1. Introduction
For specified applications where high data security must be built, the entire IoT development process is carried out in real time. The majority of data transferred via wireless applications depends on a number of variables, including data volume, size, and mode of transmission, where cloud integrations are established for high-security authentications. However, the majority of IoT apps use certain unnamed elements to secure data, which does not entirely control the accuracy of data transmission and reception [
1]. In order to improve data security and privacy during transmission and reception phases, where various parametric evaluations for data determinations are conducted, the proposed method is introduced [
2]. With a given set of data, even additional black-box design functions can be created, adding to the complexity of IoT processing methods [
3]. By adopting an external source where the cost of monitoring is increased, customers can manage some data issues, such as denial-of-service attacks, cyber-attacks, etc. [
4]. However, the suggested system includes a sophisticated data monitoring system with research characteristics for minimization scenarios, such as noise factors, malicious node detection, and data queuing reductions [
5]. Additionally, a fresh set of formulations with precise design methods is offered, and all machine learning techniques that offer additional support for the proposed system are merged [
6]. There are numerous authentication stages in the IoT development process where security and privacy must be guaranteed with the same configuration steps.
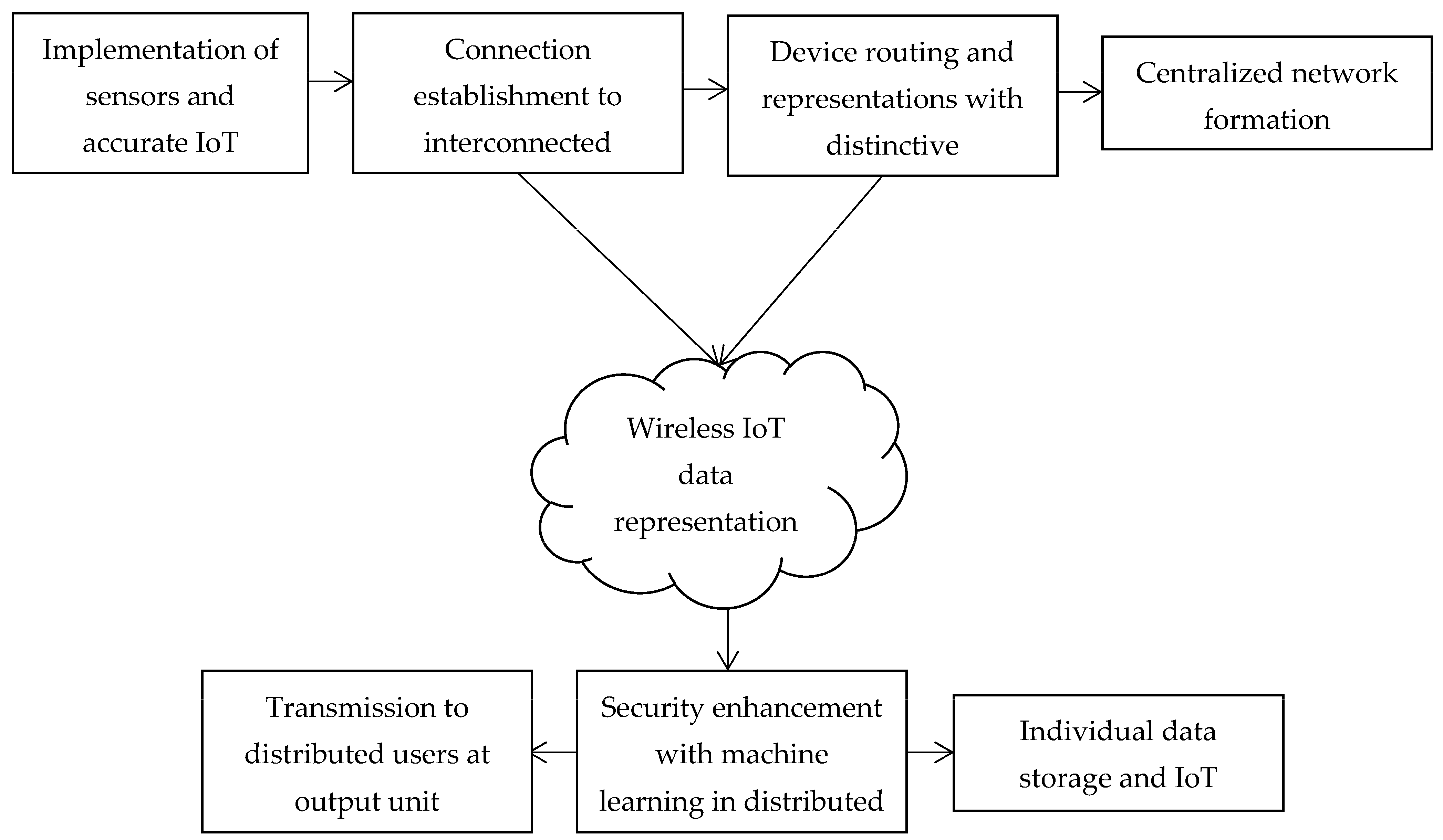
Figure 1 represents a general block diagram for different devices in the network where, at initial state, multiple sensors are connected with accurate IoT devices. Then the device representations are made with distinct connection representations, and data interconnection is prepared with more networks. Once the networks are connected, routing representation procedures are carried out for all connected sensors and components. Then a centralized network formation is made which directly provides connection to wireless networks. Since most of the IoT applications are distributed in wireless operation, high security enhancement is provided with machine learning algorithms in a distributed mode; thus, data storage and analytics for IoT operations are completed in a much clearer way. In this type of continuous secured IoT data transfer, only distributed users are connected, which in turn maximizes the privacy of the entire network.
1.1. Literature Survey
Analyzing some of the literature models that increase support for new IoT applications is therefore important. The majority of the current systems provide security and privacy for data connections in a discrete manner; however, the current technological development necessitates integrating all defined formulations. As a result, each technique is individually analyzed before being introduced in order to create a combined mechanism for data security and privacy. In order to offer information regarding data leakage that is present in various public data functions, Ref. [
1] establishes an accuracy trade-off criterion. The IoT data leakage issues will have a significant impact on the system, which in turn causes high distortion rates in real time. As a result, data security will be stronger if notation functions with privacy inputs are supplied. However, if real-time notation functions are applied, the included system will get seriously confused by system modifications, which will impact data secrecy features. Since there would be a substantial impact owing to the increased user base, mathematical models are being created to avoid data theft on social networks [
2]. This leads to the introduction of a hypothetical decision-making process with two distinct nodes, such as adversarial and ideal, where data falsification is entirely eliminated from the system. However, the number of false positives in planned systems that are not processed due to fewer requests must be detected using an informed decision-making technique.
