User-Generated Services Composition in Smart Multi-User Environments
Abstract
:1. Introduction
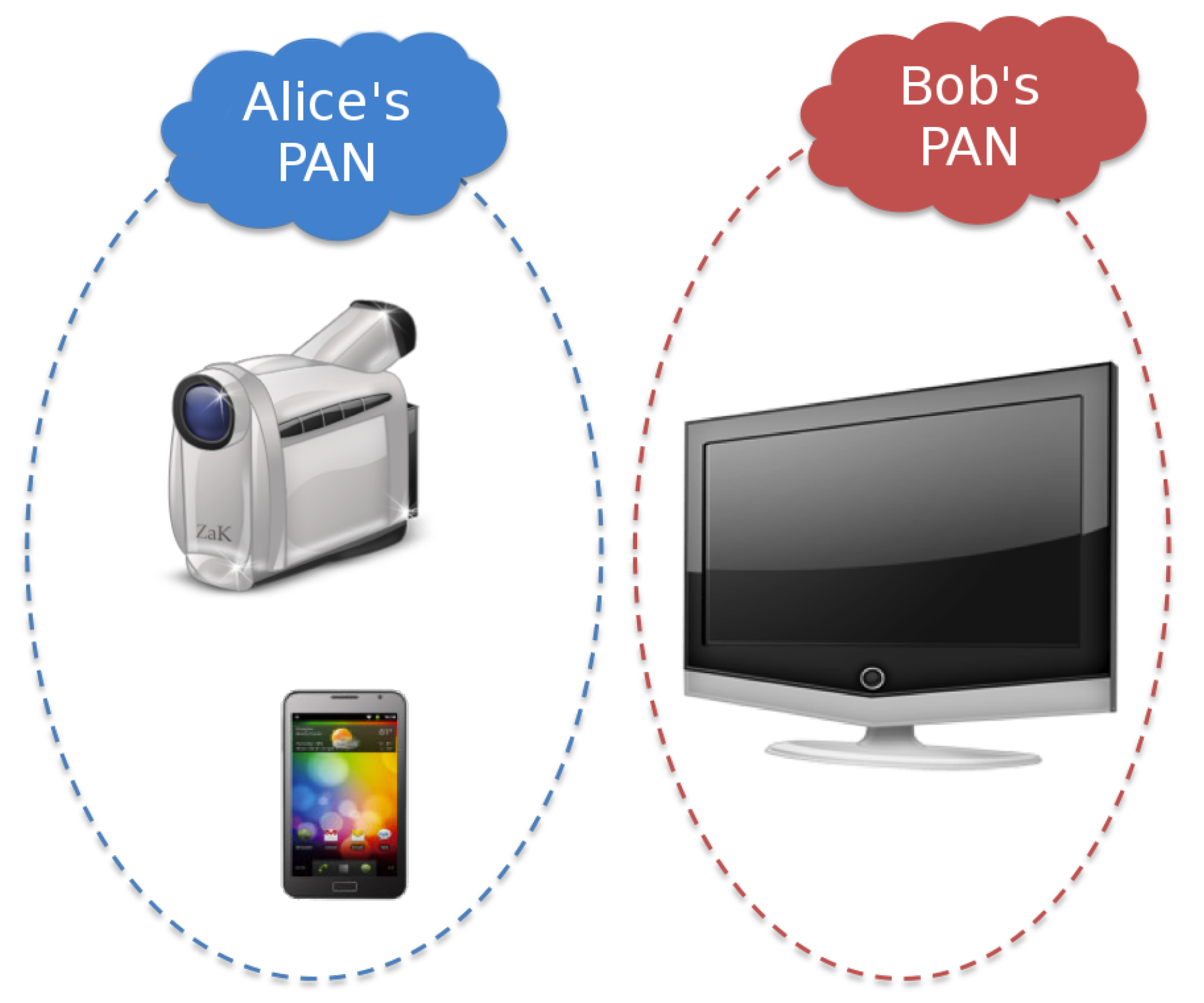
2. Reference Scenario
- Videostream allows users to receive a video stream from Alice’s camcorder/smartphone;
- Screenshot allows users to take snapshots of contents reproduced on Bob’s Smart TV.
- Alice’s parents are always allowed to use Videostream service;
- Alice’s relatives are allowed to use Videostream service only when Alice is in Catania;
- Every other subject is not allowed to use Videostream service.
