Polymorphic Hybrid CMOS-MTJ Logic Gates for Hardware Security Applications
Abstract
:1. Introduction
2. Background
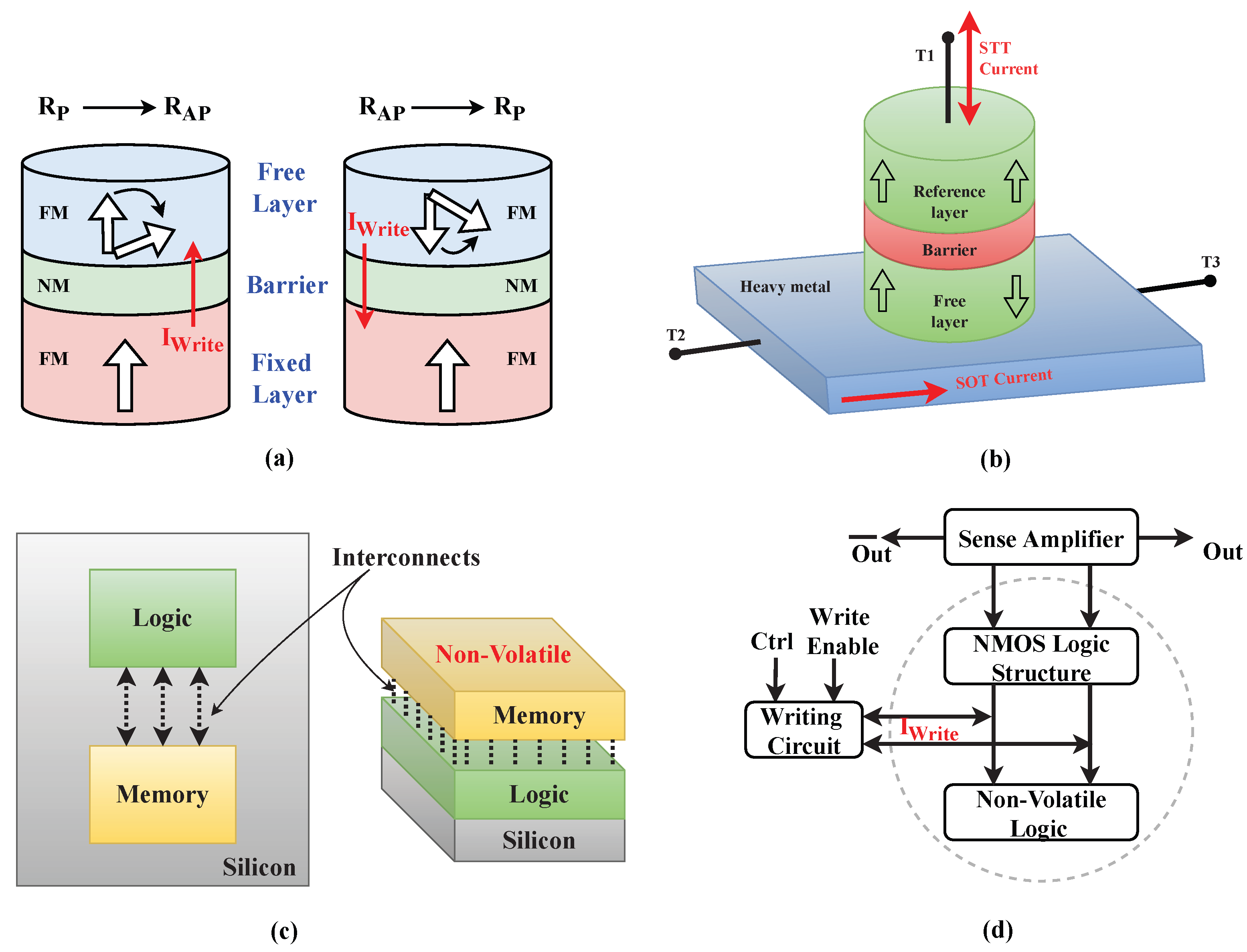
2.1. Magnetic Tunnel Junction: Construction and Switching
2.2. Logic-in-Memory Architecture
3. Proposed Work: Spintronics PGs for Hardware Security Applications
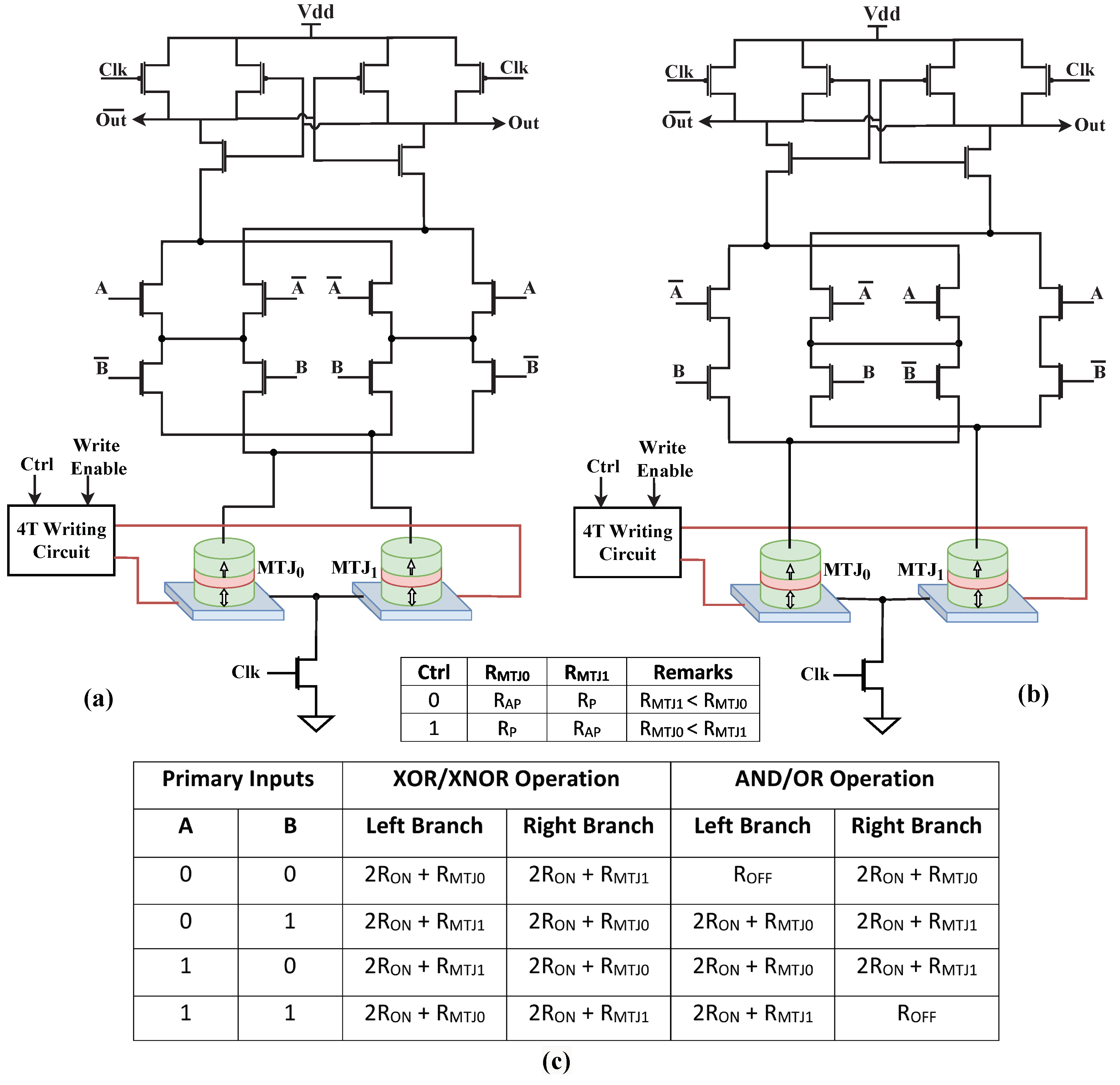
3.1. Operation of Spintronics PGs
3.2. Preventing Manufacturing-Time Tampering
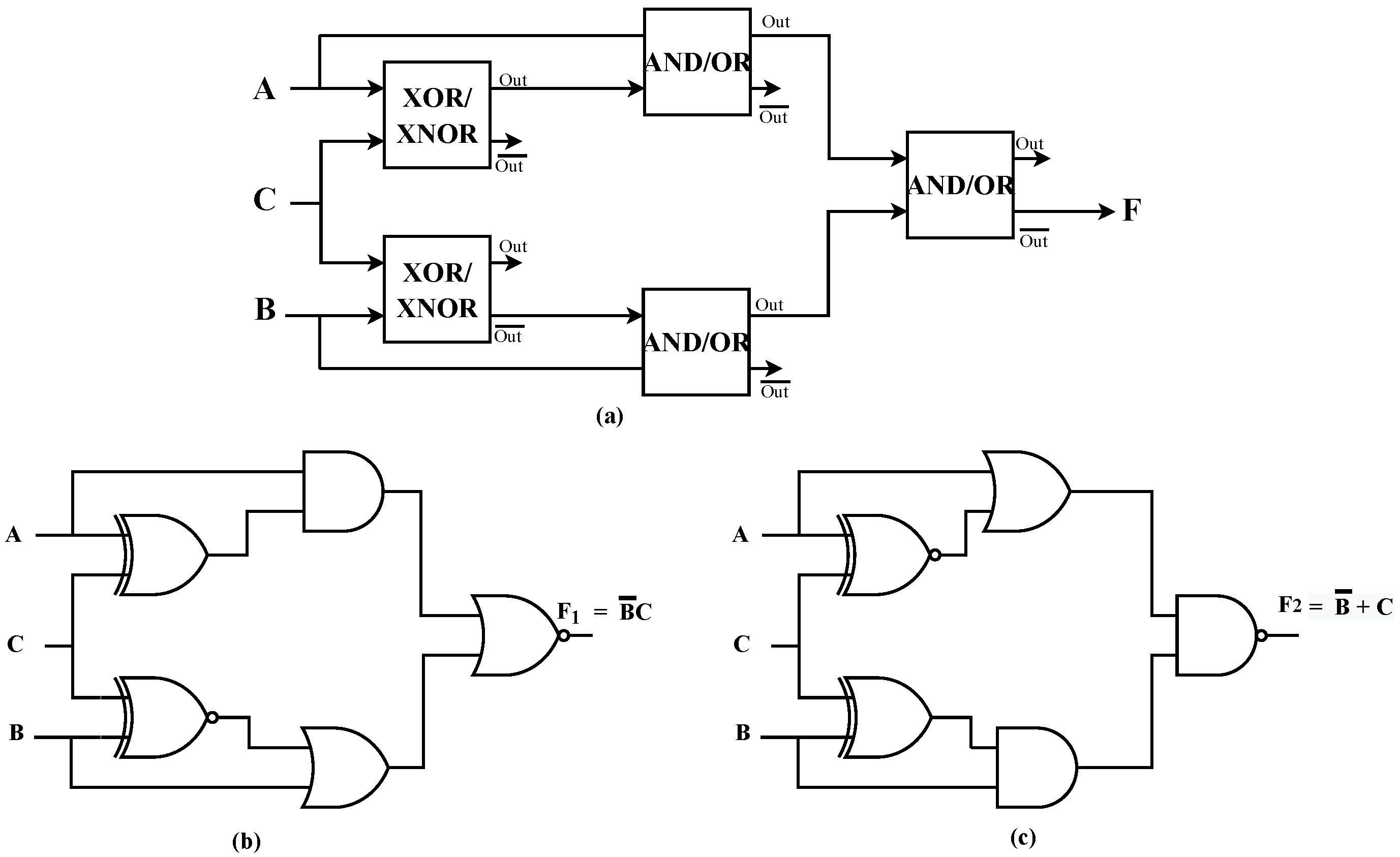
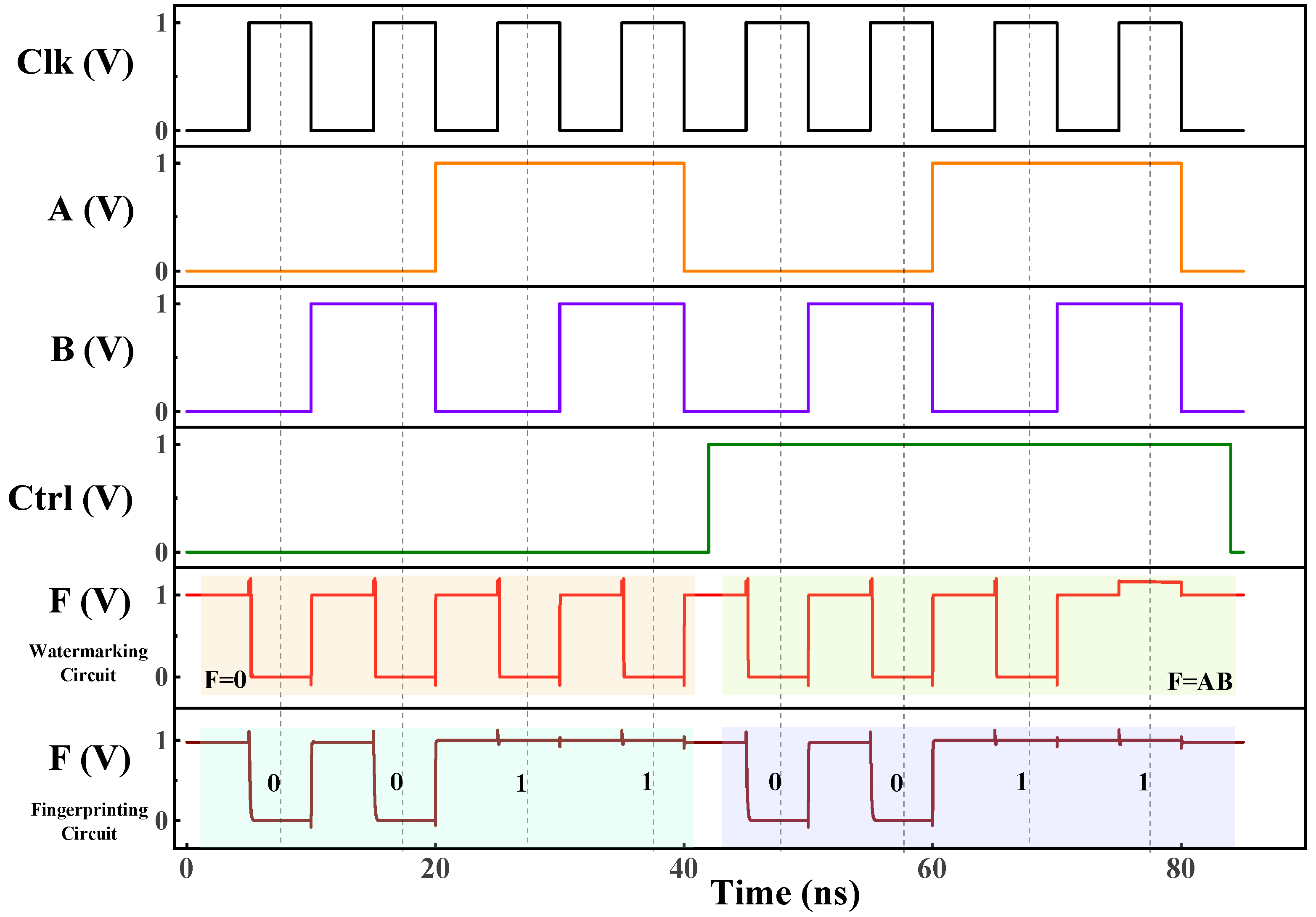
3.3. IC Watermarking
3.4. IC Fingerprinting
4. Results and Discussion
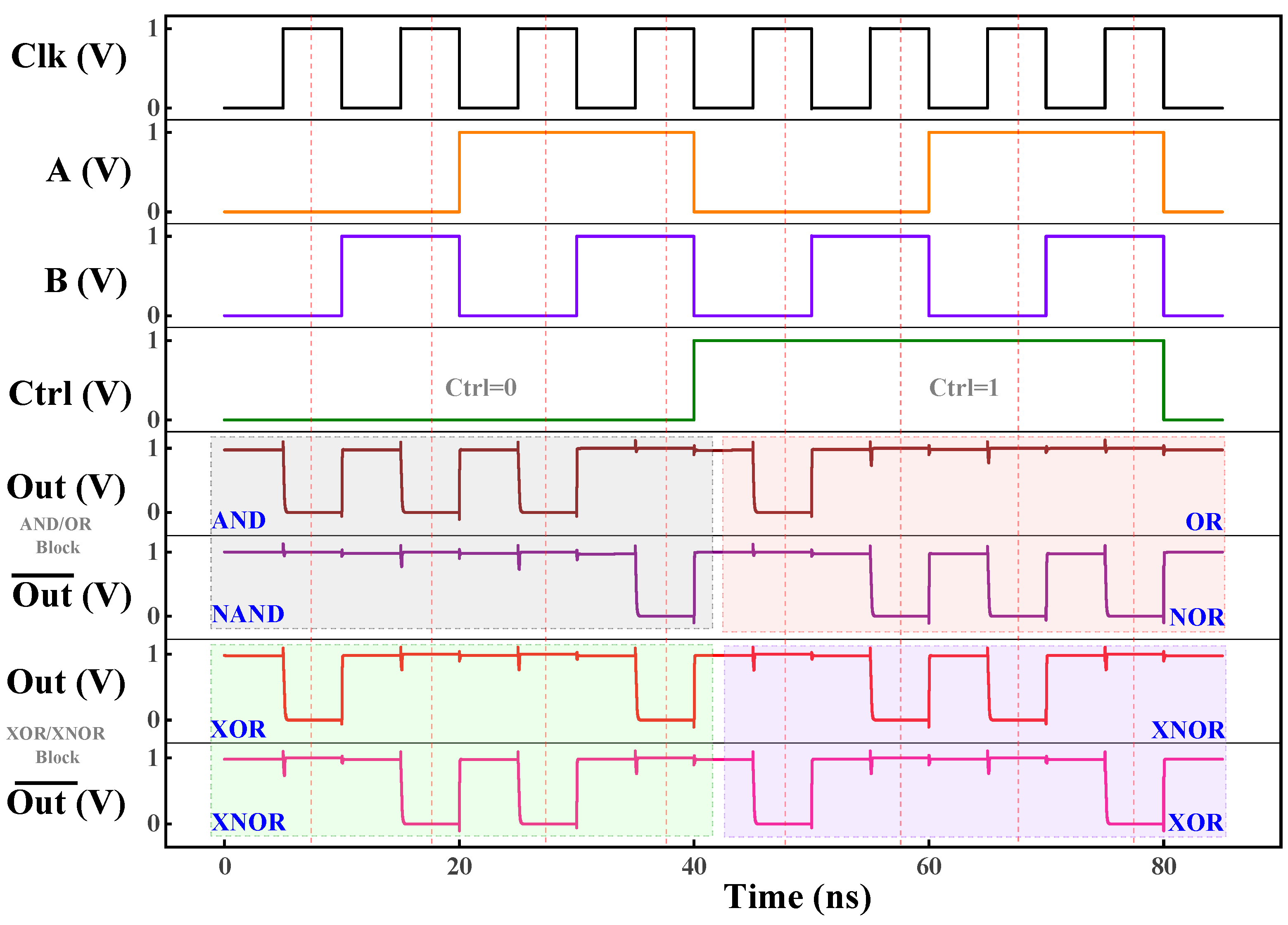
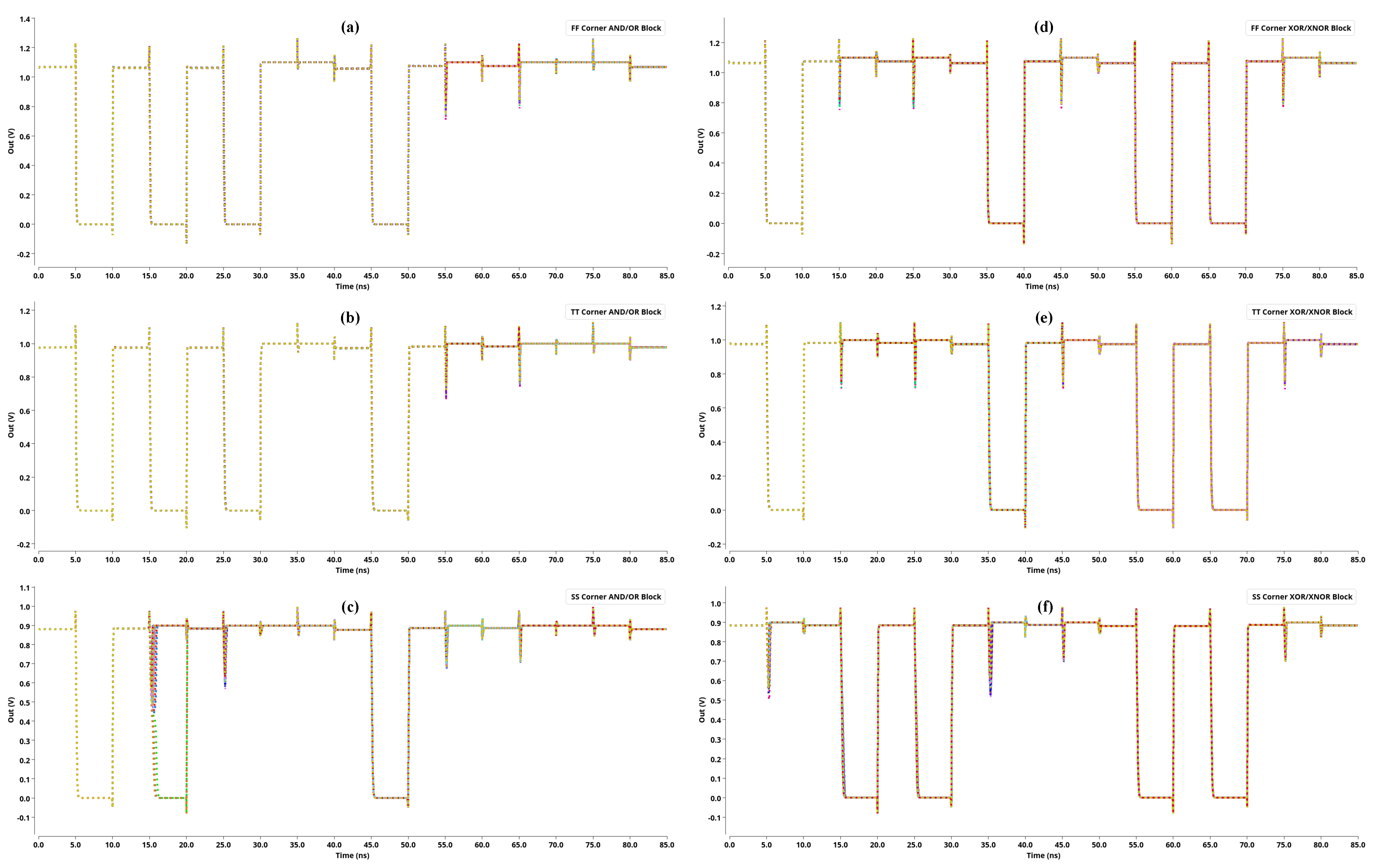
4.1. Simulation Results
4.2. Effect of Process Variation
4.3. Design Considerations, Discussion, and Challenges
5. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Semiconductor Industry Association. Available online: https://www.semiconductors.org/ (accessed on 8 February 2023).
- Guin, U.; Forte, D.; Tehranipoor, M. Anti-counterfeit techniques: From design to resign. In Proceedings of the IEEE 14th International Workshop Microprocessor Test Verification, Austin, TX, USA, 11–13 December 2013; pp. 89–94. [Google Scholar]
- Tehranipoor, M.; Guin, U.; Forte, D.; Tehranipoor, M.; Guin, U.; Forte, D. Counterfeit integrated circuits. In Counterfeit Integrated Circuits; Springer: Cham, Switzerland, 2015; pp. 15–36. [Google Scholar]
- Kumar, R.; Divyanshu, D.; Khan, D.; Amara, S.; Massoud, Y. Spin orbit torque-assisted magnetic tunnel junction-based hardware Trojan. Electronics 2022, 11, 1753. [Google Scholar] [CrossRef]
- Bhunia, S.; Tehranipoor, M. Hardware Security: A Hands-on Learning Approach; Morgan Kaufmann: Oxford, UK, 2018. [Google Scholar]
