Applications in Security and Evasions in Machine Learning: A Survey
Abstract
1. Introduction
2. Survey Methodology for Security Applications
2.1. Study Selections and Search Methods
2.2. Variable Definitions
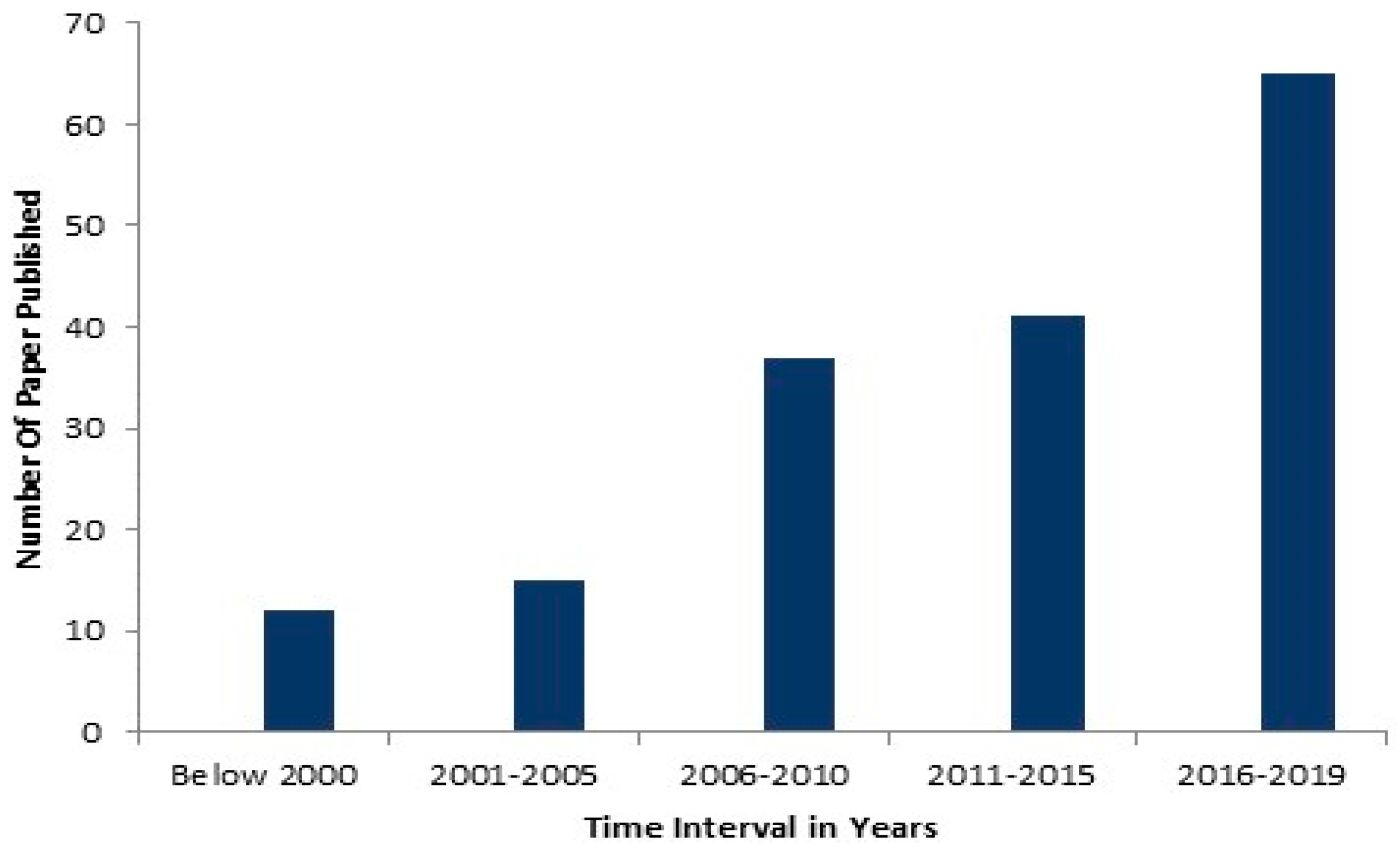
2.3. Time Period Considered
2.4. Studies Characterization
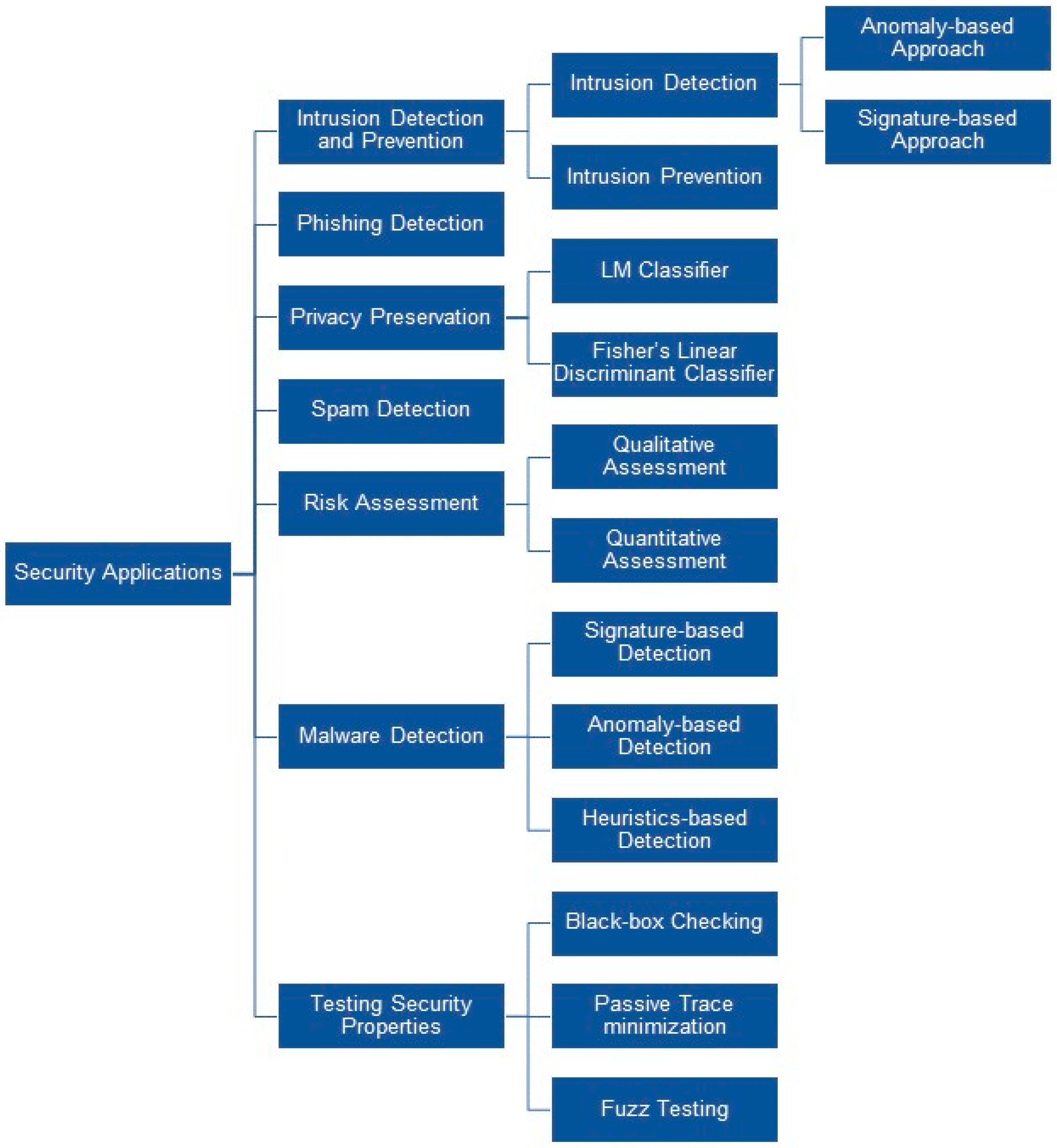
- Intrusion can be separately classified into intrusion detection and intrusion prevention techniques. Further intrusion detection can be classified into an anomaly-based and signature-based approach.
- Anomaly-based intrusion detection detects misuse in a computer or network with the help of machine learning classifiers either normal or anomalous.
- While signature-based detection is identified by the ML classifiers algorithms by identifying specific patterns such as malicious instruction sequences or byte sequences.
- Intrusion prevention is a preemptive approach that identifies potential threats with the help of ML classifiers and responds to them accordingly in order to prevent misuse.
- Phishing detection intended to detect legitimate or phishing web pages and applications which mainly exploit computer users’ vulnerability with the use of ML classifiers.
- Privacy preservation is another important aspect of security where in order to provide security of sensitive information during communication between different parties. Here ML classifiers help to prevent leakage of the sensitive data with other collaborative entities. Linear Means classifier simply computes a multiple of the original LM score function with the same sign and algorithm made confidential by encoding all real vector coefficients as integers and encrypts the input vectors coefficient wise and carries out the linear algebra operations with vectors of ciphertexts. While Fisher’s Linear Discriminant Classifier same procedure is done like LM classifiers but using gradient descent using different weight vector.
- Spam detections like blatant blocking, bulk email filter, category filter, null sender header tag validation, and null sender disposition ML classifiers are used.
- Malware detection, ML classifier formalizes and finds the principals that inhibit the data it examines. If a previously unseen sample is found then it could be the new file and based on the properties it contains the decision has been taken about malware detection. Based on the type of the signature we categorize malware detection techniques into signature-based detection, anomaly-based detection, heuristics based detection.
- Testing Security properties require to ensure the safety and authenticity of the protocol systems. In order to model the testing process in an automated manner, using three techniques namely black-box checking, passive trace minimization, and fuzz testing to fulfill the desired goal of testing security.