Utilizing a trust management framework [
3] that processes big data and has a feature set, the majority of the development process for IoT applications is carried out. It is vital to supply crowdsourcing to connected devices where multi-perspective task forces can be enabled in order to regulate the degree of confidence in data privacy. Even if these task forces are activated, confusion metrics in the real-time database will continue to impact user data. As a result, by permitting node technical features [
4] with differentiation and clustering approaches, representations are created instead of data task forces. As a result, a multi-signature platform is developed for data preservation and is used to store various transmitted signature properties. However, these features can only be used with a system if a significant amount of memory is available; as a result, a dimensionless system must be developed. In order to provide block chain technology with comprehensive system transfer function protection, a dimensionless system must be established throughout the IoT design phase, which is not achievable with real-time data transmission. Researchers take additional steps to determine the future course of IoT data security and privacy with big data deployments [
5]. Certain technological features necessitate clear verification and authentication requirements for data processing and delivery to the receiver. Such technical processes need a real-time watermarking system, since certain apps can detect environmental changes. All defined layers of open system interconnections are examined to understand the real-time effects on data security, and it has been discovered that the physical layer is crucial for preventing data theft [
6]. A convex estimating approach is presented to address such attacks because the physical layer is thought to be one of the main sources for passive attacks. Even though the physical layer is able to control attacks, the remaining top levels will still significantly disrupt the various communication layers; as a result, the same estimation algorithm must be used for the upper layers, which is a much more challenging procedure.
In order to provide high security to all data-connected networks, some system functions are carried out with resilient characteristics as offloading methods in industrial processes [
7]. If an edge computing system is created, some manual work will need to be done to determine whether an attack is coming from an internal or external user. However, because of the bulk of the data, manual operations are avoided, and only automatic attack detection is carried out on centralised servers. A lightweight authentication protocol is enabled for all communication protocols in order to transform network functioning in an automatic manner, making IoT networks very flexible against various forms of threats [
8]. To maintain data privacy in the rising cloud environment, a random provability verification method is used in the case of light-weight protocols. Even though IoT cloud storage solutions already have a reliable verification mechanism in place, system developments that are mostly the result of data attacks require an external verification method. A spectrum sharing strategy is required, per the IoT procedure with stable verification [
9], for stabilizing the complete database when using distributed ways. Data symmetry is established throughout the full IoT process with power degradation using the distributed technique, which is indicated as a two-scale authentication model. Data cannot reach the receiver if energy to IoT systems is not supplied properly; thus, appropriate power must be supplied in both scale factors. To retain all of the data in a set of records utilizing some encryption keys, evolutionary approaches must be used [
10]. To increase the effectiveness of data privacy amongst users, a data sharing scheme is enabled within the same user platform due to the requirement that the encryption keys be consistent across all IoT systems.
Table 1 lists the important works in IoT data security and privacy that use various algorithms.
1.2. Research Gap and Motivation
Most of the existing approaches provide real-time IoT information that is present at the data transfer state where different approaches are implemented for enhancing the privacy of the network. However, the major gap that is observed in existing approaches [
17,
18,
19,
20] is that data security is made using only an authentication key factor, which is not highly tolerable if multiple data are transmitted over the same network in the same time period. Even if a greater amount of data is transmitted in a distributed way, the system suffers with a misperception problem if size and representation of data are identical. Further, in IoT applications, multiple sensors are interconnected with a distinct network, thereby producing duplicate packets over the entire network, which needs to be avoided. If duplicate data are created, then external users can certainly catch the data by creating multiple destinations in the transmitted time period. Therefore, some alternate design representations must be incorporated into existing approaches to enhance the security and privacy of IoT operations.
To overcome the security and privacy gap that is present in existing approaches, the projected design is generated with analytical representations. In the proposed method, unique design factors are combined with data noise, robustness, configurations and length of the network. Moreover, with the aforementioned security factors it is possible to transmit more data in the same time period even on the same network. In addition, the response of IoT data in the system is much higher with a minimized queue, thereby making the connected network highly secured from duplicated packets. Furthermore, the designed system is combined with a machine learning algorithm by which pseudo labels are provided for each set of transmitted data, thus maximizing data privacy on a large scale.
1.3. Objectives
The proposed design for IoT representations are considered with transmission of multiple data to distributed users where the combined multi-objective case must have content as follows:
To minimize the robustness and noise factors in IoT data, thereby decreasing error functions.
To eliminate the presence of malicious nodes at low congestion factor in interconnected system operations.
To provide individual data set representations with labelled data sets even for different cluster regions.
2. Security: Analytical Representations
In order to set up a system for various expanding applications where unique design models can increase the accuracy of prediction, the mathematical approaches for IoT models are presented. However, it has been noted that individual system analysis has increased the overall complexity of network operations. Common system representations must be created and examined in order to reduce the complexity of the IoT network for different applications, which is done in this part. Additionally, the main issue of security and data privacy is also modeled mathematically using cloud storage techniques, combining all system communication layers. Every time data is communicated in the Internet of Things, it can be secured by utilizing an imprint representation in the presence of a licensed appearance. To do this, Equation (1) can be used to minimize robustness, as shown below,
where
Equation (1) indicates that it must be eliminated from the network using some represented trademarks if identical setups are generated for different data. To use the imprint configuration (2), the noise signals of the IoT data signals must be reduced as shown in the Equation:
where
describes maximum number of integrated configurations in data,
indicates total error functions.
Equation (2) shows that if transmitted data noise is decreased, it will be considerably simpler to configure the system with original data records, ensuring data privacy. The capacity of IoT transmission must be maximized with respect to system function, which can be specified using Equation (3) as follows if integrated configurations are represented.
where
Equation (3) explains that in order for IoT systems to function at high capacities, total data representations must be maximized while data separation must be carried out in underground systems. Using Equation (4), the following data replication suggests the existence of malicious nodes that must be eliminated from the network if it is operating with identical representations.
where
indicates requests that are denied from unknown users,
denotes number of detections,
, represent data privacy defense and access.
Equation (4) indicates that all malicious nodes in IoT cloud operation networks can be reduced if the number of unknown accesses is denied. However, the presence of malicious nodes is also caused by the lengthening of systems, as seen in the following formulation of Equation (5).
where
, , denote length, width and height of transmitted data, respectively.
