Image Watermarking between Conventional and Learning-Based Techniques: A Literature Review
Abstract
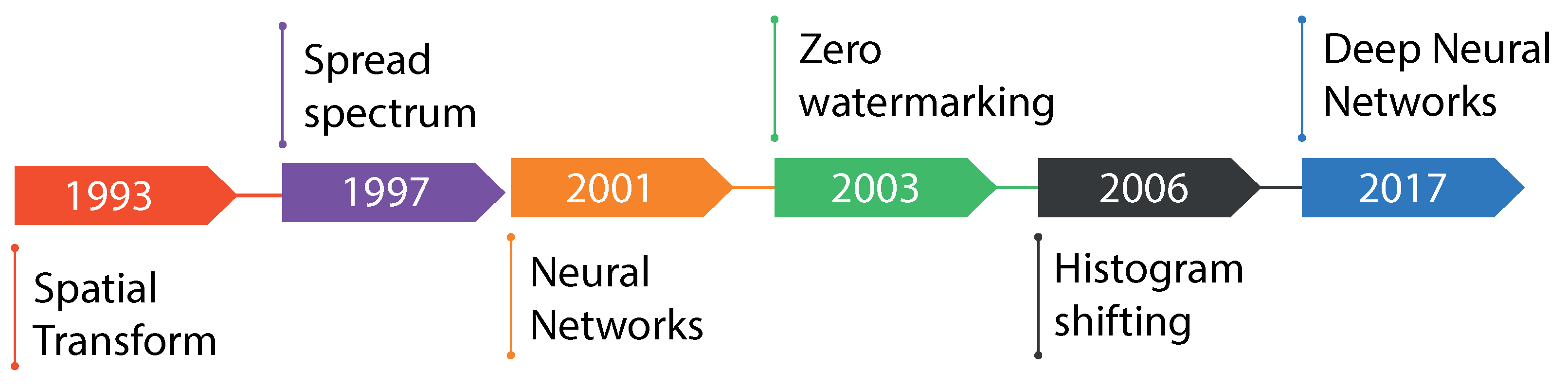
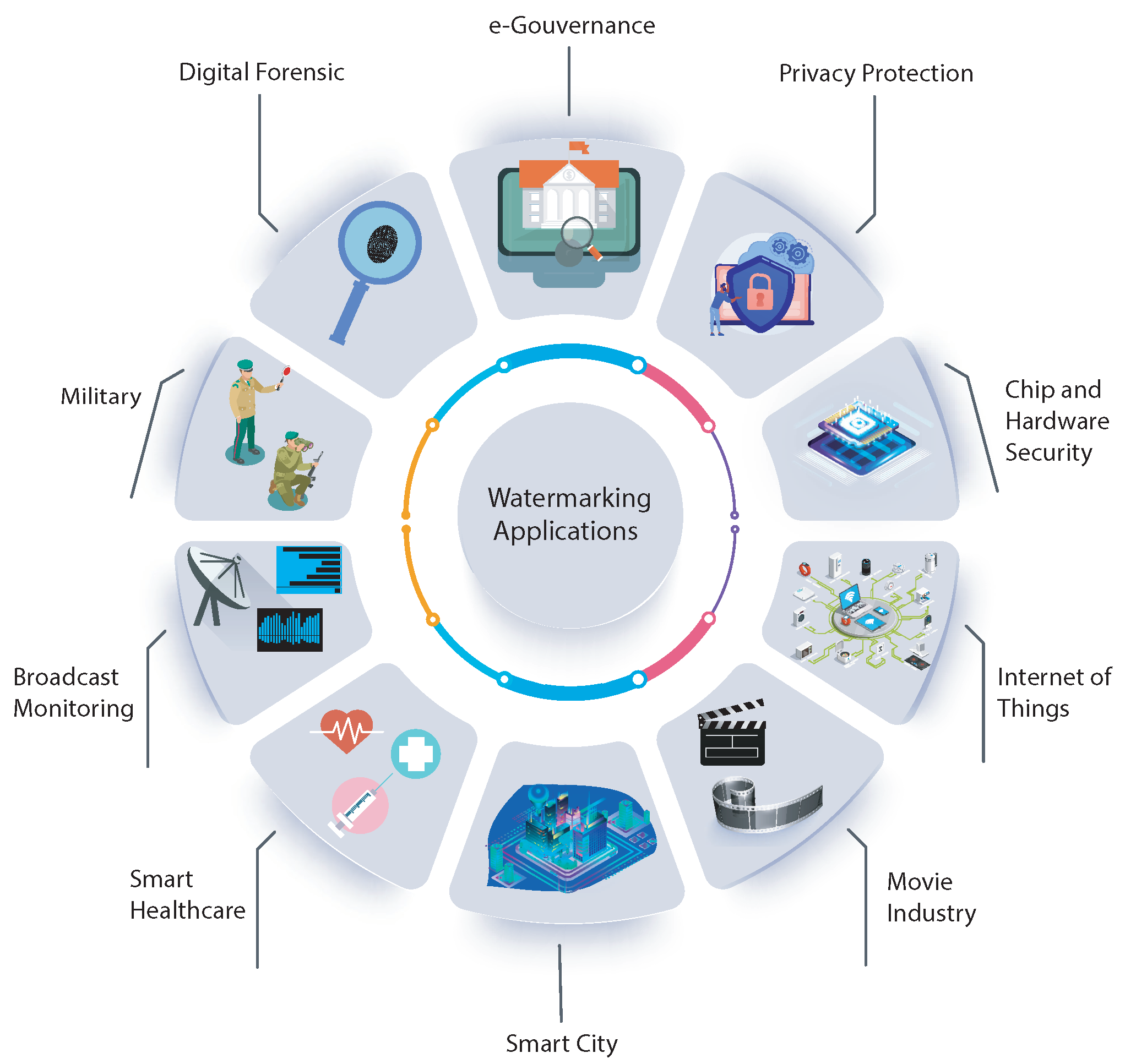
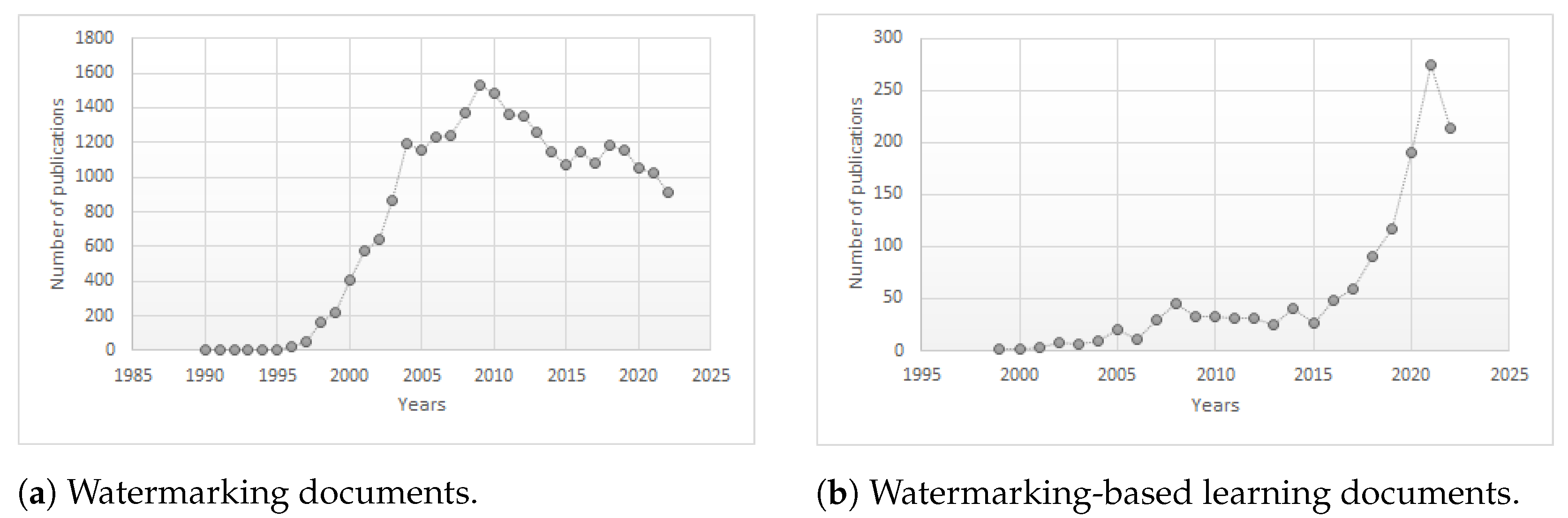
1. Introduction
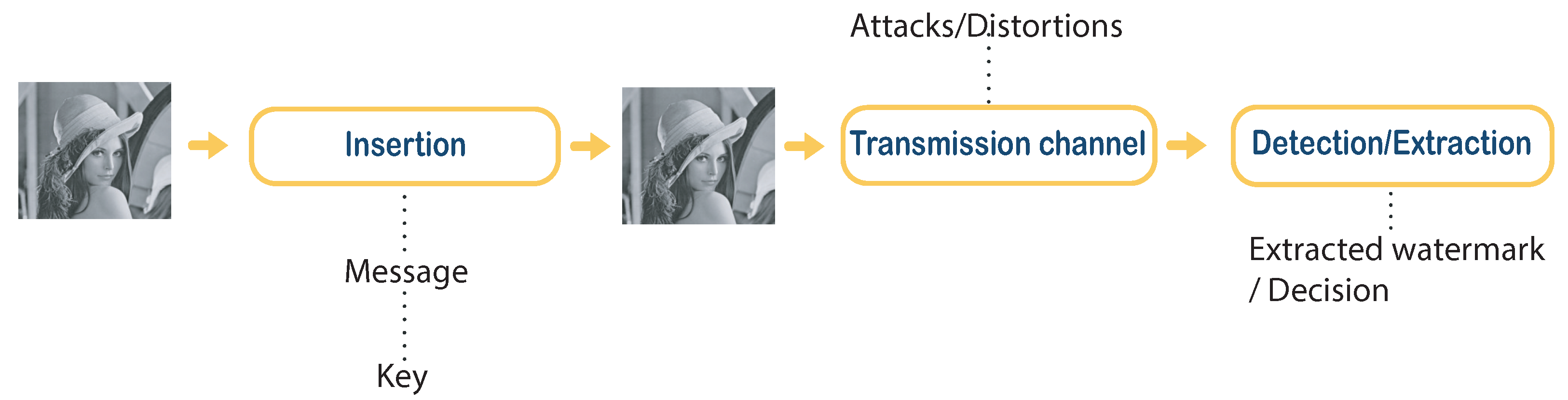
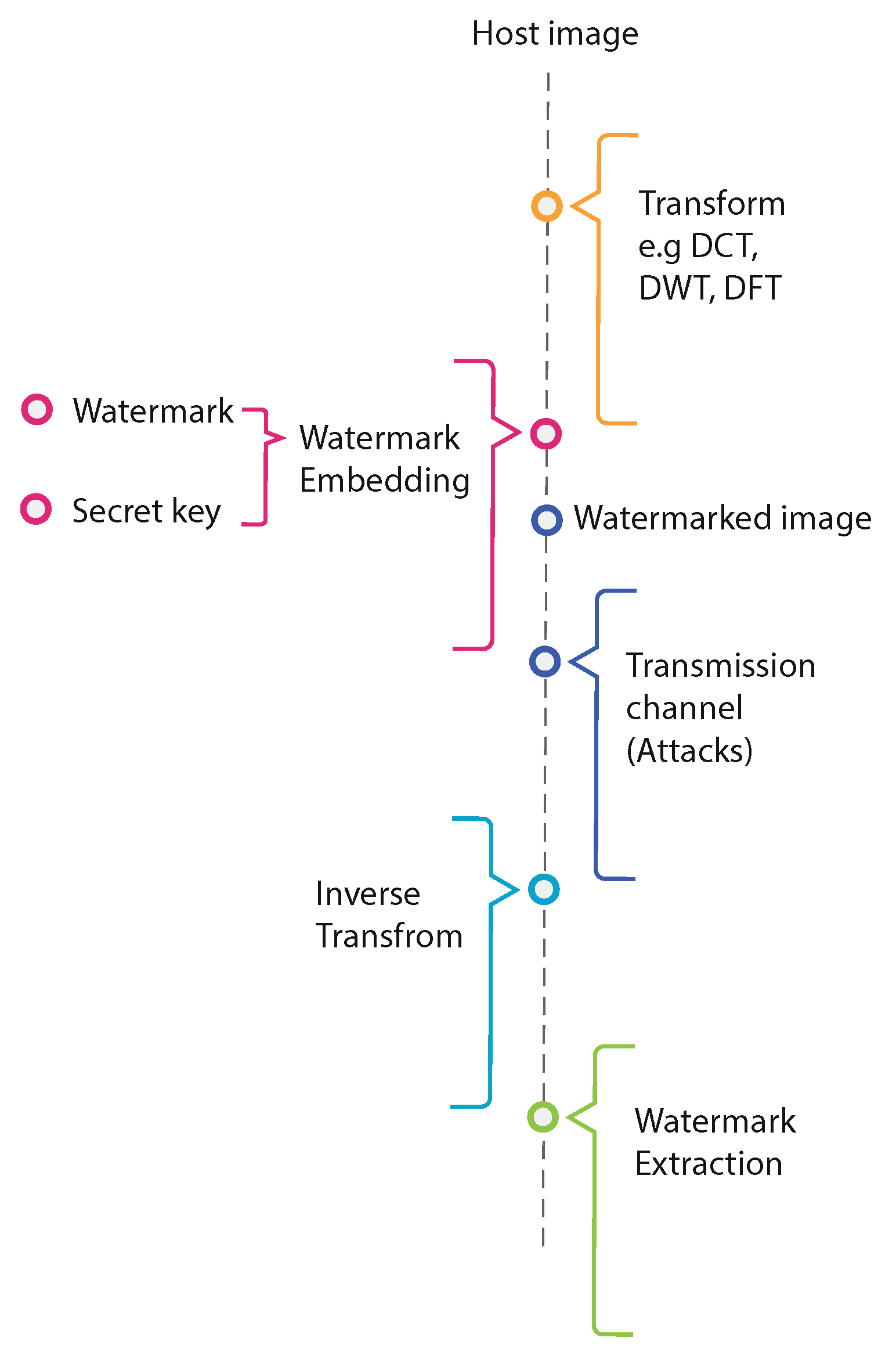
2. Image Watermarking Background
2.1. Embedding Phase
2.1.1. Additive Method
2.1.2. Substitutive Method
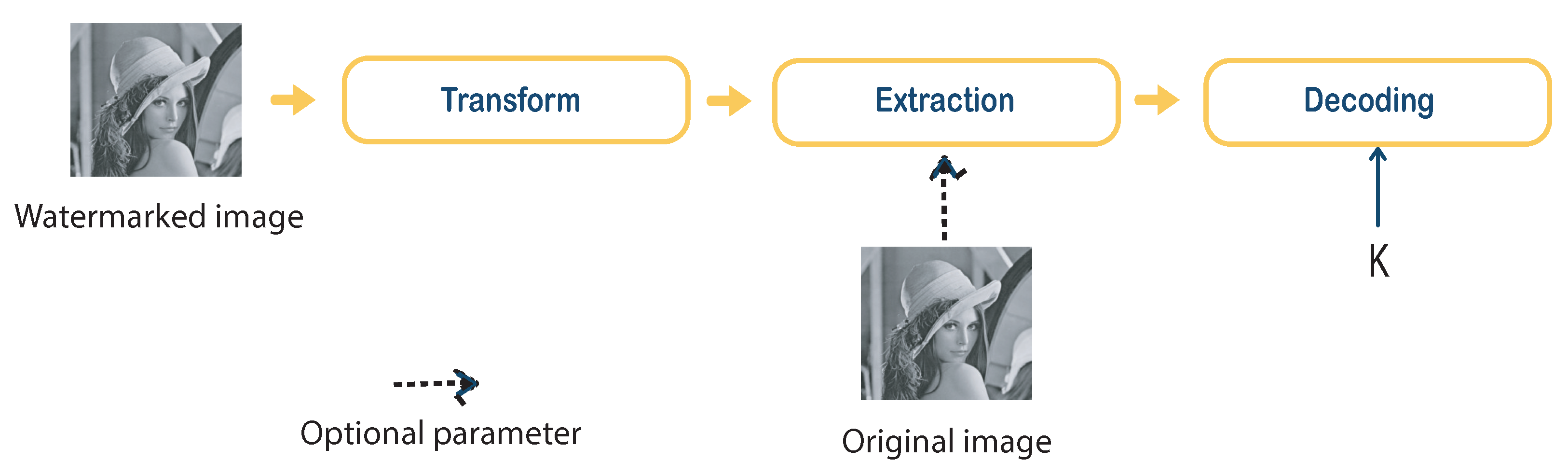
2.2. Detection Phase
2.2.1. Blind Watermarking
2.2.2. Non-Blind Watermarking
2.3. Transmission Phase
2.3.1. Unintentional Attacks
- Compression: Compression attacks are designed to reduce the amount of data encoded in the host document. This process consists of removing the perceptibly less important components while preserving the important components. JPEG and JPEG2000 are considered the most popular image compression algorithms currently in use [42].
- Filtering: Generally, filtering is used for noise reduction. This type of filtering basically has the effect of attenuating the high-frequency components of the image and therefore degrading the brand components inserted in these frequencies.
- Volumetric transformations: The basic idea behind these transformations is to adjust the brightness value of each pixel in an image using a linear or non-linear function to improve the visual aspect of the image. These transformations include histogram spreading and equalization, Gamma transformation, and so on.
- Noise: The addition of noise increases the uncertainty or ambiguity of the average information embedded in the image, which can have a masking effect on the watermark and therefore disturb its detection/extraction.
- Geometric transformations: This kind of transformation does not remove the mark, rather, it makes it undetectable while still remaining in the image. In the majority of watermarking algorithms, the watermark detector requires knowledge of the exact position of the mark in the image. These transformations cause a desynchronization between the mark inserted in the image and the detector [43]. There are several geometric transformations, for example, affine geometrical transformations (translation, rotation, and change of scale), and cropping, which consists of removing a part of the image and consequently a part of the mark. There are also local geometric transformations, such as the StirMark attack. This attack consists of a succession of random geometric distortions applied locally to several places in the image [44].
