Secure and Anonymous Voting D-App with IoT Embedded Device Using Blockchain Technology
Abstract
:1. Introduction
1.1. Main Problem
- Anonymity/Privacy—the vote is not associated with any person;
- Accuracy—the vote is not able to be modified;
- Transparency/Individual and universal verifiability—any entity can verify that their vote was received and counted properly;
- Eligibility—only eligible voters can cast a vote;
- Fairness—vote results should be available only when voting session is closed.
1.2. Our Contribution
2. Related Work
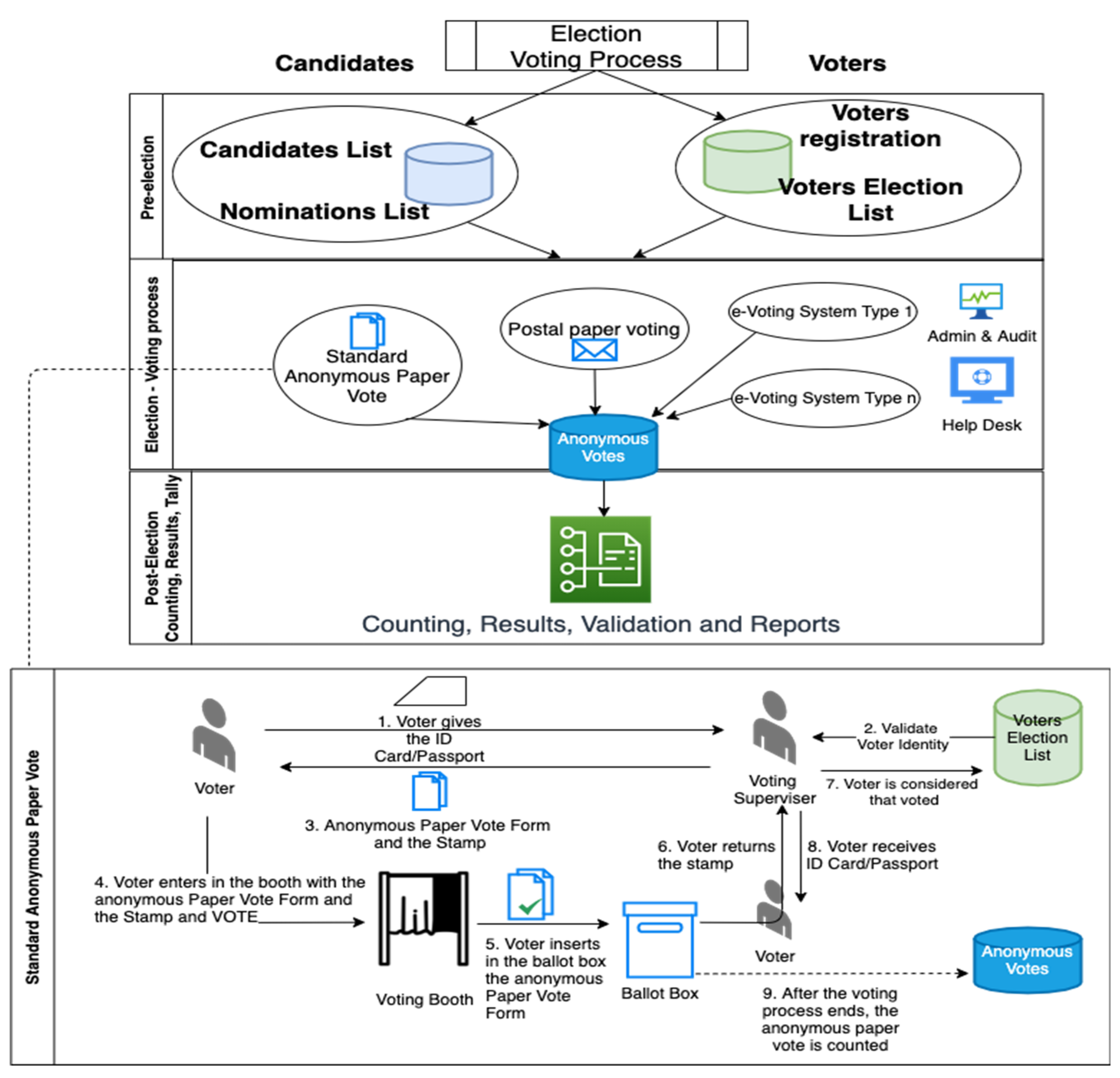
3. Methods and Techniques in Voting Systems
- Paper-based electronic voting systems are inspired by the standard anonymous paper vote, which is used as a system where votes are cast and counted by hand, using paper ballots. With the progress of automatic data acquisition (see QR codes) and electronic tabulation, these systems handle paper cards or sheets that are filled by hand but counted electronically.
- A direct-recording electronic (DRE) voting machine is an alternative that records votes as ballot results activated by the voters (buttons or a touchscreen); processes data with software applications; and records the voting data structures and ballot files in the memory components.
- A public network DRE (direct-recording electronic)/online/Internet voting system is an election system that uses electronic ballots and transmits the vote data from the polling place/office to another location (e.g., Central Election Authority) over a public network. These voting systems may also entail Internet, telephone/mobile equipment (ME), or embedded/IoT device voting. In the case of usage of polling locations/places/offices, the vote information may be sent as individual ballots as they are cast, periodically as batches of ballots throughout the election day, or as one batch at the close of voting. In the case of Internet voting, the voter may use his/her own location or may use the standard voting booths at polling locations using Internet-connected voting systems. For instance, at local and parliament elections in Estonia, most Estonian citizens carry a national identity card (e.g., Java Card smart card), and they vote with these cards. All a voter needs is a computer/tablet, an electronic card reader, and their ID card and its PIN, and they can vote from anywhere in the world. Estonian electronic votes are casted during the days of advance voting. On the election day itself, people go to the polling locations/offices/stations and fill in paper ballots.
- The voter enters in the precinct of the election office, and he/she presents the ID card or passport to the voting supervisor in the assigned room.
- The voting supervisor checks the voter identity and connects to the central database with the list of registered voters for voter validation and to avoid double/multiple voting.
- The voter supervisor gives the stamp and anonymous paper vote form to the voter.
- The voter enters in the booth with the anonymous paper vote form and the stamp to vote.
- The voter exit from the booth and fold the anonymous paper vote form and inserts it into the ballot box.
- The voter returns the used stamp to the voting supervisor.
- The voting supervisor updates the list of registered voters database with the new status of the voter (e.g., vote performed); from this moment, the same voter cannot vote anymore in the same election process.
- The voter receives back the ID card or passport.
- At the end of the day, the ballot box is opened by the voting supervisors and the vote forms are counted according to the law and regulations. The data are sent to the Central Election Authority along with the official minutes and reports.
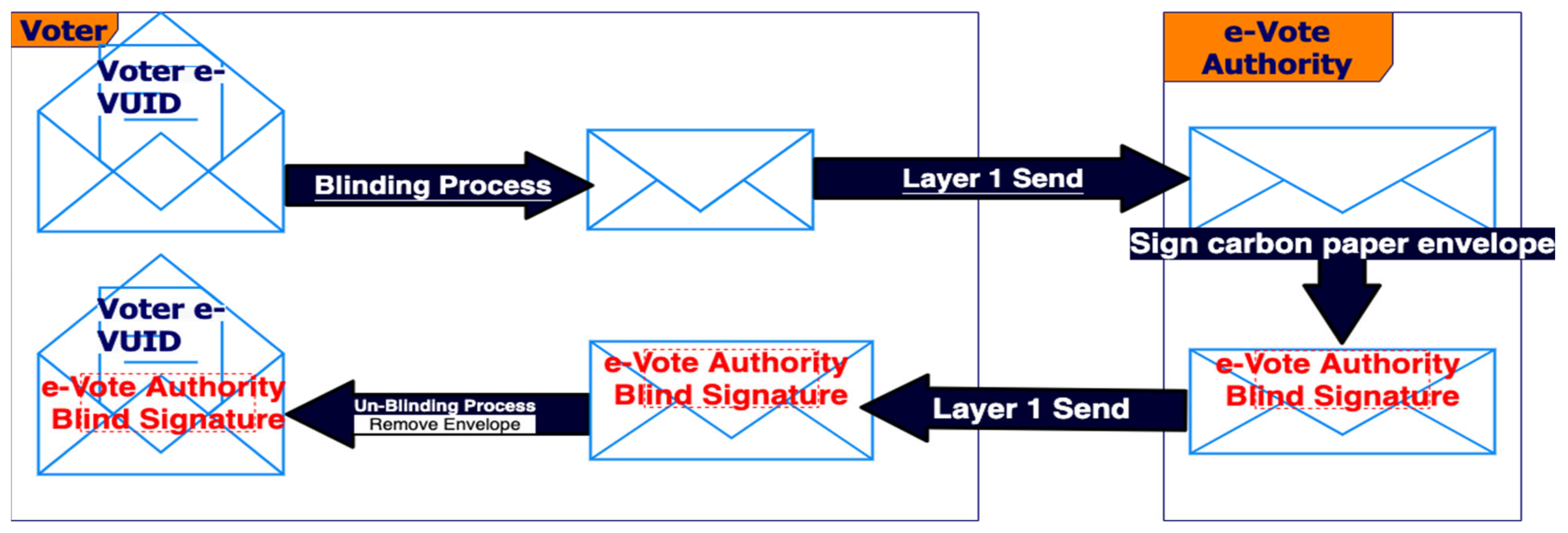
- The voter uses an IoT/embedded or mobile application in the first layer of e-VoteD-App issued/published by the Central Election Authority. Without any anonymity and presenting the ID card or passport in the app, the user triggers the generation of the “stamp”, a unique number, as a hash blind-signed by Central Election Authority e-Vote Unique Identifiers (e-VUIDs).