According to Equation (5), the concentration ranges must contain the transmitted data reproduction rates. However, in IoT networks, the data only needs to be validated using Equation (6) if the nodes contain individual data owners.
where
Equation (6) indicates that individual data segments must be examined before processing the data in order to decrease the number of rogue nodes if the group of users is very large. Therefore, Equation (7) must be used to decrease the number of individual queues for group nodes in the manner shown below,
where
represents number of connected IoT nodes to central server,
denotes shortest route to reach the destination without any queue.
All of the fundamental formulations offered in Equations (1)–(7) are set up to increase network security and will be used as the standard representation for IoT data privacy systems. Equation (8) can therefore be used to obtain the objective function of the suggested approach, which is as follows:
The goal specifies a multi-objective optimization using minimization and maximization functions while keeping an eye on both benign and malicious nodes and individual data.
Section 3 states that all machine learning algorithms will be combined to check the specified objective function.
3. Machine Learning Algorithms
Machine learning algorithms are employed in real-time applications for IoT management to determine the type of attack and provide the necessary reaction elements. Since the majority of the data in IoT applications is present in enormous quantities, it is vital to identify malicious activity. Therefore, the suggested method assesses all machine learning methods, including supervised, semi-supervised, unsupervised, and reinforcement learning. To confirm the security aspects of data privacy in IoT applications, a comparison of mathematical descriptions is also required. The main benefit of integrating machine learning algorithms with predefined system models is the rapid detection of all identical occurrences, which lowers network traffic. In addition, the detection procedure is implemented using the Internet of Concession (IoC), which is processed before the data are stored inside cloud representations. Also known as user interface systems, machine learning methods can be integrated with behavior modeling techniques. In order to ensure that there are no attack scenarios in the suggested system model, the aforementioned types might therefore develop a mapping technique to detect the presence of cyber-embezzlement. All four kinds are compared using secured parametric values with a pre-trained data set that is gathered from various application platforms in order to demonstrate zero-attack situations [
21,
22].
The security features of supervised machine learning can be enabled in two steps, allowing for both internal and external supervision. Therefore, it is always required to mark the data so that external data can be mapped quickly. However, supervised learning algorithms can be used to lessen categorization issues. Equation (9) can be used to formulate the mathematical model of supervised learning for security as follows,
where
indicates a vector set of feature extraction,
represents secured labeled data,
denotes number of possible security labels to be added.
As flexibility is restricted for complicated IoT applications, semi-supervised machine learning algorithms perform an intermediate measurement between supervised and unsupervised learning. This limitation in flexibility is mostly due to the fact that both labeled and unlabeled data sets can be employed, with some IoT applications requiring safe data storage while others do not. When security is a top priority, it is typically seen that all IoT procedures are changed to manual labeling processes, which cannot provide any further protection in the system design. As a result, using labeled data in shifting data time periods is never necessary; instead, unlabeled data can also be used by grouping all duplicate data into a single cluster. Additionally, because there are unlabeled data sets present in semi-supervised learning, where continuity processes are used, the implementation cost is also decreased. Equation (10) can be used to express semi-supervised learning with a pseudo-label set mathematically for IoT security and privacy, as shown below,
where
The process of data learning typically occurs in unsupervised machine learning techniques without any peripheral node connections; as a result, the acquired data is not trained and is displayed in the same way for data privacy. The suggested solution will turn big IoT data sets for all applications into unsupervised learning, where the data will only be taught using unlabeled data.
Even in unsupervised machine learning algorithms, the distance of data transmission can be calculated using variable k measurable locations. The
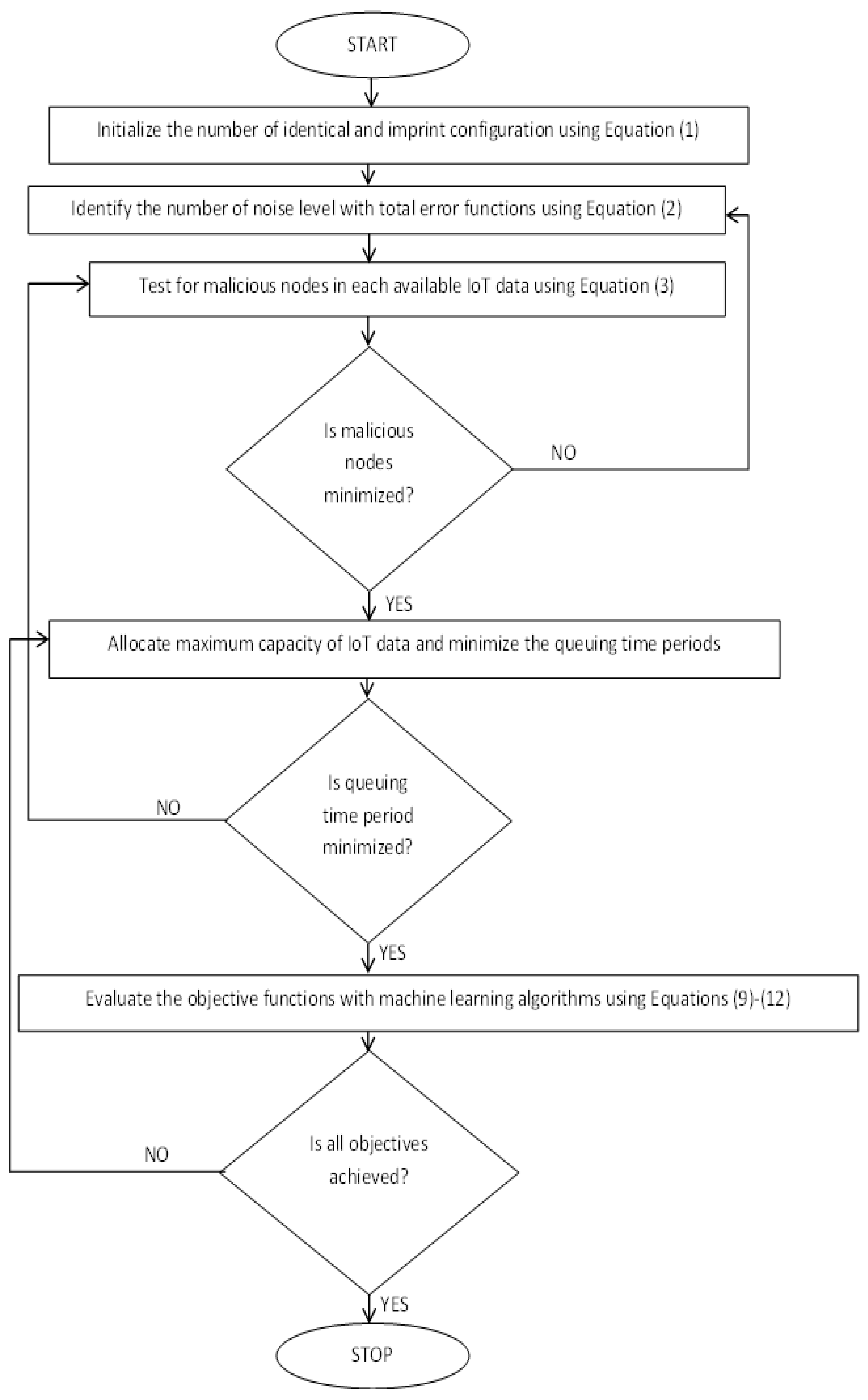
Figure 2 depicts the integrated system model with machine learning.