3. Machine Learning Applications in Security
3.1. Intrusion Detection and Prevention
3.1.1. Intrusion Detection System Approaches
Signature-Based Approach
Anomaly-Based Approach
3.1.2. Intrusion Prevention
3.2. Phishing Detection
3.3. Privacy Preservation
3.4. Spam Detection
3.5. Risk Assessment
3.6. Malware Detection
3.7. Testing Security Properties
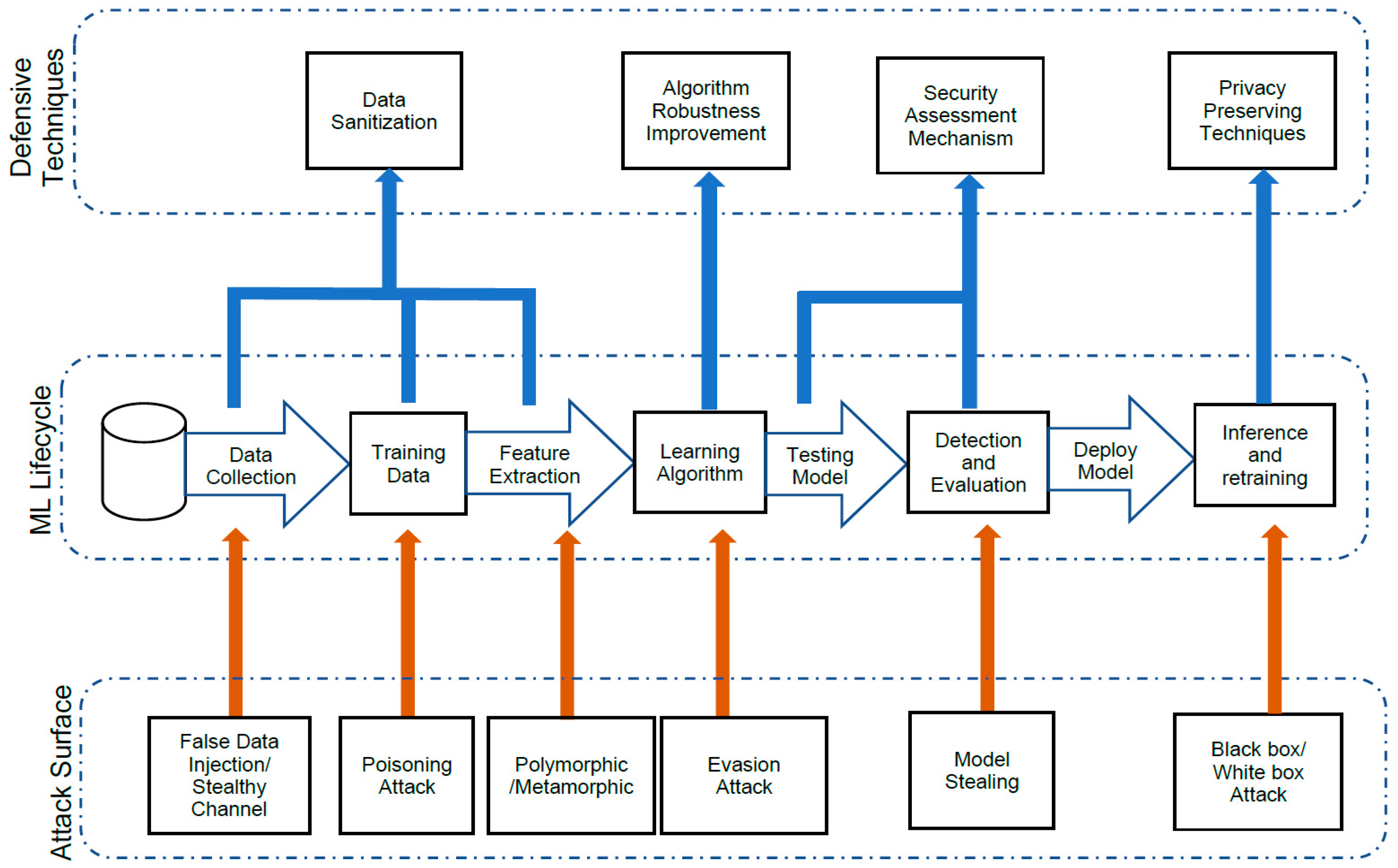
4. Review of Adversarial Attacks on Machine Learning
4.1. Machine Learning Vulnerability Analysis and Threat Model
“Software vulnerability is an instance of a flaw, caused by a mistake in the design, development or configuration of software such that it can be exploited to violate some explicit or implicit security policy.”
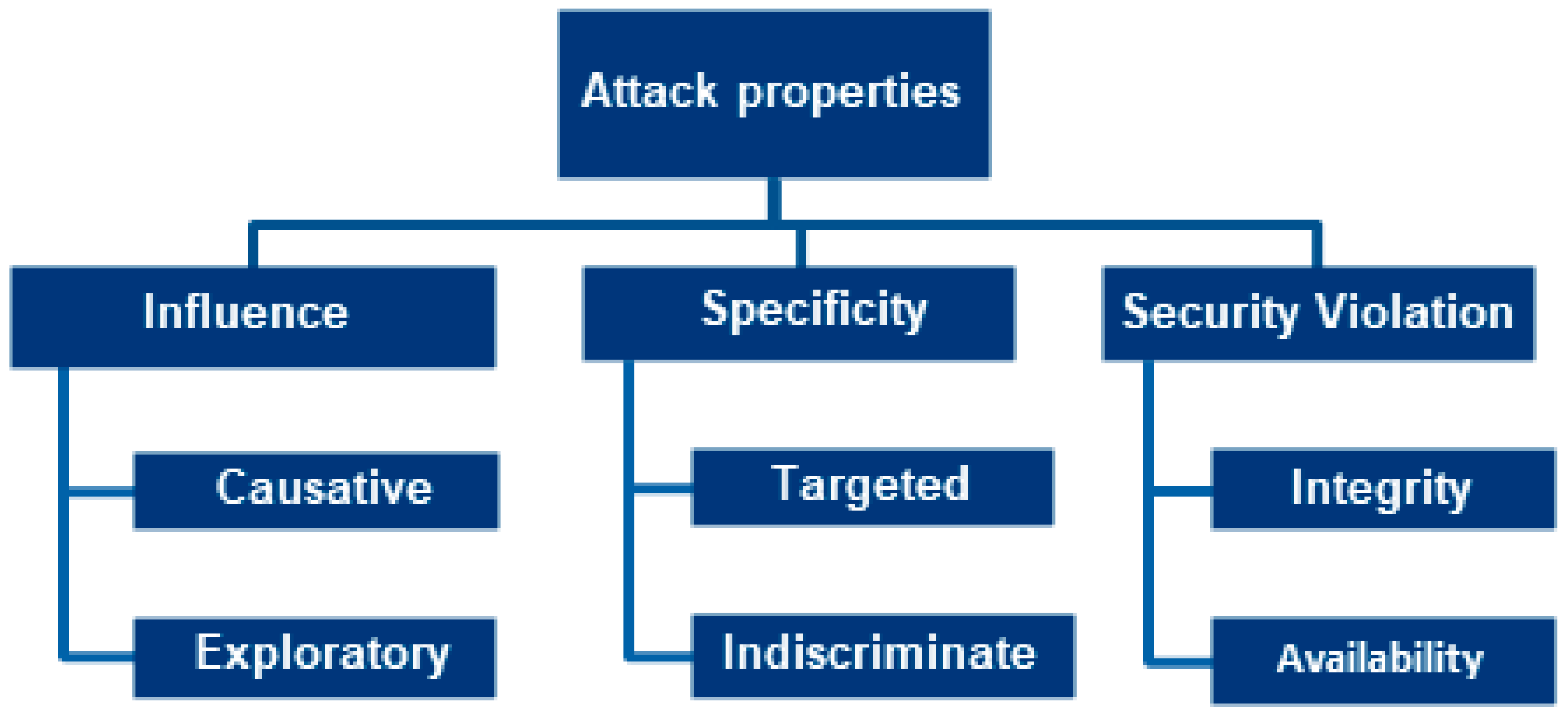
4.1.1. Categorizing of Attack Properties
- Diagnose probable vulnerabilities during training and classification in the machine learning algorithm.
- Model the types of attacks that coincide in order to recognize different threats and to evaluate the impact on the victim.
4.1.2. Attackers’ Category
4.1.3. Attacks on Machine Learning by its Security Property
- Attack scenario: the authors in [157] discussed attacks against a spam Byers in terms of indiscriminate and targeted dictionary attacks. In indiscriminate dictionary attacks, the email contains words, which are liable to show authentic messages. Accordingly, these types of email words are incorporated into information preparation and as a result, the classifiers will classify authentic emails as spam. While in the targeted dictionary attacks, the adversary considers the knowledge of a particular email instead of reading it from the recipient. Hence, the impact is limited because it is word specific. In [158], the authors presented allergy attacks on the autograph worm generation system. This attack is divided into two phases. In the beginning, based on the behavioral patterns during scanning, it distinguishes tainted nodes from the network. In the second phase, it analyses the traffic from tainted nodes and, deduces the blocking rules from the observed behavioral patterns. Thus, the autograph is persuaded by the tainted node, which is contaminated by scanning the network. The tainted node sends forged packets which results in the DoS and blocking non-malicious access from the autograph.
- Attack scenario: in [159], the authors discussed a model of mimicry attack with the use of a gradient descent method over the neural network and SVM classifier. The authors modeled attacks from both sophisticated and strong attackers’ point of view. Feature values will be changed by the attacks prior to the attack point flip labels. This attack is applied to handwritten grayscale images using the SVM classifier and to portable document format (PDF) document using neural network and SVM classifier. The authors used the feature for malicious PDF, which was extracted in [160].
- Attack scenario: in [147], the authors proposed a mechanism for threatening statistical traffic analysis by emulating the class of traffic which mimics another class. This method focuses on the detection system. The packets are modified in real-time which reduces the accuracy of classifiers. Classifiers achieve the accuracy of 98.4% on unmodified data, while it is reduced to just 4.5% after the attack.
4.2. Practical Feasibility of Attacks
4.3. Adversarial Defense Techniques
5. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Lee, Y.S.; Choi, S.S.; Choi, J.; Song, J.S. A Lightweight Malware Classification Method Based on Detection Results of Anti-Virus Software. In Proceedings of the 2017 12th Asia Joint Conference on Information Security (AsiaJCIS), Seoul, Korea, 10–11 August 2017; IEEE: Piscataway, NJ, USA, 2017; pp. 5–9. [Google Scholar]
- ESMA. 2016 Annual Report (IEEE). Available online: https://www.ieee.org/about/annual-report.html (accessed on 4 October 2019).
- Zhang, X.; Tan, Y.A.; Liang, C.; Li, Y.; Li, J. A Covert Channel over VoLTE via Adjusting Silence Periods. IEEE Access 2018, 6, 9292–9302. [Google Scholar] [CrossRef]
- Meng, W.; Tischhauser, E.W.; Wang, Q.; Wang, Y.; Han, J. When Intrusion Detection Meets Blockchain Technology: A Review. IEEE Access 2018, 6, 10179–10188. [Google Scholar] [CrossRef]
- Li, J.; Sun, L.; Yan, Q.; Li, Z.; Srisa-an, W.; Ye, H. Significant permission identification for machine learning based android malware detection. IEEE Trans. Ind. Inform. 2017, 14, 3216–3225. [Google Scholar] [CrossRef]
- Shen, J.; Wang, C.; Li, T.; Chen, X.; Huang, X.; Zhan, Z.H. Secure Data Uploading Scheme for a Smart Home System. Inf. Sci. 2018, 453, 186–197. [Google Scholar] [CrossRef]
- Sun, Z.; Zhang, Q.; Li, Y.; Tan, Y.A. DPPDL: A Dynamic Partial-Parallel Data Layout for Green Video Surveillance Storage. IEEE Trans. Circuits Syst. Video Technol. 2018, 28, 193–205. [Google Scholar] [CrossRef]
- Buczak, A.L.; Guven, E. A Survey of Data Mining and Machine Learning Methods for Cyber Security Intrusion Detection. IEEE Commun. Surv. Tutor. 2016, 18, 1153–1176. [Google Scholar] [CrossRef]
- M.Labs, Malwarebytes. State of Malware Report. p. 11. Available online: https://www.malwarebytes.com/pdf/white-papers/stateofmalware.pdf (accessed on 4 October 2019).
