Evaluation of Black-Box Web Application Security Scanners in Detecting Injection Vulnerabilities
Abstract
:1. Introduction
2. State-of-the-Art Review
- We analysed and evaluated the detection accuracy of black-box scanners against SQLi, NoSQL, and SSTI injection vulnerabilities using one of the most modern and sophisticated insecure web applications, representing a real-life e-commerce web application.
- We tested black-box scanners in four different modes to identify their limitations and gaps in practice.
- We identified the limitations of the evaluated black-box scanners’ ability to detect SQLi, NoSQL, and SSTI vulnerabilities.
3. Web Application Security Testing and Vulnerability
3.1. Structured Query Language (SQLi) Injection
3.2. Union-Based SQLi
3.3. Blind SQLi
3.4. Content-Based Blind SQLi
3.5. Time-Based Blind SQLi
3.6. NoSQLi Injection
3.7. Server-Side Template Injection
4. Our Approach towards Vulnerability Scanners
4.1. Application Vulnerability Scanners
- Can identify a specific set of security vulnerabilities in a web application;
- Can generate a text report describing the attack for each vulnerability identified;
- Has a low rate of false-positive results.
4.2. Architecture of Web Application Vulnerabilities Scanners
- The crawling module uses a crawler to navigate a web application to identify and recover web pages, input vectors (e.g., input fields of hypertext markup language forms), GET/POST request parameters and cookies. Next, the crawler generates an indexed list of all accessed uniform resource locators (URLs). The detection of a web vulnerability ultimately depends on the quality of the crawler. If it is ineffective, the scanners will not be able to detect the vulnerability [11,32].
- The attacking (fuzzing) module uses a fuzzer to analyse the URLs and input vectors identified by the crawler then sends potential attack patterns to the entry points. The fuzzer creates a list of potentially vulnerable values to trigger a vulnerability for each entry and type. For example, the fuzzer component tries to inject JavaScript malicious code to test the presence of an XSS vulnerability [11,32].
- The analysis module analyses the results obtained in the previous step to detect existing vulnerabilities and provide other modules with comments. For example, if the returned page contains a database error message in response to the input tests for an SQLi injection. In that case, the analysis module will predict a potential SQLi vulnerability in that page [11,32].
