Machine Learning-Enabled Internet of Things (IoT): Data, Applications, and Industry Perspective
Abstract
1. Introduction
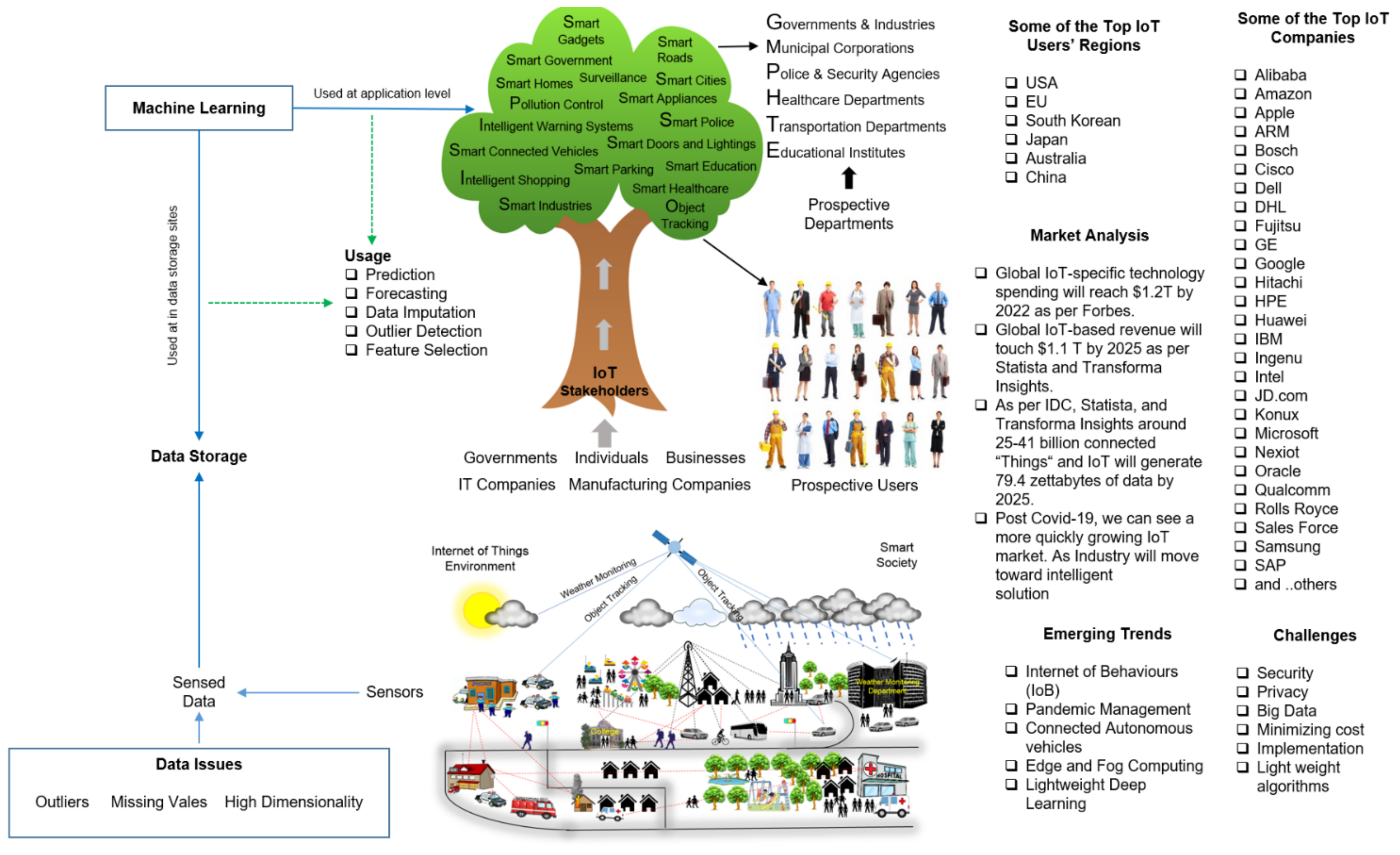
1.1. IoT Industry and Market
1.2. Data Production
1.3. Machine Learning and IoT
- The application area of IoT is enormous, as mentioned in Figure 1. Every application has data with particular properties.
- At Google’s Zeitgeist 2011 event, Google’s chief scientist Peter Norvig famously said, “We don’t have better algorithms than anyone else; we just have more data.” However, few researchers support the opposite. Which is better? A highly sophisticated MLA [25], with more data [26,27,28] or limited but high-quality data [29,30]? This question still has no answer and is one of the significant conflict areas among ML researchers, as opinions vary.
1.4. Contributions
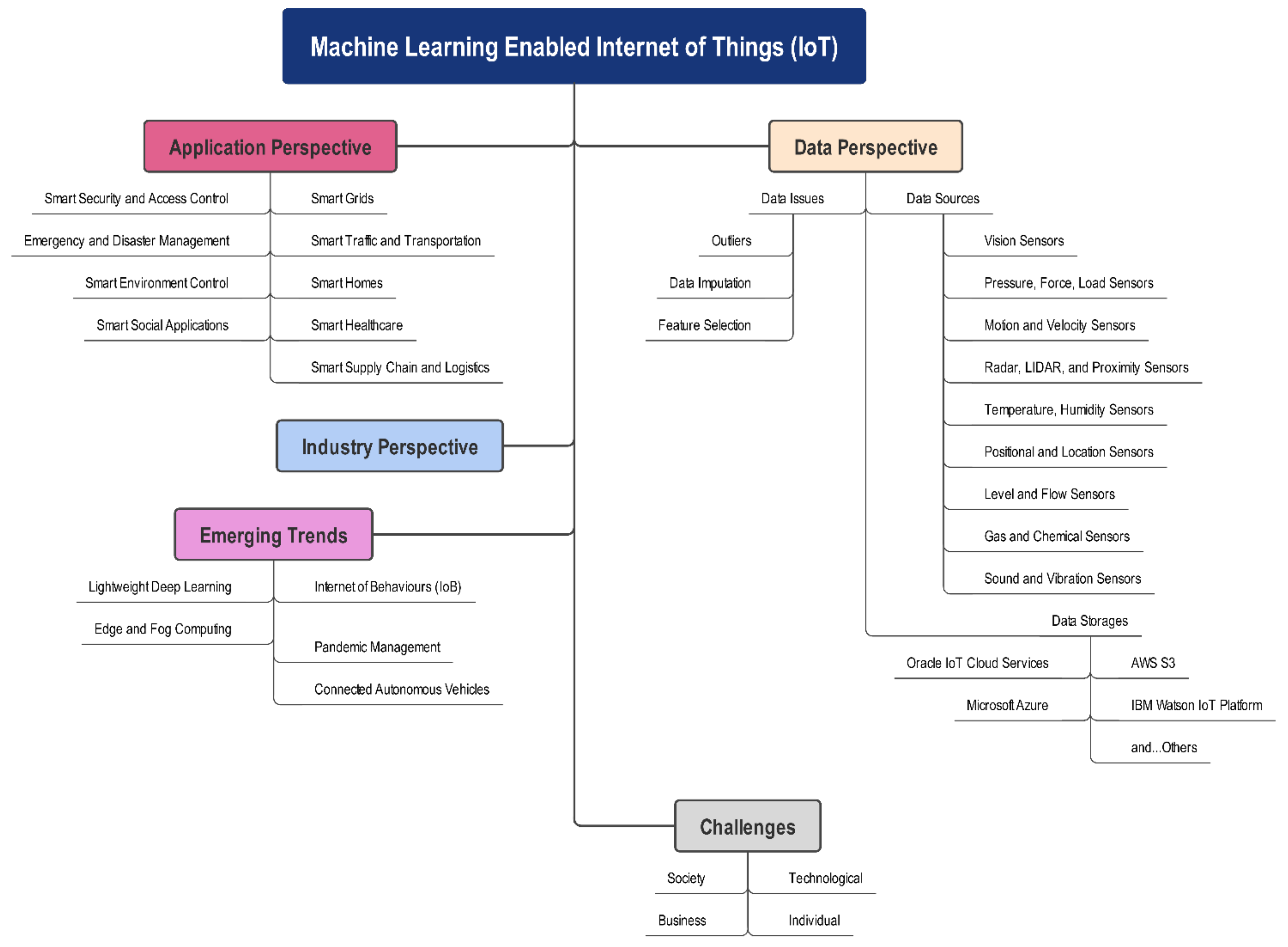
- Firstly, we classify IoT-related research and development work into three major perspectives (classes): data, application, and industry.
- Secondly, the paper gives insight into the current state-of-art research and developments in IoT with a specific focus on ML-related developments.
- Thirdly, the paper identifies emerging IoT trends that will use the machine at its core to develop futuristic and sustainable solutions.
- Lastly, the paper helps the readers to identify future opportunities in IoT-based ML research.
| No. | Paper | Year | Objectives |
|---|---|---|---|
| 1 | Siow et al. [38] | 2018 | ML-based IoT survey of IoT analytics, types, and infrastructure |
| 2 | Mohammadi et al. [39] | 2018 | Deep learning-based IoT survey of big data and streaming analytics |
| 3 | Mahdavinejad et al. [40] | 2018 | Use case based on usage of machine learning for smart-city environment |
| 4 | Alam et al. [41] | 2017 | ML-based IoT survey of data fusion techniques |
1.5. Paper Structure
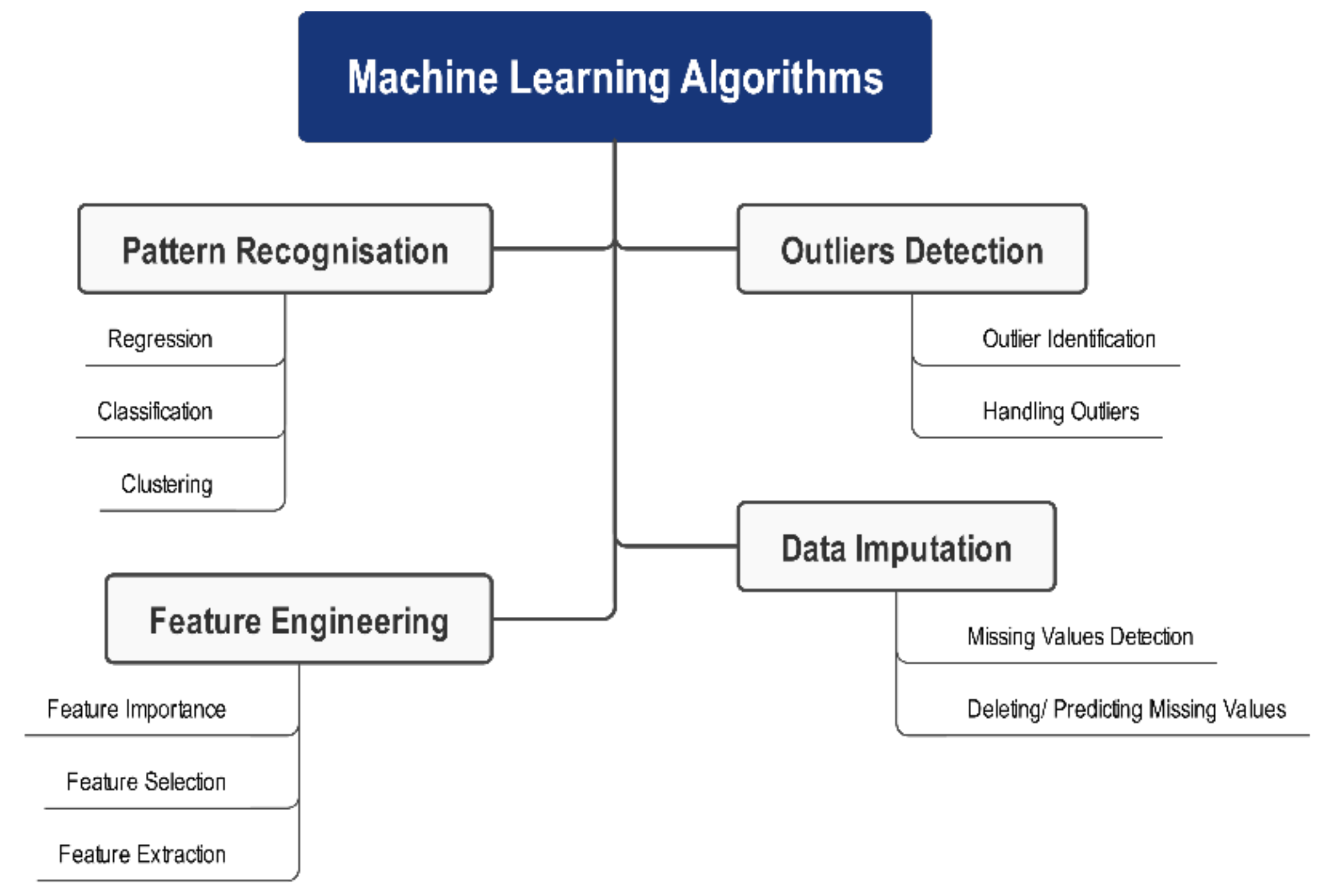
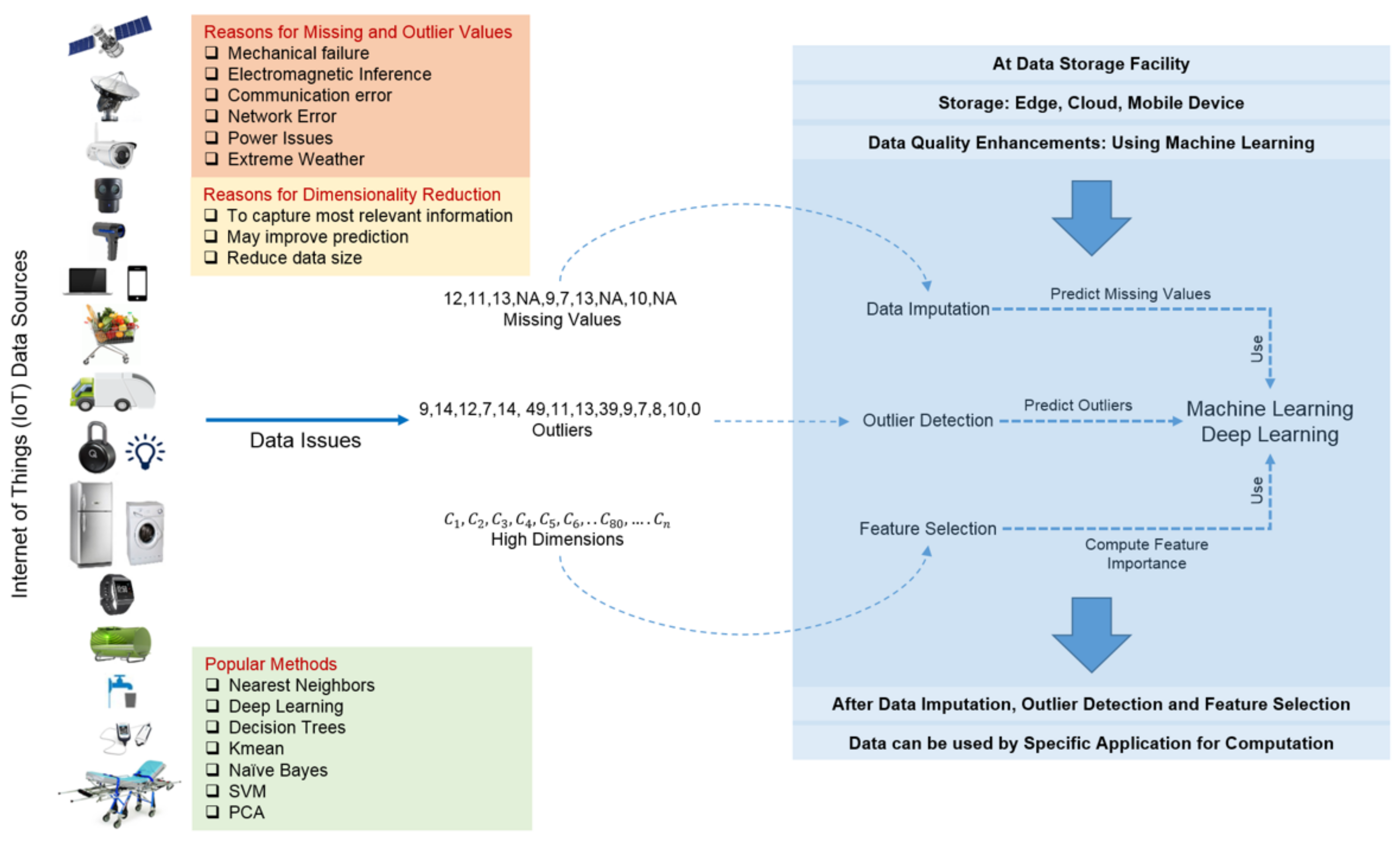
2. Data Perspective
2.1. Data Sources
2.2. Data Storage
2.3. Data Issues
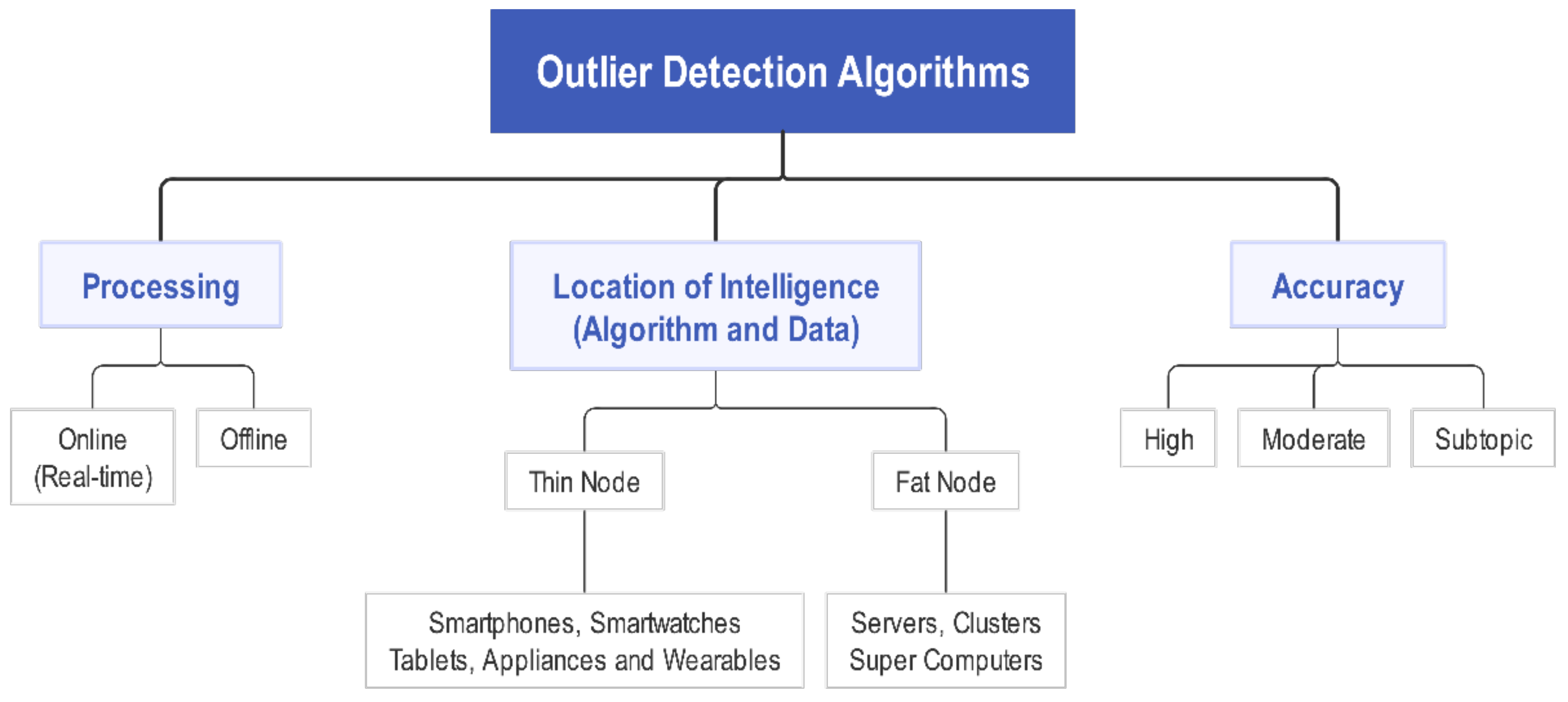
2.3.1. Outlier Detection
2.3.2. Data Imputation
2.3.3. Feature Selection
3. Applications Perspective
3.1. Smart Grids
