Enhanced Three-Dimensional Double Random Phase Encryption: Overcoming Phase Information Loss in Zero-Amplitude Singularities for Simultaneous Two Primary Data
Abstract
1. Introduction
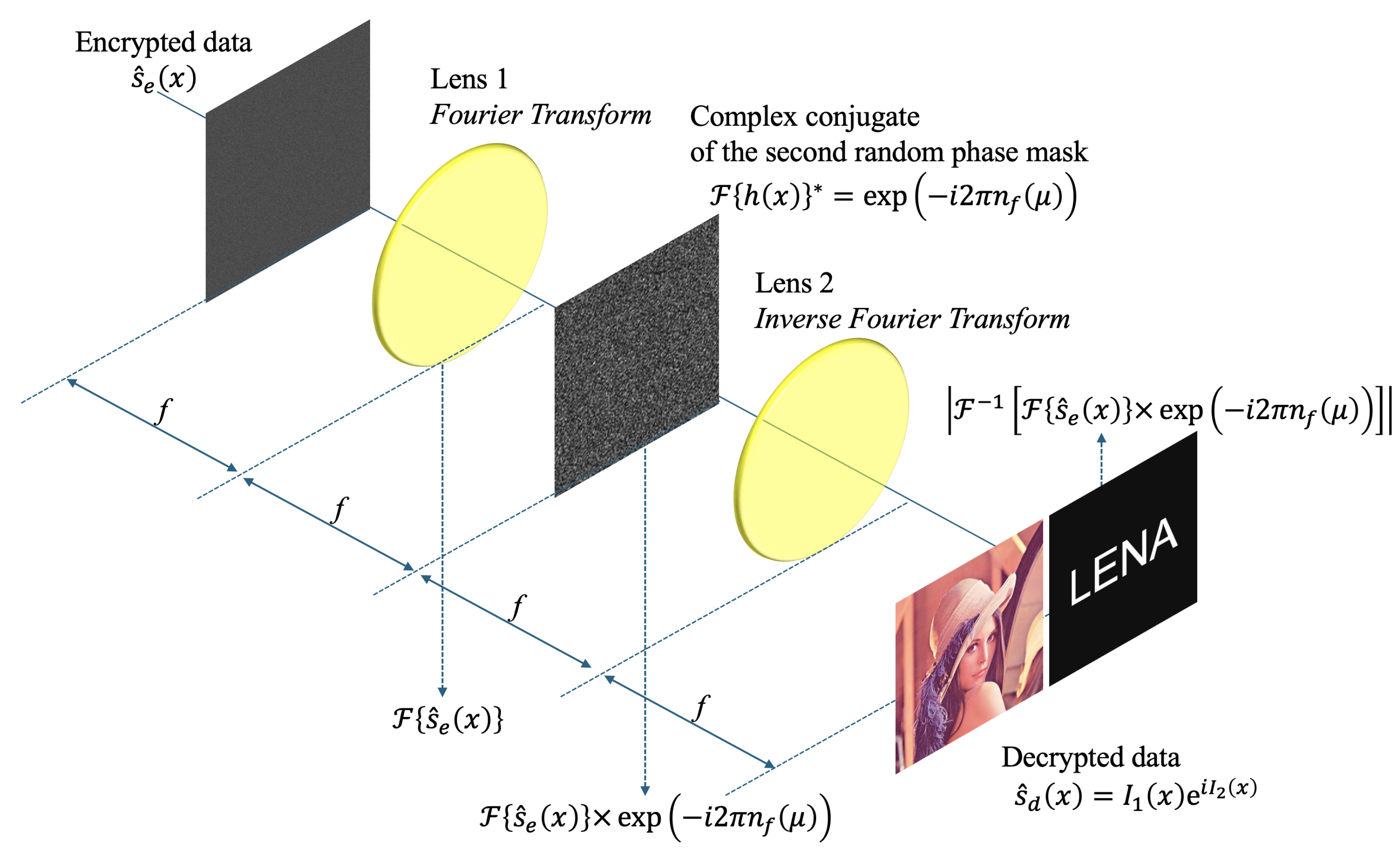
2. Principle of Double Random Phase Encryption
2.1. Encryption Process
2.2. Decryption Process
2.3. Limitations of Conventional DRPE
3. Three-Dimensional Double Random Phase Encryption for Simultaneous Two Primary Data
3.1. Acquisition of 3D Information via SAII
3.2. Simultaneous Two Primary Data Encryption Algorithm
3.3. Decryption and Separation of Simultaneous Data
4. Proposed Solution for Phase Information Loss (Biased Encoding)
4.1. Encryption Process of Our Method
4.2. Decryption and Separation of Biased Simultaneous Data
4.3. 3D Volumetric Computational Reconstruction (VCR)
5. Experimental Results and Discussion
5.1. Experimental Environment and Parameters
5.2. Performance Metrics: PSNR and PSR
5.3. Analysis of 2D Decryption Results
5.4. 3D Volumetric Reconstruction and Depth Security
5.5. Data Efficiency and Security Discussion
6. Conclusions
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
Abbreviations
| DRPE | Double Random Phase Encryption |
| PSNR | Peak Signal-to-Noise Ratio |
| PSR | Peak Sidelobe Ratio |
| RPM | Random Phase Mask |
| SAII | Synthetic Aperture Integral Imaging |
| VCR | Volumetric Computational Reconstruction |
References
- Javidi, B.; Horner, J.L. Optical pattern recognition for validation and security verification. Opt. Eng. 1994, 33, 1752–1756. [Google Scholar] [CrossRef]
- Refregier, P.; Javidi, B. Optical image encryption based on input plane and Fourier plane random encoding. Opt. Lett. 1995, 20, 767–769. [Google Scholar] [CrossRef]
- Matoba, O.; Javidi, B. Encrypted optical memory system using three-dimensional keys in the Fresnel domain. Opt. Lett. 1999, 24, 762–764. [Google Scholar] [CrossRef]
- Tan, X.; Matoba, O.; Okada-Sudo, Y.; Ide, M.; Shimura, T.; Kuroda, K. Secure optical memory system with polarization encryption. Appl. Opt. 2001, 40, 2310–2315. [Google Scholar] [CrossRef]
- Javidi, B.; Nomura, T. Securing information by use of digital holography. Opt. Lett. 2000, 25, 28–30. [Google Scholar] [CrossRef]
- Mogensen, P.C.; Gluckstad, J. Phase-only optical encryption. Opt. Lett. 2000, 25, 566–568. [Google Scholar] [CrossRef] [PubMed]
- Goudail, F.; Bollaro, F.; Javidi, B.; Refregier, P. Influence of a perturbation in a double random phase encoding system. J. Opt. Soc. Am. A 1998, 15, 2629–2638. [Google Scholar] [CrossRef]
- Matoba, O.; Nomura, T.; Perez-Cabre, E.; Millan, M.S.; Javidi, B. Optical techniques for information security. Proc. IEEE 2009, 97, 1128–1148. [Google Scholar] [CrossRef]
