1. Introduction
In recent times, the concept of the Internet of Things (IoT) has become very popular and plays a crucial role in numerous applications such as smart cities, smart grid, and smart healthcare [
1]. It has been demonstrated that IoT applications rely on wireless connections, which are vulnerable to eavesdropping attacks and active jammings [
2]. Notably, in IoT sensor networks that require high-security such as health monitoring and military surveillance, the collected data are private and confidential. Therefore, improving the security of these connections to protect users and data from attackers is important.
In wireless communication systems, the framework of security is provided in different protocol layers and can be classified into two main approaches: information-theoretic security and computational security. The former one is executed by physical layer security (PLS) techniques at the physical (PHY) layer, and the latter is a cryptography approach that performs the encryption and decryption at different layers, such as medium access control (MAC), and PHY [
3].
PLS, a well-known security approach at the PHY layer, aims to achieve information-theoretic security by exploiting channel characteristics [
4,
5]. PLS methods can secure the system by generating artificial noise [
6,
7,
8], creating beamforming [
9,
10,
11], or utilizing cooperative relay [
12,
13]. Although PLS brings some advantages such as flexible security level configurations, QoS guarantee, and less overhead as compared to the cryptography approach [
14], its hardware implementation is complex. It needs high complexity coding and perfect/imperfect channel state information of the receiver and eavesdroppers [
3]. Therefore, PLS is not a suitable security solution for small size transceivers such as IoT sensors.
In the aspect of cryptography, most of the conventional wireless communication systems implement security encryption/decryption at the upper layers, such as the MAC layer, where attackers are able to use general-purpose microprocessor and memory to collect data for cracking the encryption key. Besides, encryption at upper layers might result in the fact that many parts of transmission data are not encrypted, e.g., the MAC header and PHY header. Such information is thus vulnerable to eavesdroppers. Researchers have recently focused attention on moving the encryption to the physical layer for improving the security of wireless connections [
15,
16,
17,
18,
19]. For instance, encryption schemes at the PHY layer based on Polar codes, and chaotic sequences were proposed for the Orthogonal Frequency-Division Multiplexing (OFDM) system in [
20,
21]. Since Polar code is a high-cost encoder/decoder algorithm, it is an optional selection for a big transceiver that needs a high data rate and high reliability. Furthermore, most wireless transceivers nowadays utilize binary convolution code (BCC) encoder and Viterbi decoder as a mandatory. Therefore, a low complexity encryption method which is suitable for BCC code is needed.
Nominated as a promising solution, physical layer encryption (PLE) is considered in this work. PLE was deployed in various OFDM systems, such as constellation scrambling in the frequency domain, modulation symbols rotation [
22,
23,
24], noise enhanced constellation rotation, rateless code [
25], sparse code multiple access [
26], subcarriers encryption [
27]. The position of encryption can be placed before or after the data modulation. In case the encryption is performed after modulation, i.e., also known as phase encryption, the system is considered to be higher security because modulation type such as BPSK, QPSK, 16-256 QAM is also encrypted. However, conventional works on this method still have problems such as having high complexity for high-order modulation (64-256 QAM) and degrading packet error rate (PER) performance of the system. For that reason, PLE works in [
28], and [
29] only supports low complex modulation such as OQPSK.
Our main purpose in this work is to propose a new phase encryption method, named as joint encryption-modulation (JEM), that achieves two targets. Firstly, it does not degrade the PER performance of the communication system. Secondly, it must be low complexity despite system employs or not high-order modulation types (64-256 QAM). We introduce JEM as low complexity and high-performance solution so that the high-security phase encryption can be applied in IoT sensors’ transceiver.
In summary, the main contributions of this study are as follows:
We propose a low-complexity JEM method for performing phase encryption in the PHY layer of IoT sensor transceivers.
We provide PER and BER performance analysis of the proposed JEM method to prove that the implementation of JEM does not degrade the performance of PHY transceiver.
We practically implement the JEM method in hardware, and we show that the complexity of JEM is low despite of the modulation types (BPSK, QPSK, 16-256 QAM).
We choose and design a lightweight stream cipher Grain 128a to generate ciphering keys for the practical implementation of the proposed JEM method.
The rest of this paper is organized as follows.
Section 2 provides the background of the physical layer encryption, related work, and the basic idea of the proposed method. Then, the algorithm of the proposed JEM method is presented in
Section 3.
Section 4 describes the hardware design.
Section 5 provides numerical results and discussion. Finally,
Section 6 is the conclusion and future work.
2. Background
In this section, we introduce PLE in the PHY transceiver model. Then, we survey recent work related to our proposed method. Finally, we present the basic idea of the proposed JEM method.
2.1. PLE in the Physical Layer Transceiver Model
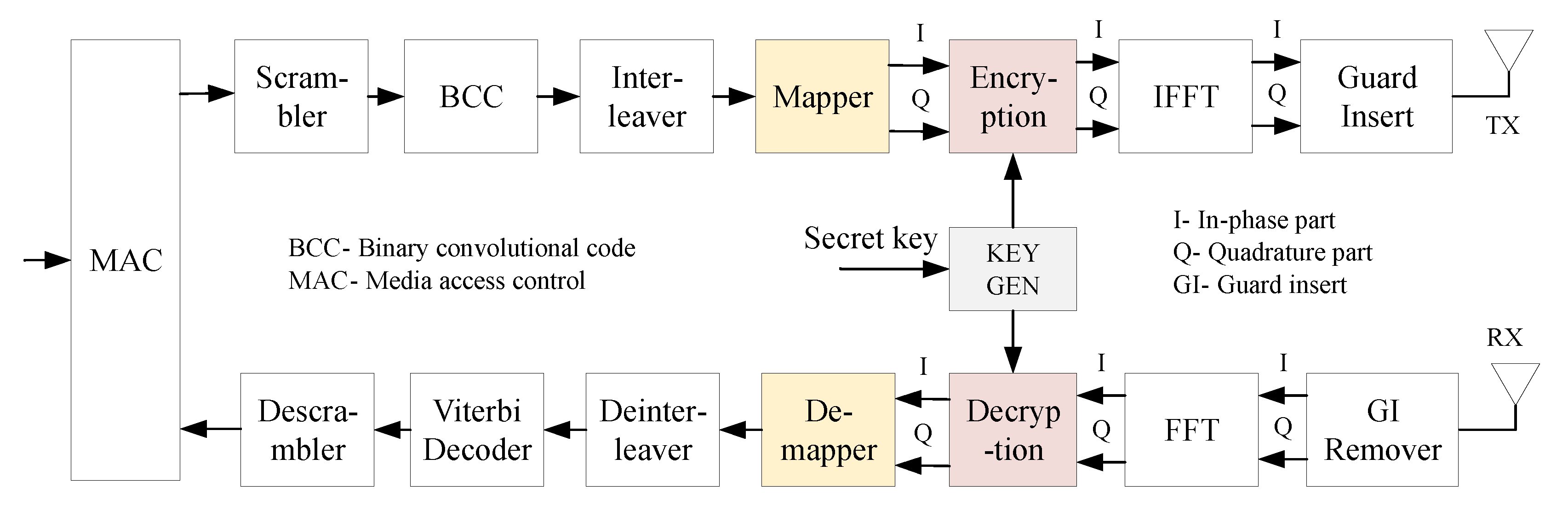
Figure 1 shows a block diagram of the PHY layer of a basic wireless communication system when implementing PLE. At the transmitter, data received from the MAC layer are scrambled, encoded by Binary convolution code (BCC), interleaved, and mapped into the constellation of predefined modulation. The modulated data are then encrypted by the ciphering key generated from the “KEY GEN” block. “KEY GEN” can be any cryptography algorithm such as Grain, RC4. Because data are encrypted after modulation, both modulated data streams (in-phase part (IP) and quadrature part (QP)) must be encrypted. The processing inside the encryption determines how the ciphering key makes a change to the modulated data. At the receiver side, the decryption is executed oppositely to recover the IP and the QP of the modulated symbols. In order to decrypt data successfully, the receiver must implement the same cryptography algorithm and keep the same secret key as the transmitter does.
