Efficient Secure Routing Mechanisms for the Low-Powered IoT Network: A Literature Review
Abstract
1. Introduction
- Q1.
- What are the applications utilized in IoT-LPN?
- Q2.
- What are the existing protocols in IoT-LPN and their strengths and limitations?
- Q3.
- What are the security objectives of WSN-IoT?
- Q4.
- What are the security issues and challenges in WSN-IoT?
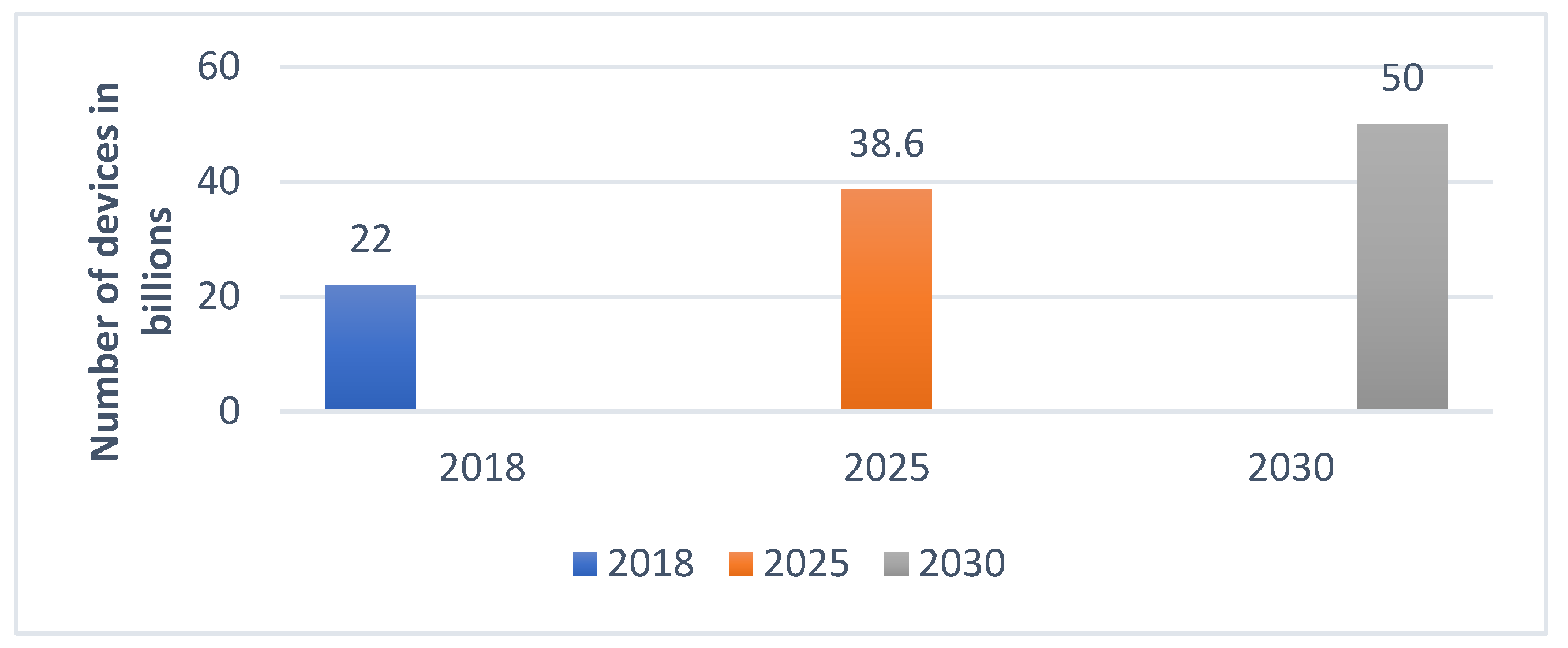
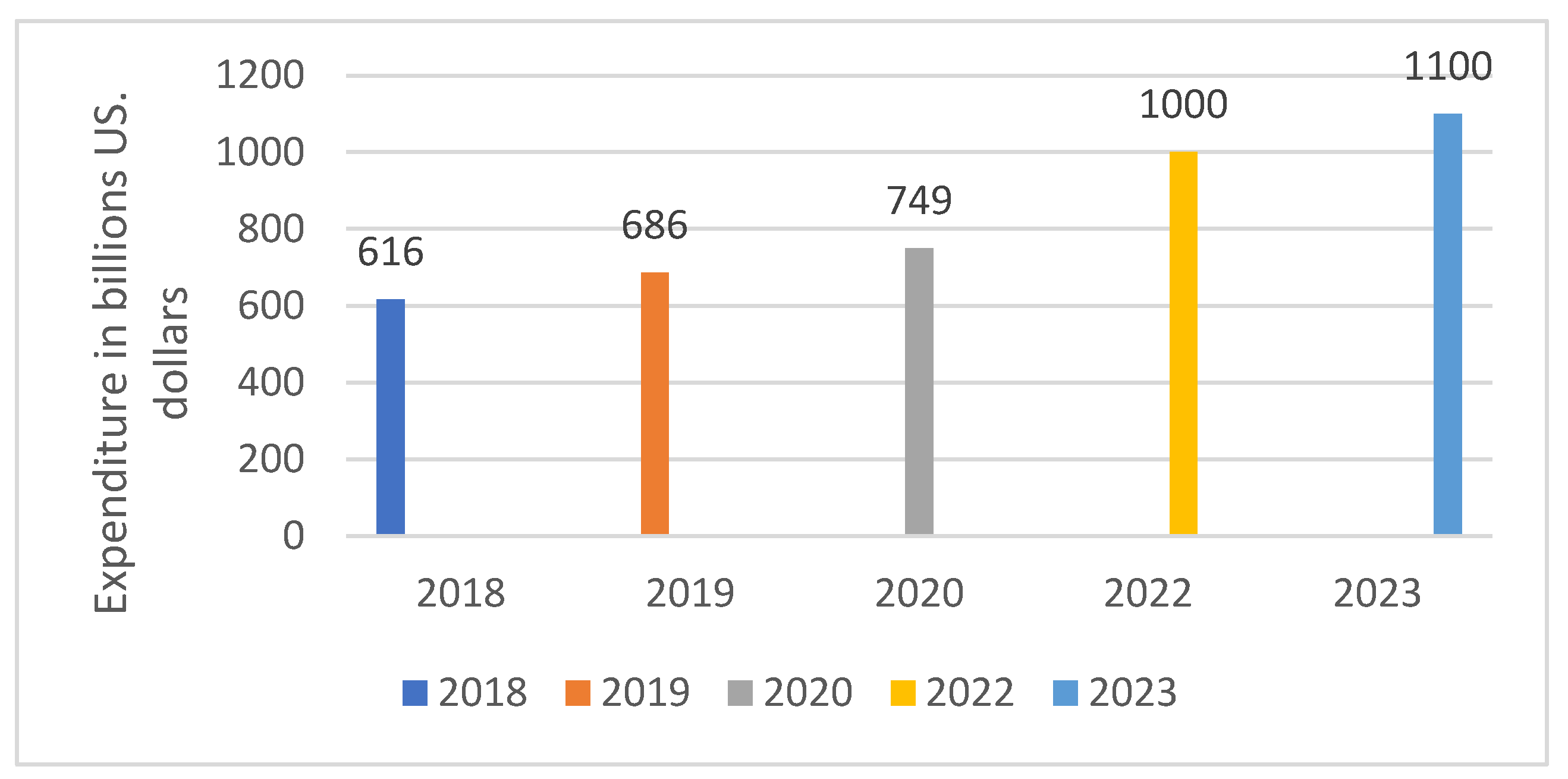
2. IoT in Industry 4.0
3. IoT-LPN Architecture and Its Applications
4. IoT-LPN Protocols
5. IoT-LPN Research Challenges
6. Security Objectives of WSN-IOT
6.1. Availability
6.2. Accountability
6.3. Confidentiality and Privacy
6.4. Auditing
6.5. Integrity
6.6. Access Control
6.7. Authentication and Authorization
7. Security Issues and Challenges in WSN-IOT
7.1. Data Confidentiality
7.2. Privacy
7.3. Trust Management
7.4. Vulnerabilities
7.5. Security
7.6. Interoperability
7.7. Identification, Authentication, and Authorization
7.8. Attacks
8. Categories of Network Attacks in WSN-IoT Layers
8.1. Physical Layer Attacks
- (1)
- Tampering
- (2)
- Malicious code injection attack
- (3)
- RF interference jamming
- (4)
- Fake node injection attack
- (5)
- Sleep denial attack
- (6)
- Side-channel attack
- (7)
- Permanent denial of service attack (PDoS)
8.2. Network Layer Attacks
- (1)
- Traffic analysis attacks
- (2)
- Wormhole attack
- (3)
- RFID spoofing and unauthorized access
- (4)
- Sybil attack
- (5)
- Routing information attack
- (6)
- Man-in-the-middle attack
- (7)
- Selective forwarding
- (8)
- Replay attack
