Virtual Replication of IoT Hubs in the Cloud: A Flexible Approach to Smart Object Management
Abstract
:1. Introduction
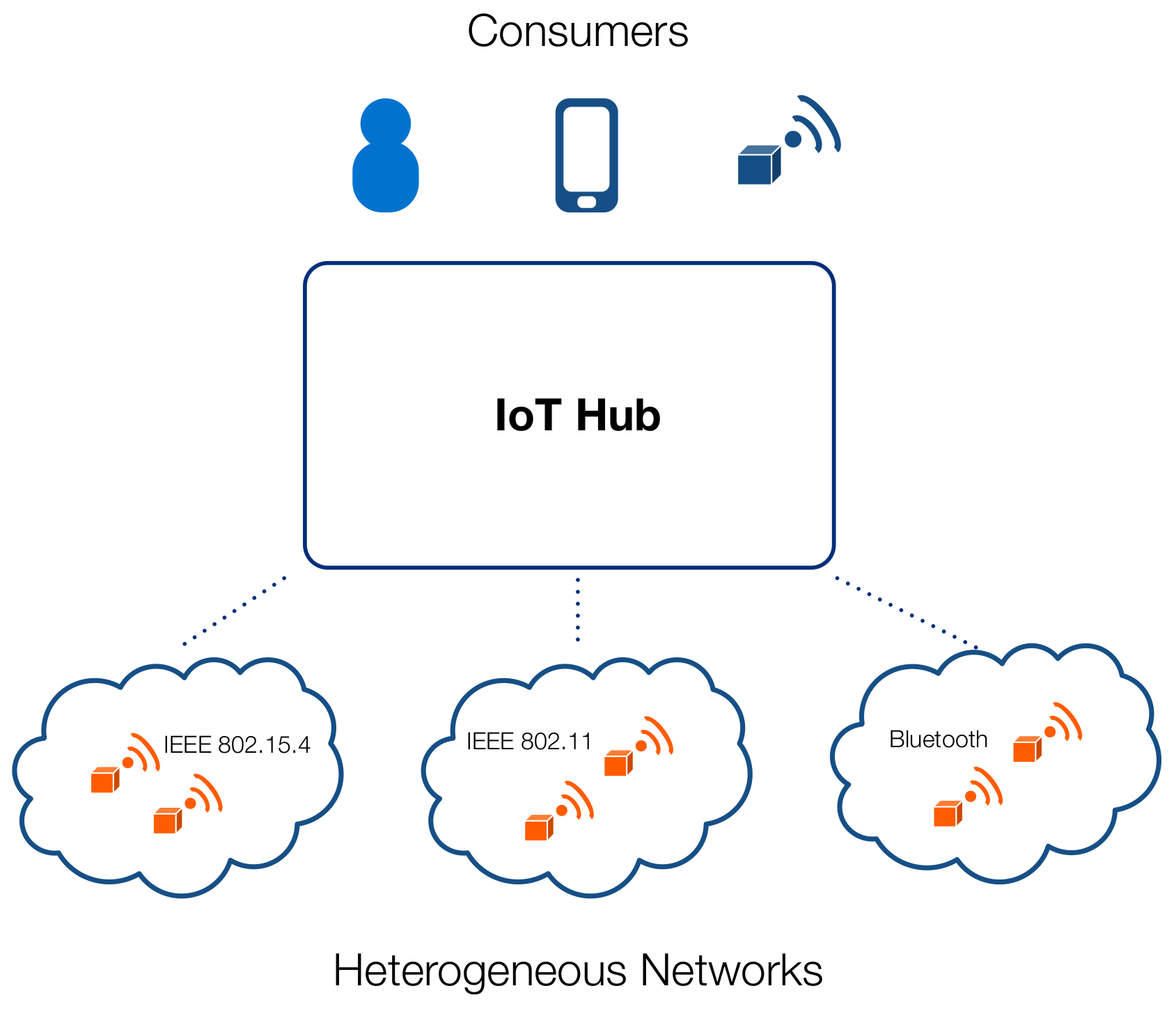
- Geographically distributed, in contrast with a fully Centralized solution associated with Cloud-based architectures;
- Low latency and high performance to support real-time applications;
- Support for mobility.
- Independence from Internet Connectivity allows to guarantee continuous service operation at the local level with no disruption in case of unreachability of Cloud. In case Internet Access is temporarily unavailable, the IoT Hub will keep the state of all Smart Objects and will automatically synchronize with the Cloud as soon as the connection resumes;
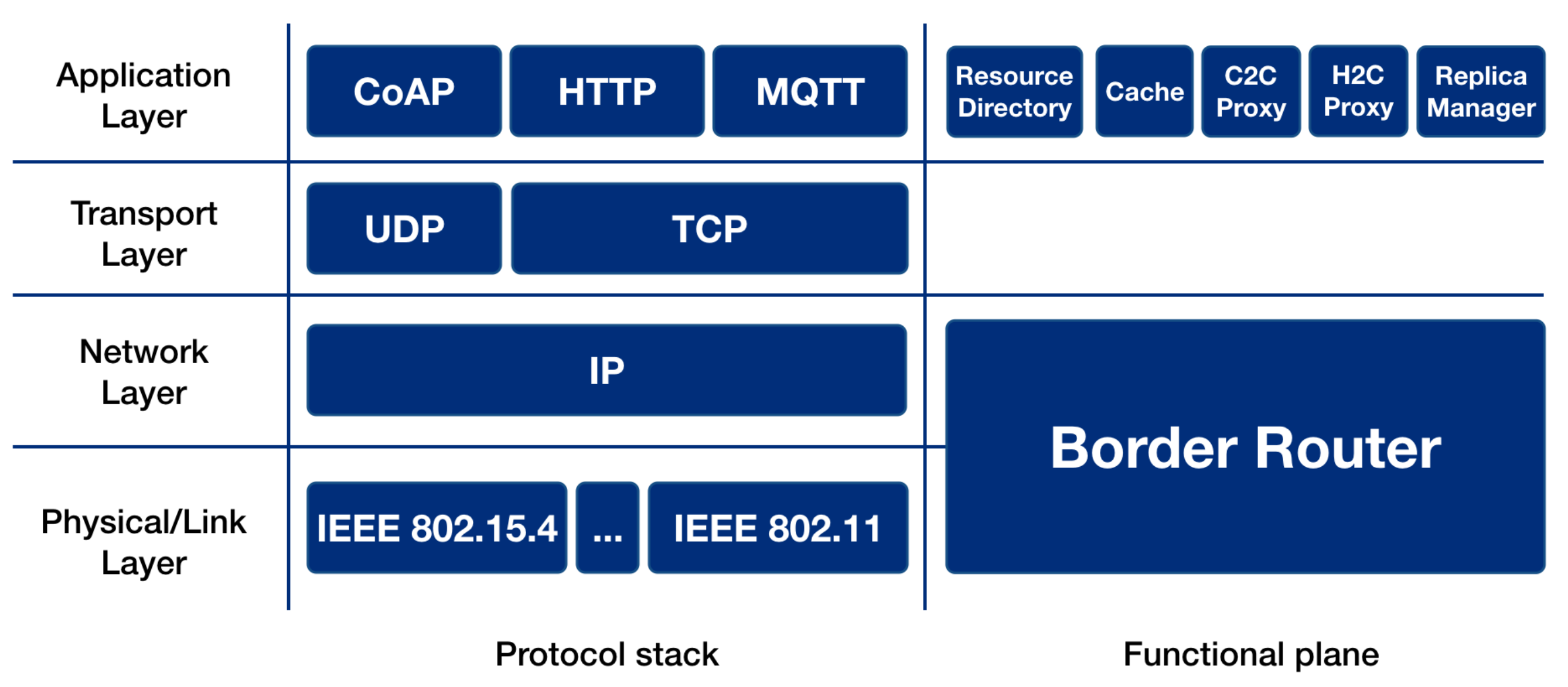
- Controlled and secure access to things. Direct access to Smart Object occurs only at the local level and may be filtered by the IoT Hub Border Router: the IoT Hub is the gateway/bridge between one or more constrained networks (e.g., IEEE 802.15.4);
- Service and Resource Discovery: the IoT Hub is able to discover which SOs are available in the network and, subsequently, to discover the resources that they host;
- Resource Directory (RD): the IoT Hub maintains a list of all CoAP resources available in the constrained networks;
- Origin Server (OS): it provides a CoAP server where resources are hosted or are to be created;
- Protocol Translation: (i) CoAP-to-CoAP (C2C) Proxy: it provides proxying capabilities for CoAP requests coming from external clients that should reach internal constrained nodes; and (ii) HTTP-to-CoAP (H2C) Proxy: it provides HTTP-to-CoAP cross-proxying (i.e., protocol translation) in order to enable access to CoAP resources by HTTP clients;
- Cache: in order to avoid unnecessary load on SOs and to minimize latencies, a cache is kept with the representation of most recently accessed resources.