4.3. Web Application Security Scanner Evaluation Criteria (WASSEC)
- Protocol Support: The scanner must support all communication protocols that are frequently used by web applications. Moreover, proxy capabilities, such as the hypertext transfer protocol(HTTP) and Socks proxies, should be supported.
- Authentication: The scanner should be able to maintain all authentication methods commonly used in a web application.
- Session Management: During a security scan, a scanner should maintain a valid session with the application.
- Crawling: The scanner should have a feature that can crawl a web application thoroughly based on the user-defined configuration.
- Parsing: To obtain information about the functionality and layout of the scanned web application, the scanner should be able to parse the most widely used web technologies.
- Testing: The scanner should be able to detect the security vulnerabilities and architectural flaws in a web application. It should also provide the user with configuration options to customize a scan.
- Command and control: The scanner should have command and control functions that enhance the user experience. For example, it schedules scans, pause and restart them, and schedule several scans simultaneously.
- Reporting: After each scan, a scanner should be able to produce a custom report.
4.4. Evaluation Metrics
- True positives (TPs) are the vulnerabilities detected by a scanner that truly exist in the code [34].
- False negatives (FNs) are the vulnerabilities that actually exist in the code but are not detected by the scanner [34].
- F-measure is the harmonic mean of precision and recall [36], which is represented as follows:
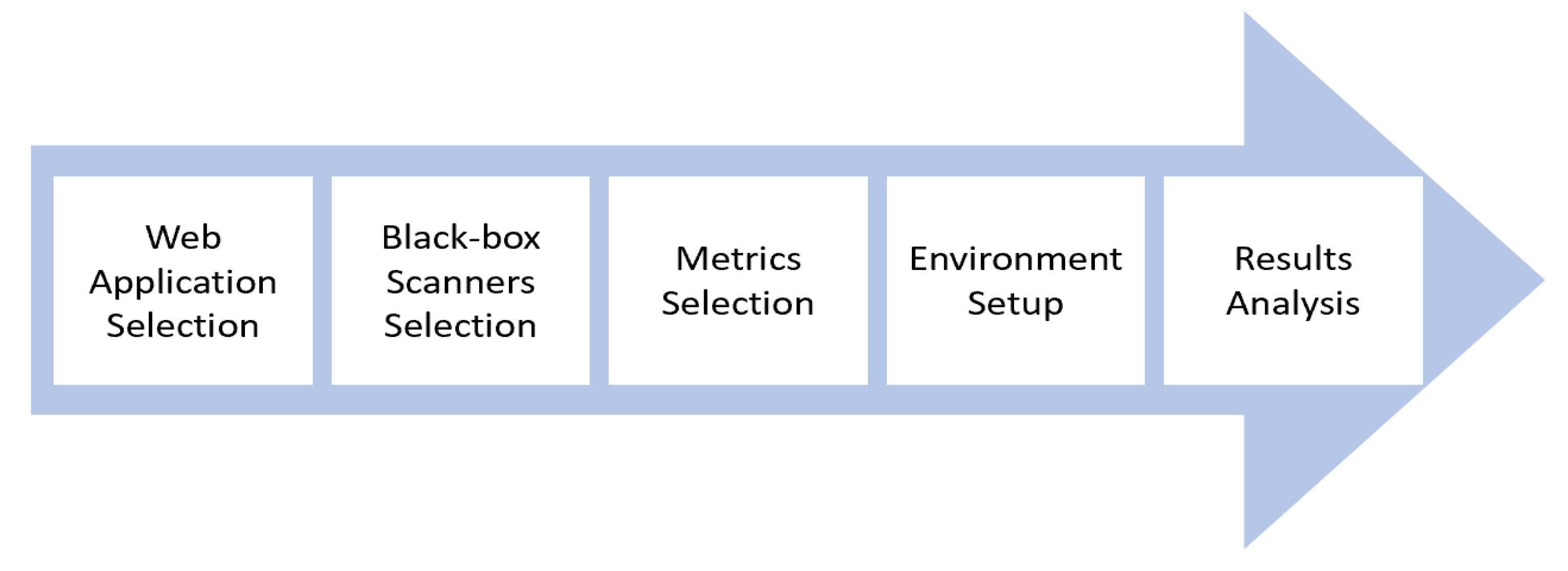
5. Research Design
5.1. Web Application Selection
5.2. Black-Box Scanners Selection
- ZAP is a free and open-source penetration testing tool for detecting vulnerabilities in web applications. It has a proxy feature for intercepting and inspecting messages sent between the client and the web application [39].
- Burp Suite Professional is a commercial web security tool that can be used to test all OWASP Top 10 vulnerabilities. It is capable of both passive and active analysis. In addition, its powerful proxy/history enables penetration testers to modify all secure HTTPS communications passing using the browser [40].
- Vega is a free and open-source tool for testing the security of web applications and detecting vulnerabilities. Moreover, it provides an automated scan for quick tests and has an intercepting proxy component [41].