where
indicates number of data points,
describes the data that is present at cluster points.
The IoT activities for various applications are carried out using an agent-based model in the reinforcement machine learning technique, where actions are translated into personalized feedback with rewards. The majority of IoT activities use solely reinforcement learning algorithms, since Q-learning rates are used to calculate data privacy values. As high-dimensional goods are transformed into low-dimensional ones at output units, further relevant decisions are made using the reinforcement learning technique. Additionally, the reinforcement learning technique permits external actors to make snap judgments and actions in response to changes in the allotted time period. As a result, Equation (12) may be used to mathematically formulate the latency representations for reinforcement learning in the IoT approach as follows,
where
The suggested method integrates all of the aforementioned machine learning algorithms with the proposed system model, allowing for real-time monitoring of each algorithm’s security and privacy percentages (
Figure 1). Additionally, the proposed method uses both labeled and unlabeled sets of data, establishing excellent security for the applications in two distinct fields of interest. The following sections offer the results of integration and its comparison cases.
4. Results and Discussions
In this section, the data representation technique is tested and validated in relation to the integrated technical outcomes for the system model that are used in real-time applications. The initial steps of the test bed system for data security are initiated via wireless link establishment, which filters out unnecessary network noise. It has been noted that automatic noise introduced by external linkages into IoT networks during the experimental setup has an impact on marginal outcomes but is addressed in the early stages of development. Additionally, a marginal representation approach is employed to process IoT applications in order to cut down on the number of settings that are exactly the same for various applications. A set of training features are provided to integrated algorithms using labeled and unlabeled data sets, since the main goal of the proposed work is to choose the same system architecture for various IoT application platforms in order to monitor necessary parameters. Users of the same network can transfer data using the impression marks by connecting two distinct communication devices in device management representations. A queue will emerge for inquiry cases if the identification factor cannot be located, allowing the system to be changed to an offloading representation. Once the offloading operations for the inquiries have been finished, the data will be sent to the designated user while maintaining privacy. Extended support cannot be offered, since duplicate data in same-node systems will be destroyed if the query is not resolved. If external users satisfy the data security risk management, the central management system will determine the amount of data that must be transmitted by the user end. Additionally, real-time analysis is performed using data set representation, which takes into account the influence of outside sources on historical data from multiple users. A collection of feature values is obtained by using a labeled flow technique for transmission scenarios after converting the full data system representations. The following scenarios are used to test the effectiveness of real-time data security and privacy procedures using machine learning algorithms.
Scenario 1: Robustness and noise reduction factors.
Scenario 2: Detection of malicious nodes.
Scenario 3: Maximization of data transfer.
Scenario 4: Reduction of data queuing.
Scenario 5: Comparison of machine learning accuracy.
All the above mentioned scenarios are carried out in connection with a simulation outcome that is analyzed using MATLAB. Since the percentage of data transfer operation for different machine learning algorithms needs to be compared, such a simulation setup is considered. Further, the real-world traffic analysis with reduction in data queuing is performed by introducing additional nodes, as internal data security support is not extended. The descriptions of all scenarios are as follows.
Scenario 1
As the data transfer confidence level will be verified for efficient operations, the IoT data transmission method must always be free from robust performance. If any data is robust when a system is formed in a secure environment, then numerous steps must be taken for systems that are vulnerable to attacks, and as a result, a system removal procedure may be framed. A poor level of privacy is assigned if it is discovered that the data sequence is altered during such removal processes. Therefore, this scenario is assessed to determine the percentage of data robustness present in two alternative configurations, such as imprinting and sharing, in IoT applications. If two data sets include the same configuration, it must be removed from the system using a licensed formation technique. Because of this, separating the two data configurations will make IoT applications less robust, which in turn will boost network privacy. Additionally, where total error functions are minimized, the aforementioned setups are used to reduce the amount of noise in the data. Therefore, the noise factor for smooth processing will be reduced by the separation values between errors and identical setups.