- Tehranipoor, M.; Salmani, H.; Zhang, X.; Wang, M.; Karri, R.; Rajendran, J.; Rosenfeld, K. Trustworthy Hardware: Trojan Detection and Design-for-Trust Challenges. Computer 2011, 44, 66–74. [Google Scholar] [CrossRef]
- Hu, W.; Chang, C.-H.; Sengupta, A.; Bhunia, S.; Kastner, R.; Li, H. An overview of hardware security and trust: Threats, countermeasures, and design tools. IEEE Trans. Comput.-Aided Des. Integr. Circuits Syst. 2021, 40, 1010–1038. [Google Scholar] [CrossRef]
- Alasad, Q.; Yuan, J.; Fan, D. Leveraging all-spin logic to improve hardware security. In Proceedings of the on Great Lakes Symposium on VLSI 2017–GLSVLSI ’17, Banff, AB, Canada, 10–12 May 2017. [Google Scholar]
- Rajendran, J.; Karri, R.; Wendt, J.B.; Potkonjak, M.; McDonald, N.; Rose, G.S.; Wysocki, B. Nano meets security: Exploring nanoelectronic devices for security applications. Proc. IEEE Inst. Electr. Electron. Eng. 2015, 103, 829–849. [Google Scholar] [CrossRef]
- Ghosh, S. Spintronics and security: Prospects, vulnerabilities, attack models, and preventions. Proc. IEEE Inst. Electr. Electron. Eng. 2016, 104, 1864–1893. [Google Scholar] [CrossRef]
- Knechtel, J. Hardware security for and beyond CMOS technology. In Proceedings of the 2021 International Symposium on Physical Design, Virtual Event, 22–24 March 2021. [Google Scholar]
- Bi, Y.; Gaillardon, P.-E.; Hu, X.S.; Niemier, M.; Yuan, J.-S.; Jin, Y. Leveraging emerging technology for hardware security–case study on silicon nanowire FETs and graphene SymFETs. In Proceedings of the 2014 IEEE 23rd Asian Test Symposium, Hangzhou, China, 16–19 November 2014. [Google Scholar]
- Matsunaga, S.; Hayakawa, J.; Ikeda, S.; Miura, K.; Endoh, T.; Ohno, H.; Hanyu, T. MTJ-Based Nonvolatile Logic-in-Memory Circuit, Future Prospects and Issues. In Proceedings of the 2009 Design, Automation & Test in Europe Conference & Exhibition, Nice, France, 20–24 April 2009. [Google Scholar]