3.2. Smart Traffic and Transportation
3.3. Smart Homes
3.4. Smart Health Care
3.5. Smart Supply Chain and Logistics
- IoT “things” can communicate promptly, allowing the possibility of knowing where they are at all times.
- Object tracking facilitated by IoT results in improved asset and fleet management, which means well-planned scheduling, better routing, and on-time product deliveries.
- Better control of mobile assets with IoT means knowing where they are and how they are used.
- Downtime will be audited closely in real time.
- It increases logistics transparency.
3.6. Smart Social Applications
3.7. Smart Environment Control
3.8. Emergency and Disaster Management
3.9. Smart Security and Access Control
4. Industry Perspective
- enable a high degree of interaction with humans with the help of text and voice
- perceive images and scenes
- perform ML from sensory inputs
- establish data correlations with external data sources, such as weather or Twitter.
5. Emerging Trends
5.1. Internet of Behavior (IoB)
5.2. Pandemic Management
5.3. Connected Autonomous Vehicles
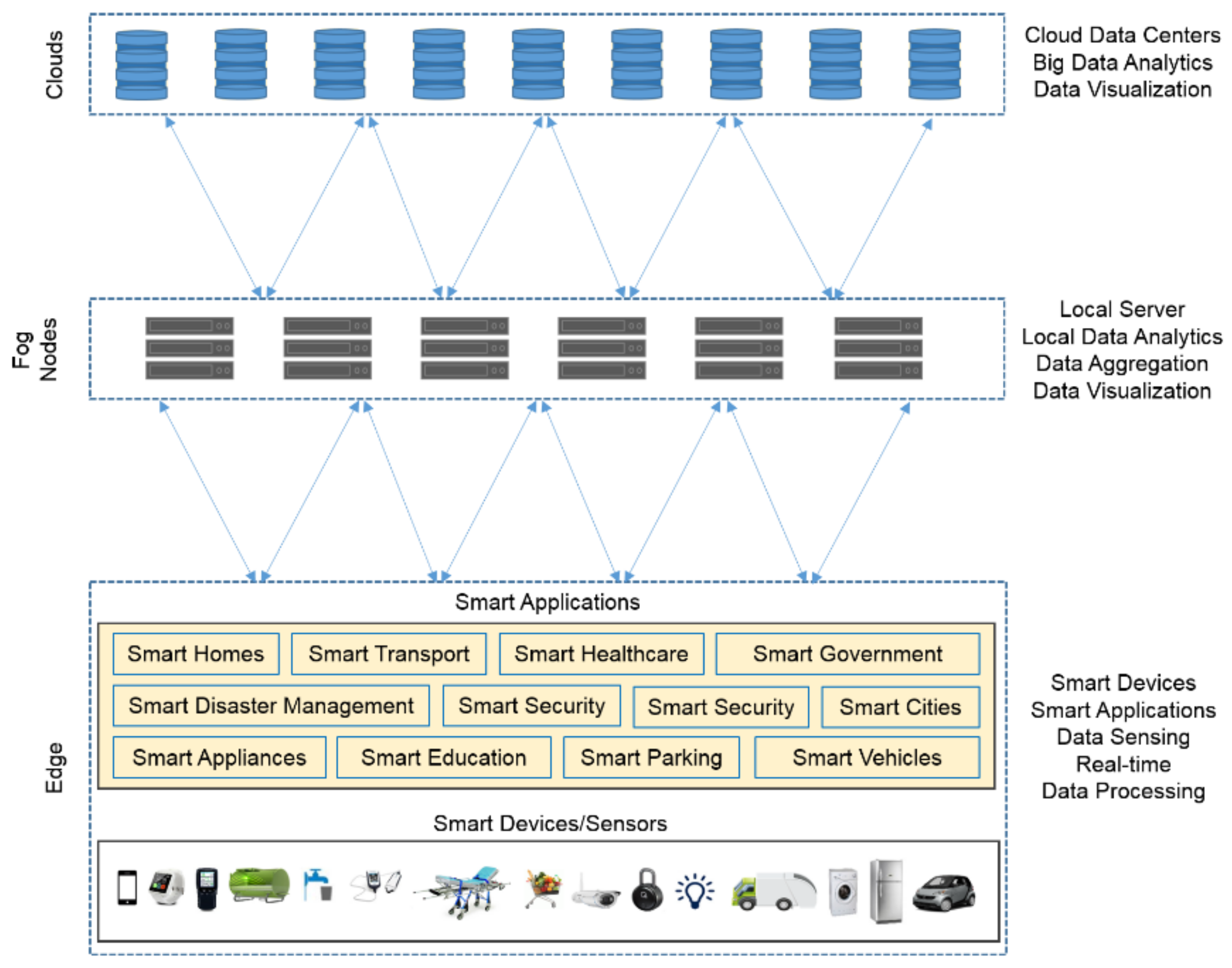
5.4. Edge and Fog Computing
5.5. Lightweight Deep Learning
6. Challenges
6.1. Technological Challenges
6.2. Individual Challenges
6.3. Business Challenges
6.4. Society Challenges
7. Conclusions
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
References
- Atzori, L.; Iera, A.; Morabito, G. The Internet of Things: A Survey. Comput. Netw. 2010, 54, 2787–2805. [Google Scholar] [CrossRef]
- Statista IoT Connected Devices Worldwide 2019–2030. Available online: https://www.statista.com/statistics/1183457/iot-connected-devices-worldwide/ (accessed on 25 June 2022).
- Transforma Insights Global IoT Market to Grow to 24.1 Billion Devices in 2030, Generating $1.5 Trillion Annual Revenue. Available online: https://transformainsights.com/news/iot-market-24-billion-usd15-trillion-revenue-2030 (accessed on 25 June 2022).
- Kar, I. The Top-Country Early-Adopters of the Internet of Things, Ranked Google Wants to Have Drones Buzzing around Offices. Available online: http://qz.com/648863/the-top-country-early-adopters-of-the-internet-of-things-ranked/ (accessed on 2 June 2022).
