Security of Cooperative Intelligent Transport Systems: Standards, Threats Analysis and Cryptographic Countermeasures
Abstract
:1. Introduction
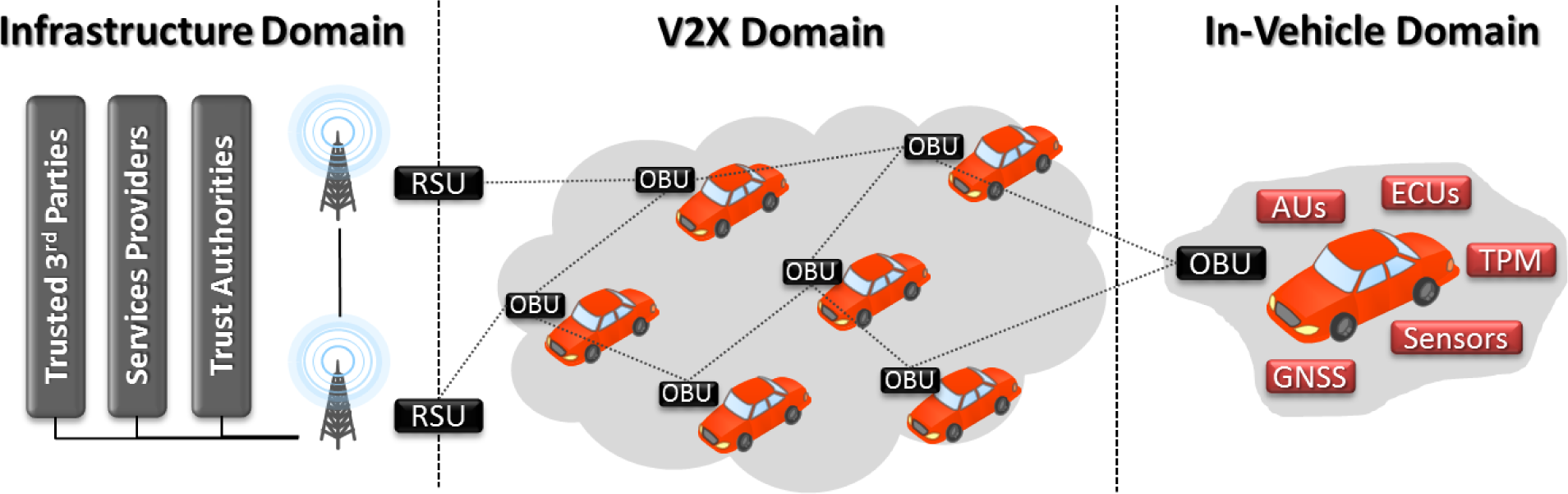
2. ITS Architecture and Applications
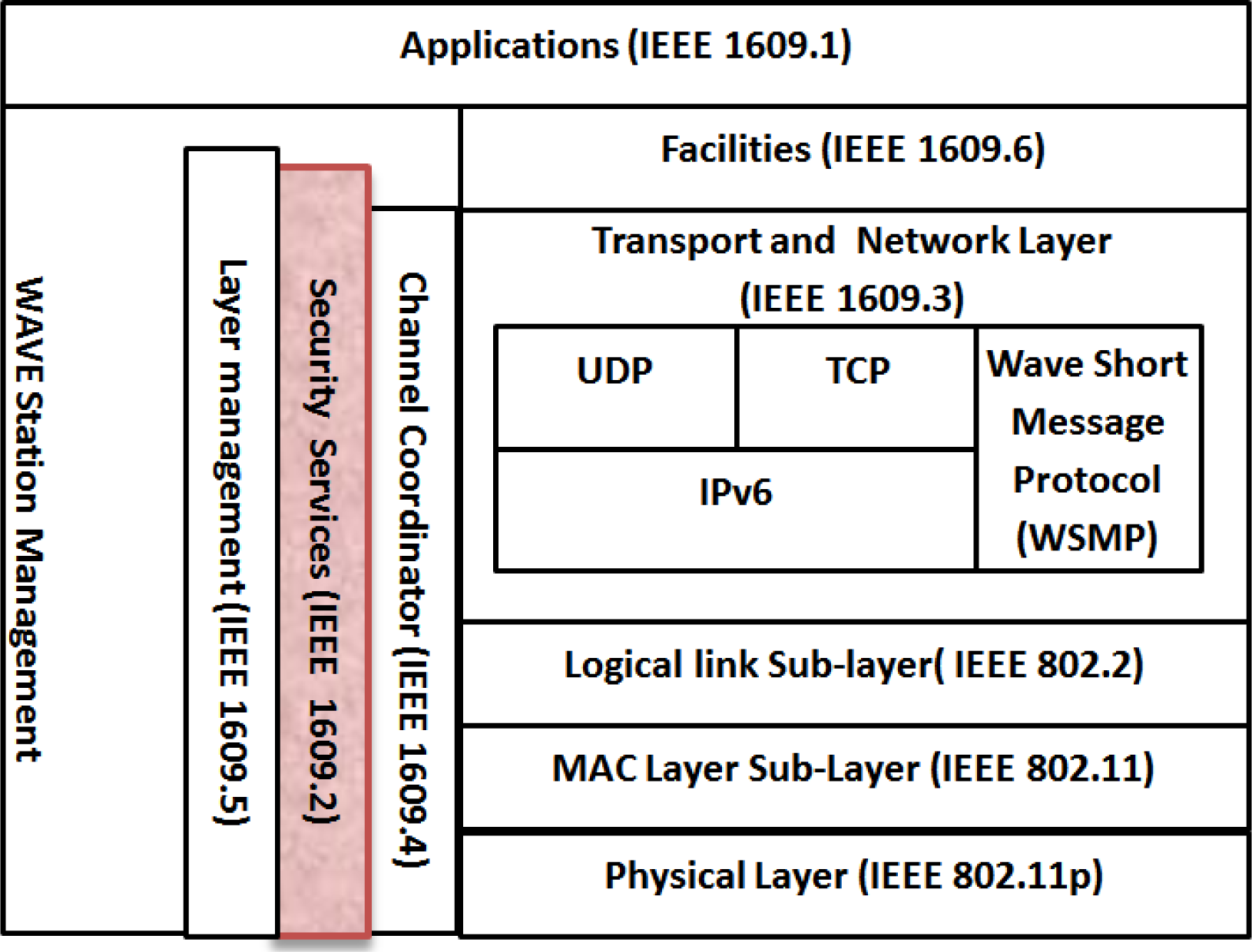
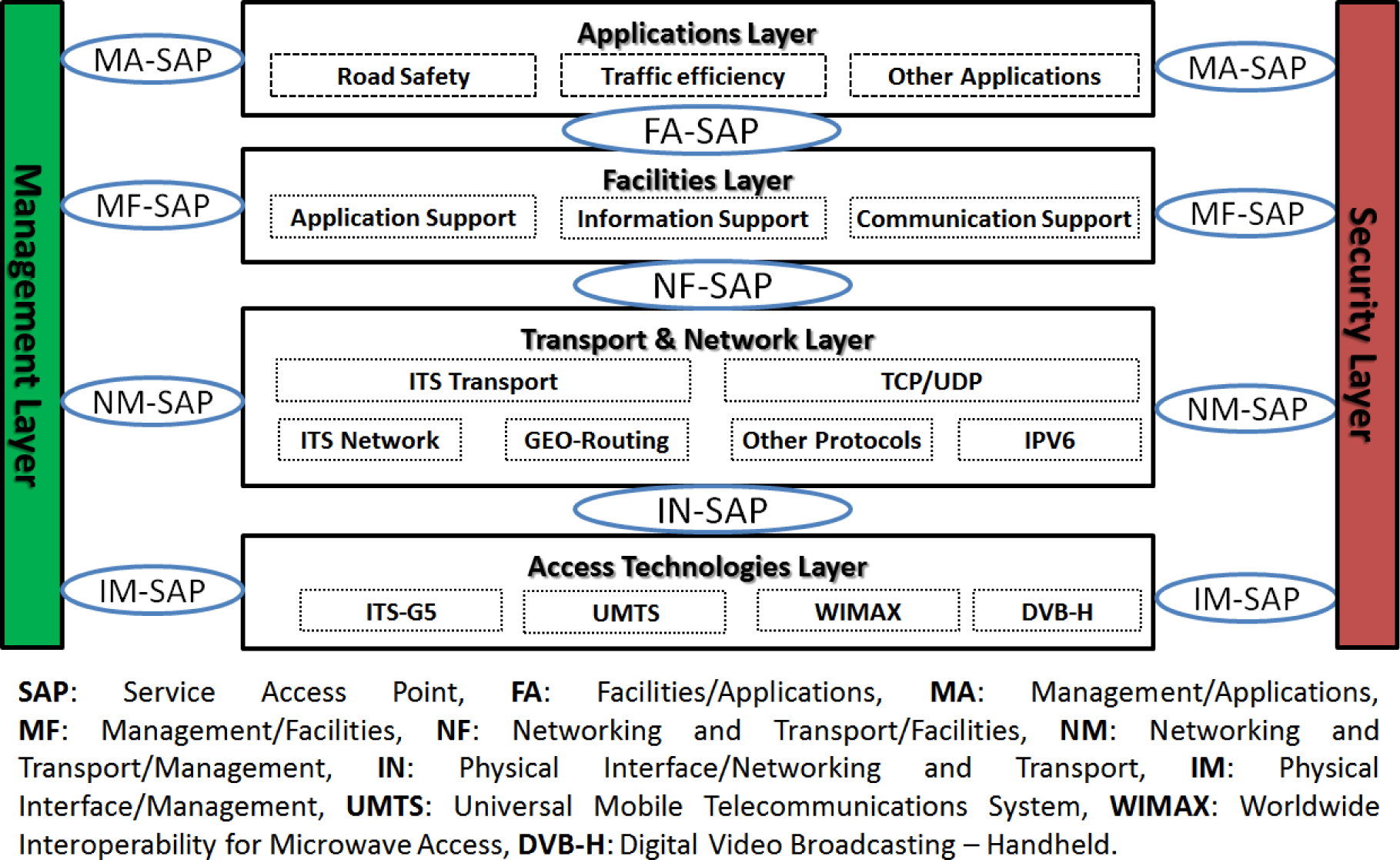
2.1. ITS Architecture
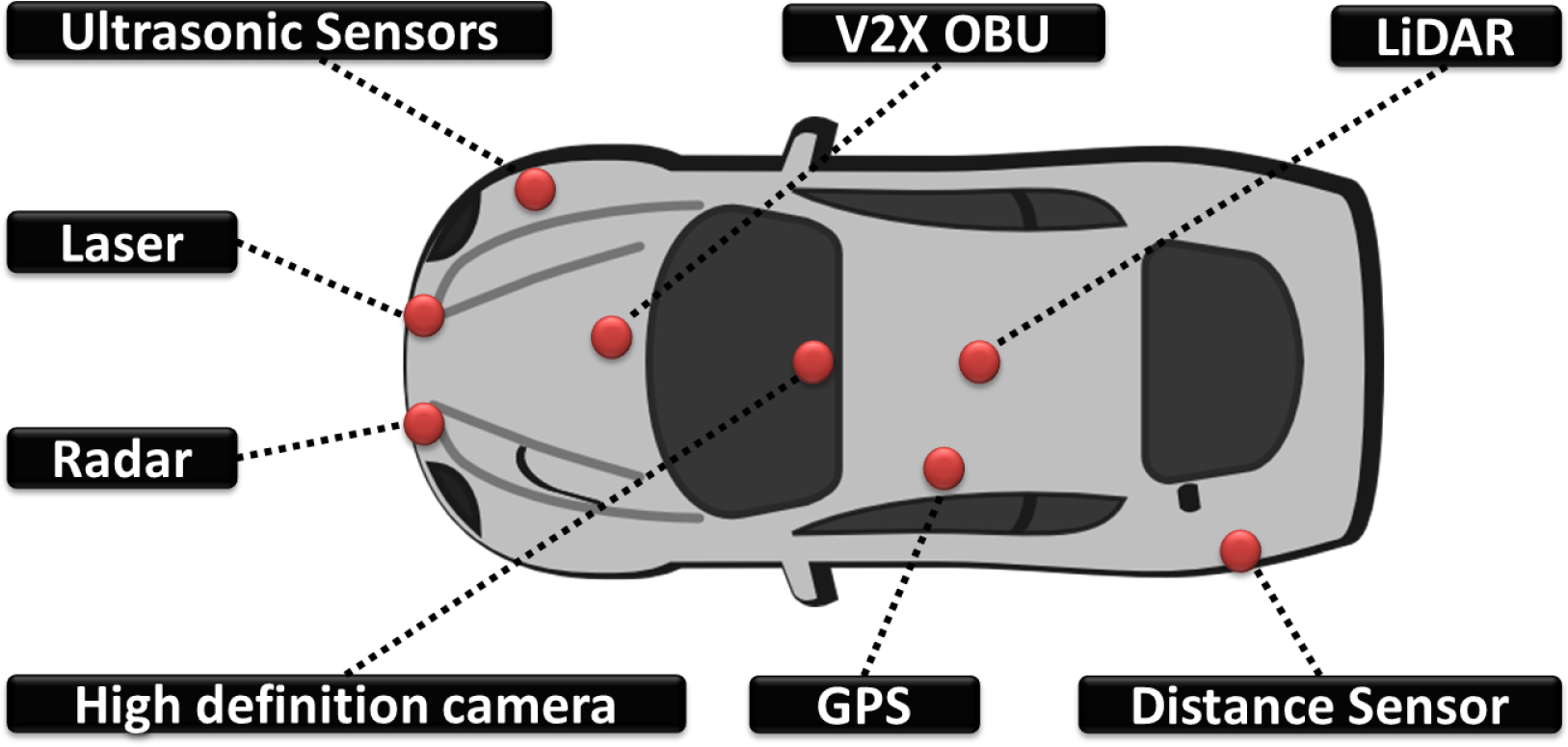
2.2. ITS Characteristics and Challenges
- Powerful capacity: ITS stations (i.e., RSUs, OBUs) are powerful in terms of energy, localization, computation, storage and data rate capabilities;
- High mobility: ITS involves a huge number of nodes that move from one location to another, with different speeds and directions, thus making the prediction of node position very difficult and necessitating node protection [25];
- Dynamic network topology: depending on their locations and speeds, ITS stations can join and/or leave the network very quickly; the resulting network topology is thus highly dynamic;
- Time sensitivity: safety information must be delivered to nodes in a short period of time (e.g., 100-ms delay for safety-related messages), thus making latency one of the most important quality of service (QoS) limitations for these kinds of networks;
- Sufficient energy: unlike wireless sensor networks (WSN), where nodes have limited resources and a small battery lifetime, ITS entities are considered as resource-rich devices (i.e., energy, storage and computation); this allows the implementation of complex algorithms to achieve a higher throughput in vehicular environments [26];
- Good physical protection: inside each ITS entity, physical protection can be ensured, giving the network immunity against physical attacks [26];
- Unbounded network size: ITS can be implemented in a small geographical area, or in cities, or even across several countries; this means that the size of the ITS network is not limited to a specific geographical area [27];
- Wireless communications: ITS entities communicate with each other and exchange information via a wireless connection; hence, some security measures and protocols must be used to ensure safe and protected communication;
- Heterogeneous V2X communication technologies: vehicles exploit different types of communication modes, such as multi-hop V2V, point-to-point V2I, short/long range V2I, etc.; in addition, connected vehicles support a wide range of communication technologies, such as IEEE 802.11p, Wi-Fi, Bluetooth, 3G/LTE, etc.;
- Heterogeneous environments: vehicles operate in various environments, such as indoor, outdoor, low and high network density, etc.;
- Security and privacy: security and privacy are of paramount importance in ITS; in most scenarios, attackers aim to affect the authentication, integrity and even the availability of the network; in this context, security protocols must be implemented with low communication overhead due to time constraint and low computation complexity to exchange quick and safe information.
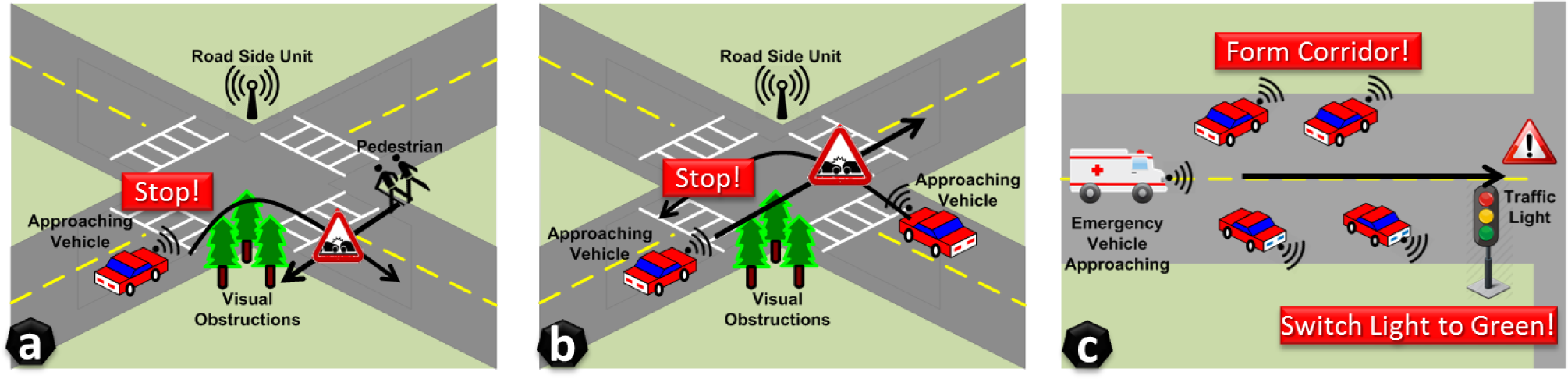
2.3. ITS Applications
2.3.1. Road Safety Applications
2.3.2. Traffic Management Applications
2.3.3. Infotainment and Comfort Applications
2.3.4. Autonomous Driving Applications
3. ITS Standards and Projects
3.1. ITS Key Enabling Standards
3.2. ITS Research Projects
4. ITS Threats Analysis and Classification
4.1. ITS Involved Entities
- The drivers: Drivers are the most important element of ITS, since they have to make vital decisions and can interact with the driving assistance systems to ensure their safety;
- The on-board unit (OBU): OBU refers to both the driver and the vehicle in the literature. OBUs can be classified into: (i) normal OBUs, which operate in a normal way; and (ii) malicious OBUs, which try to mislead the system;
- The road side unit (RSU): Similarly to OBU, RSUs can be classified into: (i) normal RSU terminals; and (ii) malicious RSU terminals, which try to mislead the system;