2.3.2. Intentional Attacks
- Cryptographic attack: The main goal of this attack is to crack the security codes and algorithms used in watermarking methods in order to remove the inserted watermark information. In this case, the attacker tries to identify the embedded secret key using exhaustive search techniques. This type of attack possesses high computational costs and it is limited, and therefore it is employed less frequently.
- Protocol attack: The idea behind this attack is to create document ownership ambiguity. Some protocol attacks are based on invertible operations, in which an attacker subtracts their watermark from the watermarked document and claims its ownership. Another type of protocol attack is the copy attack [45]. In this case, the goal is to remove the watermark from one container and place it in another target document. In all cases, the attacker can claim for the ownership of both the original and watermarked image.
3. Performance Requirements in Digital Watermarking
3.1. Robustness
- Robust watermarking: In this case, the watermark must be resistant to different attacks on the digital document, and the detection of the watermark must be effective even under those manipulations [47]. This watermarking technique is suitable for a variety of applications, including copyright protection, fingerprinting, broadcast monitoring, and copy control [48].
- Fragile watermarking: In fragile watermarking, the mark is extremely sensitive to the modifications of the watermarked document [49,50]. This technique is used to prove the authenticity and integrity of multimedia data. A fragile watermarking technique is designed to detect (with a high probability) any kind of manipulation of the watermarked document, including both incidental and intentional attacks. A comparison of the extracted watermark and the original watermark is performed to identify if the document is modified or not.
- Normalized Correlation (NC): NC computes the similarity and difference between the original watermark and the extracted watermark. The NC value of a good watermarking algorithm should be ≥0.7. Ideal algorithms provide an NC equal to 1. NC is defined as follows:where and are the original watermark and extracted watermark, respectively, of size .
- Bit Error Rate (BER): BER is also one of the measurements that evaluate the robustness of a watermarking technique. BER computes the ratio value of incorrectly extracted watermark bits from the inserted watermark bits. The closer the BER value is to 0, the greater the similarity between the extracted watermark and the original one, indicating more robustness.NI is the number of incorrectly extracted bits, while NT is the total number of bits transmitted.
3.2. Imperceptibility
- Peak signal-to-noise ratio (PSNR): PSNR is the most commonly used indicator for providing quantitative scores across the watermarked images. PSNR evaluates the invisibility requirements by comparing the similarity of the original image file to the watermarked one. The PSNR is defined as:where d is the maximum pixel value of the image and the maximum possible value for a pixel. For example, this is if the image pixels are coded with 8 bits. represents the mean square error, which is defined for two images using the following equation:where and are the original and watermarked image of dimension , respectively. The higher PSNR value can be obtained with a low value, indicating low degradation. In general, if the PSNR is greater than 40 dB, the watermark is considered invisible, while a value below 30 dB indicates significant distortions [54].
- Structural similarity index model (SSIM): The SSIM evaluates the structural similarity existing between two images. Unlike PSNR, which is based on the pixel-to-pixel difference between two images. The SSIM measure consists of combining three parameters: brightness, contrast, and structure comparison. It is computed on several windows of an image. The measure between two windows x and y is given by the following:where , , and represent the luminance function, contrast function, and structure comparison function, respectively. x and y are the pairs of local square windows of the original and the watermarked image, respectively, and the importance of each measurement is defined by the parameters , , and . Finally, the similarity between the reference image and the watermarked image is measured by the average of the SSIM calculated for each window and denoted by MSSIM:where and are the original and the watermarked, respectively, and m represents the total number of windows. The range of MSSIM is from 0 to 1; therefore, the MSSIM value must be close to 1 to show high similarity between the two images.
3.3. Capacity
3.4. Complexity
3.5. Security
- Number of Changing Pixel Rate (NPCR) and Unified Averaged Changed Intensity (UACI): Those two measures are used to evaluate the efficiency of image watermarking against potential attacks. They are usually used to analyze the resistance of the watermarked images to pixel-level changes. NPCR and UACI scores should always be close to 1 and 0.33, respectively, to achieve good security. Higher values mean resistance will be better. If W and denote the original and the extracted watermark, respectively, NPCR and UACI are defined as:where:
3.6. False Positive Rate (FPR)
4. Conventional Image Watermarking Schemes
4.1. Spatial Domain
4.2. Transform Domain
4.2.1. Discrete Cosine Transform (DCT)
4.2.2. Discrete Fourier Transform (DFT)
4.2.3. Discrete Wavelet Transform (DWT)
4.3. Hybrid Domain
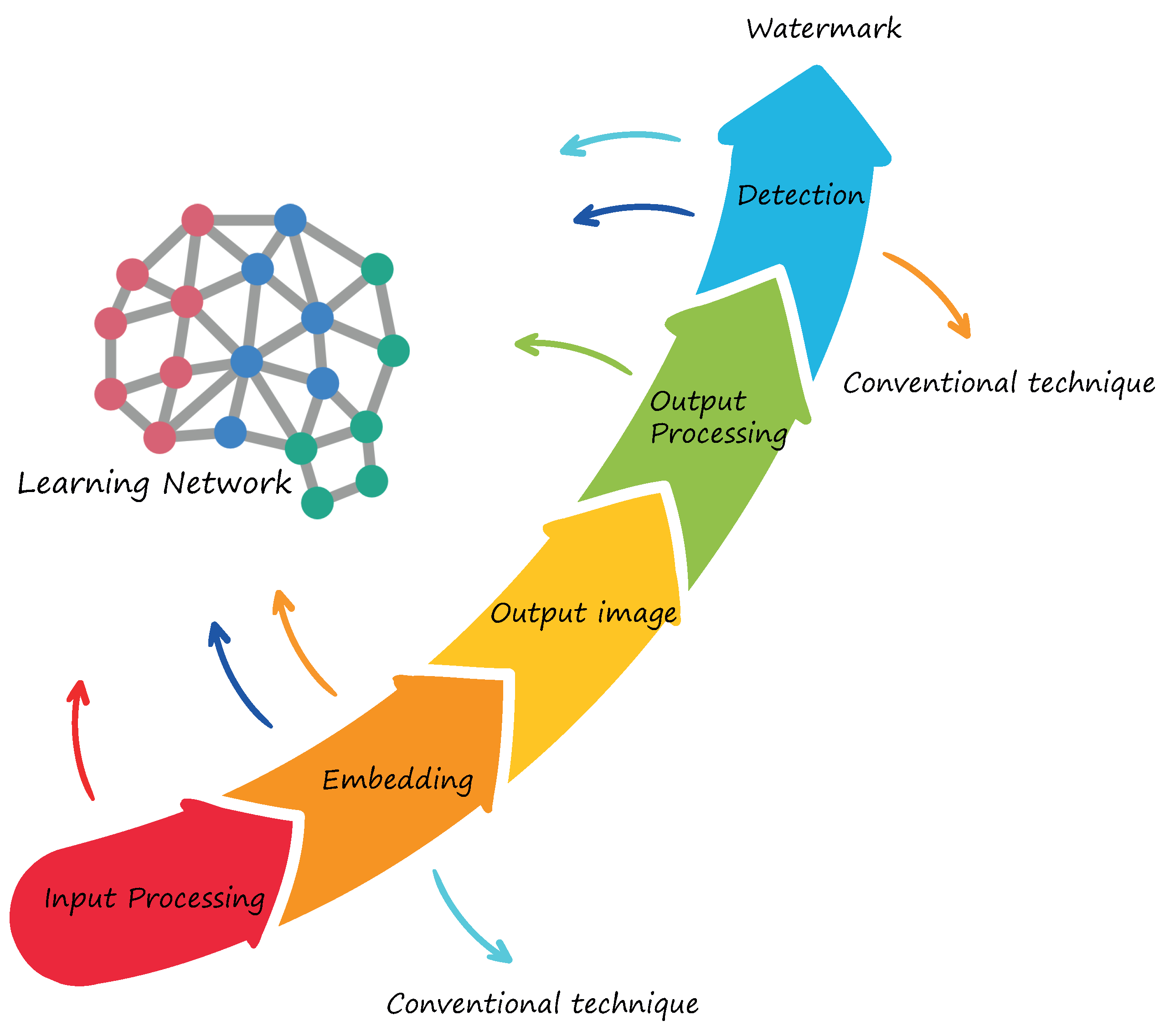
5. Deep Learning-Based Image Watermarking Schemes
5.1. Learning-Based Embedding Techniques
5.2. Learning-Based Extraction Techniques
5.3. End-to-End Learning-Based Watermarking Techniques
6. Discussion, Issues and Opportunities
7. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Pouyanfar, S.; Yang, Y.; Chen, S.C.; Shyu, M.L.; Iyengar, S. Multimedia big data analytics: A survey. ACM Comput. Surv. (CSUR) 2018, 51, 1–34. [Google Scholar] [CrossRef]
- Sengupta, A.; Mohanty, S. Everything you Wanted to Know About Watermarking: From Paper Marks to Hardware Protection. IEEE Consum. Electron. Mag. 2016, 6, 83–91. [Google Scholar] [CrossRef]
- Agarwal, N.; Singh, A.K.; Singh, P.K. Survey of robust and imperceptible watermarking. Multimed. Tools Appl. 2019, 78, 8603–8633. [Google Scholar] [CrossRef]
- Mishra, R.; Bhanodiya, P. A review on steganography and cryptography. In Proceedings of the 2015 International Conference on Advances in Computer Engineering and Applications, Ghaziabad, India, 19–20 March 2015; pp. 119–122. [Google Scholar]
- Evsutin, O.; Melman, A.; Meshcheryakov, R. Digital steganography and watermarking for digital images: A review of current research directions. IEEE Access 2020, 8, 166589–166611. [Google Scholar] [CrossRef]
- Rakhmawati, L.; Wirawan, W.; Suwadi, S. A recent survey of self-embedding fragile watermarking scheme for image authentication with recovery capability. EURASIP J. Image Video Process. 2019, 2019, 61. [Google Scholar] [CrossRef]
- Begum, M.; Uddin, M.S. Digital image watermarking techniques: A review. Information 2020, 11, 110. [Google Scholar] [CrossRef]
- Ahvanooey, M.T.; Li, Q.; Zhu, X.; Alazab, M.; Zhang, J. ANiTW: A novel intelligent text watermarking technique for forensic identification of spurious information on social media. Comput. Secur. 2020, 90, 101702. [Google Scholar] [CrossRef]
- Sharma, C.; Bagga, A.; Singh, B.K.; Shabaz, M. A novel optimized graph-based transform watermarking technique to address security issues in real-time application. Math. Probl. Eng. 2021, 2021, 5580098. [Google Scholar] [CrossRef]