2.2. Related Works
As surveyed, some typical PLE methods have been proposed in the literature. The first one is to encrypt only the sign bit of the modulated data [
30]. In this way, the encrypted data still exists on the modulation constellation. As a result, it does not degrade the BER and PER performance of the system. However, this approach remains concerned about security because it does not encrypt amplitude information of the data. Such data is available for attackers.
In [
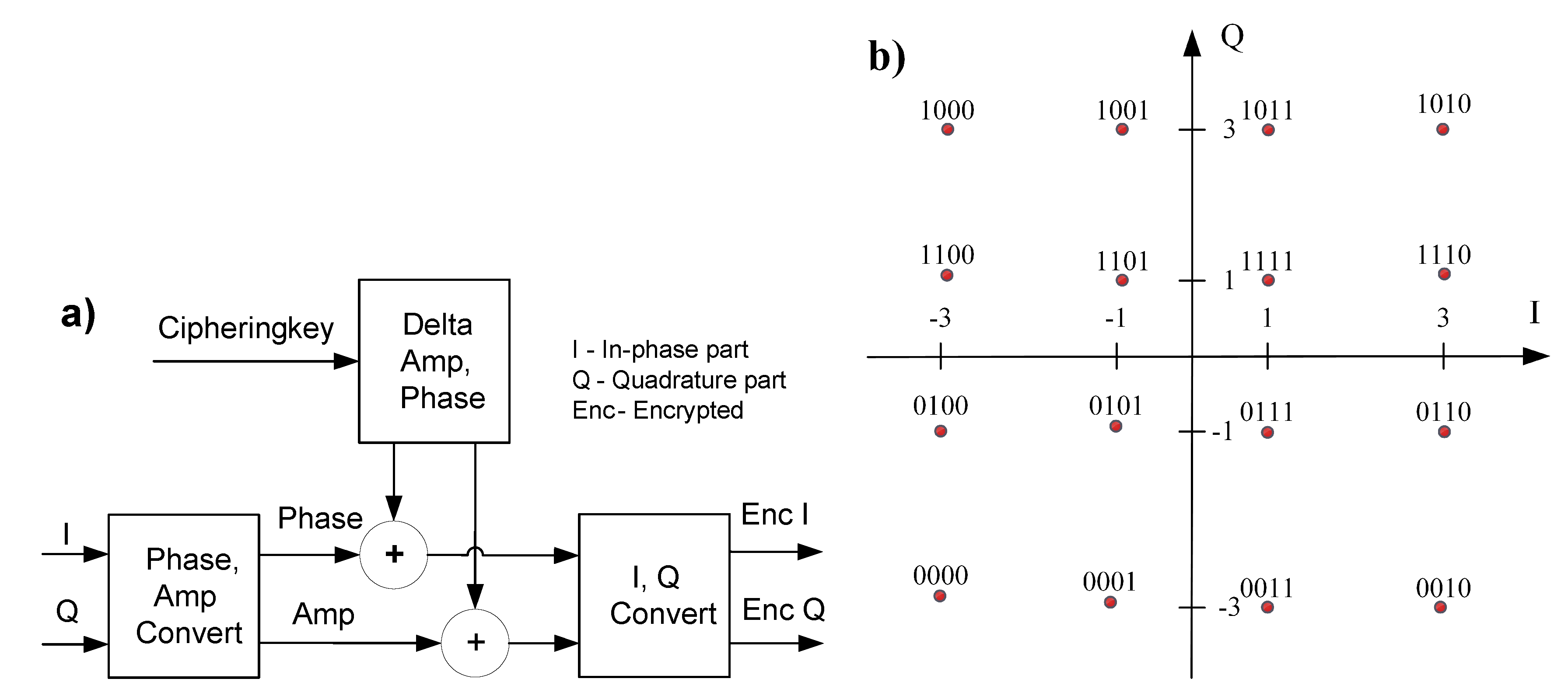
22], the authors proposed a method to encrypt both sign and amplitude information of the modulated data. To prepare for the encryption process, it firstly converts IP and QP parts of the modulated data into the corresponding amplitude, and phase components refer to
Figure 2a. At the same time, the value of the ciphering key is converted into the equivalent delta phase and delta amplitude. The encryption is performed by adding or subtracting the phase and amplitude of the modulated data with the delta phase and amplitude, respectively. Finally, the encrypted phase and amplitude must be converted back to the corresponding IP and QP components. This approach is considered to be high security because it encrypts all components of the modulated data. However, it remains two main disadvantages. Firstly, the encryption is expected to degrade the PER performance of the communication system because the encrypted data no longer locates in the constellation of modulation. As a result, the receiver has more difficulty in recovering the transmitted data and thus produces more error detection. Secondly, the complexity of encryption is high and is proportional to the complexity of modulation.
In other work [
28], the encryption was implemented at the PHY layer instead of at the MAC layer in the original 802.15.4 standard. Another encrypted 802.15.4 transceiver was also proposed in [
29]. The hardware resource-consuming was reduced by exploiting the lightweight stream cipher Simeck 32/64. However, both works [
28,
29] implemented the encryption only for low complexity OQPSK modulation.
In [
31], the authors presented an asymmetrical PLE scheme based on elliptic curve cryptography for wireless communications. The drawback of asymmetric cryptosystems is high computational overhead [
32]. In [
33], mathematical models, design frameworks, and cryptographic primitives of PLE were developed. In this work, the constellation modulation lays on the surface of the sphere, which is different from the conventional modulation.
To deal with these drawbacks of current works, a new PLE method that is low complexity does not degrade communication performance and is able to support the state-of-the-art modulation types (BPSK, QPSK, 64-256 QAM, etc.) should be developed.