- Mattern, F.; Floerkemeier, C. From the Internet of Computers to the Internet of Things. In From Active Data Management to Event-Based Systems and More; Springer: Berlin/Heidelberg, Germany, 2010; Volume 6462, pp. 242–259. [Google Scholar] [CrossRef]
- Tanwar, S.; Garg, J.; Gupta, M.; Rana, A. Opportunities and Challenges in Machine Learning with IoT. Available online: https://wandb.ai/site?utm_source=bing&utm_medium=cpc&utm_campaign=Conversions%3A+ML+Tools&utm_content=Ad+group+1&msclkid=4b1aa96029de11b0fa09ca68ba118cd4&utm_term=machine%20learning%20tools (accessed on 25 June 2022).
- Guo, B.; Zhang, D.; Yu, Z.; Liang, Y.; Wang, Z.; Zhou, X. From the Internet of Things to Embedded Intelligence. World Wide Web 2013, 16, 399–420. [Google Scholar] [CrossRef]
- Guo, B.; Zhang, D.; Wang, Z. Living with Internet of Things: The Emergence of Embedded Intelligence. In Proceedings of the 2011 International Conference on Internet of Things and 4th International Conference on Cyber, Physical and Social Computing, Dalian, China, 19–22 October 2011; pp. 297–304. [Google Scholar] [CrossRef]
- Jain, R. Recent Machine Learning Applications to Internet of Things (IoT). Abstract: Table of Contents: 1–19. Available online: https://www.cs.wustl.edu/~jain/cse570-15/ftp/iot_ml/#sec7 (accessed on 2 June 2022).
- Keim, D.A.; Munzner, T.; Rossi, F.; Verleysen, M. Bridging Information Visualization with Machine Learning (Dagstuhl Seminar 15101). Dagstuhl. Rep. 2015, 5, 7. [Google Scholar] [CrossRef]
- Davarzani, B.L.; Purdy, M. The Internet of Things Is Now a Thing 2015. Available online: https://ssir.org/articles/entry/the_internet_of_things_is_now_a_thing (accessed on 2 June 2022).
- Purdy, M.; Ladan, D. The Growth Game-Changer: How the Industrial Internet of Things Can Drive Progress and Prosperity; 2015. Available online: https://www.bl.uk/business-and-management/collection-items/suppressed-by-publisher/accenture/growth-gamechanger-how-the-industrial-internet-of-things-can-drive-progress-and-prosperity (accessed on 2 June 2022).
- Kearney, A.T. The Internet of Things: A New Path to European Prosperity; 2016. Available online: https://www.fr.kearney.com/digital-transformation/article?/a/the-internet-of-things-a-new-path-to-european-prosperity (accessed on 2 June 2022).
- Zaslavsky, A.; Perera, C.; Georgakopoulos, D. Sensing as a Service and Big Data. In Proceedings of the International Conference on Advances in Cloud Computing (ACC), Bangalore, India, 4–6 July 2012; pp. 21–29. [Google Scholar]
- Isik, O.; Jones, M.; Sidorova, A. ‘Big data’, the ‘internet of things’ and the ‘internet of signs’ daniel. Intell. Syst. Account. Financ. Manag. 2011, 176, 161–176. [Google Scholar] [CrossRef]
- Sun, Y.; Song, H.; Jara, A.; Bie, R. Internet of Things and Big Data Analytics for Smart and Connected Communities. IEEE Access 2016, 4, 766–773. [Google Scholar] [CrossRef]
- Lindstrom, M. Small Data: The Tiny Clues That Uncover Huge Trends; St. Martin’s Press: London, UK, 2016; ISBN 9781250080684. [Google Scholar]
- Kavis, M. Forget Big Data—Small Data Is Driving. Forbes 2016, 1–5. Available online: http://www.forbes.com/sites/mikekavis/2015/02/25/forget-big-data-small-data-is-driving-the-internet-of-things/#3de078be661b. (accessed on 2 June 2022).
- Chen, F.; Deng, P.; Wan, J.; Zhang, D.; Vasilakos, A.V.; Rong, X. Data Mining for the Internet of Things: Literature Review and Challenges. Int. J. Distrib. Sens. Netw. 2015, 11, 431047. [Google Scholar] [CrossRef]
- Qin, Y.; Sheng, Q.Z.; Falkner, N.J.G.; Dustdar, S.; Wang, H.; Vasilakos, A.V. When Things Matter: A Survey on Data-Centric Internet of Things. J. Netw. Comput. Appl. 2016, 64, 137–153. [Google Scholar] [CrossRef]
- Abraham, A.; Muda, A.K.; Choo, Y.H. Pattern Analysis, Intelligent Security and the Internet of Things; Springer: Cham, Switzerland, 2015; Volume 355. [Google Scholar] [CrossRef]
- Zhang, L.; Jeong, D.; Lee, S. Data Quality Management in the Internet of Things. Sensors 2021, 21, 5834. [Google Scholar] [CrossRef]
- Aggarwal, C.C.; Ashish, N.; Sheth, A. The Internet of Things: A Survey from the Data-Centric Perspective. In Managing and Mining Sensor Data; Springer: Boston, MA, USA, 2013; pp. 383–428. [Google Scholar] [CrossRef]
- Abu-Elkheir, M.; Hayajneh, M.; Ali, N.A. Data Management for the Internet of Things: Design Primitives and Solution. Sensors 2013, 13, 15582–15612. [Google Scholar] [CrossRef]
- Torrance, M. Better Algorithms Beat More Data—And Here’ s Why. Available online: http://allthingsd.com/20121128/better-algorithms-beat-more-data-and-heres-why/ (accessed on 4 July 2022).
- Cleland, S. Google’s " Infringenovation " Secrets. Available online: http://www.forbes.com/sites/scottcleland/2011/10/03/googles-infringenovation-secrets/#3e263e2373de (accessed on 6 July 2022).
- Domingos, P. A Few Useful Things to Know about Machine Learning. Commun. ACM 2012, 55, 78. [Google Scholar] [CrossRef]
- Halevy, A.; Norvig, P.; Pereira, F. The Unreasonable Effectiveness of Data. IEEE Intell. Syst. 2009, 24, 8–12. [Google Scholar] [CrossRef]
- Sessions, V.; Valtorta, M. The Effects of Data Quality on Machine Learning Algorithms. ICIQ. Available online: http://mitiq.mit.edu/ICIQ/Documents/IQ%20Conference%202006/papers/The%20Effects%20of%20Data%20Quality%20on%20Machine%20Learning%20Algorithms.pdf (accessed on 2 June 2022).
- Cortes, C.; Jackel, L.; Chiang, W. Limits on Learning Machine Accuracy Imposed by Data Quality. Available online: https://www.aaai.org/Papers/KDD/1995/KDD95-007.pdf (accessed on 2 June 2022).
- Ambasna-Jones, M. Will Automation and the Internet of Things Lead to Mass Unemployment? Available online: https://www.theguardian.com/media-network/2015/may/27/internet-of-things-automation-unemployment (accessed on 20 May 2022).
- Stewart, H. Robot Revolution: Rise of “thinking” Machines Could Exacerbate Inequality. Guardian 2015. Available online: https://cacm.acm.org/news/194049-robot-revolution-rise-of-thinking-machines-could-exacerbate-inequality/fulltext (accessed on 20 May 2022).
- Grigorik, I. Intuition & Data-Driven Machine Learning. Available online: https://www.igvita.com/2011/04/20/intuition-data-driven-machine-learning/ (accessed on 10 May 2022).
- Banko, M.; Brill, E. Mitigating the Paucity-of-Data Problem: Exploring the Effect of Training Corpus Size on Classifier Performance for Natural Language Processing. Comput. Linguist. 2001, 2011, 2–6. [Google Scholar] [CrossRef]
- Moreno-Cano, V.; Terroso-Saenz, F.; Skarmeta-Gomez, A.F. Big Data for IoT Services in Smart Cities. In Proceedings of the 2015 IEEE 2nd World Forum on Internet of Things (WF-IoT), Milan, Italy, 14–16 December 2015; pp. 418–423. [Google Scholar]
- Shanthamallu, U.S.; Spanias, A.; Tepedelenlioglu, C.; Stanley, M. A Brief Survey of Machine Learning Methods and Their Sensor and IoT Applications. In Proceedings of the 2017 8th International Conference on Information, Intelligence, Systems Applications (IISA), Larnaca, Cyprus, 27–30 August 2017; pp. 1–8. [Google Scholar]
- Sharma, K.; Nandal, R. A Literature Study on Machine Learning Fusion with IoT. In Proceedings of the International Conference on Trends in Electronics and Informatics, ICOEI, Tirunelveli, India, 23–25 April 2019; pp. 1440–1445. [Google Scholar] [CrossRef]
- Siow, E.; Tiropanis, T.; Hall, W. Analytics for the Internet of Things: A Survey. ACM Comput. Surv. 2018, 51, 1–36. [Google Scholar] [CrossRef]
- Mohammadi, M.; Al-Fuqaha, A.; Sorour, S.; Guizani, M. Deep Learning for IoT Big Data and Streaming Analytics: A Survey. IEEE Commun. Surv. Tutor. 2018, 20, 2923–2960. [Google Scholar] [CrossRef]
- Mahdavinejad, M.S.; Rezvan, M.; Barekatain, M.; Adibi, P.; Barnaghi, P.; Sheth, A.P. Machine Learning for Internet of Things Data Analysis: A Survey. Digit. Commun. Netw. 2018, 4, 161–175. [Google Scholar] [CrossRef]
- Alam, F.; Mehmood, R.; Member, S.; Katib, I.; Nasser, N.; Albogami, N.N.N.; Albeshri, A. Data Fusion and IoT for Smart Ubiquitous Environments: A Survey. IEEE Access 2017, 5, 9533–9554. [Google Scholar] [CrossRef]
- De Morais, C.M.; Sadok, D.; Kelner, J. An IoT Sensor and Scenario Survey for Data Researchers. J. Braz. Comput. Soc. 2019, 25, 4. [Google Scholar] [CrossRef]
- Wang, R.; Liu, L.; Shi, W. HydraSpace: Computational Data Storage for Autonomous Vehicles. In Proceedings of the 2020 IEEE 6th International Conference on Collaboration and Internet Computing, CIC, Atlanta, GA, USA, 1–3 December 2020; pp. 70–77. [Google Scholar] [CrossRef]
- Wan, C. Storage and the IoT: What Kind of Storage Is Needed, and Where? Available online: https://blog.westerndigital.com/storage-iot-kind-storage-needed/ (accessed on 2 June 2022).
- Llanor Alleyne Best IoT Device Management Platforms & Software. 2022. Available online: https://www.itbusinessedge.com/cloud/iot-device-management-platorms/ (accessed on 2 July 2022).
- Scully, P.; Lueth, K.L. Guide to IoT Solution Development. Available online: https://iot-analytics.com/wp/wp-content/uploads/2016/09/White-paper-Guide-to-IoT-Solution-Development-September-2016-vf.pdf (accessed on 1 June 2022).