- (9)
- Blackhole attack
- (10)
- Denial/distributed denial of service attack
8.3. Software Attacks
- (1)
- Worms, viruses, Trojan horses
- (2)
- Malware
8.4. Data Attacks
- (1)
- Data breach
- (2)
- Unauthorized access
- (3)
- Data inconsistency
9. WSN-IoT Security Mechanism in Industry 4.0
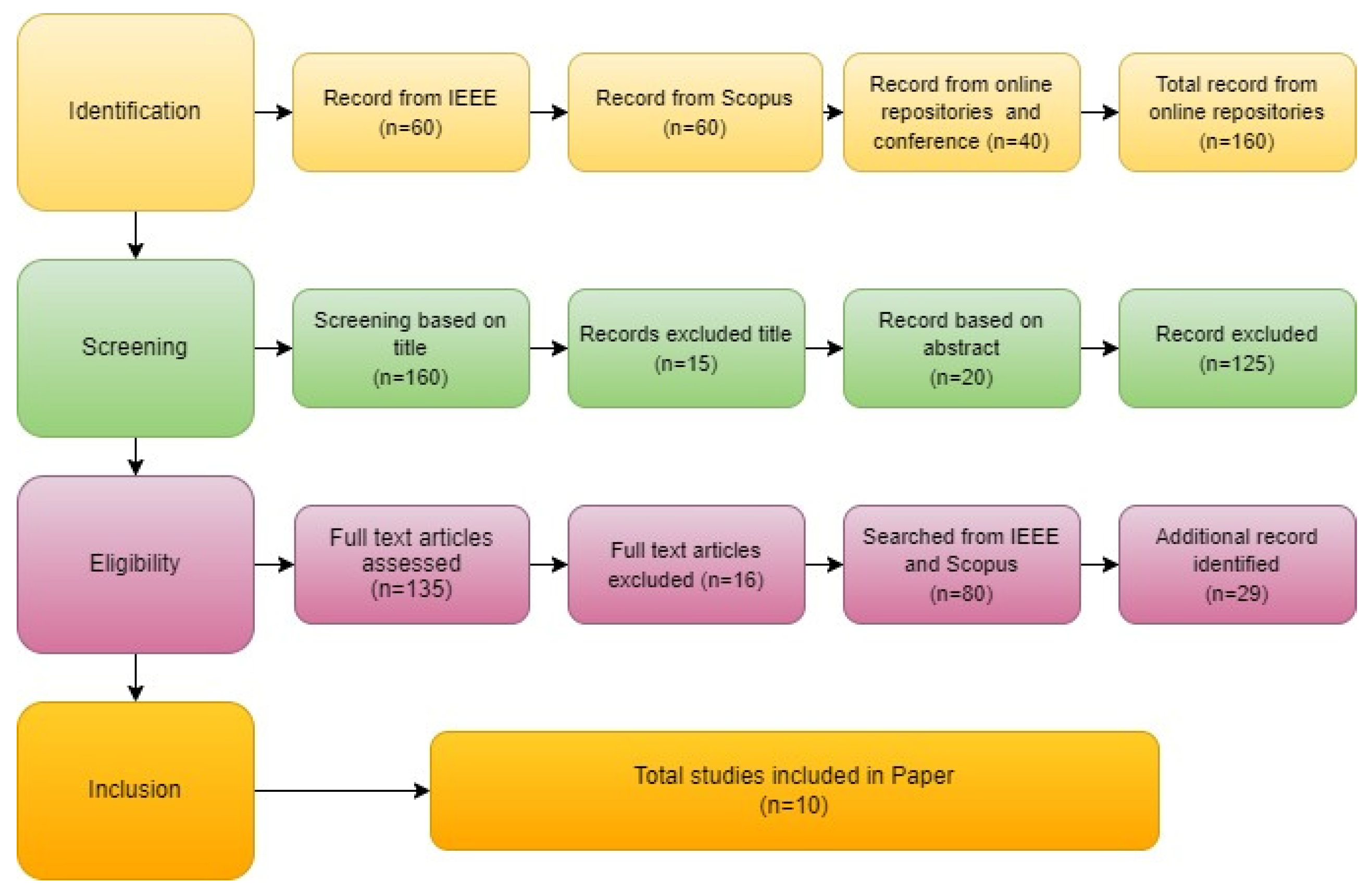
10. Existing Literature
11. Comparative Analysis
12. Conclusions and Findings
13. Future Work
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
References
- Evans, D. The Internet of Things: How the Next Evolution of the Internet Is Changing Everything. 2011. Available online: http://www.cisco.com/web/about/ac79/docs/innov/IoT_IBSG_0411FINAL (accessed on 11 December 2022).
- Lakshmi, I. The Internet of Things (IoT) and Cyber Security: Vulnerabilities, Threats, Intruders and Attacks. IOSR J. Comput. Eng. (IOSR-JCE) 2017, 19, 85–94. [Google Scholar]
- Libelium. 50 Sensor Applications for a Smarter World. 2020. Available online: https://www.libelium.com/libeliumworld/top-50-iot-sensor-applications-ranking (accessed on 11 December 2022).
- Jimenez, J.; Koster, M.; Tschofenig, H. IPSO smart objects. In a Position paper for the IOT Semantic Interoperability Workshop, 2016.
- Sethi, P.; Sarangi, S.R. Internet of things: Architectures, protocols, and applications. J. Electr. Comput. Eng. 2017, 2017, 9324035. [Google Scholar] [CrossRef]
- Statista. Several Connected Devices Worldwide 2030. 2020. Available online: https://www.statista.com/statistics/802690/worldwide-connected-devices-by-access-technology (accessed on 11 December 2022).