2.3. Basic Idea of the Proposed JEM Method
Most encryption methods nowadays perform XOR operation to data and ciphering key because of its low complexity. Unfortunately, if merely performing XOR operation into the modulated data, the results will no longer locate in the constellation map. For example, in the case of 16-QAM, as shown in
Figure 2b, the modulated data is mapped into the IP part and QP part in which the values are
. If we apply XOR operation into these values, the results may jump out of the range
. It means that the shape of the constellation is changed. Once the transmitted data is not located in the constellation point, the receiver becomes more difficult to recover the transmitted data. Consequently, the error rate increases, and the performance of communication is reduced.
For the sake of simplicity, we prefer to use XOR operation for encrypting data. At the same time, the encryption should not degrade the performance of the system. A new idea should be proposed to guarantee that the result of XOR-operation between the modulated data and the ciphering key remains in the constellation shape. Our initial idea is to convert the values of constellation points into continuous positive integers such as (16 QAM). We then encrypt these data by XOR them with the equivalent ciphering key. The encrypted data certainly remains in the range (16 QAM). Finally, the encrypted data are converted back to values of constellation points, i.e., (16-QAM).
3. The Joint Encryption-Modulation Method
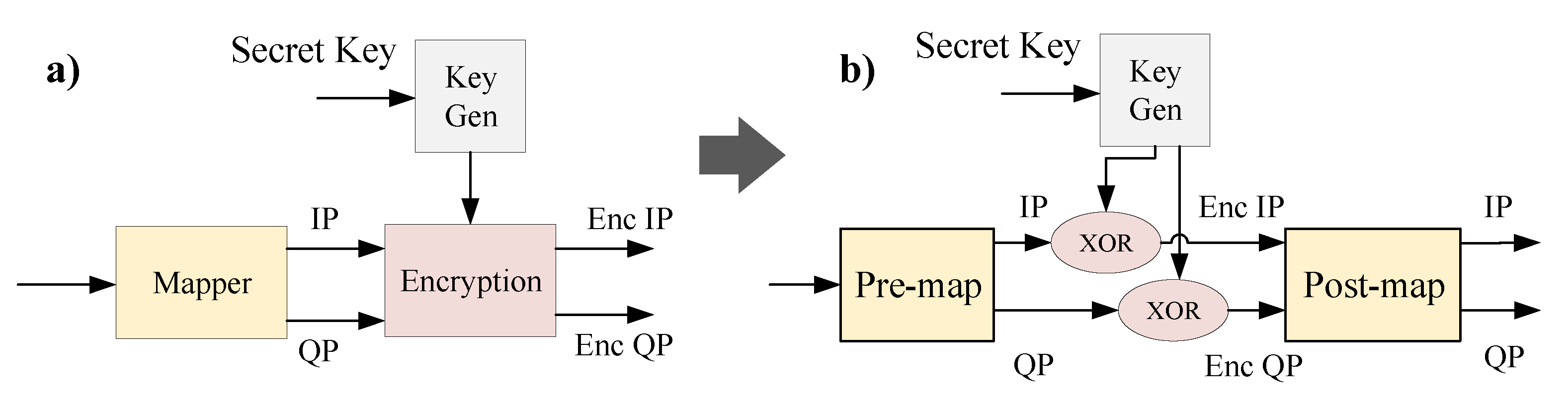
Base on the basic idea mentioned above, we propose the join-encryption-modulation (JEM) method, as shown in
Figure 3. The JEM merges the operation of mapper and encryption into one component. The encryption is divided into two stages named PRE-MAP and POST-MAP. The XOR operation is placed in between two stages to encrypt data. The detailed principle of the proposed JEM method is described as follows.
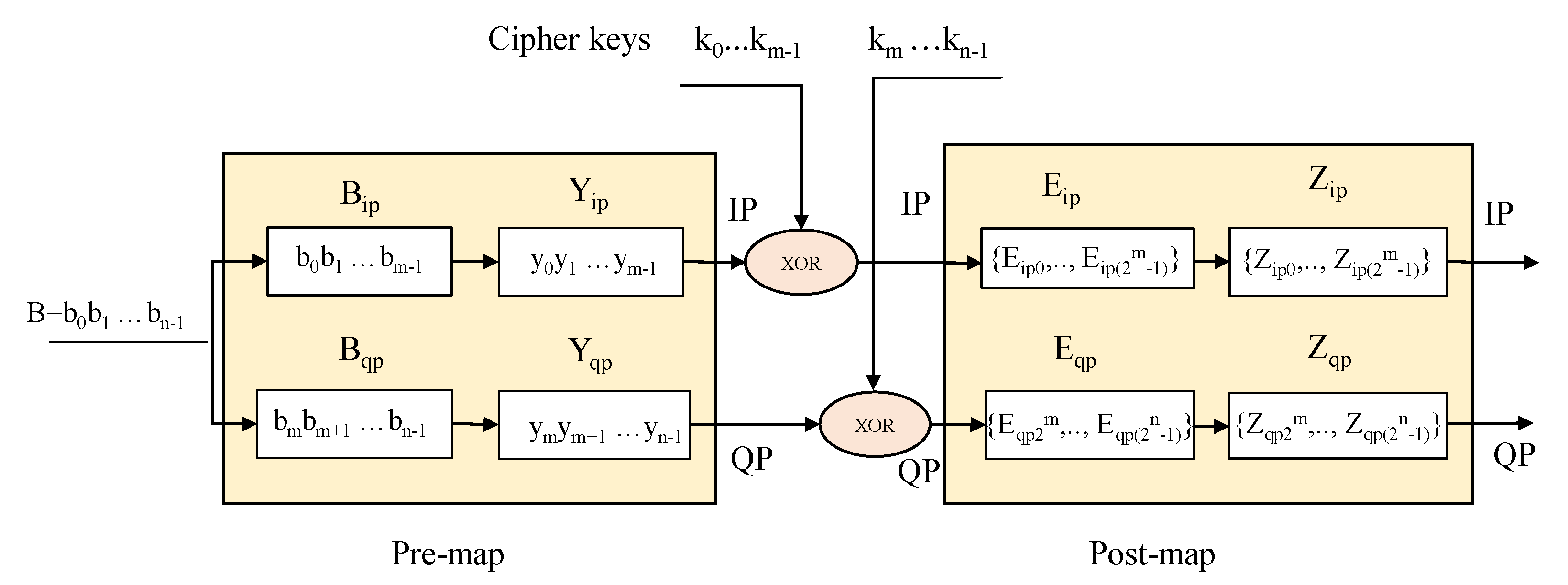
The input binary data,
, are divided into the IP part,
, and the QP part,
, where
is the number of bits per modulated symbol, and
m is the number of bits per IP or QP part. The value of
m is defined in in Equation (
1). In this study, we design and evaluate the proposed JEM for the most used modulation types up to 256-QAM of the wireless communication.