- Hodge, V.J.; Austin, J. A Survey of Outlier Detection Methodoligies. Artif. Intell. Rev. 2004, 22, 85–126. [Google Scholar] [CrossRef]
- Van Den Broeck, J.; Cunningham, S.A.; Eeckels, R.; Herbst, K. Data Cleaning: Detecting, Diagnosing, and Editing Data Abnormalities. PLoS Med. 2005, 2, 0966–0970. [Google Scholar] [CrossRef]
- Ben-gal, I. Outlier Detection. In Data Mining and Knowledge Discovery Handbook; Springer: Boston, MA, USA, 2005; pp. 131–146. [Google Scholar] [CrossRef]
- Kempf, J.; Arkko, J.; Beheshti, N.; Yedavalli, K. Thoughts on Reliability in the Internet of Things. In Proceedings of the Interconnecting Smart Objects with the Internet Workshop, Prague, Czech Republic, 25 March 2011; pp. 1–4. [Google Scholar]
- Mahmood, M.A.; Seah, W.K.G.; Welch, I. Reliability in Wireless Sensor Networks: A Survey and Challenges Ahead. Comput. Netw. 2015, 79, 166–187. [Google Scholar] [CrossRef]
- Andreas, W.; Karl, H. Data Transport Reliability in Wireless Sensor Networks; St. Petersburg State University: St. Petersburg, Russia, 2005; p. 28. [Google Scholar]
- Qiu, J.; Wu, Q.; Ding, G.; Xu, Y.; Feng, S. A Survey of Machine Learning for Big Data Processing. EURASIP J. Adv. Signal Process. 2016, 27, 327–336. [Google Scholar] [CrossRef]
- Fawzy, A.; Mokhtar, H.M.O.; Hegazy, O. Outliers Detection and Classification in Wireless Sensor Networks. Egypt. Inform. J. 2013, 14, 157–164. [Google Scholar] [CrossRef]
- Shahid, N.; Naqvi, I.H.; Qaisar, S. Bin Characteristics and Classification of Outlier Detection Techniques for Wireless Sensor Networks in Harsh Environments: A Survey. Artif. Intell. Rev. 2012, 43, 193–228. [Google Scholar] [CrossRef]
- Meratnia, N.; Havinga, P. Outlier Detection Techniques for Wireless Sensor Networks: A Survey. IEEE Commun. Surv. Tutor. 2010, 12, 159–170. [Google Scholar] [CrossRef]
- Garcia-font, V.; Garrigues, C. A Comparative Study of Anomaly Detection Techniques for Smart City Wireless Sensor Networks. Sensors 2016, 16, 868. [Google Scholar] [CrossRef]
- Alsheikh, M.A.; Lin, S.W.; Niyato, D.; Tan, H. Machine Learning in Wireless Sensor Networks: Algorithms, Strategies, and Applications. IEEE Commun. Surv. Tutor. 2014, 16, 1996–2018. [Google Scholar] [CrossRef]
- Alghanmi, N.; Alotaibi, R.; Buhari, S.M. Machine Learning Approaches for Anomaly Detection in IoT: An Overview and Future Research Directions. Wirel. Pers. Commun. 2021, 122, 2309–2324. [Google Scholar] [CrossRef]
- Cook, A.A.; Misirli, G.; Fan, Z. Anomaly Detection for IoT Time-Series Data: A Survey. IEEE Internet Things J. 2020, 7, 6481–6494. [Google Scholar] [CrossRef]
- Diro, A.; Chilamkurti, N.; Nguyen, V.D.; Heyne, W. A Comprehensive Study of Anomaly Detection Schemes in IoT Networks Using Machine Learning Algorithms. Sensors 2021, 21, 8320. [Google Scholar] [CrossRef]
- Al Samara, M.; Bennis, I.; Abouaissa, A.; Lorenz, P. A Survey of Outlier Detection Techniques in IoT: Review and Classification. J. Sens. Actuator Netw. 2022, 11, 4. [Google Scholar] [CrossRef]
- Jordaan, E.E.M.; Smits, G.G.F. Robust Outlier Detection Using SVM Regression. In Proceedings of the 2004 IEEE International Joint Conference on Neural Networks (IEEE Cat. No.04CH37541), Budapest, Hungary, 25–29 July 2004; Volume 3, pp. 2017–2022. [Google Scholar] [CrossRef]
- Yang, Z.Y.Z.; Meratnia, N.; Havinga, P. An Online Outlier Detection Technique for Wireless Sensor Networks Using Unsupervised Quarter-Sphere Support Vector Machine. In Proceedings of the 2008 International Conference on Intelligent Sensors, Sensor Networks and Information Processing, Sydney, Australia, 15–18 December 2008; pp. 151–156. [Google Scholar] [CrossRef]
- Rajasegarar, S.; Leckie, C.; Palaniswami, M.; Bezdek, J.C. Quarter Sphere Based Distributed Anomaly Detection in Wireless Sensor Networks. In Proceedings of the ICC ’07: 2007 IEEE International Conference on Communications, Glasgow, UK, 24–28 June 2007; Volume 1, pp. 3864–3869. [Google Scholar] [CrossRef]
- Münz, G.; Li, S.; Carle, G. Traffic Anomaly Detection Using K-Means Clustering. Available online: https://www.semanticscholar.org/paper/Traffic-Anomaly-Detection-Using-K-Means-Clustering-M%C3%BCnz-Li/634e2f1a20755e7ab18e8e8094f48e140a32dacd (accessed on 2 June 2022).
- Ahmed, M.; Seraj, R.; Islam, S.M.S. The K-Means Algorithm: A Comprehensive Survey and Performance Evaluation. Electronics 2020, 9, 1295. [Google Scholar] [CrossRef]
- Aubaidan, B.; Mohd, M.; Albared, M.; Author, F. Comparative Study of K-Means and K-Means++ Clustering Algorithm on Crime Domain. J. Comput. Sci. 2014, 10, 1197–1206. [Google Scholar] [CrossRef]
- Statman, A.; Rozenberg, L.; Feldman, D. K-Means+++: Outliers-Resistant Clustering. Algorithms 2020, 13, 311. [Google Scholar] [CrossRef]
- Titouna, C.; Aliouat, M.; Gueroui, M. Outlier Detection Approach Using Bayes Classifiers in Wireless Sensor Networks. Wirel. Pers. Commun. 2015, 85, 1009–1023. [Google Scholar] [CrossRef]
- Ting, J.A.; D’Souza, A.; Schaal, S. Automatic Outlier Detection: A Bayesian Approach. In Proceedings of the 2007 IEEE International Conference on Robotics and Automation, Rome, Italy, 10–14 April 2007; pp. 2489–2494. [Google Scholar] [CrossRef]
- Parto, M.; Saldana, C.; Kurfess, T. Real-Time Outlier Detection and Bayesian Classification Using Incremental Computations for Efficient and Scalable Stream Analytics for IoT for Manufacturing. Procedia Manuf. 2020, 48, 968–979. [Google Scholar] [CrossRef]
- Lam, P.; Wang, L.; Ngan, H.Y.T.; Yung, N.H.C.; Yeh, A.G.O.; Wang, L.; Ngan, H.Y.T.; Yung, N.H.C.; Yeh, A.G.O. Outlier Detection in Large-Scale Traffic Data by Naïve Bayes Method and Gaussian Mixture Model Method. Electron. Imaging 2017, 29, 73–78. [Google Scholar] [CrossRef]
- Alam, F.; Mehmood, R.; Katib, I.; Albeshri, A. Analysis of Eight Data Mining Algorithms for Smarter Internet of Things (IoT). In Proceedings of the International Workshop on Data Mining in IoT Systems (DaMIS 2016), London, UK, 19–22 September 2016; pp. 437–442. [Google Scholar] [CrossRef]
- Luo, T.; Nagarajan, S.G. Distributed Anomaly Detection Using Autoencoder Neural Networks in WSN for IoT. In Proceedings of the 2018 IEEE International Conference on Communications (ICC), Kansas City, MO, USA, 20–24 May 2018; pp. 1–6. [Google Scholar]
- Diro, A.A.; Chilamkurti, N. Distributed Attack Detection Scheme Using Deep Learning Approach for Internet of Things. Future Gener. Comput. Syst. 2018, 82, 761–768. [Google Scholar] [CrossRef]
- Zhao, K.; Pan, K.; Zhang, B. Cooperative Transmission in Mobile Wireless Sensor Networks with Multiple Carrier Frequency Offsets: A Double-Differential Approach. Math. Probl. Eng. 2014, 2014, 853821. [Google Scholar] [CrossRef]
- Ding, Z.; Mei, G.; Cuomo, S.; Li, Y.; Xu, N. Comparison of Estimating Missing Values in IoT Time Series Data Using Different Interpolation Algorithms. Int. J. Parallel Program. 2018, 48, 534–548. [Google Scholar] [CrossRef]
- Farhangfar, A.; Kurgan, L.; Dy, J. Impact of Imputation of Missing Values on Classification Error for Discrete Data. Pattern Recognit. 2008, 41, 3692–3705. [Google Scholar] [CrossRef]
- Wu, X.; Kumar, V.; Quinlan, J.R.; Ghosh, J.; Yang, Q.; Motoda, H.; Mclachlan, G.J.; Ng, A.; Liu, B.; Yu, P.S.; et al. Top 10 Algorithms in Data Mining. Knowl. Inf. Syst. 2008, 14, 1–37. [Google Scholar] [CrossRef]
- Wong, L.Z.; Chen, H.; Lin, S.; Chen, D.C. Imputing Missing Values in Sensor Networks Using Sparse Data Representations. In Proceedings of the 17th ACM International Conference on Modeling, Analysis and Simulation of Wireless and Mobile Systems—MSWiM ‘14, Montreal, QC, Canada, 21–26 September 2014; pp. 227–230. [Google Scholar] [CrossRef]
- Ni, J.; Li, L.; Qiao, F.; Wu, Q. A GS-MPSO-WKNN Method for Missing Data Imputation in Wireless Sensor Networks Monitoring Manufacturing Conditions. Trans. Inst. Meas. Control 2014, 36, 1083–1092. [Google Scholar] [CrossRef]
- Pan, R.; Yang, T.; Cao, J.; Lu, K.; Zhang, Z. Missing Data Imputation by K Nearest Neighbours Based on Grey Relational Structure and Mutual Information. Appl. Intell. 2015, 43, 614–632. [Google Scholar] [CrossRef]
- Zhang, S. Nearest Neighbor Selection for Iteratively KNN Imputation. J. Syst. Softw. 2012, 85, 2541–2552. [Google Scholar] [CrossRef]
- Weston, J. Support Vector Machine (and Statistical Learning Theory) Tutorial. Bioinformatics 2005, 21, 631–643. [Google Scholar] [CrossRef]
- Pelckmans, K.; De Brabanter, J.; Suykens, J.A.K.; De Moor, B. Handling Missing Values in Support Vector Machine Classifiers. Neural Netw. 2005, 18, 684–692. [Google Scholar] [CrossRef]
- Yang, B.; Janssens, D.; Ruan, D.; Cools, M.; Bellemans, T.; Wets, G. A Data Imputation Method with Support Vector Machines for ActivityBased Transportation Models. Adv. Intell. Soft Comput. 2012, 122, 249–257. [Google Scholar] [CrossRef]
- Yan, X.Z.; Xie, H.; Wan, T.; Luo, Q.H. A Data Predicting Method Based on LS-SVR in Wireless Sensor Network. In Proceedings of the 2010 International Conference on Broadcast Technology and Multimedia Communication, Hong Kong, China, 28–30 December 2010; p. 1. [Google Scholar]
- Zou, C. Node Data Prediction Based on SVR in Wireless Sensor Network. J. Comput. Appl. 2010, 30, 127–129. [Google Scholar] [CrossRef]
- Breiman, L.E.O. Random Forests. Mach. Learn. 2001, 45, 5–32. [Google Scholar] [CrossRef]
- Fortran Breiman and Cutler’s Random Forests for Classification and Regression. 2015. Available online: http://stat-www.berkeley.edu/users/breiman/RandomForests (accessed on 2 June 2022).