- The Central Election Authority back-end checks the voter identity and connects to the central database (e.g., via secure REST API and microservices) with the list of registered voters for voter validation and to avoid double/multiple voting.
- The Central Election Authority back-end/cloud apps give the digitally blind-signed “stamp” to the voter application.
- The voter enters in the second layer (blockchain layer) of the e-VoteD-App with the anonymous “Stamp” to vote. The “stamp” may be exchanged between the voters to increase anonymity of the system.
- The voter performs the vote in the second layer of the e-VoteD-App as a blockchain transaction according to a smart contract (partially equivalent to a paper voting form) within a fully anonymous blockchain platform (e.g., Ethereum).
- Automatically and anonymously, the “used stamp” is validated and marked as used within layer 1 at the Central Election Authority back-end/cloud apps.
- The Central Election Authority back-end/cloud apps update the list of registered voters database with the new status of the “stamp” (e.g., “stamp”/e-VUID used); from this moment, any voter cannot vote anymore on the same election process with the same stamp.
- The layer 2 blockchain decentralized application disables the possibility to reuse the “stamp”/e-VUID in the blockchain transaction according to the smart contract.
- At the end of the day, the “ballot box” (blockchain hyperledger) is opened by the Central Election Authority layer 2 blockchain decentralized application, to have access to all blockchain transactions for the electronic vote according to the smart contract. The vote transactions are validated against anonymous e-VUIDs and they are counted according to the modified law and regulations. The data are sent to the Central Election Authority along with the official minutes and reports.