- Third party entities: Third party entities can be trusted or semi-trusted, and are responsible for managing the security certificates, as well as the diverse secrets/public key pairs. Examples of such entities include the transportation regulatory agencies and the vehicle manufacturers;
- The attackers: Attackers try to violate the security of ITS systems by using several techniques. These attackers can be classified into different categories, as discussed in the following subsection.
4.2. ITS Attackers Profiles
- Active vs. passive: Active attackers transmit malicious packets to harm other nodes or a part of the network. Generally, this attacker has the authorization to operate within the network. Moreover, active nodes that have insider status could perpetrate almost any kind of attack. In contrast, passive attackers eavesdrop on the communications between the other nodes in the network, in order to extract useful information. Although it cannot cause any direct damage to the network, the gathered information could be used for future attacks. In general, passive nodes are also outsiders;
- External vs. internal: External attackers are generally not authenticated and authorized to operate within the ITS network. External attacks target generally the confidentiality and availability of the system. In contrast, internal attackers are generally part of the ITS network and can perpetrate almost any kind of attack;
- Malicious vs. rational: Malicious attackers have no specific targets, and their main goal is to destroy the network, for example by transmitting false information to vehicles in a specific geographic area [48]. In contrast, rational attackers have a specific target and can be very dangerous [49] due to their unpredictable nature.
4.3. ITS Security Requirements
- Authentication: This is one of the most important ITS security requirement, which can be classified into three sub-requirements: (i) user authentication to prevent Sybil attacks and dismiss malicious entities; (ii) source authentication to ensure that messages were generated by legitimate ITS stations; and (iii) location authentication to ensure the integrity and relevance of the received information;
- Data integrity: ITS entities (e.g., OBUs, RSUs, etc.) should be able to verify and validate the integrity of the received messages in order to prevent any unauthorized or malicious modification, manipulation or deletion during transmission;
- Privacy and anonymity: The identities of drivers and vehicles should not be easily identifiable from the exchanged messages, and the right of the driver to control the access and use of her/his personal data should be enforced;
- Availability: Exchanged information should be processed and made available in real time, requiring thus the implementation of low-overhead and lightweight cryptographic algorithms;
- Traceability and revocation: ITS authorities should be able to track malicious ITS entities that are misusing the ITS system, in order to revoke them in a timely manner. The trust authority (TA) should be able to trace the vehicle and reveal its true identity. Furthermore, in case of a dispute or when a malicious vehicle is detected, the TA must revoke it and add its identity to the revocation list;
- Authorization: It is necessary to define the access control and authorization for the different entities. Specific rules should be enforced for accessing or denying specific ITS entities access and/or use of certain functions or data;
- Non-repudiation: Each ITS entity should be uniquely associated with its information and actions in order to achieve data authenticity and origination;
- Robustness against external attacks: ITS entities should be robust against external attacks, such as availability attacks, and ITS software should be almost free of vulnerabilities (e.g., buffer overflow) and logic flaws.