- Dragomir, D.; Gheorghe, L.; Costea, S.; Radovici, A. A survey on secure communication protocols for IoT systems. In Proceedings of the 2016 International Workshop on Secure Internet of Things (SIoT), Heraklion, Greece, 26–30 September 2016; pp. 47–62. [Google Scholar]
- Pishva, D. Internet of Things: Security and privacy issues and possible solution. In Proceedings of the 2017 19th International Conference on Advanced Communication Technology (ICACT), PyeongChang, Republic of Korea, 19–22 February 2017; pp. 797–808. [Google Scholar]
- Huawei. Tap into New Growth with Intelligent Connectivity. 2018. Available online: https://www.huawei.com/minisite/gci/assets/files/gci_2018_whitepaper_en.pdf?v=20180716 (accessed on 11 December 2022).
- Vega, M. Internet of things statistics facts & predictions [2020’s update]. Retrieved Novemb. 2020, 30, 2020. [Google Scholar]
- Mukherjee, B. Iot Statistics for 2020. Available online: https://www.stoodnt.com/blog/iot-statistics-for-2020 (accessed on 8 November 2020).
- Tan, X.; Su, S.; Huang, Z.; Guo, X.; Zuo, Z.; Sun, X.; Li, L. Wireless sensor networks intrusion detection based on SMOTE and the random forest algorithm. Sensors 2019, 19, 203. [Google Scholar] [CrossRef] [PubMed]
- Ostadal, R.; Matyas, V.; Svenda, P.; Nemec, L. Crowdsourced security reconstitution for wireless sensor networks: Secrecy amplification. Sensors 2019, 19, 5041. [Google Scholar] [CrossRef]
- Gendreau, A.A.; Moorman, M. Survey of intrusion detection systems towards an end-to-end secure internet of things. In Proceedings of the 2016 IEEE 4th International Conference on the Future Internet of Things and Cloud (FiCloud), Vienna, Austria, 22–24 August 2016; pp. 84–90. [Google Scholar]
- Lee, C.-C. Security and privacy in wireless sensor networks: Advances and challenges. Sensors 2020, 20, 744. [Google Scholar] [CrossRef]
- Sicari, S.; Rizzardi, A.; Grieco, L.A.; Coen-Porisini, A. Security, privacy and trust in Internet of Things: The road ahead. Comput. Netw. 2015, 76, 146–164. [Google Scholar] [CrossRef]
- Zhou, J.; Cao, Z.; Dong, X.; Vasilakos, A.V. Security and privacy for cloud-based IoT: Challenges. IEEE Commun. Mag. 2017, 55, 26–33. [Google Scholar] [CrossRef]
- Alansari, Z.; Prasanth, A.; Belgaum, M. A comparison analysis of fault detection algorithms in wireless sensor networks. In Proceedings of the 2018 International Conference on Innovation and Intelligence for Informatics, Computing, and Technologies (3ICT), Sakhier, Bahrain, 18–20 November 2018; pp. 1–6. [Google Scholar] [CrossRef]
- Lee, T.H.; Xie, X.S.; Chang, L. RSSI-based IPv6 routing metrics for RPL in low-power and lossy networks. In Proceedings of the 2014 IEEE International Conference on Systems, Man, and Cybernetics (SMC), San Diego, CA, USA, 5–8 October 2014; pp. 1714–1719. [Google Scholar]
- Nafchi, M.Z.; Mohelská, H. Organizational culture as an indication of readiness to implement industry 4.0. Information 2020, 11, 174. [Google Scholar] [CrossRef]
- Oluyisola, O.E.; Sgarbossa, F.; Strandhagen, J.O. Smart production planning and control: Concept, use-cases and sustainability implications. Sustainability 2020, 12, 3791. [Google Scholar] [CrossRef]
- Müller, J.M.; Buliga, O.; Voigt, K.-I. Fortune favors the prepared: How SMEs approach business model innovations in Industry 4.0. Technol. Forecast. Soc. Chang. 2018, 132, 2–17. [Google Scholar] [CrossRef]
- Posada, J.; Toro, C.; Barandiaran, I.; Oyarzun, D.; Stricker, D.; De Amicis, R. Visual computing as a key enabling technology for industrie 4.0 and industrial internet. IEEE Comput. Graph. Appl. 2015, 35, 26–40. [Google Scholar] [CrossRef] [PubMed]
- Lange, S.; Pohl, J.; Santarius, T. Digitalization and energy consumption. Does ICT reduce energy demand? Ecol. Econ. 2020, 176, 106760. [Google Scholar] [CrossRef]
- Khan, I.U.; Qureshi, I.M.; Aziz, M.A.; Cheema, T.A.; Shah, S.B.H. Smart IoT Control-Based Nature Inspired Energy Efficient Routing Protocol for Flying Ad Hoc Network (FANET). IEEE Access 2020, 8, 56371–56378. [Google Scholar] [CrossRef]
- Priyadarsini, M.; Bera, P. Software-defined networking architecture, traffic management, security, and placement: A survey. Comput. Netw. 2021, 192, 108047. [Google Scholar] [CrossRef]
- Radel, J. Organizational Change and Industry 4.0 (id4). A perspective on possible future challenges for Human Resources Management. Ind. Von Morgen 2017, 5, 32–39. [Google Scholar]
- Barriquello, C.H.; Denardin, G.W.; Campos, A. A geographic routing approach for IPv6 in large-scale low-power and lossy networks. Comput. Electr. Eng. 2015, 45, 182–191. [Google Scholar] [CrossRef]
- Zhao, M.; Ho, I.W.-H.; Chong, P.H.J. An energy-efficient region-based RPL routing protocol for low-power and lossy networks. IEEE Internet Things J. 2016, 3, 1319–1333. [Google Scholar] [CrossRef]
- Liu, B.; Anand, S.V.; Perkins, C.E.; Anamalamudi, S.; Zhang, M. Asymmetric AODV-P2P-RPL in Low-Power and Lossy Networks (LLNs) 2019.
- Lorente, G.G.; Lemmens, B.; Carlier, M.; Braeken, A.; Steenhaut, K. BMRF: Bidirectional multicast RPL forwarding. Ad Hoc Netw. 2017, 54, 69–84. [Google Scholar] [CrossRef]
- Gaddour, O.; Koubâa, A.; Abid, M. Quality-of-service aware routing for static and mobile IPv6-based low-power and lossy sensor networks using RPL. Ad Hoc Netw. 2015, 33, 233–256. [Google Scholar] [CrossRef]
- Fotouhi, H.; Moreira, D.; Alves, M. mRPL: Boosting mobility in the Internet of Things. Ad Hoc Netw. 2015, 26, 17–35. [Google Scholar] [CrossRef]
- Bouaziz, M.; Rachedi, A.; Belghith, A.; Berbineau, M.; Al-Ahmadi, S. EMA-RPL: Energy and mobility aware routing for the Internet of Mobile Things. Future Gener. Comput. Syst. 2019, 97, 247–258. [Google Scholar] [CrossRef]
- Qiu, T.; Lv, Y.; Xia, F.; Chen, N.; Wan, J.; Tolba, A. ERGID: An efficient routing protocol for emergency response Internet of Things. J. Netw. Comput. Appl. 2016, 72, 104–112. [Google Scholar] [CrossRef]
- Kelsey, R.; Hui, J. Multicast Protocol for Low-Power and Lossy Networks (MPL), IETF, RFC 7731, 2016.