- Massoud, Y.; White, J. Managing On-Chip Inductive Effects. IEEE Trans. Very Large Scale Integr. (VLSI) Syst. 2002, 10, 789–798. [Google Scholar] [CrossRef]
- Massoud, Y.; White, J. Simulation and Modeling of the Effect Substrate Conductivity on Coupling Inductance and Circuit Crosstalk. IEEE Trans. Very Large Scale Integr. (VLSI) Syst. 2002, 10, 286–291. [Google Scholar] [CrossRef]
- Ragheb, T.; Massoud, Y. On the modeling of resistance in graphene nanoribbon (GNR) for future interconnect applications. In Proceedings of the IEEE/ACM International Conference on Computer-Aided Design, San Jose, CA, USA, 10–13 November 2008. [Google Scholar]
- Massoud, Y.; Nieuwoudt, A. Modeling and Design Challenges and Solutions for Carbon Nanotube-Based Interconnect in Future High-Performance Integrated Circuits. ACM J. Emerg. Technol. Comput. Syst. 2006, 2, 155–196. [Google Scholar] [CrossRef]
- Massoud, Y.; White, J. FastMag: A 3-D Fast Inductance Extraction Program for Structures with Permeable materials. In Proceedings of the IEEE/ACM International Conference on Computer-Aided Design, San Jose, CA, USA, 10–14 November 2002; pp. 478–484. [Google Scholar]
- Srinivasan, S.; Sarkar, A.; Behin-Aein, B.; Datta, S. All-spin logic device with inbuilt nonreciprocity. IEEE Trans. Magn. 2011, 47, 4026–4032. [Google Scholar] [CrossRef]
- Mishra, R.; Yang, H. Emerging Spintronics Phenomena and Applications. IEEE Trans. Magn. 2021, 57, 1–34. [Google Scholar] [CrossRef]
- Kulkarni, A.; Bindal, N.; Kaushik, B.K. Quantum Computing Circuits Based on Spin-Torque Qubit Architecture: Toward the Physical Realization of Quantum Computers. IEEE Nanotechnol. Mag. 2019, 13, 15–24. [Google Scholar] [CrossRef]