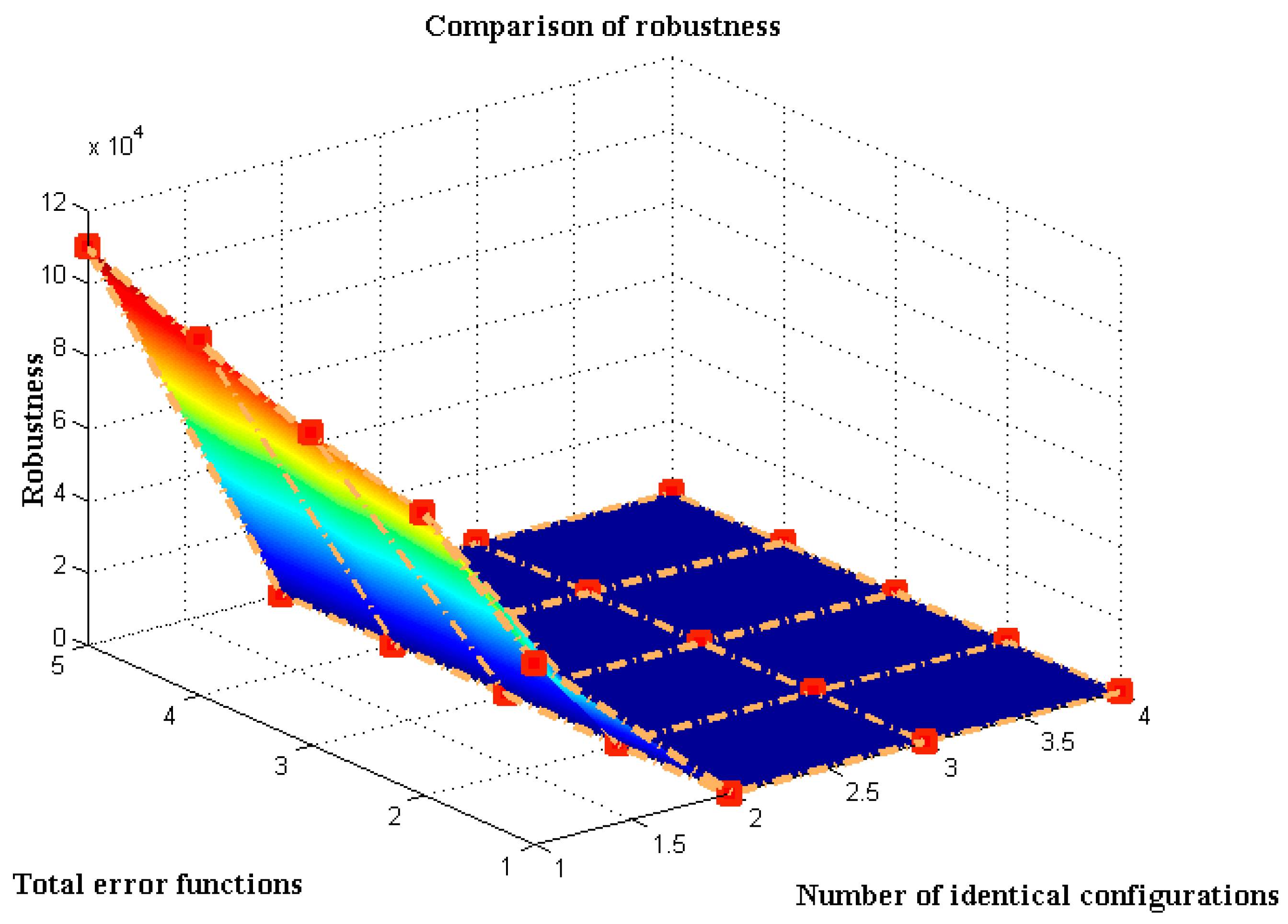
The output comparison for data robustness and noise factor, which are determined using new and current methods [
7,
17,
18], is shown in
Figure 3. The number of similar configurations is significantly bigger and equal to 50,000, 78,000, 86,000, 98,000, and 110,000, respectively, because the projected technique is integrated for studying large data set functions. The imprint modification factor must be used in the planned formulations to reduce the number of identical configurations. As a result, the error values are calculated and identified as 16, 27, 44, 61, and 83, respectively, where additional error values prevent IoT networks from processing data in a secure manner. The robustness is seen, though, as real-time values must be known from the system, even with the same level of error. After making a few observations, it was discovered that the projected method offers less robustness than the current methodology. This can be demonstrated using over 100,000 identical configurations with 83 error values. The robustness of the new and existing approaches is 52 and 147, respectively.
Scenario 2
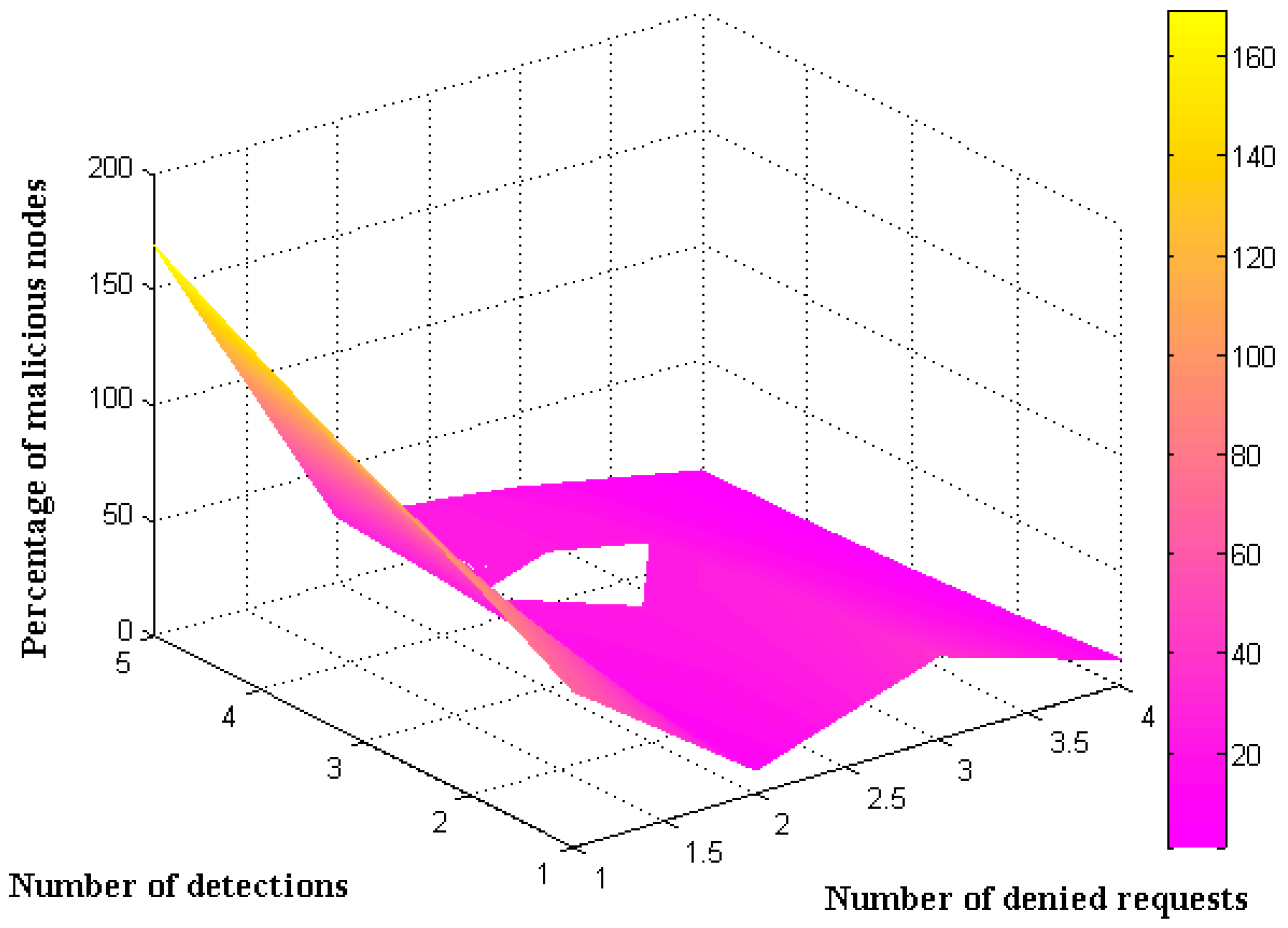
The presence of malicious nodes in an IoT network will make data security operations very difficult, so it is important to look at how many malicious nodes are present during IoT application operations. Requests must be made immediately from all users in order to examine the number of malicious nodes. If requests are not made before transmission, the data on the IoT device will be assumed to be idle. In contrast, if a request is made for data transmission, the central server examines the status of the users who made the request previously. A user can transfer data to internal receivers if the received request is legitimate, offering a secure data transmission mechanism. However, after a while, the request will be rejected by the server, which shows that some malicious nodes have been found during the data transfer. In order to prevent the presence of hostile nodes during the automated data transfer procedure, defense and access mechanisms are built. The number of malicious nodes for the proposed and existing approaches is shown in
Figure 4 [
7].