- Fadeel, K.Q.A.; El Sayed, K. ESMRF: Enhanced stateless multicast RPL forwarding for IPv6-based low-power and lossy networks. In Proceedings of the 2015 Workshop on IoT challenges in Mobile and Industrial Systems, Florence, Italy, 18 May 2015; pp. 19–24. [Google Scholar]
- Tahir, Y.; Yang, S.; McCann, J. BRPL: Backpressure RPL for high-throughput and mobile IoTs. IEEE Trans. Mob. Comput. 2017, 17, 29–43. [Google Scholar] [CrossRef]
- Bouaziz, M.; Rachedi, A.; Belghith, A. EKF-MRPL: Advanced mobility support routing protocol for internet of mobile things: Movement prediction approach. Future Gener. Comput. Syst. 2019, 93, 822–832. [Google Scholar] [CrossRef]
- Taghizadeh, S.; Bobarshad, H.; Elbiaze, H. CLRPL: Context-aware and load balancing RPL for IoT networks under heavy and highly dynamic load. IEEE Access 2018, 6, 23277–23291. [Google Scholar] [CrossRef]
- De Poorter, E.; Hoebeke, J.; Strobbe, M.; Moerman, I.; Latré, S.; Weyn, M. Sub-GHz LPWAN network coexistence, management, and virtualization: An overview and open research challenges. Wirel. Pers. Commun. 2017, 95, 187–213. [Google Scholar] [CrossRef]
- FarmBeats: AI, Edge & IoT for Agriculture. 2015. Available online: https://www.microsoft.com/en-us/research/project/farmbeats-iot-agriculture/ (accessed on 11 December 2022).
- Buurman, B.; Kamruzzaman, J.; Karmakar, G.; Islam, S. Low-power wide-area networks: Design goals, architecture, suitability to use cases and research challenge. IEEE Access 2020, 8, 17179–17220. [Google Scholar] [CrossRef]
- Ferrag, M.A.; Maglaras, L.A.; Janicke, H.; Jiang, J.; Shu, L. Authentication protocols for the internet of things: A comprehensive survey. Secur. Commun. Networks 2017, 2017, 6562953. [Google Scholar] [CrossRef]
- Iqbal, M.A.; Olaleye, O.G.; Bayoumi, M.A. A review on internet of things (IoT): Security and privacy requirements and the solution approach. Glob. J. Comput. Sci. Technol. 2016, 16, 1–9. [Google Scholar]
- Ravindran, R.; Yomas, J.; Sebastian, E.J. IoT: A review on security issues and measures. Int. J. Eng. Sci. Technol. 2015, 5, 348–351. [Google Scholar]
- Yan, Z.; Zhang, P.; Vasilakos, A.V. A survey on trust management for Internet of Things. J. Netw. Comput. Appl. 2014, 42, 120–134. [Google Scholar] [CrossRef]
- Sun, Y.; Apostolaki, M.; Birge-Lee, H.; Vanbever, L.; Rexford, J.; Chiang, M.; Mittal, P. Mittal Securing internet applications from routing attacks. Commun. ACM 2021, 64, 86–96. [Google Scholar] [CrossRef]
- Rajasekar, V.; Rajkumar, S. A Study on Impact of DIS flooding Attack on RPL-based 6LowPAN Network. Microprocess. Microsyst. 2022, 94, 104675. [Google Scholar] [CrossRef]
- Dalipi, F.; Yayilgan, S.Y. Security and privacy considerations for iot application on smart grids: Survey and research challenges. In Proceedings of the 2016 IEEE 4th International Conference on Future Internet of Things and Cloud Workshops (FiCloudW), Vienna, Austria, 22–24 August 2016; pp. 63–68. [Google Scholar]
- Fink, G.A.; Zarzhitsky, D.V.; Carroll, T.E.; Farquhar, E.D. Security and privacy grand challenges for the Internet of Things. In Proceedings of the 2015 International Conference on Collaboration Technologies and Systems (CTS), Atlanta, GA, USA, 1–5 June 2015; pp. 27–34. [Google Scholar]
- Henze, M.; Hermerschmidt, L.; Kerpen, D.; Häußling, R.; Rumpe, B.; Wehrle, K. A comprehensive approach to privacy in the cloud-based Internet of Things. Future Gener. Comput. Syst. 2016, 56, 701–718. [Google Scholar] [CrossRef]
- Hossain, M.M.; Fotouhi, M.; Hasan, R. Towards an analysis of security issues, challenges, and open problems in the internet of things. In Proceedings of the 2015 IEEE World Congress on Services, New York, NY, USA, 27 June–2 July 2015; pp. 21–28. [Google Scholar]
- Ling, Z.; Liu, K.; Xu, Y.; Jin, Y.; Fu, X. An end-to-end view of iot security and privacy. In Proceedings of the GLOBECOM 2017—2017 IEEE Global Communications Conference, Singapore, 4–8 December 2017; pp. 1–7. [Google Scholar]
- Sicari, S.; Rizzardi, A.; Miorandi, D.; Coen-Porisini, A. REATO: REActing TO Denial of Service attacks in the Internet of Things. Comput. Netw. 2018, 137, 37–48. [Google Scholar] [CrossRef]
- Abomhara, M. Department of Information and Communication Technology, University of Agder, Norway, GM Køien, and Department of Information and Communication Technology, University of Agder, Norway, Cyber security and the internet of things: Vulnerabilities, threats, intruders and attacks. J. Cyber Secur. Mobil. 2015, 4, 65–88. [Google Scholar]
- Alaba, F.A.; Othman, M.; Hashem, I.A.T.; Alotaibi, F. Internet of Things security: A survey. J. Netw. Comput. Appl. 2017, 88, 10–28. [Google Scholar] [CrossRef]
- Zhou, J.; Dong, X.; Cao, Z.; Vasilakos, A.V. Secure and privacy-preserving protocol for cloud-based vehicular DTNs. IEEE Trans. Inf. Forensics Secur. 2015, 10, 1299–1314. [Google Scholar] [CrossRef]
- Granjal, J.; Monteiro, E.; Silva, J.S. Security for the internet of things: A survey of existing protocols and open research issues. IEEE Commun. Surv. Tutor. 2015, 17, 1294–1312. [Google Scholar] [CrossRef]
- Ranjan, A.K.; Somani, G. Access control and authentication in the internet of things environment. In Connectivity Frameworks for Smart Devices; Springer: Berlin/Heidelberg, Germany, 2016; pp. 283–305. [Google Scholar]
- Iotforall. The Role of IoT and Industry 4.0 in Creating Digital Factories of Tomorrow. 2022. Available online: https://www.iotforall.com/the-role-of-iot-and-industry-4-0-in-creating-digital-factories-of-tomorrow (accessed on 11 December 2022).
