Hardware Activation by Means of PUFs and Elliptic Curve Cryptography in Field-Programmable Devices
Abstract
:1. Introduction
2. Secure Hardware Activation System
- Blocked mode. In this mode, the IP core remains blocked, without any functionality
- Demo mode. In this mode, the core maintains a limited functionality. This mode enables the possibility of distributing the core for performance and feature evaluation by the customer, in a similar way to the demo versions of software programs.
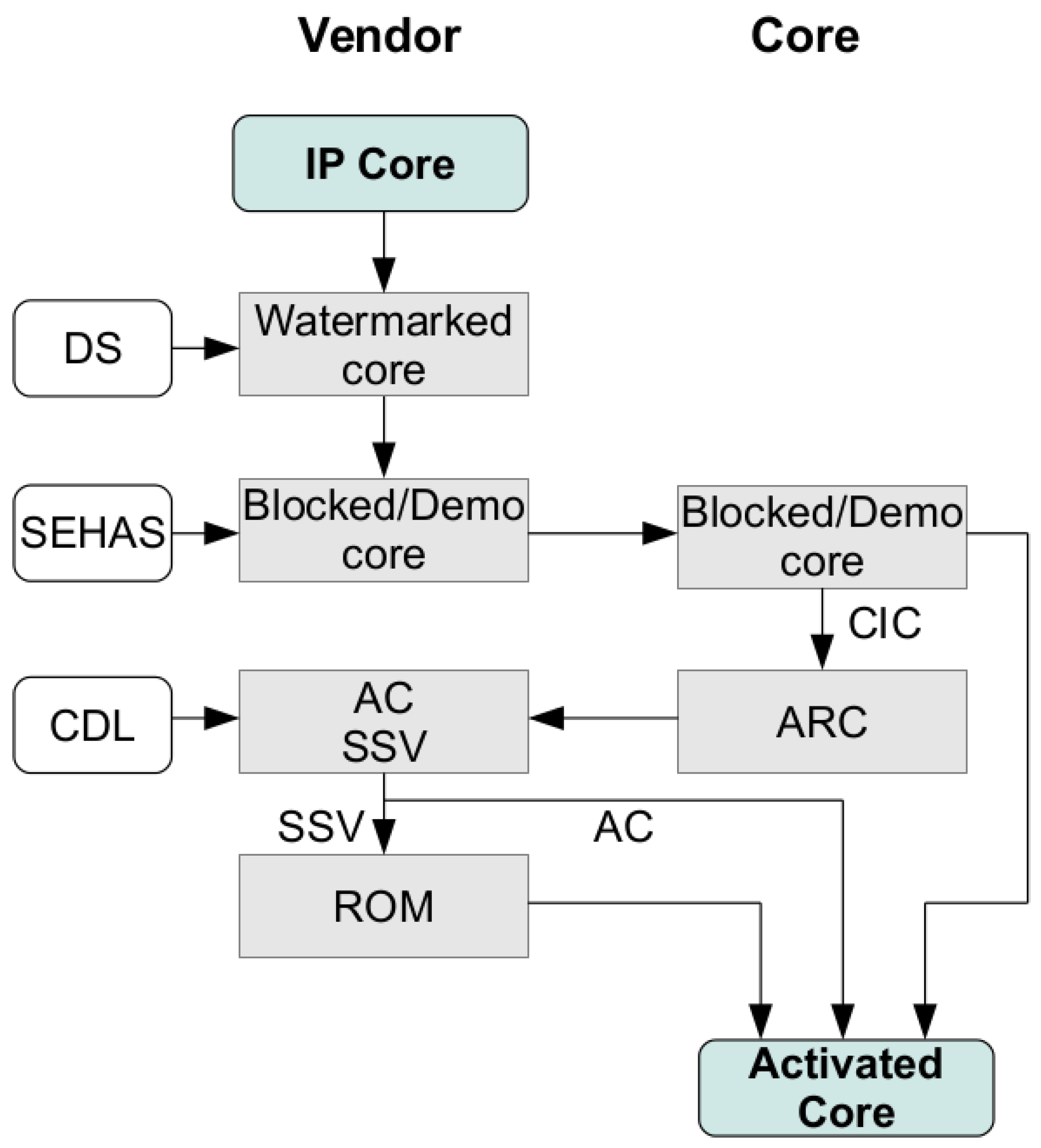
2.1. Activation Protocol
- Introduction of the SEHAS module into the core. The logic needed for extracting the DS is included into the SEHAS module, which is after that embedded into the IP core. Note that the DS is not visible from outside at any time. Also, the structure of the IP core circuit, which includes the SEHAS module and the additional logic needed for protection, will not be modified later. Thus, if a Physical Unconlable Function (PUF) is used for obtaining the Device ID (DID), the PUF’s result will remain unchanged in the next steps. As a result of this operation, an IP core in Blocked/Demo mode is obtained and supplied to the customer.