- Ishioka, T. Imputation of Missing Values for Semi-Supervised Data Using the Proximity in Random Forests. In Proceedings of the 14th International Conference on Information Integration and Web-Based Applications & Services, Munich, Germany, 2–4 December 2012; pp. 319–322. [Google Scholar] [CrossRef]
- Grzymala-busse, J.W.; Hu, M.; York, N. A Comparison of Several Approaches to Missing Attribute Values in Data Mining. In International Conference on Rough Sets and Current Trends in Computing; Springer: Berlin/Heidelberg, Germany, 2000; pp. 378–385. [Google Scholar]
- Batista, G.E.A.P.A.; Monard, M.C. A Study of K-Nearest Neighbour as an Imputation Method. In Proceedings of the Soft Computing Systems—Design, Management and Applications, HIS Conference, Santiago, Chile, 1–4 December 2002. [Google Scholar]
- Song, Q.; Shepperd, M.; Chen, X.; Liu, J. Can k -NN Imputation Improve the Performance of C4.5 with Small Software Project Data Sets? A Comparative Evaluation. J. Syst. Softw. 2008, 81, 2361–2370. [Google Scholar] [CrossRef]
- Mehala, B.; Vivekanandan, K.; Thangaiah, P.R.J. An Analysis on K-Means Algorithm as an Imputation Method to Deal with Missing Values. Asian J. Inf. Technol. 2008, 7, 434–441. [Google Scholar]
- Schmitt, P.; Mandel, J.; Guedj, M. A Comparison of Six Methods for Missing Data Imputation. Biom. Biostat. 2015, 6, 1. [Google Scholar] [CrossRef]
- Li, D.; Deogun, J.; Spaulding, W.; Shuart, B. Towards Missing Data Imputation: A Study of Fuzzy K-Means Clustering Method. Rough Sets Curr. Trends Comput. 2004, 3066, 573–579. [Google Scholar] [CrossRef]
- Hruschka, E.R.; Hruschka, E.R., Jr.; Ebecken, N.F.F. Towards Efficient Imputation by Nearest-Neighbors: A Clustering-Based Approach. In Australasian Joint Conference on Artificial Intelligence; Springer: Berlin/Heidelberg, Germany, 2004; pp. 513–525. [Google Scholar]
- Patil, B.M.; Joshi, R.C.; Toshniwal, D. Missing Value Imputation Based on K-Mean Clustering with Weighted Distance. Commun. Comput. Inf. Sci. 2010, 94, 600–609. [Google Scholar] [CrossRef]
- Chi, J.T.; Chi, E.C.; Baraniuk, R.G. A Method for K-Means Clustering of Missing Data; Rice University: Houston, TX, USA, 2016. [Google Scholar]
- Aydilek, I.B.; Arslan, A. A Hybrid Method for Imputation of Missing Values Using Optimized Fuzzy C-Means with Support Vector Regression and a Genetic Algorithm. Inf. Sci. 2013, 233, 25–35. [Google Scholar] [CrossRef]
- Kian, L.; Chu, L.; Way, L. Autonomous and Deterministic Supervised Fuzzy Clustering with Data Imputation Capabilities. Appl. Soft Comput. 2011, 11, 1117–1125. [Google Scholar] [CrossRef]
- Bu, F.; Chen, Z.; Zhang, Q.; Yang, L.T. Incomplete High-Dimensional Data Imputation Algorithm Using Feature Selection and Clustering Analysis on Cloud. J. Supercomput. 2012, 72, 2977–2990. [Google Scholar] [CrossRef]
- Tian, J.; Yu, B.; Yu, D.; Ma, S. Missing Data Analyses: A Hybrid Multiple Imputation Algorithm Using Gray System Theory and Entropy Based on Clustering. Appl. Intell. 2014, 40, 376–388. [Google Scholar] [CrossRef]
- Rey-del-castillo, P. Fuzzy Min-Max Neural Networks for Categorical Data: Application to Missing Data Imputation. Neural Comput. Appl. 2012, 21, 1349–1362. [Google Scholar] [CrossRef]
- Gautam, C.; Ravi, V. Neurocomputing Data Imputation via Evolutionary Computation, Clustering and a Neural Network. Neurocomputing 2015, 156, 134–142. [Google Scholar] [CrossRef]
- Ennett, C.M.; Frize, M.; Member, S.; Walker, C.R. Imputation of Missing Values by Integrating Neural Networks and Case-Based Reasoning. In Proceedings of the 2008 30th Annual International Conference of the IEEE Engineering in Medicine and Biology Society, Vancouver, BC, Canada, 20–25 August 2008; pp. 4337–4341. [Google Scholar]
- Ravi, V.; Krishna, M. A New Online Data Imputation Method Based on General Regression Auto Associative Neural Network. Neurocomputing 2014, 138, 106–113. [Google Scholar] [CrossRef]
- Ultsch, A.; Rolf, S. Imputation of Missing Values by Neural Networks for Data Mining Applications. Knowl. Bases Syst. 2000, 182, 3–6. [Google Scholar]
- Saar-Tsechansky, M.; Provost, F. Handling Missing Values When Applying Classification Models. J. Mach. Learn. Res. 2007, 8, 1625–1657. [Google Scholar]
- Guyon, I.; Elisseeff, A. An Introduction to Variable and Feature Selection. J. Mach. Learn. Res. 2003, 3, 1157–1182. [Google Scholar]
- Bratu, C.V.; Muresan, T.; Potolea, R. Improving Classification Accuracy through Feature Selection. In Proceedings of the 4th International Conference on Intelligent Computer Communication and Processing, Cluj-Napoca, Romania, 28–30 August 2008; pp. 25–32. [Google Scholar] [CrossRef]
- Chu, C.; Hsu, A.; Chou, K.; Bandettini, P.; Lin, C. Does Feature Selection Improve Classification Accuracy? Impact of Sample Size and Feature Selection on Classification Using Anatomical Magnetic Resonance Images. Neuroimage 2012, 60, 59–70. [Google Scholar] [CrossRef]
- Lin, K.; Lin, C.; Huang, C.; Chang, H.; Yang, C.; Lin, C.; Tang, C.Y.; Hsu, D.F.; Member, S. Feature Selection and Combination Criteria for Improving Accuracy in Protein Structure Prediction. IEEE Trans. Nanobiosci. 2007, 6, 186–196. [Google Scholar] [CrossRef]
- Janecek, A.G.K.; Gansterer, W.N.; Demel, M.A.; Ecker, G.F. On the Relationship between Feature Selection and Classification Accuracy. In Proceedings of the JMLR Workshop and Conference Proceedings, Antwerp, Belgium, 15 September 2008; pp. 90–105. [Google Scholar]
- Fonollosa, J.; Rodríguez-Luján, I.; Trincavelli, M.; Vergara, A.; Huerta, R. Chemical Discrimination in Turbulent Gas Mixtures with MOX Sensors Validated by Gas Chromatography-Mass Spectrometry. Sensors 2014, 14, 19336–19353. [Google Scholar] [CrossRef]
- Ziyatdinov, A.; Fonollosa, J.; Fernández, L.; Gutierrez-Gálvez, A.; Marco, S.; Perera, A. Bioinspired Early Detection through Gas Flow Modulation in Chemo-Sensory Systems. Sens. Actuators B Chem. 2015, 206, 538–547. [Google Scholar] [CrossRef]
- Vergara, A.; Vembu, S.; Ayhan, T.; Ryan, M.A.; Homer, M.L.; Huerta, R. Chemical Gas Sensor Drift Compensation Using Classifier Ensembles. Sens. Actuators B Chem. 2012, 166–167, 320–329. [Google Scholar] [CrossRef]
- Molina, L.C.; Belanche, L.; Nebot, À.; Girona, J. Feature Selection Algorithms: A Survey and Experimental Evaluation. In Proceedings of the 2002 IEEE International Conference on Data Mining, Maebashi, Japan, 9–12 December 2002. [Google Scholar]
- Chizi, B.; Rokach, L.; Maimon, O. A Survey of Feature Selection Techniques. In Encyclopedia of Data Warehousing and Mining, 2nd ed.; Idea Group Publishing: London, UK, 2009; pp. 1888–1895. [Google Scholar]
- Amr, T.; Iglesia, B.D. La Survey on Feature Selection. Available online: https://www.arxiv-vanity.com/papers/1510.02892/ (accessed on 2 June 2022).
- Xiang, J.; Han, X.; Duan, F.; Qiang, Y.; Xiong, X.; Lan, Y.; Chai, H. A Novel Hybrid System for Feature Selection Based on an Improved Gravitational Search Algorithm and K-NN Method. Appl. Soft Comput. J. 2015, 31, 293–307. [Google Scholar] [CrossRef]
- Li, S.; Harner, E.J.; Adjeroh, D.A. Random KNN Feature Selection—A Fast and Stable Alternative to Random Forests. BMC Bioinform. 2011, 12, 450. [Google Scholar] [CrossRef] [PubMed]
- Li, S. Random KNN Classification and Regression. 2015. Available online: https://www.coursehero.com/file/140546671/kNN-classification-and-regressionpdf/ (accessed on 2 June 2022).
- Su, M.; Chang, K.; Wei, H.; Lin, C. Feature Weighting and Selection for a Real-Time Network Intrusion Detection System Based on GA with KNN. Lect. Notes Comput. Sci. 2008, 5075, 195–204. [Google Scholar] [CrossRef]
- Chang, Y.; Lin, C. Feature Ranking Using Linear SVM. JMLR Workshop Conf. Proc. 2008, 3, 53–64. [Google Scholar]
- Jan, S.U.; Koo, I. A Novel Feature Selection Scheme and a Diversified-Input SVM-Based Classifier for Sensor Fault Classification. J. Sens. 2018, 2018, 21. [Google Scholar] [CrossRef]
- Howcroft, J.; Kofman, J.; Lemaire, E.D. Feature Selection for Elderly Faller Classification Based on Wearable Sensors. J. Neuro Eng. Rehabil. 2017, 14, 47. [Google Scholar] [CrossRef]
- Pandya, R. C5.0 Algorithm to Improved Decision Tree with Feature Selection and Reduced Error Pruning. Int. J. Comput. Appl. 2015, 117, 18–21. [Google Scholar]
- Thomas, S.; Bourobou, M.; Yoo, Y. User Activity Recognition in Smart Homes Using Pattern Clustering Applied to Temporal ANN Algorithm. Sensors 2015, 15, 11953–11971. [Google Scholar] [CrossRef]
- Wang, R. AdaBoost for Feature Selection, Classification and Its Relation with SVM, A Review. Phys. Procedia 2012, 25, 800–807. [Google Scholar] [CrossRef]
- Fürst, L.; Fidler, S.; Leonardis, A. Selecting Features for Object Detection Using an AdaBoost-Compatible Evaluation Function. Pattern Recognit. Lett. 2008, 29, 1603–1612. [Google Scholar] [CrossRef]
- Shen, L.; Bai, L. AdaBoost Gabor Feature Selection for Classification. Available online: https://www.semanticscholar.org/paper/AdaBoost-Gabor-Feature-Selection-for-Classification-Shen-Bai/9a356779ecc242c161cc77caf9052bd91aff1007 (accessed on 2 June 2022).
- Ma, J.; Cheng, J.C.P. Identifying the Influential Features on the Regional Energy Use Intensity of Residential Buildings Based on Random Forests. Appl. Energy 2016, 183, 193–201. [Google Scholar] [CrossRef]
- Leevy, J.L.; Hancock, J.; Khoshgoftaar, T.M.; Peterson, J.M. IoT Information Theft Prediction Using Ensemble Feature Selection. J. Big Data 2022, 9, 6. [Google Scholar] [CrossRef]
- Hussein, A.Y.; Falcarin, P.; Sadiq, A.T. IoT Intrusion Detection Using Modified Random Forest Based on Double Feature Selection Methods. Commun. Comput. Inf. Sci. 2022, 1548, 61–78. [Google Scholar] [CrossRef]
- Su, J.; He, S.; Wu, Y. Features Selection and Prediction for IoT Attacks. High-Confid. Comput. 2022, 2, 100047. [Google Scholar] [CrossRef]
- Taha, A.M.; Mustapha, A.; Chen, S. Naive Bayes-Guided Bat Algorithm for Feature Selection. Sci. World J. 2013, 2013, 325973. [Google Scholar] [CrossRef]
- Feng, G.; Guo, J.; Jing, B.; Sun, T. Feature Subset Selection Using Naive Bayes for Text Classification. Pattern Recognit. Lett. 2015, 65, 109–115. [Google Scholar] [CrossRef]
- Ng, A.Y. Feature Selection, L 1 vs. L 2 Regularization, and Rotational Invariance. In Proeedings of the ICML –201904: Proceedings of the twenty-first international conference on Machine learning, Banff, Alta, Canada, 4–8 July 2004. [Google Scholar] [CrossRef]
- Vail, D.L.; Veloso, M.M. Feature Selection for Activity Recognition in Multi-Robot Domains. In Proceedings of the Association for the Advancement of Artificial Intelligence Conference, Chicago, IL, USA, 13–17 July 2008. [Google Scholar]
- Ng, A.Y. Regularization and Feature Selection in Least-Squares Temporal Difference Learning. In Proceedings of the ICML ‘09: Proceedings of the 26th Annual International Conference on Machine Learning, Montreal, QC, Canada, 14–18 June 2009; p. 94305. [Google Scholar]
- Robnik-Sikonja, M.; Kononenko, I. Theoretical and Empirical Analysis of ReliefF and RReliefF. Mach. Learn. 2003, 53, 23–69. [Google Scholar] [CrossRef]
- Zhang, M.; Sawchuk, A.A. A Feature Selection-Based Framework for Human Activity Recognition Using Wearable Multimodal Sensors. In Proceedings of the ACM Conference on Ubiquitous Computing, Beijing, China, 17–21 September 2011. [Google Scholar]
- Gupta, P.; Dallas, T. Feature Selection and Activity Recognition System Using a Single Tri-Axial Accelerometer. IEEE Trans. Biomed. Eng. Feature 2014, 61, 9294. [Google Scholar] [CrossRef]
- Capela, N.A.; Lemaire, E.D.; Baddour, N. Feature Selection for Wearable Smartphone-Based Human Activity Recognition with Able Bodied, Elderly, and Stroke Patients. PLoS ONE 2015, 10, e0124414. [Google Scholar] [CrossRef]
- Zhao, L.; Dong, X. An Industrial Internet of Things Feature Selection Method Based on Potential Entropy Evaluation Criteria. IEEE Access 2018, 6, 4608–4617. [Google Scholar] [CrossRef]
- Whitmore, A.; Agarwal, A.; Da Xu, L. The Internet of Things? A Survey of Topics and Trends. Inf. Syst. Front. 2015, 17, 261–274. [Google Scholar] [CrossRef]
- Xu, L.D.; Member, S.; He, W.; Li, S. Internet of Things in Industries: A Survey. IEEE Trans. Ind. Inform. 2014, 10, 2233–2243. [Google Scholar] [CrossRef]
- United Nations. World’s Population Increasingly Urban with More than Half Living in Urban Areas. Available online: https://www.un.org/development/desa/en/news/population/world-urbanization-prospects.html (accessed on 12 June 2022).
- Kamel Boulos, M.N.; Al-Shorbaji, N.M. On the Internet of Things, Smart Cities and the WHO Healthy Cities. Int. J. Health Geogr. 2014, 13, 10. [Google Scholar] [CrossRef]
- High, P. The Top Five Smart Cities in The World. Available online: https://www.forbes.com/sites/peterhigh/2015/03/09/the-top-five-smart-cities-in-the-world/?sh=461b299667ee (accessed on 25 June 2022).
- PTI. Smart Cities to Boost Internet of Things Market in 2016: Gartner. Available online: http://timesofindia.indiatimes.com/tech/tech-news/Smart-cities-to-boost-Internet-of-Things-market-in-2016-Gartner/articleshow/50088586.cms (accessed on 29 June 2022).
- Ministry of Urban Development. Cities Profile of 20 Smart Cities. Smart Sities Mission. 2016. Available online: https://www.india.gov.in/smart-cities-mission-portal-ministry-urban-development (accessed on 2 June 2022).
- Zanella, A.; Bui, N.; Castellani, A.; Vangelista, L.; Zorzi, M. Internet of Things for Smart Cities. Internet Things J. 2014, 1, 22–32. [Google Scholar] [CrossRef]
- Monnier, O. A Smart Grid with the Internet of Things. 2014. Available online: https://www.techonline.com/tech-papers/a-smarter-grid-with-the-internet-of-things/ (accessed on 2 June 2022).
