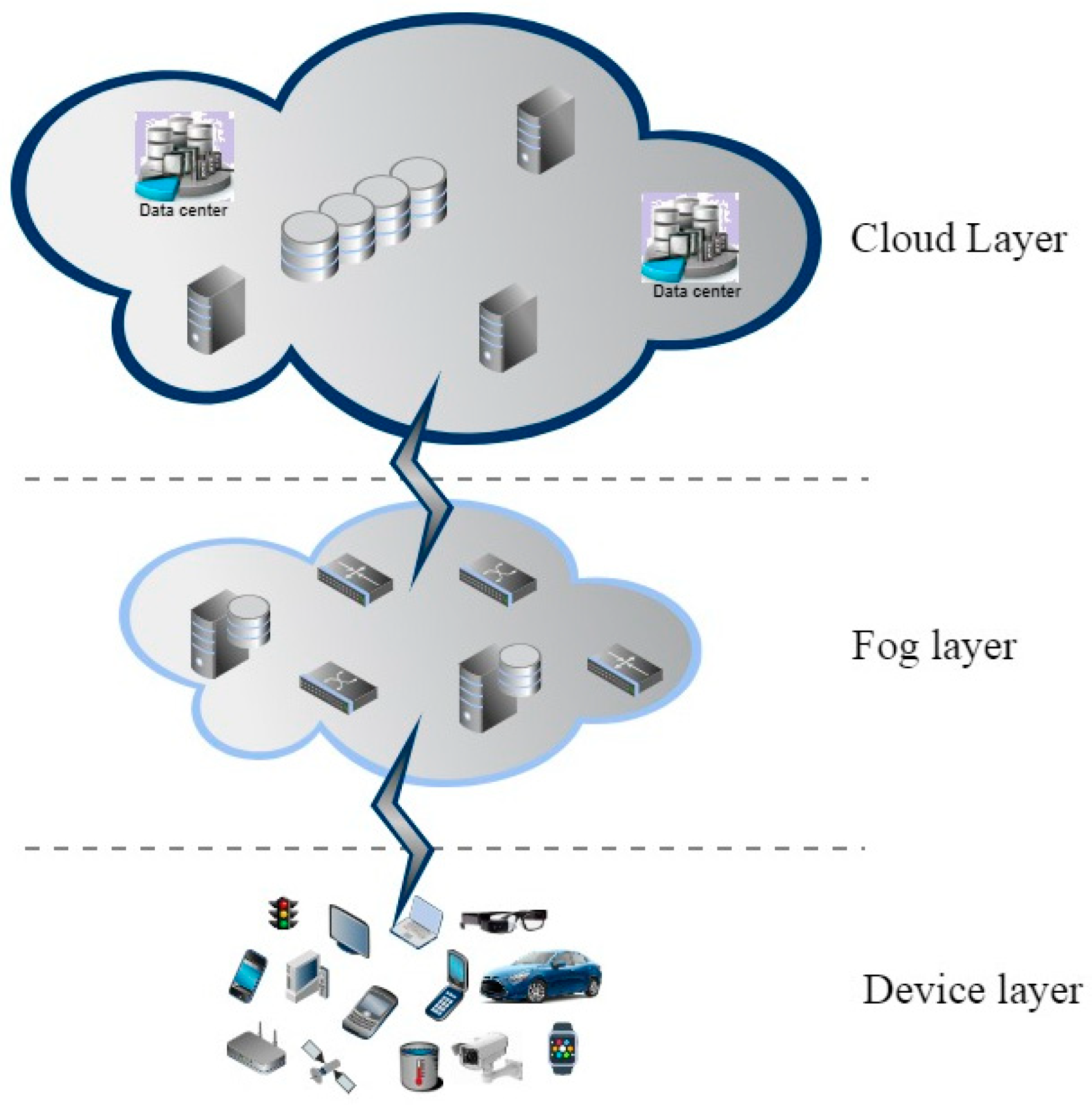
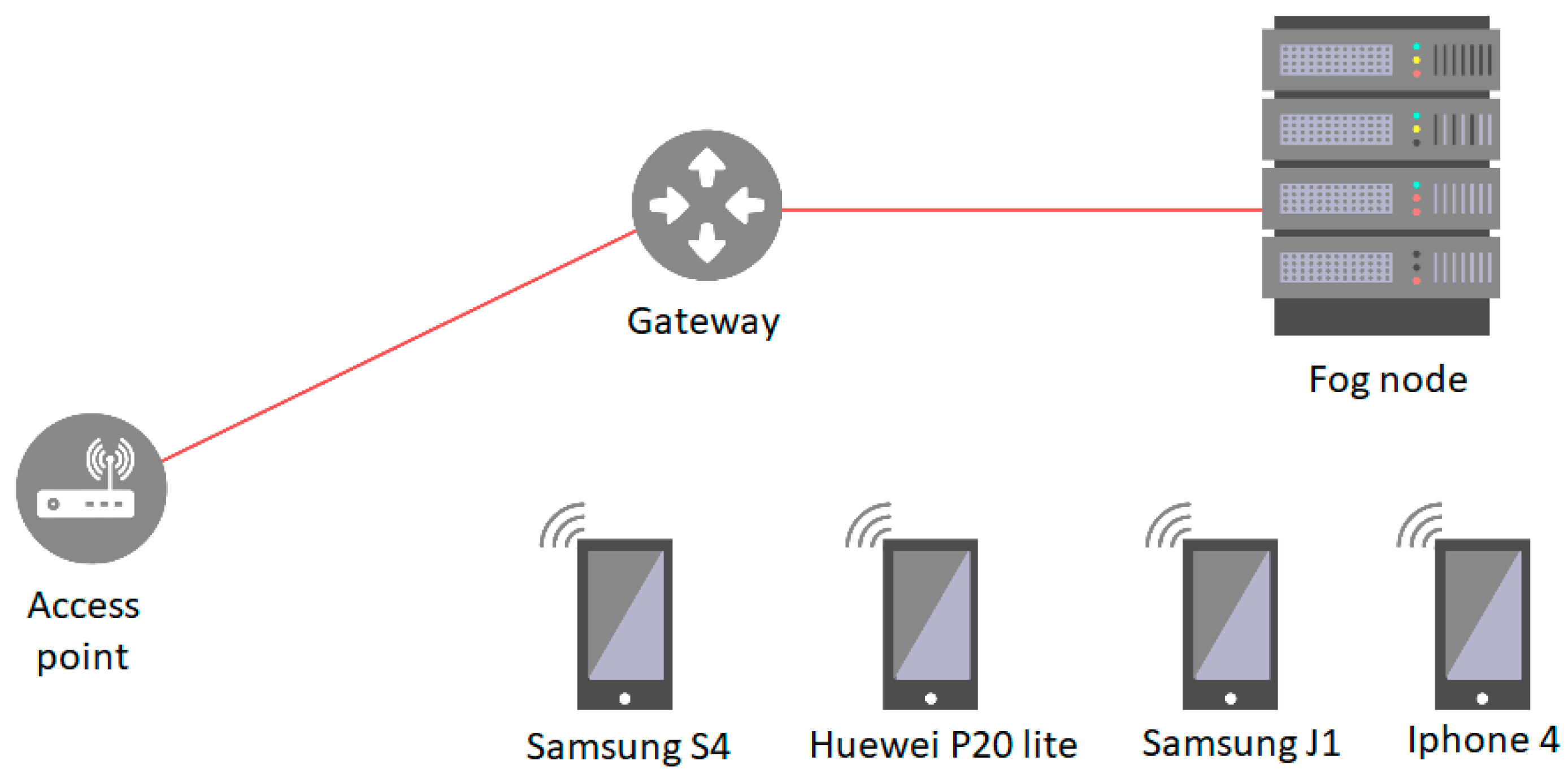
2. Fog Computing Architecture
2.1. Cloud-Fog-Device Architecture
2.2. Fog-Device Architecture
3. Security Threats
- Authentication: It is a process of validation and verification to prove one’s identity as a legitimate user.