- Skipfish is a free and open-source vulnerability scanner that prepares an interactive sitemap for the scanned web application. It runs repetitive crawls and dictionary-based scans. The obtained map is annotated with the output from several active scans [42].
- Wapiti is a free, open-source, and command-line application that scans the security of web applications. It conducts black-box scans by crawling the web pages of the target web application and looks for forms into which it may inject data. When the list of URLs, forms and their inputs has been collected, Wapiti acts like a fuzzer and injects payloads to see whether there is a potential vulnerability [43].
5.3. Metrics Selection
6. Experimental Setup and Execution
6.1. Experimental Design
- We started every scan by choosing from the four scanning modes.
- We ran the target web application (OWASP Juice Shop).
- We connected the target web application to the evaluated scanner.
- The crawler component of the scanner then explored the web application pages and identified forms and entry points.
- The scanner sent potential payload attacks to the entry points.
- The analysis module of the scanner generated analytical reports.
- We analysed these reports manually.
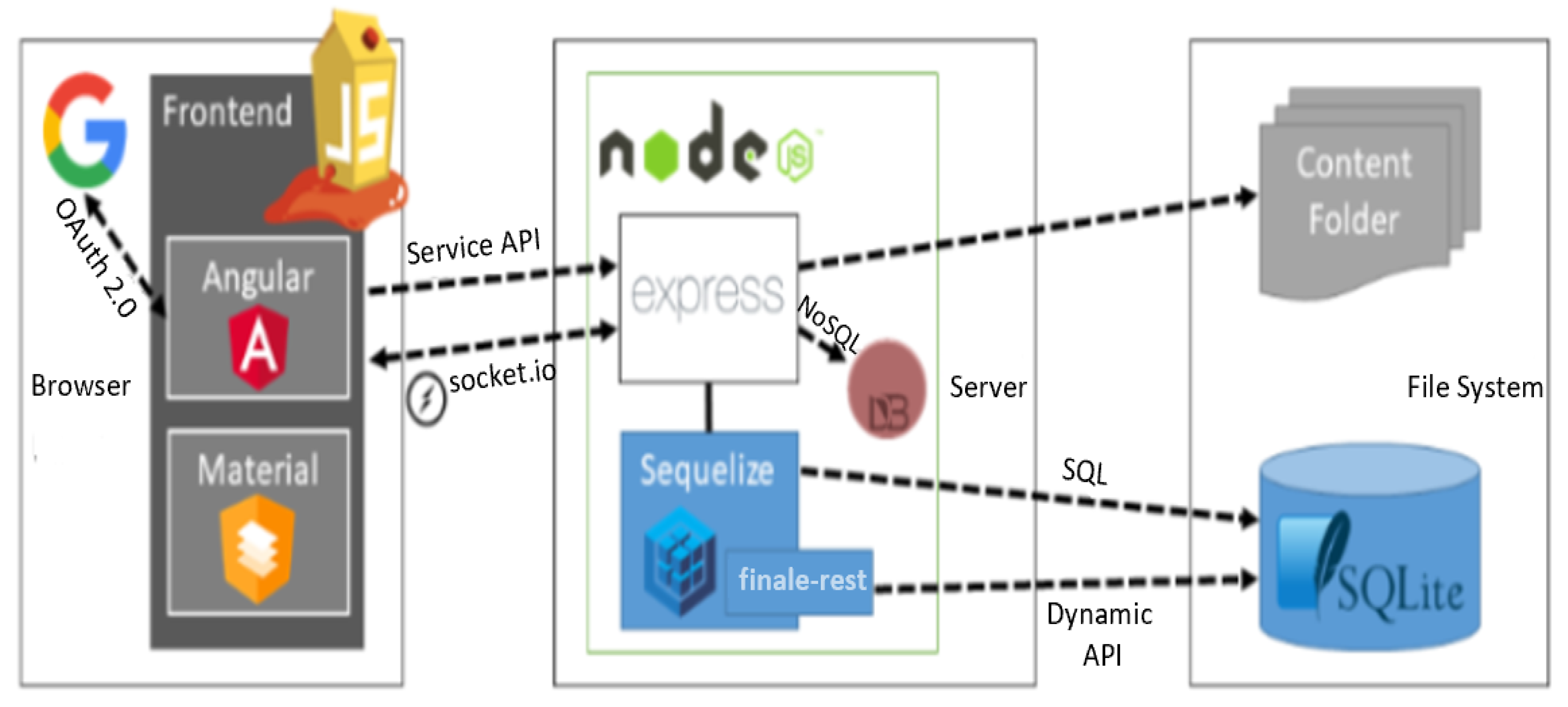
6.2. Owasp Juice Shop Application
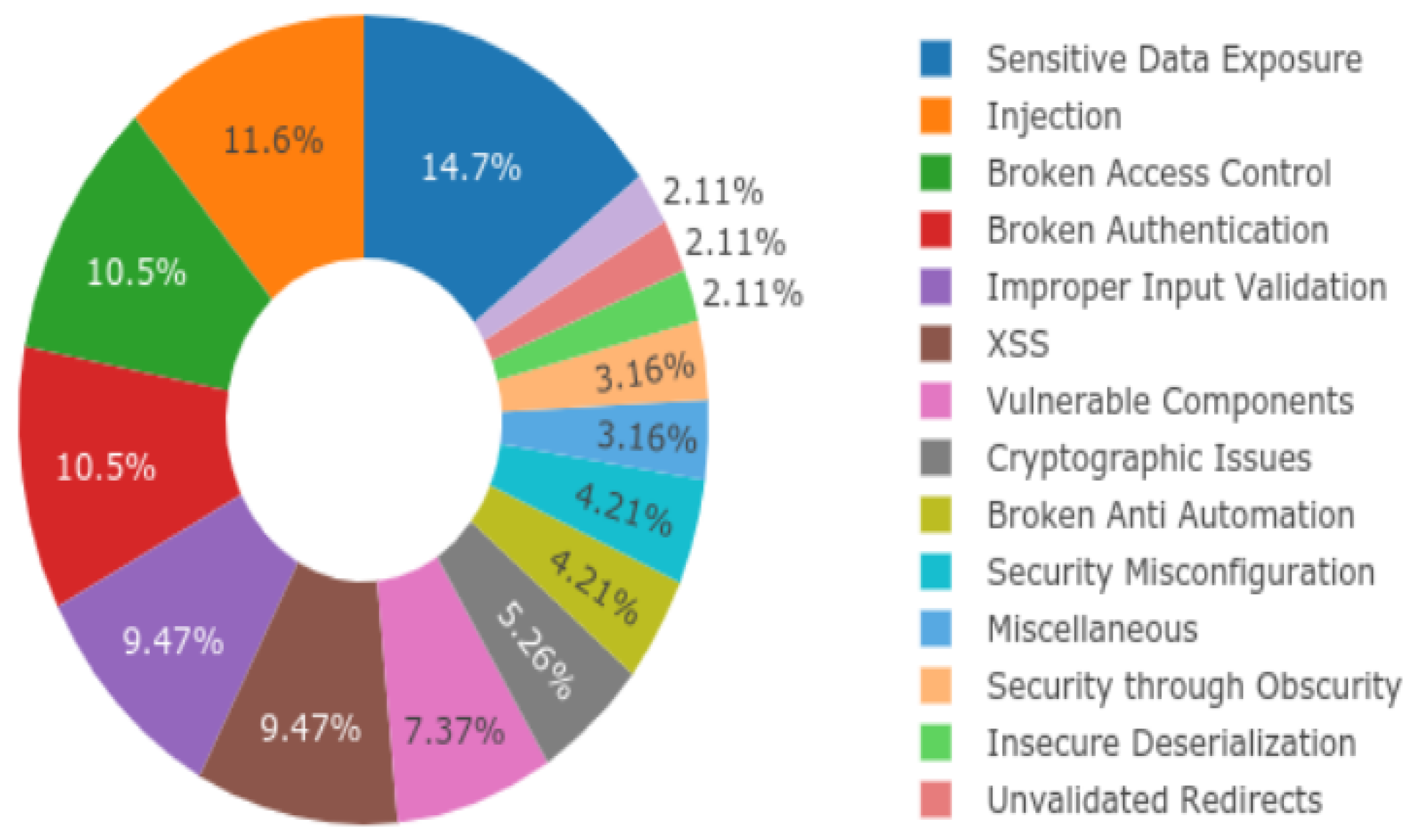
6.3. Owasp Juice Shop Tested Vulnerabilities
6.4. Web Application Vulnerability Scanner Modes
| Algorithm 1: Mode 1: Point-and-shoot (PaS) |
Description: The scanner is only provided with the OWASP Juice Shop application’s entry URL for scanning. Input OWASP Juice Shop URL: http://localhost:3000 (accessed on 8 May 2021) Output Scan report Start Set the scanner to work with a browser Launch the browser Open the OWASP Juice Shop application Add the application URL to the target scope Run the crawler Run the active scan End |
| Algorithm 2: Mode 2: Unauthenticated scan with proxy |
Description: As in mode 1, the scanner is provided with the application’s entry URL, with the exception of using a proxy component (if available) to visit all the application pages that do not need authentication manually and to fill in any forms. Input OWASP Juice Shop URL: http://localhost:3000 (accessed on 8 May 2021) Output Scan report Start Set the scanner to work with a browser Launch the browser Open the OWASP Juice Shop application Add the application URL to the target scope Run the crawler Use proxy to visit each unauthenticated page Fill in any forms Run the active scan End |