- Wang, X.; Yang, J.; Zhao, Y.; Jia, X.; Qu, G.; Zhao, W. Hardware security in spin-based computing-in-memory: Analysis, exploits, and mitigation techniques. ACM J. Emerg. Technol. Comput. Syst. 2020, 16, 1–18. [Google Scholar] [CrossRef]
- Divyanshu, D.; Kumar, R.; Khan, D.; Amara, S.; Massoud, Y. Physically unclonable function using GSHE driven SOT assisted p-MTJ for next generation hardware security applications. IEEE Access 2022, 10, 93029–93038. [Google Scholar] [CrossRef]
- Perach, B.; Kvatinsky, S. An Asynchronous and Low-Power True Random Number Generator using STT-MTJ. In Proceedings of the 2020 IEEE International Symposium on Circuits and Systems (ISCAS), Sevilla, Spain, 10–21 October 2020. [Google Scholar]
- Divyanshu, D.; Kumar, R.; Khan, D.; Amara, S.; Massoud, Y. Logic locking using emerging 2T/3T magnetic tunnel junctions for hardware security. IEEE Access 2022, 10, 102386–102395. [Google Scholar] [CrossRef]
- Divyanshu, D.; Kumar, R.; Khan, D.; Amara, S.; Massoud, Y. Design of VGSOT-MTJ-Based Logic Locking for High-Speed Digital Circuits. Electronics 2022, 11, 3537. [Google Scholar] [CrossRef]
- Divyanshu, D.; Kumar, R.; Khan, D.; Amara, S.; Massoud, Y. An Approach towards Designing Logic Locking Using Shape-Perpendicular Magnetic Anisotropy-Double Layer MTJ. Electronics 2023, 12, 479. [Google Scholar] [CrossRef]
- Stoica, A.; Zebulum, R.; Keymeulen, D. Polymorphic Electronics. In International Conference on Evolvable Systems; Springer: Berlin/Heidelberg, Germany, 2001. [Google Scholar]
- Rakheja, S.; Kani, N. Polymorphic spintronic logic gates for hardware security primitives—Device design and performance benchmarking. In Proceedings of the 2017 IEEE/ACM International Symposium on Nanoscale Architectures (NANOARCH), Newport, RI, USA, 25–26 July 2017. [Google Scholar]