- Confidentiality: This property ensures that data is not exposed to unauthorized sources. It ensures adversaries do not gain unauthorized access to data.
- Integrity: Integrity refers to the completeness and accuracy of data. It ensures that data have not been changed and hence received as accurately as sent.
- Availability: It guarantees provisioning of network services and data to authorized users when required.
- Non-repudiation: It refers to ownership of data. It ensures that sender cannot deny having sent the data and the receiver cannot deny having received the data.
4. Related Work
5. Proposed Methodology
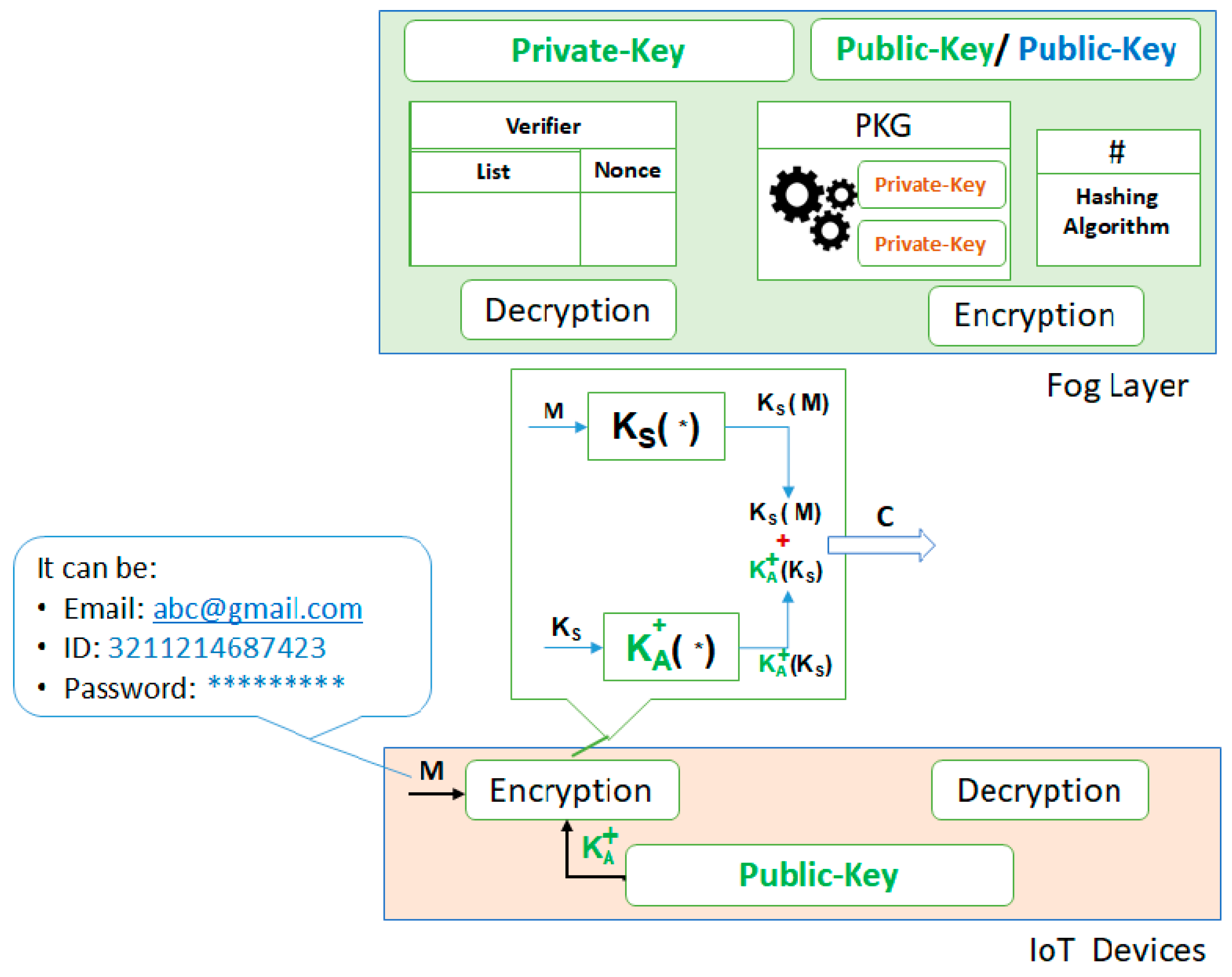
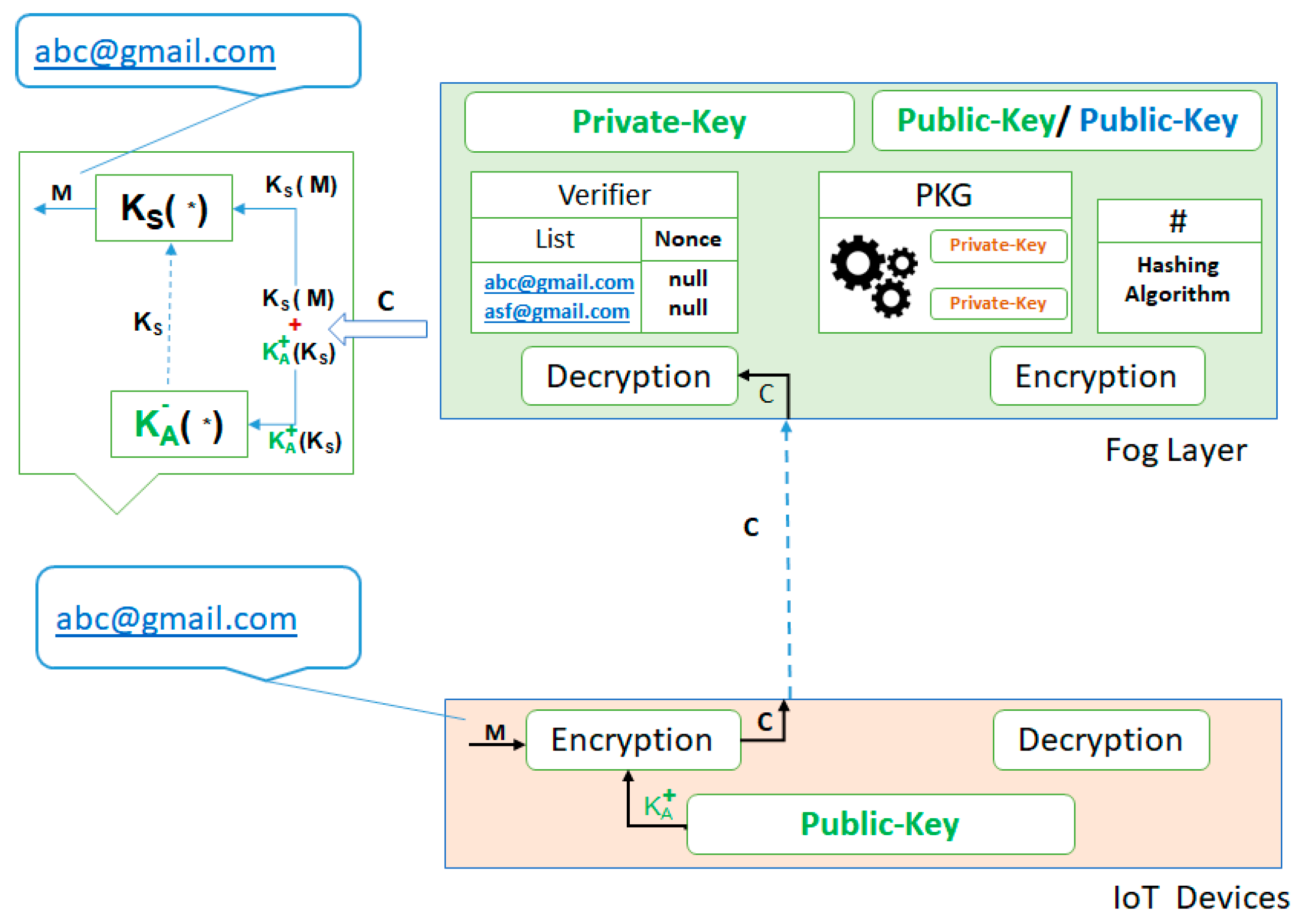
- (1)
- The device, which wants to communicate with the fog layer, provides security params denoted by IDrec, which can be any string such as an email address (e.g., abc@gmail.com), a unique identifier (e.g., 3211214687423), or password (e.g., ******).