- Only Bob’s house guests are allowed to use Screenshot service;
- Every other subject is not allowed to use Screenshot service.
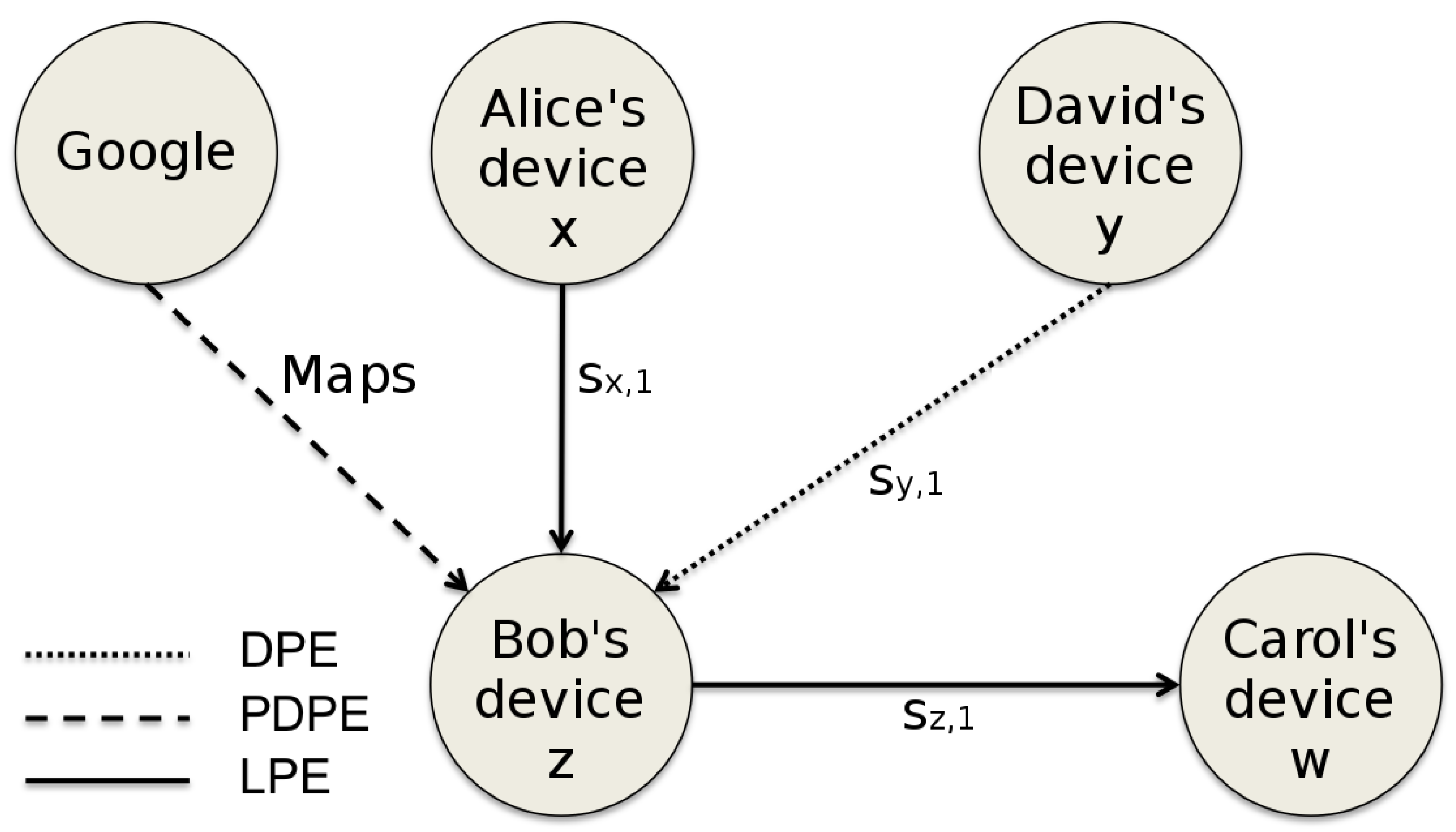
3. Security Policy Issues in UGS Composition
- Each node is a service provider, e.g., a device owned by a user providing/consuming services;
- Each edge from to indicates a service provided by that is requested by .
- Dynamicity: service related policies may change frequently;
- Context Awareness: policies may depend on contextual information (e.g., user’s context);
- Degree of Privacy: users could want to set restrictions on the disclosure degree of their policies towards other subjects (users/services).