Since the IP part and QP part are similar to each other in terms of data format, we only describe the encryption process of the IP part. The encryption of QP part is performed similarly. Note that, for BPSK, the input data only consists of the IP part. The operation of the proposed JEM for various modulation types in wireless communication is executed in the following three steps, illustrated in
Figure 4:
Step 1, PRE-MAP: The input data of IP part, denoted as
, is first mapped into the continuous pre-map values
by the following mapping rule.
where the continuous pre-map values
are calculated based on the input values
and are formulated by the following equation.
Step 2, ENCRYPTION: The pre-map data
is encrypted by a XOR-operation with the cipher keys
to obtain encrypted data
.
Step 3, POST-MAP: The encrypted data
are then mapped to the post-map values
of the conventional modulation by the mapping rule in Equation (
5). Since the IP part consists of
m bits, there are
possible combinations of them. We number these combinations according to an ascending value of combination as
.
where
, …,
are calculated as follows.
where
.
For a clear explanation of the proposed JEM, we describe in detail the operation for 16-QAM modulation in the next subsection.
JEM for 16-QAM Modulation
For 16-QAM, we have the number of bits per IP/QP part
.
Table 1 illustrates the detailed operation of the proposed JEM. Firstly, the input data IP
=
are mapped into
=
using a PRE-MAP. Then the PRE-MAP’s outputs are encrypted by a XOR-operation with the cipher key. The cipher keys
may have one of the following values {00, 01, 10, 11}. In the POST-MAP, the encrypted data
are again mapped into conventional mapper values
. In which,
may have one of the following values:
.
At the receiver, the decryption performs as the reversed operation of the proposed JEM. It is assumed that the legitimate receiver obtains the same secret key as the transmitter, so the same ciphering keys are generated. In this decryption method, we apply the hard-decision decoding method. The input values of IP and QP parts first compare with the threshold values of the conventional modulation to determine the decoded output as 1 or 0. Then, by using cipher keys, they are decrypted.
4. Hardware Design
After completing simulation and evaluating BER and PER performances of the proposed JEM, we designed the hardware to analyze the hardware complexity and to prove that our proposed JEM can be practically implemented. The hardware of the proposed JEM supports a variety of modulation types, such as BPSK, QPSK, 16-QAM, 64-QAM, and 256-QAM. In this paper, we show in detail the hardware implementation of encryption. There may be several ways to design the decryption at the receiver side. The explanation of the hardware design of decryption is out of the scope of this paper. We only show the implementation result to prove its practical feasibility.
4.1. Overview Hardware Architecture of JEM Method
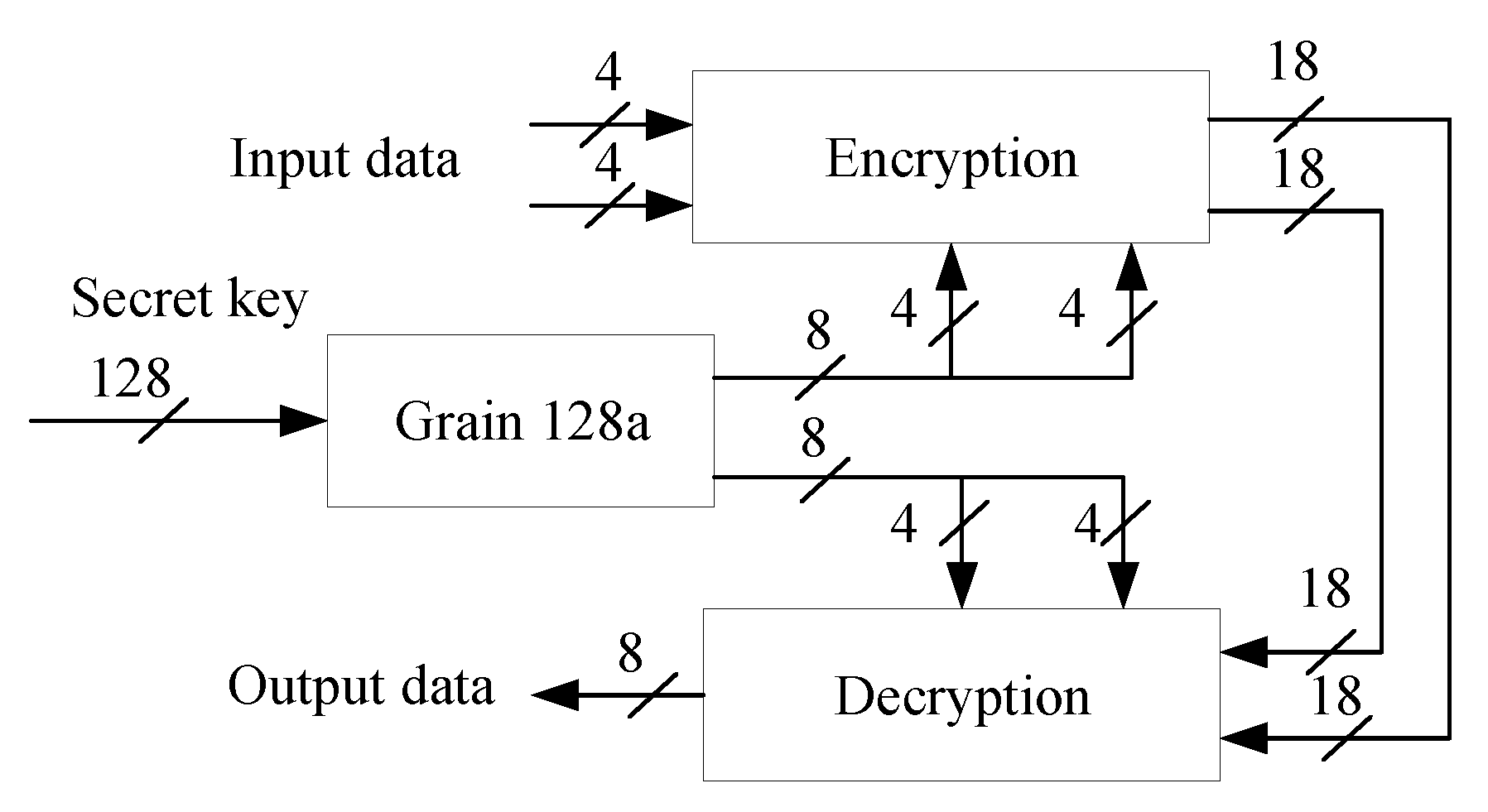
Figure 5 presents the overview hardware architecture of the JEM encryption and decryption process. It consists of three blocks, i.e., encryption, decryption, and stream cipher Grain 128a. The input data is encrypted in the encryption block using cipher keys generated by the Grain 128a block. Similarly, the decryption block decrypts the encrypted data produced by the encryption block. For the sake of comparison, we also designed the hardware of the conventional encryption and decryption method in [
22] and conventional mapper and demapper to compare with our encryption and decryption. Based on the results of [
34] and our experience in hardware implementation, we chose 18 bits as the fixed point for data representation, which does not affect the performance of the system and benefits the hardware implementation.