According to
Figure 4, it is reasonable to assume that each node will have a substantially higher number of denied requests for big data processing, such as 67, 94, 118, 143, and 169 with unknown detections. The number of unidentified detections in the suggested approach is also discovered to be 10, 13, 18, 24, and 28, in turn. The percentage of malicious nodes will be higher due to more unidentified detections, and it will decrease after some observations. The comparison analysis reveals that the current approach [
7,
19,
20] detects a greater number of malicious nodes because it only processes data with unlabeled requests. The number of malicious nodes is decreased by the combination mechanism in the proposed method, since it uses both labeled and unlabeled data. This is demonstrable by the 169 refused transmitter-side requests with a total of 28 unknown detections. The predicted and existing approaches in this situation have malicious node percentages of 1 and 17 percent, respectively. Therefore, the suggested method has a minimal number of malicious nodes, even in the face of a significant number of refused requests, effectively securing the data.
Scenario 3
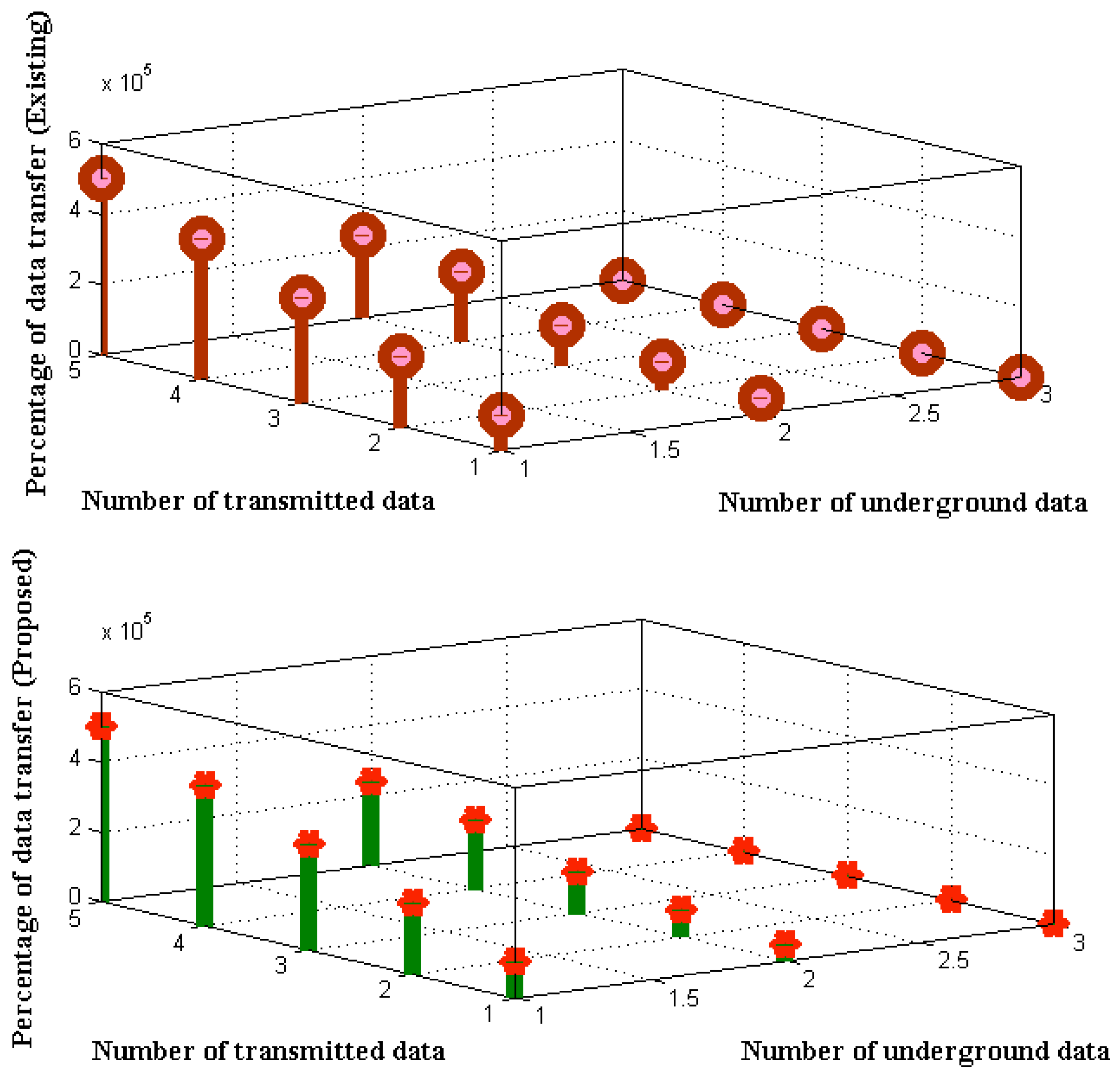
Data transfer is one of the crucial metrics in IoT applications that should be tracked in real time. When only a small quantity of data needs to be transferred, it is not necessary to examine the underground data channels; however, because the suggested method will transmit more data at once, the subsurface data must be confirmed in every situation. Furthermore, in IoT systems, the data transfer pathways of each connected node must be specified in order for independent node data transfer to occur correctly. Additionally, the number of transmissions in the system, which analyses data in three dimensions (height, breadth, and length, respectively), directly affects the amount of data transfer. Furthermore, as with subsurface IoT systems, all sent data maintain a high level of anonymity. As a result, the separated ratio of underground data transfer with transmitted data determines the percentage of data transfer functions depicted in
Figure 5.