3.1. Dynamicity
- It should be able to update/synchronize composite services’ policies when component services’ policies change. For example, referring again to Figure 3, if the policies related to service change, it is necessary to synchronize the policies of all composite services that have as a component service (in this case only );
- It should define efficient strategies to ensure that any change in component services’ policies does not lead to conflicting authorization decisions taken by the security policy of the composite service.
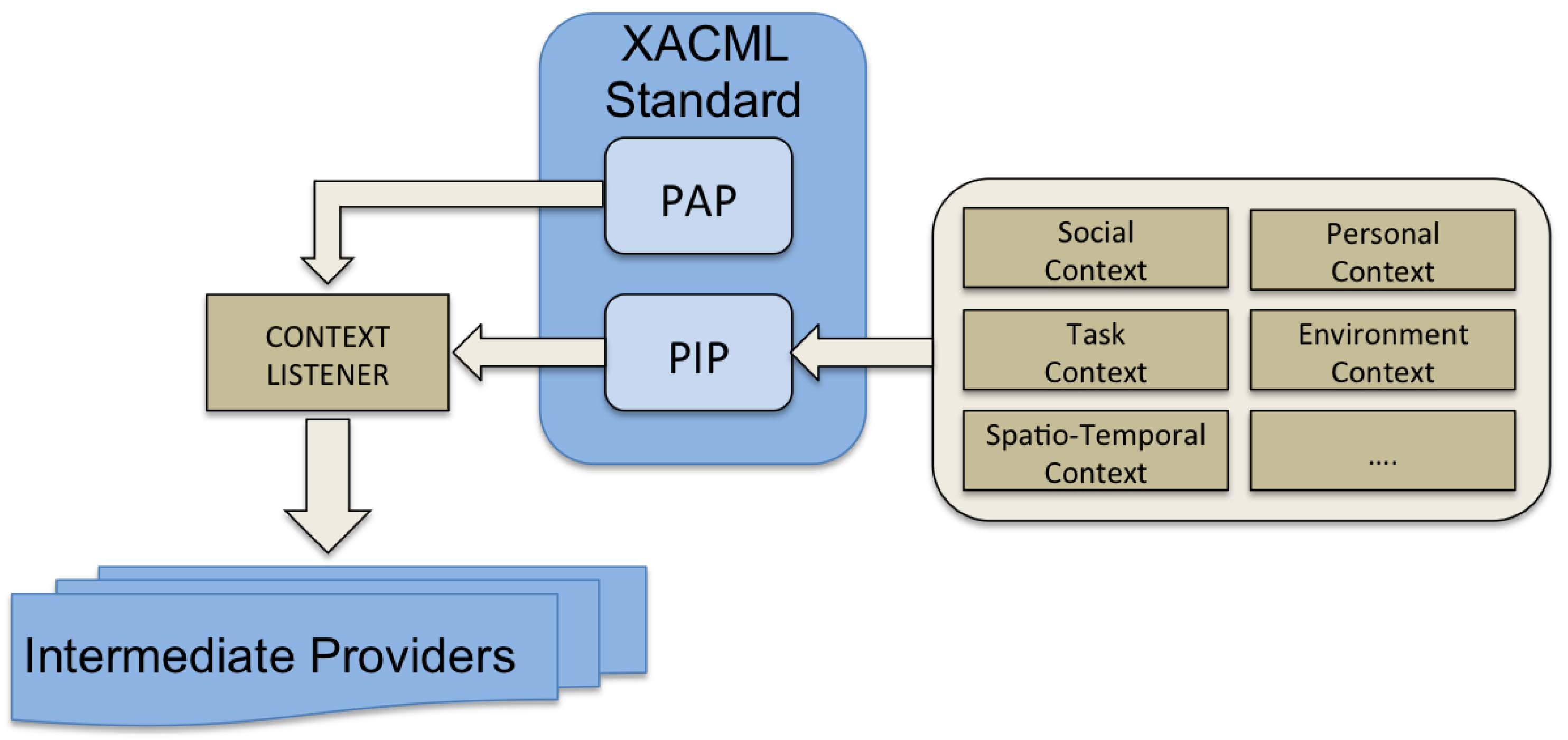
3.2. Context Awareness
3.3. Degree of Privacy
4. Proposed Policy Models
4.1. Distributed Policy Enforcement
4.2. Local Policy Enforcement
if (context_params1 < boundary1) current_policy = P1 if (context_params2 > boundary2) current_policy = P2Thus, the Context Listener periodically polls the PIP (Policy Information Point) module to obtain actual values for the contextual parameters (such as current battery level) and checks whether these values remain within the boundaries defined by the policy. When at least one of the parameters, included in the rule, exceeds its boundary, the Context Listener communicates to interested intermediate providers the current user’s context or policy.