To achieve low complexity, in addition to utilizing the proposed JEM, the lightweight keystream generator also plays an important role.
4.2. Lightweight Keystream Generator
The encryption and decryption processes need keystreams generated by cipher algorithms. There are two types of ciphers known as block-cipher and stream-cipher. In this design, we chose a stream cipher rather than a block cipher due to following reasons.
There are many types of stream ciphers, such as RC4, Grain 128a, A5, Mickey, Trivium. Although RC4 is one of the most widely used stream ciphers, it uses much more hardware resources and consumes more power than the others do [
29]. In this work, we chose stream cipher Grain 128a because it is lightweight and more suitable for IoT sensors. We developed the hardware for both RC4 and Grain 128a stream cipher for comparison and finally choose Grain 128a for implementation. The details of Grain 128a can be found in [
35]. Further, we designed the Grain 128a hardware to generate 8-bit keystreams per clock cycle to encrypt and decrypt the IP and QP parts.
As shown in
Table 2, the slices look-up tables (LUTs) of Grain 128a is less than half of RC4’s slice LUTs. In addition, the static power and area of Grain 128a is also about half of the designed RC4 version.
4.3. JEM’s Encryption and Decryption
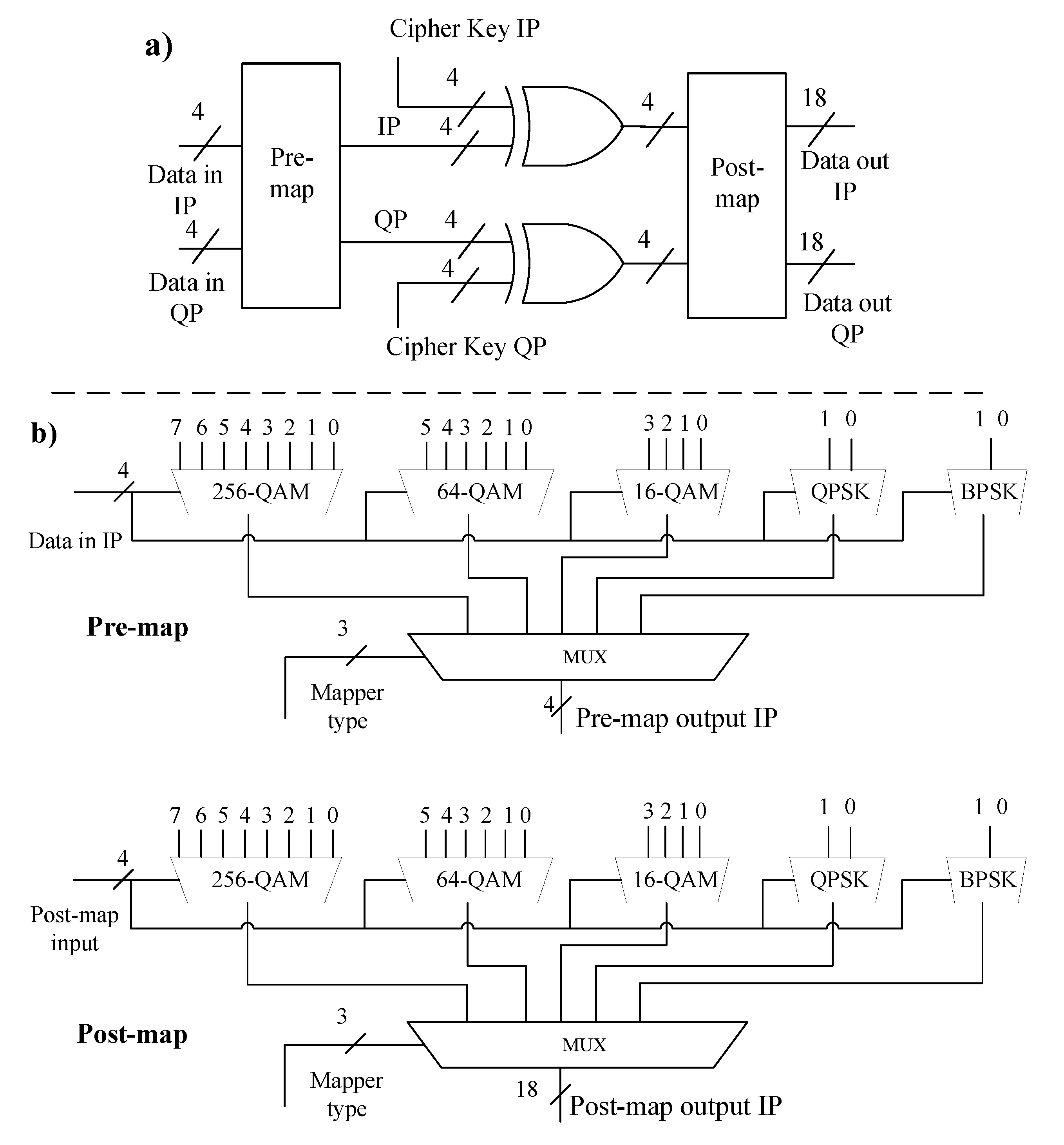
Figure 6a shows the overview hardware architecture of JEM’s encryption. It consists of a PRE-MAP block, POST-MAP block, and XOR-encryption. The PRE-MAP block converts input data into continuous positive values. Then the POST-MAP block maps data into the corresponding values of modulation constellation. PRE-MAP and POST-MAP are designed so that they support multiple modulation types such as BPSK, QPSK, 16-256 QAM.
Figure 6b shows hardware implementation inside PRE-MAP and POST-MAP. Because their functions are to map input data into predefined output data, we only need multiplexers to perform the work. No complexity calculation unit is required. Therefore, they consume significantly low hardware resources. Moreover, the encryption between PRE-MAP and POST-MAP employs only XOR gates, which is just a low complexity logic gate.