2. Related Work
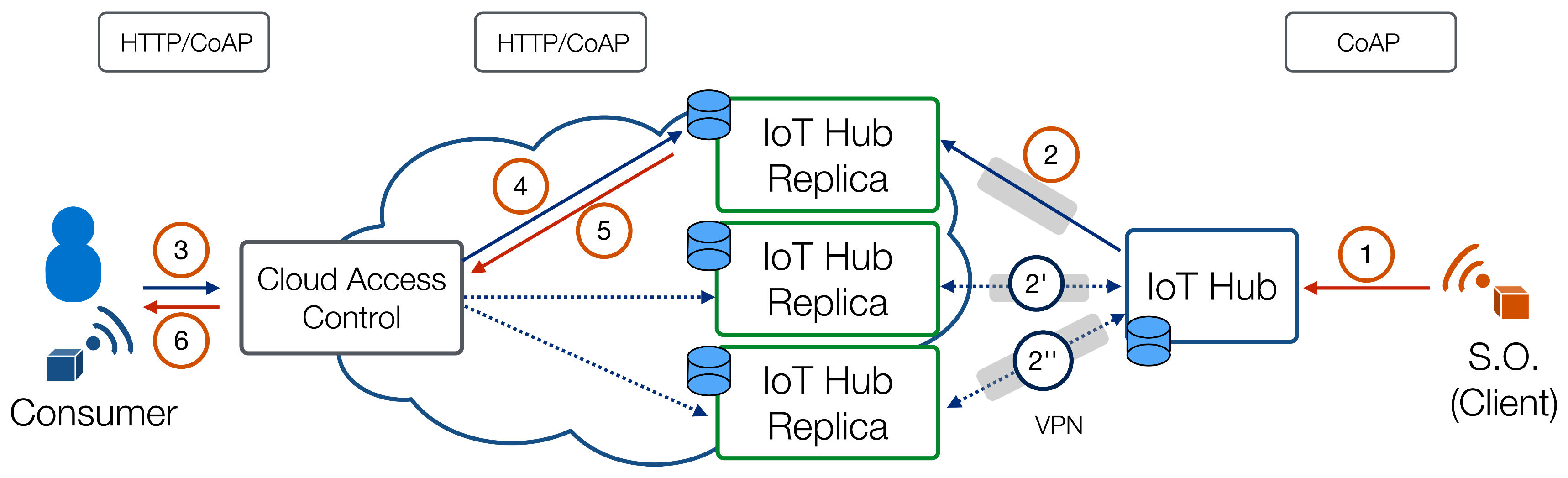
3. Architecture
3.1. The IoT Hub
- Service and Resource Discovery: the IoT Hub is able to discover which SOs are available in the network and, subsequently, to discover the resources that they host;
- LoWPAN Border Router: at the network layer, the IoT Hub is the gateway between one or more constrained networks (e.g., IEEE 802.15.4) it belongs to (through some radio interfaces it is equipped with).
- CoAP/CoAP (C2C) Proxy: at the application layer, it provides proxying capabilities for CoAP requests coming from external clients that should reach internal constrained nodes.
- HTTP/CoAP (H2C) Proxy: at the application layer, it provides cross-proxying (protocol translation) between HTTP and CoAP in order to let external HTTP clients access CoAP resources hosted by smart objects.
- Resource Directory: the IoT Hub maintains a list of all CoAP resources available in the constrained network. These resources may have been gathered through several mechanisms, such as those described in [23].
- Cache: in order to avoid unnecessary load on smart objects and to minimize latencies, a cache is kept with the representation of most recently accessed resources.
- Replica Manager: a software module responsible for the coordination and the synchronization between the IoT Hub and its replicas.
- the IoT Hub is a bottleneck of the architecture, since all traffic must pass through it even if it is not a communication endpoint;