4.3. Policy’s Context Obfuscation
1 <policy-set id="Alice’s policyset"> 2 <policy algorithm="permit-overrides"> 3 <target> 4 <subject param="cert" match="Carol.cert"/> 5 <resource param="service" match="videostream"/> 6 </target> 7 <rule id="5ABE" effect="permit"> 8 <condition> 9 <context param="location" match="home"/> 10 </condition> 11 </rule> 12 <rule effect="deny"/> 13 </policy> 14 <policy> 15 <target> 16 <subject id="F3MK"/> 17 </target> 18 <rule effect="deny"/> 19 </policy> 20 </policy-set>
1 <policy-set id="Obfuscated Alice’s policyset"> 2 <policy algorithm="permit-overrides"> 3 <target> 4 <subject param="cert" match="Carol.cert"/> 5 <resource param="service" match="videostream"/> 6 </target> 7 <rule id="5ABE" effect="permit" obfuscated> 8 <condition> 9 <context param="E67QF1" match="AR7MG6"/> 10 </condition> 11 </rule> 12 <rule effect="deny"/> 13 </policy> 14 <policy algorithm="deny-overrides"> 15 <target> 16 <subject id="F3MK" obfuscated/> 17 </target> 18 <rule effect="deny"/> 19 </policy> 20 </policy-set>
4.4. Partial Disclosure Policy Enforcement
- the initialization phase, in which an intermediate provider (Bob) can “negotiate” the policy disclosure with the component provider (Alice) requiring only the policy’s information toward a pre-determined set of subjects;
- the incremental update phase, in which the intermediate provider requires additional information every time a new subject (which is not included in the original set of the considered subjects) requires access to the service.
4.5. Considerations
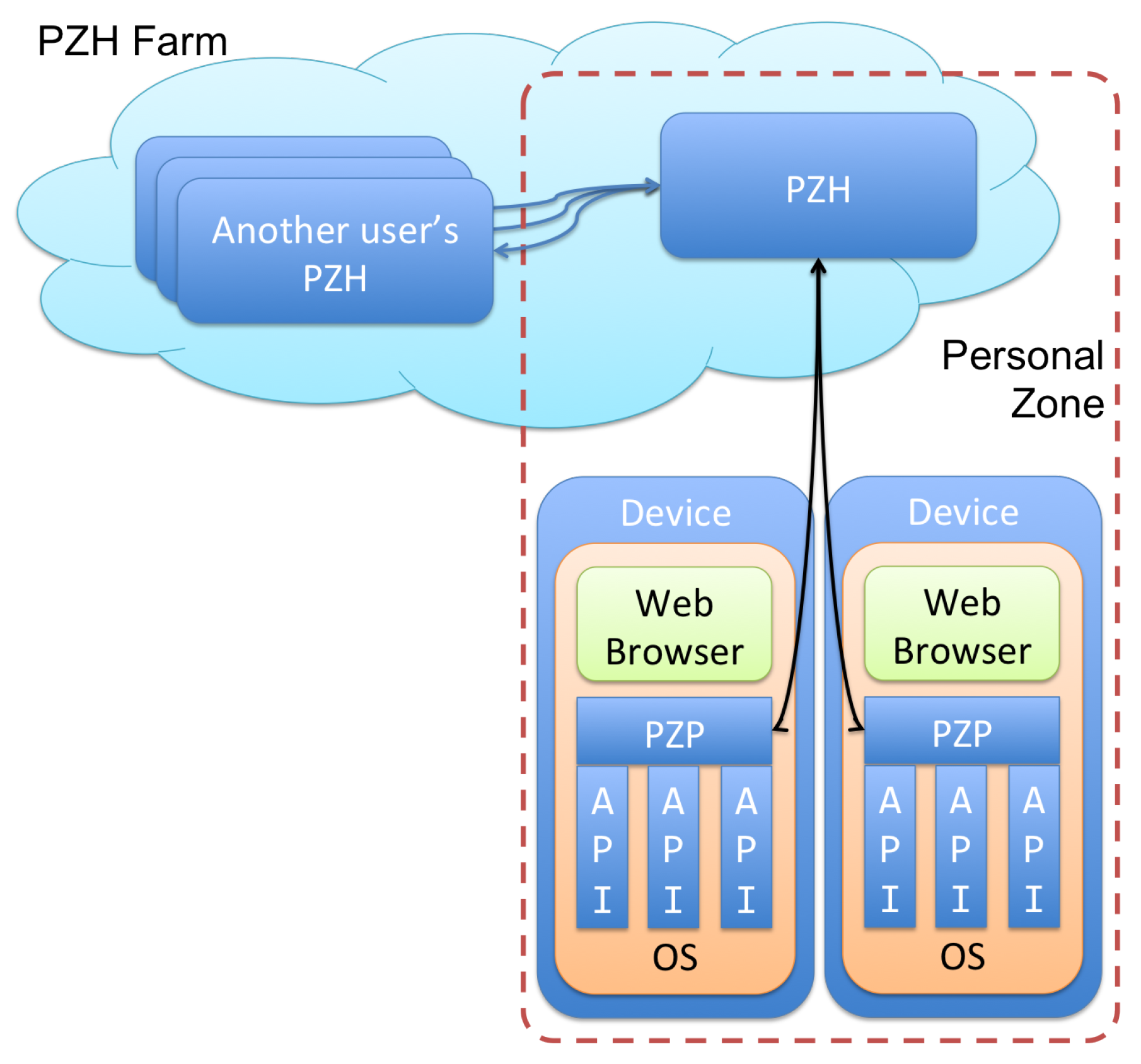
5. A Cloud Approach
5.1. Mobile Constraints
5.2. Architecture
- The Decision Wrapper creates the initial policy enforcement query based on incoming requests;
- The Access Manager makes the final decision by combining pieces of information from XACML access control and Data Handling Decision Function (DHDF);
- The DHDF Engine provides privacy and data handling functionalities;
- The Request Context manages all contextual information; it stores all the data and credentials released by a user in a given session;
- The PDP Cache (PDPC) stores PDP decisions that could be shared among personal devices.
5.3. Considerations on Design Choices
6. Related Work
7. Conclusions
Acknowledgments
Author Contributions
Conflicts of Interest
References
- IFTTT. IF This Then That. 2011. Available online: http://www.ifttt.com (accessed on 5 July 2017).
- OMA. Open Mashup Alliance. 2009. Available online: https://en.wikipedia.org/wiki/Open_Mashup_Alliance (accessed on 5 July 2017).
- APIANT. The Cloud Integration and Automation Platform | APIANT. 2016. Available online: https://apiant.com (accessed on 5 July 2017).
- Jensen, C.S.; Vicente, C.R.; Wind, R. User-Generated Content: The Case for Mobile Services. Computer 2008, 41, 116–118. [Google Scholar] [CrossRef]