- Zaldivar, D.; Lo, A.T.; Muheidat, F. Investigating the security threats on networked medical devices. In Proceedings of the 2020 10th Annual Computing and Communication Workshop and Conference (CCWC), Las Vegas, NV, USA, 6–8 January 2020; pp. 0488–0493. [Google Scholar]
- Lo’ai, A.T.; Somani, T.F. More secure Internet of Things using robust encryption algorithms against side-channel attacks. In Proceedings of the 2016 IEEE/ACS 13th International Conference of Computer Systems and Applications (AICCSA), Agadir, Morocco, 29 November–2 December 2016; pp. 1–6. [Google Scholar]
- Liu, X.; Zhao, M.; Li, S.; Zhang, F.; Trappe, W. A security framework for the internet of things in the future internet architecture. Future Internet 2017, 9, 27. [Google Scholar] [CrossRef]
- Dabbagh, M.; Rayes, A. Internet of things security and privacy. In The Internet of Things from Hype to Reality; Springer: Berlin/Heidelberg, Germany, 2019; pp. 211–238. [Google Scholar]
- Perera, C.; Ranjan, R.; Wang, L.; Khan, S.U.; Zomaya, A.Y. Big data privacy in the internet of things era. IT Prof. 2015, 17, 32–39. [Google Scholar] [CrossRef]
- Ziegeldorf, J.H.; Morchon, O.G.; Wehrle, K. Privacy in the Internet of Things: Threats and challenges. Secur. Commun. Netw. 2014, 7, 2728–2742. [Google Scholar] [CrossRef]
- Vasilomanolakis, E.; Daubert, J.; Luthra, M.; Gazis, V.; Wiesmaier, A.; Kikiras, P. On the security and privacy of internet of things architectures and systems. In Proceedings of the 2015 International Workshop on Secure Internet of Things (SIoT), Vienna, Austria, 21–25 September 2015; pp. 49–57. [Google Scholar]
- Frustaci, M.; Pace, P.; Aloi, G.; Fortino, G. Evaluating critical security issues of the IoT world: Present and future challenges. IEEE Internet Things J. 2017, 5, 2483–2495. [Google Scholar] [CrossRef]
- Gai, K.; Choo, K.-K.R.; Qiu, M.; Zhu, L. Privacy-preserving content-oriented wireless communication in internet-of-things. IEEE Internet Things J. 2018, 5, 3059–3067. [Google Scholar] [CrossRef]
- Glissa, G.; Rachedi, A.; Meddeb, A. A secure routing protocol based on RPL for Internet of Things. In Proceedings of the 2016 IEEE Global Communications Conference (GLOBECOM), Washington, DC, USA, 4–8 December 2016; pp. 1–7. [Google Scholar]
- Boubiche, D.E.; Athmani, S.; Boubiche, S.; Toral-Cruz, H. Cybersecurity issues in wireless sensor networks: Current challenges and solutions. Wirel. Pers. Commun. 2021, 117, 177–213. [Google Scholar] [CrossRef]
- Safdar, Z.; Farid, S.; Pasha, M.; Safdar, K. A security model for iot based systems. Tech. J. 2017, 22. [Google Scholar]
- Saibabu, G.; Jain, A.; Sharma, V. Security issues and challenges in IoT routing over wireless communication. Int. J. Innov. Technol. Explor. Eng. 2020, 9, 1572–1580. [Google Scholar]
- Desai, D.; Upadhyay, H. Security and privacy consideration for the internet of things in smart home environments. Int. J. Eng. Res. Dev. 2014, 10, 73–83. [Google Scholar]
- Wittenberg, C. Cause the trending Industry 4.0 in the automated industry to new requirements on user interfaces? In Proceedings of the International Conference on Human-Computer Interaction, Bamberg, Germany, 14–18 September 2015; pp. 238–245. [Google Scholar]
- Singh, M.; Rajan, M.; Shivraj, V.; Balamuralidhar, P. Secure mqtt for the internet of things (iot). In Proceedings of the 2015 Fifth International Conference on Communication Systems and Network Technologies, Gwalior, MP, India, 4–6 April 2015; pp. 746–751. [Google Scholar]
- Sengupta, J.; Ruj, S.; Bit, S.D. A comprehensive survey on attacks, security issues and blockchain solutions for IoT and IIoT. J. Netw. Comput. Appl. 2020, 149, 102481. [Google Scholar] [CrossRef]
- Herceg, I.V.; Kuč, V.; Mijušković, V.M.; Herceg, T. Challenges and driving forces for industry 4.0 implementation. Sustainability 2020, 12, 4208. [Google Scholar] [CrossRef]
- Adat, V.; Gupta, B. A DDoS attack mitigation framework for internet of things. In Proceedings of the 2017 International Conference on Communication and Signal Processing (ICCSP), Chennai, India, 6–8 April 2017; pp. 2036–2041. [Google Scholar]
- Ahemd, M.M.; Shah, M.A.; Wahid, A. IoT security: A layered approach for attacks & defenses. In Proceedings of the 2017 International Conference on Communication Technologies (ComTech), Rawalpindi, Pakistan, 19–21 April 2017; pp. 104–110. [Google Scholar]
- Airehrour, D.; Gutierrez, J.A.; Ray, S.K. SecTrust-RPL: A secure trust-aware RPL routing protocol for Internet of Things. Future Gener. Comput. Syst. 2019, 93, 860–876. [Google Scholar] [CrossRef]
- Al-Turjman, F.; Alturjman, S. Context-sensitive access in the industrial internet of things (IIoT) healthcare applications. IEEE Trans. Ind. Inform. 2018, 14, 2736–2744. [Google Scholar] [CrossRef]
- Varga, P.; PLoSz, S.; Soos, G.; Hegedus, C. Security threats and issues in automation IoT. In Proceedings of the 2017 IEEE 13th International Workshop on Factory Communication Systems (WFCS), Trondheim, Norway, 31 May–2 June 2017; pp. 1–6. [Google Scholar]
- Benazzouz, Y.; Munilla, C.; Günalp, O.; Gallissot, M.; Gürgen, L. Sharing user IoT devices in the cloud. In Proceedings of the 2014 IEEE World Forum on Internet of Things (WF-IoT), Seoul, Republic of Korea, 6–8 March 2014; pp. 373–374. [Google Scholar]
- Kumar, S.A.; Vealey, T.; Srivastava, H. Security in the internet of things: Challenges, solutions, and future directions. In Proceedings of the 2016 49th Hawaii International Conference on System Sciences (HICSS), Koloa, HI, USA, 5–8 January 2016; pp. 5772–5781. [Google Scholar]
- Huawei. Iot_Security_White_Paper_2018_V2_En.Pdf. 2018. Available online: https://carrier.huawei.com/~/media/CNBG/Downloads/Spotlight/iot-as-a-service/liantong0929-en.pdf (accessed on 12 December 2022).
- Alansari, Z.; Anuar, N.; Kamsin, A.; Belgaum, M. A systematic review of routing attacks detection in wireless sensor networks. PeerJ. Comput. Sci. 2022, 8, e1135. [Google Scholar] [CrossRef]
- Thiagarajan, S. Raising Your IoT Security Game. 2018. Available online: https://docplayer.net/90481457-Opportunities-raising-your-iot-security-game-how-to-pursue-the-author.html (accessed on 12 December 2022).