- failure of the IoT Hub would make the resources hosted by smart objects temporarily or permanently unavailable.
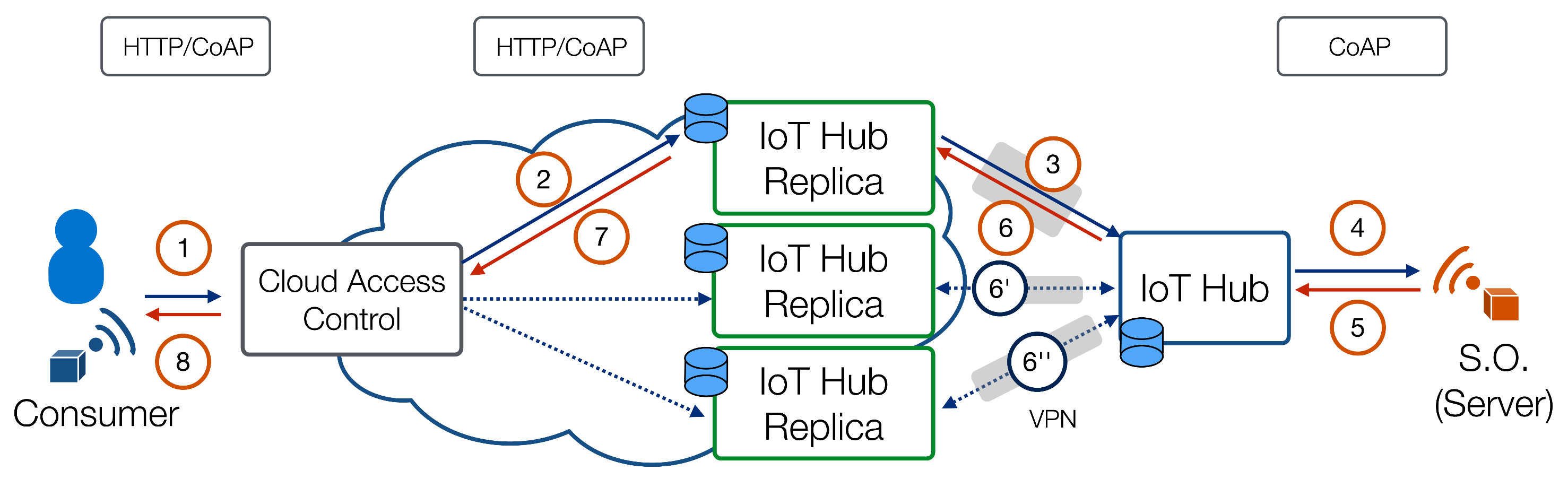
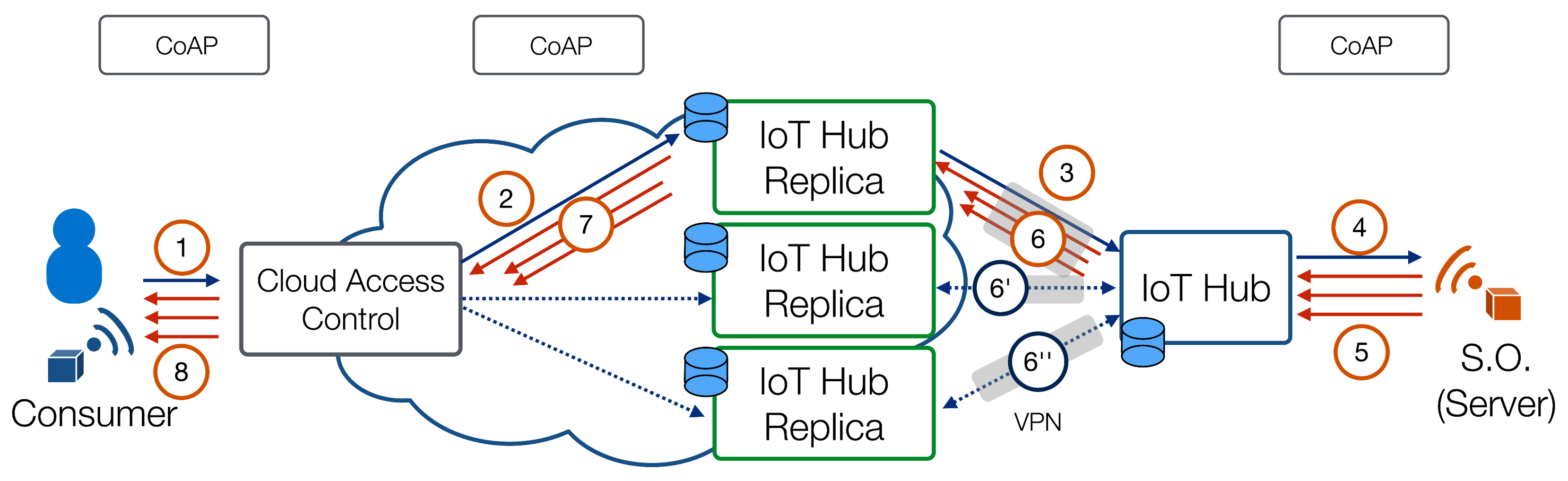
3.2. Operational Scenarios
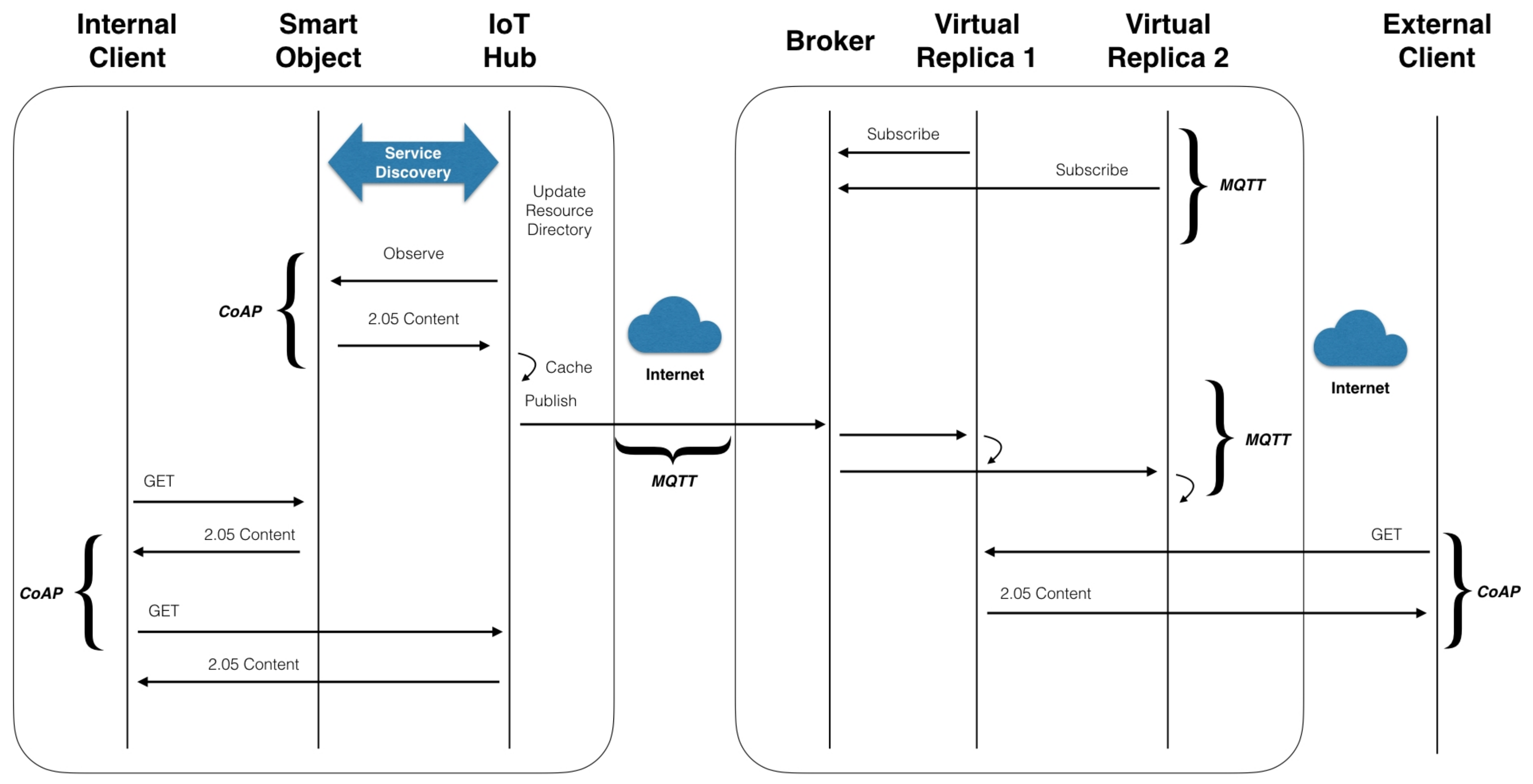
3.2.1. Polling Resources
3.2.2. Observing Resources
3.2.3. Pushing Resources
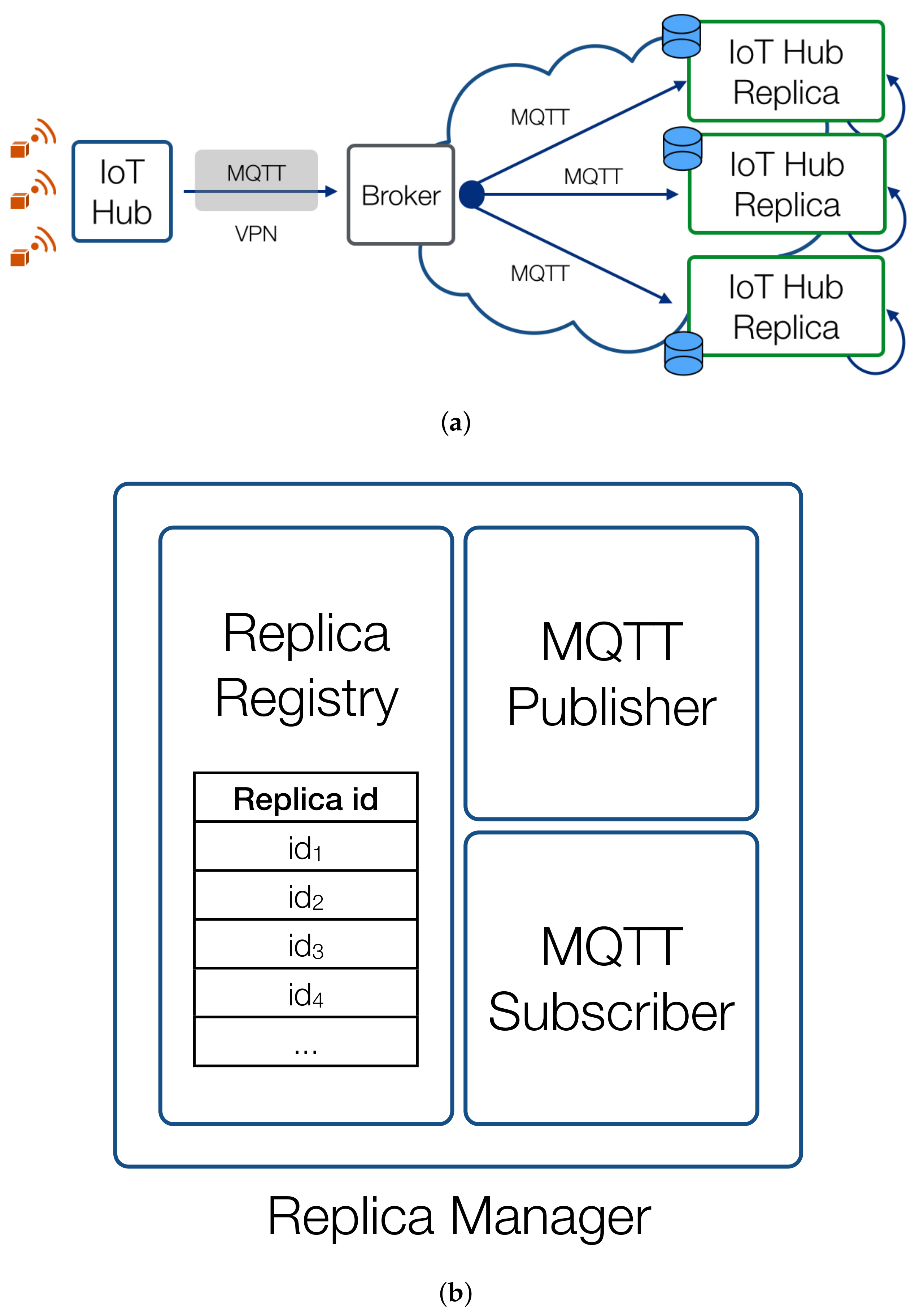
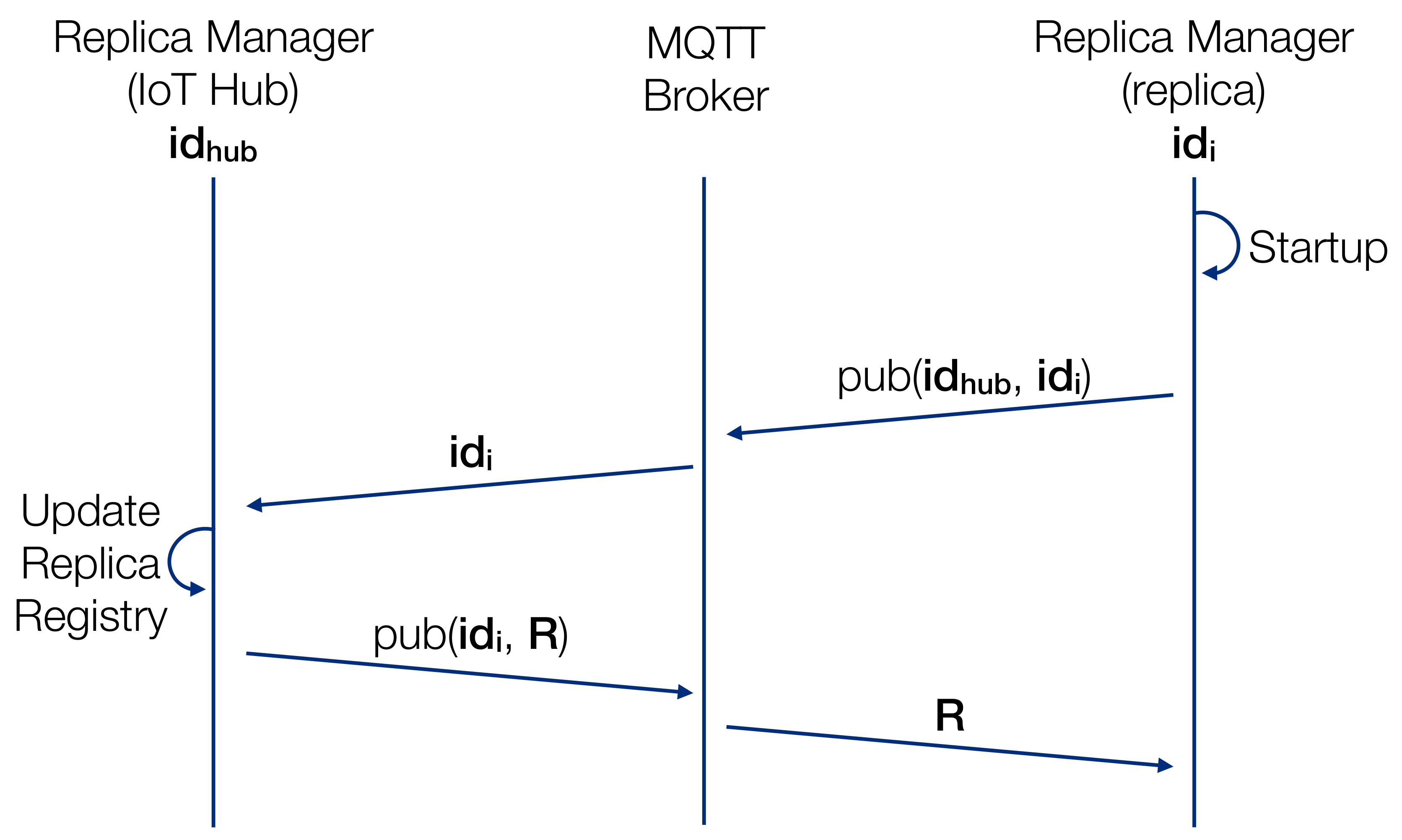
3.3. Synchronization Protocol
- The IoT Hub starts observing all the discovered resources, according to [24] to receive updates related to state changes.
- Any time the IoT Hub receives such updates it populates/refreshes its resource cache.
- The IoT Hub publishes a message (using an MQTT topic bound to the resource and the IoT Hub) related to the resource state change to the Cloud Broker to let Virtual Replicas update their mirrored state.
- Upon launch the Virtual Replicas subscribe to the Broker to receive updates for topics related to a target IoT Hub.
- Any time the IoT Hub publishes an update for a resource the Virtual Replica will receive a message and will update its state accordingly.
- Local Clients issue CoAP requests directly to the Smart Objects (if it implements CoAP) or to the IoT Hub otherwise.
- Remote and External Clients may interact with a Smart Objects only through the Virtual Replica which will be publicly accessible using its REST interface.
- A Replica Registry (RR), which contains the list of the identifiers of all the replicas of the IoT Hub.
- An MQTT subscriber, which registers to the broker to receive messages related to two topics: (i) its own identifier () and (ii) the identifier of the actual IoT Hub (); these may coincide in the case of the actual IoT Hub.
- An MQTT publisher, which publishes messages to the broker, using the method , where t is the topic and m is the message to be published.
- A lack of Internet connectivity with Cloud Virtual replicas: in this case there is no way to keep the states synchronized until the connection resumes;
- In a Pub/Sub architecture messages may be delivered to consumers at different times so that a Client requesting the state of a resource may receive different responses depending on the Virtual Replica serving the request. However, it is import to point out that all replicas are typically being executed in Cloud Environments/Carrier-grade Data Centers which guarantee high availability and reliable and low latency connectivity, thus minimizing the inconsistency time windows.
4. Experimental Analysis
4.1. Experimental Setup
- Smart objects: Real and virtual nodes with CoAP modules based on the Californium framework [30].
- Resource External Consumer: Real and virtual external consumers implementing HTTP and CoAP modules to dynamically interact and consume available resources managed by the platform and active IoT Hubs and smart objects.