- Data confidentiality: Exchanged messages should be properly encrypted and protected in order to prevent the disclosure of sensitive information to malicious nodes or unauthorized parties;
4.4. Classification of ITS Attacks and Cryptographic Countermeasures
4.4.1. Attacks on Availability and Countermeasures
- Jamming attacks: This kind of attack is realized at the physical layer, and its goal is to disrupt the communication channel [53] by transmitting noisy signals with high frequency, so as to increase the interference level. This leads to attaining a lower signal-to-noise ratio (SNR) and makes the vehicles unable to communicate with other vehicles and RSU stations [54]. The effects of jamming can be detected using specific techniques [53,55] and can be mitigated, for example, by randomizing the frequency hopping spread spectrum (FHSS) mechanism of the orthogonal frequency-division multiplexing (OFDM) standard [56], using efficient pseudo-random generator algorithms;
- Flooding attacks: This type of attack consists of flooding the network with a huge volume of dummy messages that are intentionally generated by malicious nodes [57], making thus the OBUs and RSUs unable to communicate over the wireless channel. This can lead, for example, to accidents if the basic safety messages are not received in time by the legitimate vehicles;
- Sybil attacks: The main goal of Sybil attacks is to jam the network by employing false nodes identities [16,58]. Therefore, legitimate vehicles conclude that the malicious messages are coming from legitimate vehicles and cannot detect the real identities of the attackers. To overcome this attack, a central validation authority (CVA) can be deployed to validate the entities in real time. The process of validation can be direct or indirect: for the direct one, any incoming node should authenticate itself with the CVA by establishing a direct connection. On the other hand, indirect validation enables an already authenticated entity to accept an incoming entity. The certificates that are used by the CVA are generally temporary [17]. Moreover, the authentication process should be further strengthened by using distance bounding protocols, such as the bit commitment and zero-knowledge methods [59]. Furthermore, other solutions to Sybil attacks consist of validating unknown nodes with the method of secure location verification [60];
- Malware attacks: Malware attacks consist of virus, worms and Trojan horses that can affect the vehicular network [51], as well as the software components of the OBU and RSUs [17,18]. Such attacks can lead to dangerous consequences for ITS systems and can be mitigated by using anti-virus and anti-malware software. However, modern polymorphic and/or metamorphic malware can transform their structures and properties during the replication phase, thus making their detection much more difficult [61]. The typical cryptographic countermeasure consists of signing software updates and to verify them prior to their installation by the ECUs and OBUs;
- Spamming attacks: The main goal of spamming attacks is to consume the network bandwidth and to introduce a high latency in the network, by sending spamming messages (e.g., advertisement messages) to a group of users. The control of this type of message is more difficult [18,51], due to the lack of centralized infrastructure [62];
- Black hole attacks: The black hole attack exists in any kind of ad hoc network, including ITS, and is considered as a conventional attack against availability. In fact, a black hole is formed within the network when malicious nodes fail or refuse to propagate messages. The black hole attack means that the malicious node indicates that it is part of the network and is able to participate, while this is not the practical case [17,51]. This kind of attack is very dangerous for several ITS applications, especially for latency-sensitive road safety applications;
- Gray hole attacks: The gray hole attack is considered a variant of the black hole attack and consists of dropping the data packets related to specific ITS applications [63] during the routing process;
- Sink hole attacks: The sink hole attack can be used to prepare other attacks, such as gray hole and black hole attacks. In this attack, the packets of neighboring nodes are transmitted through malicious nodes, which can lead to eliminating or modifying the received packets before re-transmitting them eventually;
- Worm hole attacks: The worm hole attack is a DoS attack that requires the participation of at least two nodes, where an attacker ‘A’ sends a message to an attacker ‘B’, who is geographically far from him. This message suggests to neighboring nodes of ‘B’ that ‘A’ is their neighbor [64]. This attack allows two or more legitimate nodes and non-neighbors to exchange control packets between them [65] and to create non-existent routes;
- Tunneling attacks: The tunneling attack is similar to the worm hole attack [51] with the minor difference that it uses the same network to establish a private connection (or tunnel). It aims at connecting two distant parts of the vehicular network by using an additional communication channel, such as a hidden tunnel [66]. Thus, the victims of two distant parts of the network can communicate as neighbors.
4.4.2. Attacks on Authenticity/Identification and Countermeasures
- Falsified entities attacks: In the falsified entities attack, the attacker obtains a valid identifier and passes for another legitimate node. This constitutes a violation of the authentication process. Every ITS entity has a network identifier, which allows distinguishing it from the other nodes of the ITS system [17]. For example, rogue access points (AP) can be deployed along the roads to mimic legitimate RSUs and to launch attacks on the associated users and vehicles [67]. This attack can be prevented by implementing proper authentication mechanisms, for example by using a public key infrastructure, where each ITS entity is associated with a valid certificate, which is signed by the ITS authority;
- Cryptographic replication attacks: In this kind of attack, keys and/or certificates are duplicated to create ambiguity. This can prevent the authorities from identifying a vehicle, especially in the case of a dispute. The first countermeasure consists of the use of certified and disposable keys to resist these attacks. Another solution is the real-time verification of the certificate validity through a certificate revocation list (CRL) [47,68]. However, this solution is challenging in the context of ITS, since it requires cross-certification trusts between the different certification authorities involved in the ITS security scheme [68];
- GNSS spoofing and injection attacks: In ITS, position information is of crucial importance and must be accurate and authentic [18]. Such information is generally obtained from Global Navigation Satellite Systems (GNSS). In this context, the GNSS spoofing and injection attack is considered as the most dangerous threat on cooperative ITS [15]. It consists of providing the neighboring vehicles with false location information. The exact location information is generally obtained from a GPS system. Each vehicle is equipped with a GPS receiver, then the attack can be achieved using a transmitter generating localization signals stronger than those generated by the real GPS satellites [17,69]. The successful GPS spoofing attack can facilitate other attacks, such as attacks against location-based identification methods. This attack can be prevented by using bit commitment and signature schemes with positioning systems that accept only authentic location data [59,70];
- Timing attacks: In ITS safety applications, the timely delivery/reception of safety messages is of prime importance to ensure the safety of drivers and passengers. In this context, the timing attack consists of delaying the transmission of latency-sensitive messages so that the safety requirements are not achieved [71]. This attack can be enabled by forcing legitimate ITS entities to transmit their messages through a malicious node or tunnel, which will delay the reception of these messages by the other legitimate entities. The most common countermeasure consists of time-stamping the delay-sensitive packets at the cost, however, of more complex time synchronization mechanisms.
4.4.3. Attacks on Integrity/Data Trust and Countermeasures
- Masquerading attacks: This kind of attack is hidden, uses a valid identity (known as a mask) to ensure that it has the appearance of an authentic node, tries to produce false messages and broadcasts them to neighbor vehicles in order to attain specific objectives, for example to slow down the speed of a vehicle. A malicious node attempts to act as an emergency vehicle and, thus, cheats the other vehicles. To overcome this attack, a certificate revocation list (CRL) is used to maintain the identities of the detected malicious vehicles, which is furthermore distributed to the overall nodes within the ITS network. Even though this solution can reduce the effects of the masquerading attack [47], it requires the implementation of an efficient malicious nodes detection technique;
- Data playback attacks: This attack consists of replaying (broadcasting) a previously transmitted message [73], for example to manipulate the vehicle location and/or the nodes’ routing tables [51]. To provide robustness against this kind of attack, a cache can be implemented at the OBUs and RSUs stations to compare the recently received messages with the oldest ones in order to reject the duplicated messages (e.g., based on sequence numbers or timestamping information). Moreover, secure session tokens can be generated to uniquely identify a communication session between two legitimate entities, and nonces (i.e., a random number used only once in cryptographic systems) can be exploited to ensure that each message is processed only once;
- Data alteration attacks: This kind of attack consists of breaking the integrity of the exchanged messages by modifying, deleting, constructing or altering their content [66]. Additionally, it can affect the availability and the non-repudiation services. The attacker falsifies received messages to achieve its own benefits by leading the driver to change the decision, such as by indicating that a given route is congested or not. Another dangerous threat consists of the injection of false safety messages, thus impacting the safety of the drivers and vehicles [15]. Several techniques can be employed to overcome this threat, such as vehicular public key infrastructure (VPKI) or zero-knowledge to ensure the authentication between vehicles and for signing ITS messages [74,75]. Another efficient method consists of establishing group communications, as discussed in [75,76], where the keys can be managed by a group key management (GKM) system [77]. This means that an intruder should not be able to communicate with the group members;
- Map database poisoning attacks: Based on the exchanged messages (e.g., broadcast safety messages), each OBU builds and maintains a local map database to keep track of all surrounding vehicles, events and points of interest. This attack consists of sending malicious messages to impact the accuracy of the local map databases of ITS entities and, thus, to impact the safety of ITS applications and users. The main countermeasure consists of verifying the signatures of the received messages and detecting and blacklisting the misbehaving nodes;
- Data tampering attacks: This attack can be realized by a legitimate node, can destroy the network and causes dangerous consequences, such as accidents [51], by fabricating and broadcasting false messages. Its mechanism consists of hiding the true safety messages to legitimate users and tries to generate and inject fake security alert messages in the network. The main countermeasure is to sign and verify the transmitted messages. A non-repudiation mechanism is also required to detect the attacker identity, which should be added to the CRLs [51];
- Man-in-the-middle attacks: The man-in-the-middle attack can be achieved in several contexts. As its name indicates, the attacker is inserted between the transmitter and the receiver. In the case of ITS, the attacker can be an OBU or RSU, which is inserted between two vehicles that communicate. The attacker controls the communication between the two victims [17], while they believe that they are in direct communication with each other. In the literature, the man-in-the-middle attack is used to violate the authentication, integrity and non-repudiation mechanisms. A typical cryptographic countermeasure consists of using digital certification to properly authenticate the legitimate users [78].
4.4.4. Attacks on Confidentiality and Countermeasures
- Eavesdropping attacks: An eavesdropping attack affects only the network confidentiality and does not impact the network resources and availability [18]. This kind of attack enables the attacker to extract sensitive information from the transmitted packets, such as the location information of the vehicles. To provide resistance against this kind of attack, all sensitive data that have crucial importance should be encrypted so as to ensure the privacy of the involved ITS entities and their communications;
- Data interception attacks: This attack affects the user privacy in addition to confidentiality. This attack is dangerous and consists of listening to the network for a certain duration and then tries to analyze the collected traffic data to extract the maximum amount of useful information. The same countermeasure that permits providing resistance to eavesdropping can be adopted to resist traffic analysis attacks;
- Brute force attacks: The brute force attack can be performed against the confidentiality of exchanged messages or the authentication process. For example, this attack can reveal the network identifier of the vehicle by using an extensive dictionary search approach. However, due to the dynamic nature of the ITS network, connection times are relatively short, and hence, a brute force attack is not easy to conduct, since it is time consuming and resource intensive. Furthermore, this attack can become harder when using stronger encryption and key generation algorithms [51].