- Djedjig, N.; Tandjaoui, D.; Medjek, F.; Romdhani, I. Trust-aware and cooperative routing protocol for IoT security. J. Inf. Secur. Appl. 2020, 52, 102467. [Google Scholar] [CrossRef]
- Behera, T.M.; Mohapatra, S.K.; Samal, U.C.; Khan, M.S.; Daneshmand, M.; Gandomi, A.H. Residual energy-based cluster-head selection in WSNs for IoT application. IEEE Internet Things J. 2019, 6, 5132–5139. [Google Scholar] [CrossRef]
- Tan, Y.; Yang, W.; Yoshida, K.; Takakuwa, S. Application of IoT-aided simulation to manufacturing systems in the cyber-physical system. Machines 2019, 7, 2. [Google Scholar] [CrossRef]
- Haque, M.; Asikuzzaman, M.; Khan, I.U.; Ra, I.-H.; Hossain, M.; Shah, S.B.H. Comparative study of IoT-based topology maintenance protocol in a wireless sensor network for structural health monitoring. Remote Sens. 2020, 12, 2358. [Google Scholar] [CrossRef]
- Bulaghi, Z.A.; Navin, A.H.Z.; Hosseinzadeh, M.; Rezaee, A. SENET: A novel architecture for IoT-based body sensor networks. Inform. Med. Unlocked 2020, 20, 100365. [Google Scholar] [CrossRef]
- Sharma, R.; Prakash, S. Enhancement of relay nodes communication approach in WSN-IoT for underground coal mine. J. Inf. Optim. Sci. 2020, 41, 521–531. [Google Scholar] [CrossRef]
- Kamel, S.O.M.; Hegazi, N.H. A proposed model of IoT security management system, based on a study of internet of things (IoT) security. Int. J. Sci. Eng. Res. 2018, 9, 1227–1244. [Google Scholar]
- Rathee, G.; Balasaraswathi, M.; Chandran, K.P.; Gupta, S.D.; Boopathi, C. A secure IoT sensors communication in industry 4.0 using blockchain technology. J. Ambient. Intell. Humaniz. Comput. 2021, 12, 533–545. [Google Scholar] [CrossRef]
- Garg, S.; Kaur, K.; Kaddoum, G.; Choo, K.-K.R. Toward secure and provable authentication for Internet of Things: Realizing industry 4.0. IEEE Internet Things J. 2019, 7, 4598–4606. [Google Scholar] [CrossRef]
- Wan, J.; Tang, S.; Shu, Z.; Li, D.; Wang, S.; Imran, M. Software-defined industrial internet of things in the context of industry 4.0. IEEE Sens. J. 2016, 16, 7373–7380. [Google Scholar] [CrossRef]
- Rahman, A.; Sara, U.; Kundu, D.; Islam, S.; Islam, M.; Hasan, M. Distb-sdoindustry: Enhancing security in industry 4.0 services based on the distributed blockchain through software-defined networking-IoT enabled architecture. arXiv 2020, arXiv:2012.10011. [Google Scholar] [CrossRef]
- Wu, Y.; Dai, H.-N.; Wang, H. Convergence of blockchain and edge computing for secure and scalable IIoT critical infrastructures in industry 4.0. IEEE Internet Things J. 2020, 8, 2300–2317. [Google Scholar] [CrossRef]
- Wan, J.; Chen, B.; Imran, M.; Tao, F.; Li, D.; Li, C. Toward dynamic resources management for IoT-based manufacturing. IEEE Commun. Mag. 2018, 56, 52–59. [Google Scholar] [CrossRef]
- Hornillo-Mellado, S.; Martín-Clemente, R.; Baena-Lecuyer, V. Prediction of satellite shadowing in smart cities with application to IoT. Sensors 2020, 20, 475. [Google Scholar] [CrossRef]
- Dasgupta, S.; Saha, B. HMA-ID mechanism: A hybrid mayfly optimization-based apriori approach for intrusion detection in a big data application. Telecommun. Syst. 2022, 80, 77–89. [Google Scholar] [CrossRef]
- Samy, A.; Yu, H.; Zhang, H. Fog-based attack detection framework for the internet of things using deep learning. IEEE Access 2020, 8, 74571–74585. [Google Scholar] [CrossRef]
- Anbar, M.; Al-Amiedy, T.; Hasbullah, I. Routing Protocol for Low Power and Lossy Network. Encyclopedia. Available online: https://encyclopedia.pub/entry/23039 (accessed on 19 December 2022).
- Alimi, K.O.A.; Ouahada, K.; Abu-Mahfouz, A.; Rimer, S. A survey on the security of low power wide area networks: Threats, challenges, and potential solutions. Sensors 2020, 20, 5800. [Google Scholar] [CrossRef] [PubMed]
- Raza, U.; Kulkarni, P.; Sooriyabandara, N. Low power wide area networks: An overview. IEEE Commun. Surv. Tutor. 2017, 19, 855–873. [Google Scholar] [CrossRef]
- Muzammal, S.M.; Murugesan, R.K.; Jhanjhi, N.; Hossain, M.; Yassine, A. Trust and Mobility-Based Protocol for Secure Routing in the Internet of Things. Sensors 2022, 22, 6215. [Google Scholar] [CrossRef] [PubMed]
| Protocol | Foundation | Routing Solution | Description | Strengths | Limitations |
|---|---|---|---|---|---|
| ER-RPL [28] | RPL | P2P support | ER-RPL prevents the whole network from flooding with P2P route-finding packets, lowering network energy usage. Furthermore, the technique enables the transmission of P2P messages and utilizes the structure produced by default RPL for various traffic patterns. | It prevents the whole network from flooding with P2P control messages, resulting in significant energy savings and an increase in the P2P packet delivery ratio. | Some location-aware nodes are required (e.g., GPS) to have a complex strategy; additional control messages are added in addition to the essential RPL messages. |
| P2P-RPL [29,30] | RPL | P2P support | P2P-RPL allows RPL networks to have better P2P data traffic and develops new P2P routes on demand as an alternative to RPL-built P2P routes. Communications sent between these nodes follow a single path. | Allows for constructing alternative P2P routes to meet application routing needs while avoiding using a root node for P2P message forwarding. | Increases the overheads and energy consumption of the network by flooding it with control packets. |
| geographic routing approachGeoRank [31] | RLP and Greedy Other Adaptive Face Routing GOAFR | P2P support | GeoRank seeks to improve 6LoWPAN’s P2P functionality and minimize the number of control messages needed. It first uses the list of DODAG roots to determine the distance between the source and destination. The node transmits a message to its neighbor with one hop to the message destination and then passes the packet to the referenced parent. | Reduces scalability by avoiding the usage of DAO messages, allowing memory consumption. | RPL control messages are changed by default. Static nodes or GPS-enabled devices are required. |
| BMRF [32] | SMRF and RPL | Multicast communication | Except for the root node, when a node in the BMRF wants to send a multicast message, it sends it upstream and downward. Upward sending is conducted using unicast transmission, whereas downward sending is accomplished through the BMRF mode; this behavior aids in avoiding packet duplication. | SMRF improves both upstream and downstream multicast data forwarding. Increases the packet delivery ratio while reducing the number of radio transmissions and energy usage. | Increases memory consumption by a small amount. End-to-end latency and incorrect parameter settings can lead to low productivity. |
| SMRF [33] | RPL | Multicast communication | SMRF presents a cross-layer technique for multicast forwarding operations that enhances the working of Radio Duty Cycling (RDC) protocols. SMRF operates in storage mode with IETF multicast support. When compared to the default strategy, the conventional solution provides better outcomes. | RPL’s multicast data forwarding should be improved. Reduces the energy waste caused by multicast RPL’s many unicast transmissions. The processing of duplicated multicast packets is avoided. | Only downward multicast broadcasting is permitted. High end-to-end latency is possible. SMRF processes only packets transmitted from the node’s selected parent. Messages received from child nodes are not processed or forwarded as a result. |
| mRPL [34,35] | RPL and Smart-HOP | Mobile node support | Smart-HOP employs RPL-control messages similar to beacons in mRPL. The mechanism is separated into two phases due to two types of nodes: mobile nodes (MN) and access points (AP). An MN broadcasts a sequence of n DIS beacons to a serving AP during the data transfer phase. Based on the n received messages, the serving AP computes the average received signal strength indication (RSSI) value. | In RPL, provides quick and dependable mobility support. Provides a technique for avoiding collisions and loops. Interoperable with RPL by default. Reduces packet loss and delay rate. | A small amount increases the length of the control messages. Increases the number of control messages sent and received. |