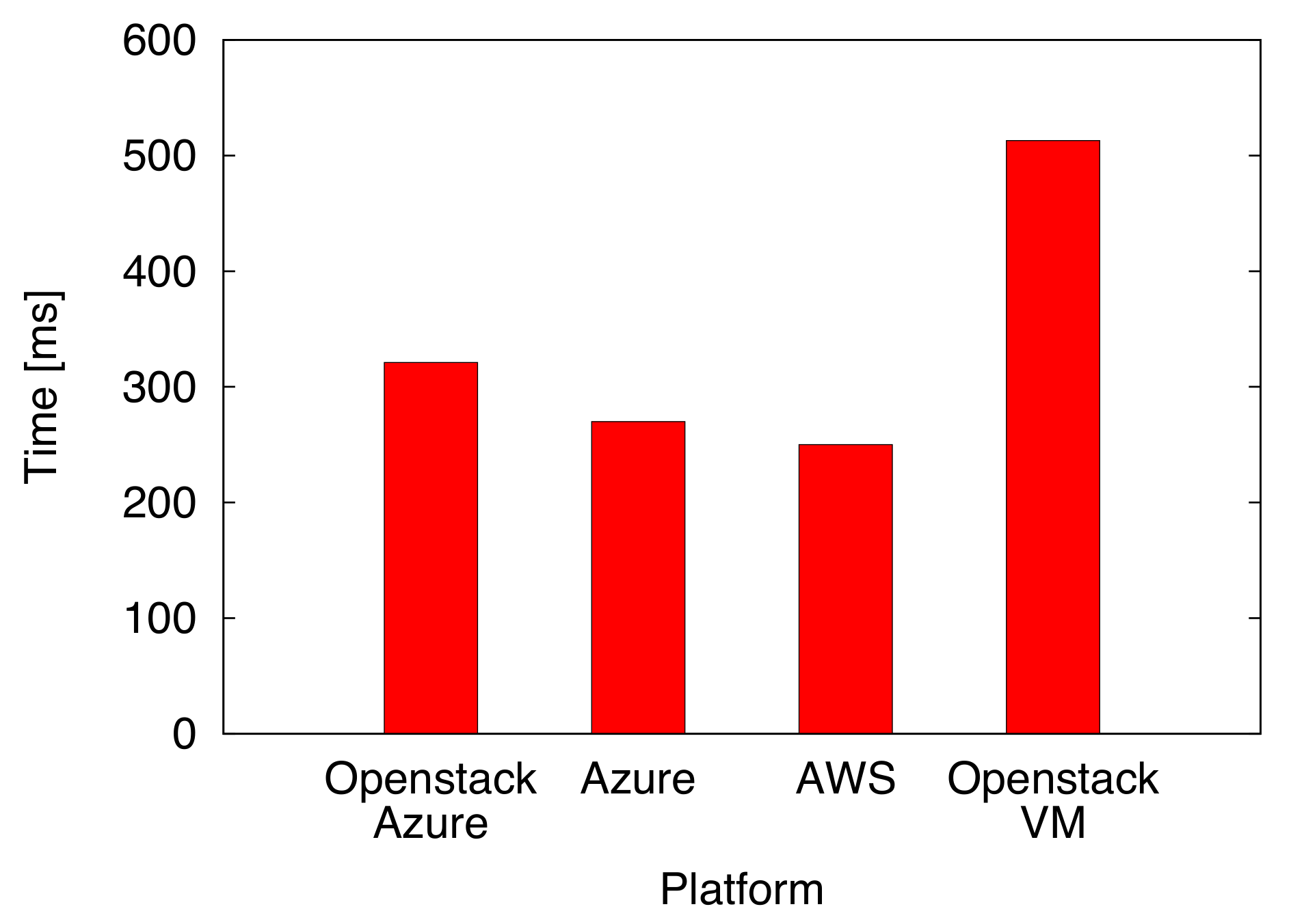
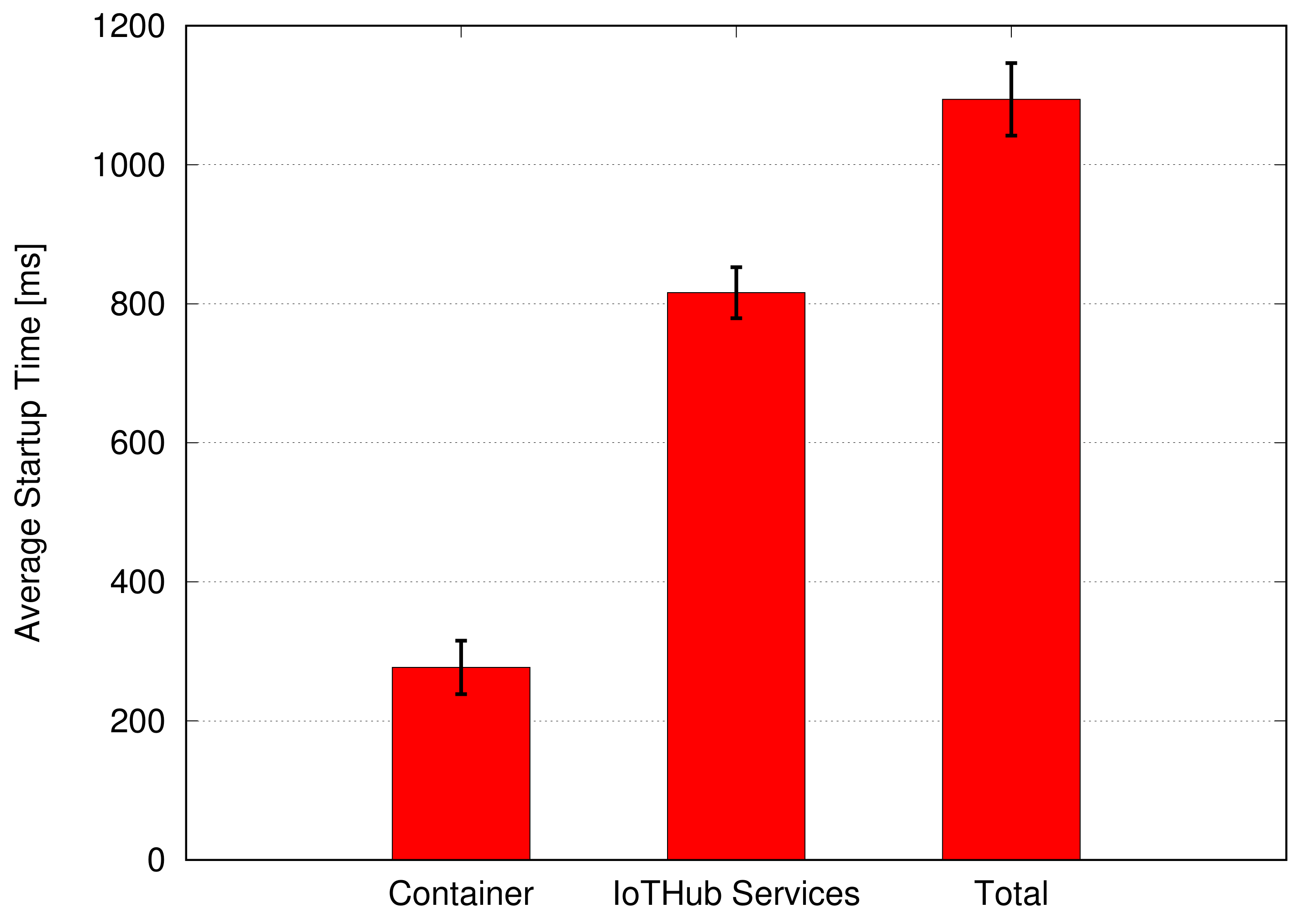
- IoT Hub Replica Creation Time (dimension: [s]): the time required to create and run, on the target Cloud infrastructure, a new instance of an IoT Hub Replica.