- Zhao, Z.; Laga, N.; Crespi, N. A survey of user generated service. In Proceedings of the 2009 IC-NIDC IEEE International Conference on Network Infrastructure and Digital Content, Beijing, China, 6–8 November 2009; pp. 241–246. [Google Scholar]
- Xia, F.; Yang, L.T.; Wang, L.; Vinel, A. Internet of Things. Int. J. Commun. Syst. 2012, 25, 1101–1102. [Google Scholar] [CrossRef]
- Fuhrhop, C.; Lyle, J.; Faily, S. The webinos Project. In Proceedings of the 21st International Conference Companion on World Wide Web, WWW’12 Companion, New York, NY, USA, 16–20 April 2012; pp. 259–262. [Google Scholar]
- Marine-Roig, E.; Clavé, S.A. Tourism analytics with massive user-generated content: A case study of Barcelona. J. Destin. Mark. Manag. 2015, 4, 162–172. [Google Scholar] [CrossRef]
- Ventura, D.; Monteleone, S.; La Torre, G.; La Delfa, G.C.; Catania, V. Smart EDIFICE—Smart EveryDay interoperating future devICEs. In Proceedings of the 2015 International Conference on Collaboration Technologies and Systems (CTS), Atlanta, GA, USA, 1–5 June 2015; pp. 19–26. [Google Scholar]
- Speiser, S. Policy of Composition ≠ Composition of Policies. In Proceedings of the 2011 IEEE International Symposium on Proceedings of the Policies for Distributed Systems and Networks (POLICY), Pisa, Italy, 6–8 June 2011; pp. 121–124. [Google Scholar]
- Guinard, D.; Trifa, V.; Karnouskos, S.; Spiess, P.; Savio, D. Interacting with the SOA-Based Internet of Things: Discovery, Query, Selection, and On-Demand Provisioning of Web Services. IEEE Trans. Serv. Comput. 2010, 3, 223–235. [Google Scholar] [CrossRef]
- Catania, V.; La Torre, G.; Monteleone, S.; Panno, D.; Patti, D. User-Generated services: Policy Management and access control in a cross-domain environment. In Proceedings of the 2015 International Wireless Communications and Mobile Computing Conference (IWCMC), Dubrovnik, Croatia, 24–28 August 2015; pp. 668–673. [Google Scholar]
- Catania, V.; La Torre, G.; Monteleone, S.; Patti, D.; Vercelli, S.; Ricciato, F. A novel approach to Web of Things: M2M and enhanced javascript technologies. In Proceedings of the 2012 IEEE International Conference on Green Computing and Communications (GreenCom), Besancon, France, 20–23 November 2012; pp. 726–730. [Google Scholar]
- Satoh, F.; Tokuda, T. Security Policy Composition for Composite Web Services. IEEE Trans. Serv. Comput. 2011, 4, 314–327. [Google Scholar] [CrossRef]
- Dong, C.; Russello, G.; Dulay, N. Shared and Searchable Encrypted Data for Untrusted Servers. In Data and Applications Security XXII; Lecture Notes in Computer Science; Atluri, V., Ed.; Springer: Berlin/Heidelberg, Germany, 2008; Volume 5094, pp. 127–143. [Google Scholar]
- Webinos. Webinos Developer Portal. Available online: https://developer.webinos.org (accessed on 5 July 2017).