- The IoT device that wants to communicate with the fog layer generates a small size secret-key Ks (e.g., 128 bit) for the encryption of IDrec. A nonce value is also added with that IDrec. Then, secret-key is used to encrypt the IDrec along with the provided nonce.
- Encrypt the already generated small size secret-key Ks by using the fog layer public key and then, combine both the cipher text (encrypted (IDrec + nonce) and encrypted (secret-key)), denoted as C.
- The cipher text C is forwarded to the fog layer for the authentication, as shown in Figure 3.
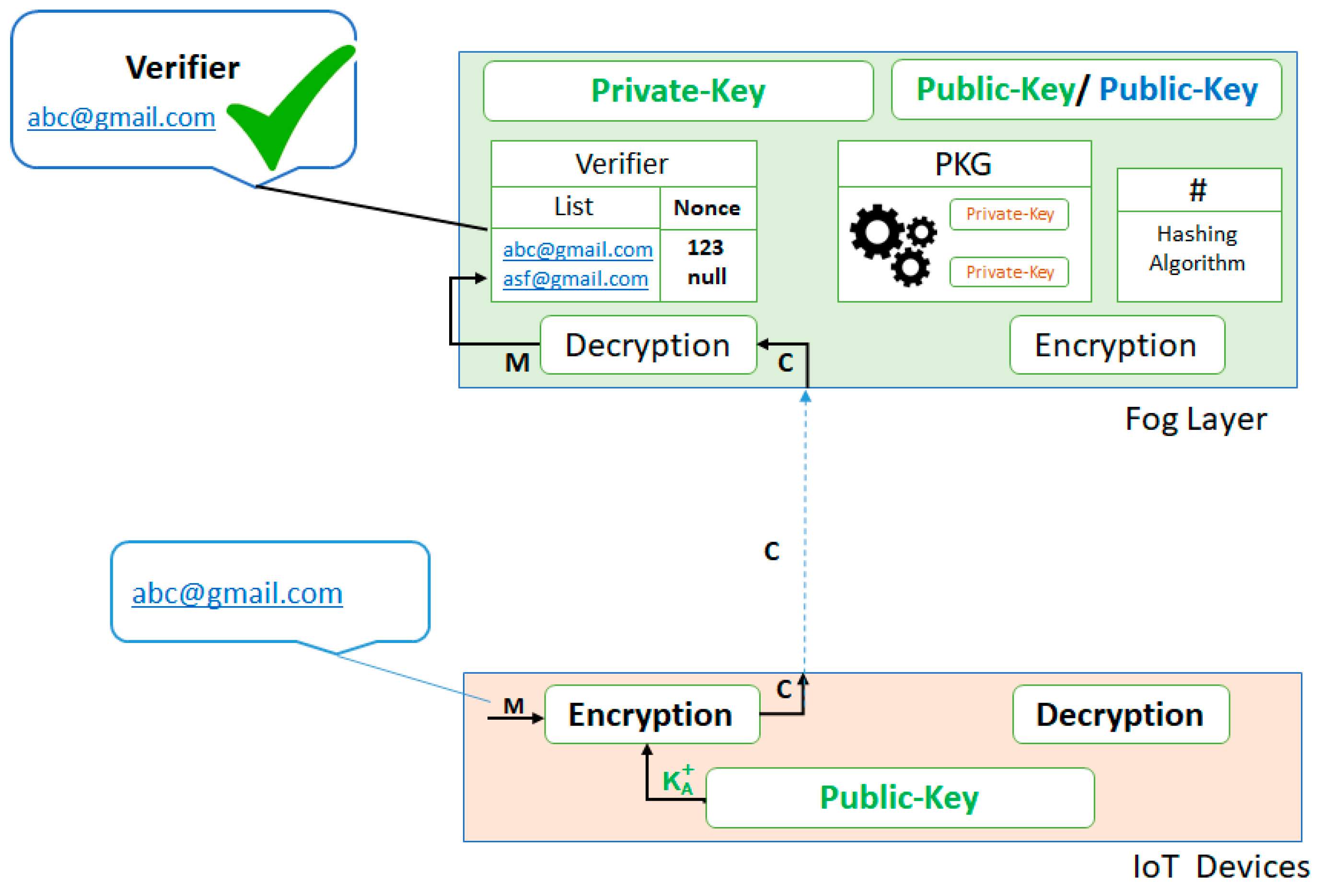
- (2)
- Cipher text C is received at the fog layer, where a decryption algorithm (fog layer private key) is applied to get the original message, thereby separating both the information received in the cipher text C (i.e., IDrec + nonce and secret-key Ks).
- Apply the fog layer private key on the encrypted secret key Ks to get the original secret key (Ks).
- Apply the secret key Ks on the cipher text (IDrec + nonce) to get the original IDrec and nonce values, as shown in Figure 4.
- The Verifier at the fog layer authenticates the received IDrec against the list of registered devices. If it is matched then the Verifier saves its nonce, as shown in Figure 5.
- After authentication, the Verifier sends a request to the PKG to generate a private key for that authenticated IoT device.
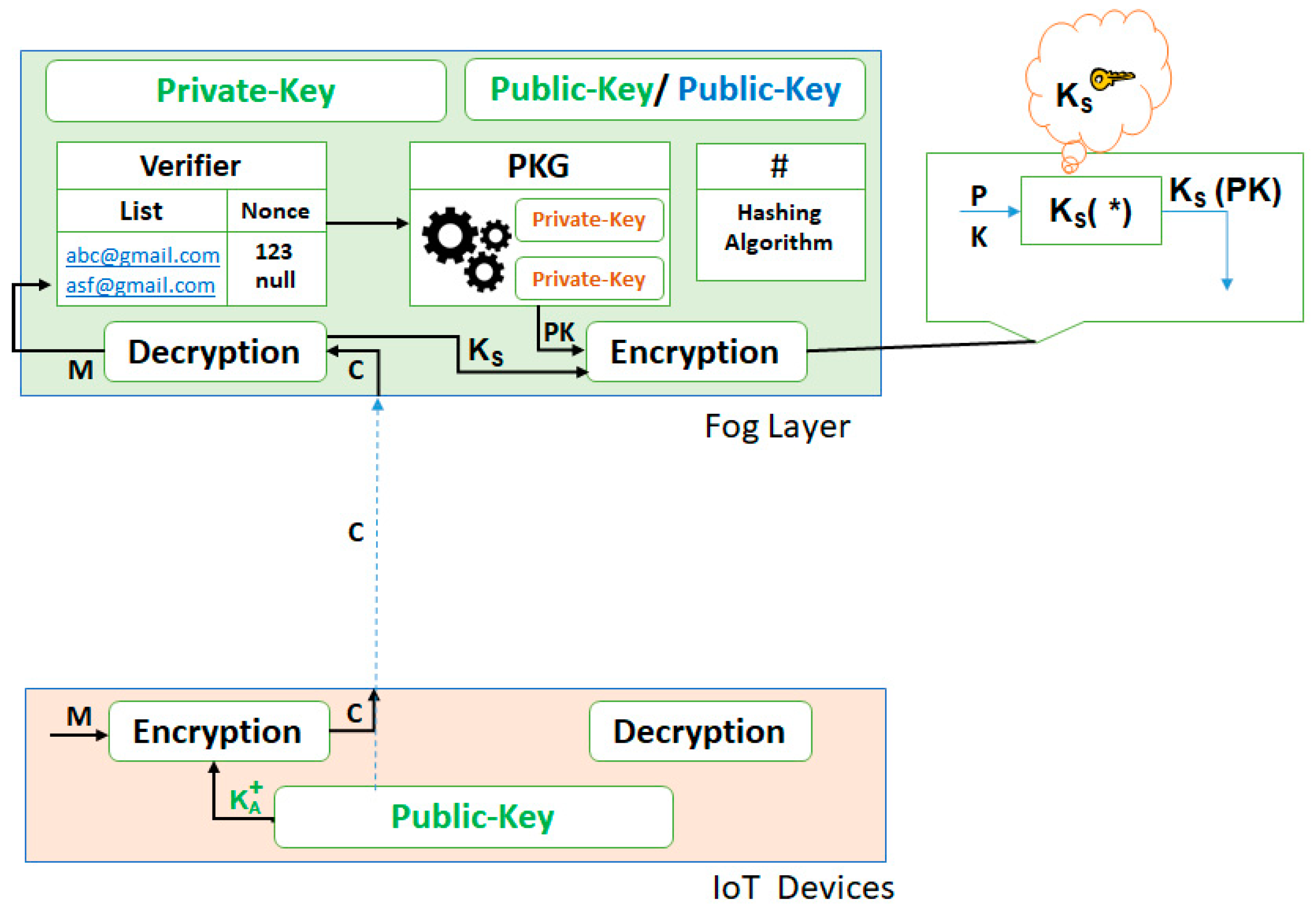
- (3)
- The PKG generates private keys for the authenticated devices and sends those keys to the encryption algorithm for encryption.