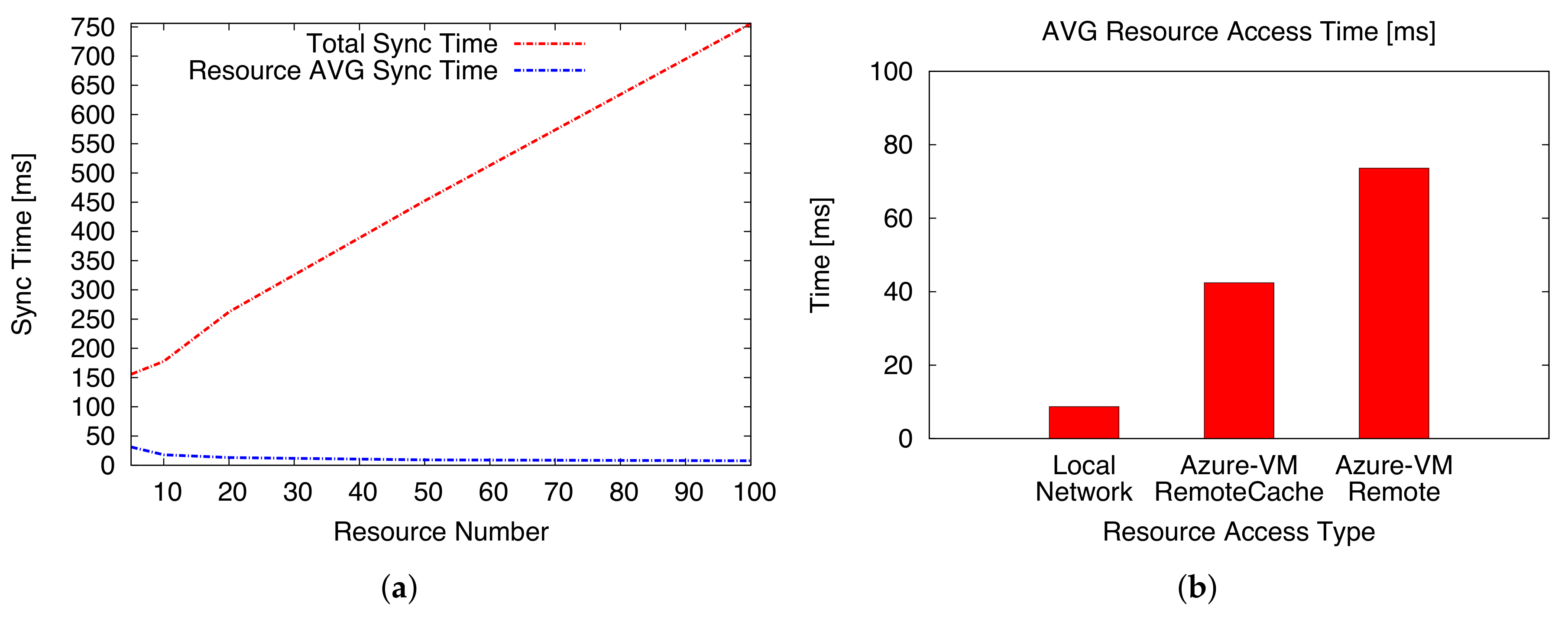
- Resource Synchronization Time (dimension: [ms]): the elapsed time needed to synchronize a new resource between two IoT Hubs.
- Resource Access Time (dimension: [ms]): the time required to access and retrieve a response for a resource of interest. It can be associated with different configurations: (i) direct and local access to the CoAP Server smart object (e.g., if the consumer and the node are in the same network); (ii) remote access through the Cloud and communication with the physical Hub; (iii) remote access to the cached value stored on an IoT Hub Replica.
- CPU Usage % (adimensional: [percentage]): the percentage of CPU used by the IoT Hub core process.
- Memory Usage % (adimensional: [percentage]): the memory percentage used by the core process of the IoT Hub.
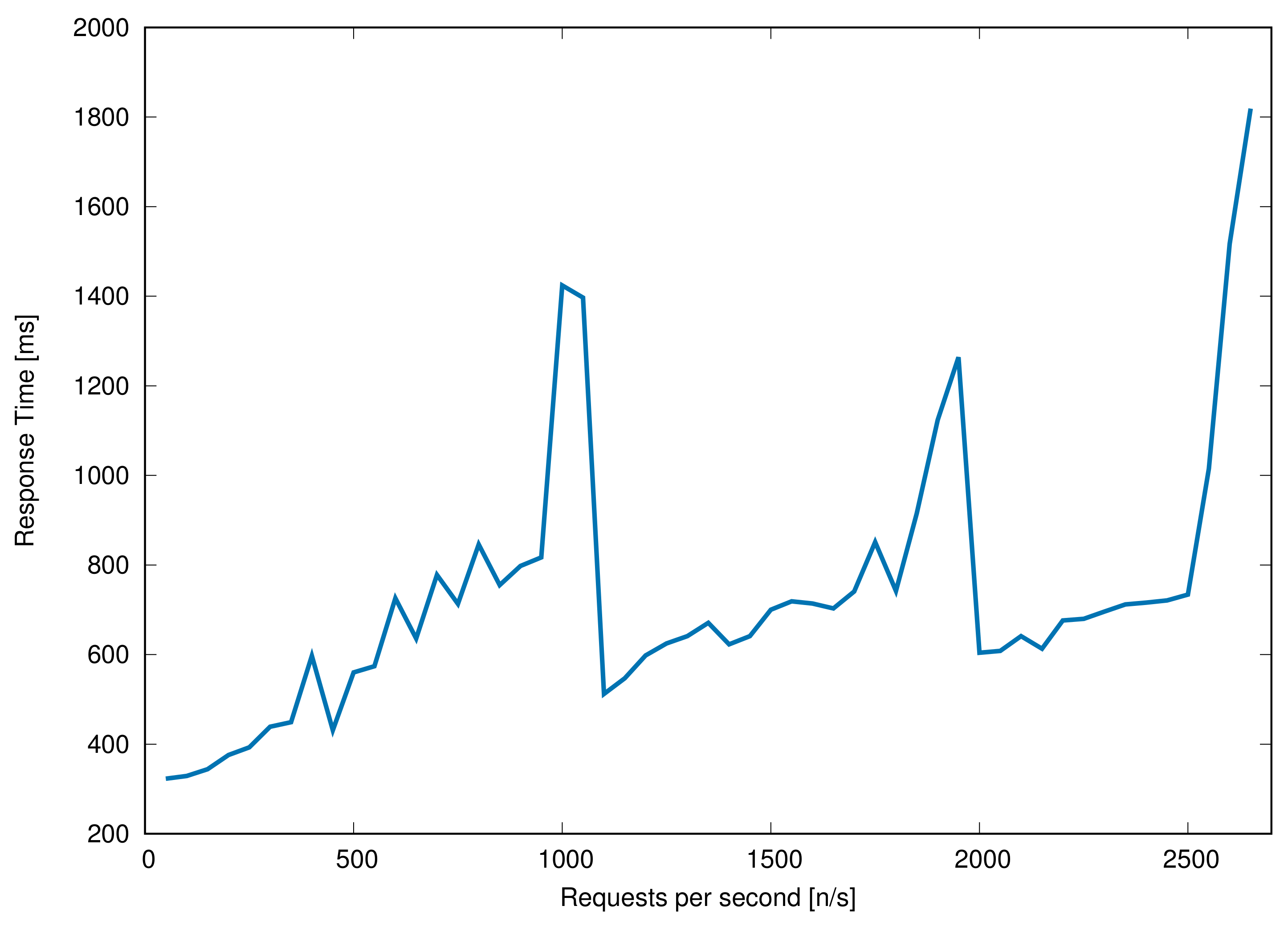
4.2. Performance Evaluation
5. Conclusions
Author Contributions
Conflicts of Interest
References
- Bormann, C.; Ersue, M.; Keranen, A. Terminology for Constrained-Node Networks; RFC 7228 (Informational); Internet Engineering Task Force (IETF): Fremont, CA, USA, 2014. [Google Scholar]
- Vasseur, J.P.; Dunkels, A. Interconnecting Smart Objects with IP—The Next Internet; Morgan Kaufmann: Burlington, MA, USA, 2010. [Google Scholar]
- Falk, J.; Kucherawy, M. RPL: IPv6 Routing Protocol for Low-Power and Lossy Networks; RFC 6650; Internet Engineering Task Force (IETF): Fremont, CA, USA, 2012. [Google Scholar]
- Shelby, Z.; Hartke, K.; Bormann, C. The Constrained Application Protocol (CoAP); RFC 7252 (Proposed Standard); Internet Engineering Task Force (IETF): Fremont, CA, USA, 2014. [Google Scholar]
- MQTT. Message Queue Telemetry Transport. Available online: http://mqtt.org/ (accessed on 1 March 2018).