- Balzarotti, D.; Cova, M.; Felmetsger, V.; Jovanovic, N.; Kirda, E.; Kruegel, C.; Vigna, G. Saner: Composing static and dynamic analysis to validate sanitization in web applications. In Proceedings of the 2008 IEEE Symposium on Security and Privacy, Oakland, CA, USA, 18–22 May 2008; IEEE: Piscataway, NJ, USA, 2008; pp. 387–401. [Google Scholar]
- Shar, L.K.; Briand, L.C.; Tan, H.B.K. Web Application Vulnerability Prediction Using Hybrid Program Analysis and Machine Learning. IEEE Trans. Dependable Secur. Comput. 2015, 12, 688–707. [Google Scholar] [CrossRef]
- Rohlf, C.; Ivnitskiy, Y. The security challenges of client-side just-in-time engines. IEEE Secur. Priv. 2012, 10, 84–86. [Google Scholar] [CrossRef]
- Shen, J.; Zou, D.; Jin, H.; Yang, K.; Yuan, B.; Li, W. Security OF Cyberspace A Protective Mechanism for the Access Control System in the Virtual Domain. China Commun. 2016, 13, 129–142. [Google Scholar] [CrossRef]
- Navarro-Arribas, G.; Torra, V. Information fusion in data privacy: A survey. Inf. Fusion 2012, 13, 235–244. [Google Scholar] [CrossRef]
- Yuan, J.; Member, S.; Yu, S. Privacy Preserving Back-Propagation Neural Network Learning Made Practical with Cloud Computing. IEEE Trans. Parallel Distrib. Syst. 2014, 25, 212–221. [Google Scholar] [CrossRef]
- Smith, J.E.; Clark, A.R.; Staggemeier, A.T.; Serpell, M.C. A genetic approach to statistical disclosure control. IEEE Trans. Evol. Comput. 2012, 16, 431–441. [Google Scholar] [CrossRef]
- Matthews, G.J.; Harel, O. Data confidentiality: A review of methods for statistical disclosure limitation and methods for assessing privacy. Stat. Surv. 2011, 5, 1–29. [Google Scholar] [CrossRef]
- Niksefat, S.; Kaghazgaran, P.; Sadeghiyan, B. Privacy issues in intrusion detection systems: A taxonomy, survey and future directions. Comput. Sci. Rev. 2017, 25, 69–78. [Google Scholar] [CrossRef]
- Axelsson, S. The Base-Rate Fallacy and the Difficulty of Intrusion Detection. ACM Trans. Inf. Syst. Secur. 2000, 3, 186–205. [Google Scholar] [CrossRef]
- Shon, T.; Moon, J. A hybrid machine learning approach to network anomaly detection. Inf. Sci. (NY) 2007, 177, 3799–3821. [Google Scholar] [CrossRef]
- Bhoiwala, J.P.; Jhaveri, R.H. Cooperation Based Defense Mechanism against Selfish Nodes in DTNs. ACM Int. Conf. Proc. Ser. 2017. [Google Scholar] [CrossRef]
- Jhaveri, R.H. Secure Routing in Mobile Ad-Hoc Networks: Attacks and Solutions; LAMBERT Academic Publishing: Saarbrücken, Germany, 2017. [Google Scholar]
- Vidal, J.M.; Orozco, A.L.S.; Villalba, L.J.G. Alert correlation framework for malware detection by anomaly-based packet payload analysis. J. Netw. Comput. Appl. 2017, 97, 11–22. [Google Scholar] [CrossRef]
- Cohen, Y.; Hendler, D.; Rubin, A. Detection of malicious webmail attachments based on propagation patterns. Knowl. Based Syst. 2018, 141, 67–79. [Google Scholar] [CrossRef]
- Paxson, V. Bro: A system for detecting network intruders in real-time. Comput. Netw. 1999, 31, 2435–2463. [Google Scholar] [CrossRef]
- Jhaveri, R.H.; Patel, N.M. A sequence number based bait detection scheme to thwart grayhole attack in mobile ad hoc networks. Wirel. Netw. 2015, 21, 2781–2798. [Google Scholar] [CrossRef]
- Jhaveri, R.H.; Patel, N.M. Attack-pattern discovery based enhanced trust model for secure routing in mobile ad-hoc networks. Int. J. Commun. Syst. 2017, 30, e3148. [Google Scholar] [CrossRef]
- Jhaveri, R.H. MR-AODV: A solution to mitigate blackhole and grayhole attacks in AODV based MANETs. In Proceedings of the 2013 Third International Conference on Advanced Computing and Communication Technologies (ACCT), Rohtak, India, 6–7 April 2013; IEEE: Piscataway, NJ, USA, 2013; pp. 254–260. [Google Scholar]
- Jhaveri, R.H. Reliable Approach to Prevent Blackhole and Grayholes Attacks in Mobile ad-hoc Networks; IET Editorial Book; IET: London, UK, 2013; pp. 261–280. [Google Scholar]
- Jhaveri, R.H.; Patel, N.M.; Jinwala, D.C.; Ortiz, J.H.; de la Cruz, A.P. A Composite Trust Model for Secure Routing in Mobile Ad-Hoc Networks; Ortiz, J.H., de la Cruz, A.P., Eds.; IntechOpen: London, UK, 2017; pp. 19–45. [Google Scholar]
- Overill, R.E. How Re (Pro) active Should an IDS be? In Proceedings of the 1st International Workshop on Recent Advances in Intrusion Detection (RAID), Louvain-la-Neuve, Belgium, 14–16 September 1998; pp. 1–6. [Google Scholar]
- Francisco, S.; Martin, D.; Schulman, A. Infranet: Circumventing web censorship and surveillance. In Proceedings of the 11 the USENIX Security Symposium, Berkeley, CA, USA, 5–9 August 2002. [Google Scholar]
- Rhodes, B.C.; Mahaffey, J.A.; Cannady, J.D. Multiple self-organizing maps for intrusion detection. In Proceedings of the 23rd National Information Systems Security Conference, Baltimore, MD, USA, 16–19 October 2000; pp. 16–19. [Google Scholar]
- Yamada, A.; Miyake, Y. Intrusion detection system to detect variant attacks using learning algorithms with automatic generation of training data. In Proceedings of the IEEE Coding and Computing, Las Vegas, NV, USA, 4–6 April 2005; IEEE: Piscataway, NJ, USA, 2005; pp. 1–6. [Google Scholar]
- Lippmann, R.P.; Cunningham, R.K. Improving intrusion detection performance using keyword selection and neural networks. Comput. Netw. 2000, 34, 597–603. [Google Scholar] [CrossRef]
- Wong, W.T.; Hsu, S.H. Application of SVM and ANN for image retrieval. Eur. J. Oper. Res. 2006, 173, 938–950. [Google Scholar] [CrossRef]
- Borges, P.; Sousa, B.; Ferreira, L.; Saghezchi, F.B.; Mantas, G.; Ribeiro, J.; Simoes, P. Towards a Hybrid Intrusion Detection System for Android-based PPDR terminals. In Proceedings of the 2017 IFIP/IEEE Symposium on Integrated Network and Service Management (IM), Lisbon, Portugal, 8–12 May 2017; IEEE: Piscataway, NJ, USA, 2017; pp. 1034–1039. [Google Scholar]
- Karthick, R.R.; Hattiwale, V.P.; Ravindran, B. Adaptive network intrusion detection system using a hybrid approach. In Proceedings of the IEEE Fourth International Conference on Communication Systems and Networks, Bangalore, India, 3–7 January 2012; IEEE: Piscataway, NJ, USA, 2012; pp. 1–7. [Google Scholar]
- Freund, Y.; Schapire, R.E. Experiments with a new boosting algorithm. In Proceedings of the ICML’96 Proceedings of the Thirteenth International Conference on International Conference on Machine Learning, Bari, Italy, 3–6 July 1996; pp. 148–156. [Google Scholar]
- Bauer, E.; Kohavi, R.; Chan, P.; Stolfo, S.; Wolpert, D. An Empirical Comparison of Voting Classification Algorithms: Bagging, Boosting, and Variants. Mach. Learn. 1999, 36, 105–139. [Google Scholar] [CrossRef]
- Breiman, L. Random forests. Mach. Learn. 2001, 45, 5–32. [Google Scholar] [CrossRef]
- Parmanto, B.; Munro, P.W.; Doyle, H.R. Improving committee diagnosis with resampling techniques. Adv. Neural Inf. Process. Syst. 1996, 8, 882–888. [Google Scholar]
- Ma, T.; Wang, F.; Cheng, J.; Yu, Y.; Chen, X. A Hybrid Spectral Clustering and Deep Neural Network Ensemble Algorithm for Intrusion Detection. Sensors (Basel) 2016, 16, 1701. [Google Scholar] [CrossRef]
- Fries, T. A fuzzy-genetic approach to network intrusion detection. In Proceedings of the GECCO’08 10th Annual Conference Companion on Genetic and Evolutionary Computation, Atlanta, GA, USA, 12–16 July 2008; pp. 2141–2146. [Google Scholar]
- Tsai, C.F.; Lin, C.Y. A triangle area based nearest neighbors approach to intrusion detection. Pattern Recognit. 2010, 43, 222–229. [Google Scholar] [CrossRef]
- Van, N.T.; Thinh, T.N.; Sach, L.T. An anomaly-based network intrusion detection system using Deep learning. In Proceedings of the 2017 International Conference on System Science and Engineering (ICSSE), Ho Chi Minh City, Vietnam, 21–23 July 2017; IEEE: Piscataway, NJ, USA, 2017; pp. 210–214. [Google Scholar]
- Viegas, E.K.; Santin, A.O.; Oliveira, L.S. Toward a reliable anomaly-based intrusion detection in real-world environments. Comput. Netw. 2017, 127, 200–216. [Google Scholar] [CrossRef]
- Ghanem, K.; Aparicio-Navarro, F.J.; Kyriakopoulos, K.G.; Lambotharan, S.; Chambers, J.A. Support Vector Machine for Network Intrusion and Cyber-Attack Detection. In Proceedings of the 2017 Sensor Signal Processing for Defence Conference (SSPD), London, UK, 6–7 December 2017; IEEE: Piscataway, NJ, USA, 2017; pp. 1–5. [Google Scholar]
- Al-Yaseen, W.L.; Othman, Z.A.; Nazri, M.Z.A. Hybrid Modified K -Means with C4.5 for Intrusion Detection Systems in Multiagent Systems. Sci. World J. 2015. [Google Scholar] [CrossRef]
- Ross, J.; Morgan, Q.; Publishers, K. Book Review: C4. 5: Programs for Machine Learning. Mach. Learn. 1994, 16, 235. [Google Scholar]
- Abadeh, M.S.; Habibi, J.; Barzegar, Z.; Sergi, M. A parallel genetic local search algorithm for intrusion detection in computer networks. Elsevier Eng. Appl. Artif. Intell. 2007, 20, 1058–1069. [Google Scholar] [CrossRef]
- Giacinto, G.; Perdisci, R.; del Rio, M.; Roli, F. Intrusion detection in computer networks by a modular ensemble of one-class classifiers. Inf. Fusion 2008, 9, 69–82. [Google Scholar] [CrossRef]
- Gajin, V.T.S. Ensemble classifiers for supervised anomaly-based network intrusion detection. In Proceedings of the 2017 13th IEEE International Conference on Intelligent Computer Communication and Processing (ICCP), Cluj-Napoca, Romania, 7–9 September 2017; IEEE: Piscataway, NJ, USA, 2017; pp. 13–19. [Google Scholar]