- Mohammed, A.A.; Abdullah, M.A.; Awad, S.R.; Alghareb, F.S. A Novel FDCT-SVD Based Watermarking with Radon Transform for Telemedicine Applications. Int. J. Intell. Eng. Syst. 2022, 15, 343–354. [Google Scholar]
- Sharma, S.; Zou, J.J.; Fang, G. A Novel Multipurpose Watermarking Scheme Capable of Protecting and Authenticating Images With Tamper Detection and Localisation Abilities. IEEE Access 2022, 10, 85677–85700. [Google Scholar] [CrossRef]
- Wazirali, R.; Ahmad, R.; Al-Amayreh, A.; Al-Madi, M.; Khalifeh, A. Secure watermarking schemes and their approaches in the IoT technology: An overview. Electronics 2021, 10, 1744. [Google Scholar] [CrossRef]
- Lee, Y.J.; Na, W.S. E-Passport Advanced Security Technique Using Biometric Information Watermarking. J. Comput. Theor. Nanosci. 2021, 18, 1540–1549. [Google Scholar] [CrossRef]
- Kumar, M.; Aggarwal, J.; Rani, A.; Stephan, T.; Shankar, A.; Mirjalili, S. Secure video communication using firefly optimization and visual cryptography. Artif. Intell. Rev. 2022, 55, 2997–3017. [Google Scholar] [CrossRef]
- Anand, A.; Singh, A.K. Watermarking techniques for medical data authentication: A survey. Multimed. Tools Appl. 2021, 80, 30165–30197. [Google Scholar] [CrossRef]
- Ross, A.; Banerjee, S.; Chowdhury, A. Security in smart cities: A brief review of digital forensic schemes for biometric data. Pattern Recognit. Lett. 2020, 138, 346–354. [Google Scholar] [CrossRef]
- Li, D.; Deng, L.; Gupta, B.B.; Wang, H.; Choi, C. A novel CNN based security guaranteed image watermarking generation scenario for smart city applications. Inf. Sci. 2019, 479, 432–447. [Google Scholar] [CrossRef]
- Wan, W.; Wang, J.; Zhang, Y.; Li, J.; Yu, H.; Sun, J. A comprehensive survey on robust image watermarking. Neurocomputing 2022, 488, 226–247. [Google Scholar] [CrossRef]
- Abdullatif, M.; Zeki, A.M.; Chebil, J.; Gunawan, T.S. Properties of digital image watermarking. In Proceedings of the 2013 IEEE 9th International Colloquium on Signal Processing and Its Applications, Kuala Lumpur, Malaysia, 8–10 March 2013; pp. 235–240. [Google Scholar]
- Jiao, L.; Zhao, J. A Survey on the New Generation of Deep Learning in Image Processing. IEEE Access 2019, 7, 172231–172263. [Google Scholar] [CrossRef]
- Amrit, P.; Singh, A.K. Survey on watermarking methods in the artificial intelligence domain and beyond. Comput. Commun. 2022, 188, 52–65. [Google Scholar] [CrossRef]
- Sy, N.C.; Kha, H.H.; Hoang, N.M. An efficient robust blind watermarking method based on convolution neural networks in wavelet transform domain. Int. J. Mach. Learn. Comput 2020, 10, 675–684. [Google Scholar] [CrossRef]
- Wang, X.; Ma, D.; Hu, K.; Hu, J.; Du, L. Mapping based residual convolution neural network for non-embedding and blind image watermarking. J. Inf. Secur. Appl. 2021, 59, 102820. [Google Scholar] [CrossRef]
- Usha Nandini, D.; Divya, S. A literature survey on various watermarking techniques. In Proceedings of the 2017 International Conference on Inventive Systems and Control (ICISC), Coimbatore, India, 19–20 January 2017; pp. 1–4. [Google Scholar] [CrossRef]
- Rani, B.U.; Praveena, B.; Ramanjaneyulu, K. Literature Review on Digital Image Watermarking; ICARCSET ’15; Association for Computing Machinery: New York, NY, USA, 2015. [Google Scholar] [CrossRef]
- Salah, E.; Amine, K.; Redouane, K.; Fares, K. A Fourier transform based audio watermarking algorithm. Appl. Acoust. 2021, 172, 107652. [Google Scholar] [CrossRef]
- Yu, X.; Wang, C.; Zhou, X. A survey on robust video watermarking algorithms for copyright protection. Appl. Sci. 2018, 8, 1891. [Google Scholar] [CrossRef]
- Kamaruddin, N.S.; Kamsin, A.; Por, L.Y.; Rahman, H. A review of text watermarking: Theory, methods, and applications. IEEE Access 2018, 6, 8011–8028. [Google Scholar] [CrossRef]
- Evsutin, O.; Dzhanashia, K. Watermarking schemes for digital images: Robustness overview. Signal Process. Image Commun. 2022, 100, 116523. [Google Scholar] [CrossRef]
- Hosam, O. Attacking image watermarking and steganography-a survey. Int. J. Inf. Technol. Comput. Sci. 2019, 11, 23–37. [Google Scholar] [CrossRef]
- Cox, I.J.; Kilian, J.; Leighton, F.T.; Shamoon, T. Secure spread spectrum watermarking for multimedia. IEEE Trans. Image Process. 1997, 6, 1673–1687. [Google Scholar] [CrossRef]
- Cox, I.; Miller, M.; Bloom, J.; Fridrich, J.; Kalker, T. Digital Watermarking and Steganography; Morgan Kaufmann: Burlington, MA, USA, 2007. [Google Scholar]
- Zhang, L.; Wei, D. Robust and reliable image copyright protection scheme using downsampling and block transform in integer wavelet domain. Digit. Signal Process. 2020, 106, 102805. [Google Scholar] [CrossRef]
- Riad, R.; Ros, F.; Harba, R.; Douzi, H.; El Hajji, M. Pre-processing the cover image before embedding improves the watermark detection rate. In Proceedings of the 2014 Second World Conference on Complex Systems (WCCS), Agadir, Morocco, 10–12 November 2014; pp. 705–709. [Google Scholar] [CrossRef]
- Kishore, R.R. A novel and efficient blind image watermarking in transform domain. Procedia Comput. Sci. 2020, 167, 1505–1514. [Google Scholar]
- Yuan, Z.; Liu, D.; Zhang, X.; Su, Q. New image blind watermarking method based on two-dimensional discrete cosine transform. Optik 2020, 204, 164152. [Google Scholar] [CrossRef]
- Kaur, M.; Neeru, N. A Review on Digital Watermarking Using LSB. Int. J. 2015, 5, 210–2014. [Google Scholar]
- Chen, B.; Wornell, G.W. Quantization index modulation: A class of provably good methods for digital watermarking and information embedding. IEEE Trans. Inf. Theory 2001, 47, 1423–1443. [Google Scholar] [CrossRef]
- Rosales-Roldan, L.; Chao, J.; Nakano-Miyatake, M.; Perez-Meana, H. Color image ownership protection based on spectral domain watermarking using QR codes and QIM. Multimed. Tools Appl. 2018, 77, 16031–16052. [Google Scholar] [CrossRef]
- Zhang, X.; Su, Q.; Yuan, Z.; Liu, D. An efficient blind color image watermarking algorithm in spatial domain combining discrete Fourier transform. Optik 2020, 219, 165272. [Google Scholar] [CrossRef]
- Anbarjafari, G.; Ozcinar, C. Imperceptible non-blind watermarking and robustness against tone mapping operation attacks for high dynamic range images. Multimed. Tools Appl. 2018, 77, 24521–24535. [Google Scholar] [CrossRef]
- Muñoz-Ramirez, D.O.; Ponomaryov, V.; Reyes-Reyes, R.; Kyrychenko, V.; Pechenin, O.; Totsky, A. A robust watermarking scheme to JPEG compression for embedding a color watermark into digital images. In Proceedings of the 2018 IEEE 9th International Conference on Dependable Systems, Services and Technologies (DESSERT), Ukraine, Kyiv, 24–27 May 2018; pp. 619–624. [Google Scholar]
- Licks, V.; Jordan, R. Geometric attacks on image watermarking systems. IEEE Multimed. 2005, 12, 68–78. [Google Scholar] [CrossRef]
- Kutter, M.; Petitcolas, F.A. Fair benchmark for image watermarking systems. In Security and Watermarking of Multimedia Contents; SPIE: Bellingham, DC, USA, 1999; Volume 3657, pp. 226–239. [Google Scholar]
- Kutter, M.; Voloshynovskiy, S.V.; Herrigel, A. Watermark copy attack. In Security and Watermarking of Multimedia Contents II; SPIE: Bellingham, DC, USA, 2000; Volume 3971, pp. 371–380. [Google Scholar]
- Pal, P.; Singh, H.V.; Verma, S.K. Study on watermarking techniques in digital images. In Proceedings of the 2018 2nd International Conference on Trends in Electronics and Informatics (ICOEI), Tirunelveli, India, 11–12 May 2018; pp. 372–376. [Google Scholar]
- Fares, K.; Khaldi, A.; Redouane, K.; Salah, E. DCT & DWT based watermarking scheme for medical information security. Biomed. Signal Process. Control 2021, 66, 102403. [Google Scholar]