- (4)
- The secret key Ks, which is received from the IoT device, is used to encrypt the PKG generated private key PK, as shown in Figure 6.
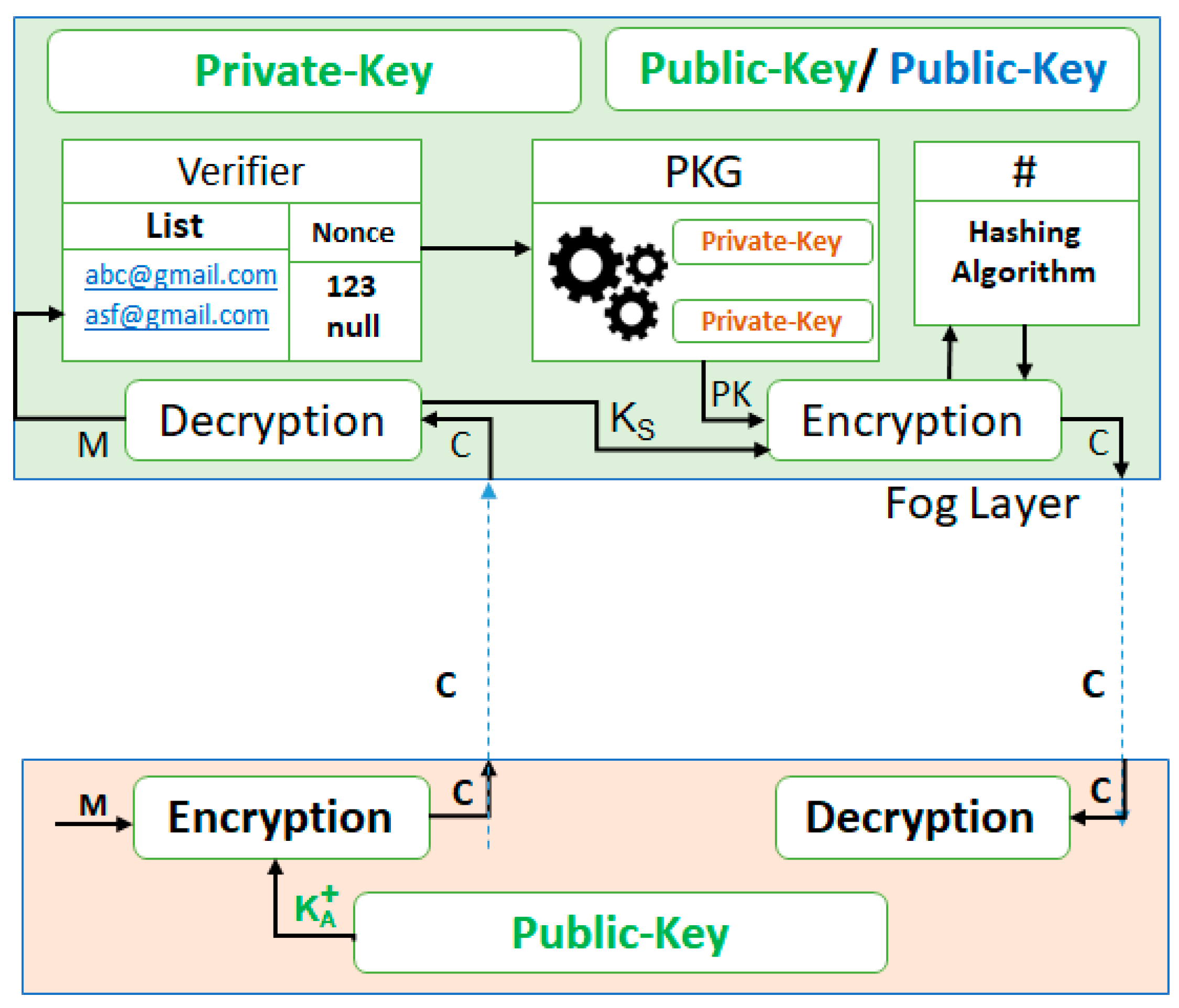
- (5)
- In addition, for the non-repudiation requirement, the cipher text is further encrypted with the fog layer’s private key, and sends this information back to the authenticated device, as shown in Figure 7. The device can then apply the fog layer’s public key to ensure that the message is indeed received from the fog layer.
- (6)
- The authenticated IoT device then applies the decryption process to get the private key PK from the received cipher text and:
- Applies the secret key (Ks) on the encrypted message to get the private key PK.
- (7)
- After successfully receiving the private key PK in a secure manner, authenticated IoT device can communicate with the fog layer through this private key PK.
- (8)
- The private key PK is then used for the encryption and decryption on both sides to enable end-to-end security.