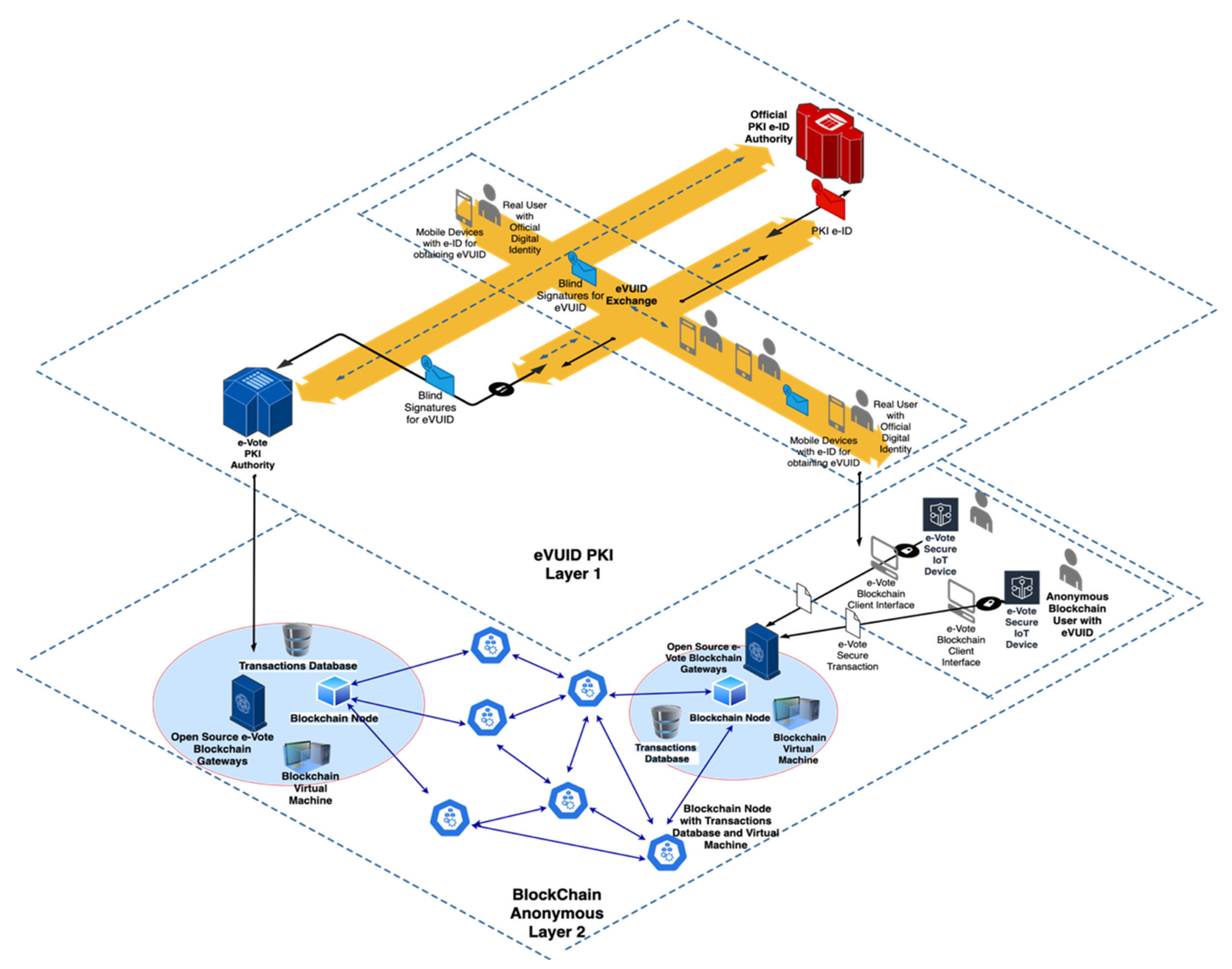
4. Architecture and Cryptographic Schemes of e-VoteD-App
- ▪
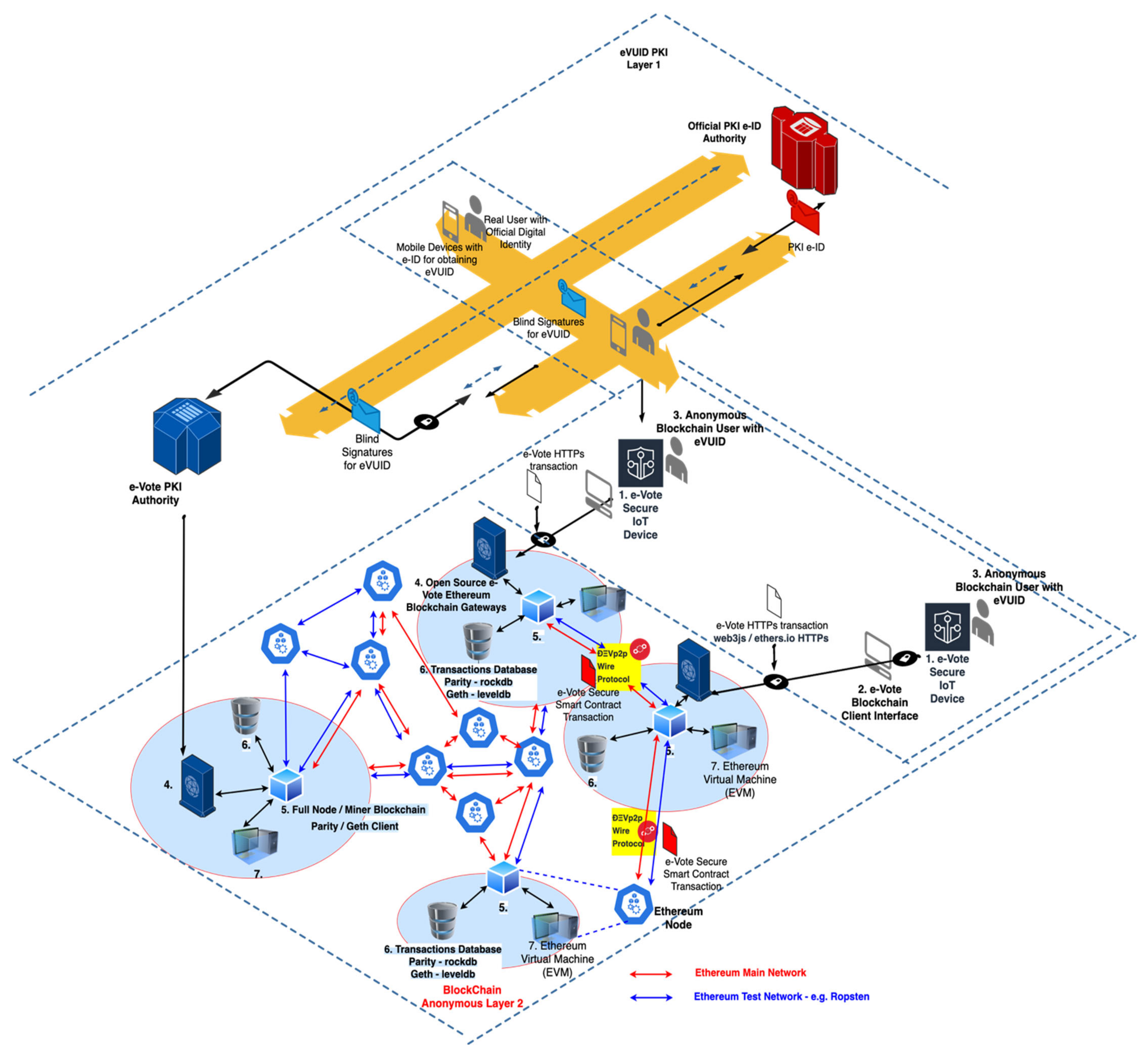
- Layer 1 (Top) is responsible for voters’ generation of the e-VUIDs (e-Vote Unique Identifiers) necessary for an anonymous ballot process. It is based on the blind signatures, and mainly, the voters generate 32 bytes VUID and obtain the blind signatures (RSA 2048 bits) from the e-vote authority.
- ▪
- Layer 2 (Bottom) is fully based on blockchain technology, and the users from the first layer use e-VUIDs in an anonymous and secure manner.
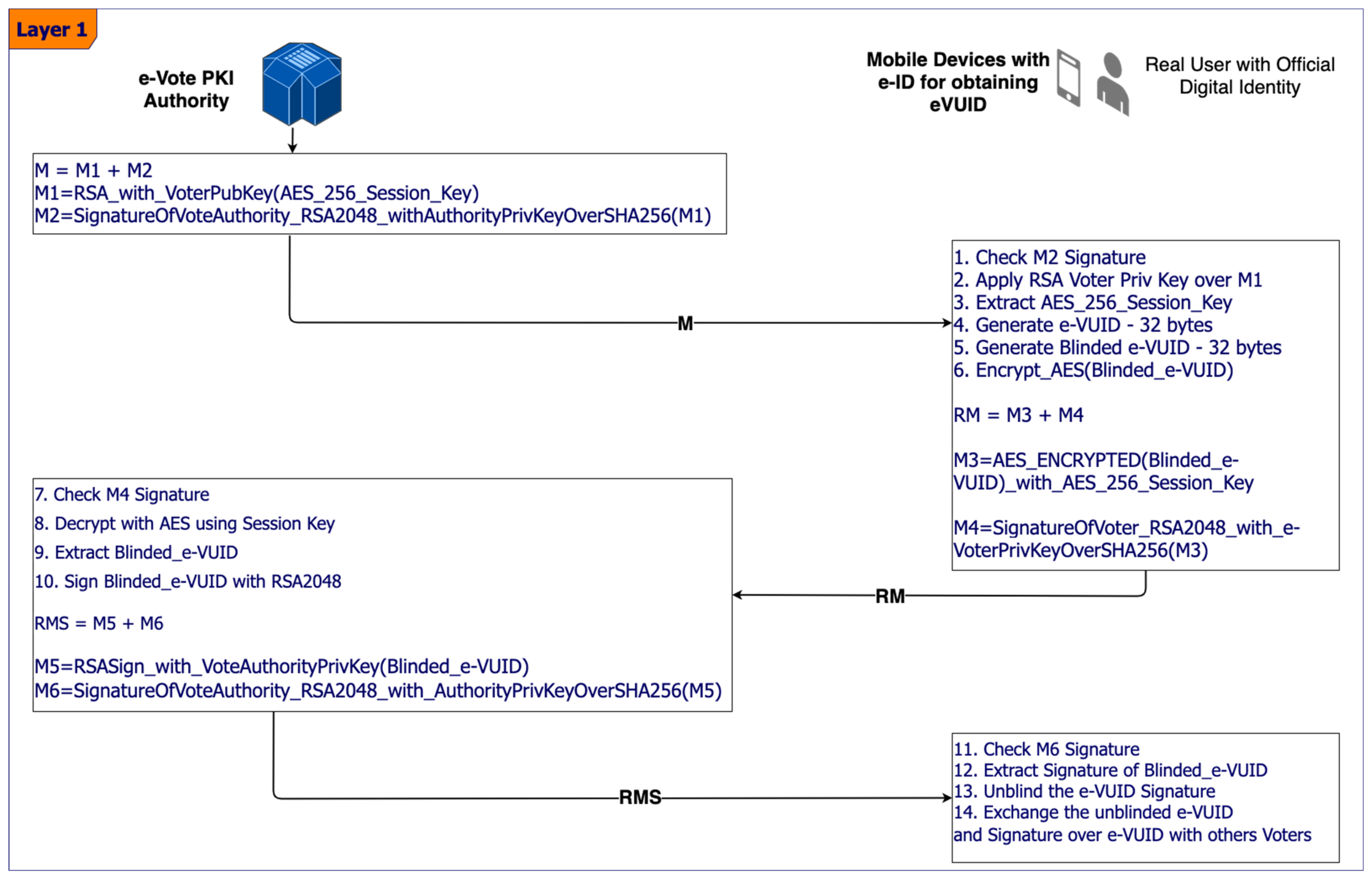
4.1. First Layer of the Architecture for Anonymity in the e-VoteD-App Solution
- Sender V (voter) chooses a blinding factor k (with gcd(k, n) = 1), as a random number between 1 and n. Then, the message M (e-vote UID or blockchain address) is blinded by computing (e = exponent of the public key of A—Authority for the e-vote and n = public modulus of A):
- The receiver A signs T (d = exponent of the secret key of receiver A):
- The sender V receives Td and unblinds it by computing:
- The user V will “blind” this message with the random k = 3 (with condition gcd (3, 14) = 1 and the modular multiplicative inverse of 3, which is ) => the “blinded” value: ; therefore, T obtained is T = 10.
- The e-vote solution authority (user A) receives T = 10 and will never know the real message M = 2. The authority A will apply the RSA private key —(Td) = 12.
- When the voter V receives the signature of the e-vote solution authority, then V will extract from the signed T the unblinded signature by computing: .
- ▪
- As validation, the voter sees if ? It is true, therefore, that it is as if we would have sent the value M = 2 without any blinding to the user A—the e-voting authority—in order to sign the user V message with A’s RSA private key.