According to
Figure 5, the quantity of subterranean data that must be transferred for IoT applications is set at 100,000,000, 200,000,000, 300,000,000, 400,000,000, and 500,000,000 bits. At first, however, only a partial amount of data is transmitted as desired by various users; 46,000, 78,000, 116,000, 198,000, and 236,000 bits of data are transferred in the initial state, with the remaining data being transmitted at the following phase of transmission. According to the amount of communicated data, it is seen that the suggested method’s percentage of data transfer after separation functions is maximized at the conclusion of every stage, whereas the maximizing of the existing method is only accomplished to a limited degree. This may be demonstrated by using beginning and final transferred bits that are set to 100,000 and 500,000, respectively, where the percentage of full data transmission for the current and predicted models using machine learning algorithms is 82, 91, and 93, respectively. Therefore, the results of the data transfer demonstrate that the suggested IoT system is capable of transferring all data without using an insufficient procedure.
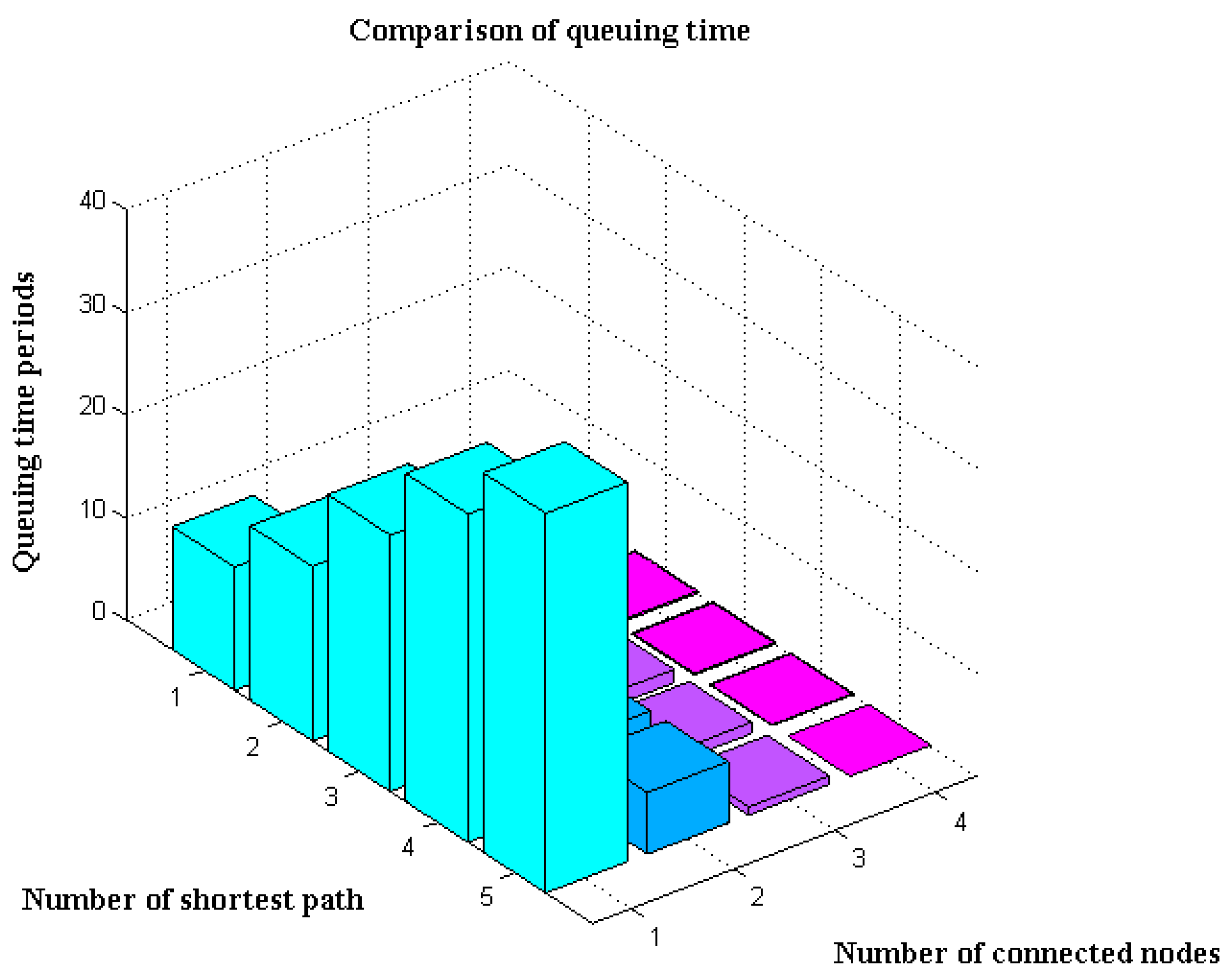
Scenario 4
The number of queuing time periods over the entire network must be kept to a minimum for data privacy in IoT applications. More time will go unused if a transmitted data packet deviates from the path and tries to remain in a specific queue. Therefore, the break will affect any remaining data, lowering the percentage of data transmissions. The proposed method tracks the duration of data queuing to prevent such reductions in data flow. Shortest routes are taken into account while determining individual paths for this type of monitoring system. However, if the first shortest path is congested, the remaining paths will be picked to prevent data queuing. Once the shortest path has been determined, the number of nodes linked to the central server for data transmission is examined; if there is a greater amount of data present, it will be transferred via alternate routes. The data transmission functions’ queuing time period is depicted in
Figure 6.
According to
Figure 6, there are 12, 17, 25, 32, and 37 connected nodes in a network, with the minimum path distances being 3, 5 and 6, respectively. Using the connected node transfer mechanism, the results of the current [
7,
17,
19] and proposed methods are compared. In the event that an existing path is made available or if it is congested with traffic, the data that is delivered for IoT applications will concentrate on alternate paths. Therefore, even when paths and distance alter in an unanticipated pattern, precise measurements of queuing time periods are still made. It can be seen from the comparison of queuing times that the current technique offers a larger queue for transmitting specific data. However, the projected model using machine learning techniques (which in this case takes into account both labeled and unlabeled data) only offers a short waiting time. This may be evaluated using six constant pathways with 25, 32, and 37 connected nodes, where the queuing times for the proposed and existing methods are respectively 1.3, 1.1, and 0.8 seconds and 0.16, 0.1, and 0 seconds.