| Algorithm 3: Mode 3: Point-and-shoot with user credentials |
Description: The scanner is given the OWASP Juice Shop application entry URL and provided with valid login credentials (such as username and password or authentication token) to help the scanner access the authenticated pages. Input OWASP Juice Shop URL: http://localhost:3000 (accessed on 8 May 2021) User credentials Output Scan report Start Set the scanner to work with a browser Launch the browser Open the OWASP Juice Shop application Add the application URL to the target scope Log in the application with legitimate credentials Configure the scanner using user credentials in scanning Run the crawler Run the active scan End |
| Algorithm 4: Mode 4: Authenticated scan with proxy |
Description: As in mode 2, the scanner is provided with the application’s URL and valid login credentials to help the scanner access the authenticated pages. Moreover, if the scanner has a proxy component, it is used to visit every page manually, including pages that need authentication, and to fill in any forms. Input OWASP Juice Shop URL: http://localhost:3000 (accessed on 8 May 2021) User credentials Output Scan report Start Set the scanner to work with a browser Launch the browser Open the OWASP Juice Shop application Add the application URL to the target scope Log in the application with legitimate credentials Configure the scanner using user credentials Run the crawler Use a proxy to visit every page in the application Fill in any forms Run the active scan End |
7. Results Analysis
7.1. Experimental Results
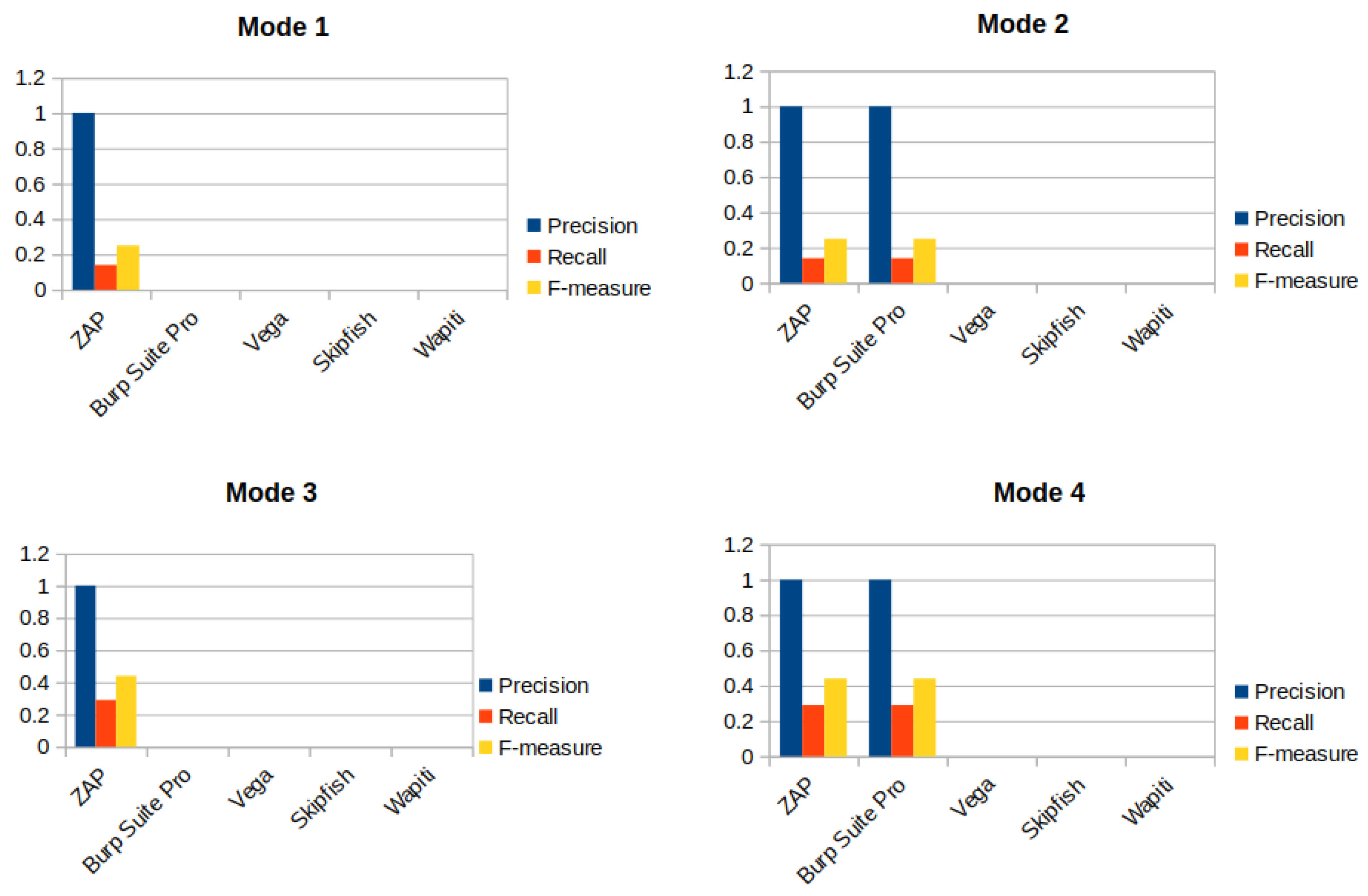
7.2. Mode 1 Results
- FNs: It is clear from Table 4 that the number of undetected vulnerabilities (FN) was significantly higher than the detected (TP) and wrongly detected (FP) values in this mode.
- TPs: As we can see from Table 4, most scanners failed to detect any known vulnerability, apart from the ZAP scanner, which found one SQLi injection vulnerability in the home page.
- FPs: Because we only scanned injection vulnerabilities, no scanner detected any injection vulnerability that did not really exist.
7.3. Mode 2 Results
- FNs: The number of undetected vulnerabilities (FNs) in this mode was the same as in Mode 1, with the exception of the Burp Suite Professional scanner, which detected one vulnerability.Thus, the number of FNs decreased by one.