- Hansen, J.V.; Lowry, P.B.; Meservy, R.D.; McDonald, D.M. Genetic programming for prevention of cyberterrorism through dynamic and evolving intrusion detection. Decis. Support Syst. 2007, 43, 1362–1374. [Google Scholar] [CrossRef]
- Jhaveri, R.H. DoS Attacks in Mobile Ad Hoc Networks: A Survey DoS Attacks in Mobile Ad-hoc Networks: A Survey. In Proceedings of the 2012 Second International Conference on Advanced Computing & Communication Technologies, Rohtak, Haryana, India, 7–8 January 2012; IEEE: Piscataway, NJ, USA, 2012; pp. 535–541. [Google Scholar]
- Prichard, J.J.; Macdonald, L.E. Cyber Terrorism: A Study of the Extent of Coverage in Computer Security Textbooks. J. Inf. Technol. Educ. 2004, 3, 279–289. [Google Scholar]
- Gunawardena, S.H.; Kulkarni, D.; Gnanasekaraiyer, B. A Steganography-based framework to prevent active attacks during user authentication. In Proceedings of the 2013 8th International Conference on Computer Science & Education, Colombo, Sri Lanka, 26-28 April 2013; IEEE: Piscataway, NJ, USA, 2013; pp. 383–388. [Google Scholar]
- Allen, J.; Gomez, L.; Green, M.; Ricciardi, P.; Sanabria, C.; Kim, S. Social Network Security Issues: Social Engineering and Phishing Attacks. In Proceedings of the Student-Faculty Research Day, CSIS, White Plains, NY, USA, 4 May 2012; pp. 1–7. [Google Scholar]
- Applegate, S.D. Social engineering: Hacking the wetware! Inf. Secur. J. 2009, 18, 40–46. [Google Scholar] [CrossRef]
- Khonji, M.; Iraqi, Y.; Jones, A. Phishing detection: A literature survey. IEEE Commun. Surv. Tutor. 2013, 15, 2091–2121. [Google Scholar] [CrossRef]
- Li, Y.; Xiao, R.; Feng, J.; Zhao, L. A semi-supervised learning approach for detection of phishing webpages. Optik 2013, 124, 6027–6033. [Google Scholar] [CrossRef]
- Smadi, S.; Aslam, N.; Zhang, L. Detection of online phishing email using dynamic evolving neural network based on reinforcement learning. Decis. Support Syst. 2018, 107, 88–102. [Google Scholar] [CrossRef]
- Hamid, I.R.A.; Abawajy, J.H. An approach for profiling phishing activities. Comput. Secur. 2014, 45, 27–41. [Google Scholar] [CrossRef]
- Basnet, R. Feature Selection for Improved Phishing Detection. In Proceedings of the International Conference on Industrial, Engineering and Other Applications of Applied Intelligent Systems, Dalian, China, 9–12 June 2012; Springer: Berlin/Heidelberg, Germany, 2012. [Google Scholar]
- Li, Y.; Wang, G.; Nie, L.; Wang, Q.; Tan, W. Distance Metric Optimization Driven Convolutional Neural Network for Age-Invariant Face Recognition. Pattern Recognit. 2018, 75, 51–62. [Google Scholar] [CrossRef]
- Chatterjee, M.; Namin, A.S. Deep Reinforcement Learning for Detecting Malicious Websites. arXiv 2019, arXiv:1905.09207. [Google Scholar]
- Hamid, I.R.A.; Abawajy, J. Hybrid feature selection for phishing email detection. In Proceedings of the International Conference on Algorithms and Architectures for Parallel Processing, Melbourne, Australia, 24–26 October 2011; Springer: Berlin/Heidelberg, Germany, 2011; Volume 7017, pp. 266–275. [Google Scholar]
- Li, T.; Li, J.; Liu, Z.; Li, P.; Jia, C. Differentially private Naive Bayes learning over multiple data sources. Inf. Sci. 2018, 444, 89–104. [Google Scholar] [CrossRef]
- Martin, D.J.; Kifer, D.; Machanavajjhala, A.; Gehrke, J.; Halpern, J.Y. Worst-Case Background Knowledge for Privacy-Preserving Data Publishing. In Proceedings of the 2007 IEEE 23rd International Conference on Data Engineering, Istanbul, Turkey, 15–20 April 2007; IEEE: Piscataway, NJ, USA, 2007; pp. 126–135. [Google Scholar]
- Machanavajjhala, A.; Kifer, D.; Gehrke, J. L-Diversity: Privacy Beyond k-Anonymity. In Proceedings of the 22nd International Conference on Data Engineering (ICDE’06), Atlanta, GA, USA, 3–7 April 2006; IEEE: Piscataway, NJ, USA, 2006; Volume 1. [Google Scholar]
- Li, N. t -Closeness: Privacy Beyond k-Anonymity and –Diversity. In Proceedings of the IEEE 23rd International Conference on Data Engineering, Istanbul, Turkey, 11–15 April 2007; IEEE: Piscataway, NJ, USA, 2007; pp. 106–115. [Google Scholar]
- Sweeney, L. k -ANONYMITY: A Model for Protecting Privacy. Int. J. Uncertain. Fuzziness Knowl. Based Syst. 2002, 10, 1–14. [Google Scholar] [CrossRef]
- Gao, C.Z.; Cheng, Q.; He, P.; Susilo, W.; Li, J. Privacy-preserving Naive Bayes classifiers secure against the substitution-then-comparison attack. Inf. Sci. 2018, 444, 72–88. [Google Scholar] [CrossRef]
- Jia, Q.; Guo, L.; Jin, Z.; Fang, Y. Preserving Model Privacy for Machine Learning in Distributed Systems. IEEE Trans. Parallel Distrib. Syst. 2018, 29, 1808–1822. [Google Scholar] [CrossRef]
- Graepel, T.; Lauter, K.; Naehrig, M. ML confidential: Machine learning on encrypted data. In Proceedings of the International Conference on Information Security and Cryptology, Seoul, Korea, 28–30 November 2012; Springer: Berlin/Heidelberg, Germany, 2013; Volume 7839, pp. 1–21. [Google Scholar]
- Li, P.; Li, J.; Huang, Z.; Li, T.; Gao, C.Z.; Yiu, S.M.; Chen, K. Multi-key privacy-preserving deep learning in cloud computing. Future Gener. Comput. Syst. 2017, 74, 76–85. [Google Scholar] [CrossRef]
- Li, J.; Wang, L.; Wang, L.; Wang, X.; Huang, Z.; Li, J. Verifiable Chebyshev Maps-Based Chaotic Encryption Schemes with Outsourcing Computations in the Cloud/Fog Scenarios. Concurr. Comput. Pract. Exp. 2018, 31, e4523. [Google Scholar] [CrossRef]
- Shen, J.; Gui, Z.; Ji, S.; Shen, J.; Tan, H.; Tang, Y. Cloud-aided Lightweight Certificateless Authentication Protocol with Anonymity for Wireless Body Area Networks. J. Netw. Comput. Appl. 2018, 106, 117–123. [Google Scholar] [CrossRef]
- Cao, Y.; Zhou, Z.; Sun, X.; Gao, C. Coverless Information Hiding Based on the Molecular Structure Images of Material. Comput. Mater. Contin. 2018, 54, 197–207. [Google Scholar]
- Xiang, C.; Tang, C.; Cai, Y.; Xu, Q. Privacy-preserving face recognition with outsourced computation. Soft Comput. 2016, 20, 3735–3744. [Google Scholar] [CrossRef]
- Xu, J.; Wei, L.; Zhang, Y.; Wang, A.; Zhou, F.; Gao, C.H. Dynamic Fully Homomorphic Encryption-based Merkle Tree for Lightweight Streaming Authenticated Data Structures. J. Netw. Comput. Appl. 2018, 107, 113–124. [Google Scholar] [CrossRef]
- Naercio, M.; Borrego, C.; Pereira, P.; Correia, M. PRIVO: A privacy-preserving opportunistic routing protocol for delay tolerant networks. In Proceedings of the 2017 IFIP Networking Conference (IFIP Networking) and Workshops, Stockholm, Sweden, 12–16 June 2017; IEEE: Piscataway, NJ, USA, 2018; pp. 1–9. [Google Scholar]
- Zhang, Q.; Yang, L.T.; Chen, Z. Privacy-Preserving Deep Computation Model on Cloud for Big Data Feature Learning. IEEE Trans. Comput. 2016, 65, 1351–1362. [Google Scholar] [CrossRef]
- Li, P.; Li, T.; Ye, H.; Li, J.; Chen, X.; Xiang, Y. Privacy-preserving machine learning with multiple data providers. Future Gener. Comput. Syst. 2018, 87, 341–350. [Google Scholar] [CrossRef]
- Shokri, R.; Shmatikov, V. Privacy-preserving deep learning. In Proceedings of the 22nd ACM SIGSAC Conference on Computer and Communications Security, Denver, CO, USA, 12–16 October 2015; ACM: New York, NY, USA, 2015; pp. 1310–1321. [Google Scholar]
- Gao, C.Z.; Cheng, Q.; Li, X.; Xia, S.B. Cloud-assisted privacy-preserving profile-matching scheme under multiple keys in the mobile social network. Clust. Comput. 2019, 22, 1655–1663. [Google Scholar] [CrossRef]
- Li, P.; Li, J.; Huang, Z.; Gao, C.Z.; Chen, W.B.; Chen, K. Privacy-preserving outsourced classification in cloud computing. Clust. Comput. 2018, 21, 277–286. [Google Scholar] [CrossRef]
- Zhang, X.; Chen, X.; Wang, J.; Zhan, Z.; Li, J. Verifiable privacy-preserving single-layer perceptron training scheme in cloud computing. Soft Comput. 2018, 22, 7719–7732. [Google Scholar] [CrossRef]
- Vaidya, J.; Shafiq, B.; Basu, A.; Hong, Y. Differentially private naive bayes classification. In Proceedings of the IEEE/WIC/ACM International Joint Conferences on Web Intelligence (WI) and Intelligent Agent Technologies (IAT), Atlanta, GA, USA, 17–20 November 2013; Volume 1, pp. 571–576. [Google Scholar]
- Ye, H.; Liu, J.; Wang, W.; Li, P.; Li, T.; Li, J. Secure and efficient outsourcing differential privacy data release scheme in Cyber-physical system. Future Gener. Comput. Syst. 2018. [Google Scholar] [CrossRef]
- Zhang, T.; Zhu, Q. Dynamic Differential Privacy for ADMM-Based Distributed Classification Learning. IEEE Trans. Inf. Forensics Secur. 2017, 12, 172–187. [Google Scholar] [CrossRef]
- Zhu, H.; Liu, X.; Lu, R.; Li, H. Efficient and Privacy-Preserving Online Medical Prediagnosis Framework Using Nonlinear SVM. IEEE J. Biomed. Heal. Inform. 2017, 21, 838–850. [Google Scholar] [CrossRef] [PubMed]
- Jagannathan, G.; Wright, R.N. Privacy-Preserving Distributed k -Means Clustering over Arbitrarily Partitioned Data. In Proceedings of the Eleventh ACM SIGKDD International Conference on Knowledge Discovery in Data Mining, Chicago, IL, USA, 21–24 August 2005; ACM: New York, NY, USA, 2005; pp. 593–599. [Google Scholar]