- Zhao, W.; Belhaire, E.; Chappert, C.; Mazoyer, P. Spin Transfer Torque (STT)-MRAM–Based Runtime Reconfiguration FPGA Circuit. ACM Trans. Embed. Comput. Syst. 2009, 9, 14. [Google Scholar] [CrossRef]
- Guo, W.; Prenat, G.; Dieny, B. A Novel Architecture of Non-Volatile Magnetic Arithmetic Logic Unit Using Magnetic Tunnel Junctions. J. Phys. D Appl. Phys. 2014, 47, 165001. [Google Scholar] [CrossRef]
- Roohi, A.; DeMara, R.F. PARC: A Novel Design Methodology for Power Analysis Resilient Circuits Using Spintronics. IEEE Trans. Nanotechnol. 2019, 18, 885–889. [Google Scholar] [CrossRef]
- Angizi, S.; He, Z.; Chen, A.; Fan, D. Hybrid Spin-CMOS Polymorphic Logic Gate with Application in in-Memory Computing. IEEE Trans. Magn. 2020, 56, 1–15. [Google Scholar] [CrossRef]
- Zhang, Y.; Yan, B.; Wu, W.; Li, H.; Chen, Y. Giant Spin Hall Effect (GSHE) Logic Design for Low Power Application. In Proceedings of the Design, Automation & Test in Europe Conference & Exhibition (DATE), Grenoble, France, 9–13 March 2015. [Google Scholar]
- Patnaik, S.; Rangarajan, N.; Knechtel, J.; Sinanoglu, O.; Rakheja, S. Advancing Hardware Security Using Polymorphic and Stochastic Spin-Hall Effect Devices. In Proceedings of the 2018 Design, Automation & Test in Europe Conference & Exhibition (DATE), Dresden, Germany, 19–23 March 2018. [Google Scholar]
- Zhang, Y.; Yan, B.; Kang, W.; Cheng, Y.; Klein, J.O.; Zhang, Y.; Chen, Y.; Zhao, W. Compact Model Subvolume MTJ Its Des. Appl. Nanoscale Technol. Nodes. IEEE Trans. Electron Devices. 2015, 62, 2048–2055. [Google Scholar] [CrossRef]
- Wang, Z.; Zhao, W.; Deng, E.; Klein, J.-O.; Chappert, C. Perpendicular-Anisotropy Magnetic Tunnel Junction Switched by Spin-Hall-Assisted Spin-Transfer Torque. J. Phys. D Appl. Phys. 2015, 48, 065001. [Google Scholar] [CrossRef]
- von Neumann, J. First Draft of a Report on the EDVAC (1945). In Ideas That Created the Future; The MIT Press: Cambridge, MA, USA, 2021; pp. 89–106. [Google Scholar]