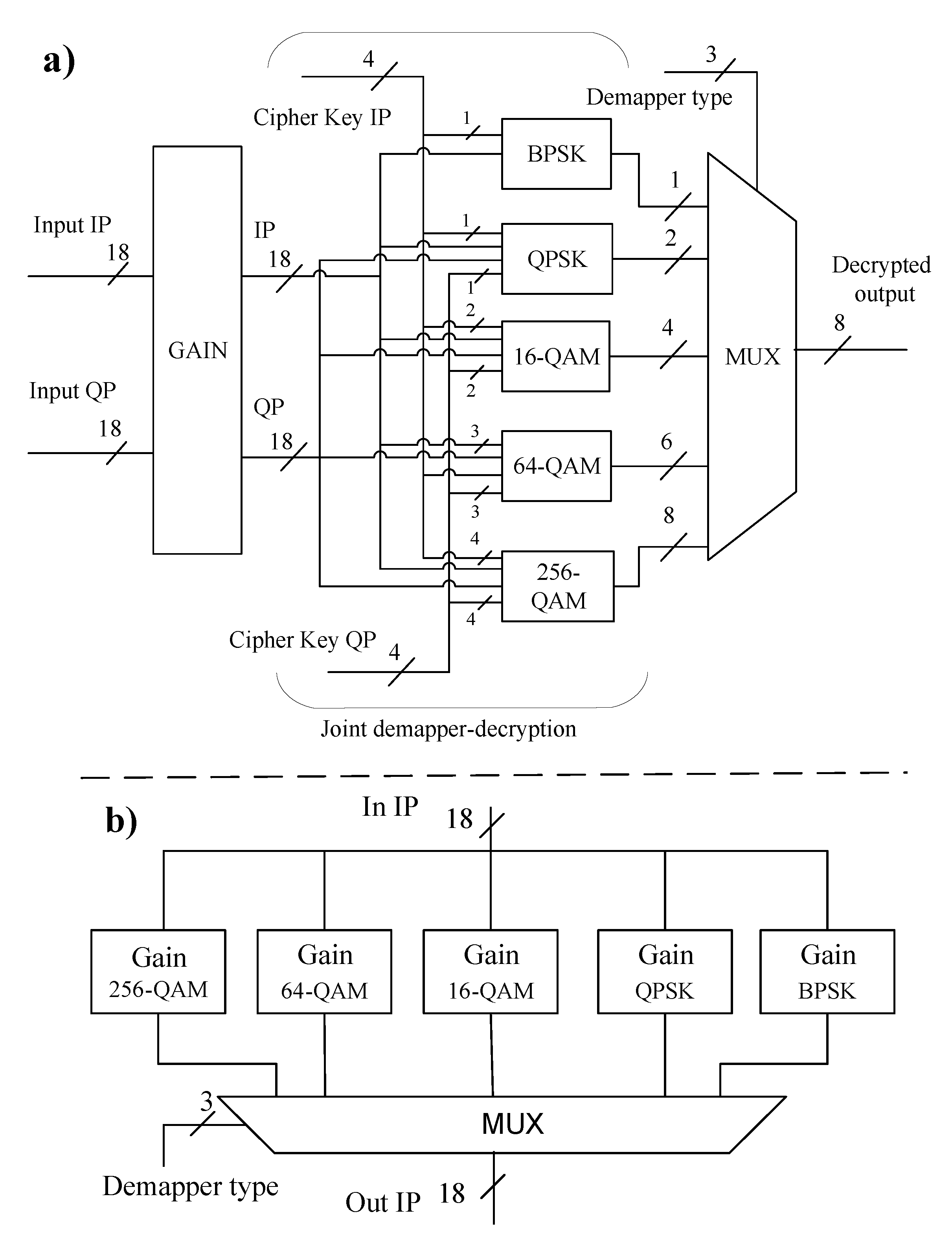
Figure 7a shows the overview hardware architecture of JEM decryption at the receiver side. It consists of a Gain block, joint demapper-decryption, and a MUX block. In this regard, the gain block is responsible for recovering any decrease in the amplitude of the input data by multiplying with a corresponding gain constant of each modulation type, as illustrated in
Figure 7b. The joint demapper-decryption supports different modulation types. In this block, we use several binary fix-point comparators to compare the input data with the threshold values to determine the output values. Then, depending on the value of the cipher key, the decrypted output data is decided.
5. Numerical Results and Evaluation
In this section, we show and analyze the performance simulation and hardware implementation results of the proposed JEM method.
5.1. Simulation Results
Our simulation model follows the IEEE 802.11ah wireless communication network, which is suitable for IoT applications.
Table 3 shows some important parameters used in the simulation. We simulated the system for high order modulations such as 16-QAM, 64-QAM, and 256-QAM. It is assumed that the channel was corrupted by the additive white Gaussian noise (AWGN). The transfer data is random, with 100 bytes per packet. The simulation was run 10,000 times.
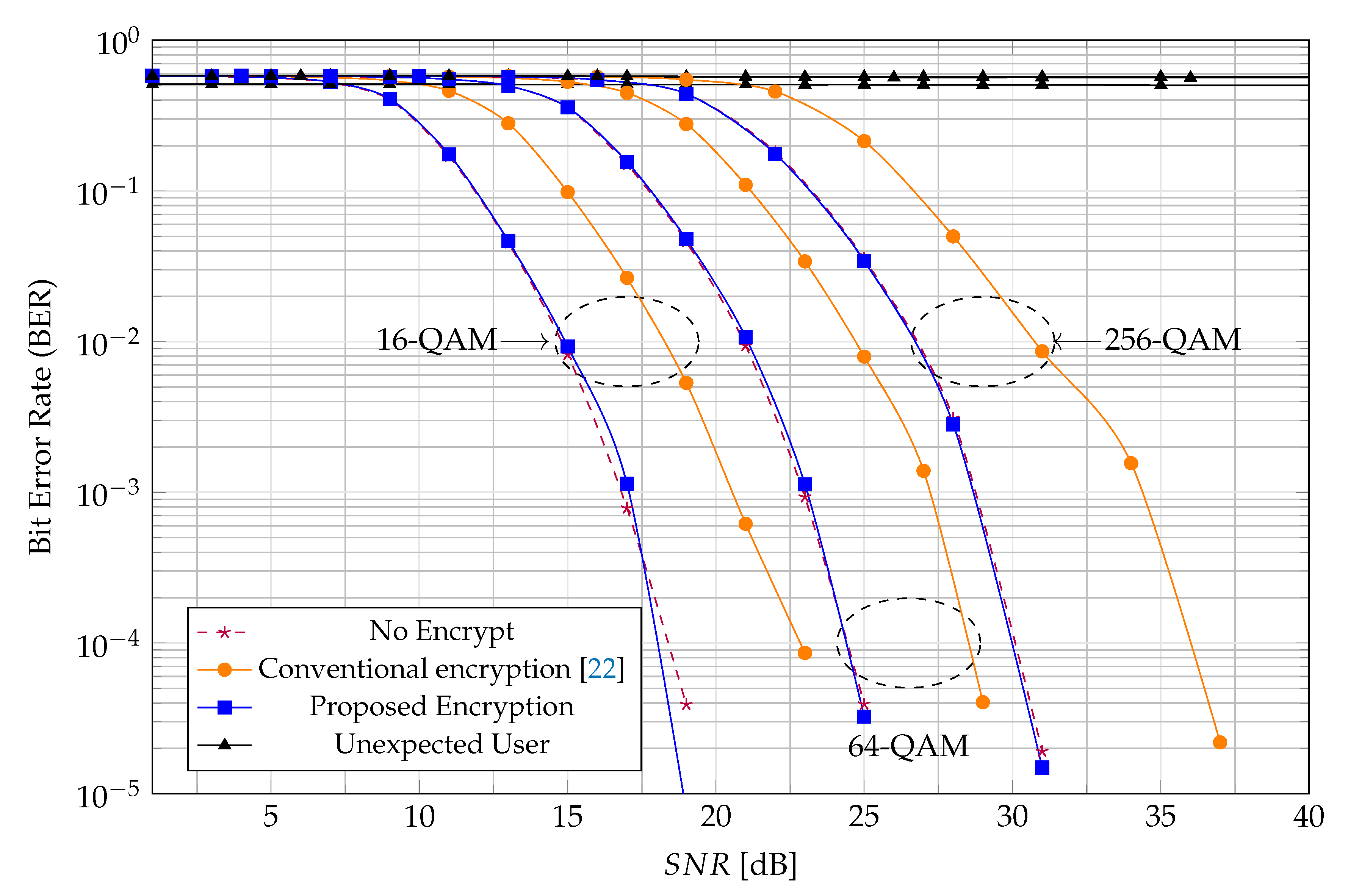
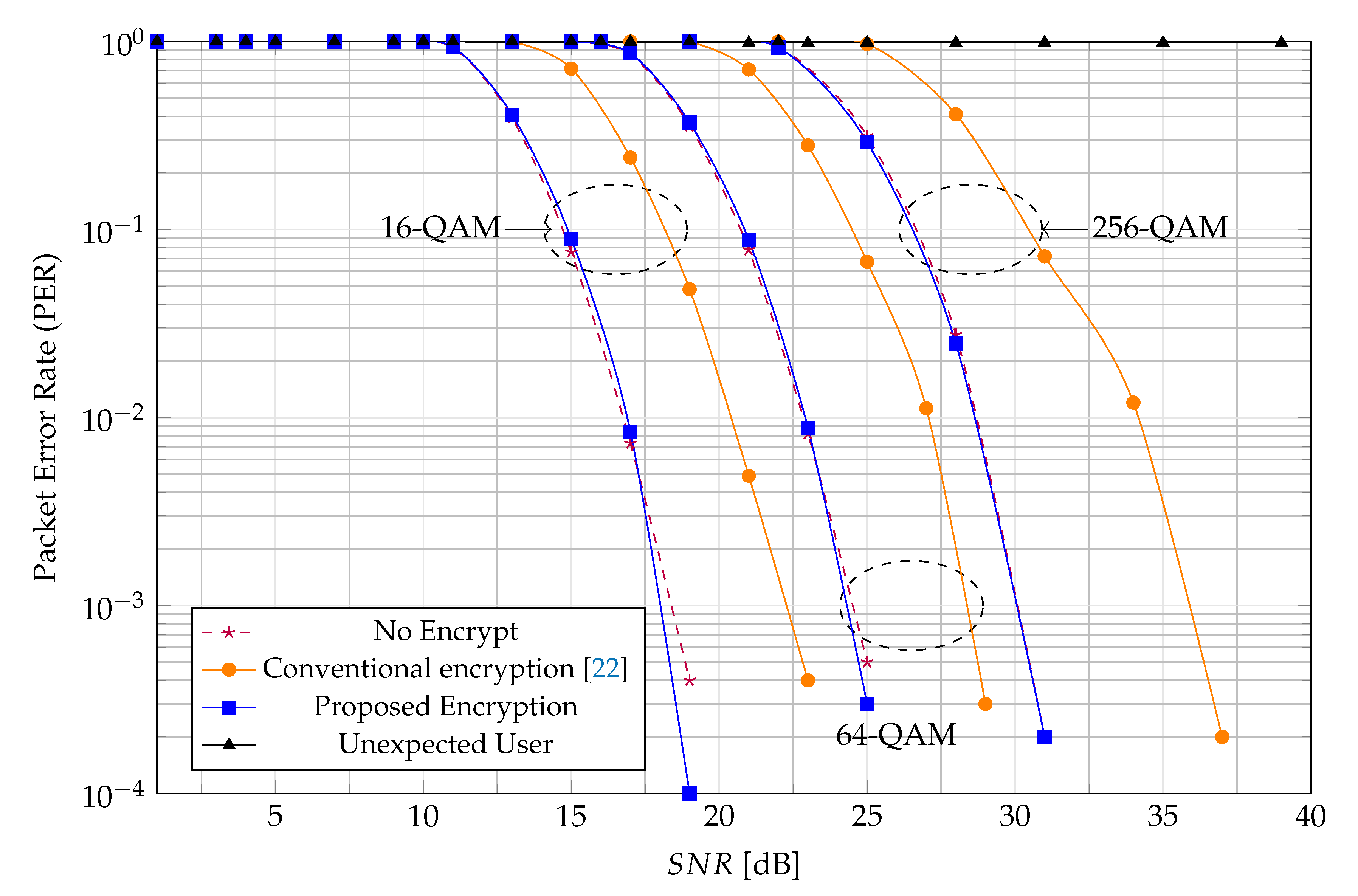
Figure 8 and
Figure 9 show the BER and PER performance of the system for four cases: with the proposed encryption, with no encryption, using the conventional encryption method in [
22], and with an unexpected user who does not obtain the correct key at the receiver side (an eavesdropper). From these figures, we can make the following observations.