- Ardagna, C.A.; De Capitani di Vimercati, S.; Paraboschi, S.; Pedrini, E.; Samarati, P. An XACML-based privacy-centered access control system. In Proceedings of the first ACM Workshop on Information Security Governance, Chicago, IL, USA, 13 November 2009; pp. 49–58. [Google Scholar]
- Moses, T. Extensible Access Control Markup Language 2.0 Specification Set. Available online: http://www.oasis-open.org (accessed on 5 July 2017).
- Lyle, J.; Monteleone, S.; Faily, S.; Patti, D.; Ricciato, F. Cross-platform access control for mobile web applications. In Proceedings of the 2012 IEEE International Symposium on Policies for Distributed Systems and Networks (POLICY), Chapel Hill, NC, USA, 16–18 July 2012; pp. 37–44. [Google Scholar]
- Tacken, J.; Flake, S.; Golatowski, F.; Prüter, S.; Rust, C.; Chapko, A.; Emrich, A. Towards a Platform for User-Generated Mobile Services. In Proceedings of the 2010 IEEE 24th International Conference on Advanced Information Networking and Applications Workshops (WAINA), Perth, Australia, 20–23 April 2010; pp. 532–538. [Google Scholar]
- Shelton, T.; Poorthuis, A.; Zook, M. Social media and the city: Rethinking urban socio-spatial inequality using user-generated geographic information. Landsc. Urban Plan. 2015, 142, 198–211. [Google Scholar] [CrossRef]
- Venerandi, A.; Quattrone, G.; Capra, L.; Quercia, D.; Saez-Trumper, D. Measuring Urban Deprivation from User Generated Content. In Proceedings of the 18th ACM Conference on Computer Supported Cooperative Work & Social Computing (CSCW), Vancouver, BC, Canada, 14–18 March 2015; pp. 254–264. [Google Scholar]
- Stavrianea, A.; Kavoura, A. Social media’s and online user-generated content’s role in services advertising. AIP Conf. Proc. 2015, 1644, 318–324. [Google Scholar]
- Deng, S.; Huang, L.; Wu, H.; Wu, Z. Constraints-Driven Service Composition in Mobile Cloud Computing. In Proceedings of the 2016 IEEE International Conference on Web Services (ICWS), San Francisco, CA, USA, 27 June–2 July 2016; pp. 228–235. [Google Scholar]
- Ortiz, A.; Hussein, D.; Park, S.; Han, S.; Crespi, N. The Cluster Between Internet of Things and Social Networks: Review and Research Challenges. IEEE Int. Things J. 2014, 1, 206–215. [Google Scholar] [CrossRef]
- Jara, A.J.; Zamora-Izquierdo, M.A.; Skarmeta, A.F. Interconnection Framework for mHealth and Remote Monitoring Based on the Internet of Things. IEEE J. Sel. Areas Commun. 2013, 31, 47–65. [Google Scholar] [CrossRef]
- Lee, S.; Chong, I. User-centric intelligence provisioning in web-of-objects based IoT service. In Proceedings of the 2013 International Conference on ICT Convergence (ICTC), Jeju, Korea, 14–16 October 2013; pp. 44–49. [Google Scholar]
- Toninelli, A.; Montanari, R.; Kagal, L.; Lassila, O. A Semantic Context-aware Access Control Framework for Secure Collaborations in Pervasive Computing Environments. In Proceedings of the 5th International Conference on The Semantic Web; Springer-Verlag: Berlin, Germany, 2006; pp. 473–486. [Google Scholar]