- Kim, J.; Ryu, K.; Kang, S.H.; Jung, S.-O. A Novel Sensing Circuit for Deep Submicron Spin Transfer Torque MRAM (STT-MRAM). IEEE Trans. Very Large Scale Integr. VLSI Syst. 2012, 20, 181–186. [Google Scholar] [CrossRef]
- Bagheriye, L.; Toofan, S.; Saeidi, R.; Moradi, F. Offset-Compensated High-Speed Sense Amplifier for STT-MRAMs. IEEE Trans. Very Large Scale Integr. VLSI Syst. 2018, 26, 1051–1058. [Google Scholar] [CrossRef]
- Kang, W.; Pang, T.; Lv, W.; Zhao, W. Dynamic Dual-Reference Sensing Scheme for Deep Submicrometer STT-MRAM. IEEE Trans. Circuits Syst. I Regul. Pap. 2017, 64, 122–132. [Google Scholar] [CrossRef]
- Song, B.; Na, T.; Kim, J.; Kim, J.P.; Kang, S.H.; Jung, S.-O. Latch Offset Cancellation Sense Amplifier for Deep Submicrometer STT-RAM. IEEE Trans. Circuits Syst. I Regul. Pap. 2015, 62, 1776–1784. [Google Scholar] [CrossRef]
- Na, T.; Woo, S.-H.; Kim, J.; Jeong, H.; Jung, S.-O. Comparative Study of Various Latch-Type Sense Amplifiers. IEEE Trans. Very Large Scale Integr. VLSI Syst. 2014, 22, 425–429. [Google Scholar] [CrossRef]
- Bian, Z.; Hong, X.; Guo, Y.; Naviner, L.; Ge, W.; Cai, H. Investigation of PVT-Aware STT-MRAM Sensing Circuits for Low-VDD Scenario. Micromachines 2021, 12, 551. [Google Scholar] [CrossRef]
- Zhang, Y.; Zhao, W.; Kang, W.; Deng, E.; Klein, J.-O.; Revelosona, D. Current-Induced Magnetic Switching for High-Performance Computing. In Spintronics-Based Computing; Springer International Publishing: Cham, Switzeerland, 2015; pp. 1–51. [Google Scholar]
- Barla, P.; Joshi, V.K.; Bhat, S. A novel low power and reduced transistor count magnetic arithmetic logic unit using hybrid STT-MTJ/CMOS circuit. IEEE Access 2020, 8, 6876–6889. [Google Scholar] [CrossRef]