- Generation of the Activation Request Code (ARC). The customer enables the generation of the ARC by introducing a given control sequence to the core. This ARC is the public key of the ECC PKC [22] established for securing the information exchange between the vendor and the core. The private key is obtained from the DS and the DID, thus including information about the IP core and the implementation device. Summarizing this all, the private-public key pair of the core are the CIC (Combined Identification Code, obtained concatenating the DS and the DID) and the ARC. Once the ARC is generated, it is sent to the vendor. In this way, the customer has no information about the DS or the DID, since only the public key (ARC) is sent.
- Generation of the Activation Code (AC) and the Secure Shared Value (SSV). The vendor generates its private-public key pair. The private key is named Core-Device License (CDL), and the public key is the Activation Code. Using the CDL (private key of the vendor), and the ARC (public key of the core), the Secure Shared Value (SSV) is computed. The same SSV can be derived from the CIC (private key of the core) and the AC (Public Key of the vendor).
- Generation of the ROM configuration. The SEHAS module contains a ROM, which includes part of the combinational logic of the protected core. Depending on the ROM contents, the core will be in Blocked, Demo or Activated mode. In this step, the vendor generates a ROM configuration that modifies the logic functionality of the core. This new ROM configuration enables the switch to the Activated mode by means of the SSV. Also, the vendor sends the AC to the customer. Again, the exchanged information is a public key, and the ROM configuration corresponds to modified logic functions without useful information. Moreover, the ROM contents could be encrypted if more security was needed, using a private-key cryptosystem. AES-128 can be implemented using only 444 LUTs [30], maintaining high levels of security with low area overhead. The private key to be used for ROM encription/decription will be the Digital Signature (DS) of the IP core.
- Activation of the protected core. The customer performs the ROM configuration, and supplies the AC to the core. The SEHAS module internally computes the SSV using the AC (public key of the vendor) and the CIC (private key of the core), then switching to the Activated Mode.
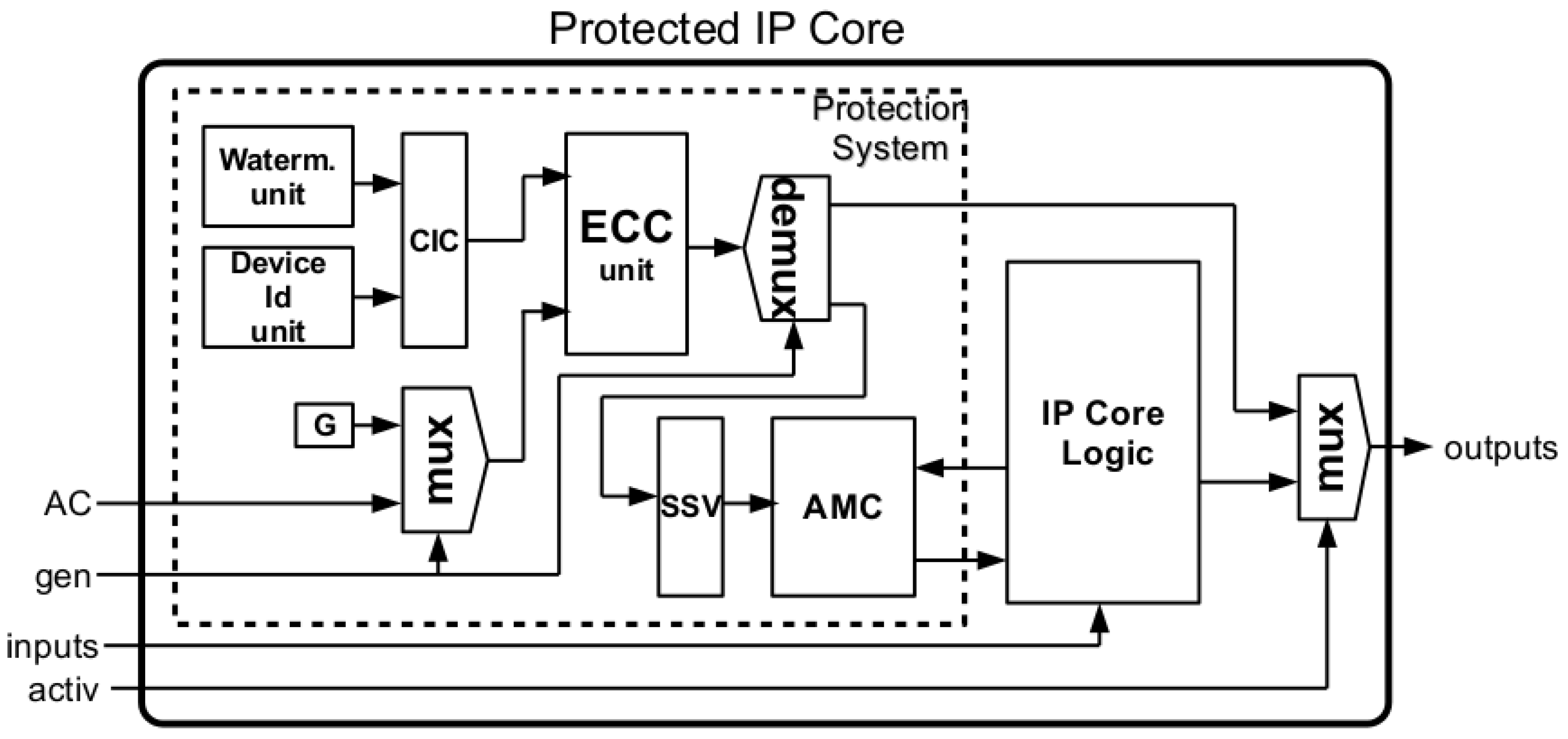
2.2. Hardware Structure for SEHAS Implementation
- Watermarking Unit. Operation 1 of the activation process is performed through one of the watermarking techniques from those available in the literature [6,9]. As a result of applying such method, a DS will be stored in the protected core. The watermarking unit is the responsible for extracting the DS previously stored in the watermarked core, as it was detailed in Operation 2 above. The DS extracted will be concatenated with the DID generated by the Device Identification Unit, resulting in the CIC that is needed for completing Operation 3.