| BRPL [36] | RPL and backpressure routing | Mobile node support | BRPL supports the creation of numerous logical topologies based on distinct Optical Fiber(OFs). For each Directed Acyclic Grap (DAG), each Backpressure RPL BRPL node maintains a buffered packet queue. DODAG Information Object (DIO) messages communicate information between nodes, such as the maximum queue length, RPL rank, and queue length. As a result, each node that receives a DIO message must update the information about the packet sender in the neighbor database. | Improves RPL to accommodate mobility and dynamic traffic loads, reduces packet loss significantly, and may exist together in a network using default RPL. | End-to-end latency is momentarily increased. |
| Emergency Response IoT based on Global Information DecisionERGID [37] | SPEED | QoS and Energy Efficiency | ERGID is a routing system for IoT applications that promises rapid emergency response and reliable data delivery. It relies on two distinct methods. For example, the delay iterative method (DIM) classifies the nodes of a potential route based on a global delay calculation. This method is used to prevent a legitimate route from being ignored. The second method, residual energy probability choice (REPC), allows for residual energy information throughout the message-forwarding process. | For emergency response applications, it provides reduced latency and load balancing. Reduces average latency and packet loss rate without increasing energy usage by selecting routes based on global information. | Uses many control messages to keep delayed information current and accurate. Calculations and routing table updates are required regularly. |
| Quality of Services (QoS) RPL [38] | RPL | QoS and Energy Efficiency | QoS RPL is a routing metric based on transmission delay that aims to better meet the energy efficiency and QoS criteria in LLNs. During the routing protocol operation, the information regarding energy and latency is mapped onto the control messages, while each node that receives a packet computes and updates this information. | Improves LLN energy efficiency and QoS while lowering delay and energy usage. | Reduces the ratio of packets delivered, which can disrupt load balancing, leading to an increase in control message overhearing. |
| LOAGng-IoT [39] | LOADng | QoS and Energy Efficiency | LOADng-IoT also has a route caching technique to decrease route search costs and a new error message for when an IC node loses its Internet connection. As a result, the idea enables LOADng to address better the QoS and energy efficiency needs of various IoT applications. | Allows LOADng to identify and maintain routes in diverse networks more efficiently. Allows nodes to identify Internet gateways without prior setup and provides a strategy for reducing the overhead created during route discovery. | Also necessitates the addition of an extra field to the average LOADng control messages. Memory use may be increased by using the route cache method. |
| RPLca+ [40] | RPL | QoS and Energy Efficiency | RPLca+ comprises two specialized libraries, one for estimating link quality and the other for managing neighbor tables. The first library aims to improve RPL operations using a hybrid link-monitoring architecture to evaluate connection quality with minimal overheads. The second library consists of a series of approaches for neighbor table management. | Improves data delivery reliability in RPL and offers a dynamic link; the quality estimator establishes the policies for the project. Routing table management enhances packet delivery rates. | Boosts energy usage by submitting implementation overheads. |
| Sr. No | Security Objectives of WSN-IoT | Definition | Layers |
|---|---|---|---|
| 1 | Availability | Accessibility is the nature of keeping the service accessible for clients. | Perception Layer |
| 2 | Accountability | Accountability is one of the IoT frameworks’ basic properties, but it cannot preempt network attacks and IoT vulnerabilities. | Network Layer |
| 3 | Confidentiality and Privacy | Confidentiality is otherwise known as as secrecy; to fulfill the security requirements, it is implemented to prevent unauthorized clients from getting information. | Network Layer |
| 4 | Auditing | This is an essential component; without it, the framework’s criteria for meeting security requirements will not be accomplished. It is used to recognize the security shortcomings of the IoT. | Network Layer |
| 5 | Integrity | It enables legitimate and authorized access to modify data following requirements, but only under certain conditions. | Network Layer |
| 6 | Access Control | It gives clients/users explicit roles or verified admittance to utilize network assets to view, alter, or modify data. | Application Layer |
| 7 | Authentication and Authorization | Authentication is the user’s verification, which is the primary security necessity as it recognizes users as validated clients utilizing security frameworks such as cryptography algorithms. | Network, Application Layer |
| Sr. No | Services | Challenges |
|---|---|---|
| 1 | Data Confidentiality | Data confidentiality is a significant concern in WSN-IoT frameworks since the customer can access the details and system administration. As a result, an IoT device access management system is required to identify the legitimate user and allow system access. |
| 2 | Privacy | Entities are linked, and information is conveyed and traded across the Internet, providing client safety while posing various hazards to sensitive data in numerous ways. There is a high chance of security vulnerabilities, such as sniffing and spoofing, unapproved access, and data alteration through unauthorized modification of WSN-IoT nodes. |
| 3 | Trust management | IoT layers have a distinct and diverse set of devices. Every device generates massive amounts of data subject to numerous attacks, risks, and concerns. These flaws are extended to each IoT layer and highly affect the quality of information or administration. |
| 4 | Vulnerabilities | Vulnerabilities are the loopholes that allow the attacker to access the device unethically and steal important information. Vulnerabilities in WSN-IoT exist at numerous levels, including user devices, scripts, hardware, methodologies, etc., which cause the framework to fail. |
| 5 | Security | Security is a significant concern in all fields. The growth in the number of connected devices to communication networks in the Internet of Things [61] leads to increased security risks and new security challenges, such as unauthorized access. With the help of unauthorized access, attackers can steal information and take complete control of smart appliances which causes inconvenience to their users. |
| 6 | Interoperability | WSN-IoT devices that are poorly designed might harm network resources. However, the customer rarely pays attention to the products and services that lack versatility. |
| 7 | Authentication, Identification, and Authorization | An attacker can access the network by inserting erroneous statements if the authentication is poorly handled. However, it is challenging to ensure authentication nowadays because of the wireless media’s existence and the nature of sensor networks. |
| 8 | Attacks | An important issue is an assault by hackers and rogue nodes that damages the machines on the network. The current security limits imposed on WSN-IoT render it vulnerable to various threats. |
| Author Name and Year | Proposed Solution | Limitations |
|---|---|---|
| Geetanjali Rathee et al., 2020 [97] | Applying blockchain technology significantly increases wireless sensor security by comparing security metrics. It maintains worker confidentiality and accountability and tracks each sensor’s operation. WSN-IoT artifacts and sensors are accumulated on the blockchain. The architecture is tested against the likelihood of an attack succeeding, the system’s ability to detect an attack, and a falsification attack. | I time it takes to examine a single block before it is added to the blockchain is not mentioned. |
| Sahil Garg et al., 2019 [98] | The protocol’s performance has been assessed, with the commonly used AVISPA, PUFs, ECC, and a host of other cryptographic primitives being used in the design of our stable, lightweight, and reliable authentication system for WSN-IoT environments, revealing that the proposed protocol supports shared authentication between WSN-IoT nodes and servers, as well as being resistant to a variety of security threats. | The protocIl is for research and academic purposes, and the implementation of the presented protocol has not been subjected to real-world application. |