- TPs: In Mode 2, both the ZAP and Burp Suite scanners detected only one vulnerability. The one detected by ZAP was already found during Mode 1 scanning. The Burp Suite was likely able to detect the vulnerability because we filled in the login form manually to provide the scanner with privileged credentials; then, the scanner was able to access the vulnerable login page.
- FPs: None of the scanners detected any injection vulnerabilities that did not really exist in the application.
7.4. Mode 3 Results
- FNs: ZAP scanner achieved the fewest number of FNs (five).
- TPs: Table 6 shows that using the scanner in a proxy mode to access the unauthenticated pages in the application manually increased the number of detected vulnerabilities by one for the ZAP scanner only. However, other scanners that had a proxy (i.e.Burp Suite Professional and Vega) did not detect any, even when we manually accessed the vulnerable pages.
- FPs: None of the scanners detected any injection vulnerabilities that did not really exist in the application.
7.5. Mode 4 Results
- FNs: Vega had the highest number of undetected vulnerabilities. In contrast, ZAP and Burp Suite had the fewest FN values (five each).
- TPs: Both ZAP and Burp Suite detected two injection vulnerabilities.
- FPs: None of the scanners detected any injection vulnerabilities that did not really exist in the application.
7.6. Results Summary
8. Evaluation
8.1. Precision, Recall, and F-Measure
8.2. Discussion: Finding Key Gaps
9. Comparison with Previous Work
10. Conclusions and Future Work
- Evaluate more black-box scanners. In this paper, we evaluated only five. However, there are a growing number on the market. Therefore, future studies can scan the same application, OWASP Juice Shop, with a different selection of the most widely used scanners.
- Test other vulnerabilities. The OWASP Juice Shop application contains 14 categories of vulnerabilities and includes some that no research has ever tested. In this paper, we focused only on injection vulnerabilities. However, future research should include other types.
- Analyse the identified vulnerability detection limitations. Because our work evaluated open-source scanners, other researchers now have the opportunity to access and review the source code. Therefore, future studies should examine the design issues and limitations in greater detail.
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Conflicts of Interest
References
- Internet Users. Available online: https://www.internetlivestats.com/watch/internet-users (accessed on 8 May 2021).