| Algorithm 1: FSS—Authentication and Private-Key Generation Algorithm |
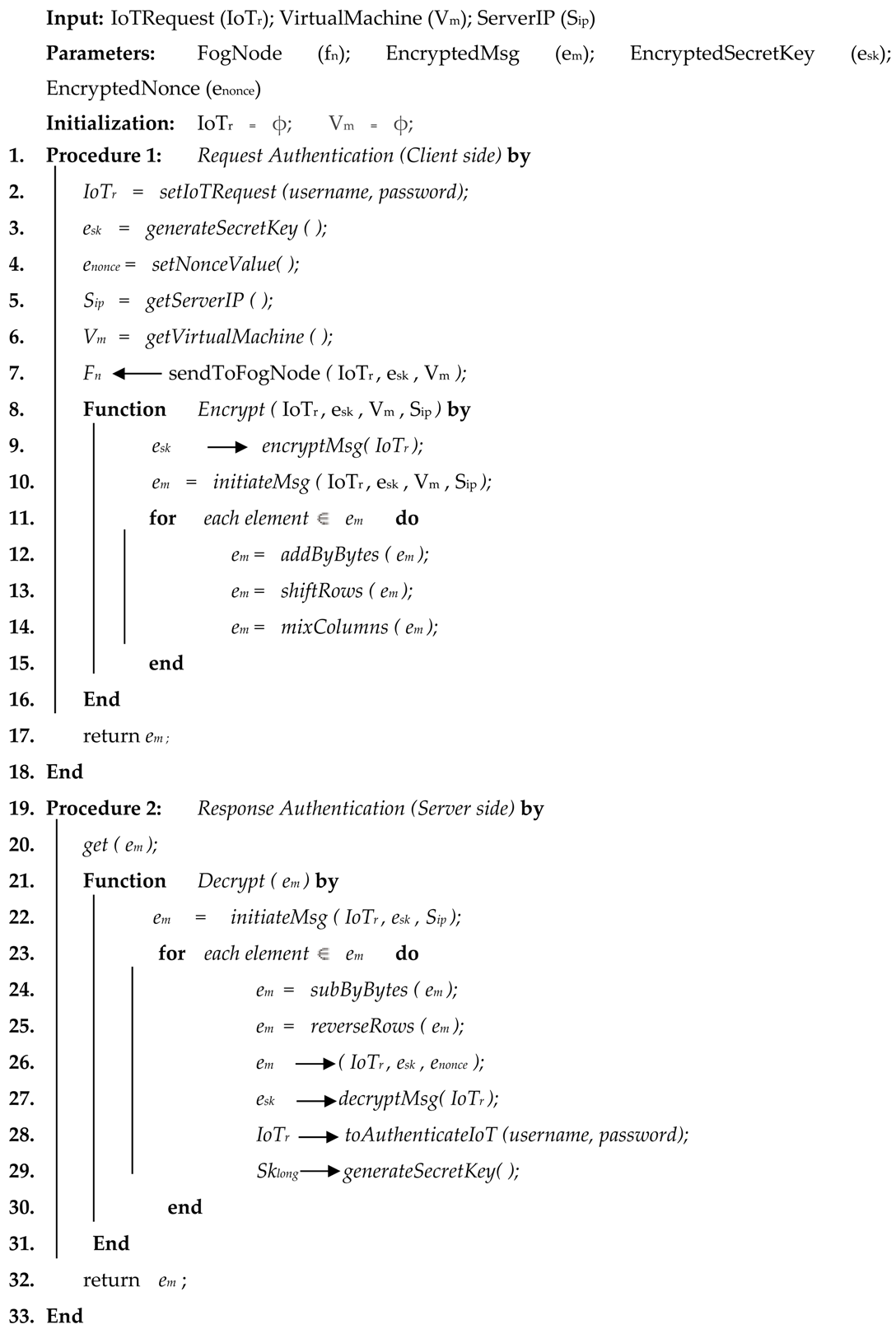 |
6. Evaluation Results
7. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- Ni, J.; Zhang, K.; Lin, X.; Shen, X.S. Securing fog computing for internet of things applications: Challenges and solutions. IEEE Commun. Surv. Tutor. 2017, 20, 601–628. [Google Scholar] [CrossRef]
- Abuarqoub, A.; Abusaimeh, H.; Hammoudeh, M.; Uliyan, D.; Abu-Hashem, M.A.; Murad, S.; Al-Jarrah, M.; Al-Fayez, F. A Survey on Internet of Thing Enabled Smart Campus Applications. In Proceedings of the International Conference on Future Networks and Distributed Systems, (ICFNDS ’17), New York, NY, USA, 19–20 July 2017; pp. 1–7. [Google Scholar]
- Baker, T.; Asim, M.; Tawfik, H.; Aldawsari, B.; Buyya, R. An energy-aware service composition algorithm for multiple cloud-based IoT applications. J. Netw. Comput. Appl. 2017, 89, 96–108. [Google Scholar] [CrossRef]
- Camhi, J. Former Cisco CEO John Chambers Predicts 500 Billion Connected Devices by 2025. Business Insider, 2015. Available online: https://www.businessinsider.com/former-cisco-ceo-500-billion-connected-devices-by-2025-2015-11?r=US&IR=T&IR=T (accessed on 15 December 2018).
- Federal Trade Commission. Internet of Things: Privacy & Security in a Connected World; Federal Trade Commission: Washington, DC, USA, 2015.
- Yi, S.; Hao, Z.; Qin, Z.; Li, Q. Fog computing: Platform and applications. In Proceedings of the 2015 Third IEEE Workshop on Hot Topics in Web Systems and Technologies (HotWeb), Washington, DC, USA, 12–13 November 2015; pp. 73–78. [Google Scholar]
- Mahmud, R.; Kotagiri, R.; Buyya, R. Fog computing: A taxonomy, survey and future directions. In Internet of Everything; Springer: Singapore, 2018; pp. 103–130. [Google Scholar]
- Maamar, Z.; Baker, T.; Sellami, M.; Asim, M.; Ugljanin, E.; Faci, N. Cloud vs edge: Who serves the Internet-of-Things better? Internet Technol. Lett. 2018, 1, e66. [Google Scholar] [CrossRef]
- Liang, K.; Zhao, L.; Chu, X.; Chen, H.H. An integrated architecture for software defined and virtualized radio access networks with fog computing. IEEE Netw. 2017, 31, 80–87. [Google Scholar] [CrossRef]
- Agustin, J.P.C.; Jacinto, J.H.; Limjoco, W.J.R.; Pedrasa, I. IPv6 routing protocol for low-power and lossy networks implementation in network simulator—3. In Proceedings of the TENCON 2017—2017 IEEE Region 10 Conference, Penang, Malaysia, 5–8 November 2017; pp. 3129–3134. [Google Scholar]
- Lee, K.; Kim, D.; Ha, D.; Rajput, U.; Oh, H. On security and privacy issues of fog computing supported Internet of Things environment. In Proceedings of the 6th International Conference on Network of the Future (NOF), Montreal, QC, Canada, 30 September–2 October 2015; pp. 1–3. [Google Scholar]
- Yi, S.; Qin, Z.; Li, Q. Security and privacy issues of fog computing: A survey. In Proceedings of the International Conference on Wireless Algorithms, Systems, and Applications, Qufu, China, 10–12 August 2015; pp. 685–695. [Google Scholar]
- Atwady, Y.; Hammoudeh, M. A survey on authentication techniques for the internet of things. In Proceedings of the International Conference on Future Networks and Distributed Systems, Cambridge, UK, 19–20 July 2017; p. 8. [Google Scholar]
- Trappe, W.; Howard, R.; Moore, R.S. Low-energy security: Limits and opportunities in the internet of things. IEEE Secur. Priv. 2015, 13, 14–21. [Google Scholar] [CrossRef]
- Fan, Q.; Ansari, N. Towards Workload Balancing in Fog Computing Empowered IoT. IEEE Trans. Netw. Sci. Eng. 2018, 22, 820–823. [Google Scholar] [CrossRef]
- Yousefpour, A.; Ishigaki, G.; Gour, R.; Jue, J.P. On reducing iot service delay via fog offloading. IEEE Internet Things J. 2018, 5, 998–1010. [Google Scholar] [CrossRef]