- Nazir, A.; Raza, S.; Chuah, C.N. Unveiling facebook: A measurement study of social network-based applications. In Proceedings of the 8th ACM SIGCOMM Conference on Internet Measurement, Vouliagmeni, Greece, 20–22 October 2008; ACM: New York, NY, USA, 2008; pp. 43–56. [Google Scholar]
- Liu, Z.; Wu, Z.; Li, T.; Li, J.; Shen, C. GMM and CNN Hybrid Method for Short Utterance Speaker Recognition. IEEE Trans. Ind. Inform. 2018, 14, 3244–3252. [Google Scholar] [CrossRef]
- Ntoulas, A.; Najork, M.; Manasse, M.; Fetterly, D. Detecting spam web pages through content analysis. In Proceedings of the 15th International Conference on World Wide Web, Edinburgh, Scotland, 23–26 May 2006; ACM: New York, NY, USA, 2006; p. 83. [Google Scholar]
- Zhou, D.; Burges, C.J.C.; Tao, T. Transductive link spam detection. In Proceedings of the Adversarial Information Retrieval on the Web (AIRWeb), Banff, AB, Canada, 8 May 2007; p. 21. [Google Scholar]
- Wang, C.; Shen, J.; Liu, Q.; Ren, Y.; Li, T. A Novel Security Scheme based on Instant Encrypted Transmission for Internet-of-Things. Secur. Commun. Netw. 2018. [Google Scholar] [CrossRef]
- Webb, S.; Caverlee, J.; Pu, C. Predicting Web Spam with HTTP Session Information. In Proceedings of the CIKM’08 17th ACM Conference on Information and Knowledge Management, Napa Valley, CA, USA, 26–30 October 2008; ACM: New York, NY, USA, 2008; pp. 339–348. [Google Scholar]
- Radlinski, F. Addressing malicious noise in clickthrough data. In Proceedings of the Learning to Rank for Information Retrieval Workshop at SIGIR, Ithaca, NY, USA, 2 December 2007. [Google Scholar]
- Sydow, M.; Piskorski, J.; Weiss, D.; Castillo, C. Application of Machine Learning in Combating Web Spam; IOS Press: Amsterdam, The Netherlands, 2007. [Google Scholar]
- Erdélyi, M.; Garzó, A.; Benczúr, A.A. Web Spam Classification: A Few Features Worth More. In Proceedings of the WebQuality’11 2011 Joint WICOW/AIRWeb Workshop on Web Quality, Hyderabad, India, 28 March 2011; ACM: New York, NY, USA, 2011; p. 27. [Google Scholar]
- Chen, C.; Zhang, J.; Xie, Y.; Xiang, Y.; Zhou, W.; Hassan, M.M.; Alrubaian, M. A Performance Evaluation of Machine Learning-Based Streaming Spam Tweets Detection. IEEE Trans. Comput. Soc. Syst. 2016, 2, 65–76. [Google Scholar] [CrossRef]
- Singh, A.; Batra, S. Ensemble based spam detection in social IoT using probabilistic data structures. Future Gener. Comput. Syst. 2018, 81, 359–371. [Google Scholar] [CrossRef]
- Wang, X.; Liu, K.; Zhao, J. Detecting Deceptive Review Spam via Attention-Based Neural Networks. In Proceedings of the National CCF Conference on Natural Language Processing and Chinese Computing, Dunhuang, China, 9–14 October 2019; Springer: Berlin/Heidelberg, Germany, 2018; Volume 1, pp. 866–876. [Google Scholar]
- Shirani-Mehr, H. SMS Spam Detection using Machine Learning Approach. Int. J. Inform. Secur. Sci. 2012, 2, 1–4. [Google Scholar]
- Kolari, P.; Java, A.; Finin, T.; Oates, T.; Joshi, A. Detecting Spam Blogs: A Machine Learning Approach. In Proceedings of the National Conference on Artificial Intelligence, Boston, MA, USA, 16–20 July 2006; AAAI Press: Cambridge, MA, USA, 2006; Volume 6, pp. 1351–1356. [Google Scholar]
- Huang, Z.; Liu, S.; Mao, X.; Chen, K.; Li, J. Insight of the protection for data security under selective opening attacks R. Inf. Sci. (NY) 2017, 412–413, 223–241. [Google Scholar] [CrossRef]
- Munteanu, A.; Fotache, D.; Dospinescu, O. Information Systems Security Risk Assessment: Harmonization with International Accounting Standards. In Proceedings of the 2008 International Conference on Computational Intelligence for Modelling Control & Automation, Vienna, Austria, 10–12 December 2008; IEEE: Piscataway, NJ, USA, 2009; pp. 1111–1117. [Google Scholar]
- Asosheh, A.; Dehmoubed, B.; Khani, A. A new quantitative approach for information security risk assessment. In Proceedings of the 2nd IEEE International Conference on Computer Science and Information Technology, Dallas, TX, USA, 8–11 June 2009; IEEE: Piscataway, NJ, USA, 2009; pp. 222–227. [Google Scholar]
- Guan, B.-C.; Lo, C.-C.; Wang, P.; Hwang, J.-S. Evaluation of information security related risks of an organization—The application of the multi-criteria decision-making method. In Proceedings of the IEEE 37th Annual 2003 International Carnahan Conference on Security Technology, Taipei, Taiwan, 14–16 October 2003; IEEE: Piscataway, NJ, USA; 2003; pp. 168–175. [Google Scholar]
- Munir, R.; Mufti, M.R.; Awan, I.; Hu, Y.F.; Disso, J.P. Detection, mitigation and quantitative security risk assessment of invisible attacks at enterprise network. In Proceedings of the 2015 3rd International Conference on Future Internet of Things and Cloud, Rome, Italy, 24–26 August 2015; IEEE: Piscataway, NJ, USA, 2015; pp. 256–263. [Google Scholar]
- Saripalli, P.; Walters, B. QUIRC: A Quantitative Impact and Risk Assessment Framework for Cloud Security. In Proceedings of the 2010 IEEE 3rd International Conference on Cloud Computing, Miami, FL, USA, 5–10 July 2010; IEEE: Piscataway, NJ, USA, 2010; pp. 280–288. [Google Scholar]
- Ralston, P.A.S.; Graham, J.H.; Hieb, J.L. Cyber security risk assessment for SCADA and DCS networks. ISA Trans. 2007, 46, 583–594. [Google Scholar] [CrossRef]
- de Barros Correia, R.; Pirmez, L.; da Costa Carmo, L.F.R. Evaluating security risks following a compliance perspective. In Proceedings of the 2008 11th IEEE High Assurance Systems Engineering Symposium, Nanjing, China, 3–5 December 2008; IEEE: Piscataway, NJ, USA, 2008; pp. 27–36. [Google Scholar]
- Liu, Y.; Ling, J.; Liu, Z.; Shen, J.; Gao, C. Finger Vein Secure Biometric Template Generation Based on Deep Learning. Soft Comput. 2018, 22, 2257–2265. [Google Scholar] [CrossRef]
- Wang, J.; Chaudhury, A.; Rao, H.R. A value-at-risk approach to information security investment. Inf. Syst. Res. 2008, 19, 106–120. [Google Scholar] [CrossRef]
- Wallace, L.; Keil, M.; Rai, A. Understanding software project risk: A cluster analysis. Inf. Manag. 2004, 42, 115–125. [Google Scholar] [CrossRef]
- Eminagaoglu, M. A Qualitative Information Security Risk Assessment Model using Machine Learning Techniques. In Proceedings of the ICT2012 Second International Conference on Advances in Information Technologies and Communication, Amsterdam, The Netherlands, 27–29 June 2018. [Google Scholar]
- Jing, Y.; Ahn, G.-J.; Zhao, Z.; Hu, H. RiskMon: Continuous and Automated Risk Assessment of Mobile Applications. In Proceedings of the 4th ACM Conference on Data and Application Security and Privacy, San Antonio, TX, USA, 3–5 March 2014; ACM: New York, NY, USA, 2014; pp. 99–110. [Google Scholar]
- Guntamukkala, N.; Dara, R.; Grewal, G. A Machine-Learning Based Approach for Measuring the Completeness of Online Privacy Policies. In Proceedings of the 2015 IEEE 14th International Conference on Machine Learning and Applications (ICMLA), Miami, FL, USA, 9–11 December 2015; IEEE: Piscataway, NJ, USA, 2016; pp. 289–294. [Google Scholar]
- Wei, Q.; De-Zheng, Z. Security Metrics Models and Application with SVM in Information Security Management. In Proceedings of the 2007 International Conference on Machine Learning and Cybernetics, Hong Kong, China, 19–22 August 2007; IEEE: Piscataway, NJ, USA, 2007; Volume 6, pp. 3234–3238. [Google Scholar]
- Marwan, M.; Kartit, A.; Ouahmane, H. ScienceDirect Security Enhancement in Healthcare Cloud using Machine Learning. Procedia Comput. Sci. 2018, 127, 388–397. [Google Scholar] [CrossRef]
- Christodorescu, M.; Jha, S.; Seshia, S.A.; Song, D.; Bryant, R.E. Semantics-Aware Malware Detection. In Proceedings of the 2005 IEEE Symposium on Security and Privacy (S&P’05), Oakland, CA, USA, 8–11 May 2005; IEEE: Piscataway, NJ, USA, 2005; pp. 32–46. [Google Scholar]
- Alam, S.; Traore, I.; Sogukpinar, I. Annotated Control Flow Graph for Metamorphic Malware Detection. Comput. J. 2014, 58, 2608–2621. [Google Scholar] [CrossRef]
- Sulaiman, A.; Ramamoorthy, K.; Mukkamala, S.; Sung, A.H. Malware Examiner using Disassembled Code (MEDiC). In Proceedings of the Sixth Annual IEEE SMC Information Assurance Workshop, West Point, NY, USA, 15–17 June 2005; IEEE: Piscataway, NJ, USA, 2005; Volume 2005, pp. 428–429. [Google Scholar]
- Sung, A.H.; Xu, J.; Chavez, P.; Mukkamala, S. Static Analyzer of Vicious Executables (SAVE). In Proceedings of the 20th Annual Computer Security Applications Conference, Tucson, AZ, USA, 6–10 December 2004; IEEE: Piscataway, NJ, USA, 2004; pp. 326–334. [Google Scholar]
- Kreibich, C.; Crowcroft, J. Honeycomb—Creating Intrusion Detection Signatures Using Honeypots. ACM SIGCOMM Comput. Commun. Rev. 2004, 34, 51–56. [Google Scholar] [CrossRef]
- Li, W.J.; Wang, K.; Stolfo, S.J.; Herzog, B. Fileprints: Identifying file types by n-gram analysis. In Proceedings of the Sixth Annual IEEE SMC Information Assurance Workshop, West Point, NY, USA, 15–17 June 2005; IEEE: Piscataway, NJ, USA, 2005; Volume 2005, pp. 64–71. [Google Scholar]
- Choudhary, S.P.; Vidyarthi, M.D. A Simple Method for Detection of Metamorphic Malware using Dynamic Analysis and Text Mining. Procedia Comput. Sci. 2015, 54, 265–270. [Google Scholar] [CrossRef]
- Patcha, A.; Park, J.M. An overview of anomaly detection techniques: Existing solutions and latest technological trends. Comput. Netw. 2007, 51, 3448–3470. [Google Scholar] [CrossRef]