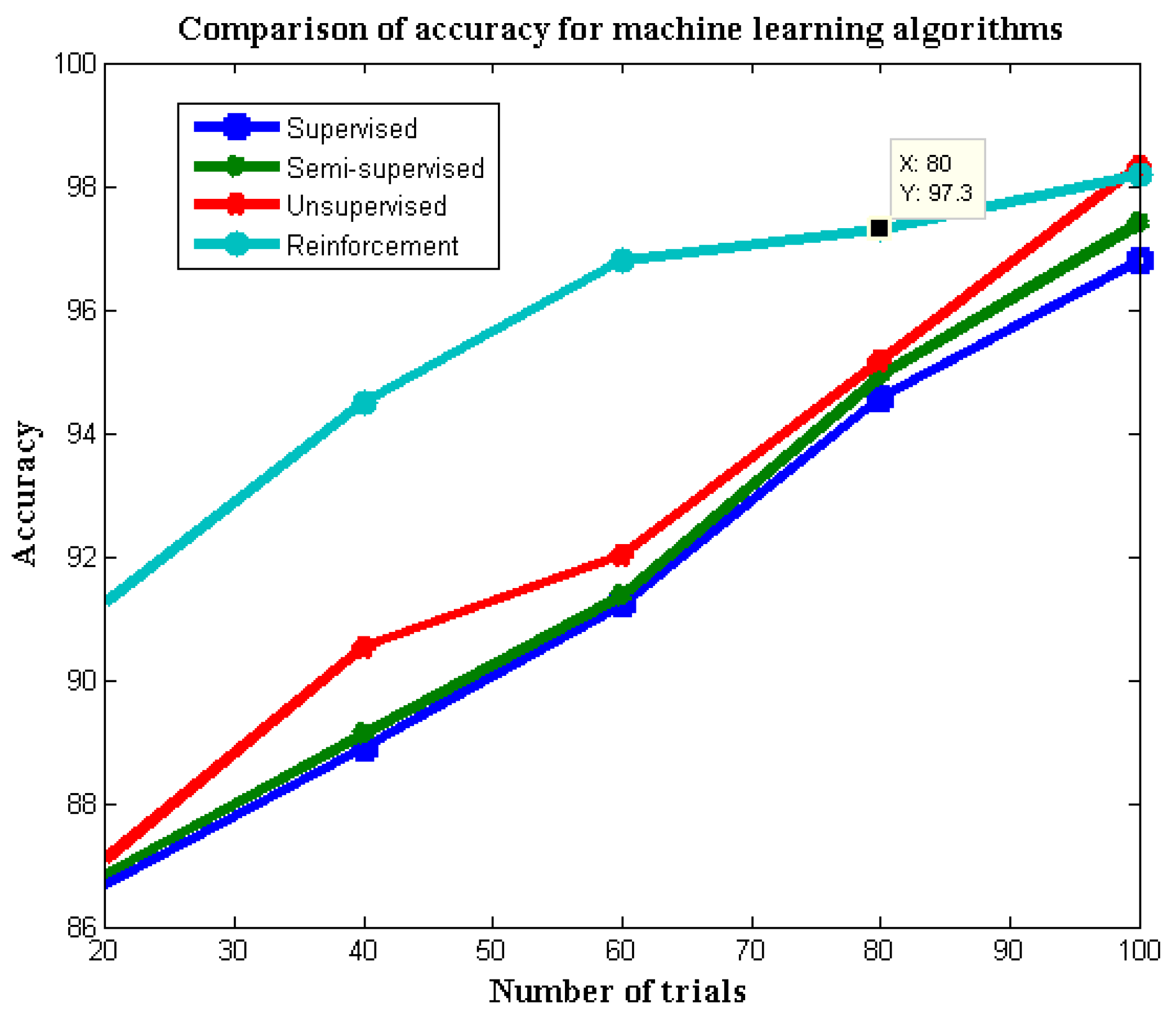
Scenario 5
For IoT applications that incorporate machine learning algorithms into a single platform, a comparison of precise measurement models is always required. Therefore, the proposed approach for measuring the percentage of accuracy for all four types of machine learning algorithms uses two sets of measurement data: one set of labeled data and the other set of unlabeled data. The suggested method carries out accuracy measurements by defining both labeled and unlabeled data, and a special case study for reinforcement learning is given. Due to these differences, the suggested method takes into account a cluster point function to determine the sample values in differentiated set functions.
Figure 7 compares the accuracy of machine learning algorithms in maintaining data for Internet of Things applications.
Input trials are shown in step variations of 20 in
Figure 7, which are increased to 100 for better observation scenarios. The analysis of both labeled and unlabeled sequence sets requires time for each iteration period, but the computing time for reinforcement learning is significantly higher than for the other three types of machine learning algorithms. Due to the existence of distinguishing characteristics in data set measures, the reinforcement learning method outperforms the other three in accuracy measurements. The accuracy of measurement for supervised, semi-supervised, unsupervised, and reinforcement learning algorithms, respectively, is equivalent to 96.8, 97.39, 98.31, and 98.18 percent. This may be confirmed using large iterations of roughly 100.
Validation Metrics
In the proposed method, performance metrics is carried out by examining data space complexity, where operations are carried out on the challenging data. The space complexity in the proposed method usually defines the data size to be present for an particular operational case study. In order to simulate such executions, a high amount of memory space is needed after wireless data transmission takes place. Thus, in the representation architecture itself a separate block is provided for data storage and analytics segments, thereby making the system perform effective data transfer operations at the same network with low complexity. Further, a large data set is provided in the case of a machine learning algorithm; therefore, the initial space complexity will be higher, and thereafter the data flow will be segmented for further reduction in complexity cases.
Figure 8 provides a comparison of space complexity with existing approaches [
17,
18] for a greater amount of data functions where the projected model proves to have low data space complexity. To verify the validation metrics, the best epochs are considered in changing steps of 20 and extend till 100 in order to determine the exact state of operation. In the starting time period before allocating the data to different segments the space complexity is higher, but after IoT data segmentation with high security the complexity is reduced. This can be proved with the best epochs of 20 and 80, where complexity for proposed method is 12 and 3 percentage, whereas with the same epoch the existing approach provides a complex data storage operation of 35 and 18 percentage, respectively. Hence, with machine learning optimization it is possible to further reduce the complexity of operations, as only the pseudo-label data set is enabled.