4.2. Second Layer of the Architecture for the e-Voting Solution Using Blockchain
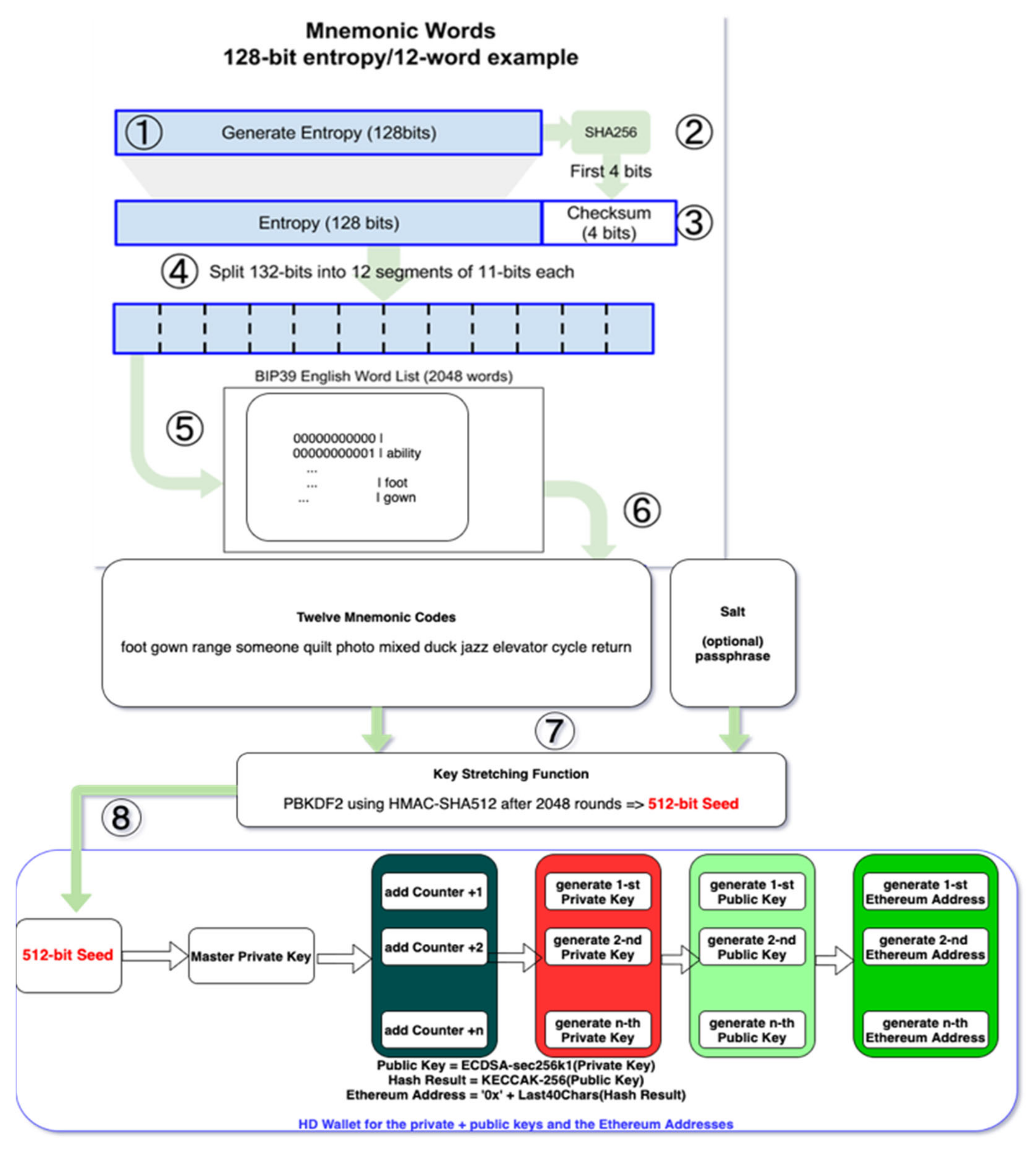
- The user/system generates the entropy from fingers movement/tapping on the screen or buttons, system time, etc., as a number of 128 bits—step 1;
- SHA-256 is applied to the entropy, and the first 4 bits from the result are concatenated with initial entropy number—step 2 and 3;
- The 132-bits number is split into 12 segments of 11 bits each—step 4;
- According to BIP39 English Word List standard, the twelve mnemonic codes are extracted, and the end-user must store them securely if the (IoT) device is destroyed—step 5;
- These twelve codes (words) together with a Salt, which optionally may be controlled by a passphrase, are the input for the Key Stretching Function—step 6;
- The Key Stretching Function is a PBKDF2 (Password-Based Key Derivation Function) using HMAC-SHA512 (Hash-based Message Authentication Code with Secure Hash Algorithm and output on 512 bits). After 2048 rounds a 512-bits seed is obtained—step 7;
- The 512-bits seed is the input for the Master Private Key. If the HD wallet stores n Ethereum addresses, then it will store n private numbers and public keys. For each Ethereum address the HD wallet generates from the master key in a deterministic way the n private keys by adding a counter—step 8;
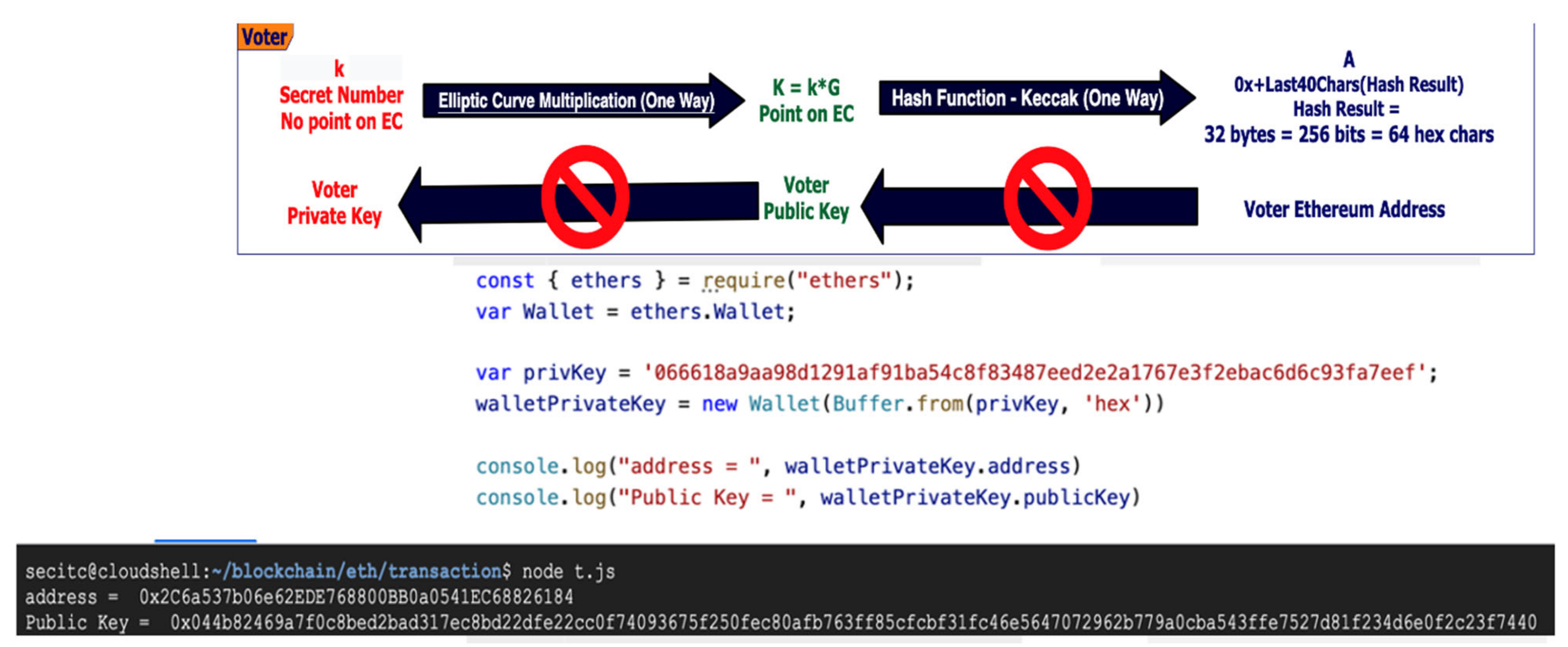
- For each private key (number), a public key on the elliptic curve secp256k1 is generated. From each public key, an Ethereum address for the e-vote process is generated, as shown in Figure 6.
- Contract Accounts—controlled by their contract code.
- ME—Layer 1: Mobile Equipment of the voters for sharing the e-vote tokens, to have a token exchange protocol based on blind electronic signatures—see Figure 3 and Equations (1)–(3).