- Yahyaoui, H.; Almulla, M. Context-based specification of Web service policies using WSPL. In Proceedings of the 2010 Fifth International Conference on Digital Information Management (ICDIM), Thunder Bay, ON, Canada, 5–8 July 2010; pp. 496–501. [Google Scholar]
- Kapsalis, V.; Hadellis, L.; Karelis, D.; Koubias, S. A Dynamic Context-aware Access Control Architecture for e-Services. Comput. Secur. 2006, 25, 507–521. [Google Scholar] [CrossRef]
- Cheaito, M.; Laborde, R.; Barrere, F.; Benzekri, A. An extensible XACML authorization decision engine for context aware applications. In Proceedings of the 2009 Joint Conferences on the Pervasive Computing (JCPC), Tamsui, Taipei, Taiwan, 3–5 December 2009; pp. 377–382. [Google Scholar]
- Li, H.; Yang, Y.; He, Z.; Hu, G. Context-aware Access Control Policy Research for Web Service. In Proceedings of the 2011 First International Conference on Instrumentation, Measurement, Computer, Communication and Control (IMCCC), Beijing, China, 21–23 October 2011; pp. 529–532. [Google Scholar]
- Mohan, A.; Blough, D.M. An attribute-based authorization policy framework with dynamic conflict resolution. In Proceedings of the 9th Symposium on Identity and Trust on the Internet, Gaithersburg, MD, USA, 13–15 April 2010; ACM: New York, NY, USA, 2010; pp. 37–50. [Google Scholar]
- Kayes, A.; Han, J.; Colman, A. An ontology-based approach to context-aware access control for software services. In International Conference on Web Information Systems Engineering; Springer: Berlin/Heidelberg, Germany, 2013; pp. 410–420. [Google Scholar]





| # | Alice’s Context | Alice’s Policy | Conflict? |
|---|---|---|---|
| 1 | A is in Catania | C is A’s relative | NO |
| 2 | A is in Catania | C isn’t A’s relative | YES |
| 3 | A isn’t in Catania | C is A’s relative | YES |
| 4 | A isn’t in Catania | C isn’t A’s relative | YES |
© 2017 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Catania, V.; La Torre, G.; Monteleone, S.; Panno, D.; Patti, D. User-Generated Services Composition in Smart Multi-User Environments. J. Sens. Actuator Netw. 2017, 6, 20. https://doi.org/10.3390/jsan6030020
Catania V, La Torre G, Monteleone S, Panno D, Patti D. User-Generated Services Composition in Smart Multi-User Environments. Journal of Sensor and Actuator Networks. 2017; 6(3):20. https://doi.org/10.3390/jsan6030020
Chicago/Turabian StyleCatania, Vincenzo, Giuseppe La Torre, Salvatore Monteleone, Daniela Panno, and Davide Patti. 2017. "User-Generated Services Composition in Smart Multi-User Environments" Journal of Sensor and Actuator Networks 6, no. 3: 20. https://doi.org/10.3390/jsan6030020
APA StyleCatania, V., La Torre, G., Monteleone, S., Panno, D., & Patti, D. (2017). User-Generated Services Composition in Smart Multi-User Environments. Journal of Sensor and Actuator Networks, 6(3), 20. https://doi.org/10.3390/jsan6030020