- Shayan, M.; Basu, K.; Karri, R. Hardware Trojans Inspired IP Watermarks. IEEE Des. Test. 2019, 36, 72–79. [Google Scholar] [CrossRef]
- Wang, T.; Cui, X.; Yu, D.; Aramoon, O.; Dunlap, T.; Qu, G.; Cui, X. Polymorphic Gate Based IC Watermarking Techniques. In Proceedings of the 2018 23rd Asia and South Pacific Design Automation Conference (ASP-DAC), Jeju, Republic of Korea, 22–25 January 2018. [Google Scholar]
- Qu, G.; Potkonjak, M. Intellectual Property Protection in VLSI Designs: Theory and Practice; Springer: New York, NY, USA, 2011. [Google Scholar]
- Wang, T.; Cui, X.; Yu, D.; Aramoon, O.; Dunlap, T.; Qu, G.; Cui, X. A Novel Polymorphic Gate Based Circuit Fingerprinting Technique. In Proceedings of the 2018 on Great Lakes Symposium on VLSI, Chicago, IL, USA, 23–25 May 2018; ACM: New York, NY, USA, 2018. [Google Scholar]
- Chandrakasan, N.R. Digital Integrated Circuits: A Design Perspective; Pearson Education: Delhi, India, 2017. [Google Scholar]
- Chun, K.C.; Zhao, H.; Harms, J.D.; Kim, T.-H.; Wang, J.-P.; Kim, C.H. A scaling roadmap and performance evaluation of in-plane and perpendicular MTJ based STT-MRAMs for high-density cache memory. IEEE J. Solid-State Circuits 2013, 48, 598–610. [Google Scholar] [CrossRef]



| Parameter | STT-MTJ Values | SOT-MTJ Values |
|---|---|---|
| MTJ Dimension | 40 nm × 40 nm | 40 nm × 40 nm |
| MTJ Shape | Circular | Circular |
| Oxide barrier thickness | 0.85 nm | 0.85 nm |
| Free layer thickness | 0.7 nm | 0.7 nm |
| Heavy metal dimensions | – | 60 nm × 40 nm × 3 nm |
| Resistance area product | 10 um | 10 um |
| Tunnel Magnetoresistance | 200% | 200% |
| Temperature | 300 K | 300 K |
| Technology parameters | default [36] | default [37] |
| Logic Operation | STT-MTJ-Based | SOT-MTJ-Based | ||
|---|---|---|---|---|
| Fall Time | Delay | Fall Time | Delay | |