- Garg, V.K.; Sharma, S. Role of IoT and Machine Learning in Smart Grid. Lect. Notes Electr. Eng. 2022, 841, 701–715. [Google Scholar] [CrossRef]
- Bryant, R.; Hensel, C. From Data to Knowledge to Action: Enabling the Smart Grid. arXiv 2020, arXiv:2008.00055. [Google Scholar]
- Zhang, D.; Han, X.; Deng, C. Review on the Research and Practice of Deep Learning and Reinforcement Learning in Smart Grids. CSEE J. Power Energy Syst. 2018, 4, 362–370. [Google Scholar] [CrossRef]
- Wu, L.L.; Kaiser, G.E.; Rudin, C.; Waltz, D.L.; Anderson, R.N.; Boulanger, A.G.; Pooleery, M. Evaluating Machine Learning for Improving Power Grid Reliability. Comput. Sci. 2011, 2011, 934. [Google Scholar]
- Wang, M.; Perera, C.; Jayaraman, P.P.; Zhang, M.; Strazdins, P.; Ranjan, R. City Data Fusion: Sensor Data Fusion in the Internet of Things. Int. J. Distrib. Syst. Technol. 2015, 7, 15–36. [Google Scholar] [CrossRef]
- Rudin, C.; Ertekin, S.; Passonneau, R.; Radeva, A.; Tomar, A.; Xie, B.; Lewis, S.; Riddle, M.; Pangsrivinij, D.; McCormick, T. Analytics for Power Grid Distribution Reliability in New York City. Interfaces 2014, 44, 364–383. [Google Scholar] [CrossRef]
- Aman, S.; Yin, W.; Simmhan, Y.; Prasanna, V. Machine Learning for Demand Forecasting in Smart Grid. Available online: http://ceng.usc.edu/~simmhan/pubs/aman-socalsgs-2011.pdf (accessed on 2 June 2022).
- Mirowski, P.; Chen, S.; Kam Ho, T.; Yu, C.-N. Demand Forecasting in Smart Grids. Bell Labs Tech. J. 2014, 18, 3–17. [Google Scholar] [CrossRef]
- Shawkat Ali, A.B.M.; Azad, S. Demand Forecasting in Smart Grid. In Smart Grids; Springer: London, UK, 2013; pp. 135–150. [Google Scholar] [CrossRef]
- Khodayar, M.E.; Wu, H. Demand Forecasting in the Smart Grid Paradigm: Features and Challenges. Electr. J. 2015, 28, 51–62. [Google Scholar] [CrossRef]
- Mateo, F.; Carrasco, J.J. Machine Learning Techniques for Short-Term Electric Power Demand Prediction. Available online: https://www.semanticscholar.org/paper/Machine-Learning-Techniques-for-Short-Term-Electric-Mateo-Fern%C3%A1ndez/135715962dae1875bb4d67f2d6aed795a8178bdc (accessed on 2 June 2022).
- Kotillova, A.; Koprinska, I.; Rana, M. Statistical and Machine Learning Methods for Electricity Demand Prediction. Lect. Notes Comput. Sci. 2012, 2012, 535–542. [Google Scholar] [CrossRef]
- Khotanzad, A.; Elragal, H.; Lu, T.L. Combination of Artificial Neural-Network Forecasters for Prediction of Natural Gas Consumption. IEEE Trans. Neural Netw. 2000, 11, 464–473. [Google Scholar] [CrossRef]
- Jin-ming, W.; Xin-heng, L. The Forecast of Energy Demand on Artificial Neural Network. Network 2009, 3, 31–35. [Google Scholar] [CrossRef]
- Li, Z.-S.; Zhang, G.-Q.; Li, D.-M.; Liu, X.-H.; Mei, S.; Wu, J. Neural Network Prediction of Energy Demand and Supply in China. Proc. Inst. Civ. Eng.-Energy 2007, 60, 4. [Google Scholar] [CrossRef]
- Chen, B.; Zhao, L.; Lu, J.H. Wind Power Forecast Using RBF Network and Culture Algorithm. In Proceedings of the 1st International Conference on Sustainable Power Generation and Supply, SUPERGEN ’09, Nanjing, China, 6–7 April 2009. [Google Scholar] [CrossRef]
- Chang, W. Short-Term Load Forecasting Using Radial Basis Function Neural Network. J. Comput. Commun. 2015, 3, 40–45. [Google Scholar] [CrossRef]
- Sim, M.; Musilek, P.; Pelik, E. Recurrent Neural Network Based Gating for Natural Gas Load Prediction System. In Proceedings of the 2006 IEEE International Joint Conference on Neural Network Proceedings, Vancouver, BC, Canada, 16–21 July 2006; pp. 3736–3741. [Google Scholar]
- Lee, K.Y.; Cha, Y.T.; Ku, C.C. A Study on Neural Networks for Short-Term Load Forecasting. In Proceedings of the First International Forum on Applications of Neural Networks to Power Systems, Seattle, WA, USA, 23–26 July 1991. [Google Scholar]
- Neupane, B.; Perera, K.; Aung, Z.; Woon, W. Artificial Neural Network-Based Electricity Price Forecasting for Smart Grid Deployment. In Proceedings of the 2012 International Conference on Computer Systems and Industrial Informatics, Sharjah, United Arab Emirates, 18–20 December 2012; pp. 1–6. [Google Scholar] [CrossRef]
- Kumaran, J.; Ravi, G. Long-Term Sector-Wise Electrical Energy Forecasting Using Artificial Neural Network and Biogeography-Based Optimization. Electr. Power Compon. Syst. 2015, 43, 1225–1235. [Google Scholar] [CrossRef]
- Pellegrini, M. Short-Term Load Demand Forecasting in Smart Grids Using Support Vector Regression. In Proceedings of the 2015 IEEE 1st International Forum on Research and Technologies for Society and Industry Leveraging a Better Tomorrow (RTSI), Turin, Italy, 16–18 September 2015; pp. 264–268. [Google Scholar]
- Aung, Z.; Toukhy, M.; Williams, J. Towards Accurate Electricity Load Forecasting in Smart Grids. Proc. DBKDA 2012, 2012, 51–57. [Google Scholar]
- List, C.; Authors, O.F.; Masri, D.; Zeineldin, H.; Woon, W.L. Electricity Price and Demand Forecasting under Smart Grid Environment. In Proceedings of the 2015 IEEE 15th International Conference on Environment and Electrical Engineering (EEEIC), Rome, Italy, 10–13 June 2015; pp. 2–4. [Google Scholar]
- Sun, Y.; Braga-Neto, U.; Dougherty, E. Impact of Missing Value Imputation on Classification for DNA Microarray Gene Expression Data—A Model-Based Study. EURASIP J. Bioinform. Syst. Biol. 2009, 2009, 504069. [Google Scholar] [CrossRef]
- Mocanu, E.; Nguyen, P.H.; Gibescu, M.; Larsen, E.M.; Pinson, P. Demand Forecasting at Low Aggregation Levels Using Factored Conditional Restricted Boltzmann Machine. In Proceedings of the 2016 Power Systems Computation Conference (PSCC), Genoa, Italy, 20–24 June 2016. [Google Scholar]
- Hossain, E.; Khan, I.; Un-Noor, F.; Sikander, S.S.; Sunny, M.S.H. Application of Big Data and Machine Learning in Smart Grid, and Associated Security Concerns: A Review. IEEE Access 2019, 7, 13960–13988. [Google Scholar] [CrossRef]
- Bazzan, A.L.C.; Klügl, F. Introduction to Intelligent Systems in Traffic And Transportation. In Synthesis Lectures on Artificial Intelligence and Machine Learning (SLAIML); Springer: Berlin/Heidelberg, Germany, 2013; Volume 7, pp. 1–137. [Google Scholar] [CrossRef]
- Zantalis, F.; Koulouras, G.; Karabetsos, S.; Kandris, D. A Review of Machine Learning and IoT in Smart Transportation. Future Internet 2019, 11, 94. [Google Scholar] [CrossRef]
- Gónzalez, L.C.; Martínez, F.; Carlos, M.R. Identifying Roadway Surface Disruptions Based on Accelerometer Patterns. IEEE Lat. Am. Trans. 2014, 12, 455–461. [Google Scholar]
- Brisimi, T.S.; Cassandras, C.G.; Osgood, C.; Paschalidis, I.C.; Zhang, Y. Sensing and Classifying Roadway Obstacles in Smart Cities: The Street Bump System. IEEE Access Smart Cities 2016, 3536, 1301–1312. [Google Scholar] [CrossRef]
- Darbari, M.; Yagyasen, D.; Tiwari, A. Intelligent Traffic Monitoring Using Internet of Things (IoT) with Semantic Web. Adv. Intell. Syst. Comput. 2015, 1, 455–462. [Google Scholar] [CrossRef]
- Liang, M.; Huang, X.; Chen, C.; Chen, X.; Tokuta, A. Counting and Classification of Highway Vehicles by Regression Analysis. IEEE Trans. Intell. Transp. Syst. 2015, 16, 2878–2888. [Google Scholar] [CrossRef]
- Araghi, S.; Khosravi, A.; Johnstone, M.; Creighton, D. Intelligent Traffic Light Control of Isolated Intersections Using Machine Learning Methods. In Proceedings of the 2013 IEEE International Conference on Systems, Man, and Cybernetics, Manchester, UK, 13–16 October 2013; pp. 3627–3632. [Google Scholar] [CrossRef]
- Mannion, P.; Duggan, J.; Howley, E. Parallel Reinforcement Learning for Traffic Signal Control. Procedia Comput. Sci. 2015, 52, 956–961. [Google Scholar] [CrossRef]
- Alam, F.; Mehmood, R.; Katib, I. D2TFRS: An Object Recognition Method for Autonomous Vehicles Based on RGB and Spatial Values of Pixels. In Proceedings of the Lecture Notes of the Institute for Computer Sciences, Social-Informatics and Telecommunications Engineering, LNICST; Springer, Cham, Switzerland, 2018; Volume 224, pp. 155–168. [Google Scholar]
- Hsu, J. Deep Learning Makes Driverless Cars Better at Spotting Pedestrians. Available online: http://spectrum.ieee.org/cars-that-think/transportation/advanced-cars/deep-learning-makes-driverless-cars-better-at-spotting-pedestrians (accessed on 10 June 2022).
- Korosec, K. Elon Musk Says Tesla Vehicles Will Drive Themselves in Two Years. Available online: http://fortune.com/2015/12/21/elon-musk-interview/ (accessed on 10 June 2022).
- Cook, D.J.; Youngblood, M.; Das, S.K. A Multi-Agent Approach to Controlling a Smart Environment. Lect. Notes Comput. Sci. 2006, 4008, 165–182. [Google Scholar] [CrossRef]
- Kabir, M.H.; Hoque, M.R.; Seo, H.; Yang, S. Machine Learning Based Adaptive Context-Aware System for Smart Home Environment. Int. J. Smart Home 2015, 9, 55–62. [Google Scholar] [CrossRef]
- Dixit, A.; Naik, A. Use of Prediction Algorithms in Smart Homes. Int. J. Mach. Learn. Comput. 2014, 4, 157–162. [Google Scholar] [CrossRef][Green Version]
- Choi, S.; Kim, E.; Oh, S. Human Behavior Prediction for Smart Homes Using Deep Learning. In Proceedings of the 2013 RO-MAN, Gyeongju, Korea, 26–29 August 2013; IEEE: Manhattan, NY, USA, 2013; p. 1. [Google Scholar]
- Fahad, L.G.; Ali, A.; Rajarajan, M. Learning Models for Activity Recognition in Smart Homes. Lect. Notes Electr. Eng. 2015, 339, 819–826. [Google Scholar] [CrossRef]
- Taiwo, O.; Ezugwu, A.E.; Oyelade, O.N.; Almutairi, M.S. Enhanced Intelligent Smart Home Control and Security System Based on Deep Learning Model. Wirel. Commun. Mob. Comput. 2022, 2022, 961. [Google Scholar] [CrossRef]
- Islam, S.M.R.; Kwak, D.; Kabir, H.; Hossain, M.; Kwak, K.-S. The Internet of Things for Health Care: A Comprehensive Survey. IEEE Access 2015, 3, 678–708. [Google Scholar] [CrossRef]
- Bellandi, V.; Ceravolo, P.; Damiani, E.; Siccardi, S. Smart Healthcare, IoT and Machine Learning: A Complete Survey. Intell. Syst. Ref. Libr. 2022, 212, 307–330. [Google Scholar] [CrossRef]
- Chatzinikolaou, T.; Vogiatzi, E.; Kousis, A.; Tjortjis, C. Smart Healthcare Support Using Data Mining and Machine Learning. In EAI/Springer Innovations in Communication and Computing; Springer: Cham, Switzerland, 2022; pp. 27–48. [Google Scholar]
- Dawadi, P.N.; Cook, D.J.; Schmitter-edgecombe, M.; Parsey, C. Automated Assessment of Cognitive Health Using Smart Home Technologies. Technol. Health Care 2013, 21, 323–343. [Google Scholar] [CrossRef]
- Dawadi, P.N.; Cook, D.J.; Schmitter-edgecombe, M. Automated Cognitive Health Assessment Using Smart Home Monitoring of Complex Tasks. IEEE Trans. Syst. Man Cybern. Syst. 2013, 43, 1302–1313. [Google Scholar] [CrossRef]
- Vyas, N.; Farringdon, J.; Andre, D.; Stivoric, J.I. Machine Learning and Sensor Fusion for Estimating Continuous Energy Expenditure. In Proceedings of the Twenty-Third Innovative Applications of Artificial Intelligence Conference, San Francisco, CA, USA, 9–11 August 2011; pp. 1613–1620. [Google Scholar]
- Boursalie, O.; Samavi, R.; Doyle, T.E. M4CVD: Mobile Machine Learning Model for Monitoring Cardiovascular Disease. Procedia Comput. Sci. 2015, 63, 384–391. [Google Scholar] [CrossRef]
- Smith, S. 5 Ways the IBM Watson Is Changing Health Care, from Diagnosing Disease to Treating It. Available online: http://www.medicaldaily.com/5-ways-ibm-watson-changing-health-care-diagnosing-disease-treating-it-364394 (accessed on 12 June 2022).