- Verma, V.S.; Jha, R.K. An overview of robust digital image watermarking. IETE Tech. Rev. 2015, 32, 479–496. [Google Scholar] [CrossRef]
- Qin, C.; Ji, P.; Zhang, X.; Dong, J.; Wang, J. Fragile image watermarking with pixel-wise recovery based on overlapping embedding strategy. Signal Process. 2017, 138, 280–293. [Google Scholar] [CrossRef]
- Zhang, H.; Wang, C.; Zhou, X. Fragile watermarking for image authentication using the characteristic of SVD. Algorithms 2017, 10, 27. [Google Scholar] [CrossRef]
- Feng, B.; Li, X.; Jie, Y.; Guo, C.; Fu, H. A novel semi-fragile digital watermarking scheme for scrambled image authentication and restoration. Mob. Netw. Appl. 2020, 25, 82–94. [Google Scholar] [CrossRef]
- Qi, X.; Xin, X. A singular-value-based semi-fragile watermarking scheme for image content authentication with tamper localization. J. Vis. Commun. Image Represent. 2015, 30, 312–327. [Google Scholar] [CrossRef]
- Zhou, N.R.; Hou, W.M.X.; Wen, R.H.; Zou, W.P. Imperceptible digital watermarking scheme in multiple transform domains. Multimed. Tools Appl. 2018, 77, 30251–30267. [Google Scholar] [CrossRef]
- Cheddad, A.; Condell, J.; Curran, K.; Mc Kevitt, P. Digital image steganography: Survey and analysis of current methods. Signal Process. 2010, 90, 727–752. [Google Scholar] [CrossRef]
- Wang, C.; Zhang, H.; Zhou, X. A self-recovery fragile image watermarking with variable watermark capacity. Appl. Sci. 2018, 8, 548. [Google Scholar] [CrossRef]
- Sutojo, T.; Rachmawanto, E.H.; Sari, C.A. Fast and efficient image watermarking algorithm using discrete tchebichef transform. In Proceedings of the 2017 5th International Conference on Cyber and IT Service Management (CITSM), Denpasar, Bali, Indonesia, 8–10 August 2017; pp. 1–5. [Google Scholar]
- Bhalerao, S.; Ansari, I.A.; Kumar, A. A secure image watermarking for tamper detection and localization. J. Ambient. Intell. Humaniz. Comput. 2021, 12, 1057–1068. [Google Scholar] [CrossRef]
- Zhou, N.R.; Luo, A.W.; Zou, W.P. Secure and robust watermark scheme based on multiple transforms and particle swarm optimization algorithm. Multimed. Tools Appl. 2019, 78, 2507–2523. [Google Scholar] [CrossRef]
- Bravo-Solorio, S.; Nandi, A.K. Secure fragile watermarking method for image authentication with improved tampering localisation and self-recovery capabilities. Signal Process. 2011, 91, 728–739. [Google Scholar] [CrossRef]
- Makbol, N.M.; Khoo, B.E.; Rassem, T.H. Security analyses of false positive problem for the SVD-based hybrid digital image watermarking techniques in the wavelet transform domain. Multimed. Tools Appl. 2018, 77, 26845–26879. [Google Scholar] [CrossRef]
- Ansari, I.A.; Pant, M.; Ahn, C.W. Robust and false positive free watermarking in IWT domain using SVD and ABC. Eng. Appl. Artif. Intell. 2016, 49, 114–125. [Google Scholar] [CrossRef]
- Kumar, S.; Dutta, A. Performance analysis of spatial domain digital watermarking techniques. In Proceedings of the 2016 International Conference on Information Communication and Embedded Systems (ICICES), Chennai, India, 25–26 February 2016; pp. 1–4. [Google Scholar]
- Pardhu, T.; Perli, B.R. Digital image watermarking in frequency domain. In Proceedings of the 2016 International Conference on Communication and Signal Processing (ICCSP), Tamilnadu, India, 6–8 April 2016; pp. 0208–0211. [Google Scholar]
- Begum, M.; Uddin, M.S. Analysis of digital image watermarking techniques through hybrid methods. Adv. Multimed. 2020, 2020, 7912690. [Google Scholar] [CrossRef]
- Tanwar, L.; Panda, J. Review of different transforms used in digital image watermarking. In Proceedings of the 2018 2nd IEEE International Conference on Power Electronics, Intelligent Control and Energy Systems (ICPEICES), Delhi, India, 22–24 October 2018; pp. 1165–1171. [Google Scholar]
- Fazli, S.; Khodaverdi, G. Trade-Off between Imperceptibility and Robustness of LSB Watermarking Using SSIM Quality Metrics. In Proceedings of the 2009 Second International Conference on Machine Vision, Dubai, United Arab Emirates, 28–30 December 2009; pp. 101–104. [Google Scholar] [CrossRef]
- Tanaka, K.; Nakamura, Y.; Matsui, K. Embedding secret information into a dithered multi-level image. In Proceedings of the IEEE Conference on Military Communications, Monterey, CA, USA, 30 September–3 October 1990; Volume 1, pp. 216–220. [Google Scholar] [CrossRef]
- Yeo, I.K.; Kim, H. Generalized patchwork algorithm for image watermarking. Multimed. Syst. 2003, 9, 261–265. [Google Scholar] [CrossRef]
- Thongkor, K.; Amornraksa, T.; Delp, E.J. Digital watermarking for camera-captured images based on just noticeable distortion and Wiener filtering. J. Vis. Commun. Image Represent. 2018, 53, 146–160. [Google Scholar] [CrossRef]
- Pan-Pan, N.; Xiang-Yang, W.; Yu-Nan, L.; Hong-Ying, Y. A robust color image watermarking using local invariant significant bitplane histogram. Multimed. Tools Appl. 2017, 76, 3403–3433. [Google Scholar] [CrossRef]
- Belferdi, W.; Behloul, A.; Noui, L. A Bayer pattern-based fragile watermarking scheme for color image tamper detection and restoration. Multidimens. Syst. Signal Process. 2019, 30, 1093–1112. [Google Scholar] [CrossRef]
- Abraham, J.; Paul, V. An imperceptible spatial domain color image watermarking scheme. J. King Saud Univ.-Comput. Inf. Sci. 2019, 31, 125–133. [Google Scholar] [CrossRef]
- Gull, S.; Loan, N.A.; Parah, S.A.; Sheikh, J.A.; Bhat, G.M. An efficient watermarking technique for tamper detection and localization of medical images. J. Ambient. Intell. Humaniz. Comput. 2020, 11, 1799–1808. [Google Scholar] [CrossRef]
- Rinki, K.; Verma, P.; Singh, R.K. A novel matrix multiplication based LSB substitution mechanism for data security and authentication. J. King Saud Univ.-Comput. Inf. Sci. 2022, 34, 5510–5524. [Google Scholar] [CrossRef]
- Wang, H.; Su, Q. A color image watermarking method combined QR decomposition and spatial domain. Multimed. Tools Appl. 2022, 81, 37895–37916. [Google Scholar] [CrossRef]
- Mustaqim Abrar, M.; Pal, A.; Sazzad, S. Bit Plane Slicing and Quantization-Based Color Image Watermarking in Spatial Domain. In Proceedings of International Joint Conference on Advances in Computational Intelligence; Springer: Berlin, Gernmany, 2021; pp. 371–383. [Google Scholar]
- Araghi, T.K.; Manaf, A.; Zamani, M.; Araghi, S.K. A survey on digital image watermarking techniques in spatial and transform domains. Int. J. Adv. Image Process. Tech. 2016, 3, 6–10. [Google Scholar]
- Jimson, N.; Hemachandran, K. DFT Based Coefficient Exchange Digital Image Watermarking. In Proceedings of the 2018 Second International Conference on Intelligent Computing and Control Systems (ICICCS), Madurai, India, 14–15 June 2018; pp. 567–571. [Google Scholar] [CrossRef]
- Mahto, D.K.; Singh, A.K. A survey of color image watermarking: State-of-the-art and research directions. Comput. Electr. Eng. 2021, 93, 107255. [Google Scholar] [CrossRef]
- Tsui, T.K.; Zhang, X.P.; Androutsos, D. Color image watermarking using multidimensional Fourier transforms. IEEE Trans. Inf. Forensics Secur. 2008, 3, 16–28. [Google Scholar] [CrossRef]
- Rangel-Espinoza, K.; Fragoso-Navarro, E.; Cruz-Ramos, C.; Reyes-Reyes, R.; Nakano-Miyatake, M.; Pérez-Meana, H.M. Adaptive removable visible watermarking technique using dual watermarking for digital color images. Multimed. Tools Appl. 2018, 77, 13047–13074. [Google Scholar] [CrossRef]
- Loan, N.A.; Hurrah, N.N.; Parah, S.A.; Lee, J.W.; Sheikh, J.A.; Bhat, G.M. Secure and robust digital image watermarking using coefficient differencing and chaotic encryption. IEEE Access 2018, 6, 19876–19897. [Google Scholar] [CrossRef]
- Vishwakarma, V.P.; Sisaudia, V. Gray-scale image watermarking based on DE-KELM in DCT domain. Procedia Comput. Sci. 2018, 132, 1012–1020. [Google Scholar] [CrossRef]