4.4.5. Attacks on Privacy and Countermeasures
4.4.6. Attacks on Non-Repudiation/Accountability and Countermeasures
4.5. ITS Security Architectures
- PKI-based security architectures: Public key infrastructure-based architectures rely on asymmetric encryption/decryption algorithms to provide several security services, such as certificates generation, renewal and revocation, signing and issuing, checking and auditing. A certificate provided by a PKI aims to link a public key with the owner’s identification and encryption technology. PKI requires the use of a certificate revocation list (CRL) in order to ensure safe and secure management in real network environments. This requirement can be considered as a critical problem and introduces high communication overhead. A detailed list of recent PKI-based security schemes and their evaluation in terms of communication overheads are presented in [84];
- Crypto-based security architectures: Crypto-based approaches are generally based on symmetric and asymmetric security algorithms to provide several security services. For instance, [85] provides a novel ITS security scheme that can provide privacy, data confidentiality and integrity and non-repudiation by using symmetric block cipher algorithm and a certificate-based public key cryptography scheme. The privacy and data confidentiality is ensured by employing the robust block cipher Advanced Encryption Standard (AES) [86];
- ID-based security architectures: In order to cancel the overhead of CRL- and PKI-based approaches, ID-based security architectures can be adopted, in which an encryption algorithm is employed for the generation of pseudonyms. ID-based security method aims to guarantee ID privacy, a precondition for the protection of user safety and privacy. The key point lies in generating irreversible algorithm for pseudonyms based on an ID with firm confirmation that only one pseudonym is available within the same entity to prevent Sybil attacks. Indeed, [87] employs ID-based encryption for pseudonym generation and conducts control of signature and identify authentication through a threshold scheme to satisfy security and privacy requirements. ID-based encryption is also used by [88] to ensure robust and secure V2I, V2V and I2V authentication processes. Finally, ID-based encryption can also be employed to generate the public keys from the entities identifiers [89], reducing thus the overhead of PKI-based solutions.
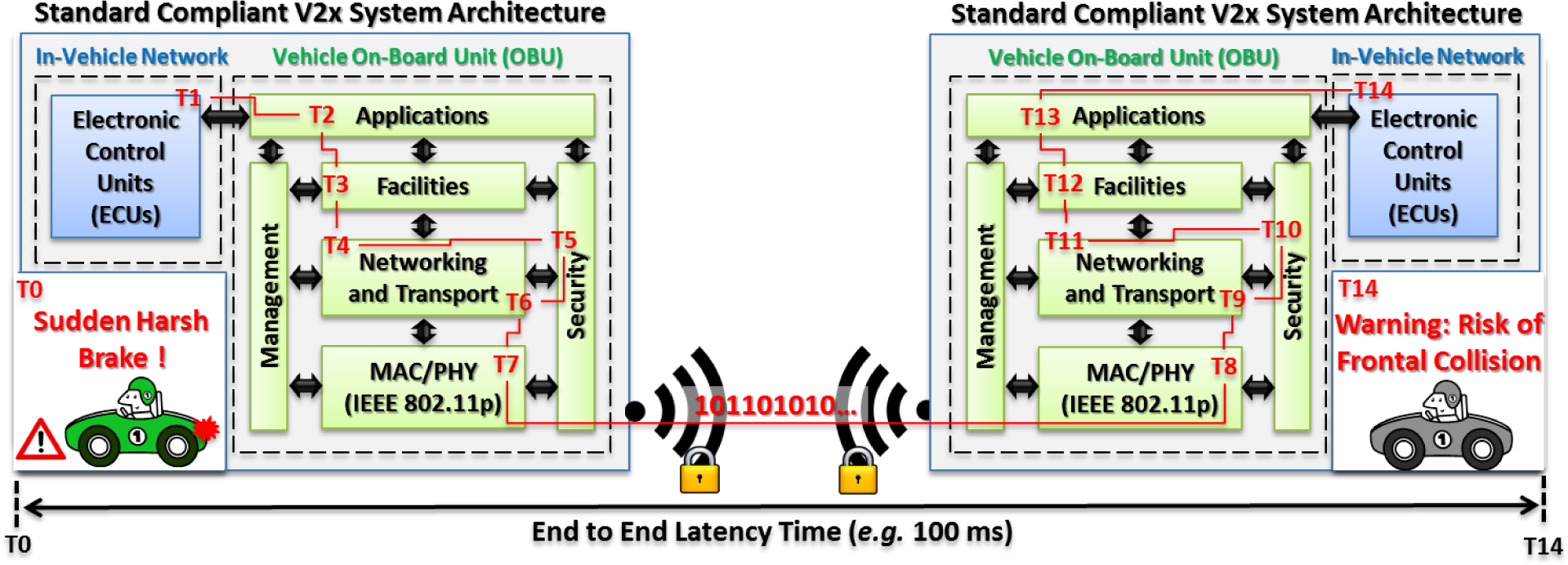
5. Securing ITS Applications: A Practical Case Study
5.1. ETSI TC ITS V2X Reference Architecture
5.2. The Collision Risk Warning Application Case Study
- At time T0, a vehicle (on the left side) performs a sudden and harsh braking due to a detected hazard;
- At time T1, the information related to this harsh braking event is available at the in-vehicle’s ECUs;
- At time T2, this information is received by the vehicle’s OBU by the corresponding ITS application;
- At time T3, a DENM message is built at the facilities layer, including all of the required information (e.g., timestamp, location, speed, event-type, etc.);
- At time T4, the DENM message is received and processed by the networking and transport layer;
- At time T5, the DENM message is signed by the security layer using an elliptic curve digital signature algorithm (ECDSA) [12] and is encapsulated (Encap) into a secured message, which includes the certificate of the ITS station;
- At time T6, the signed DENM message is received again by the networking layer and is queued;
- At time T7, the packet is transmitted over the air by the IEEE 802.11p MAC and PHY layers. Eventually, the packet might be re-transmitted multiple times due to collisions and/or harsh propagation conditions at the PHY layer;
- At time T8, the packet is finally received by a neighbor vehicle’s OBU (vehicle on the right side of Figure 2);
- From time T9 to T13, the message undergoes the reverse flow, i.e., the message is decapsulated (Decap) and verified (using ECDSA) by the security layer and is made available to the ITS application layer at time T13;
- At time T14, a warning message is displayed to the vehicle’s driver for taking immediate action or an automatic action is triggered by the vehicle’s ECUs (e.g., emergency brake, speed reduction, etc.).
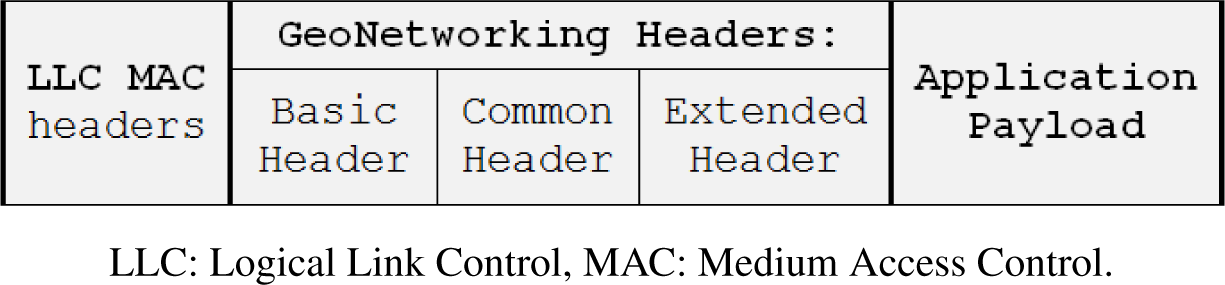
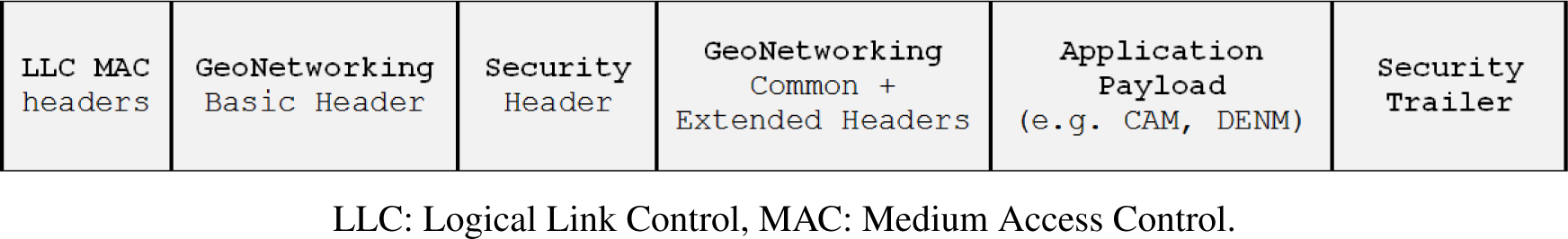
5.3. ETSI Security Layer: TS 103 097
5.3.1. Security Headers
 |
5.3.2. Certificate Format
 |
5.3.3. Security Profiles
- A message digest is computed using a Secure Hash Algorithm (SHA) with a 256 bits block size (i.e., SHA-256) over the protocol_version, header_fields, payload_field, the length of the trailer_fields and the type of the signature trailer field;
- The message digest is then signed using ecdsa_nistp256_with_sha256 and the private key of the ITS station certificate;
- The signer information and the generated signature are stored inside the signer_info and signature structures, respectively.
- The content of the SecuredMessage is checked against the rules of the corresponding security profile;
- The certificate is validated against timing, location and security considerations; in case the signer’s certificate is unknown, a request_unrecognized_certificate is generated;
- The signature of the message is checked using the same steps as in the signature process.