- Total Number of Websites. Available online: https://www.internetlivestats.com/watch/websites (accessed on 8 May 2021).
- Verizon. 2020 Data Breach Investigations Report. Technical Report, Verizon. 2020. Available online: https://www.cisecurity.org/wp-content/uploads/2020/07/The-2020-Verizon-Data-Breach-Investigations-Report-DBIR.pdf (accessed on 8 May 2021).
- OWASP. OWASP Top 10 -2017 the Ten Most Critical Web Application Security Risks; Technical Report; OWASP: Wakefield, MA, USA, 2017. [Google Scholar]
- State of the Internet Security. Available online: https://www.akamai.com/uk/en/multimedia/documents/state-of-the-internet/soti-security-a-year-in-review-report-2019.pdf (accessed on 8 May 2021).
- Braga, M. What We Know about the Equifax Breach—And What We Don’t. 2017. Available online: https://www.cbc.ca/news/science/equifax-canada-breach-sin-cybersecurity-what-we-know-1.4297532 (accessed on 8 May 2021).
- Khalil, R.F. Why Johnny Still Can’t Pentest: A Comparative Analysis of Open-Source Black-box Web Vulnerability Scanners. Ph.D. Thesis, Université d’Ottawa/University of Ottawa, Ottawa, ON, Canada, 2018. [Google Scholar]
- Makino, Y.; Klyuev, V. Evaluation of web vulnerability scanners. In Proceedings of the 2015 IEEE 8th International Conference on Intelligent Data Acquisition and Advanced Computing Systems: Technology and Applications (IDAACS), Warsaw, Poland, 24–26 September 2015; Volume 1, pp. 399–402. [Google Scholar]
- Suto, L. Analyzing the Accuracy and Time Costs of Web Application Security Scanners. 2010. Available online: http://www.think-secure.nl/uk/Accuracy_and_Time_Costs_of_Web_App_Scanners.pdf (accessed on 8 May 2021).
- Bau, J.; Bursztein, E.; Gupta, D.; Mitchell, J. State of the art: Automated black-box web application vulnerability testing. In Proceedings of the 2010 IEEE Symposium on Security and Privacy, Oakland, CA, USA, 16–19 May 2010; pp. 332–345. [Google Scholar]
- Doupé, A.; Cova, M.; Vigna, G. Why Johnny can’t pentest: An analysis of black-box web vulnerability scanners. In Proceedings of the International Conference on Detection of Intrusions and Malware, and Vulnerability Assessment, Cagliari, Italy, 14–16 July 2021; Springer: Berlin/Heidelberg, Germany, 2010; Volume 6201, pp. 111–131. [Google Scholar]
- Khoury, N.; Zavarsky, P.; Lindskog, D.; Ruhl, R. Testing and Assessing Web Vulnerability Scanners for Persistent SQL Injection Attacks. In Proceedings of the First International Workshop on Security and Privacy Preserving in E-Societies, New York, NY, USA, 9 June 2011; Association for Computing Machinery: New York, NY, USA, 2011; pp. 12–18. [Google Scholar] [CrossRef]
- Khoury, N.; Zavarsky, P.; Lindskog, D.; Ruhl, R. An analysis of black-box web application security scanners against stored SQLi injection. In Proceedings of the 2011 IEEE Third International Conference on Privacy, Security, Risk and Trust and 2011 IEEE Third International Conference on Social Computing, Boston, MA, USA, 9–11 October 2011; pp. 1095–1101. [Google Scholar]
- Parvez, M.; Zavarsky, P.; Khoury, N. Analysis of effectiveness of black-box web application scanners in detection of stored SQLi injection and stored XSS vulnerabilities. In Proceedings of the 2015 10th International Conference for Internet Technology and Secured Transactions (ICITST), London, UK, 14–16 December 2015; pp. 186–191. [Google Scholar]
- Idrissi, S.; Berbiche, N.; Guerouate, F.; Shibi, M. Performance evaluation of web application security scanners for prevention and protection against vulnerabilities. Int. J. Appl. Eng. Res. 2017, 12, 11068–11076. [Google Scholar]
- Sutton, M.; Greene, A.; Amini, P. Fuzzing: Brute Force Vulnerability Discovery, 3rd ed.; Pearson Education: London, UK, 2007. [Google Scholar]
- Doupé, A.; Cavedon, L.; Kruegel, C.; Vigna, G. Enemy of the state: A state-aware black-box web vulnerability scanner. In Presented as part of the 21st USENIX Security Symposium (USENIX Security 12), Bellevue, WA, USA, 11–13 August 2021; USENIX Association: Bellevue, WA, USA, 2012; pp. 523–538. [Google Scholar]
- Muñoz, F.R.; Cortes, I.I.S.; Villalba, L.J.G. Enlargement of vulnerable web applications for testing. J. Supercomput. 2017, 74, 6598–6617. [Google Scholar] [CrossRef]
- OWASP Foundation. Available online: https://owasp.org (accessed on 8 May 2021).