- Moosazadeh, M.; Ekbatanifard, G. A new DCT-based robust image watermarking method using teaching-learning-based optimization. J. Inf. Secur. Appl. 2019, 47, 28–38. [Google Scholar] [CrossRef]
- Wang, J.; Wan, W.B.; Li, X.X.; De Sun, J.; Zhang, H.X. Color image watermarking based on orientation diversity and color complexity. Expert Syst. Appl. 2020, 140, 112868. [Google Scholar] [CrossRef]
- Zhang, Y.; Wang, Z.; Zhan, Y.; Meng, L.; Sun, J.; Wan, W. JND-aware robust image watermarking with tri-directional inter-block correlation. Int. J. Intell. Syst. 2021, 36, 7053–7079. [Google Scholar] [CrossRef]
- Liao, X.; Li, K.; Yin, J. Separable data hiding in encrypted image based on compressive sensing and discrete fourier transform. Multimed. Tools Appl. 2017, 76, 20739–20753. [Google Scholar] [CrossRef]
- Riad, R.; Harba, R.; Douzi, H.; Ros, F.; Elhajji, M. Robust Fourier Watermarking for ID Images on Smart Card Plastic Supports. Adv. Electr. Comput. Eng. 2016, 16, 23–30. [Google Scholar] [CrossRef]
- Riad, R.; Ros, F.; Gourrame, K.; Hajji, M.E.; Douzi, H.; Harba, R. A preventive and curative watermarking scheme for an industrial solution. Multimed. Tools Appl. 2022, 1–29. [Google Scholar] [CrossRef]
- Gourrame, K.; Douzi, H.; Harba, R.; Riad, R.; Ros, F.; Amar, M.; Elhajji, M. A zero-bit Fourier image watermarking for print-cam process. Multimed. Tools Appl. 2019, 78, 2621–2638. [Google Scholar] [CrossRef]
- Prajwalasimha, S.; Chethan Suputhra, S.; Mohan, C. Performance Analysis of Combined Discrete Fourier Transformation (DFT) and Successive Division based Image Watermarking Scheme. Int. J. Recent Technol. Eng. 2019, 8, 34–39. [Google Scholar]
- Fares, K.; Amine, K.; Salah, E. A robust blind color image watermarking based on Fourier transform domain. Optik 2020, 208, 164562. [Google Scholar] [CrossRef]
- Chen, W.; Zhu, C.; Ren, N.; Seppänen, T.; Keskinarkaus, A. Screen-cam robust and blind watermarking for tile satellite images. IEEE Access 2020, 8, 125274–125294. [Google Scholar] [CrossRef]
- Hsu, L.Y.; Hu, H.T. Blind watermarking for color images using EMMQ based on QDFT. Expert Syst. Appl. 2020, 149, 113225. [Google Scholar] [CrossRef]
- Cedillo-Hernandez, M.; Cedillo-Hernandez, A.; Garcia-Ugalde, F.J. Improving dft-based image watermarking using particle swarm optimization algorithm. Mathematics 2021, 9, 1795. [Google Scholar] [CrossRef]
- Poljicak, A.; Donevski, D.; Jelusic, P.B.; Cigula, T. Robust DFT watermarking method with gray component replacement masking. Multimed. Tools Appl. 2022, 81, 30365–30386. [Google Scholar] [CrossRef]
- Huynh-The, T.; Hua, C.H.; Tu, N.A.; Hur, T.; Bang, J.; Kim, D.; Amin, M.B.; Kang, B.H.; Seung, H.; Lee, S. Selective bit embedding scheme for robust blind color image watermarking. Inf. Sci. 2018, 426, 1–18. [Google Scholar] [CrossRef]
- Tan, Y.; Qin, J.; Xiang, X.; Ma, W.; Pan, W.; Xiong, N.N. A robust watermarking scheme in YCbCr color space based on channel coding. IEEE Access 2019, 7, 25026–25036. [Google Scholar] [CrossRef]
- Zhang, L.; Wei, D. Image watermarking based on matrix decomposition and gyrator transform in invariant integer wavelet domain. Signal Process. 2020, 169, 107421. [Google Scholar] [CrossRef]
- Al-Otum, H.M. Secure and robust host-adapted color image watermarking using inter-layered wavelet-packets. J. Vis. Commun. Image Represent. 2020, 66, 102726. [Google Scholar] [CrossRef]
- Kumar, S.; Singh, B.K. DWT based color image watermarking using maximum entropy. Multimed. Tools Appl. 2021, 80, 15487–15510. [Google Scholar] [CrossRef]
- Anand, A.; Singh, A.K. Joint watermarking-encryption-ECC for patient record security in wavelet domain. IEEE Multimed. 2020, 27, 66–75. [Google Scholar] [CrossRef]
- Yuan, S.; Magayane, D.A.; Liu, X.; Zhou, X.; Lu, G.; Wang, Z.; Zhang, H.; Li, Z. A blind watermarking scheme based on computational ghost imaging in wavelet domain. Opt. Commun. 2021, 482, 126568. [Google Scholar] [CrossRef]
- Darwish, S.M.; Al-Khafaji, L.D.S. Dual watermarking for color images: A new image copyright protection model based on the fusion of successive and segmented watermarking. Multimed. Tools Appl. 2020, 79, 6503–6530. [Google Scholar] [CrossRef]
- Kang, X.; Chen, Y.; Zhao, F.; Lin, G. Multi-dimensional particle swarm optimization for robust blind image watermarking using intertwining logistic map and hybrid domain. Soft Comput. 2020, 24, 10561–10584. [Google Scholar] [CrossRef]
- Swaraja, K.; Meenakshi, K.; Kora, P. An optimized blind dual medical image watermarking framework for tamper localization and content authentication in secured telemedicine. Biomed. Signal Process. Control 2020, 55, 101665. [Google Scholar]
- Alzahrani, A.; Memon, N.A. Blind and robust watermarking scheme in hybrid domain for copyright protection of medical images. IEEE Access 2021, 9, 113714–113734. [Google Scholar] [CrossRef]
- Zheng, P.; Zhang, Y. A robust image watermarking scheme in hybrid transform domains resisting to rotation attacks. Multimed. Tools Appl. 2020, 79, 18343–18365. [Google Scholar] [CrossRef]
- Ernawan, F.; Ariatmanto, D.; Firdaus, A. An improved image watermarking by modifying selected DWT-DCT coefficients. IEEE Access 2021, 9, 45474–45485. [Google Scholar] [CrossRef]
- Dargan, S.; Kumar, M.; Ayyagari, M.R.; Kumar, G. A survey of deep learning and its applications: A new paradigm to machine learning. Arch. Comput. Methods Eng. 2020, 27, 1071–1092. [Google Scholar] [CrossRef]
- Liu, W.; Wang, Z.; Liu, X.; Zeng, N.; Liu, Y.; Alsaadi, F.E. A survey of deep neural network architectures and their applications. Neurocomputing 2017, 234, 11–26. [Google Scholar] [CrossRef]
- Naranjo-Torres, J.; Mora, M.; Hernández-García, R.; Barrientos, R.J.; Fredes, C.; Valenzuela, A. A review of convolutional neural network applied to fruit image processing. Appl. Sci. 2020, 10, 3443. [Google Scholar] [CrossRef]
- Bagheri, M.; Mohrekesh, M.; Karimi, N.; Samavi, S.; Shirani, S.; Khadivi, P. Image watermarking with region of interest determination using deep neural networks. In Proceedings of the 2020 19th IEEE International Conference on Machine Learning and Applications (ICMLA), Virtual Event, 14–17 December 2020; pp. 1067–1072. [Google Scholar]
- Sun, L.; Xu, J.; Liu, S.; Zhang, S.; Li, Y.; Shen, C. A robust image watermarking scheme using Arnold transform and BP neural network. Neural Comput. Appl. 2018, 30, 2425–2440. [Google Scholar] [CrossRef]
- Cu, V.L.; Nguyen, T.; Burie, J.C.; Ogier, J.M. A robust watermarking approach for security issue of binary documents using fully convolutional networks. Int. J. Doc. Anal. Recognit. (IJDAR) 2020, 23, 219–239. [Google Scholar] [CrossRef]
- Ingaleshwar, S.; Dharwadkar, N.V. Water chaotic fruit fly optimization-based deep convolutional neural network for image watermarking using wavelet transform. Multimed. Tools Appl. 2021, 1–25. [Google Scholar] [CrossRef]
- Sinhal, R.; Jain, D.K.; Ansari, I.A. Machine learning based blind color image watermarking scheme for copyright protection. Pattern Recognit. Lett. 2021, 145, 171–177. [Google Scholar] [CrossRef]
- Kandi, H.; Mishra, D.; Gorthi, S.R.S. Exploring the learning capabilities of convolutional neural networks for robust image watermarking. Comput. Secur. 2017, 65, 247–268. [Google Scholar] [CrossRef]
- Vukotić, V.; Chappelier, V.; Furon, T. Are deep neural networks good for blind image watermarking? In Proceedings of the 2018 IEEE International Workshop on Information Forensics and Security (WIFS), Hong Kong, China, 11–13 December 2018; pp. 1–7. [Google Scholar]
- Vukotić, V.; Chappelier, V.; Furon, T. Are classification deep neural networks good for blind image watermarking? Entropy 2020, 22, 198. [Google Scholar] [CrossRef]