- Gorji, A.; Abadi, M. Detecting Obfuscated JavaScript Malware Using Sequences of Internal Function Calls. In Proceedings of the 2014 ACM Southeast Regional Conference, Kennesaw, GA, USA, 28–29 March 2014; ACM: New York, NY, USA, 2014; p. 64. [Google Scholar]
- Bayer, U.; Comparetti, P.M.; Hlauschek, C.; Kruegel, C.; Kirda, E. Scalable, Behavior-Based Malware Clustering. In Proceedings of the Network and Distributed System Security Symposium, San Diego, CA, USA, 8–11 February 2009; Volume 272, pp. 51–88. [Google Scholar]
- Jhaveri, R.H.; Patel, N.; Zhong, Y.; Sangaiah, A. Sensitivity Analysis of an Attack-Pattern Discovery Based Trusted Routing Scheme for Mobile Ad-Hoc Networks in Industrial IoT. IEEE Access 2018, 6, 20085–20103. [Google Scholar] [CrossRef]
- Das, S.; Liu, Y.; Zhang, W.; Chandramohan, M. Semantics-based online malware detection: Towards efficient real-time protection against malware. IEEE Trans. Inf. Forensics Secur. 2016, 11, 289–302. [Google Scholar] [CrossRef]
- Arp, D.; Spreitzenbarth, M.; Hübner, M.; Gascon, H.; Rieck, K. Drebin: Effective and Explainable Detection of Android Malware in Your Pocket. In Proceedings of the Network and Distributed System Security Symposium (NDSS), San Diego, CA, USA, 23–26 February 2014. [Google Scholar]
- Gavrilut, D.; Cimpoesu, M.; Anton, D.; Ciortuz, L. Malware detection using machine learning. In Proceedings of the 2009 International Multiconference on Computer Science and Information Technology, Mragowo, Poland, 12–14 October 2009; IEEE: Piscataway, NJ, USA, 2009; pp. 735–741. [Google Scholar]
- Xu, Z.; Ray, S.; Subramanyan, P.; Malik, S. Malware detection using machine learning based analysis of virtual memory access patterns. In Proceedings of the Conference on Design, Automation & Test in Europe, Lausanne, Switzerland, 27–31 March 2017; European Design and Automation Association: Leuven, Belgium, 2017; pp. 169–174. [Google Scholar]
- Rieck, K.; Holz, T.; Willems, C. Learning and Classification of Malware Behavior. In Proceedings of the International Conference on Detection of Intrusions and Malware, and Vulnerability Assessment, Paris, France, 10–11 July 2008; Springer: Berlin/Heidelberg, Germany, 2008; pp. 108–125. [Google Scholar]
- Patel, N.J.; Jhaveri, R.H. Detecting packet dropping nodes using machine learning techniques in Mobile ad-hoc network: A survey. In Proceedings of the 2015 International Conference on Signal Processing and Communication Engineering Systems, Guntur, India, 2–3 January 2015; IEEE: Piscataway, NJ, USA, 2015; pp. 468–472. [Google Scholar]
- Thompson, H.H. Why security testing is hard. IEEE Secur. Priv. 2003, 1, 83–86. [Google Scholar] [CrossRef]
- Mitchell, J.C.; Mitchell, M.; Stern, U. Automated Analysis of Cryptographic Protocols Using Murcp. In Proceedings of the 1997 IEEE Symposium on Security and Privacy, Oakland, CA, USA, 4–7 May 1997; IEEE: Piscataway, NJ, USA, 1997; pp. 141–151. [Google Scholar]
- Vardhan, A.; Sen, K.; Viswanathan, M.; Agha, G. Learning to verify safety properties. In Proceedings of the International Conference on Formal Engineering Methods, Seattle, WA, USA, 8–12 November 2004; Springer: Berlin/Heidelberg, Germany, 2004; pp. 274–289. [Google Scholar]
- Dupont, P. Incremental regular inference. In Proceedings of the International Colloquium on Grammatical Inference, Tokyo, Japan, 20–22 September 2006; Springer: Berlin/Heidelberg, Germany, 1996; Volume 1147, pp. 222–237. [Google Scholar]
- Shu, G.; Lee, D. Testing security properties of protocol implementations—A machine learning based approach. In Proceedings of the 27th International Conference on Distributed Computing Systems, Toronto, ON, Canada, 25–27 June 2007; IEEE: Piscataway, NJ, USA, 2007. [Google Scholar]
- Shu, G.; Hsu, Y.; Lee, D. Detecting Communication Protocol Security Flaws by Formal Fuzz Testing and Machine Learning. In Proceedings of the International Conference on Formal Techniques for Networked and Distributed Systems, Tokyo, Japan, 10–13 June 2008; Springer: Berlin/Heidelberg, Germany, 2008; pp. 299–304. [Google Scholar]
- Ghaffarian, S.M.; Shahriari, H.R. Software Vulnerability Analysis and Discovery Using Machine-Learning and Data-Mining Techniques. ACM Comput. Surv. 2017, 50, 56. [Google Scholar] [CrossRef]
- Sánchez-Carmona, A.; Robles, S.; Borrego, C. PrivHab+: A secure geographic routing protocol for DTN. Comput. Commun. 2016, 78, 56–73. [Google Scholar] [CrossRef]
- Carlos, B.; Amadeo, M.; Molinaro, A.; Jhaveri, R.H. Privacy-Preserving Forwarding using Homomorphic Encryption for Information-Centric Wireless Ad Hoc Networks. IEEE Commun. Lett. 2019, 23, 1708–1711. [Google Scholar]
- Lin, Q.; Yan, H.; Huang, Z.; Chen, W.; Shen, J.; Tang, Y. An ID-based linearly homomorphic signature scheme and its application in the blockchain. IEEE Access 2018, 6, 20632–20640. [Google Scholar] [CrossRef]
- Lin, Q.; Li, J.; Huang, Z.; Chen, W.; Shen, J. A short linearly homomorphic proxy signature scheme. IEEE Access 2018, 6, 12966–12972. [Google Scholar] [CrossRef]
- Roli, F.; Biggio, B.; Fumera, G. Pattern Recognition Systems under Attack. In Proceedings of the Iberoamerican Congress on Pattern Recognition, Havana, Cuba, 28–31 October 2019; Springer: Berlin/Heidelberg, Germany, 2013; Volume 3287, pp. 350–357. [Google Scholar]
- Šrndić, N.; Laskov, P. Practical evasion of a learning-based classifier: A case study. In Proceedings of the 2014 IEEE Symposium on Security and Privacy, San Jose, CA, USA, 18–21 May 2014; IEEE: Piscataway, NJ, USA, 2014; pp. 197–211. [Google Scholar]
- Biggio, B.; Bul, S.R.; Pillai, I.; Mura, M. Poisoning Complete-Linkage Hierarchical Clustering. In Proceedings of the Joint IAPR International Workshops on Statistical Techniques in Pattern Recognition (SPR) and Structural and Syntactic Pattern Recognition (SSPR), Joensuu, Finland, 20–22 August 2014; Springer: Berlin/Heidelberg, Germany, 2014; pp. 42–52. [Google Scholar]
- Tygar, J.D. Adversarial machine learning. IEEE Internet Comput. 2011, 15, 4–6. [Google Scholar] [CrossRef]
- Xiaoa, F.R.H.; Biggiob, B.; Nelsonb, B.; Xiaoa, H.; Eckerta, C.; Department, A. Support Vector Machines Under Adversarial Label Contamination. Neurocomputing 2015, 160, 53–62. [Google Scholar] [CrossRef]
- Barreno, M.; Bartlett, P.L.; Chi, F.J.; Joseph, A.D.; Nelson, B.; Rubinstein, B.I.; Tygar, J.D. Open problems in the security of learning. In Proceedings of the 1st ACM workshop on Workshop on AISec, Alexandria, VA, USA, 27 October 2008; ACM: New York, NY, USA, 2008; p. 19. [Google Scholar]
- Chung, S.P.; Mok, A.K. Allergy Attack Against Automatic Signature Generation. In Proceedings of the International Workshop on Recent Advances in Intrusion Detection, Hamburg, Germany, 20–22 September 2006; Springer: Berlin/Heidelberg, Germany, 2006; pp. 61–80. [Google Scholar]
- Biggio, B.; Corona, I.; Maiorca, D.; Nelson, B.; Šrndić, N.; Laskov, P.; Roli, F. Evasion Attacks against Machine Learning at Test Time. In Proceedings of the Joint European Conference on Machine Learning and Knowledge Discovery in Databases, Prague, Czech Republic, 23–27 September 2013; Springer: Berlin/Heidelberg, Germany, 2013; Volume 8190, pp. 387–402. [Google Scholar]
- Maiorca, D.; Giacinto, G.; Corona, I. A Pattern Recognition System for Malicious PDF Files Detection Davide. In Proceedings of the International Workshop on Machine Learning and Data Mining in Pattern Recognition, Berlin, Germany, 13–20 July 2012; Springer: Berlin/Heidelberg, Germany, 2012; pp. 510–524. [Google Scholar]
- Goodfellow, J.I.; Shlens, J.; Szegedy, C. Explaining and harnessing adversarial examples. arXiv 2015, arXiv:1412.6572. [Google Scholar]
- Porter, F.A.; Chin, E.; Hanna, S.; Song, D.; Wagner, D. Android permissions demystified. In Proceedings of the 18th ACM Conference on Computer and Communications Security, Chicago, IL, USA, 17–21 October 2011; ACM: New York, NY, USA, 2011; pp. 627–638. [Google Scholar]
- Huang, X.; Biggio, B.; Brown, G.; Fumera, G.; Eckert, C.; Roli, F. Is feature selection secure against training data poisoning? In Proceedings of the International Conference on Machine Learning, Lille, France, 6–11 July 2015; pp. 1689–1698. [Google Scholar]
- Sen, C.; Xue, M.; Fan, L.; Hao, S.; Xu, L.; Zhu, H.; Li, B. Automated poisoning attacks and defenses in malware detection systems: An adversarial machine learning approach. Comput. Secur. 2018, 73, 326–344. [Google Scholar]
- Nelson, B.; Barreno, M.; Chi, F.J.; Joseph, A.D.; Rubinstein, B.I.; Saini, U.; Xia, K. Misleading learners: Co-opting your spam filter. In Machine Learning in Cyber Trust; Springer: Boston, MA, USA, 2009; pp. 17–51. [Google Scholar]
- Florian, T.; Kurakin, A.; Papernot, N.; Goodfellow, I.; Boneh, D.; McDaniel, P. Ensemble adversarial training: Attacks and defenses. arXiv 2017, arXiv:1705.07204. [Google Scholar]
- Martin, A.; Chu, A.; Goodfellow, I.; McMahan, H.B.; Mironov, I.; Talwar, K.; Zhang, L. Deep learning with differential privacy. In Proceedings of the 2016 ACM SIGSAC Conference on Computer and Communications Security, Vienna, Austria, 24–28 October 2016; ACM: New York, NY, USA, 2016; pp. 308–318. [Google Scholar]