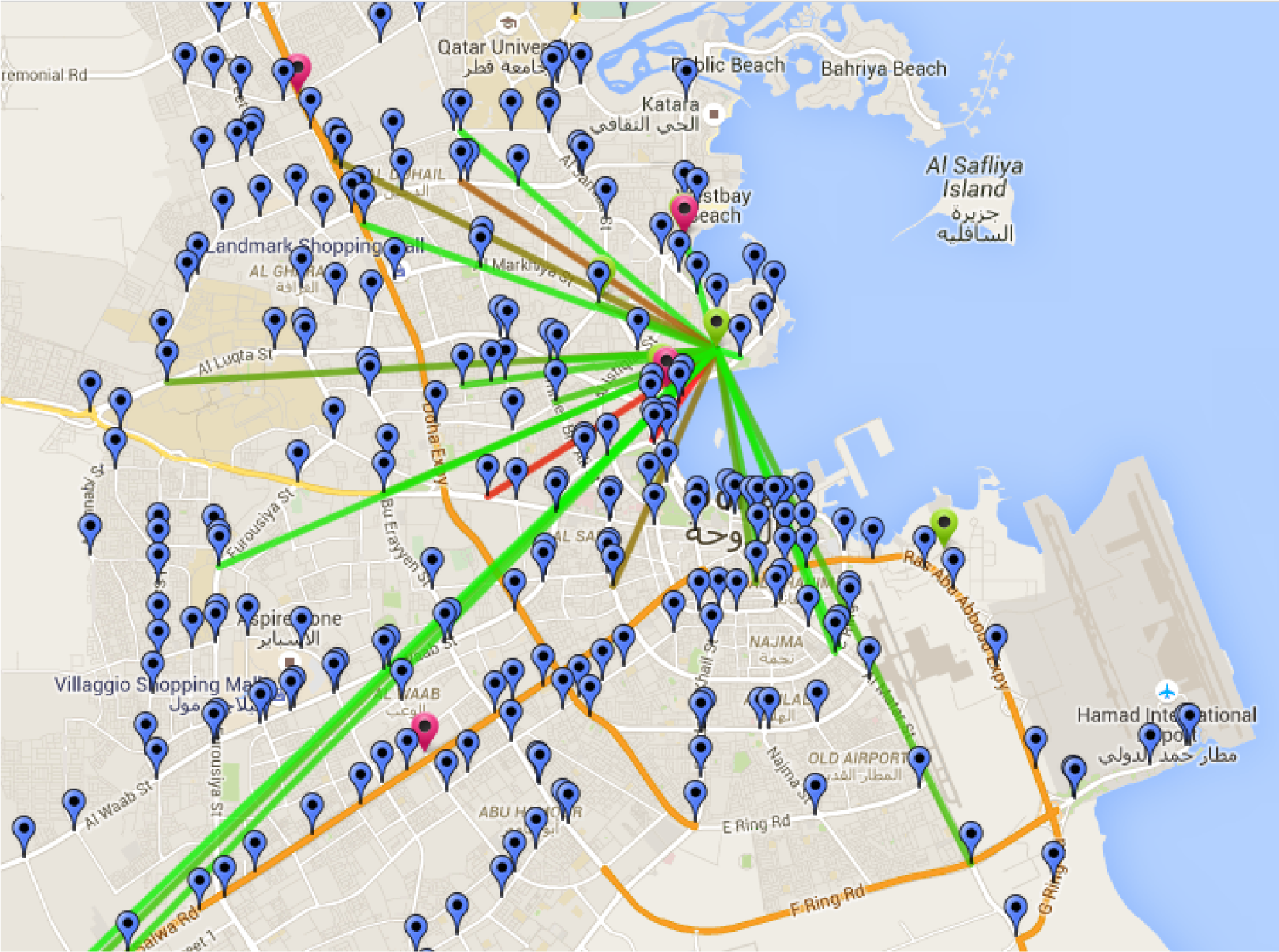
5.4. Test-Bed Platform
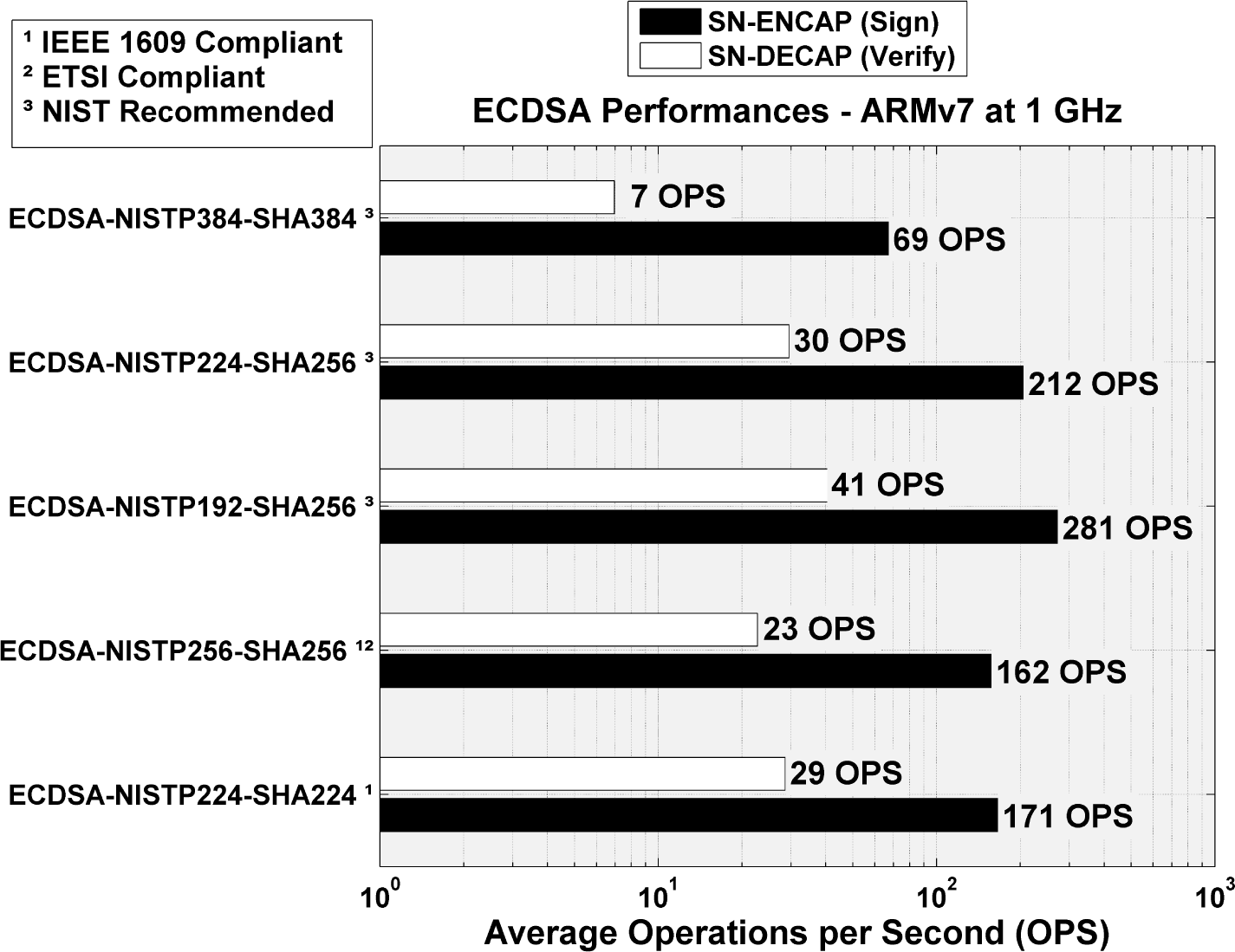
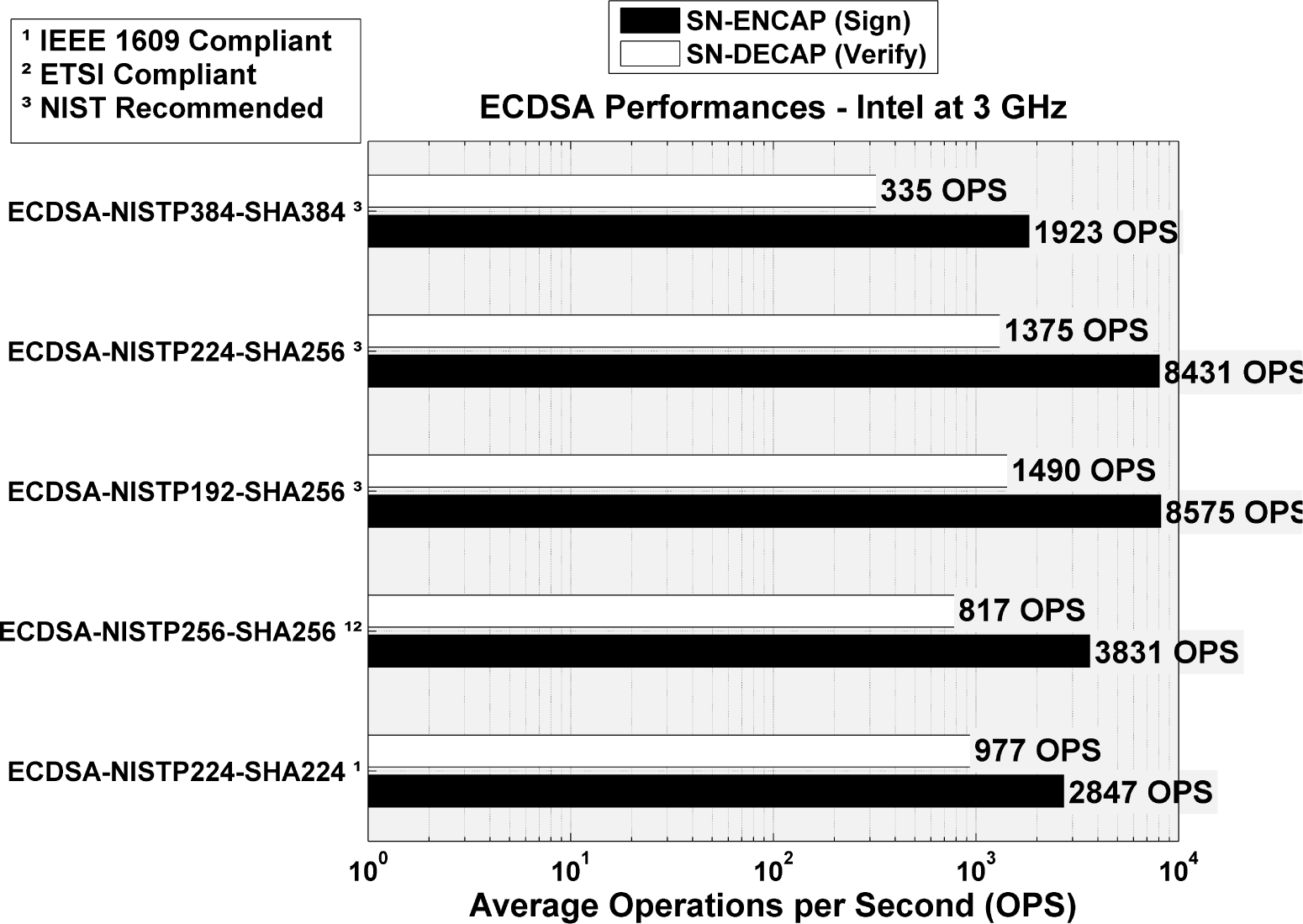
5.5. Experimental Results
5.6. Lessons Learned
6. Research Challenges and Opportunities
7. Conclusions
Acknowledgments
Author Contributions
Conflicts of Interest
References
- International Energy Agency. How Many Cars Will Be on the Planet in the Future? Available online: http://www.iea.org/aboutus/faqs/transport/ accessed on 21 May 2015.