- Naha, R.K.; Garg, S.; Georgakopoulos, D.; Jayaraman, P.P.; Gao, L.; Xiang, Y.; Ranjan, R. Fog Computing: Survey of trends, architectures, requirements, and research directions. IEEE Access 2018, 6, 47980–48009. [Google Scholar] [CrossRef]
- Alrawais, A.; Alhothaily, A.; Hu, C.; Cheng, X. Fog computing for the internet of things: Security and privacy issues. IEEE Internet Comput. 2017, 21, 34–42. [Google Scholar] [CrossRef]
- Ammar, M.; Russello, G.; Crispo, B. Internet of Things: A survey on the security of IoT frameworks. J. Inf. Secur. Appl. 2018, 38, 8–27. [Google Scholar] [CrossRef]
- Mahmood, Z. Fog Computing: Concepts, Frameworks and Technologies; Springer International Publishing: New York, NY, USA, 2018. [Google Scholar]
- Stojmenovic, I.; Wen, S.; Huang, X.; Luan, H. An overview of fog computing and its security issues. Concurr. Comput. Pract. Exp. 2016, 28, 2991–3005. [Google Scholar] [CrossRef]
- Khan, S.; Parkinson, S.; Qin, Y. Fog computing security: A review of current applications and security solutions. J. Cloud Comput. 2017, 6, 19. [Google Scholar] [CrossRef]
- Mukherjee, M.; Matam, R.; Shu, L.; Maglaras, L.; Ferrag, M.A.; Choudhury, N.; Kumar, V. Security and privacy in fog computing: Challenges. IEEE Access 2017, 5, 19293–19304. [Google Scholar] [CrossRef]
- Naher, N.; Haque, M.M. Authentication of Diffie-Hellman Protocol against Man-in-the-Middle Attack Using Cryptographically Secure CRC. In Proceedings of the International Ethical Hacking Conference 2018; Springer: Singapore, 2019; pp. 139–150. [Google Scholar]
- Lu, Y.; Da Xu, L. Internet of Things (IoT) cybersecurity research: A review of current research topics. IEEE Internet Things J. 2018. [Google Scholar] [CrossRef]
- Pinkas, B.; Sander, T. Securing passwords against dictionary attacks. In Proceedings of the 9th ACM conference on Computer and communications security, Washington, DC, USA, 18–22 November 2002; pp. 161–170. [Google Scholar]
- Sathiyaseelan, A.M.; Joseph, V.; Srinivasaraghavan, A. A proposed system for preventing session hijacking with modified one-time cookies. In Proceedings of the Big Data Analytics and Computational Intelligence (ICBDAC), Chirala, India, 23–25 March 2017; pp. 451–454. [Google Scholar]
- Mejri, M.N.; Ben-Othman, J.; Hamdi, M. Survey on VANET security challenges and possible cryptographic solutions. Veh. Commun. 2014, 1, 53–66. [Google Scholar] [CrossRef]
- Gupta, B.B.; Arachchilage, N.A.; Psannis, K.E. Defending against phishing attacks: Taxonomy of methods, current issues and future directions. Telecommun. Syst. 2018, 67, 247–267. [Google Scholar] [CrossRef]
- Stojmenovic, I.; Wen, S. The fog computing paradigm: Scenarios and security issues. In Proceedings of the Federated Conference on Computer Science and Information Systems (FedCSIS), Warsaw, Poland, 7–10 September 2014; pp. 1–8. [Google Scholar]
- Du, R.; Zhao, C.; Li, S.; Li, J. A Strategy of Network Coding Against Wiretapping Attack Based on Network Segmentation. In Proceedings of the Second International Conference on Communications, Signal Processing, and Systems; Springer: Cham, Switzerland, 2014; pp. 1137–1144. [Google Scholar]
- Hamed, T.; Ernst, J.B.; Kremer, S.C. A survey and taxonomy of classifiers of intrusion detection systems. In Computer and Network Security Essentials; Springer: Cham, Switzerland, 2018; pp. 21–39. [Google Scholar]
- Bonomi, F.; Milito, R.; Natarajan, P.; Zhu, J. Fog computing: A platform for internet of things and analytics. In Big Data and Internet of Things: A Roadmap for Smart Environments; Springer: Cham, Switzerland, 2014; pp. 169–186. [Google Scholar]
- Hong, K.; Lillethun, D.; Ramachandran, U.; Ottenwälder, B.; Koldehofe, B. Mobile fog: A programming model for large-scale applications on the internet of things. In Proceedings of the Second ACM SIGCOMM Workshop on Mobile Cloud Computing, Hong Kong, China, 16 August 2013; pp. 15–20. [Google Scholar]