- Kazemi, M.; Pourmina, M.; Mazinan, A. Analysis of watermarking framework for color image through a neural network-based approach. Complex Intell. Syst. 2020, 6, 213–220. [Google Scholar] [CrossRef]
- Zear, A.; Singh, A.K.; Kumar, P. A proposed secure multiple watermarking technique based on DWT, DCT and SVD for application in medicine. Multimed. Tools Appl. 2018, 77, 4863–4882. [Google Scholar] [CrossRef]
- Zear, A.; Singh, A.K.; Kumar, P. Robust watermarking technique using back propagation neural network: A security protection mechanism for social applications. Int. J. Inf. Comput. Secur. 2017, 9, 20–35. [Google Scholar] [CrossRef]
- Huynh-The, T.; Hua, C.H.; Tu, N.A.; Kim, D.S. Robust image watermarking framework powered by convolutional encoder-decoder network. In Proceedings of the 2019 Digital Image Computing: Techniques and Applications (DICTA), Perth, Australia, 2–4 December 2019; pp. 1–7. [Google Scholar]
- Mellimi, S.; Rajput, V.; Ansari, I.A.; Ahn, C.W. A fast and efficient image watermarking scheme based on Deep Neural Network. Pattern Recognit. Lett. 2021, 151, 222–228. [Google Scholar] [CrossRef]
- Sinhal, R.; Ansari, I.A.; Jain, D.K. Real-time watermark reconstruction for the identification of source information based on deep neural network. J. Real-Time Image Process. 2020, 17, 2077–2095. [Google Scholar] [CrossRef]
- Zhong, X.; Huang, P.C.; Mastorakis, S.; Shih, F.Y. An automated and robust image watermarking scheme based on deep neural networks. IEEE Trans. Multimed. 2020, 23, 1951–1961. [Google Scholar] [CrossRef]
- Hamamoto, I.; Kawamura, M. Neural watermarking method including an attack simulator against rotation and compression attacks. IEICE Trans. Inf. Syst. 2020, 103, 33–41. [Google Scholar] [CrossRef]
- Mun, S.M.; Nam, S.H.; Jang, H.; Kim, D.; Lee, H.K. Finding robust domain from attacks: A learning framework for blind watermarking. Neurocomputing 2019, 337, 191–202. [Google Scholar] [CrossRef]
- Zhu, L.; Wen, X.; Mo, L.; Ma, J.; Wang, D. Robust location-secured high-definition image watermarking based on key-point detection and deep learning. Optik 2021, 248, 168194. [Google Scholar] [CrossRef]
- Lee, J.E.; Seo, Y.H.; Kim, D.W. Convolutional neural network-based digital image watermarking adaptive to the resolution of image and watermark. Appl. Sci. 2020, 10, 6854. [Google Scholar] [CrossRef]
- Mun, S.M.; Nam, S.H.; Jang, H.U.; Kim, D.; Lee, H.K. A robust blind watermarking using convolutional neural network. arXiv 2017, arXiv:1704.03248. [Google Scholar]
- Ahmadi, M.; Norouzi, A.; Karimi, N.; Samavi, S.; Emami, A. ReDMark: Framework for residual diffusion watermarking based on deep networks. Expert Syst. Appl. 2020, 146, 113157. [Google Scholar] [CrossRef]
- Kim, W.H.; Kang, J.; Mun, S.M.; Hou, J.U. Convolutional neural network architecture for recovering watermark synchronization. Sensors 2020, 20, 5427. [Google Scholar] [CrossRef] [PubMed]
- Fierro-Radilla, A.; Nakano-Miyatake, M.; Cedillo-Hernandez, M.; Cleofas-Sanchez, L.; Perez-Meana, H. A robust image zero-watermarking using convolutional neural networks. In Proceedings of the 2019 7th International Workshop on Biometrics and Forensics (IWBF), Cancun, Mexico, 2–3 May 2019; pp. 1–5. [Google Scholar]
- Ge, S.; Xia, Z.; Tong, Y.; Weng, J.; Liu, J. A Screen-Shooting Resilient Document Image Watermarking Scheme using Deep Neural Network. arXiv 2022, arXiv:2203.05198. [Google Scholar] [CrossRef]
- Guo, S.; Zhang, T.; Qiu, H.; Zeng, Y.; Xiang, T.; Liu, Y. The hidden vulnerability of watermarking for deep neural networks. arXiv 2020, arXiv:2009.08697. [Google Scholar]
- Lv, L. Smart Watermark to Defend against Deepfake Image Manipulation. In Proceedings of the 2021 IEEE 6th International Conference on Computer and Communication Systems (ICCCS), Chengdu, China, 23–26 April 2021; pp. 380–384. [Google Scholar]
- Nguyen, T.T.; Nguyen, Q.V.H.; Nguyen, D.T.; Nguyen, D.T.; Huynh-The, T.; Nahavandi, S.; Nguyen, T.T.; Pham, Q.V.; Nguyen, C.M. Deep learning for deepfakes creation and detection: A survey. Comput. Vis. Image Underst. 2022, 223, 103525. [Google Scholar] [CrossRef]
- Yu, Y.; Ni, R.; Zhao, Y. Mining generalized features for detecting ai-manipulated fake faces. arXiv 2020, arXiv:2010.14129. [Google Scholar]


| Reference | Approaches | Objectives | Cover/Watermark Size | Evaluation Metric | Advantages and Weaknesses |
|---|---|---|---|---|---|
| [70] | Invariant significant bitplane probability density | Robustness against desynchronization attacks | 512 × 512 pseudorandom sequence of 85 bits | PSNR, MSE, SSIM | + Resistance to common image-processing attacks and desynchronization attacks - High computational complexity - Less robust against JPEG compression and scaling |
| [73] | LSB, ISB | Tamper detection and localization of medical/general images | 256 × 256 64 × 64 | PSNR, SSIM, BER | + Low complexity + Highly visual image - Fragile - Lack of irreversibility |
| [74] | LSB substitution mechanism | Enhance the conventional LSB technique of digital image watermarking | 700 × 700 100 × 100 | PSNR, NCC | + Low complexity + High-quality image - Non-blind - Less robust against median filtering and speckle noise |
| Reference | Approaches | Objectives | Cover/Watermark Size | Evaluation Metric | Advantages and Weaknesses |
|---|---|---|---|---|---|
| [83] | DCT DE KELM | Achieve good balance between robustness and invisibility | PSNR, NC | + Robust against numerous attacks - Fragile to rotational attacks | |
| [85] | DCT JND Arnold transform | Achieve good balance between robustness and invisibility | 512 × 512 64 × 64 | PSNR, SSIM, NC, BER | + Resist different attacks, such as median filter and image rotation - Security and complexity analysis are inadequate |
| [94] | QDFT EPA MSPSAM MM, PSO | Provide better robustness against JPEG attacks and contrast enhancement | Objective Value PSNR MSSIM BER | + Resist several image-processing attacks, including JPEG attacks - High computational time | |
| [95] | DFT, PSO | Improve performance, in particular the security | COCO dataset 32-bit binary watermark | VIF PSNR Average BCR BER | + Withstand image-processing attacks and geometrical ones - Payload needs to be improved |
| [101] | DWT Entropy Alpha blending | Reduce computational cost considering robustness and imperceptibility | PSNR SSIM NCC | + Low computational cost + Higher PSNR value + Robust against various sorts of attacks - Non-blind - Testing with one type of watermark data is inadequate - Security and complexity analysis need to be discussed in detail | |
| [102] | DWT Paillier cryptosystem Turbo code Step space-filling curve | Provide robustness and security of the EPR data | text watermark and different sizes of watermark image | NPSR UACI BER NC | + Robust and secure for medical-image watermarking - Lack of computational complexity test |
| Reference | Approaches | Objectives | Cover/Watermark Size | Evaluation Metric | Advantages and Weaknesses |
|---|---|---|---|---|---|
| [108] | DWT DCT SVD | Robustness against rotation attacks | 512 × 512 Multiple sizes | NC, PSNR | + Robust against various types of attacks including rotation attacks - Few attack analytics - Security was not considered in the scheme |
| [109] | DWT DCT Arnold transform | Improve imperceptibility considering robustness | 512 × 512 32 ×32 | ARE SSIM PSNR NC BER | + High PSNR and SSIM values - Lower BER values under various attacks - Limited embedding capacity |
| Reference | Architecture | Goal | Embedding Location | Cover/Watermark Size | Evaluation Metric | Advantages and Weaknesses |
|---|---|---|---|---|---|---|