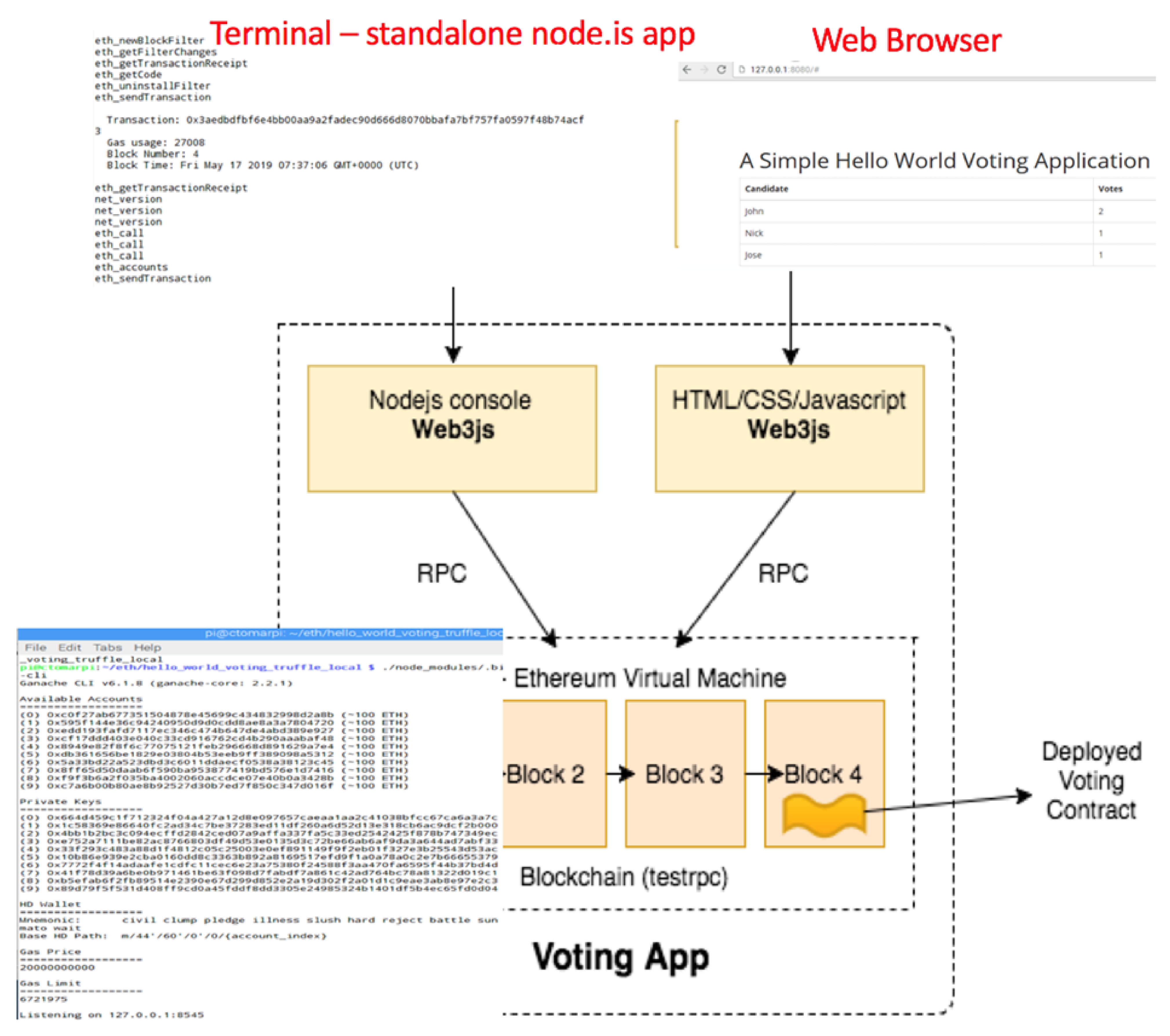
- IoTeD—Layer 2: IoT Embedded Device of the voters, which connects to the Ethereum Virtual Machine via Ethereum gateway and runs HD (Hierarchically Deterministic) wallet for e-voting process—see Annex A for the mathematical formalism.
- PrivBN—Layer 2: Private Blockchain Network:
- ○
- Ethereum Virtual Machines linked to nodes and databases.
- ○
- HD—Hierarchically Deterministic wallets.
- ○
- Ethereum light-weight nodes—Mobile and IoT embedded devices.
- ○
- Full Ethereum nodes—servers and e-voting tokens validation platform.
- e-VUIDVP—Layer 1: The electronic Voting UID Validation Platform, which checks the e-voting tokens validity and is a full node within the private Ethereum network.
- e-Vote secure IoT device with a secure element, which runs the cryptographic functions for the ECDSA and securely stores the keys.
- e-Vote blockchain client interface, which is a browser (e.g., Chrome, Firefox, Edge, Opera, etc.) extension/application that natively connects to the first component.
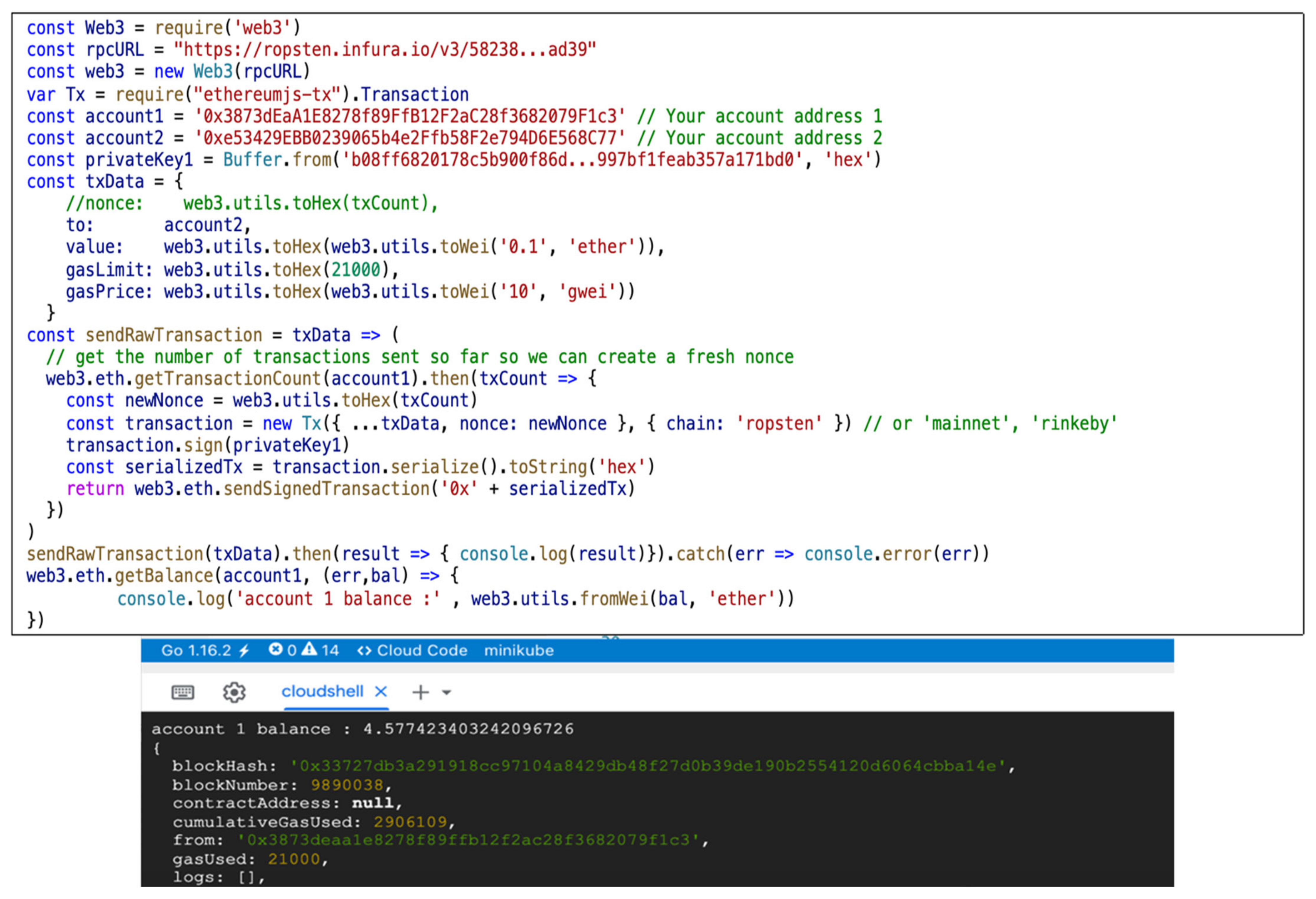
- The voter who acts anonymously in the blockchain but presents a valid e-VUID blindly signed by the e-Vote Authority. In addition, the voter operates the first and second component to create the proper anonymous vote according to the smart contract. The vote is a special transaction that will be processed by the EVM and replicated in all blockchain nodes. Because the voter may not have the required hardware to run a full Ethereum node, an open-source library such as web3js or ethers.io can be used in order to submit the transactions to the 4-th component.