- SQL Injection. Available online: https://owasp.org/www-community/attacks/SQL_Injection (accessed on 8 May 2021).
- SQL Injection UNION Attacks. Available online: https://portswigger.net/web-security/sql-injection/union-attacks (accessed on 8 May 2021).
- Al-Khurafi, O.B.; Al-Ahmad, M.A. Survey of web application vulnerability attacks. In Proceedings of the 2015 4th International Conference on Advanced Computer Science Applications and Technologies (ACSAT), Kuala Lumpur, Malaysia, 8–10 December 2015; pp. 154–158. [Google Scholar]
- Banach, Z. How Blind SQL Injection Works. 2020. Available online: https://www.invicti.com/blog/web-security/how-blind-sql-injection-works/ (accessed on 8 May 2021).
- Acunetix. What Are Blind SQL Injections. Available online: https://www.acunetix.com/websitesecurity/blind-sql-injection/ (accessed on 8 May 2021).
- Banach, Z. What Is NoSQL Injection and How Can You Prevent It? 2020. Available online: https://www.invicti.com/blog/web-security/what-is-nosql-injection/ (accessed on 8 May 2021).
- Sachdeva, V.; Gupta, S. Basic NOSQL Injection Analysis And Detection On MongoDB. In Proceedings of the 2018 International Conference on Advanced Computation and Telecommunication (ICACAT), Bhopal, India, 28–29 December 2018; pp. 1–5. [Google Scholar]
- Hou, B.; Qian, K.; Li, L.; Shi, Y.; Tao, L.; Liu, J. MongoDB NoSQL injection analysis and detection. In Proceedings of the 2016 IEEE 3rd International Conference on Cyber Security and Cloud Computing (CSCloud), Beijing, China, 25–27 June 2016; pp. 75–78. [Google Scholar]
- Knowledge Base of Relational and NoSQL Database Management Systems. Available online: https://db-engines.com/en (accessed on 8 May 2021).
- Server-Side Template Injection. Available online: https://portswigger.net/web-security/server-side-template-injection (accessed on 8 May 2021).
- Kettle, J. Server-Side Template Injection. 2015. Available online: https://portswigger.net/research/server-side-template-injection (accessed on 8 May 2021).
- Black, P.E.; Fong, E.; Okun, V.; Gaucher, R. Software assurance tools: Web application security scanner functional specification version 1.0. Nist Spec. Publ. 2008, 2008, 269–500. [Google Scholar]
- Kagorora, F.; Li, J.; Hanyurwimfura, D.; Camara, L. Effectiveness of web application security scanners at detecting vulnerabilities behind ajax/json. Int. J. Innov. Res. Sci. Eng. Technol. 2015, 4, 4179–4188. [Google Scholar]
- Web ApplicationSecurity Consortium and others; Web application security scanner evaluation criteria. Web Appl. Secur. Consort. 2009, 1, 1–26.
- Antunes, N.; Vieira, M. Benchmarking vulnerability detection tools for web services. In Proceedings of the 2010 IEEE International Conference on Web Services, Miami, FL, USA, 5–10 July 2010; pp. 203–210. [Google Scholar]
- Antunes, N.; Vieira, M. Assessing and comparing vulnerability detection tools for web services: Benchmarking approach and examples. IEEE Trans. Serv. Comput. 2014, 8, 269–283. [Google Scholar] [CrossRef]
- Powers, D.M. Evaluation: From precision, recall and F-measure to ROC, informedness, markedness and correlation. arXiv 2011, arXiv:2010.16061v1. [Google Scholar]
- Siles, R.; Bennetts, S. OWASP Vulnerable Web Application Directory Project. 2019. Available online: https://owasp.org/www-project-vulnerable-web-applications-directory/ (accessed on 8 May 2021).
- Kimminich, B. OWASP Juice Shop Project; Technical report; OWASP: Bel Air, MD, USA, 2020. [Google Scholar]
- OWASP Zed Attack Proxy (ZAP). Available online: https://www.zaproxy.org (accessed on 8 May 2021).
- Burp Suite Scanner. Available online: https://portswigger.net/burp/vulnerability-scanner (accessed on 8 May 2021).
- Vega Vulnerability Scanner. Available online: https://subgraph.com/vega/ (accessed on 8 May 2021).
- skipfish(1)—Linux Man Page. Available online: ps://linux.die.net/man/1/skipfish (accessed on 8 May 2021).
- The Web-Application Vulnerability Scanner. Available online: https://wapiti.sourceforge.io (accessed on 8 May 2021).
- Antunes, N.; Vieira, M. On the metrics for benchmarking vulnerability detection tools. In Proceedings of the 2015 45th Annual IEEE/IFIP International Conference on Dependable Systems and Networks, Rio de Janeiro, Brazil, 22–25 June 2015; pp. 505–516. [Google Scholar]
- Kimminich, B. Pwning OWASP Juice Shop. 2017. Available online: https://pwning.owasp-juice.shop/ (accessed on 8 May 2021).