| AND | 117.71 ps | 132.48 ps | 167.74 ps | 96.20 ps |
| OR | 99.16 ps | 25.40 ps | 154.95 ps | 70.60 ps |
| NAND | 115.48 ps | 25.30 ps | 154.33 ps | 70.20 ps |
| NOR | 146.40 ps | 161.60 ps | 170.15 ps | 98.00 ps |
| XOR | 106.88 ps | 27.60 ps | 171.40 ps | 99.30 ps |
| XNOR | 106.53 ps | 27.50 ps | 164.53 ps | 93.40 ps |
| Process Corner | Temperature (°C) | Supply Voltage (Vdd) | AND/OR Operation | XOR/XNOR Operation |
|---|---|---|---|---|
| Fast–best (FF) | −25 °C | 1.1 V | Pass | Pass |
| Typical (TT) | 25 °C | 1.0 V | Pass | Pass |
| Slow–worst (SS) | 75 °C | 0.9 V | Fail | Fail |
| Design | Morph Method | Device Used |
|---|---|---|
| [13] | Wired program | STT-MTJ |
| [33] | Three keys | 5T-DWM device |
| [34] | Preset and set lines | GSHE MTJ |
| [35] | Control signal | GSHE switch |
| [46] | Control signal | STT MTJ |
| This Work | Control signal | SOT and STT MTJ |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Kumar, R.; Divyanshu, D.; Khan, D.; Amara, S.; Massoud, Y. Polymorphic Hybrid CMOS-MTJ Logic Gates for Hardware Security Applications. Electronics 2023, 12, 902. https://doi.org/10.3390/electronics12040902
Kumar R, Divyanshu D, Khan D, Amara S, Massoud Y. Polymorphic Hybrid CMOS-MTJ Logic Gates for Hardware Security Applications. Electronics. 2023; 12(4):902. https://doi.org/10.3390/electronics12040902
Chicago/Turabian StyleKumar, Rajat, Divyanshu Divyanshu, Danial Khan, Selma Amara, and Yehia Massoud. 2023. "Polymorphic Hybrid CMOS-MTJ Logic Gates for Hardware Security Applications" Electronics 12, no. 4: 902. https://doi.org/10.3390/electronics12040902
APA StyleKumar, R., Divyanshu, D., Khan, D., Amara, S., & Massoud, Y. (2023). Polymorphic Hybrid CMOS-MTJ Logic Gates for Hardware Security Applications. Electronics, 12(4), 902. https://doi.org/10.3390/electronics12040902