Firstly, the proposed JEM has nearly the same BER and PER performances as the unencrypted system for all modulation types (16-QAM, 64-QAM, and 256-QAM). This means that the proposed JEM does not degrade the BER or PER performance. The reason is that the proposed JEM does not change the constellation of modulated symbols. Consequently, it does not affect the error correction performance of the system. Secondly, these figures also show that the conventional method in [
22] degrades the BER and PER performances about 3 dB as compared with the proposed JEM at the observation point of
and
. This result confirms our statement in
Section 2. The main reason for BER and PER performance degradation of [
22] is that the encrypted data of [
22] (which is transmitted to the receiver) do not locate on the constellation points anymore. The transmitted data is thus more sensitive to noise and interference during transmission. In addition, the receiver has more difficulty in recovering the transmitted data, which originally does not locate on the constellation. Error detection rate increases and BER/PER performance degrades.
Finally, the figures show that an unexpected user, who does not have the correct key has approximately 50% BER, and 100% PER. Note that a bit has value either 0 or 1; the 50% of BER is a random bit error rate detection in case the receiver has no information about the transmitter. It does not mean that the receiver of unexpected users can detect the transmitted data. PER = 100% shows that the unexpected user completely not be able to recover the transmitted data. It means the proposed JEM method successfully protects data from an unexpected user who does not own the correct private key.
5.2. Implementation Results
The hardware circuits mentioned in this work were designed by Verilog hardware description language and verified by using the ModelSim simulation tool. FPGA synthesis was performed with Intel Quartus II using a Cyclone IVE EP4CE115F29C7 device. The ASIC synthesis was executed at 16 Mhz frequency by Synopsys’ Design Compiler using VDEC’s Rohm 180 nm technology library.