- Device Identification Unit. This unit provides the Device ID (DID), using a FPGA vendor specific function or a Physical Unclonable Function (PUF). In Section 3, these different possibilities will be considered. The DID obtained is combined with the DS supplied by the watermarking unit, generating the CIC.
- ECC Unit. The ECC unit performs the cryptographic operations needed by SEHAS. When the gen input takes the ‘0’ value, the ECC unit computes the ARC from the CIC and the base point G [22] (Operation 3). Note that activ input must take the value ‘1’ for obtaining the ARC at the output of the core. When gen input takes the ‘1’ value, ECC computes the SSV from the CIC and the AC, required for activating the core (Operation 6).
- SSV Register. The SSV register maintains the SSV value computed by the ECC unit, allowing the IP core to operate in Activated mode while powered on.
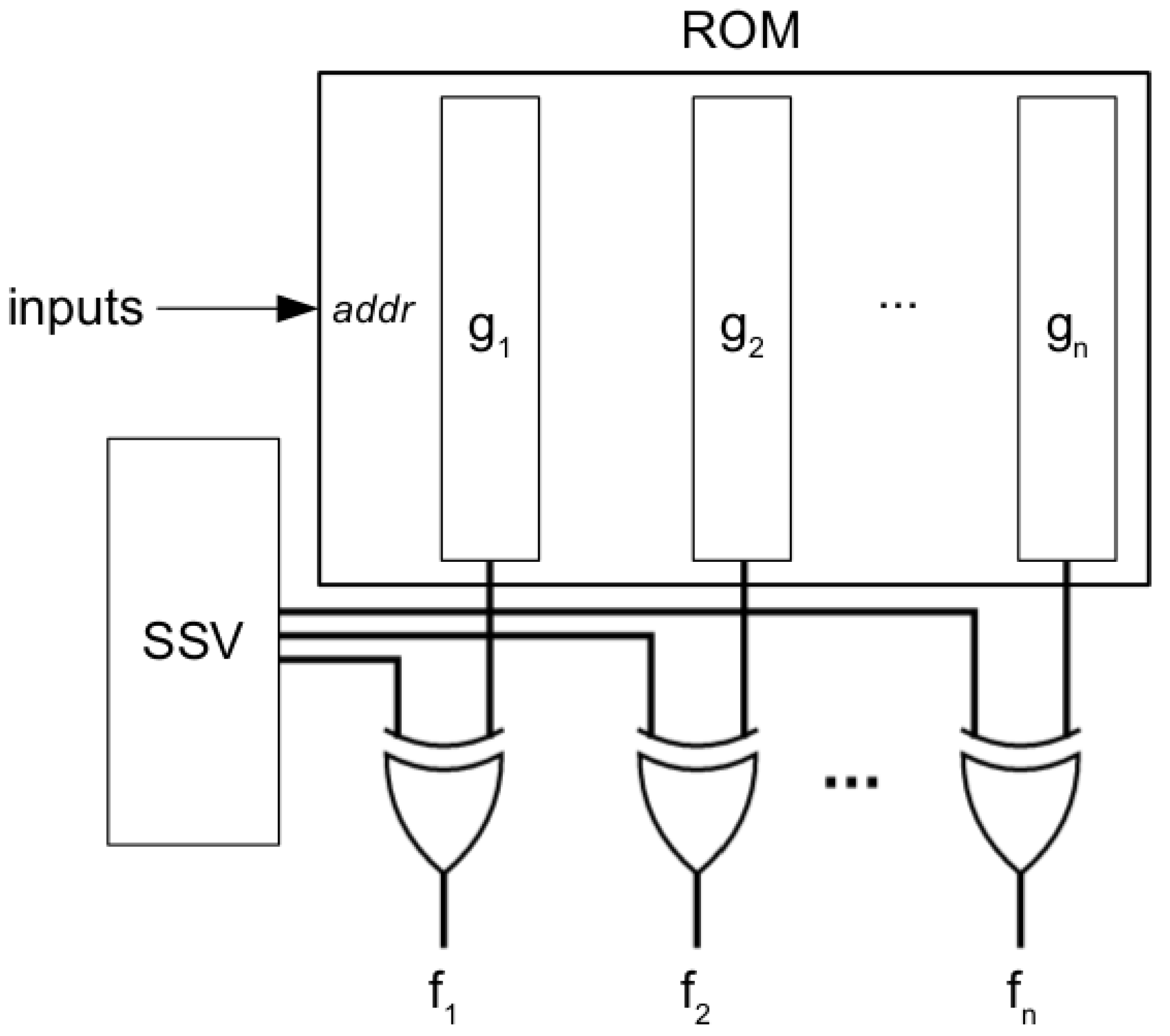
- AMC. The AMC block contains part of the combinational logic of the IP core under protection. The combinational functions are implemented using a ROM, with additional logic XOR-ing the functions with the SSV. Depending on the ROM configuration and the SSV, the core will be in Blocked, Demo or Activated mode.
3. SEHAS Blocks Implementations
3.1. Device Identification in FPGAs Using PUFs
- Variability. The PUF should generate a different DID for each device, and this DID must have good random statistical properties over different devices.