- Bonomi, F.; Milito, R.; Zhu, J.; Addepalli, S. Fog Computing and Its Role in the Internet of Things. In Proceedings of the First Edition of the MCC Workshop on Mobile Cloud Computing, Helsinki, Finland, 13–17 August 2012; ACM: New York, NY, USA, 2012; pp. 13–16. [Google Scholar]
- Aazam, M.; Khan, I.; Alsaffar, A.; Huh, E.N. Cloud of Things: Integrating Internet of Things and cloud computing and the issues involved. In Proceedings of the 2014 11th International Bhurban Conference on Applied Sciences and Technology (IBCAST), Islamabad, Pakistan, 14–18 January 2014; pp. 414–419. [Google Scholar]
- Aazam, M.; Hung, P.P.; Huh, E.N. Smart gateway based communication for cloud of things. In Proceedings of the 2014 IEEE Ninth International Conference on Intelligent Sensors, Sensor Networks and Information Processing (ISSNIP), Singapore, 21–24 April 2014; pp. 1–6. [Google Scholar]
- Kleine, O. The smart service proxy—A middlebox for a semantic Web of things. In Proceedings of the 2015 12th Annual IEEE International Conference on Sensing, Communication, and Networking (SECON), Seattle, WA, USA, 22–25 June 2015; pp. 160–162. [Google Scholar]
- Yannuzzi, M.; Milito, R.; Serral-Gracià, R.; Montero, D.; Nemirovsky, M. Key ingredients in an IoT recipe: Fog Computing, Cloud computing, and more Fog Computing. In Proceedings of the 2014 IEEE 19th International Workshop on Computer Aided Modeling and Design of Communication Links and Networks (CAMAD), Athens, Greece, 1–3 December 2014; pp. 325–329. [Google Scholar]
- Coulson, G.; Porter, B.; Chatzigiannakis, I.; Koninis, C.; Fischer, S.; Pfisterer, D.; Bimschas, D.; Braun, T.; Hurni, P.; Anwander, M.; et al. Flexible Experimentation in Wireless Sensor Networks. Commun. ACM 2012, 55, 82–90. [Google Scholar] [CrossRef]
- Karkazis, P.; Trakadas, P.; Zahariadis, T.; Chatzigiannakis, I.; Dohler, M.; Vitaletti, A.; Antoniou, A.; Leligou, H.C.; Sarakis, L. Resource and Service Virtualisation in M2M and IoT Platforms. Int. J. Intell. Eng. Inform. 2015, 3, 205–224. [Google Scholar] [CrossRef]
- Kim-Hung, L.; Datta, S.K.; Bonnet, C.; Hamon, F.; Boudonne, A. A scalable IoT framework to design logical data flow using virtual sensor. In Proceedings of the 2017 IEEE 13th International Conference on Wireless and Mobile Computing, Networking and Communications (WiMob), Rome, Italy, 9–11 October 2017; pp. 1–7. [Google Scholar]
- Datta, S.K.; Bonnet, C. An edge computing architecture integrating virtual IoT devices. In Proceedings of the 2017 IEEE 6th Global Conference on Consumer Electronics (GCCE), Nagoya, Japan, 24–27 October 2017; pp. 1–3. [Google Scholar]
- Docker. Container Platform. Available online: https://www.docker.com (accessed on 1 March 2018).
- Rufino, J.; Alam, M.; Ferreira, J.; Rehman, A.; Tsang, K.F. Orchestration of containerized microservices for IIoT using Docker. In Proceedings of the 2017 IEEE International Conference on Industrial Technology (ICIT), Toronto, ON, Canada, 22–25 March 2017; pp. 1532–1536. [Google Scholar]
- Großmann, M.; Klug, C. Monitoring Container Services at the Network Edge. In Proceedings of the 2017 29th International Teletraffic Congress (ITC 29), Genoa, Italy, 4–8 September 2017; Volume 1, pp. 130–133. [Google Scholar]
- Ismail, B.I.; Goortani, E.M.; Karim, M.B.A.; Tat, W.M.; Setapa, S.; Luke, J.Y.; Hoe, O.H. Evaluation of Docker as Edge computing platform. In Proceedings of the 2015 IEEE Confernece on Open Systems (ICOS), Bandar Melaka, Malaysia, 24–26 August 2015; pp. 130–135. [Google Scholar]
- Xu, Y.; Mahendran, V.; Radhakrishnan, S. SDN docker: Enabling application auto-docking/undocking in edge switch. In Proceedings of the 2016 IEEE Conference on Computer Communications Workshops (INFOCOM WKSHPS), San Francisco, CA, USA, 10–14 April 2016; pp. 864–869. [Google Scholar]
- Ramalho, F.; Neto, A. Virtualization at the network edge: A performance comparison. In Proceedings of the 2016 IEEE 17th International Symposium on A World of Wireless, Mobile and Multimedia Networks (WoWMoM), Coimbra, Portugal, 21–24 June 2016; pp. 1–6. [Google Scholar]
- Morabito, R. A performance evaluation of container technologies on Internet of Things devices. In Proceedings of the 2016 IEEE Conference on Computer Communications Workshops (INFOCOM WKSHPS), San Francisco, CA, USA, 10–14 April 2016; pp. 999–1000. [Google Scholar]
- Morabito, R.; Petrolo, R.; Loscrí, V.; Mitton, N. Enabling a lightweight Edge Gateway-as-a-Service for the Internet of Things. In Proceedings of the 2016 7th International Conference on the Network of the Future (NOF), Buzios, Brazil, 16–18 November 2016; pp. 1–5. [Google Scholar]
- Cirani, S.; Davoli, L.; Ferrari, G.; Leone, R.; Medagliani, P.; Picone, M.; Veltri, L. A Scalable and Self-Configuring Architecture for Service Discovery in the Internet of Things. IEEE Internet Things J. 2014, 1, 508–521. [Google Scholar] [CrossRef]
- Hartke, K. Observing Resources in the Constrained Application Protocol (CoAP); RFC 7641 (Proposed Standard); Internet Engineering Task Force (IETF): Fremont, CA, USA, 2015. [Google Scholar]
- Cheshire, S.; Krochmal, M. Multicast DNS; RFC 6762 (Proposed Standard); Internet Engineering Task Force (IETF): Fremont, CA, USA, 2013. [Google Scholar]
- Cheshire, S.; Krochmal, M. DNS-Based Service Discovery; RFC 6763 (Proposed Standard); Internet Engineering Task Force (IETF): Fremont, CA, USA, 2013. [Google Scholar]
- Boucadair, M.; Penno, R.; Wing, D. Universal Plug and Play (UPnP) Internet Gateway Device-Port Control Protocol Interworking Function (IGD-PCP IWF); RFC 6970 (Proposed Standard); Internet Engineering Task Force (IETF): Fremont, CA, USA, 2013. [Google Scholar]
- Lamport, L. Paxos made simple. ACM Sigact News 2001, 32, 18–25. [Google Scholar]
- Ongaro, D.; Ousterhout, J.K. In search of an understandable consensus algorithm. In Proceedings of the 2014 USENIX Annual Technical Conference, Philadelphia, PA, USA, 19–20 June 2014; pp. 305–319. [Google Scholar]
- Kovatsch, M.; Lanter, M.; Shelby, Z. Californium: Scalable Cloud Services for the Internet of Things with CoAP. In Proceedings of the 4th International Conference on the Internet of Things (IoT 2014), Cambridge, MA, USA, 6–8 October 2014. [Google Scholar]
- Raspberry Pi Foundation. Message Queue Telemetry Transport. Available online: http://www.raspberrypi.org/ (accessed on 1 March 2018).