- Open-source e-vote Ethereum blockchain gateway. For the PoC, the authors used infura.io gateway, but this is not open-source, although is free of usage with some certain limitations. This component must be open-source to avoid any concern regarding malicious behavior. The component is responsible for receiving the transactions via HTTPs interface but fully cooperating and running a full Ethereum node including the communication with the EVM.
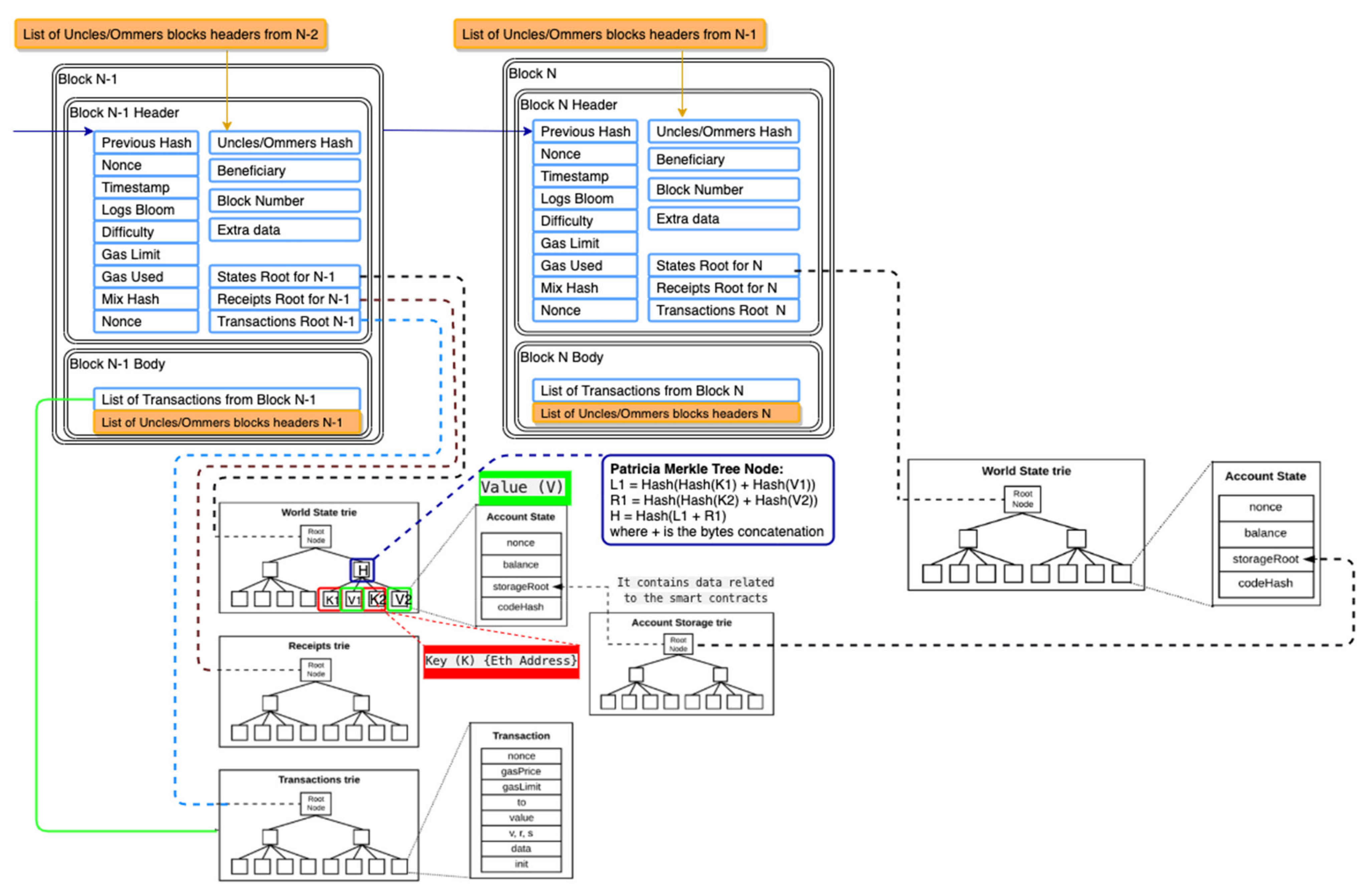
- The node is running a software Ethereum client such as Parity or Geth. The main Ethereum clients use two different database software solutions to store their tries. Parity, which is Ethereum’s Rust client, uses rocksdb, whereas the Geth client and Ethereum’s Go, C++ and Python clients all