| Sep 2021 | Database Management System |
|---|---|
| 1 | Oracle |
| 2 | MySQL |
| 3 | Microsoft SQLServer |
| 4 | PostgreSQL |
| 5 | MongoDB |
| 6 | IBM DB2 |
| 7 | Redis |
| 8 | Elasticsearch |
| 9 | SQLite |
| 10 | Cassandra |
| Scanner | Vendor | Version | License |
|---|---|---|---|
| Burp Suite Pro | PortSwiger | 2020.7 | Commercial |
| ZAP | OWASP | 2.9.0 | Apache v 2.0 |
| Vega | Subgraph | 1.0 | Open-source |
| Skipfish | 2.10b | Free | |
| Wapiti | Informática Gesfor | 3.0.3 | Open-source |
| Vulnerability | Number | Login Required |
|---|---|---|
| Blind SQLi | 1 | 0 |
| Union-based SQLi Injection | 1 | 0 |
| SQLi Injection | 1 | 0 |
| NoSQL Injection | 3 | 2 |
| SSTi | 1 | 1 |
| Total Number of Vulnerabilities | 7 | |
| Scanner | FN | TP | FP |
|---|---|---|---|
| ZAP | 6 | 1 | 0 |
| Burp Suite | 7 | 0 | 0 |
| Vega | 7 | 0 | 0 |
| Skipfish | 7 | 0 | 0 |
| Wapiti | 7 | 0 | 0 |
| Scanner | FN | TP | FP |
|---|---|---|---|
| ZAP | 6 | 1 | 0 |
| Burp Suite | 6 | 1 | 0 |
| Vega | 7 | 0 | 0 |
| Skipfish | 7 | 0 | 0 |
| Wapiti | 7 | 0 | 0 |
| Scanner | FN | TP | FP |
|---|---|---|---|
| ZAP | 5 | 2 | 0 |
| Burp Suite | 7 | 0 | 0 |
| Vega | 7 | 0 | 0 |
| Skipfish | - | - | - |
| Wapiti | - | - | - |
| Scanner | FN | TP | FP |
|---|---|---|---|
| ZAP | 5 | 2 | 0 |
| Burp Suite | 5 | 2 | 0 |
| Vega | 7 | 0 | 0 |
| Skipfish | - | - | - |
| Wapiti | - | - | - |
| Burp Suite | ZAP | Vega | Skipfish | Wapiti | |
|---|---|---|---|---|---|
| Blind SQLi | ❍ | ● | ❍ | ❍ | ❍ |
| Union-based SQLi | ❍ | ❍ | ❍ | ❍ | ❍ |
| SQLi | ● | ● | ❍ | ❍ | ❍ |
| NoSQL | ◗ | ❍ | ❍ | ❍ | ❍ |
| SSTi | ❍ | ❍ | ❍ | ❍ | ❍ |
| Mode | Scanner | Precision% | Recall% | F-Measure% |
|---|---|---|---|---|
| Mode 1 | ZAP | 100% | 14% | 25% |
| Burp Suite Pro | 0% | 0% | 0% | |
| Vega | 0% | 0% | 0% | |
| Skipfish | 0% | 0% | 0% | |
| Wapiti | 0% | 0% | 0% | |
| Mode 2 | ZAP | 100% | 14% | 25% |
| Burp Suite Pro | 100% | 14% | 25% | |
| Vega | 0% | 0% | 0% | |
| Skipfish | 0% | 0% | 0% | |
| Wapiti | 0% | 0% | 0% | |
| Mode 3 | ZAP | 100% | 29% | 44% |
| Burp Suite Pro | 0% | 0% | 0% | |
| Vega | - | - | - | |
| Skipfish | - | - | - | |
| Wapiti | - | - | - | |
| Mode 4 | ZAP | 100% | 29% | 44% |
| Burp Suite Pro | 100% | 29% | 44% | |
| Vega | - | - | - | |
| Skipfish | - | - | - | |
| Wapiti | - | - | - |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Althunayyan, M.; Saxena, N.; Li, S.; Gope, P. Evaluation of Black-Box Web Application Security Scanners in Detecting Injection Vulnerabilities. Electronics 2022, 11, 2049. https://doi.org/10.3390/electronics11132049
Althunayyan M, Saxena N, Li S, Gope P. Evaluation of Black-Box Web Application Security Scanners in Detecting Injection Vulnerabilities. Electronics. 2022; 11(13):2049. https://doi.org/10.3390/electronics11132049
Chicago/Turabian StyleAlthunayyan, Muzun, Neetesh Saxena, Shancang Li, and Prosanta Gope. 2022. "Evaluation of Black-Box Web Application Security Scanners in Detecting Injection Vulnerabilities" Electronics 11, no. 13: 2049. https://doi.org/10.3390/electronics11132049
APA StyleAlthunayyan, M., Saxena, N., Li, S., & Gope, P. (2022). Evaluation of Black-Box Web Application Security Scanners in Detecting Injection Vulnerabilities. Electronics, 11(13), 2049. https://doi.org/10.3390/electronics11132049