- Yao, Y.; Ling, S.; Chi, E. Investigation on distributed k-means clustering algorithm of homomorphic encryption. Comput. Technol. Dev. 2017, 27, 81–85. [Google Scholar]
- Metzen, J.H.; Genewein, T.; Fischer, V.; Bischoff, B. On detecting adversarial perturbations. arXiv 2017, arXiv:1702.04267. [Google Scholar]
- Kathrin, G.; Papernot, N.; Manoharan, P.; Backes, M.; McDaniel, P. Adversarial perturbations against deep neural networks for malware classification. arXiv 2016, arXiv:1606.04435. [Google Scholar]

| Search Engine | Query |
|---|---|
| IEEE Xplore | (machine learning AND applications AND security) OR (Adversarial Attacks AND machine learning) 1 |
| Springer | (machine learning AND applications AND security) OR (security properties OR defense AND machine learning) OR (adversarial attacks AND machine learning) 2 |
| Web of Science | (machine learning AND application AND security) OR (security properties OR defense AND machine learning) OR (adversarial attacks AND machine learning) 2 |
| Science Direct | (machine learning AND application AND security) OR (security properties OR defense AND machine learning) OR (adversarial attacks AND machine learning) 2 |
| Variable | Explanation |
|---|---|
| Study | |
| Year | Publication year |
| Type of Study | Rationale regarding outcome analysis |
| Problems | Rationale of problem identification, address, and solution |
| Security applications | |
| Methodology | Types of machine learning algorithms used in the approach |
| Type of classifier | Which type of classifiers are adopted for simulation |
| Performance metrics | Types of performance metrics and accuracy achieved |
| Data acquisition | Type of datasets are used in training and testing |
| Application approach | wether security applications anomaly, misuse or hybrid detections based approach used |
| Adversarial analysis | |
| Security properties | Type of security property consists of the existing approach |
| Defense approach | Which type of defense approach |
| Reference | [34] | [35] | [36] | [37] | [38] | [43] | [44] | [45] |
|---|---|---|---|---|---|---|---|---|
| Type Of Algorithm | Decision tree algorithm | Neural network | Artificial Neural network, SVM | k-means clusturing + semi-supervised Algorithm | Hidden Markow Model + Naïve Biase | Spectral clustering + Deep Neural Network, SVM, Random Forest, Back Propagation Neural Network | Genetic Algorithm | TANN, SVM, k-means + k-NN |
| Advantage | No data preparation required | Ability to detect a new type of attack with less computation | Frequency-base encoding is more effective for intrusion detection | Low impact on mobile in terms of battery consumption, CPU/memory usage | Highly Accurate | Accuracy is high for attack detection, error rate is low for all tested data sets, able to classify sparse attacks | Adopts changes in environment, robust against noise and detects unknown types of attacks | Accuracy rate and detection rate is high for single class |
| Limitation and challenge | False positives found for known attacks in defense advance research project agency | Stealthy attack which hides the keywords requires additional action | Improper parameter selection cause overfitting in ANN | Selective policy implemented for monitoring suspicious events | HMM requires more than 5 states to maintain high accuracy | Requires to optimize weight parameter and threshold for each DNN layer | Compared to rule optimization method false positive rate is high | Low accuracy for more than one class |
| Performance Metrics | True positives, false positives, false negatives, true negatives | False alarms Detection Rate—80% | Attack detection Rate—95.9%, false positive rate | CPU usage, RAM usage, battery usage, sent/Received packets | Accuracy—100%, false alarm rate | Accuracy—91.97%, recall—92.23%, error rate—7.9% | False positives and intrusion detection rate—99.6% | Accuracy—96.91%, false positive rate, detFalse positives and intrusion detection rate—99.6% ection rate—98.95% |
| Classifier type | Single | Single | Single | Hybrid | Hybrid | Ensemble | Single | Hybrid |
| Reference | [46] | [47] | [48] | [49] | [51] | [52] | [53] |
|---|---|---|---|---|---|---|---|
| Type of Algorithm/Technique | Deep learning | Decision tree, naïve Bayes | Support vector machine | Hybrid modified k-means + C 4.5, Bayes net, Naïve Bayes, LibSVM, JRip, sequential minimal optimization, k Instance base | Genetic local search algorithm | Parzen density estimation, k-means, v-SVC (Support vector classifier) | Bagged tree, ada boost, RUS boost, logit boost, gentle boost |
| Advantage | Accuracy of intrusion detection and attack classification is high | Considered real-world network properties to increase accuracy | Datasets comprise with non-homogeneous features, shows high accuracy | Construct clusters with all cases characterized by significant differences among the instance which leads to higher accuracy | Needs less training time, high detection rate, low false alarm rate | v-SVC algorithm performs better than its competitors, high detection rate, low false alarm rate, accurately models the traffic of each service | Provides comparative study of ensemble ML methods for imbalance datasets |
| Limitation and challenge | Training for stack auto-encoder is time-consuming | False-positive rate increases while detecting new types of attacks | IDS accuracy decreases when analyzing the probing datasets | Precision is less compared to other methods like naïve Bayes, J48 NB tree | Discovered trade-off between false alarm and detection rate with the value of local search procedure | False alarm rate is increased when the detection rate is increased for the approach | Needs to require designing ML algorithm variations with all relevant security issues |
| Performance Metrics | Accuracy—99.98%, error rate—0.02% | False positives, false negatives, accuracy—97.42% | False-negative rate—0%, detection rate—100%, false positive rate—0%, overall success rate—100% | Accuracy—91.13%, detection rate—85.26%, false alarm rate—2.99%, precision—96.65%, specificity—97.01%, F-measure—90.56% | Detection rate—92.4%, classification rate—93%, false alarm rate—0.15% | Detection rate—94.31%, false alarm rate—9.49% | Sensitivity, specificity, precision—99.3%, |
| Type of classifier | Single | Single | Single | Hybrid | Hybrid | Ensemble | Ensemble |
| References | [63] | [64] | [65] | [66] | [67] |
|---|---|---|---|---|---|
| No. of Feature Sets | 20 | 177 | 5 | 50 | 7 |
| Feature Selection Method | Information gain | CFS, WFS | Segmentation | URL segmetation | Hybrid |
| Type of Algorithm/Technique | AdaBoost, sequential minimization, optimization | Naïve Bayes, logistic regression, random forest | Support vector machine, transductive SVM (TSVM) | Neural network, reinforcement learning | Bayesian Network algorithm |
| Advantage | Low false positive and false negative rates, overfitting issues, solve as produced a less error rate | Using greedy forward search technique of selected feature sets yield higher accuracy and improved training time | Higher accuracy and higher precision compare to SVM | Able to recognize zero-day phishing attack | Able to achieve high accuracy for fusion of content-based and behavior-based approach |
| Limitation and challenge | Accuracy could be improved by integrating k-means and two-step clustering approach | Slower technique, degradation of classification accuracy for a new type of datasets | Less flexible in terms of learning | Does not mitigate various privacy concern and malicious bots | As feature selection is content-based, image content attack can bypass this approach |
| Performance Metrics | Error rate—18%, false positives, false negatives, accuracy—98.4% | Error rate—1.6%, false positive rate—1%, false negative rate—2.7% | Accuracy—91.1%, precision, recall | Precision—86.7%, recall—88%, accuracy—90%, F-measure—87.3% | False negatives—4.2%, false positives—4.1%, precision—96%, recall—96%, error—4%, accuracy—96% |
| Types of ML Classifiers | Ensemble | Hybrid | Single | Hybrid | Hybrid |
| Time for Classifying Test Vector | Classifier Computing Time in the Training Stage | Time for Data Encryption in the Training Stage | |
|---|---|---|---|
| LM classifier (encrypted data) | Constant with number of training vector increases | Grows linearly | Grows linearly |
| Fisher’s Linear Discriminant classifier (encrypted data) | Constant with number of training vector increases | Grows quadratically | Grows linearly |
| Reference | [74] | [75] | [76] | [82] | [91] | [92] | [93] |
|---|---|---|---|---|---|---|---|
| Application/Domain | Distributed system | Cryptography | Cloud Computing | Cloud and big data | Network | Healthcare | Data mining |
| Type of Algorithm | Support vector machine | Linear means classifier, Fisher’s Linear discriminant classifier | Deep learning | Deep learning | Altering the direction method of multipliers | Nonlinear Support vector machine | K-means Clustering |
| Advantage | Preserves privacy of data classification and similarity evaluation | Retain confidentiality of training and test data | Preserves privacy of data and training model | Efficiently deals with big data | Enables distributed training over network collaborative nodes and guarantees preservation of privacy at each update | Sensitive health information not disclosed during online prediagnosis services | Provides privacy preserving over horizontally, vertically and arbitrarily partitioned data |