- Abdo, J.B. Authentication proxy as a service. In Proceedings of the Second International Conference on Fog and Mobile Edge Computing (FMEC), Valencia, Spain, 8–11 May 2017; pp. 45–49. [Google Scholar]
- Ethelbert, O.; Moghaddam, F.F.; Wieder, P.; Yahyapour, R. A JSON Token-Based Authentication and Access Management Schema for Cloud SaaS Applications. arXiv, 2017; arXiv:1710.08281. [Google Scholar]
- Dsouza, C.; Ahn, G.J.; Taguinod, M. Policy-driven security management for fog computing: Preliminary framework and a case study. In Proceedings of the IEEE 15th International Conference on Information Reuse and Integration (IRI), Redwood City, CA, USA, 13–15 August 2014; pp. 16–23. [Google Scholar]
- Bamasag, O.; Toumi, K.Y. Efficient multicast authentication in internet of things. In Proceedings of the International Conference on Information and Communication Technology Convergence (ICTC), Jeju, Korea, 19–21 October 2016; pp. 429–435. [Google Scholar]
- Salman, O.; Abdallah, S.; Elhajj, I.H.; Chehab, A.; Kayssi, A. Identity-based authentication scheme for the internet of things. In Proceedings of the IEEE Symposium on Computers and Communication (ISCC), Messina, Italy, 27–30 June 2016; pp. 1109–1111. [Google Scholar]
- Kalkan, K.; Zeadally, S. Securing internet of things (iot) with software defined networking (sdn). IEEE Commun. Mag. 2017, 56, 186–192. [Google Scholar] [CrossRef]
- Porambage, P.; Schmitt, C.; Kumar, P.; Gurtov, A.; Ylianttila, M. Two-phase authentication protocol for wireless sensor networks in distributed IoT applications. In Proceedings of the Wireless Communications and Networking Conference (WCNC), Istanbul, Turkey, 6–9 April 2014; pp. 2728–2733. [Google Scholar]
- Challa, S.; Wazid, M.; Das, A.K.; Kumar, N.; Reddy, A.G.; Yoon, E.J.; Yoo, K.Y. Secure signature-based authenticated key establishment scheme for future IoT applications. IEEE Access 2017, 5, 3028–3043. [Google Scholar] [CrossRef]
- Raz, A.K.; Kenley, C.R.; DeLaurentis, D.A. System architecting and design space characterization. Syst. Eng. 2018, 21, 227–242. [Google Scholar] [CrossRef]
- Parnell, G.S. (Ed.) Trade-Off Analytics: Creating and Exploring the System Tradespace; John Wiley & Sons: Hoboken, NJ, USA, 2016. [Google Scholar]
| Property | Attack | Description |
|---|---|---|
| Authentication | Brute Force | The attacker guesses a person’s password, user name, secret key (e.g., used for encryption and decryption), and credit card number by each and every possible combination using automated trial and error process [23]. |
| Insufficient Authentication | Allow invaders to access a website that contains sensitive and important contents. These websites are not directly addressable without the user’s necessity to accurately verify their identity [23]. | |
| Man-in-the-Middle | The adversary devises access the networks and insert themselves in between the server and User to gain unauthorized control [24]. | |
| Replay attacks | The identity of IoT devices is spoofed, altered, or replayed in order to intercept or retransmit the data [25]. | |
| Dictionary | All possible words from a dictionary are used to make an attack on authentication data [26]. | |
| Eavesdropping | Malicious invaders capture the packets and read its content by listening the communication channels. If the encryption and decryption algorithms are not used in data, then this attack may be quite effective [25]. | |
| Session Hijacking | Transmission Control Protocol (TCP) session is hijacked to steal session tokens to gain the unauthorized access to a server [27]. | |
| Key and/or Certificate Replication attack | Duplicate keys or certificates of identification proof are used to create ambiguity to disrupt the identification and authentication process [28]. | |