| Jiafu Wan et al., 2016 [99] | Software-defined IIoT is proposed as a modern paradigm for industrial environments. It introduces features that make the network more scalable. The IIoT architecture can handle physical devices and an interface for information-sharing mechanisms via a conveniently customizable networking protocol. Additionally, the equipment’s improved intelligence would boost the system’s reliability and the availability of various services. | Information about the network attacks that the proposed software-defined IIoT can tackle is not mentioned. |
| Anichur Rahman et al., 2017 [100] | Industry 4.0 implementations in SDN-IoT-powered environments are faced with distributed blockchain-based authentication. The blockchain enhances the protection and privacy of Industry 4.0 services. The blockchain has the potential to lead in terms of security, secrecy, and confidentiality. Furthermore, the SDN-IoT integrates various Industry 4.0 services with increased security and stability. | The introduction of blockchain technology is also in its early stages. There is no study of the various threats, such as denial of service (DoS) and flooding attacks. Packet arrival rate, data response time, throughput, and other evaluation parameters are not specified. |
| Yulei Wu et al., 2020 [101] | Security and scalability have become top priorities in Industry 4.0, IoT, and IIoT. IoT and IIoT are implemented as vital technologies in Industry 4.0, and the blockchain and edge computing paradigms are briefly addressed. Integrating these two paradigms will contribute to developing stable and scalable critical infrastructure. The state-of-the-art WSN-IoT and IIoT infrastructure protection and privacy solutions and scalability solutions are evaluated and addressed. | Several possible research challenges and open problems are discussed but not adequately addressed or provided with a solution. |
| Jiafu Wan et al., 2018 [102] | Object Linking and Embedding (OLE) for process control technology, software-defined industrial networks, and device-to-device communications technology are combined with ontology modeling and multi-agent technology to achieve complex resource management. For innovative factory management for IoT-driven production, a load balancing mechanism based on Jena logic and Contract-Net Protocol technology provides a solution for complex resource utilization problems in Industry 4.0. | The sharing and reusing technologies of the ontology knowledge base are not mentioned without a scheduling system and algorithm optimization. |
| Sr.no | Author Name and Year | Contribution | Research Gaps |
|---|---|---|---|
| 1 | Susana H. Mellado et al., 2020 [103] | The technique has a low computing load and is very attractive for producing coverage maps that can be used for the optimum distribution of network resources. | The evaluation of output connectivity protocol requirements for satellite-based WSN-IoT simulations in virtual environments is lacking. |
| 2 | Trupti M. Behera et al., 2019 [91] | The algorithm considers residual energy, initial energy, and the cluster heads’ desired value to select the following cluster heads for the network that fit WSN-IoT applications to maximize throughput, lifetime, and residual energy. | Does not consider further CH selection parameters in a mobile node network that continually changes its role. |
| 3 | Yifei Tan et al., 2019 [92] | Capable of collecting real-time data from an IoT-aided production device and creating a Design Thinking (DT) model that essentially represents the actual system’s real situation. | Other essential features of DT are the lack of experimentation and optimization to forecast future positions or results. |
| 4 | Md. Ershadul Haque et al., 2020 [93] | The system is suitable for measurements of vibrations or earthquake events. The simulation results show that the EECDS-SGETRot mode offers the best products for a better version of the monitoring network and nodes that sinks can reach. | Not all of the nodes engage in data collection. |
| 5 | Zohre A. Bulaghi et al., 2020 [94] | The design reduces the amount of energy used by wireless sensors. The method is also helpful for determining the architectural location of sensors in WSNs, the total number of sensors required, and reliability. | The design contains some drawbacks and does not function on data in real-time. |
| 6 | Ravi Sharma & Shiva Prakash, 2020 [95] | Framework architecture for implementation patterns of relay nodes and load balancing between them to increase the network lifespan. This strengthens the deployment pattern of relay nodes for the sensor network. | The different network measurement criteria, such as network lifetime, overhead transmission costs, average electricity usage, and adequate overall area coverage, are still unknown. |
| 7 | Nabil D. et al., 2020 [90] | A new security mechanism, “Metric-based Routing Protocol for Low-power and Lossy Networks (RPL) Trustworthiness Scheme (MRTS),” is introduced to address the RPL vulnerabilities. Furthermore, the simulations indicate that MRTS is far more effective regarding energy consumption, packet delivery ratio, changes in node rank, and throughput. | The proposed strategies are highly complex since the reintegration of classified isolated nodes affects the model’s efficacy and raises new issues. |
| 8 | S. Dasgupta and B. Saha, [104] | Machine learning was used to predict the types of DDoS attacks. XGBoost and Random Forest were used to reach the DDoS prediction system for the research. The UNWS-np-15 dataset from GitHub was simulated with Python. After using machine learning models to assess model performance, a confusion matrix was produced. The accuracy (PR) and recall (RE) of Random Forest in the first classification are 89%. The AC on this model is 89%, which is good. | It is imperative to provide a user-friendly, quicker substitute for deep learning calculations that delivers better results in a shorter amount of time. |
| 9 | Samy et al., [105] | Authors have slightly complicated the design of generic models to function successfully. The researcher has employed several different methods of categorization in their efforts to forecast DDOS assaults. Additionally, the authors used the support vector machine (SVM), the K-nearest neighbor (KNN) method, and the random forest (RF) algorithm. The SVM has a 99.5% accuracy rate for identifying DDoS assaults, whereas the KNN and RF have accuracy rates of 97.5% and 98.74%, respectively. | The author wants to work with real-time datasets, but this model only works with offline datasets. As a result, we must begin transferring this work to real-time fraud detection applications centered on supervised learning models. |
| Factors | Dragomir [7] | Gendreau and Moorman [14] | Iqbal et al. [45] | Dalipi and Yayilgan [50] | Alansari et al. [88] | Anbar, et al. [106] | Adefemi Alimi et al. [107] | Raza et al. [108] | Muzammal et al. [109] | This Paper |
|---|---|---|---|---|---|---|---|---|---|---|
| LPN architecture | 0 | 0 | 0 | 0 | 0 | 0 | 1 | 0 | 1 | 1 |
| LPN application | 0 | 0 | 0 | 0 | 1 | 0 | 1 | 1 | 1 | 1 |
| Physical layer attacks | 0 | 0 | 0 | 0 | 1 | 0 | 0 | 0 | 0 | 1 |
| Network layer attacks | 0 | 1 | 1 | 0 | 1 | 1 | 1 | 1 | 1 | 1 |
| Software attacks | 0 | 0 | 0 | 0 | 0 | 0 | 1 | 0 | 0 | 1 |
| Data attacks | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 1 |
| WSN issues and challenges | 0 | 1 | 0 | 0 | 1 | 0 | 0 | 1 | 1 | 1 |
| IoT-LPN research challenges | 0 | 0 | 0 | 0 | 0 | 0 | 1 | 1 | 0 | 1 |
| Security objectives/factor | 1 | 0 | 1 | 1 | 0 | 1 | 1 | 1 | 1 | 1 |
| Protocols discussion | 1 | 0 | 0 | 1 | 0 | 1 | 1 | 1 | 0 | 1 |
| Industry 4.0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 1 |
| Total Score | 2 | 2 | 2 | 2 | 4 | 3 | 7 | 6 | 5 | 11 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Hussain, M.Z.; Hanapi, Z.M. Efficient Secure Routing Mechanisms for the Low-Powered IoT Network: A Literature Review. Electronics 2023, 12, 482. https://doi.org/10.3390/electronics12030482
Hussain MZ, Hanapi ZM. Efficient Secure Routing Mechanisms for the Low-Powered IoT Network: A Literature Review. Electronics. 2023; 12(3):482. https://doi.org/10.3390/electronics12030482
Chicago/Turabian StyleHussain, Muhammad Zunnurain, and Zurina Mohd Hanapi. 2023. "Efficient Secure Routing Mechanisms for the Low-Powered IoT Network: A Literature Review" Electronics 12, no. 3: 482. https://doi.org/10.3390/electronics12030482
APA StyleHussain, M. Z., & Hanapi, Z. M. (2023). Efficient Secure Routing Mechanisms for the Low-Powered IoT Network: A Literature Review. Electronics, 12(3), 482. https://doi.org/10.3390/electronics12030482