- Microsoft. Microsoft Azure-Cloud platform. Available online: http://azure.microsoft.com/it-it/ (accessed on 1 March 2018).
- Amazon. Amazon EC2. Available online: http://aws.amazon.com/ec2/ (accessed on 1 March 2018).
- Rackspace, NASA. OpenStack Cloud Software-Open Source Software for Building Private and Public Clouds. Available online: https://www.openstack.org/ (accessed on 1 March 2018).
- Oracle Java VM. Java. Available online: https://www.oracle.com/java/index.html (accessed on 1 March 2018).
- Dhurjati, D.; Kowshik, S.; Adve, V.; Lattner, C. Memory Safety Without Runtime Checks or Garbage Collection. In Proceedings of the 2003 ACM SIGPLAN Conference on Language, Compiler, and Tool for Embedded Systems, San Diego, CA, USA, 11–13 June 2003. [Google Scholar]
- Pfisterer, D.; Romer, K.; Bimschas, D.; Kleine, O.; Mietz, R.; Truong, C.; Hasemann, H.; Kröller, A.; Pagel, M.; Hauswirth, M.; et al. SPITFIRE: Toward a semantic web of things. IEEE Commun. Mag. 2011, 49, 40–48. [Google Scholar] [CrossRef]
- Chatzigiannakis, I.; Hasemann, H.; Karnstedt, M.; Kleine, O.; Kröller, A.; Leggieri, M.; Pfisterer, D.; Römer, K.; Truong, C. True self-configuration for the IoT. In Proceedings of the 2012 3rd IEEE International Conference on the Internet of Things, Wuxi, China, 24–26 October 2012; pp. 9–15. [Google Scholar]
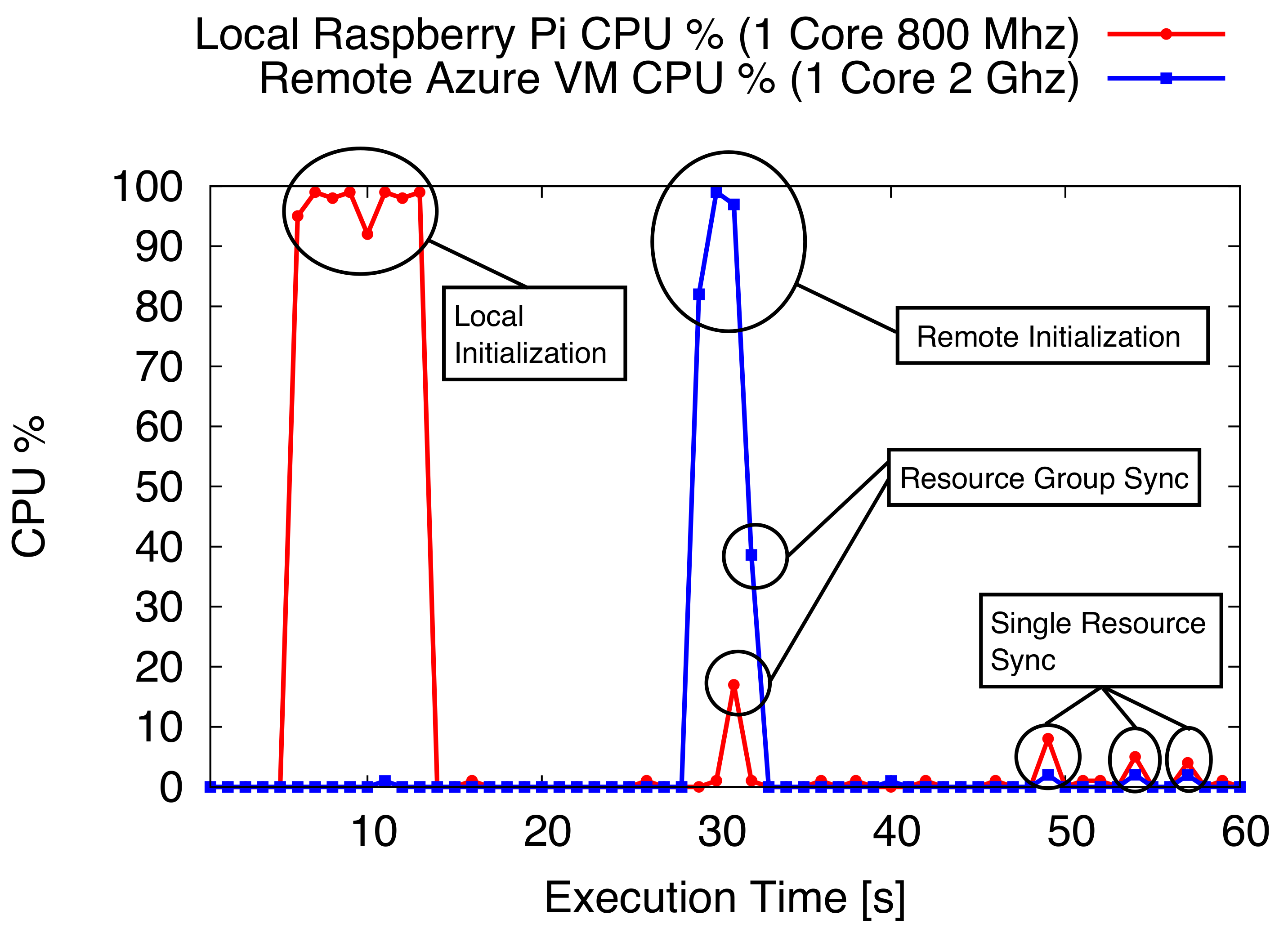
| Hub | Initialization | Res. Add | Sync Res. Group | Sync Single Res. |
|---|---|---|---|---|
| [Local] Raspberry Pi CPU | 96% | 17.45% | 15.15% | 6.93% |
| [Local] Raspberry Pi Memory | +2.7% | +0.02% | +0.01% | +0.002% |
| [Remote] Azure VM Remote CPU | 97% | NA | 34.22% | 1.93% |
| [Remote] Azure VM Memory | +1.9% | NA | +0.01% | +0.001% |
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Cirani, S.; Ferrari, G.; Mancin, M.; Picone, M. Virtual Replication of IoT Hubs in the Cloud: A Flexible Approach to Smart Object Management. J. Sens. Actuator Netw. 2018, 7, 16. https://doi.org/10.3390/jsan7020016
Cirani S, Ferrari G, Mancin M, Picone M. Virtual Replication of IoT Hubs in the Cloud: A Flexible Approach to Smart Object Management. Journal of Sensor and Actuator Networks. 2018; 7(2):16. https://doi.org/10.3390/jsan7020016
Chicago/Turabian StyleCirani, Simone, Gianluigi Ferrari, Mirko Mancin, and Marco Picone. 2018. "Virtual Replication of IoT Hubs in the Cloud: A Flexible Approach to Smart Object Management" Journal of Sensor and Actuator Networks 7, no. 2: 16. https://doi.org/10.3390/jsan7020016
APA StyleCirani, S., Ferrari, G., Mancin, M., & Picone, M. (2018). Virtual Replication of IoT Hubs in the Cloud: A Flexible Approach to Smart Object Management. Journal of Sensor and Actuator Networks, 7(2), 16. https://doi.org/10.3390/jsan7020016