- Carnicer, A.; Montes-Usategui, M.; Arcos, S.; Juvells, I. Vulnerability to chosen-cyphertext attacks of optical encryption schemes based on double random phase keys. Opt. Lett. 2005, 30, 1644–1646. [Google Scholar] [CrossRef] [PubMed]
- Clemente, P.; Duran, V.; Torres-Company, V.; Tajahuerce, E.; Lancis, J. Optical encryption based on computational ghost imaging. Opt. Lett. 2010, 35, 2391–2393. [Google Scholar] [CrossRef] [PubMed]
- Liao, M.; Zheng, S.; Pan, S.; Lu, D.; He, W.; Situ, G.; Peng, X. Deep-learning-based ciphertext-only attack on optical double random phase encryption. Opto-Elec. Adv. 2021, 4, 200016. [Google Scholar] [CrossRef]
- Tian, P.; Su, R. A novel virtual optical image encryption scheme created by combining chaotic S-Box with double random phase encoding. Sensors 2022, 22, 5325. [Google Scholar] [CrossRef]
- Li, M.; Wang, M.; Fan, H.; Liu, Y.; Zhang, H.; Nan, H. On the security of image cryptosystems using DRPE based on scrambling and diffusion. Opt. Quan. Elec. 2024, 56, 241. [Google Scholar] [CrossRef]
- Markman, A.; Javidi, B.; Tehranipoor, M. Photon-counting security tagging and verification using optically encoded QR codes. IEEE. Photo. J. 2013, 6, 6800609. [Google Scholar] [CrossRef]
- Markman, A.; Javidi, B. Full-phase photon-counting double-random-phase encryption. J. Opt. Soc. Am. A 2014, 31, 394–403. [Google Scholar] [CrossRef] [PubMed]
- Cho, M.; Javidi, B. Three-dimensional photon counting double-random-phase encryption. Opt. Lett. 2013, 38, 3198–3201. [Google Scholar] [CrossRef]
- Lippmann, G. La Photographie Integrale. Comp. Ren. Acad. des Sci. 1908, 146, 446–451. [Google Scholar]
- Stern, A.; Javidi, B. Three-dimensional image sensing, visualization, and processing using integral imaging. Proc. IEEE 2006, 94, 591–607. [Google Scholar] [CrossRef]
- Levoy, M. Light fields and computational imaging. IEEE Comput. Mag. 2006, 39, 46–55. [Google Scholar] [CrossRef]
- Martinez-Cuenca, R.; Saavedra, G.; Martinez-Corral, M.; Javidi, B. Progress in 3-D multiperspective display by integral imaging. Proc. IEEE 2009, 97, 1067–1077. [Google Scholar] [CrossRef]
- Jang, J.-S.; Javidi, B. Improved viewing resolution of three-dimensional integral imaging by use of nonstationary micro-optics. Opt. Lett. 2002, 27, 324–326. [Google Scholar] [CrossRef]
- Jang, J.-S.; Javidi, B. Three-dimensional synthetic aperture integral imaging. Opt. Lett. 2002, 27, 1144–1146. [Google Scholar] [CrossRef] [PubMed]
- Jang, J.-S.; Javidi, B. Improvement of viewing angle in integral imaging by use of moving lenslet arrays with low fill factor. Appl. Opt. 2003, 42, 1996–2002. [Google Scholar] [CrossRef] [PubMed]
- Jang, J.-S.; Javidi, B. Large depth-of-focus time-multiplexed three-dimensional integral imaging by use of lenslets with nonuniform focal lengths and aperture sizes. Opt. Lett. 2003, 28, 1924–1926. [Google Scholar] [CrossRef] [PubMed]