| [113] | R-CNN | Find the good stength factor used to determine the appropriate location for embedding | DCT-DWT sub-blocks | 512 × 512 4 × 4 | PSNR = 49.10 dB SSIM = 0.99 NC = 1 BER = 0 | + High image quality + Robust against several image-processing attacks, such as JPEG, Gaussian noise, and median filter - Comparison with one existing method is inadequate - Robustness should be investigated in detail - Lower embedding capacity |
| [116] | CNNs | Find the optimal region to conceal the watermark | DWT coefficients | MRI scans | correlation coefficient = 1 PSNR = 45.2 dB (without noise scenario) | + High values of correlation coefficient and PSNR - Non-blind - Focus only on imperceptibility |
| [117] | ANN | Reduce computational cost of the embedding process | Y channel coefficients | 512 × 512 32 × 32 | PSNR = 39.9 dB SSIM = 0.99 (Lena image) Avg BER = 0.05 Avg embedding time = 0.41 s | + Low computational complexity + Robust against different signal-processing operations - Performance should be studied with multiple watermarks - Geometric attacks must be studied |
| [118] | Auto-encoder | Learning codebook images | Vectorised codebook image | 128 × 128 64 × 64 | Avg PSNR = 42.03 dB NC = 0.96 crop() | + High security + Imperceptibility and robustness - Non-blind - High computational cost |
| Reference | Architecture | Goal | Embedding Location | Cover/Watermark Size | Evaluation Metric | Advantages and Weaknesses |
|---|---|---|---|---|---|---|
| [17] | Fast R-CNN | Learn to extract the watermark | Block-DCT component | - - | Avg. PSNR = 49.10 dB Extraction time = 1.19 s | + High PSNR values - Focus only on imperceptibility |
| [123] | BPNN | Remove noise spikes from the watermarked image | S vector of the host image | 512 × 512 64 × 64 | NC = 0.98 PSNR = 34.78 dB (peppers image, gain = 0.1) | + Good imperceptibility and robustness - High computational complexity - Performance needs to be investigated with multiple watermaks |
| [124] | Encoder–Decoder | Recover robust watermark from the host image | DWT coefficients | 512 × 512 64 × 64 | Avg NC = 0.99 Avg PSNR = 47.85 dB Avg SSIM = 0.99 | + Withstand image transformations and geometric distortions - High PSNR values - Security performance should be investigated |
| [125] | DNN | Identify changes made by attacks | Block LWT component | 512 × 512 32 × 32 | Avg NC = 0.98 Avg PSNR = 44.11 dB | + Robust against common image-processing attacks + Fast watermark extraction - Needs further improvement in robustness performance |
| [23] | R-CNN | Map the relationship between the host image and the watermark image | DCT-SVD sub-blocks | 512 × 512 32 × 32 | NC = 0.9930 (salt and pepper 0.5) | + Outperform the false detection problem + Support multi-type watermark + High security and robustness - Less robust to rotation and cropping - Lack of complexity analysis |
| Reference | Architecture | Goal | Embedding Location | Cover/Watermark Size | Evaluation Metric | Advantages and Weaknesses |
|---|---|---|---|---|---|---|
| [127] | Image fusion framework | Improve robustness and efficiency | Concatenation of the host image with the watermark image | 128 × 128 32 × 32 | PSNR = 39.72 dB BER = 0 (cropping ) | + Good performance against typical attacks + Require only the watermarked image for extraction + Applicable in challenging camera processes - Image fusion leads to data loss and slows data processing - Geometric attacks must be investigated |
| [128] | Generator–discriminator network | Achieve robustness against rotation and JPEG compression | Luminosity value of the image | 4608 × 3456 8 bit | Avg PSNR = 36.3 dB BER = 0.08 (JPEG Q = 50) | + High robustness against rotation and JPEG compression attacks - Could resist only a limited number of attacks - Execution time must be investigated - Low embedding capacity |
| [129] | Backpropagation, Auto-encoders WMnet | Find the robust domain from attacks | Image blocks | 512 × 512 24 bit | PSNR = 40 dB NC = 1 (Rotation 10°) SSIM = 0.98 NC = 1 (Gaussian filtering) | + Optimized robustness and high image quality - Solution for high-definition image is not provided - Low NC values for rotation and cropping |
| [130] | Keypoint detection MDResNet | Solve high-definition image watermarking problems | Various scale-invariant regions | 512 × 512 px 512 × 512 bit | PSNR = 43.68 dB SSIM = 0.97 NC = 0.96 BER = 0.01 | + Robust to both common signal operations and geometric attacks + Support high-definition image - High embedding execution time - Robustness to several attacks must be improved |
| [131] | CNNs | Learn invisible and robust watermarking | Concatenation of the pre-processed cover and the pre-processed watermark | 128 × 128 8 × 8 | PSNR = 40.58 dB BER = 0.01 (JPEG s = 90) | + Embedding and extraction without restrictions on the cover and the watermark + Good balance between invisibility and robustness - BER values for some geometric attacks are inadequate - Lack of complexity analysis |
| [132] | CNNs | Secure robustness of watermarking | Host image blocks | 512 × 512 64 × 64 | PSNR = 39.9 dB (peppers image) NC = 0.98 (Resizing , with registration) | + Withstand different types of attacks - Higher detection time - Poor results against rotation |
| [133] | ReDMark | Learn new watermarking algorithm in any desired transform domain | Addition of the residual watermark and the host image | 512 × 512 32 × 32 | PSNR = 40.24 dB SSIM = 0.98 () BER = 1.6 (JPEG) | + Improved security and robustness especially against JPEG - Withstand only known attacks from training phase - Increasing strength factor decreases PSNR and SSIM |
| [134] | Template generation network | Recover watermark from geometric distortions | Predefined locations of the image | 512 × 512 512 × 512 | PSNR = 43.66 dB SSIM = 0.98 BER = 0.12 (Rotation 50°) | + Robust to geometric attacks + High imperceptibility - Large-scale image must be investigated - Focus only on geometric attacks - Lack of execution time analysis |
| [135] | Master share framework | Learn zero watermarking | Combination of inherent image features with owner’s watermark sequence | 300 × 300 10 × 10 | PSNR = 33.15 dB (Compression 100) BER = 0.01 NC = 0.98 (Gaussian filtering ) | + Low computational cost + Robust against several types of attacks - Lack of comparison with existing techniques - Robustness analysis are inadequate especially for synchronization attacks |
| [136] | Encoder–Decoder | Resist screen-shooting attacks | Concatenation of the cover and the watermark | 400 × 400 100 bit | PSNR = 34.10 dB SSIM = 0.91 CPP = 6.88 Average bit accuracy > 97 | + High performance against screen-shooting attacks - Lower embedding capacity - Testing with one type of watermark data is inadequate - Image captures are taken with care |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Boujerfaoui, S.; Riad, R.; Douzi, H.; Ros, F.; Harba, R. Image Watermarking between Conventional and Learning-Based Techniques: A Literature Review. Electronics 2023, 12, 74. https://doi.org/10.3390/electronics12010074
Boujerfaoui S, Riad R, Douzi H, Ros F, Harba R. Image Watermarking between Conventional and Learning-Based Techniques: A Literature Review. Electronics. 2023; 12(1):74. https://doi.org/10.3390/electronics12010074
Chicago/Turabian StyleBoujerfaoui, Said, Rabia Riad, Hassan Douzi, Frédéric Ros, and Rachid Harba. 2023. "Image Watermarking between Conventional and Learning-Based Techniques: A Literature Review" Electronics 12, no. 1: 74. https://doi.org/10.3390/electronics12010074
APA StyleBoujerfaoui, S., Riad, R., Douzi, H., Ros, F., & Harba, R. (2023). Image Watermarking between Conventional and Learning-Based Techniques: A Literature Review. Electronics, 12(1), 74. https://doi.org/10.3390/electronics12010074