- Repeatability. The PUF should generate always the same DID in the same device, independently of the operating conditions.

- Xilinx Spartan-3AN Starter Kit (with xc3s700an-4fgg484 devices)
- Xilinx Spartan-6 SP605 Evaluation Platform (with xc6slx45t-3fgg484 devices)
- Xilinx Virtex-6 ML605 Evaluation Platform (with xc6vlx240t-1ff1156 devices)
- Altera DE-1 (with Cyclone II EP2C20F484C7 devices)
- Altera DE-2 (with Cyclone II EP2C35F672C6 devices)

| Device | # PUF Bits | # LUTs/LEs | Delay (ns) |
|---|---|---|---|
| Cyclone II EP2C20F484C7 (Altera) | 32 | 1241 (LEs) | 4.18 |
| 48 | 1849 (LEs) | 4.67 | |
| 64 | 2457 (LEs) | 4.98 | |
| Cyclone II EP2C35F672C6 (Altera) | 32 | 1241 (LEs) | 4.08 |
| 48 | 1849 (LEs) | 4.49 | |
| 64 | 2457 (LEs) | 4.89 | |
| Spartan 3AN xc3s700an-4fgg484 (Xilinx) | 32 | 897 (4-input LUTs) | 4.78 |
| 48 | 1329 (4-input LUTs) | 5.59 | |
| 64 | 1732 (4-input LUTs) | 5.66 | |
| Spartan 6 xc6slx45t-3fgg484 (Xilinx) | 32 | 732 (6-input LUTs) | 4.39 |
| 48 | 1084 (6-input LUTs) | 4.92 | |
| 64 | 1436 (6-input LUTs) | 5.26 | |
| Virtex 6 xc6vlx240t-1ff1156 (Xilinx) | 32 | 732 (6-input LUTs) | 2.83 |
| 48 | 1084 (6-input LUTs) | 2.85 | |
| 64 | 1436 (6-input LUTs) | 2.71 |
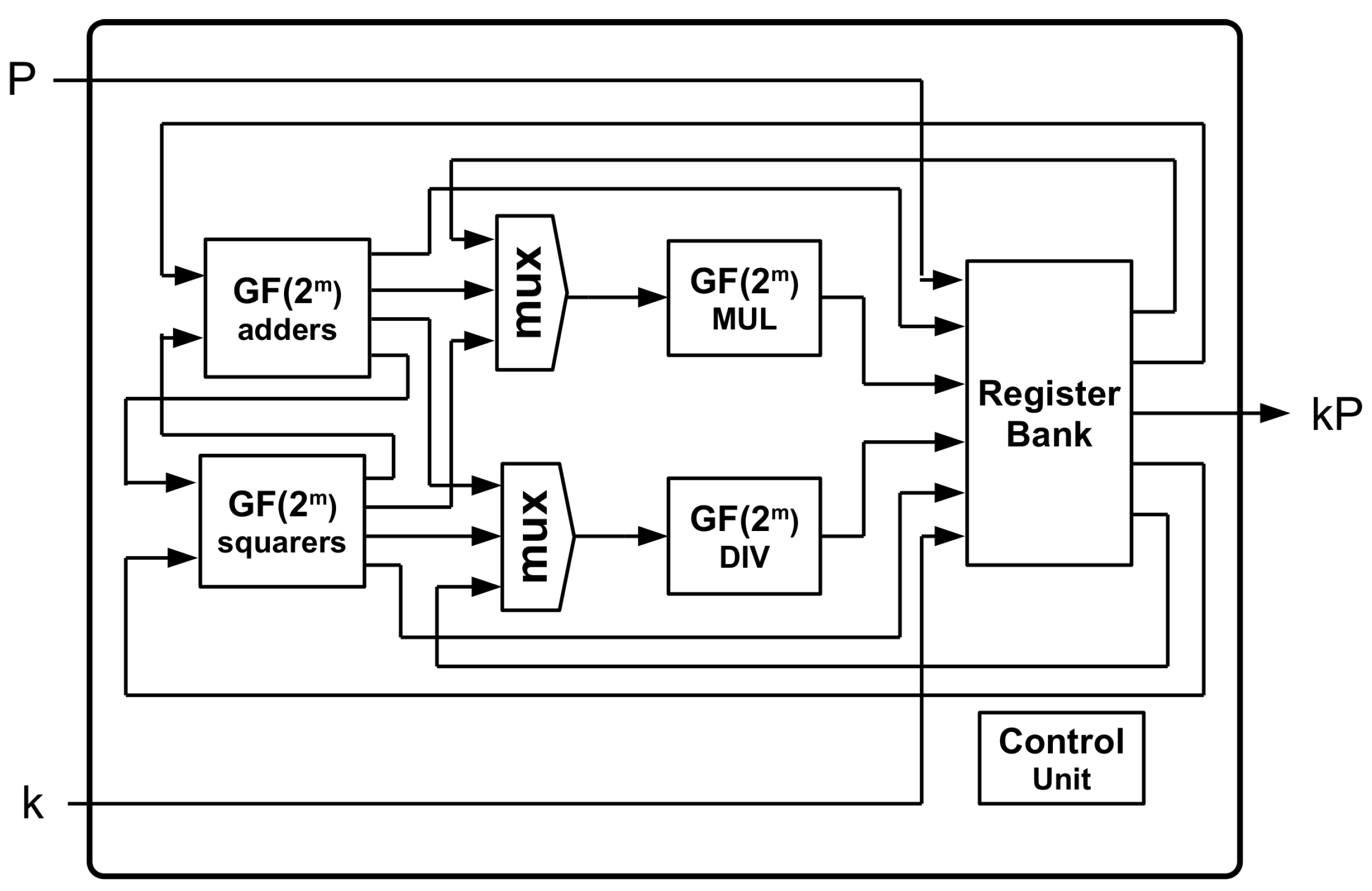
3.2. Low Area ECC Unit for Implementing a PKC in IP Cores
3.2.1. Elliptic Curves over Finite Fields
3.2.2. Domain Parameters for the ECC Unit
- (reduction polynomial for the field)
- (number of elements of the subgroup)