use leveldb. Each full-node client (Parity or Geth) manages the transactions, the state machine, and execution of the EVM—Ethereum Virtual Machine—for each transaction and contract by executing them into EVM.
- Transaction database stores all transactions and is replicated by each node client (component 5) after Proof of Work consensus across the network using ÐΞVp2p Wire Protocol. As mentioned before, the node client Parity uses rocksdb, and Geth uses leveldb.
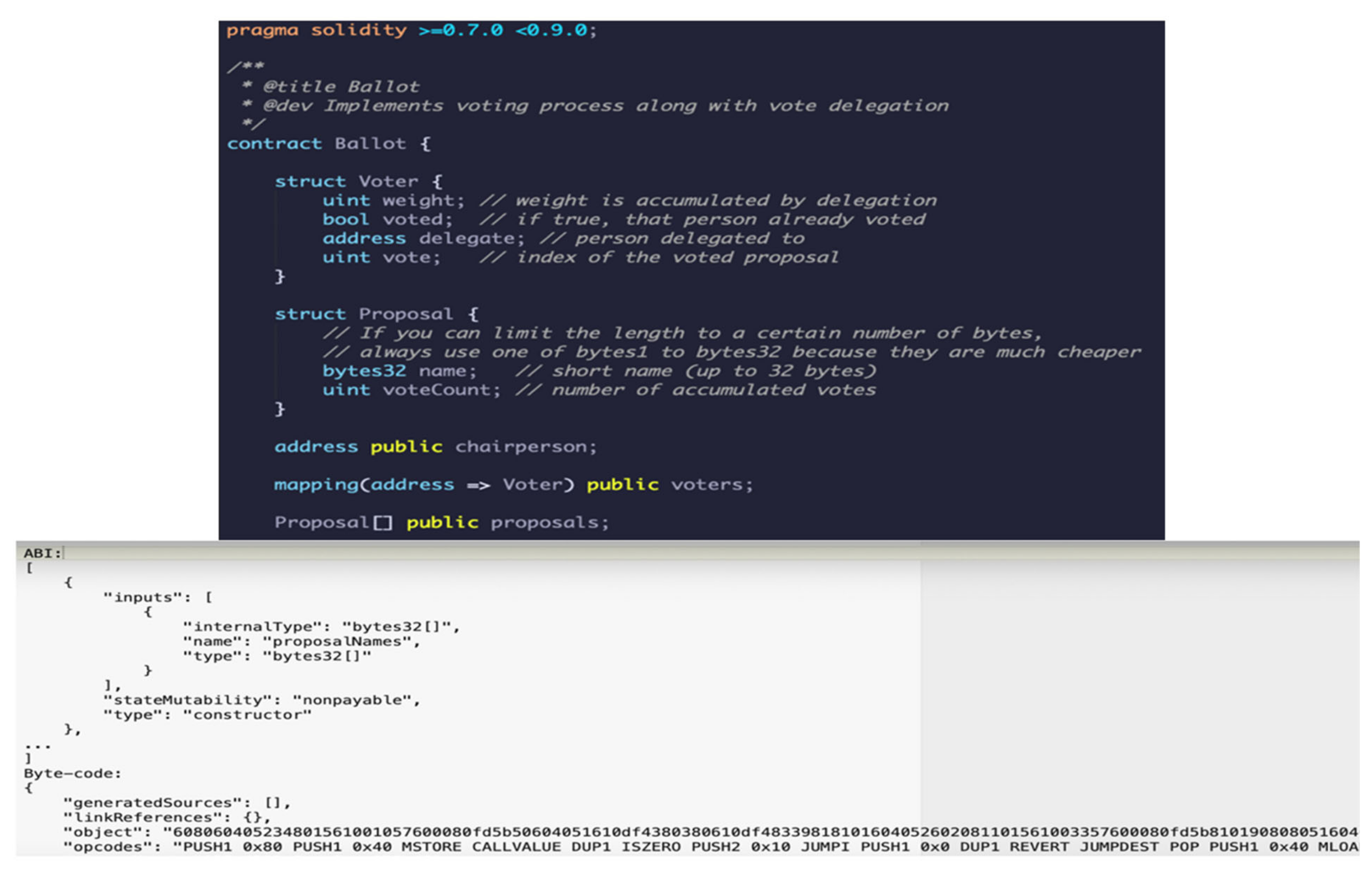
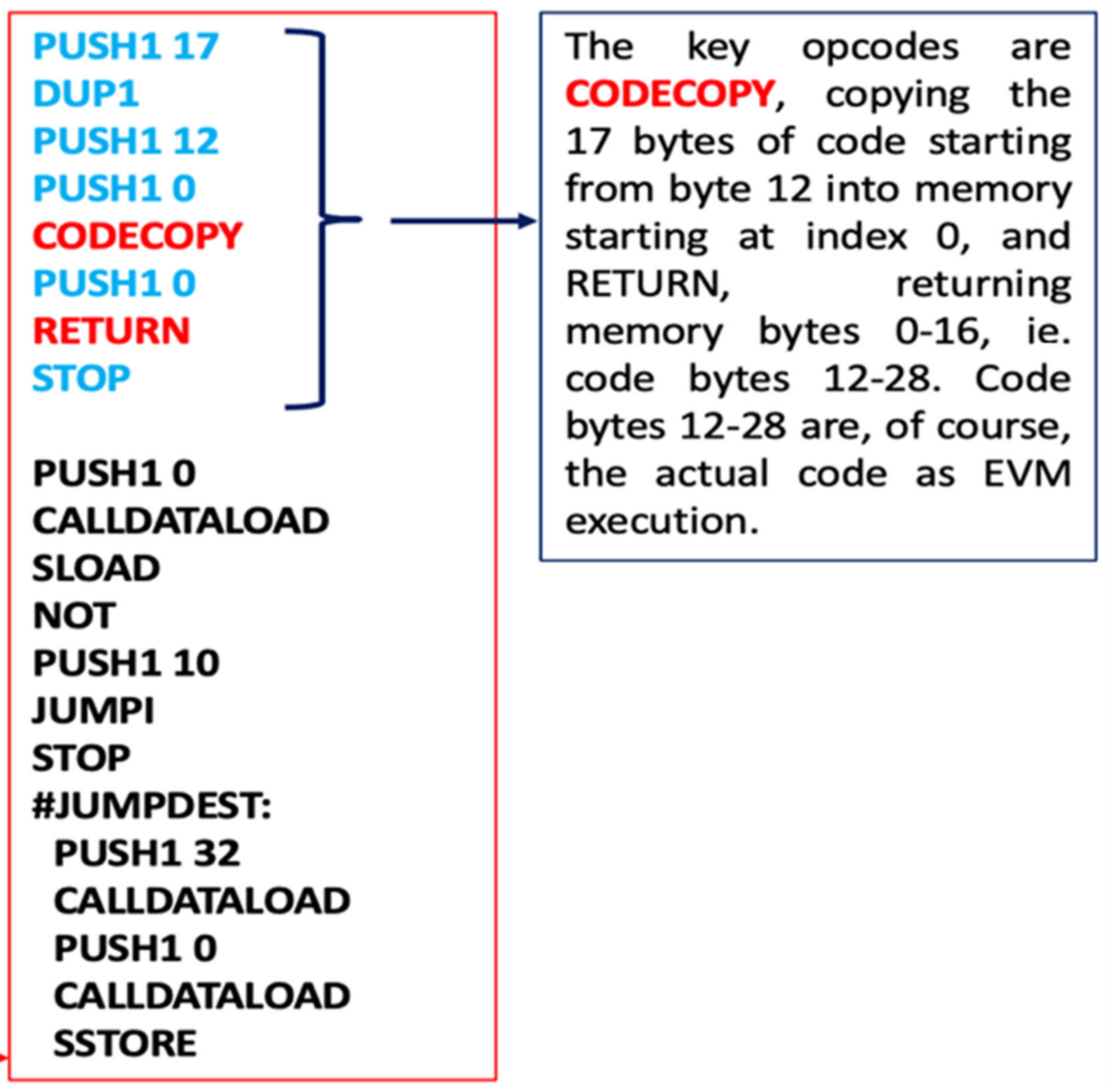
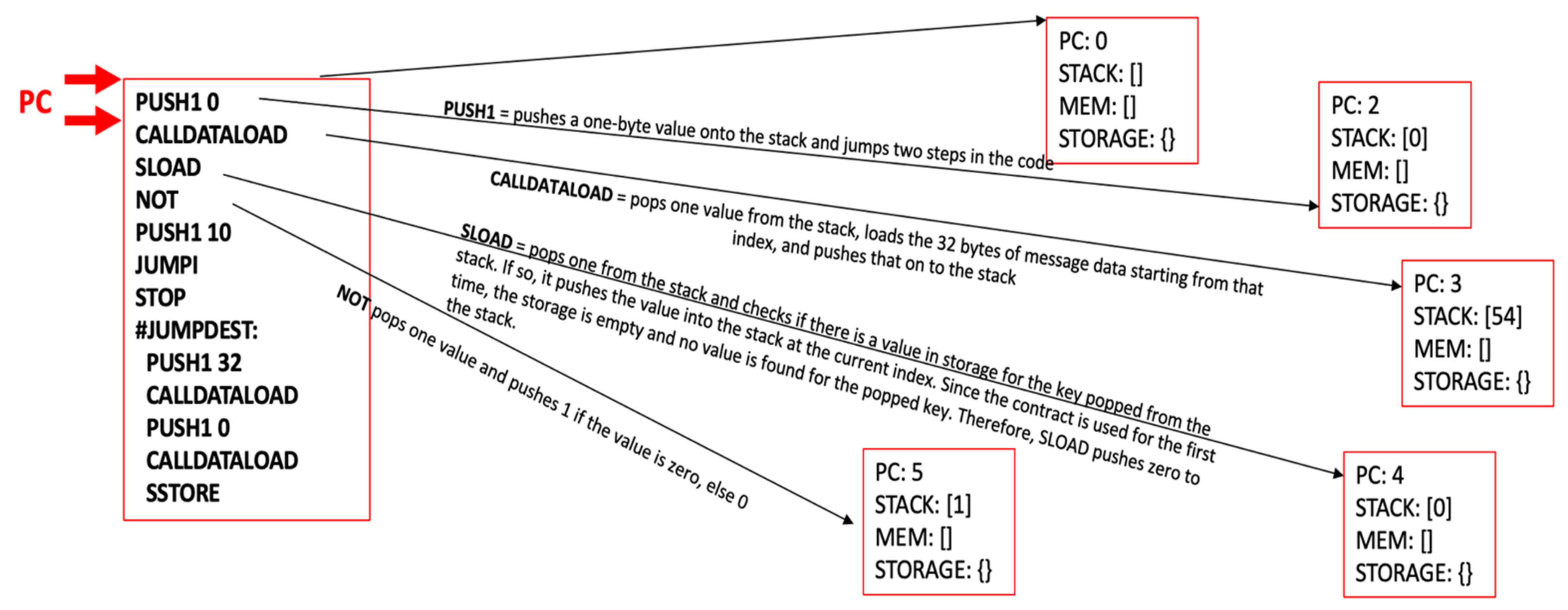
- EVM—Ethereum Virtual Machine—executes the bytecode produced from the smart contracts written in Solidity or Vyper. The authors used a Solidity smart contract for the anonymous e-vote process.