- Ellis, S.; Morris, H.D.; Santagate, J. IoT-Enabled Analytic Applications Revolutionize Supply Chain Planning and Execution. Iran. J. Inform. Process. Manag. 2015, 37, 1. [Google Scholar]
- Braun, G. The Internet of Things and the Modern Supply Chain. 2015. Available online: www.c3solutions.com (accessed on 2 June 2022).
- Deliottee. The Warehouse of Tomorrow, Today Ubiquitous Computing, Internet of Things, Machine Learning. 2015. Available online: https://www2.deloitte.com/be/en/pages/technology/enterprise-technology-and-performance/solutions/emea-center-of-excellence-for-sap-extended-warehouse-management.html (accessed on 2 June 2022).
- Carbonneau, R.; Laframboise, K. Forecasting Supply Chain Demand Using Machine Learning Algorithms. In Distributed Artificial Intelligence, Agent Technology, and Collaborative Applications; Oakland University: Oakland, CA, USA, 2009; pp. 2009–2011. [Google Scholar] [CrossRef]
- Zhengxia, W.; Laisheng, X. Modern Logistics Monitoring Platform Based on the Internet of Things. In Proceedings of the 2010 International Conference on Intelligent Computation Technology and Automation, Changsha, China, 11–12 May 2010. [Google Scholar]
- Gai, K.; Qiu, M.; Zhao, H.; Dai, W. Anti-Counterfeit Scheme Using Monte Carlo Simulation for E-Commerce in Cloud Systems. In Proceedings of the 2015 IEEE 2nd International Conference on Cyber Security and Cloud Computing, New York, NY, USA, 3–5 November 2015; pp. 74–79. [Google Scholar]
- Machida, T.; Yamamoto, D.; Iwamoto, M.; Sakiyama, K. Implementation of Double Arbiter PUF and Its Performance Evaluation. In Proceedings of the 20th Asia and South Pacific Design Automation Conference (ASP-DAC), Chiba, Japan, 19–22 January 2015; pp. 6–7. [Google Scholar]
- Liu, B.; Zhang, L. A Survey of Opinion Mining and Sentiment Analysis. In Mining Text Data; Aggarwal, C., Zhai, C., Eds.; Springer: New York, NY, USA, 2013; pp. 415–463. [Google Scholar]
- Bouchlaghem, R. A Machine Learning Approach for Classifying Sentiments in Arabic Tweets. In Proceedings of the 6th International Conference on Web Intelligence, Mining and Semantics, Nîmes, France, 13–15 June 2016. [Google Scholar]
- Duwairi, R.M. Arabic Sentiment Analysis Using Supervised Classification. In Proceedings of the 2014 International Conference on Future Internet of Things and Cloud (FiCloud), Barcelona, Spain, 27–29 August 2014. [Google Scholar]
- Science, C.; Trivandrum, E.; Science, C.; Trivandrum, E. Sentiment Analysis in Twitter Using Machine Learning Techniques. In Proceedings of the 2013 Fourth International Conference on Computing, Communications and Networking Technologies (ICCCNT), Tiruchengode, India, 4–6 July 2013. [Google Scholar]
- Fisher, A.; Prucha, N. Detecting Jihadist Messages on Twitter. In Proceedings of the 2015 European Intelligence and Security Informatics Conference, Manchester, UK, 7–9 September 2015. [Google Scholar]
- Akbar, A.; Carrez, F.; Moessner, K.; Zoha, A. Predicting Complex Events for Pro-Active IoT Applications. In Proceedings of the 2015 IEEE 2nd World Forum on Internet of Things (WF-IoT), Milan, Italy, 14 –16 December 2015. [Google Scholar]
- Roberts, F. IoT Project Brings Clean, Safe Water to Thousands in Africa. Available online: https://internetofbusiness.com/iot-project-clean-safe-water-africa/ (accessed on 20 June 2022).
- Shafi, U.; Mumtaz, R.; Anwar, H.; Qamar, A.M.; Khurshid, H. Surface Water Pollution Detection Using Internet of Things. In Proceedings of the 15th International Conference on Smart Cities: Improving Quality of Life Using ICT & IoT (HONET-ICT), Islamabad, Pakistan, 8–10 October 2018. [Google Scholar]
- Mishra, A. Air Pollution Monitoring System Based on IoT: Forecasting and Predictive Modeling Using Machine Learning. In Proceedings of the Conference: International Conference on Applied Electromagnetics, Signal Processing & Communication (AESPC), Bhubaneswar, India, 22–24 October 2018. [Google Scholar]
- Elvitigala, C.S.; Sudantha, B. Machine Learning Capable, IoT Air Pollution Monitoring System with Upgradable Sensor Array. In Proceedings of the ISIS Conference, Daegu, Korea, 11–14 October 2017. [Google Scholar]
- Ray, P.P.; Mukherjee, M.; Shu, L. Internet of Things for Disaster Management: State-of-the-Art and Prospects. IEEE Access 2017, 5, 18818–18835. [Google Scholar] [CrossRef]
- Nesa, N.; Ghosh, T.; Banerjee, I. Outlier Detection in Sensed Data Using Statistical Learning Models for IoT. In Proceedings of the 2018 IEEE Wireless Communications and Networking Conference (WCNC), Barcelona, Spain, 15–18 April 2018; pp. 1–6. [Google Scholar]
- Salehi, M.; Rashidi, L. A Survey on Anomaly Detection in Evolving Data: With Application to Forest Fire Risk Prediction. SIGKDD Explor. Newsl. 2018, 20, 13–23. [Google Scholar] [CrossRef]
- Pughazhendhi, G.; Raja, A.; Ramalingam, P.; Elumalai, D.K. Earthosys—Tsunami Prediction and Warning System Using Machine Learning and IoT. In Proceedings of the International Conference on Computational Intelligence and Data Engineering; Chaki, N., Devarakonda, N., Sarkar, A., Debnath, N.C., Eds.; Springer: Singapore, 2019; pp. 103–113. [Google Scholar]
- Knight, W. How Japan’s Earthquake and Tsunami Warning Systems Work. Available online: https://www.technologyreview.com/2011/03/11/260021/how-japans-earthquake-and-tsunami-warning-systems-work/ (accessed on 2 June 2022).
- Andaloussi, Y.; El Ouadghiri, M.D.; Maurel, Y.; Bonnin, J.M.; Chaoui, H. Access Control in IoT Environments: Feasible Scenarios. In Proceedings of the 8th International Symposium on Frontiers in Ambient and Mobile Systems (FAMS-2018), Brisbane, QSL, Australia, 8 May 2018; pp. 1031–1036. [Google Scholar]
- Xiao, L.; Wan, X.; Lu, X.; Zhang, Y.; Wu, D. IoT Security Techniques Based on Machine Learning: How Do IoT Devices Use AI to Enhance Security? IEEE Signal Process. Mag. 2018, 35, 41–49. [Google Scholar] [CrossRef]
- Hussain, F.; Hussain, R.; Hassan, S.A.; Hossain, E. Machine Learning in IoT Security: Current Solutions and Future Challenges. IEEE Commun. Surv. Tutor. 2020, 22, 1686–1721. [Google Scholar] [CrossRef]
- Hasan, M.; Islam, M.D.M.; Zarif, M.I.I.; Hashem, M.M.A. Attack and Anomaly Detection in IoT Sensors in IoT Sites Using Machine Learning Approaches. Internet Things 2019, 7, 100059. [Google Scholar] [CrossRef]
- Khalifa, W.H.; Roushdy, M.I.; Salem, A.B.-M. Machine Learning Techniques for Intelligent Access Control. In New Approaches in Intelligent Image Analysis. Intelligent Systems Reference Library; Kountchev, R., Nakamatsu, K., Eds.; Springer: Cham, Switzerland, 2019. [Google Scholar]
- Lee, S.-H.; Yang, C.-S. An Intelligent Home Access Control System Using Deep Neural Network. In Proceedings of the 2017 IEEE International Conference on Consumer Electronics—Taiwan (ICCE-TW), Taipei, Taiwan, 12–14 June 2017. [Google Scholar]
- Marr, B. What Is Industry 4.0? Here’s A Super Easy Explanation for Anyone. Available online: https://www.forbes.com/sites/bernardmarr/2018/09/02/what-is-industry-4-0-heres-a-super-easy-explanation-for-anyone/?sh=c8fe9769788a (accessed on 23 June 2022).
- Barnes, J. Azure Machine Learning Microsoft Azure Essentials; Microsoft Press: New York, NY, USA, 2015; ISBN 9780735698178. [Google Scholar]
- Barga, R.; Fontama, V.; Tok, W.H. Predictive Analytics with Microsoft Azure Machine Learning. In Predictive Analytics with Microsoft Azure Machine Learning; Apress: New York, NY, USA, 2015; ISBN 978-1-4842-1200-4. [Google Scholar]
- Studio, M.V. Scott Hanselman’s Best Demo! IoT, Azure, Machine Learning & More. Available online: https://www.youtube.com/watch?v=u5oTz1e5qqE (accessed on 2 June 2022).
- Higginbotham, S. IBM Is Bringing in Watson to Conquer The Internet of Things. Available online: http://fortune.com/2015/12/15/ibm-watson-iot/ (accessed on 23 June 2022).
- IBM. Watson Internet of Things. Available online: http://www.ibm.com/internet-of-things/iot-solutions/watson-iot-platform/ (accessed on 23 June 2022).
- Knowles, G.; Melamed, A.; Fisher, A. Accelerate the Development of Cognitive Computing in Your IoT App. Available online: http://www.ibm.com/developerworks/library/iot-cc-watson-iot-platform-trs/iot-cc-watson-iot-platform-trs-pdf.pdf (accessed on 20 June 2022).
- News Room IBM and Cisco Combine the Power of Watson Internet of Things with Edge Analytics. Available online: https://www-03.ibm.com/press/us/en/pressrelease/49845.wss (accessed on 25 June 2022).
- Tilley, A. IBM And Cisco Partner to Bring Watson Closer To The “Internet Of Things”. Available online: http://www.forbes.com/sites/aarontilley/2016/06/02/ibm-cisco-watson-internet-of-things/#1c0c0bda564a (accessed on 23 June 2022).
- Bilac, S. Machine Learning in the Cloud, with TensorFlow. Available online: https://research.googleblog.com/2016/03/machine-learning-in-cloud-with.html (accessed on 23 June 2022).
- Kepes, B. Splunk Ups the Machine-Learning Ante. Available online: http://www.computerworld.com/article/3125517/big-data/splunk-ups-the-machine-learning-ante.html (accessed on 26 June 2022).
- Morphy, E. Splunk Enhances Machine Learning with 300 New Algorithms. Available online: http://www.cmswire.com/big-data/splunk-enhances-machine-learning-with-300-new-algorithms/ (accessed on 2 June 2022).
- News AWS IoT Now Supports Integration with Amazon Machine Learning and AWS CloudTrail. Available online: https://aws.amazon.com/about-aws/whats-new/2016/04/aws-iot-now-supports-integration-with-amazon-machine-learning-and-aws-cloudtrail/ (accessed on 25 June 2022).
- Yegulalp, S. Amazon Dumbs down Machine Learning for the Rest of Us. Available online: http://www.infoworld.com/article/2908498/amazon-web-services/amazon-machine-learning-for-the-rest-us.html (accessed on 27 June 2022).
- CB Insights. Sensors, Plus Brains: 17 IoT Companies Using Artificial Intelligence Tech. Available online: https://www.cbinsights.com/blog/artificial-intelligence-iot-company-list/ (accessed on 25 June 2022).
- Elayan, H.; Aloqaily, M.; Member, S.; Karray, F.; Guizani, M. Internet of Behavior (IoB) and Explainable AI Systems for Influencing IoT Behavior; Cornell University: Ithaca, NY, USA, 2022. [Google Scholar]
- Javaid, M.; Haleem, A.; Singh, R.P.; Rab, S.; Suman, R. Internet of Behaviours (IoB) and Its Role in Customer Services. Sens. Int. 2021, 2, 100122. [Google Scholar] [CrossRef]
- Pinochet, L.H.C.; Lopes, E.L.; Srulzon, C.H.F.; Onusic, L.M. The Influence of the Attributes of “Internet of Things” Products on Functional and Emotional Experiences of Purchase Intention. Innov. Manag. Rev. 2018, 15, 303–320. [Google Scholar] [CrossRef]
- Stary, C. The Internet-of-Behavior as Organizational Transformation Space with Choreographic Intelligence. Commun. Comput. Inf. Sci. 2020, 1278, 113–132. [Google Scholar] [CrossRef]
- Singh, R.P.; Javaid, M.; Haleem, A.; Suman, R. Internet of Things (IoT) Applications to Fight against COVID-19 Pandemic. Diabetes Metab. Syndr. Clin. Res. Rev. 2020, 14, 521–524. [Google Scholar] [CrossRef]
- Kolankari, P. As COVID-19 Hounds the World, AI and IoT Lead the Charge in Healthcare 4.0. Economic Times, 4 August 2020. [Google Scholar]
- Mishra, S. The Growing Role of IoT in COVID-19 Response. Available online: https://www.iotforall.com/the-growing-role-of-iot-in-covid-19-response/ (accessed on 16 June 2022).