- (cofactor)
- (base point)
3.2.3. Scalar-Point Product Using the Montgomery Ladder Algorithm
| Algorithm 1: Algorithm 1 Montgomery ladder |
| Require: k, P |
| Ensure: |
|
|
|
|
|
|
|
|
|
| Device | #LUTs/LEs | Delay (ns) |
|---|---|---|
| Cyclone II EP2C20F484C7 (Altera) | 6093 (LEs) | 10.53 |
| Cyclone II EP2C35F672C6 (Altera) | 6079 (LEs) | 9.06 |
| Spartan 3AN xc3s700an-4fgg484 (Xilinx) | 6525 (4-input LUTs) | 13.98 |
| Spartan 6 xc6slx45t-3fgg484 (Xilinx) | 4618 (6-input LUTs) | 7.95 |
| Virtex 6 xc6vlx240t-1ff1156 (Xilinx) | 4336 (6-input LUTs) | 5.12 |
3.3. Activation Modes Circuit (AMC) Design
- The vendor can provide the functions sending only the ROM configuration. This method does not produce any modification in the original circuit and, consequently, does not affect the PUF output.
- The vendor can provide functions for entering in Demo mode, if desired, without changing the structure of the circuit.
3.4. SEHAS Area and Performance Analysis
- SEHAS-DID-ROM. In this design, the DID provided by the device manufacturers is used. Thus, DNA_PORT has been used for Xilinx devices, while ALTCHIP_ID was not available for the Altera devices used for tests. Regarding the AMC, a ROM with no encryption is used, resulting in the design with lowest area overhead.
- SEHAS-PUF48-ROM. This design assumes the unavailability of a DID supplied by the manufacturers, and makes use of a 48-bit NANDTO PUF. The AMC includes a ROM with no encryption.