- Schulein, R.; DaneshPanah, M.; Javidi, B. 3D imaging with axially distributed sensing. Opt. Lett. 2009, 34, 2012–2014. [Google Scholar] [CrossRef]
- Cho, M.; Shin, D. 3D integral imaging display using axially recorded multiple images. J. Opt. Soc. Korea 2013, 17, 410–414. [Google Scholar] [CrossRef]
- Hong, S.-H.; Jang, J.-S.; Javidi, B. Three-dimensional volumetric object reconstruction using computational integral imaging. Opt. Exp. 2004, 12, 483–491. [Google Scholar] [CrossRef]
- Cho, B.; Kopycki, P.; Martinez-Corral, M.; Cho, M. Computational volumetric reconstruction of integral imaging with improved depth resolution considering continuously non-uniform shifting pixels. Opt. Laser Eng. 2018, 111, 114–121. [Google Scholar] [CrossRef]
- Jang, J.-Y.; Cho, M. Three-dimensional double random phase encryption for simultaneous two-primary data. Electronics 2024, 13, 823. [Google Scholar] [CrossRef]
- Javidi, B. Nonlinear joint power spectrum based optical correlation. Appl. Opt. 1989, 28, 2358–2367. [Google Scholar] [CrossRef]
- Huang, C.; Peng, Y.; Deng, W. A dendrite net learning multi-objective artificial bee colony algorithm for UAV. Appl. Soft Comput. 2026, 189, 114449. [Google Scholar] [CrossRef]
















| Method | Conventional Method | Our Proposed Method | ||
|---|---|---|---|---|
| Metric | PSNR [dB] | SSIM | PSNR [dB] | SSIM |
| LENA text | 57.1856 | 0.9995 | 57.1856 | 0.9995 |
| Lena test | 8.2346 | 0.0665 | 59.9642 | 1 |
| MANDRILL text | 55.8164 | 0.9993 | 55.8164 | 0.9993 |
| Mandrill test | 8.2869 | 0.0460 | 49.5853 | 0.9998 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license.
Share and Cite
Cho, M.; Lee, M.-C. Enhanced Three-Dimensional Double Random Phase Encryption: Overcoming Phase Information Loss in Zero-Amplitude Singularities for Simultaneous Two Primary Data. Electronics 2026, 15, 896. https://doi.org/10.3390/electronics15040896
Cho M, Lee M-C. Enhanced Three-Dimensional Double Random Phase Encryption: Overcoming Phase Information Loss in Zero-Amplitude Singularities for Simultaneous Two Primary Data. Electronics. 2026; 15(4):896. https://doi.org/10.3390/electronics15040896
Chicago/Turabian StyleCho, Myungjin, and Min-Chul Lee. 2026. "Enhanced Three-Dimensional Double Random Phase Encryption: Overcoming Phase Information Loss in Zero-Amplitude Singularities for Simultaneous Two Primary Data" Electronics 15, no. 4: 896. https://doi.org/10.3390/electronics15040896
APA StyleCho, M., & Lee, M.-C. (2026). Enhanced Three-Dimensional Double Random Phase Encryption: Overcoming Phase Information Loss in Zero-Amplitude Singularities for Simultaneous Two Primary Data. Electronics, 15(4), 896. https://doi.org/10.3390/electronics15040896