- World Health Organization (WHO). Global Status Report on Road Safety 2013; Technical Report; World Health Organization (WHO): Geneva, Switzerland, 2013. [Google Scholar]
- Automobile Association of America. Cost of Auto Crashes and Statistics. Available online: http://www.rmiia.org/auto/traffic_safety/Cost_of_crashes.asp accessed on 21 May 2015.
- GSM Association (GSMA). Connected Car Forecast: Global Connected Car Market to Grow Threefold within Five Years; Technical Report; GSM Association (GSMA): London, UK, 2013. [Google Scholar]
- Sharef, B.T.; Alsaqour, R.A.; Ismail, M. Vehicular communication ad hoc routing protocols: A survey. J. Netw. Comput. Appl. 2014, 40, 363–396. [Google Scholar]
- Da Cunha, F.D.; Boukerche, A.; Villas, L.; Viana, A.C.; Loureiro, A.A.F. Data Communication in VANETs: A Survey, Challenges and Applications; Technical Report RR-8498; INRIA Saclay: Palaiseau, France, 2014. [Google Scholar]
- IEEE Guide for Wireless Access in Vehicular Environments (WAVE)—Architecture. IEEE Std. 1609.0-2013 2014, 1–78. [CrossRef]
- Part 11: Wireless LAN Medium Access Control (MAC) and Physical Layer (PHY) Specifications Amendment 6: Wireless Access in Vehicular Environments. IEEE 802.11p Publ. Stand. 2010, 1–51. [CrossRef]
- IEEE Standard for Information Technology—Telecommunications and Information Exchange between Systems-Local and Metropolitan Area Networks-Specific Requirements-Part 11: Wireless LAN Medium Access Control (MAC) and Physical Layer (PHY) Specifications. IEEE Std 802.11-2012 1997, 1–2793. [CrossRef]
- ETSI—Intelligent Transport Systems. Available online: http://www.etsi.org/technologies-clusters/technologies/intelligent-transport accessed on 21 May 2015.
- Festag, A. Cooperative intelligent transport systems standards in europe. IEEE Commun. Mag. 2014, 52, 166–172. [Google Scholar]
- Pietro, R.D.; Guarino, S.; Verde, N.; Domingo-Ferrer, J. Security in wireless ad-hoc networks—A survey. Comput. Commun. 2014, 51, 1–20. [Google Scholar]
- Mejri, M.N.; Ben-Othman, J.; Hamdi, M. Survey on VANET security challenges and possible cryptographic solutions. Veh. Commun. 2014, 1, 53–66. [Google Scholar]
- Engoulou, R.G.; Bellaiche, M.; Pierre, S.; Quintero, A. VANET security surveys. Comput. Commun 2014, 44, 1–13. [Google Scholar]
- Petit, J.; Shladover, S. Potential Cyberattacks on Automated Vehicles. IEEE Trans. Intell. Transp. Syst. 2015, 16, 546–556. [Google Scholar]
- Vinoth Kumar, P.; Maheshwari, M. Prevention of Sybil attack and priority batch verification in VANETs, Proceedings of the 2014 International Conference on Information Communication and Embedded Systems (ICICES), Chennal, India, 27–28 February 2014; pp. 1–5.
- Al-kahtani, M. Survey on security attacks in Vehicular Ad hoc Networks (VANETs), Proceedings of the 2012 6th International Conference on Signal Processing and Communication Systems (ICSPCS), Gold Coast, Australia, 12–14 December 2012; pp. 1–9.
- Dhamgaye, A.; Chavhan, N. Survey on security challenges in VANET. Int. J. Comput. Sci. Netw. 2013, 2, 88–96. [Google Scholar]
- Checkoway, S.; McCoy, D.; Kantor, B.; Anderson, D.; Shacham, H.; Savage, S.; Koscher, K.; Czeskis, A.; Roesner, F.; Kohno, T. Comprehensive Experimental Analyses of Automotive Attack Surfaces; USENIX Security: San Francisco, CA, USA, 2011. [Google Scholar]
- Woo, S.; Jo, H.J.; Lee, D.H. A Practical Wireless Attack on the Connected Car and Security Protocol for In-Vehicle CAN. IEEE Trans. Intell. Transp. Syst. 2015, 16, 993–1006. [Google Scholar]
- Amoozadeh, M.; Raghuramu, A.; Chuah, C.N.; Ghosal, D.; Zhang, H.; Rowe, J.; Levitt, K. Security vulnerabilities of connected vehicle streams and their impact on cooperative driving. IEEE Commun. Mag. 2015, 53, 126–132. [Google Scholar]
- Nowdehi, N.; Olovsson, T. Experiences from implementing the ETSI ITS SecuredMessage service, Proceedigns of the 2014 IEEE Intelligent Vehicles Symposium Proceedings, Dearborn, Michigan, USA, 8–11 June 2014; pp. 1055–1060.
- Moalla, R.; Lonc, B.; Segarra, G.; Laguna, M.; Papadimitratos, P.; Petit, J.; Labiod, H. Experimentation with the PRESERVE VSS and the Score@F System, Proceedings of the 5th Conference on Transport Research Arena (TRA), Paris, France, 14–17 April 2014.
- ETSI TS 103 097 V1.2.1 (2015–06)—Intelligent Transport Systems (ITS); Security; Security Header and Certificate Formats. Available online: http://www.etsi.org/deliver/etsi_ts/103000_103099/103097/01.02.01_60/ts_103097v010201p.pdf accessed on 14 June 2015.
- Moustafa, H.; Zhang, Y. Vehicular Networks: Techniques, Standards, and Applications; Auerbach Publications; Boca Raton, FL, USA, 2009. [Google Scholar]
- Cheng, H.T.; Shan, H.; Zhuang, W. Infotainment and road safety service support in vehicular networking: From a communication perspective. Mech. Syst. Signal Process. 2011, 25, 2020–2038. [Google Scholar]
- Raw, R.S.; Kumar, M.; Singh, N. Security Challenges, Issues and Their Solutions for VANET. Int. J. Netw. Secur. Its Appl. 2013, 5, 95–105. [Google Scholar] [CrossRef]
- Al-Sultan, S.; Al-Doori, M.M.; Al-Bayatti, A.H.; Zedan, H. A comprehensive survey on vehicular Ad Hoc network. J. Netw. Comput. Appl. 2014, 37, 380–392. [Google Scholar]
- Bhoi, S.; Khilar, P. Vehicular communication: A survey. IET Netw. 2014, 3, 204–217. [Google Scholar]
- Lebre, M.A.; Mouel, F.L.; Menard, E.; Dillschneider, J.; Denis, R. VANET Applications: Hot Use Cases. 2014, pp. 1–36. Available online: https://hal.inria.fr/hal-01024271 access on 6 July 2015.
- Jadranka, D.; Beate, M.; Gereon, M. European Roadmap Smart Systems for Automated Driving; Technical Report Version 1.2; European Technology Platform on Smart Systems Integration (EPoSS): Berlin, Germany, 2015. [Google Scholar]
- Rezgui, J.; Cherkaoui, S.; Chakroun, O. Deterministic access for dsrc/802.11 p vehicular safety communication, Proceedings of the 2011 7th International Wireless Communications and Mobile Computing Conference (IWCMC), Istanbul, Turkey, 4–8 July 2011; pp. 595–600.
- 1609 WG—Dedicated Short Range Communication Working Group. IEEE Standards Development Working Group. Available online: http://standards.ieee.org/develop/wg/1609_WG.html accessed on 21 May 2015.
- Open Vehicular Secure Platform (OVERSEE). Available online: https://www.oversee-project.com/ accessed on 21 May 2015.
- E-Safety Vehicle Intrusion Protected Applications (EVITA. Available online: http://www.evita-project.org/ accessed on 21 May 2015.
- Privacy Enabled Capability in Co-operative Systems and Safety Applications (PRECIOSA). Available online: http://www.transport-research.info/web/projects/project_details.cfm?id=44532 accessed on 21 May 2015.
- Intellidrive for Safety, Mobility, and User Fee Project: Driver Performance and Distraction Evaluation. Available online: http://www.its.umn.edu/Research/ProjectDetail.html?id=2011091 accessed on 21 May 2015.
- Cooperative Systems for Road Safety—Smart Vehicles on Smart Roads (SAFESPOT). Available online: http://www.safespot-eu.org/ accessed on 21 May 2015.
- Secure Vehicular Communication EU Funded Project. Available online: http://cordis.europa.eu/project/rcn/80592_en.html accessed on 21 May 2015.
- Cooperative Cars and Roads for Safer and Intelligent Transportation Systems (CopITS). Available online: http://www.copits.org accessed on 21 May 2015.
- Communications for eSafety (COMeSafety2). Available online: http://www.comesafety.org accessed on 21 May 2015.
- Preparing Secure Vehicle-to-X Communication Systems (PRESERVE). Available online: http://www.preserve-project.eu accessed on 21 May 2015.
- Advanced Cellular Technologies for Connected Cars (CellCar). Available online: http://www.cellcar.org accessed on 21 May 2015.
- Cooperative Systems for Smart Mobility Services and Solutions (CosMob). Available online: http://www.cosmob.org accessed on 21 May 2015.
- Security and Safety Modelling (SESAMO). Available online: http://www.sesamo-project.eu accessed on 21 May 2015.
- Engineering Security and Performance Aware Vehicular Applications for Safer and Smarter Roads (SafeITS). Available online: http://www.safeits.org accessed on 21 May 2015.
- Raya, M.; Hubaux, J.P. Securing vehicular ad hoc networks. J. Comput. Secur. 2007, 15, 39–68. [Google Scholar]
- Vighnesh, N.; Kavita, N.; Urs, S.R.; Sampalli, S. A novel sender authentication scheme based on hash chain for Vehicular Ad-Hoc Networks, Proceedings of the 2011 IEEE Symposium on Wireless Technology and Applications (ISWTA), Langkawi, Malaysia, 25–28 September 2011; pp. 96–101.
- Sabahi, F. The Security of Vehicular Adhoc Networks, Proceedings of the 2011 Third International Conference on Computational Intelligence, Communication Systems and Networks (CICSyN), Bali, Indonesia, 26–28 July 2011; pp. 338–342.