- SEHAS-DID-AES. This design considers a SEHAS protection module taking advantage of DID functions provided by device manufacturers, and including an AMC with a ROM encrypted using AES-128.
- SEHAS-PUF48-AES. Finally, a design using a 48-bit PUF and AES encrypted ROM is considered.
| Design | Device | #LUTs/LEs | Delay (ns) |
|---|---|---|---|
| SEHAS-DID-ROM | Cyclone II EP2C20F484C7 (Altera) | n/a | n/a |
| Cyclone II EP2C35F672C6 (Altera) | n/a | n/a | |
| Spartan 3AN xc3s700an-4fgg484 (Xilinx) | 7151 (4-input LUTs) | 14.98 | |
| Spartan 6 xc6slx45t-3fgg484 (Xilinx) | 5194 (6-input LUTs) | 8.15 | |
| Virtex 6 xc6vlx240t-1ff1156 (Xilinx) | 4934 (6-input LUTs) | 5.52 | |
| SEHAS-PUF48-ROM | Cyclone II EP2C20F484C7 (Altera) | 10251 (LEs) | 12.33 |
| Cyclone II EP2C35F672C6 (Altera) | 10249 (LEs) | 11.26 | |
| Spartan 3AN xc3s700an-4fgg484 (Xilinx) | 10551 (4-input LUTs) | 13.98 | |
| Spartan 6 xc6slx45t-3fgg484 (Xilinx) | 8250 (6-input LUTs) | 8.33 | |
| Virtex 6 xc6vlx240t-1ff1156 (Xilinx) | 7154 (6-input LUTs) | 5.94 | |
| SEHAS-DID-AES | Cyclone II EP2C20F484C7 (Altera) | n/a | n/a |
| Cyclone II EP2C35F672C6 (Altera) | n/a | n/a | |
| Spartan 3AN xc3s700an-4fgg484 (Xilinx) | 7545 (4-input LUTs) | 14.10 | |
| Spartan 6 xc6slx45t-3fgg484 (Xilinx) | 5515 (6-input LUTs) | 8.35 | |
| Virtex 6 xc6vlx240t-1ff1156 (Xilinx) | 5109 (6-input LUTs) | 5.72 | |
| SEHAS-PUF48-AES | Cyclone II EP2C20F484C7 (Altera) | 10695 (LEs) | 15.43 |
| Cyclone II EP2C35F672C6 (Altera) | 10670 (LEs) | 14.27 | |
| Spartan 3AN xc3s700an-4fgg484 (Xilinx) | 10995 (4-input LUTs) | 15.43 | |
| Spartan 6 xc6slx45t-3fgg484 (Xilinx) | 8591 (6-input LUTs) | 8.65 | |
| Virtex 6 xc6vlx240t-1ff1156 (Xilinx) | 7371 (6-input LUTs) | 6.14 |
3.5. Security Analysis
- Generating and sending the ROM to the customer. The ROM contains part of the logic functions needed for the functioning of the IP core, XORed with the SSV. Although the content of the ROM is meaningless, it must be large enough to prevent brute-force and statistical attacks. In fact, a ROM containing only four 3-input functions (32 bits) can be easily broken by brute-force. Also, if the designer includes trivial functions, statistical analysis could provide information about the SSV. Thus, the ROM must contain at least 163 bits of effective information (for maintaining the 163 bits of the ECC domain), in order to avoid a weakness in the protection chain. In this scheme, the selection of the adequate functions to be included into the ROM is responsibility of the IP core designer. This weakness can be avoided by encrypting the ROM using a private-key cryptosystem like AES-128 [30]. If the DS is used as private key, the vendor and the IP core can share it without interchanging additional keys, while securing the ROM contents. SEHAS provides this feature at the cost of 444 additional LUTs.
- Computation of the SSV into the IP core. At boot time, the SSV is computed using the Activation Code and the CIC. This moment can be used for trying side channel attacks over the ECC unit. For avoiding this issue, the ECC unit has been designed using the Montgomery ladder algorithm [28], which takes the same number of clock cycles independently of the scalar involved in the scalar-point operation.
4. Conclusions
Acknowledgments
Author Contributions
Conflicts of Interest
References
- Keating, M.; Bricaud, P. Reuse Methodology Manual for System-on-a-Chip Designs; Kluwer Academic Publishers: Dordrecht, The Netherlands, 2007. [Google Scholar]
- Cox, I.; Miller, M.; Bloom, J. Digital Watermarking: Principles & Practice; Morgan Kaufmann: Burlington, MA, USA, 2001. [Google Scholar]
- Charbon, E.; Torunoglu, I. Watermarking Techniques for Electronic Circuit Designs; Lecture Notes in Computer Science; Springer: Berlin, Germany; Heidelberg, Germany, 2003; Volume 2613, pp. 147–169. [Google Scholar]
- Kahng, B.; Lach, J.; Mangione-Smith, W.H.; Mantik, S.; Markov, I.L.; Potkonjak, M.; Tucker, P.; Wang, H.; Wolfe, G. Watermarking techniques for intellectual property protection. In Proceedings of the Design Automation Conference, San Francico, CA, USA, 15–19 June 1998; pp. 776–781.