| Confidentiality | Packet Capturing (Packet Sniffing) | Attacker captures the data and information packets from Ethernet frames during communication. They can also read the sensitive information such as passwords, usernames, and credit card numbers if the traffic of the network is not encrypted [29,30]. |
| Wiretapping | One or more edges may get affected in such attacks to compromise the transient data confidentiality. Adversaries wiretap a links to obtain a part of data for decoding a packet [31]. | |
| Non-Repudiation | Repudiation Attack | Either false information is spread, or real event or transaction denial is attempted by the attacker to prove themselves as legitimate participants. |
| Masquerading | It is a kind of impersonation attack where adversary may attempt to impersonate the identity of other nodes for communication and transaction processing [32]. |
| Name | Description | |||||
|---|---|---|---|---|---|---|
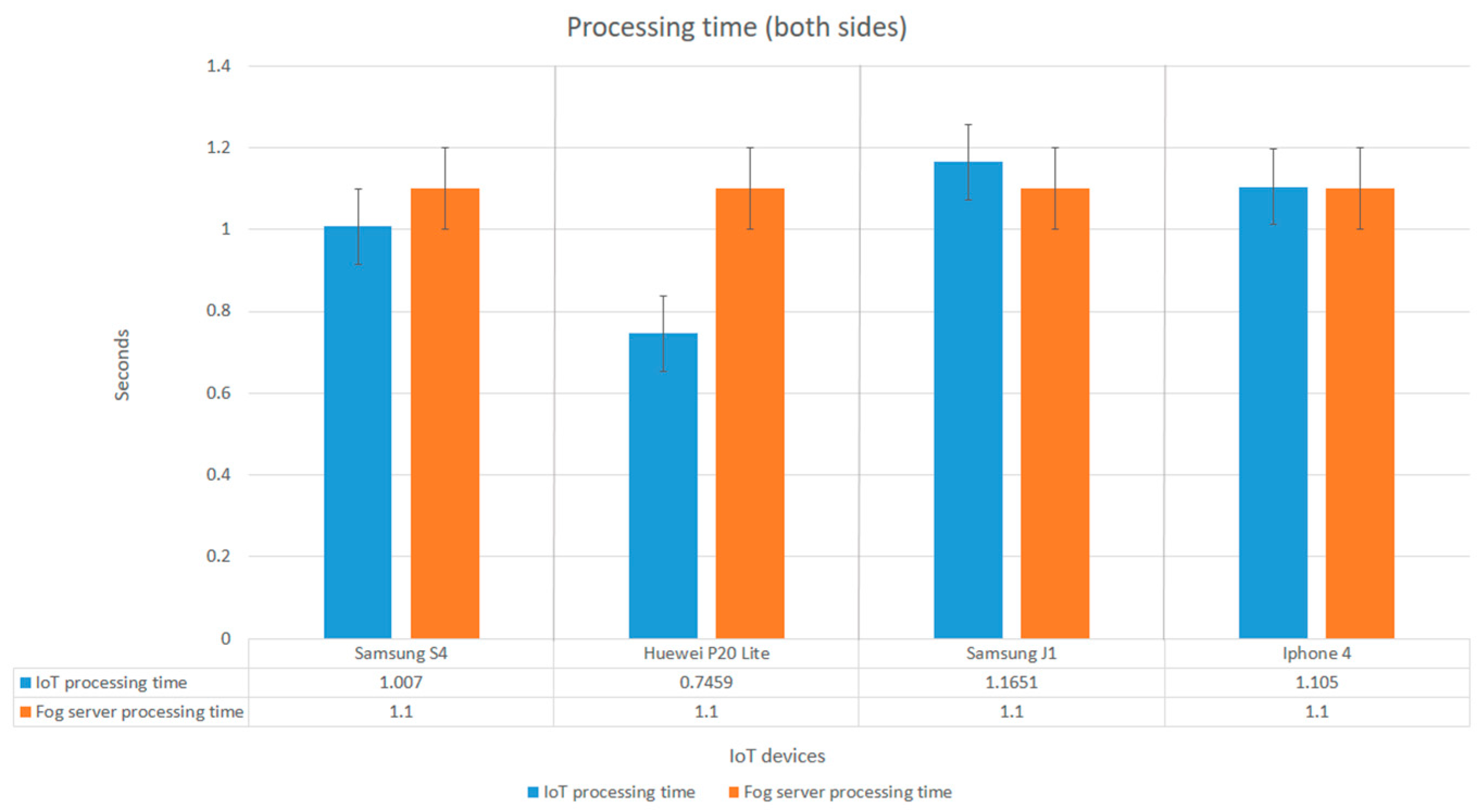
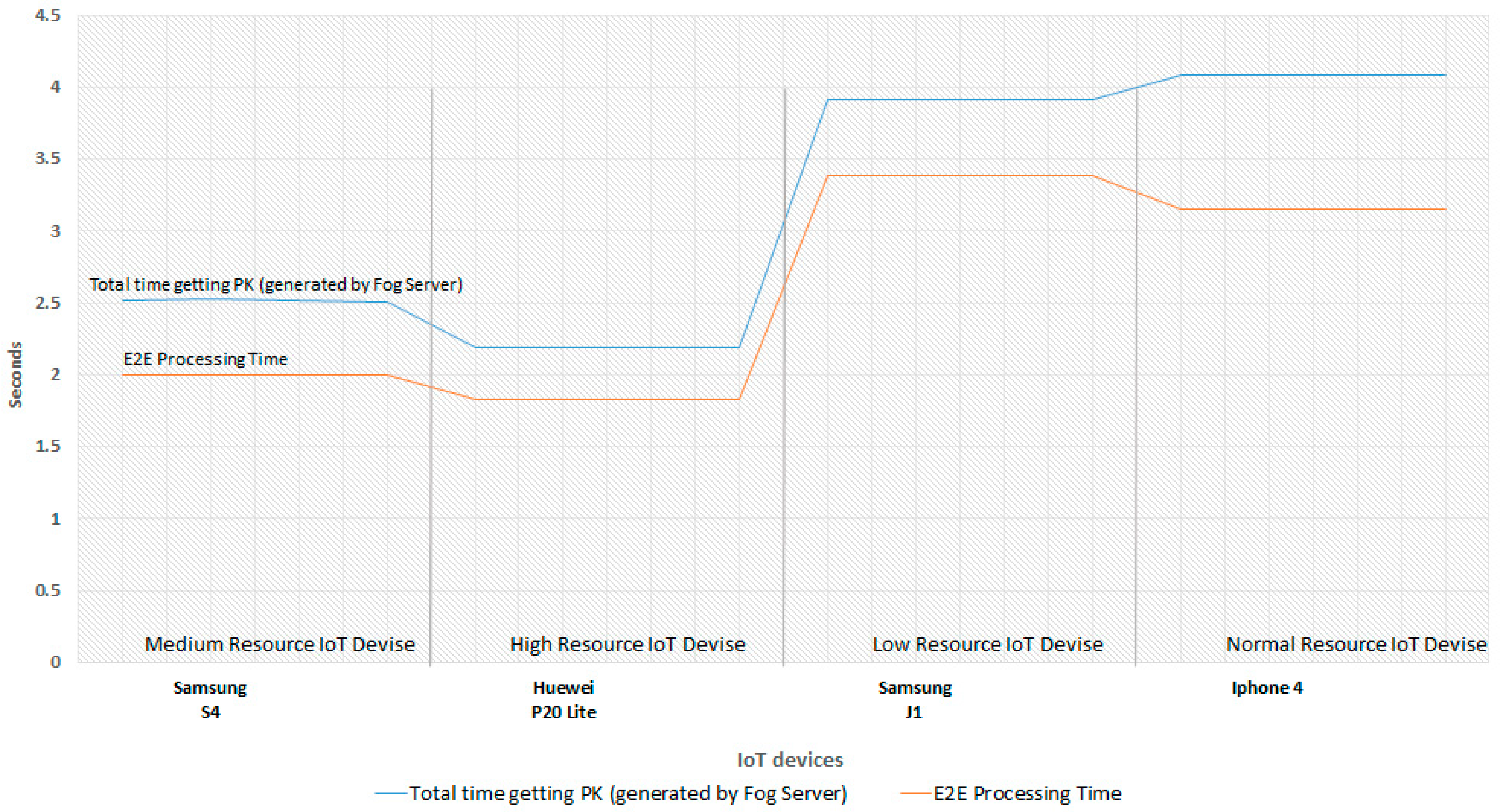
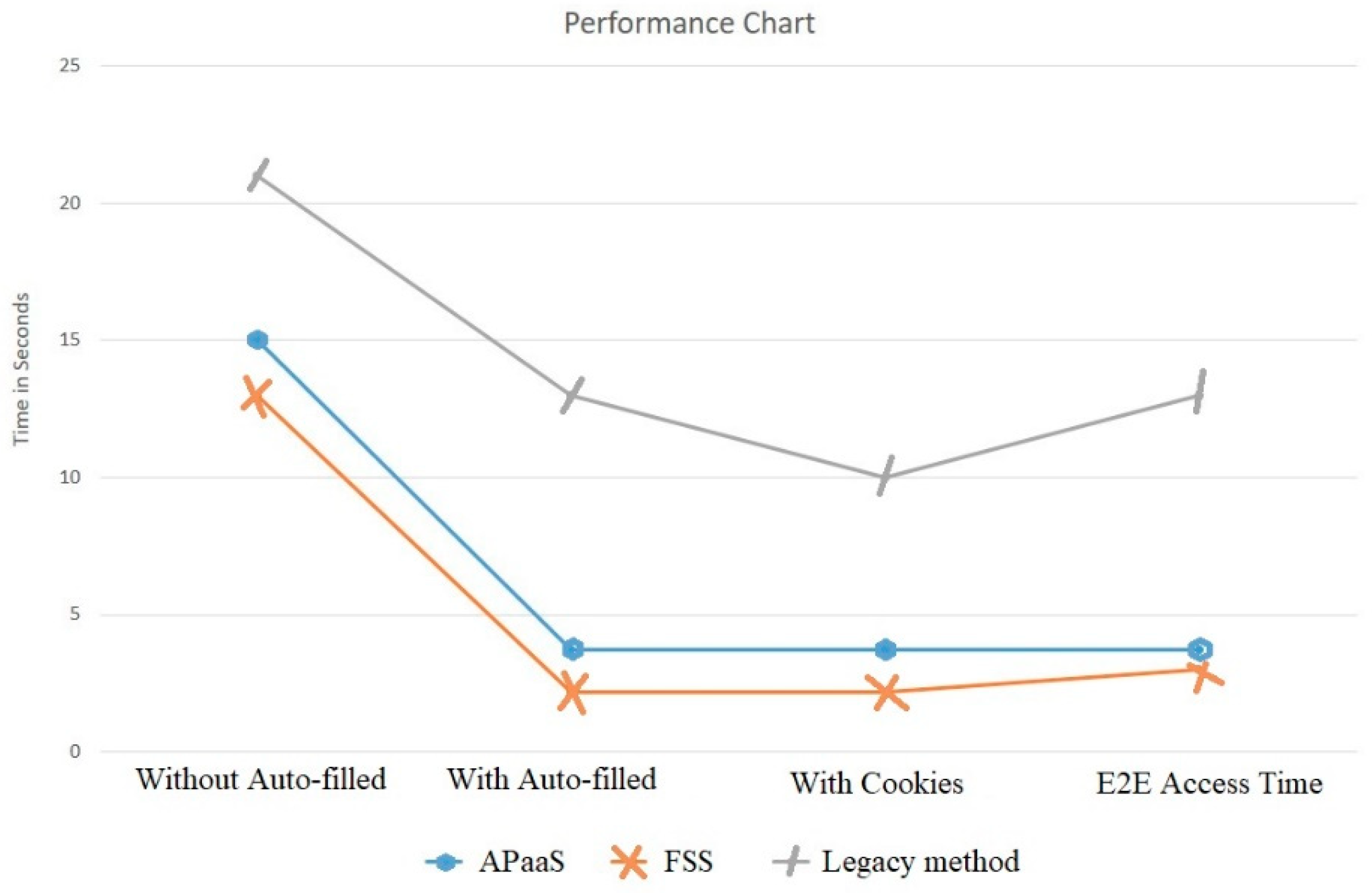
| 1 | Computer device | “HP core I3, Ram 6 GB, Hard drive 1TB, Operating System: windows 64 bit | ||||
| 2 | IoT devices | Samsung S4 | Huawei P20 Lite | Samsung Galaxy J1 | Apple iphone 4 | |
| 3 | Processor | CPU | Quad-core 1.6 GHz Cortex-A15 & quad-core 1.2 GHz Cortex-A7 | Octa-core (4 × 2.36 GHz Cortex-A53 + 4 × 1.7 GHz Cortex-A53) | 1.2 GHz Dual Core Cortex-A7 | 1 GHz Apple A4 |
| Chipset | Exynos 5 Octa 5410 Chipset | HiSilicon Kirin 659 | Spreadtrum | Apple A4 | ||
| GPU | IT SGX544MP3 | Mali-T830 MP2 | Mali-400 | PowerVR SGX535 | ||
| RAM | 2 GB | 4 GB | 512 MB | 512 MB | ||
| 4 | Distance between E2E | 500 m | 500 m | 500 m | 500 m | |
| 4 | Connection type | 4G LTE | 4G LTE | 3G | 2G | |
| 5 | “Size of the users login page” | 87 KB | 87 KB | 87 KB | 87 KB | |
| 6 | Manually filling users required credentials | approx. 13 s | approx. 11 s | approx. 17 s | approx. 13 s | |
| 7 | “Automated filling of credentials and sign in” | ~2 s | ~2 s | ~2 s | ~2 s | |
| 8 | Client-side key generation time (auto) | ~0.007 s | ~0.0059 s | ~0.0191 s | ~0.013 s | |
| 9 | Client-side message encryption (using secret key) time | ~0.2 s | ~0.17 s | ~0.2 s | ~0.246 s | |
| 10 | Client-side secret key encryption (using fog server public key) time | ~0.3 s | ~0.2 s | ~0.373 s | ~0.3 s | |
| 11 | Fog server-side verification time | ~0.06 s | ~0.06 s | ~0.06 s | ~0.06 s | |
| 12 | Fog server PK generation time | ~0.04 s | ~0.04 s | ~0.04 s | ~0.04 s | |
| 13 | Fog server PK encryption (using secret key) time | ~0.2 s | ~0.2 s | ~0.2 s | ~0.2 s | |
| 14 | Fog server PK encryption (using fog private key) time | ~0.3 s | ~0.3 s | ~0.3 s | ~0.3 s | |
| 15 | E2E response time for sharing PK | ~2 s | ~1.83 s | ~3.39 s | ~3.15 s | |
| 16 | Total time for getting PK | ~2.5 s | ~2.19 s | ~3.91 s | ~4.083 s | |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Abbas, N.; Asim, M.; Tariq, N.; Baker, T.; Abbas, S. A Mechanism for Securing IoT-enabled Applications at the Fog Layer. J. Sens. Actuator Netw. 2019, 8, 16. https://doi.org/10.3390/jsan8010016
Abbas N, Asim M, Tariq N, Baker T, Abbas S. A Mechanism for Securing IoT-enabled Applications at the Fog Layer. Journal of Sensor and Actuator Networks. 2019; 8(1):16. https://doi.org/10.3390/jsan8010016
Chicago/Turabian StyleAbbas, Nadeem, Muhammad Asim, Noshina Tariq, Thar Baker, and Sohail Abbas. 2019. "A Mechanism for Securing IoT-enabled Applications at the Fog Layer" Journal of Sensor and Actuator Networks 8, no. 1: 16. https://doi.org/10.3390/jsan8010016
APA StyleAbbas, N., Asim, M., Tariq, N., Baker, T., & Abbas, S. (2019). A Mechanism for Securing IoT-enabled Applications at the Fog Layer. Journal of Sensor and Actuator Networks, 8(1), 16. https://doi.org/10.3390/jsan8010016