- Intelligent Transport Systems (Its), Security, Threat, Vulnerability and Risk Analysis (TVRA); Technical Report ETSI TR 102 893 V1.1.1; ETSI: Sophia Antipolis, France, 2010. Available online: http://www.etsi.org/deliver/etsi_tr/102800_102899/102893/01.01.01_60/tr_102893v010101p.pdf accessed on 6 July 2015.
- Zeadally, S.; Hunt, R.; Chen, Y.S.; Irwin, A.; Hassan, A. Vehicular ad hoc networks (VANETS): status, results, and challenges. Telecommun. Syst. 2012, 50, 217–241. [Google Scholar]
- Mirkovic, J.; Reiher, P. A taxonomy of DDoS attack and DDoS defense mechanisms. ACM SIGCOMM Comput. Commun. Rev. 2004, 34, 39–53. [Google Scholar]
- Tengstrand, S.; Fors, K.; Stenumgaard, P.; Wiklundh, K. Jamming and interference vulnerability of IEEE 802.11p, Proceedings of the 2014 International Symposium on Electromagnetic Compatibility (EMC Europe), Gothenburg, Sweden, 1–4 September 2014; pp. 533–538.
- Sumra, I.A.; Ahmad, I.; Hasbullah, H.; bin Ab Manan, J.L. Classes of attacks in VANET, Proceedings of the 2011 Saudi International Electronics, Communications and Photonics Conference (SIECPC), Riyadh, Saudi Arabia, 24–26 April 2011; pp. 1–5.
- Hamieh, A.; Ben-Othman, J.; Mokdad, L. Detection of radio interference attacks in VANET, Proceedings of the Global Telecommunications Conference (GLOBECOM), Honolulu, Hawaii, USA, 2009; pp. 1–5.
- Malla, A.M.; Sahu, R.K. Security attacks with an effective solution for DoS attacks in VANET. Int. J. Comput. Appl. 2013, 66, 45–49. [Google Scholar]
- RoselinMary, S.; Maheshwari, M.; Thamaraiselvan, M. Early detection of DoS attacks in VANET using attacked packet detection algorithm (apda), Proceedings of the 2013 International Conference on Information Communication and Embedded Systems (ICICES), Tamilnadu, India, 21–22 February 2013; pp. 237–240.
- Shrivastava, D.; Pandey, A. others. A Study of Sybil and Temporal Attacks in Vehicular Ad Hoc Networks: Types, Challenges, and Impacts. Int. J. Comput. Appl. Technol. Res. 2014, 3, 284–291. [Google Scholar]
- Wolf, M. Vehicular security mechanisms. In Security Engineering for Vehicular IT Systems; Springer: Wiesbaden, Germany, 2009; pp. 121–165. [Google Scholar]
- Xiao, B.; Yu, B.; Gao, C. Detection and localization of sybil nodes in VANETs, Proceedings of the 2006 Workshop on Dependability Issues in Wireless ad Hoc Networks and Sensor Networks, Los Angeles, CA, USA, 29 September 2006; ACM: New York, NY, USA, 2006; pp. 1–8.
- Zhang, T.; Antunes, H.; Aggarwal, S. Defending Connected Vehicles Against Malware: Challenges and a Solution Framework. IEEE Internet Things J 2014, 1, 10–21. [Google Scholar]
- Sumra, I.A.; Hasbullah, H.; Ahmad, I.; bin Ab Manan, J.L. Forming vehicular web of trust in VANET, Proceedings of the Saudi International Electronics, Communications and Photonics Conference (SIECPC), Riyadh, Saudi Arabia, 24–26 April 2011; pp. 1–6.
- Nogueira, M.; Silva, H.; Santos, A.; Pujolle, G. A security management architecture for supporting routing services on WANETs. IEEE Trans. Netw. Serv. Manag. 2012, 9, 156–168. [Google Scholar]
- Sedjelmaci, H.; Senouci, S. A new Intrusion Detection Framework for Vehicular Networks, Proceedings of the 2014 IEEE International Conference on Communications (ICC), Clayton, Australia, 10–14 June 2014; pp. 538–543.
- Safi, S.M.; Movaghar, A.; Mohammadizadeh, M. A novel approach for avoiding wormhole attacks in VANET, Proceedings of the First Asian Himalayas International Conference on Internet (AH-ICI 2009), Kathmundu, Nepal, 3–5 November 2009; pp. 1–6.
- Rawat, A.; Sharma, S.; Sushil, R. VANET: Security attacks and its possible solutions. J. Inf. Oper. Manag. 2012, 3, 301–304. [Google Scholar]
- Han, H.; Xu, F.; Tan, C.; Zhang, Y.; Li, Q. VR-Defender: Self-Defense Against Vehicular Rogue APs for Drive-Thru Internet. IEEE Trans. Veh. Technol. 2014, 63, 3927–3934. [Google Scholar]
- Raya, M.; Papadimitratos, P.; Hubaux, J.P. Securing Vehicular Communications. IEEE Wirel. Commun. 2006, 13, 8–15. [Google Scholar]
- Warner, J.S.; Johnston, R.G. GPS spoofing countermeasures. Homel. Secur. J. 2003, pp. 1–8. Available online: http://permalink.lanl.gov/object/tr?what=info:lanl-repo/lareport/LA-UR-03-6163 accessed on 6 July 2015.
- He, L.; Zhu, W.T. Mitigating DoS attacks against signature-based authentication in VANETs, Proceedings of the 2012 IEEE International Conference on Computer Science and Automation Engineering (CSAE), Zhangjiajie, China, 25–27 May 2012; 3, pp. 261–265.
- Sumra, I.A.; Ab Manan, J.L.; Hasbullah, H. Timing attack in vehicular network, Proceedings of the 15th WSEAS International Conference on Computers, World Scientific and Engineering Academy and Society (WSEAS), Corfu Island, Greece, 2011; pp. 151–155.
- Fuentes, J.M.d.; González-Tablas, A.I.; Ribagorda, A. Overview of security issues in Vehicular Ad-hoc Networks. In Handbook of Research on Mobility and Computing; IGI Global: Hershey, PA, USA, 2010. [Google Scholar]
- Mikki, M.; Mansour, Y.; Yim, K. Privacy Preserving Secure Communication Protocol for Vehicular Ad Hoc Networks, Proceedings of the 2013 Seventh International Conference on Innovative Mobile and Internet Services in Ubiquitous Computing (IMIS), Taichung, Taiwan, 3–5 July 2013; pp. 188–195.
- Blum, J.; Eskandarian, A. The threat of intelligent collisions. IT Prof. 2004, 6, 24–29. [Google Scholar]
- Domingo-Ferrer, J.; Wu, Q. Safety and privacy in vehicular communications. In Privacy in Location-Based Applications; Springer: Berlin, Germany, 2009; pp. 173–189. [Google Scholar]
- Kaushik, S.S. Review of different approaches for privacy scheme in VANETs. Int. J. Adv. Eng. Technol. 2013, 5, 2231–1963. [Google Scholar]
- Sharma, S.; Krishna, C. An Efficient Distributed Group Key Management Using Hierarchical Approach with Elliptic Curve Cryptography, Proceedings of the 2015 IEEE International Conference on Computational Intelligence Communication Technology (CICT), Ghaziabad U.P., India, 13–14 February 2015; pp. 687–693.
- Varshney, N.; Roy, T.; Chaudhary, N. Security protocol for VANET by using digital certification to provide security with low bandwidth, Proceedings of the 2014 International Conference on Communications and Signal Processing (ICCSP), Melmaruvathur, India, 3–5 April 2014; pp. 768–772.
- Pathan, A.S.K. Security of self-organizing networks: MANET, WSN, WMN, VANET; CRC Press: Boca Raton, FL, USA, 2010. [Google Scholar]
- Badra, M.; Hamida, E.B. A Novel Cryptography based Privacy Preserving Solution for Urban Mobility and Traffic Control, Proceedings of the 7th IFIP International Conference on New Technologies, Mobility and Security (NTMS 2015), New York, NY, USA, 27–29 July 2015.
- Priya, K.; Karuppanan, K. Secure privacy and distributed group authentication for VANET, Proceedings of the 2011 International Conference on Recent Trends in Information Technology (ICRTIT), Chennai, India, 3–5 July 2011; pp. 301–306.
- Armknecht, F.; Festag, A.; Westhoff, D.; Zeng, K. Cross-layer privacy enhancement and non-repudiation in vehicular communication, Proceedings of the 2007 ITG-GI Conference on Communication in Distributed Systems (KiVS), VDE, Bern, Switzerland, 26 February–2 March 2007; pp. 1–12.
- Li, Z.; Chigan, C. On Joint Privacy and Reputation Assurance for Vehicular Ad Hoc Networks. IEEE Trans. Mob. Comput. 2014, 13, 2334–2344. [Google Scholar]
- Kortesniemi, Y.; Särelä, M. Survey of certificate usage in distributed access control. Comput. Secur. 2014, 44, 16–32. [Google Scholar]
- Wang, N.W.; Huang, Y.M.; Chen, W.M. A novel secure communication scheme in vehicular ad hoc networks. Comput. Commun. 2008, 31, 2827–2837. [Google Scholar]
- Daemen, J.; Rijmen, V. AES proposal: Rijndael; Technical Report; National Institute of Standards and Technology: Gaithersburg, MD, USA, 2003. [Google Scholar]
- Karagiannis, G.; Altintas, O.; Ekici, E.; Heijenk, G.; Jarupan, B.; Lin, K.; Weil, T. Vehicular Networking: A Survey and Tutorial on Requirements, Architectures, Challenges, Standards and Solutions. IEEE Commun. Surv. Tutor. 2011, 13, 584–616. [Google Scholar]
- Lu, H.; Li, J.; Guizani, M. A novel ID-based authentication framework with adaptive privacy preservation for VANETs, Proceedings of the Computing, Communications and Applications Conference (ComComAp), Hong Kong, China, 11–13 January 2012; pp. 345–350.
- Sun, J.; Zhang, C.; Zhang, Y.; Fang, Y. An identity-based security system for user privacy in vehicular ad hoc networks. IEEE Trans. Parallel Distrib. Syst. 2010, 21, 1227–1239. [Google Scholar]
- Menouar, H.; Filali, F.; Abu-Dayya, A. Experimental evaluation of 5.9 GHz link asymmetry using standards-compliant implementation, Proceedings of the 2013 21st IEEE International Conference on Network Protocols (ICNP), Goettingen, Germany, 7–10 October 2013; pp. 1–6.