- Houshanfar, F.; Hong, I.; Potkonjak, M. Behavioral synthesis techniques for intellectual property protection. ACM Trans. Des. Autom. Electr. Syst. 2005, 10, 523–545. [Google Scholar] [CrossRef]
- Castillo, E.; Meyer-Baese, U.; García, A.; Parrilla, L.; Lloris, A. IPP@HDL: Efficient intellectual property protection scheme for IP cores. IEEE Trans. Very Large Scale Integr. Syst. 2007, 15, 578–591. [Google Scholar] [CrossRef]
- Castillo, E.; Morales, D.P.; García, A.; Parrilla, L.; Todorovich, E.; Meyer-Baese, U. Design Time Optimization for Hardware Watermarking Protection of HDL Designs. Sci. World J. 2015. [Google Scholar] [CrossRef] [PubMed]
- Ziener, D.; Teich, J. Power Signature Watermarking of IP Cores for FPGAs. J. Signal Process. Syst. 2008, 51, 123–136. [Google Scholar] [CrossRef]
- Parrilla, L.; Castillo, E.; Todorovich, E.; García, A.; Morales, D.P.; Botella, G. Improvements for the applicability of power-watermarking to embedded IP cores protection: e-coreIPP. Digit. Signal Process. 2015, 44, 110–122. [Google Scholar] [CrossRef]
- Narasimhan, S.; Chakraborty, R.; Bhunia, S. Hardware IP Protection During Evaluation Using Embedded Sequential Trojan. IEEE Des. Test 2011, 99, 1. [Google Scholar] [CrossRef]
- Saha, D.; Sur-Kolay, S. Secure Public Verification of IP Marks in FPGA Design Through a Zero-Knowledge Protocol. IEEE Trans. Very Large Scale Integr. Syst. 2012, 20, 1749–1757. [Google Scholar] [CrossRef]
- Kean, T.; Mclaren, E.; Marsh, C. Verifying the authenticity of chip designs with the Design Tag system. In Proceedings of the IEEE International Workshop on Hardware-Oriented Security and Trust, Anaheim, CA, USA, 9 June 2008; pp. 59–64.
- Sridhar, L.; Prabha, V.L. RFID Based Access Control Protection Scheme for SRAM FPGA IP Cores. Microprocess. Microsyst. 2013, 37, 629–640. [Google Scholar] [CrossRef]
- Parrilla, L.; Castillo, E.; Meyer-Baese, U.; García, A.; González, D.; Todorovich, E.; Boemo, E.; Lloris, A. Watermarking strategies for IP protection of micro-processor cores. In Proceedings of the SPIE 7703, Independent Component Analyses, Wavelets, Neural Networks, Biosystems, Orlando, FL, USA, 5 April 2010.
- Pappu, R.S.; Recht, B.; Taylor, J.; Gershenfeld, N. Physical one-way functions. Science 2002, 297, 2026–2030. [Google Scholar] [CrossRef] [PubMed]
- Suh, G.E.; O’Donnell, C.W.; Devadas, S. Aegis: A Single-Chip Secure Processor. IEEE Des. Test Comput. 2007, 24, 570–580. [Google Scholar] [CrossRef]
- Suh, G.E.; Devadas, S. Physical Unclonable Functions for Device Authentication and Secret Key Generation. In Proceedings of the Design Automation Conference, San Diego, CA, USA, 4–8 June 2007.
- Anderson, J.H. A PUF design for secure FPGA-based embedded systems. In Proceedings of the 2010 Asia and South Pacific Design Automation Conference, Taipei, Taiwan, 18–21 January 2010; IEEE Press: Piscataway, NJ, USA, 2010; pp. 1–6. [Google Scholar]
- Kumar, S.; Guajardo, J.; Maes, R.; Schrijen, G.J.; Tuyls, P. The butterfly PUF: Protecting IP on every FPGA. In Proceedings of the IEEE International Workshop on Hardware-Oriented Security and Trust, Anaheim, CA, USA, 9 June 2008; pp. 67–70.