| Limitation and challenge | increasing data, dimensions require more polynomials leads to high computational cost | Multiple data owners’ data cannot be handled using a single ML method without disclosing data | FHE scheme is practically not implemented | Gets excessive overhead to accomplish encryption/decryption and leads to deploying more cloud servers | Practical results of PVP and DVP are not as per a theoretical analysis | No of support vectors are fixed up to 60 in real environment experiments and overhead found for the computation | Intermediate cluster assignment potentially leak information |
| Performance Metrics | Classification accuracy- 97.21%, computational cost, data similarity | Accuracy, training time | Not Applicable | Training time, classification accuracy- 87.2% | Empirical loss, misclassification error rate, privacy-accuracy trade-off | Accuracy- 94%, computational complexity | Computational complexity |
| Sanitization methods as supplement to ML algorithm | OMPE | Homomorphic encryption scheme | Multi-key fully homomorphic encryption | BGV homomorphic encryption scheme | Dual variable perturbation, Primal variable perturbation | Polynomial aggregation techniques, light-weight multi-party random masking | Random shares, secure scalar product protocol, Yaos circuit evaluation protocol |
| Reference | [103] | [104] | [105] | [106] | [107] |
|---|---|---|---|---|---|
| Type of ML Algorithm | Random Forest C4.5, Naïve Bayes, KNN Bayes Network, SVM | KNN, Naïve Bias, Logistic Regression | Neural Network | Multinomial Naïve Bayes, SVM, KNN, Random Forest Adaboost with a decision tree | SVM |
| Advantage | Enables real-time spam detection | Framework collects timely updates in an effective and adaptive manner | Detect deceptive review spam by linguistic and behavioral features | Reduces the overall error rate | Classifiers can be easily retrained as characters and tactics of sploggers changes |
| Limitation | Require continuous training and updating the data sets in order to maintain detection accuracy | As the framework is tested for tweeter only, other social media platform results may differ as features change | Proposed approach is compared with off-the-shelf classification algorithms | Due to the lack of real database of SMS a chance of under performance during the classification | Continuous updating of the feature sets is required |
| Performance Metrics | Precision, recall, F-measure—93.6% | Precision—94%, recall—87.66%, F score—88.11% | Precision—88.9%, recall—91.3%, F values—90.1% | Spams caught—94.47%, blocked ham, accuracy—98.88% | Threshold probability, accuracy—95% |
| Medium of Spam | Tweeter | Tweeter | Linguistic phrases | SMS | Blogs |
| Reference | [119] | [120] | [121] | [122] | [123] |
|---|---|---|---|---|---|
| Type of ML Algorithm | Random Forest, J48, K-Nearest Neighbor | SVM | Linear SVM, K-Nearest Neighbor, Random Forest | SVM | SVM, Fuzzy c-means clustering |
| Scheme Importance | Quantifiable risk assessed in a robust and reliable way | Automatically measure the risk induced by the user | Automated techniques to enumerate the integrity of the privacy policy and notifying the users about the important sections | Leads towards effective assistance and assessment to improve controlling information risk | Secure environment in cloud without revealing sensitive data |
| Limitation | Fuzzification, statistical, the numerical method can improve the performance | Doesn’t address third-party applications, unauthorized access possible | Low degree of transparency may generate ambiguous results | Approach is designed for a single organization | Pixel texture feature can be added to enhance image segmentation |
| Performance Metrics | Accuracy—100% | Risk score | Accuracy—75% | Classifier Margin | Accuracy |
| Type of Risk | Qualitative Risk | Qualitative Risk | Quantitative Risk | Quantitative Risk | Qualitative Risk |
| Types of risk Identification | Security risk of the institution | Android mobile app risk | Privacy Policy Risk | Information risk | Disclosure of medical information |
| Reference | [135] | [136] | [137] | [138] | [139] |
|---|---|---|---|---|---|
| Type of ML Algorithm | J48, naïve bayes, SVM, LR, SMO, MLP | Linear SVM | Cascade one-sided perceptron, Cascade kernelized one-sided perceptron | Random Forest, Logistic Regression, SVM | SVM |
| Advantage | Able to get the high-level semantics of the malware | Able to protect user to install the application from an untrusted source | Non-stochastic version of algorithm enables parallelized training process to increase the speed | High detection accuracy against the kernel level rootkits and user level memory corruption report | Able to identify unknown families and behavior which are not present in the learning corpus |
| Limitation | Unable to detect kernel rootkits | When new code is loaded dynamic triggering is not possible | Accuracy is less when scaling up with the large datasets | For entire programme, Epochhistogram size should be chosen carefully which requires human effort | Relies on single program execution of malware binary |
| Performance Metrics | False positive rate, false negative rate, Accuracy- 99.7% | False detection, missing detection, accuracy- 93% | Sensitivity measure value, specificity measure value, accuracy measure value- 88.84%, True positives, false positives | False positives, true positives | Accuracy- 88%, confusion matrix |
| Type(s) of Malware detected | Backdoors, exploits, user-level rootkits, exploit, flooder, hack tools, net-Worm, Trojan, virus | Fake installer, DroidKungfu, Palnkton, opfake, GingerMaster, BaseBridge, Iconosys, Knim, FakeDoc, Geinimi, Adrd, DroidDream, LinuxLottor, GoldDream, MobileTx, FakeRun, Sendpay, Gappusin, Imlog, SMSreg | Backdoor, hack Tool, rootkit, Trojan, worms | Root kits | Worm, backdoors, trojans |
| Type of features employed to the classifiers for detection | Memory, network, file system, process- related system calls | Suspicious API calls, requests permissions, application components, filtered intents, network addresses, hardware features, used permission, restricted API calls | Binary type feature set | Architectural events, memory address, instruction mix | Frequency of contained string, string features (name & list of key-value pairs) |
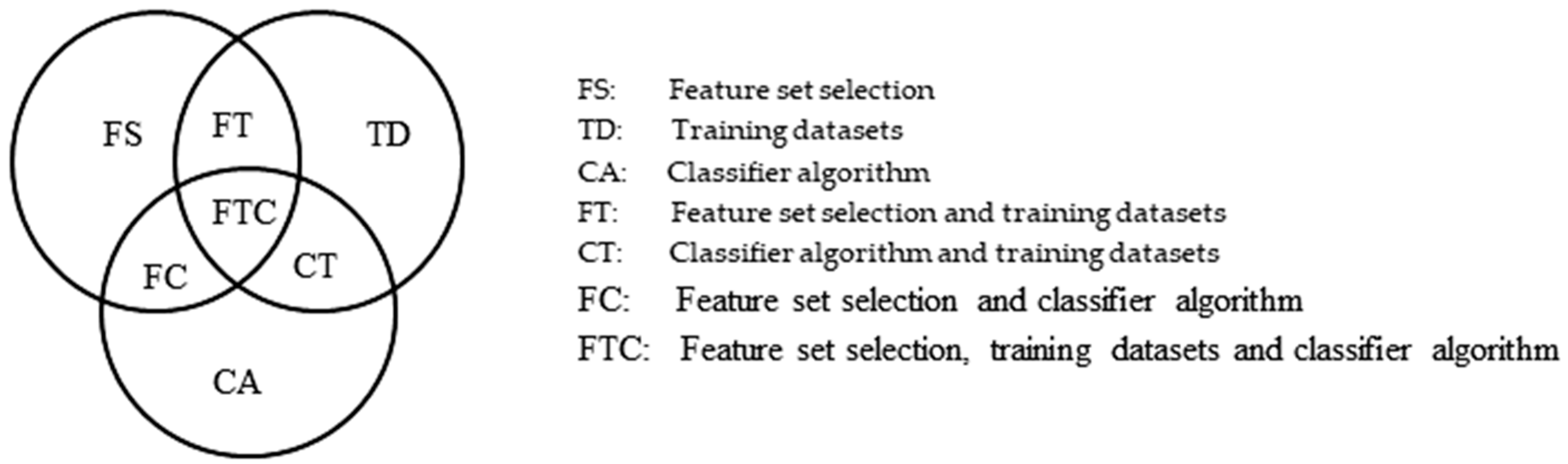
| Attacker Type | ||||
|---|---|---|---|---|
| Weak Attacker | Strong Attacker | Sophisticated Attacker | ||
| Classifier Level | FS | • | • | • |
| TD | • | • | • | |
| CA | • | |||
| FT | • | • | ||
| CT | • | |||
| FC | • | |||
| FTC | • | |||
| Reference | [165] | [166] | [167] | [168] | [169] | [170] |
|---|---|---|---|---|---|---|
| Technique | Data Sanitization | Ensemble method | Differential privacy | Holomorphic encryption | Adversarial training | Defense distillation |
| Type of security property | Protect availability and integrity | Protect availability and integrity | Preserve privacy and integrity | Preserve privacy and integrity | Protect availability and integrity | Protect availability and integrity |
| Advantage | Based on RONI sanitization rejects samples which include a negative impact | Ensemble the training data with perturbations transferred from other models | Give protection against strong attacker over training mechanism and model parameters | Able to protect data privacy multi-party computational environment and directly process encrypted data | Provides the examples of adversarial training and labels during training to identify adversarial in future | Reduces sensitivity of networks to adversarial manipulation of their inputs also leverages the resilience to adversarial crafting |
| Disadvantage | RONI defense fails to detect a focused attack | Not considered black box adversaries that attack a model via other means | Differential privacy accuracyis less | This approach is designed only for the horizontal data objects only | Ensemble approach provides limited resistance to adversarial perturbation | Add only restricted amount of features also gradually cannot change the features |
| Type of approach | Reactive | Reactive | Proactive | Proactive | Reactive | Proactive |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Sagar, R.; Jhaveri, R.; Borrego, C. Applications in Security and Evasions in Machine Learning: A Survey. Electronics 2020, 9, 97. https://doi.org/10.3390/electronics9010097
Sagar R, Jhaveri R, Borrego C. Applications in Security and Evasions in Machine Learning: A Survey. Electronics. 2020; 9(1):97. https://doi.org/10.3390/electronics9010097
Chicago/Turabian StyleSagar, Ramani, Rutvij Jhaveri, and Carlos Borrego. 2020. "Applications in Security and Evasions in Machine Learning: A Survey" Electronics 9, no. 1: 97. https://doi.org/10.3390/electronics9010097
APA StyleSagar, R., Jhaveri, R., & Borrego, C. (2020). Applications in Security and Evasions in Machine Learning: A Survey. Electronics, 9(1), 97. https://doi.org/10.3390/electronics9010097