In theory, we need only 2 XOR gates and multiplexers to implement JEM encoder at the transmitter side of the system supporting N types of modulation. For example, the IEEE 802.11ah system supports five types of modulation (BPSK, QPSK, 16QAM, 64QAM, and 256 QAM) that will need two XOR gates and ten multiplexers for JEM encryption. On the other hand, the complexity of JEM decryption will depend on the decryption algorithm used. In this research, we have successfully developed JEM decryption to recover the encrypted data. However, the detailed explanation of JEM decryption as well as analyzing its complexity are out of the scope of this paper.
It is worth noting that the system employing our JEM method does not need to implement Mapper at the transmitter side and Demapper at the receiver side as the conventional work has. That is because Mapper and Demapper have been merged into JEM encryption and JEM decryption, respectively. For the sake of fairness, we compare JEM encryption with the combination of conventional encryption in [
22] and Mapper. We compare JEM decryption with the combination of conventional decryption in [
22] and Demapper. We synthesized hardware circuits in both hardware platforms FPGA and ASIC. FPGA synthesis results are shown in
Table 4, and ASIC synthesis results are shown in
Table 5. Based on these results, the merits of the JEM method are exposed as follows.
5.2.1. Low FPGA Resource
Table 4 shows that the amount of slice LUTs of JEM encryption is just about 6.5% (229 versus 3516) of that of the conventional work. The amount of slice LUTs of JEM decryption is about 17.8% (713 versus 4016) of that of conventional work. Similarly, the number of registers of JEM encryption and JEM decryption are respectively about 3.8% and 6.7% of those of the conventional work. Overall, the total LUTs of JEM encryption and decryption is just 12.5% of that of conventional encryption and decryption. It means that the JEM method helps to reduce FPGA hardware resources by 87.5%. Our proposed JEM method consumes low FPGA hardware resources.
5.2.2. Small Area
Table 5 shows that ASIC areas of JEM encryption and JEM decryption are respectively about 2.2% (9902 μm
2 versus 436,942 μm
2) and 22.7% (124,372 μm
2 versus 116,628 μm
2) of that of the conventional work. In total, ASIC area of JEM method (encryption + decryption) is about 13.5% of that of conventional work in [
22]. It means that the JEM method helps to reduce ASIC hardware cost by 86.5%.
5.2.3. Low Power Consumption
Table 5 also shows that the JEM method requires less static power consumption than that of the conventional work. In detail, power consumptions of JEM encryption and JEM decryption are respectively 2.5% (0.09 mW versus 3.62 mW) and 31% (1.63 mW versus 5.32 mW) of those of the conventional work in [
22]. The total power consumption of the JEM method is 19.4% of that of conventional work. It means that power consumption is reduced by 80.6%.
Due to the significant reduction in FPGA hardware resource, ASIC area, and ASIC power consumption, the proposed JEM method is a candidate for employing phase encryption in the PHY layer of IoT sensors’ transceiver.
5.3. Security Analysis
Security of JEM is guaranteed because it is a type of phase encryption and it encrypts all bits of the transmitted data. Readers refer to [
27,
28,
29] for the detail analysis and evidence on security of phase encryption. In this work, we propose JEM as a low complexity method that is able to encrypt all bits of modulated data using the existing ciphering key. The strength of security over several types of attacks (Brute force search, etc.) is not affected by JEM method itself but depends on the algorithms that generate the ciphering key. Any cipher algorithms such as Grain 128a, RC4, advanced encryption standard (AES), etc., can be applied for JEM method. The selection of cipher algorithms for JEM method is a trade-off between security requirement and circuit complexity.
In our prototype work, we select Grain 128a stream cipher algorithm to generate ciphering key for JEM method. Security of Grain 128a has been proved in [
35]. Security of our combined JEM and Grain 128a encryption is analyzed through many aspects as follows.
5.3.1. Brute Force Search Attack
In brute force search, all possible combinations of encrypted data have to be collected and analyzed by an exhaustive search operation. Grain 128a has a 128-bit secret key. Therefore, there are
alternative values of ciphering key. Let say system employs 256-QAM modulation, there are 256 possible symbols are encrypted by ciphering keys. It means that the brute force search engine must collect and analyze
possible combinations of encrypted data to be able to successfully decrypt a data frame. For such huge number of combinations, it is difficult enough for brute force search attack. System is considered to be sufficient secure according to current standard [
36].
5.3.2. Traffic Analysis Attack
As a phase encryption, JEM method encrypts not only the transmitted information but also PHY preamble. Consequently, the adversary (or attackers) can not precisely detect the timing of the data transmission due to the difficulties of identifying and synchronizing valid frames. In other words, the proposed JEM method has sufficient resistivity against traffic analysis attacks.
5.3.3. Confidentiality
In the worse case that the eavesdropper successfully decrypts a valid frame by using brute force search, the system still preserves its confidentiality because the entire correct data (from many data frames) can not be recovered without a correct secret key.
5.3.4. Integrity
Thanks to the encryption provided at the PHY layer, all the upper layers’ headers (includes MAC header) are encrypted. Consequently, the system can easily detect whether the source address or the data has been unexpectedly modified or changed during the transmission or not. In short, the system with JEM method achieves better integrity.
5.3.5. Confusion of the Constellations
Confusion of the constellations is an essential factor of the security of the physical layer encryption. JEM method encrypts information relates to types of modulations (BPSK, QPSK, 16-QAM, or 256-QAM, etc.). The adversary (or attackers, eavesdroppers) are thus confused on what the shape of constellation being used. Their attack methods become less efficient.
6. Conclusions
In this study, we have proposed a low complexity join-encryption-modulation (JEM) method for performing phase encryption at the PHY layer of IoT sensors’ transceiver. The BER/PER performance simulation has been conducted. The results have shown that the JEM method does not degrade BER/PER performance of the PHY system, while the BER/PER performance degradation caused by conventional work is about 3 dB. We have also developed hardware circuits of the JEM method and conventional method and synthesized the circuits on two hardware platforms FPGA and ASIC. The results have shown that our proposed JEM method can support multiple modulation types. Hardware resource of the JEM method is only about 12.5% (FPGA resource), or 13.5% (ASIC area) of that of the conventional work. ASIC static power consumption of JEM is about 19.4% of that of conventional work. Because of such a remarkable reduction of hardware complexity, the proposed JEM is a candidate for employing high-security phase encryption at the PHY layer of IoT sensors’ transceiver.
However, it could be seen that the hardware resource of our developed JEM decryption is still high. Further research for reducing the hardware complexity of JEM decryption is needed. Our future work is to find algorithm and low complexity hardware circuit to decrypt JEM encryption. In addition, our plan is to develop the IEEE 802.11ah PHY transceiver that implements JEM encryption and decryption.