- Lim, D.; Lee, J.W.; Gassend, B.; Suh, G.E.; van Dijk, M.; Devadas, S. Extracting secret keys from integrated circuits. IEEE Trans. Very Large Scale Integr. Syst. 2005, 13, 1200–1205. [Google Scholar]
- Morozov, S.; Maiti, A.; Schaumont, P. A Comparative Analysis of Delay Based PUF Implementations on FPGA. In Reconfigurable Computing: Architectures, Tools and Applications; Springer: Berlin, Germany; Heidelberg, Germany, 2010; pp. 382–387. [Google Scholar]
- IEEE Standard Specifications for Public-Key Cryptography. In IEEE Std 1363–2000; IEEE: Washington, DC, USA, 2000. [CrossRef]
- IEEE Standard Specifications for Public-Key Cryptography - Amendment 1: Additional Techniques. In IEEE Std 1363a-2004 (Amendment to IEEE Std 1363-2000); IEEE: Washington, DC, USA, 2004. [CrossRef]
- Koblitz, N. Elliptic curve cryptosystems. Math. Comput. 1987, 48, 203–209. [Google Scholar] [CrossRef]
- Vanstone, S.A. Next generation security for wireless: Elliptic curve cryptography. Comput. Secur. 2003, 22, 412–415. [Google Scholar] [CrossRef]
- Batina, L.; Mentens, N.; Sakiyama, K.; Preneel, B.; Verbauwhede, I. Low-Cost Elliptic Curve Cryptography for Wireless Sensor Networks. In Security and Privacy in Ad-Hoc and Sensor Networks; LNCS 4357; Springer: Berlin, Germany; Heidelberg, Germany, 2006; pp. 6–17. [Google Scholar]
- Lauter, K. The Advantages of Elliptic Curve Cryptography for Wireless Security. IEEE Wirel. Commun. 2004, 11, 62–67. [Google Scholar] [CrossRef]
- Sutter, G.; Deschamps, J.J.; Imaña, J.L. Efficient Elliptic Curve Point Multiplication Using Digit-Serial Binary Field Operations. IEEE Trans. Ind. Electron. 2013, 60, 217–225. [Google Scholar] [CrossRef]
- Parrilla, L.; Lloris, A.; Castillo, E.; García, A. Minimum-clock-cycle Itoh-Tsujii algorithm hardware implementation for cryptography applications over GF(2m) fields. Electron. Lett. 2012, 48, 1126–1128. [Google Scholar] [CrossRef]
- Chodowiec, P.; Gaj, K. Very Compact FPGA Implementation of the AES Algorithm; Lecture Notes in Computer Science; Springer: Berlin, Germany; Heidelberg, Germany, 2003; Volume 2779, pp. 319–333. [Google Scholar]
- Cohen, H. Handbook of Elliptic and Hyperelliptic Curve Cryptography; Chapman & Hall/CRC: London, UK, 2005; ISBN 9781420034981. [Google Scholar] [CrossRef]
- FIPS PUB 186-4: Digital Signature Standard (DSS); Federal Information Processing Standards Publication: Gaithersburg, MD, USA, 2013. [CrossRef]
- Deschamps, J.P.; Imaña, J.L.; Sutter, G.D. Hardware Implementation of Finite-Field Arithmetic; Electronic Engineering Series; McGraw-Hill: New York, NY, USA, 2009. [Google Scholar]
- Kim, C.H.; Hong, C.P. High-speed division architecture for GF(2m). Electron. Lett. 2002, 38, 835–836. [Google Scholar] [CrossRef]
- Simpson, E.; Schaumont, P. Offline Hardware/Software Authentication for Reconfigurable Platforms; Lecture Notes in Computer Science; Springer: Berlin, Germany; Heidelberg, Germany, 2006; Volume 4249, pp. 311–323. [Google Scholar]
- Guajardo, J.; Kumar, S.S.; Schrijen, G.J.; Tuyls, P. FPGA Intrinsic PUFs and Their Use for IP Protection; Lecture Notes in Computer Science; Springer: Berlin, Germany; Heidelberg, Germany, 2007; Volume 4727, pp. 63–80. [Google Scholar]
© 2016 by the authors; licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons by Attribution (CC-BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Parrilla, L.; Castillo, E.; Morales, D.P.; García, A. Hardware Activation by Means of PUFs and Elliptic Curve Cryptography in Field-Programmable Devices. Electronics 2016, 5, 5. https://doi.org/10.3390/electronics5010005
Parrilla L, Castillo E, Morales DP, García A. Hardware Activation by Means of PUFs and Elliptic Curve Cryptography in Field-Programmable Devices. Electronics. 2016; 5(1):5. https://doi.org/10.3390/electronics5010005
Chicago/Turabian StyleParrilla, Luis, Encarnación Castillo, Diego P. Morales, and Antonio García. 2016. "Hardware Activation by Means of PUFs and Elliptic Curve Cryptography in Field-Programmable Devices" Electronics 5, no. 1: 5. https://doi.org/10.3390/electronics5010005
APA StyleParrilla, L., Castillo, E., Morales, D. P., & García, A. (2016). Hardware Activation by Means of PUFs and Elliptic Curve Cryptography in Field-Programmable Devices. Electronics, 5(1), 5. https://doi.org/10.3390/electronics5010005