- Higginbotham, S. Tracking COVID-19 With the IoT May Put Your Privacy at Risk. Available online: https://spectrum.ieee.org/tracking-covid19-with-the-iot-may-put-your-privacy-at-risk (accessed on 28 June 2022).
- Alam, F.; Almaghthawi, A.; Katib, I.; Albeshri, A.; Mehmood, R. IResponse: An AI and IoT-Enabled Framework for Autonomous COVID-19 Pandemic Management. Sustainability 2021, 13, 3797. [Google Scholar] [CrossRef]
- Talebian, A.; Mishra, S. Predicting the Adoption of Connected Autonomous Vehicles: A New Approach Based on the Theory of Diffusion of Innovations. Transp. Res. Part C Emerg. Technol. 2018, 95, 363–380. [Google Scholar] [CrossRef]
- Alam, F.; Mehmood, R.; Katib, I.; Altowaijri, S.; Albeshri, A. TAAWUN: A Decision Fusion and Feature Specific Road Detection Approach for Connected Autonomous Vehicles. Mob. Netw. Appl. 2019, 2019, 1–17. [Google Scholar] [CrossRef]
- Morris, D.Z. Google Self-Driving Car in Serious Crash in Mountain View. Fortune. 2016. Available online: http://fortune.com/2016/09/25/crash-google-self-driving-car/ (accessed on 20 June 2022).
- Levin, S.; Woolf, N. Tesla Driver Killed While Using Autopilot Was Watching Harry Potter, Witness Says. 2016. Available online: https://www.theguardian.com/technology/2016/jul/01/tesla-driver-killed-autopilot-self-driving-car-harry-potter (accessed on 20 June 2022).
- Elliott, D.; Keen, W.; Miao, L. Recent Advances in Connected and Automated Vehicles. J. Traffic Transp. Eng. 2019, 6, 109–131. [Google Scholar] [CrossRef]
- Ye, L.; Yamamoto, T. Evaluating the Impact of Connected and Autonomous Vehicles on Traffic Safety. Phys. A Stat. Mech. Its Appl. 2019, 526, 121009. [Google Scholar] [CrossRef]
- Cisco. Fog Computing and the Internet of Things: Extend the Cloud to Where the Things Are. CISCO White Paper 2016, 6. Available online: https://docslib.org/doc/7133745/fog-computing-and-the-internet-of-things-extend-the-cloud-to-where-the-things-are (accessed on 2 June 2022).
- Gonzalez, N.M.; Goya, W.A.; De, R.; Pereira, F.; Langona, K.; Silva, E.A.; Melo De Brito Carvalho, C.; Miers, C.C.; Mångs, J.-E.; Sefidcon, A. Fog Computing: Data Analytics and Cloud Distributed Processing on the Network Edges. In Proceedings of the 2016 35th International Conference of the Chilean Computer Science Society (SCCC), Valparaiso, Chile, 10–14 October 2016. [Google Scholar]
- Greenfield, D. Fog Computing vs. Edge Computing: What’s the Difference? Available online: https://www.automationworld.com/fog-computing-vs-edge-computing-whats-difference (accessed on 28 June 2022).
- LeCun, Y.; Bengio, Y.; Hinton, G. Deep Learning. Nature 2015, 521, 436–444. [Google Scholar] [CrossRef]
- Yao, S.; Zhao, Y.; Zhang, A.; Hu, S.; Shao, H.; Zhang, C.; Su, L.; Abdelzaher, T. Deep Learning for the Internet of Things. Computer 2018, 51, 32–41. [Google Scholar] [CrossRef]
- Zhao, T.; Xie, Y.; Wang, Y.; Cheng, J.; Guo, X.; Hu, B.; Chen, Y. A Survey of Deep Learning on Mobile Devices: Applications, Optimizations, Challenges, and Research Opportunities. Proc. IEEE 2022, 110, 334–354. [Google Scholar] [CrossRef]
- Duong, C.N.; Quach, K.G.; Jalata, I.; Le, N.; Luu, K. MobiFace: A Lightweight Deep Learning Face Recognition on Mobile Devices. In Proceedings of the 2019 IEEE 10th International Conference on Biometrics Theory, Applications and Systems (BTAS), Tampa, FL, USA, 23 September 2019; pp. 1–6. [Google Scholar]
- Agarwal, P.; Alam, M. A Lightweight Deep Learning Model for Human Activity Recognition on Edge Devices. Procedia Comput. Sci. 2020, 167, 2364–2373. [Google Scholar] [CrossRef]
- Martindez-Díaz, Y.; Luevano, L.S.; Mendez-Vazquez, H.; Nicolas-Diaz, M.; Chang, L.; Gonzalez-Mendoza, M. ShuffleFaceNet: A Lightweight Face Architecture for Efficient and Highly-Accurate Face Recognition. In Proceedings of the 2019 IEEE/CVF International Conference on Computer Vision Workshop (ICCVW), Seoul, Korea, 27–28 October 2019. [Google Scholar] [CrossRef]
- Sliwa, B.; Piatkowski, N.; Wietfeld, C. LIMITS: Lightweight Machine Learning for IoT Systems with Resource Limitations. In Proceedings of the ICC 2020—2020 IEEE International Conference on Communications (ICC), Dublin, Ireland, 7–11 June 2020. [Google Scholar] [CrossRef]
- Shuvo, S.B.; Ali, S.N.; Swapnil, S.I.; Al-Rakhami, M.S.; Gumaei, A. CardioXNet: A Novel Lightweight Deep Learning Framework for Cardiovascular Disease Classification Using Heart Sound Recordings. IEEE Access 2021, 9, 36955–36967. [Google Scholar] [CrossRef]
- Luo, L. Applying Lightweight Deep Learning-Based Virtual Vision Sensing Technology to Realize and Develop New Media Interactive Art Installation. Comput. Intell. Neurosci. 2022, 2022, 9119316. [Google Scholar] [CrossRef]
- Pang, S.; Wang, S.; Rodríguez-Patón, A.; Li, P.; Wang, X. An Artificial Intelligent Diagnostic System on Mobile Android Terminals for Cholelithiasis by Lightweight Convolutional Neural Network. PLoS ONE 2019, 14, e0221720. [Google Scholar] [CrossRef]
- Winoto, A.S.; Kristianus, M.; Premachandra, C. Small and Slim Deep Convolutional Neural Network for Mobile Device. IEEE Access 2020, 8, 125210–125222. [Google Scholar] [CrossRef]
- Nižetić, S.; Šolić, P.; López-de-Ipiña González-de-Artaza, D.; Patrono, L. Internet of Things (IoT): Opportunities, Issues, and Challenges towards a Smart and Sustainable Future. J. Clean. Prod. 2020, 274, 122877. [Google Scholar] [CrossRef]
- Idrees Sarhan, Q. Internet of Things: A Survey of Challenges and Issues. Int. J. Internet Things Cyber Assur. 2018, 1, 40–75. [Google Scholar] [CrossRef]
- Malekshahi Rad, M.; Rahmani, A.M.; Sahafi, A.; Nasih Qader, N. Social Internet of Things: Vision, Challenges, and Trends. Hum. Cent. Comput. Inf. Sci. 2020, 10, 52. [Google Scholar] [CrossRef]
- Sadique, K.M.; Rahmani, R.; Johannesson, P. Towards Security on Internet of Things: Applications and Challenges in Technology. Procedia Comput. Sci. 2018, 141, 199–206. [Google Scholar] [CrossRef]
- O’Halloran, J. Connectivity Issues Disrupting Most Businesses’ IoT Roll-Outs. Available online: https://www.computerweekly.com/news/252509991/Connectivity-issues-disrupting-most-businesses-IoT-roll-outs (accessed on 2 June 2022).
- IoT Connectivity: Challenges and Strategies. Available online: https://www.telecomreview.com/index.php/articles/reports-and-coverage/5319-iot-connectivity-challenges-and-strategies (accessed on 2 June 2022).
- Rahul, Y.; Weizhe, Z.; Neeraj, K.; Omprakash, K. Recent Trends and Challenges in Fog/Edge Computing for Internet of Things. Available online: https://www.hindawi.com/journals/wcmc/si/975923/ (accessed on 2 June 2022).
- Abi Sen, A.A.; Eassa, F.A.; Jambi, K.; Yamin, M. Preserving Privacy in Internet of Things: A Survey. Int. J. Inf. Technol. 2018, 10, 189–200. [Google Scholar] [CrossRef]
- Falcone, R.; Sapienza, A. On the Users’ Acceptance of IoT Systems: A Theoretical Approach. Information 2018, 9, 53. [Google Scholar] [CrossRef]
- Beştepe, F.; Yildirim, S.Ö. Acceptance of IoT-Based and Sustainability-Oriented Smart City Services: A Mixed Methods Study. Sustain. Cities Soc. 2019, 526, 121009. [Google Scholar] [CrossRef]
- Patil, Y. 6 Key Challenges to Consider for Successful IoT Implementation. Available online: https://www.saviantconsulting.com/blog/iot-implementation-challenges-enterprises.aspx (accessed on 2 June 2022).
- Akhairamka, P. The 15 Key Challenges with IoT Project Development in 2021. Available online: https://iot-analytics.com/challenges-iot-project-development/ (accessed on 2 June 2022).
- IoT. Business.News IoT News—IoT Market Growth Will Slow down due to the COVID-19 Pandemic and the Limited Take-up of LPWA Solutions. Available online: https://iotbusinessnews.com/2021/02/25/20654-iot-market-growth-will-slow-down-due-to-the-covid-19-pandemic-and-the-limited-take-up-of-lpwa-solutions/ (accessed on 2 June 2022).
- Developer Burnout and a Global Chip Shortage: The IoT Is Facing a Perfect Storm|ZDNet. Available online: https://www.zdnet.com/article/developer-burn-out-and-a-global-chip-shortage-the-iot-is-facing-a-perfect-storm/ (accessed on 2 June 2022).
- IDC. News European IoT Spending Continues Its Double-Digit Growth, Despite Global Uncertainty and Slow Demand, Says IDC. Available online: https://www.idc.com/getdoc.jsp?containerId=prEUR149276822 (accessed on 2 June 2022).
- Bernard Marr The 5 Biggest Internet of Things (IoT) Trends In 2021 Everyone Must Get Ready for Now. Available online: https://www.forbes.com/sites/bernardmarr/2020/10/26/the-5-biggest-internet-of-things-iot-trends-in-2021-everyone-must-get-ready-for-now/?sh=5c8dd2c641fd (accessed on 2 June 2022).
- Chohan, S.R.; Hu, G. Success Factors Influencing Citizens’ Adoption of IoT Service Orchestration for Public Value Creation in Smart Government. IEEE Access 2020, 8, 208427–208448. [Google Scholar] [CrossRef]



| Type of Sensors | Type of Data | Possible Applications | Data Challenges |
|---|---|---|---|
| Vision | Images & Videos | Satellites, Autonomous Vehicles, Robots, Tracking | Feature Selection |
| Force, Pressure, Load | Numeric Readings | Industry, Autonomous Vehicles, Robots, Healthcare | Outliers, Missing Values |
| Motion & Velocity | Numeric Readings | Satellites, Autonomous Vehicles, Robots, Tracking | Outliers, Missing Values |
| Gas & Chemical | Numeric Readings | Pollution, Industry, Healthcare | Outliers, Missing Values |
| Temperature, Humidity, Moisture | Numeric Readings | Fire warning, Weather, Industry, Healthcare | Outliers, Missing Values |
| Radar, Lidar, Proximity & IR | Numeric Readings | Satellites, Autonomous Vehicles, Robots, Tracking, Defence, Space | Outliers, Missing Values |
| Positioning & Location | Numeric & Coordinates Readings | Satellites, Autonomous Vehicles, Robots, Tracking, Mobile Applications | Outliers, Missing Values |
| Level & Flow | Numeric Readings | Industry, Dams, Tanks | Outliers, Missing Values |
| Sound & Vibration | Numeric Readings | Industry, Dams, Tanks, Healthcare | Outliers, Missing Values |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Bzai, J.; Alam, F.; Dhafer, A.; Bojović, M.; Altowaijri, S.M.; Niazi, I.K.; Mehmood, R. Machine Learning-Enabled Internet of Things (IoT): Data, Applications, and Industry Perspective. Electronics 2022, 11, 2676. https://doi.org/10.3390/electronics11172676
Bzai J, Alam F, Dhafer A, Bojović M, Altowaijri SM, Niazi IK, Mehmood R. Machine Learning-Enabled Internet of Things (IoT): Data, Applications, and Industry Perspective. Electronics. 2022; 11(17):2676. https://doi.org/10.3390/electronics11172676
Chicago/Turabian StyleBzai, Jamal, Furqan Alam, Arwa Dhafer, Miroslav Bojović, Saleh M. Altowaijri, Imran Khan Niazi, and Rashid Mehmood. 2022. "Machine Learning-Enabled Internet of Things (IoT): Data, Applications, and Industry Perspective" Electronics 11, no. 17: 2676. https://doi.org/10.3390/electronics11172676
APA StyleBzai, J., Alam, F., Dhafer, A., Bojović, M., Altowaijri, S. M., Niazi, I. K., & Mehmood, R. (2022). Machine Learning-Enabled Internet of Things (IoT): Data, Applications, and Industry Perspective. Electronics, 11(17), 2676. https://doi.org/10.3390/electronics11172676