- IEEE Standard for Information technology—Local and metropolitan area networks—Specific requirements—Part 11: Wireless LAN Medium Access Control (MAC) and Physical Layer (PHY) Specifications Amendment 6: Wireless Access in Vehicular Environments. IEEE Std 802.11p-2010 (Amendment to IEEE Std 802.11-2007 as amended by IEEE Std 802.11k-2008, IEEE Std 802.11r-2008, IEEE Std 802.11y-2008, IEEE Std 802.11n-2009, and IEEE Std 802.11w-2009) 2010, 1–51. [CrossRef]
- IEEE Standard for Wireless Access in Vehicular Environments Security Services for Applications and Management Messages. IEEE Std. 1609.2-2013 (Revis. IEEE Std. 1609.2-2006) 2013, 1–289. [CrossRef]
- ETSI TS 102 941 V1.1.1—Intelligent Transport Systems (ITS); Security; Trust and Privacy Management; Technical Report; ETSI: Sophia Antipolis, France, 2012.
- Turner, S.; Brown, D.; Yiu, K.; Housley, R.; Polk, T. Elliptic Curve Cryptography Subject Public Key Information. Internet Eng. Task Force (IETF)—RFC 5480. 2009, pp. 1–20. Available online: https://tools.ietf.org/html/rfc5480 accessed on 6 July 2015.
- Nowdehi, N.; Olovsson, T. Experiences from implementing the ETSI ITS SecuredMessage service, Proceedings of the 2014 IEEE Intelligent Vehicles Symposium Proceedings, Dearborn, Michigan, USA, 8–11 June 2014; pp. 1055–1060.
- Moalla, R.; Lonc, B.; Segarra, G.; Laguna, M.; Papadimitratos, P.; Petit, J.; Labiod, H. Experimentation with the PRESERVE VSS and the Score@F System, Proceedings of the 5th Conference on Transport Research Arena (TRA), Paris, France, 14–17 April 2014.
- Fraunhofer FOKUS WebValidator for TS 103 097. Available online: https://werkzeug.dcaiti.tu-berlin.de/etsi/ts103097/ accessed on 21 May 2015.
- Draft ETSI TS 102 723-8 V1.0.4—Intelligent Transport Systems (ITS). In OSI Cross-Layer Topis; Part 8: Interface between Security Entity and Network and Transport Layer; Technical Report; ETSI: Sophia Antipolis, France, 2014.
- Bouncy Castle Crypto APIs. Available online: http://www.bouncycastle.org accessed on 21 May 2015.
- Monteiro, R.; Sargento, S.; Viriyasitavat, W.; Tonguz, O. Improving VANET protocols via network science, Proceedings of the 2012 IEEE Vehicular Networking Conference (VNC), Seoul, South Korea, 14–16 November 2012; pp. 17–24.
- Rocha, B.P.S.; Costa, D.N.O.; Moreira, R.A.; Rezende, C.G.; Loureiro, A.A.F.; Boukerche, A. Adaptive Security Protocol Selection for Mobile Computing. J. Netw. Comput. Appl. 2010, 33, 569–587. [Google Scholar]
- Yang, L.; Guo, J.; Wu, Y. Piggyback Cooperative Repetition for Reliable Broadcasting of Safety Messages in VANETs, Proceedings of the 6th IEEE Consumer Communications and Networking Conference (CCNC 2009), Las Vegas, Nevada, USA, 10–13 January 2009; pp. 1–5.
- Krishnan, H.; Weimerskirch, A. Verify-on-Demand—A Practical and Scalable Approach for Broadcast Authentication in Vehicle-to-Vehicle Communication. SAE Int. J. Passeng. Cars—Mech. Syst. 2011, 4, 536–546. [Google Scholar]
- Anaya, J.J.; Talavera, E.; Jimenez, F.; Gomez, N.; Naranjo, J.E. A Novel Geo-Broadcast Algorithm for V2V Communications over WSN. Electronics 2014, 3, 521–537. [Google Scholar]
- Yuan, E.; Malek, S.; Schmerl, B.; Garlan, D.; Gennari, J. Architecture-based Self-protecting Software Systems, Proceedings of the 9th International ACM Sigsoft Conference on Quality of Software Architectures (QoSA ’13), Vancouver, BC, Canada, 17–21 June 2013; pp. 33–42.



| Applications | Use Cases | Communication Modes | Radio Coverage | TX Frequency | Critical Latency |
|---|---|---|---|---|---|
| Active road safety | Intersection collision warning, Lane change assistance, etc. | Broadcasting, Cooperative messaging, etc. | From 300m to 20Km | 10Hz | ≤ 100ms |
| Traffic Efficiency and Management | Regulatory speed limit notification | Periodic/permanent message broadcast | From 300m to 5Km | 1–10Hz | – |
| Green light optimal speed advisory | 10Hz | ≤ 100ms | |||
| Cooperative Navigation | Electronic toll collection | Internet vehicle and unicast full duplex session | From 0m to 1Km | 1Hz | ≤ 200ms |
| Adaptive cruise control, Vehicle highway automatic system | Cooperation awareness | 2Hz | ≤ 100ms | ||
| Global Internet Services | Insurance and financial services, Fleet management, etc. | Access to Internet | From 0m to full range | 1Hz | ≤ 500ms |
| Cooperative Local Services | Point of interest notifications | Periodic/permanent message broadcast | From 0m to full range | 1Hz | ≤ 500ms |
| Electronic commerce | Full duplex communications | ||||
| Media downloading | Access to Internet |
| Characteristics | Vehicular Communication Technologies | ||
|---|---|---|---|
| 802.11p (WAVE) | 802.11 a/b/g/n (Wi-Fi) | Cellular (3G, LTE) | |
| Mode of operation | Ad hoc, Infrastructure | Ad hoc, Infrastructure | Infrastructure |
| Communication type | V2V, V2I | V2I | V2I |
| Bit rate | Up to 27 Mbps | Up to 54 Mbps | Up to 2 Mbps |
| Communication range | Up to 1000 m | Up to 100 m | Up to 15,000 m |
| Support for mobility | High | Low | High |
| Frequency bands | 5, 86 to 5.92 GHz | [2.4, 5.2] GHz | [800, 900, 1800, 1900] MHz |
| Channel bandwidth | [10, 20] MHz | 1 to 40 MHz | 25 MHz (GSM), 60 MHz (UMTS1) |
| Related standards | IEEE, ISO, ETSI | IEEE | ETSI, 3GPP2 |
| Security Requirement | Broadcast | Unicast | Security Mechanisms |
|---|---|---|---|
| Confidentiality | ✘ | ✓ | Encryption on sensitive messages; randomizing traffic patterns |
| Authenticity | ✓ | ✓ | Message signature Trusted hardware module; active detection systems |
| Integrity | ✓ | ✓ | Message signature and other integrity metrics for content delivery |
| Authorization | ✓ | ✓ | Certificate accompanying message signature |
| Non-repudiation of origin | ✓ | ✓ | Message signature |
| Non-repudiation of receipt | ✘ | ✘ | Not necessary |
| Anti-replay | ✓ | ✓ | Message signature containing verifiable time variant data |
| Plausibility verification | ✓ | ✓ | Check mechanisms ensured by IEEE P1609.2. |
| Availability | ✓ | ✓ | Pseudo-random frequency hopping Access control and signature-based authentication |
| Privacy | ✓ | ✓ | Pseudonymity, unlinkability ID-based system for user privacy |
| Compromised Security Services
| Availability | Authentication | Non-Repudiation | Integrity | Privacy | Confidentiality |
|---|---|---|---|---|---|---|
| Attacks | ||||||
| Denial of service attacks (DoS) | ✓ | |||||
| Jamming attack | ✓ | |||||
| Sybil attack | ✓ | ✓ | ||||
| Variants of DoS (greedy, Black hole, gray hole, sink hole Wormhole, malware, masquerading Spamming, tunneling) | ✓ | ✓ | ✓ | ✓ | ✓ | |
| Loss of event traceability | ✓ | |||||
| Illusion | ✓ | ✓ | ||||
| Replay | ✓ | ✓ | ||||
| Key and/or certificate replication | ✓ | ✓ | ||||
| GPS spoofing/position faking | ✓ | ✓ | ||||
| Message tampering/suppression/fabrication/alteration | ✓ | ✓ | ✓ | |||
| Broadcast tampering | ✓ | |||||
| Node impersonation | ✓ | ✓ | ✓ | |||
| Brute force | ✓ | |||||
| Eavesdropping | ✓ | |||||
| Traffic analysis | ✓ | ✓ | ||||
| Tracking/social engineering | ✓ | |||||
| Timing attack | ✓ | |||||
| Man in the middle attack | ✓ | ✓ | ✓ |
| Cryptographic Algorithms | Intel CPU at 1 GHz | Intel CPU at 3 GHz | ||
|---|---|---|---|---|
| SN-ENCAP | SN-DECAP | SN-ENCAP | SN-DECAP | |
| ecdsa_nistp192_with_sha256 | 3.56 ± 0.10 | 24.43 ± 0.23 | 0.12 ± 0.006 | 0.67 ± 0.014 |
| ecdsa_nistp224_with_sha224 | 5.84 ± 0.28 | 34.91 ± 0.46 | 0.35 ± 0.022 | 1.02 ± 0.048 |
| ecdsa_nistp224_with_sha256 | 4.73 ± 0.17 | 33.82 ± 0.33 | 0.12 ± 0.003 | 0.73 ± 0.013 |
| ecdsa_nistp256_with_sha256 | 6.17 ± 0.16 | 44.03 ± 0.31 | 0.26 ± 0.012 | 1.22 ± 0.047 |
| ecdsa_nistp384_with_sha384 | 14.55 ± 0.20 | 143.63 ± 0.5 | 0.52 ± 0.019 | 2.98 ± 0.036 |
© 2015 by the authors; licensee MDPI, Basel, Switzerland This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Hamida, E.B.; Noura, H.; Znaidi, W. Security of Cooperative Intelligent Transport Systems: Standards, Threats Analysis and Cryptographic Countermeasures. Electronics 2015, 4, 380-423. https://doi.org/10.3390/electronics4030380
Hamida EB, Noura H, Znaidi W. Security of Cooperative Intelligent Transport Systems: Standards, Threats Analysis and Cryptographic Countermeasures. Electronics. 2015; 4(3):380-423. https://doi.org/10.3390/electronics4030380
Chicago/Turabian StyleHamida, Elyes Ben, Hassan Noura, and Wassim Znaidi. 2015. "Security of Cooperative Intelligent Transport Systems: Standards, Threats Analysis and Cryptographic Countermeasures" Electronics 4, no. 3: 380-423. https://doi.org/10.3390/electronics4030380
APA StyleHamida, E. B., Noura, H., & Znaidi, W. (2015). Security of Cooperative Intelligent Transport Systems: Standards, Threats Analysis and Cryptographic Countermeasures. Electronics, 4(3), 380-423. https://doi.org/10.3390/electronics4030380