- Type 1: Transactions for transferring a value between two Ethereum addresses—EOAs (e.g, change the sender and receiver account balances)
- Type 2: Transactions for deploying a contract (e.g., creating an account, the contract account is an Ethereum address for the e-Vote smart contract)
- Type 3: Transactions for sending a message call to a contract (e.g., setting a value as vote in the smart contract by sending a message call that executes a setter method)
- Acceptable usage of the EVM includes running business logic (control structures as branching—if-then-else) and verifying signatures and other cryptographic operations;
- Unacceptable usage includes using the EVM as a Message-Oriented Middleware, e-mail or text messaging system, artificial intelligence genetic algorithms, graph analysis, or machine learning.
- For each transaction there is a price quota associated, GASPRICE, and a transaction value, STARTGAS;
- The STARTGAS is the number of units assigned to the transaction, and the GASPRICE represents the fee paid for the transaction per each unit;
- When sending a transaction, the first operation during evaluation is to subtract STARTGAS multiplied with the GASPRICE Wei in addition to the transaction’s value from the sender’s account balance. The GASPRICE is set by the sender of the transaction, but it can be refused by miners if GASPRICE value is too low.
5. Implementation Issues and Results
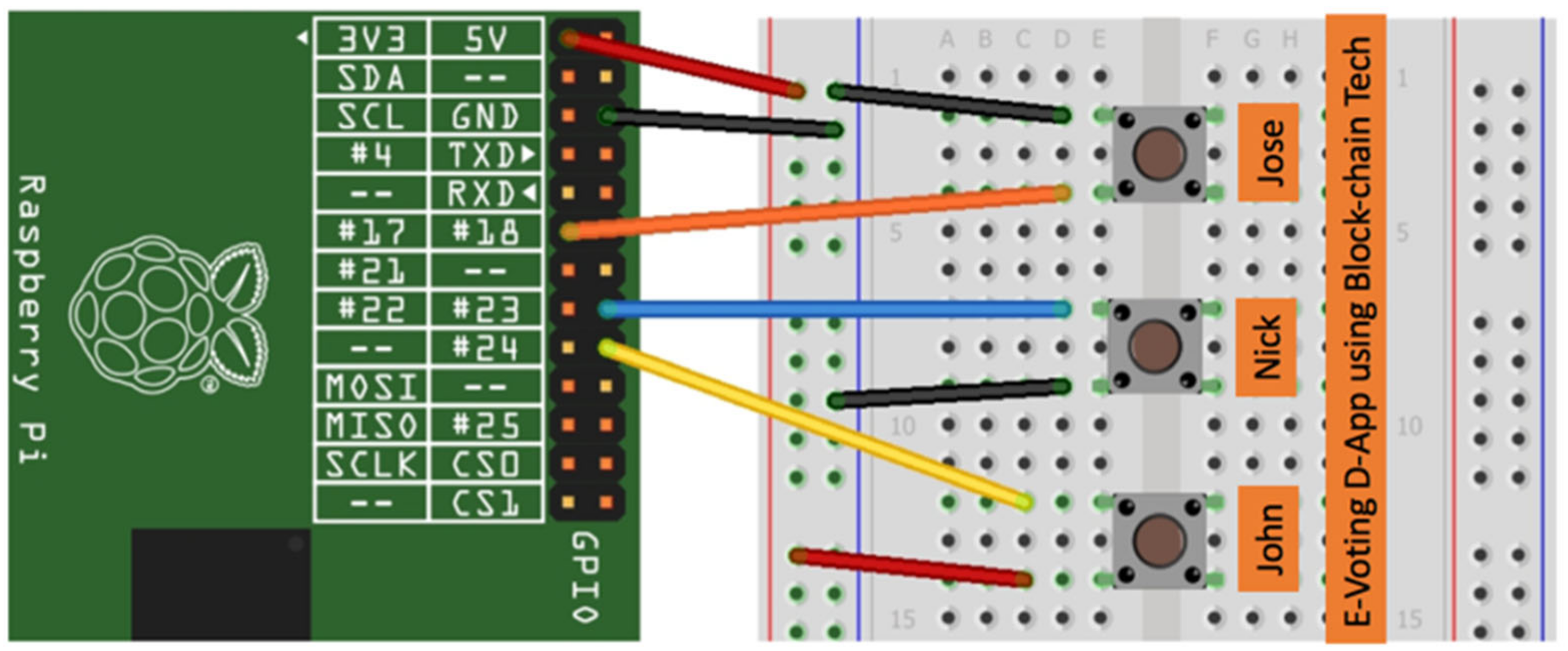
- The IoT device featured buttons in order to perform the vote —please see Figure 15;
- Raspberry PI or i.MX 7ULP EVK board~50 USD/200 USD
- Breadboard for Buttons/LCD~10 USD
- Buttons~5 USD or Display LCD-3.5″ 320 × 480~40 USD
6. Discussion and Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- Chaum, D. Blind Signatures for Untraceable Payments. In Advances in Cryptology; Springer: Boston, MA, USA, 1983; pp. 199–203. [Google Scholar]
- Hardwick, F.S.; Gioulis, A.; Akram, R.N.; Markantonakis, K. E-Voting with Blockchain: An E-Voting Protocol with Decentralisation and Voter Privacy. In Proceedings of the 2018 IEEE International Conference on Internet of Things (iThings) and IEEE Green Computing and Communications (GreenCom) and IEEE Cyber, Physical and Social Computing (CPSCom) and IEEE Smart Data (SmartData), Halifax, NS, Canada, 30 July–3 August 2018. [Google Scholar]
- Tso, R.; Liu, Z.-Y.; Hsiao, J.-H. Distributed E-Voting and E-Bidding Systems Based on Smart Contract. Electronics 2019, 8, 422. [Google Scholar] [CrossRef] [Green Version]
- Devi, L.; Kedar, D.; Malik, S.K.; Dubey, K. Decentralized Voting Application. Int. J. Eng. Sci. Comput. 2018, 8, 19117–19119. [Google Scholar]
- Khan, K.M.; Arshad, J.; Khan, M.M. Secure Digital Voting System based on Blockchain Technology. Int. J. Electron. Gov. Res. 2018, 14, 53–62. [Google Scholar] [CrossRef]
- Rakhe, R.; Kale, R.; Bisht, P.; Balbudhe, K.S. E-Voting System using Blockchain Technology for Distributed Environment. Int. J. Innov. Res. Sci. Eng. Technol. 2019. [Google Scholar] [CrossRef]
- Kim, H.R.; Min, K.; Hong, S.-P. A Study on Ways to Apply the Blockchain-based Online Voting System. Int. J. Control. Autom. 2017, 10, 121–130. [Google Scholar] [CrossRef]
- Arun, V.; Dutta, A.; Rajeev, S.; Mathew, R.V. E-Voting using a Decentralized Ethereum Application. Int. J. Eng. Adv. Technol. 2019, 8, 830–833. [Google Scholar]
- Boucher, P. What if Blockchain Technology Revolutionised Voting? September 2016. Available online: https://www.europarl.europa.eu/RegData/etudes/ATAG/2016/581918/EPRS_ATA(2016)581918_EN.pdf (accessed on 16 December 2021).
- McCorry, P.; Shahandashti, S.F.; Hao, F. A Smart Contract for Boardroom Voting with Maximum Voter Privacy. In Financial Cryptography and Data Security; Springer International Publishing: Berlin/Heidelberg, Germany, 2017. [Google Scholar]
- Arun, S.S.; Shibani, S.S.; Kamath, V.R.; Raj, D.C.V. Blockchain Enabled E-Voting System. Int. J. Adv. Res. Comput. Commun. Eng. 2019, 8, 77–81. [Google Scholar] [CrossRef]
- Gajek, S.; Lewandowsky, M. Trustless, Censorship-Resilient and Scalable Votings in the Permission-Based Blockchain Model. In Proceedings of the Euro-Par 2020: Parallel Processing Workshops. Euro-Par 2020, Warsaw, Poland, 24−25 August 2020; Lecture Notes in Computer Science. Springer: Berlin/Heidelberg, Germany, 2020. [Google Scholar]
- Wei, C.C.Z.; Wen, C.C. Blockchain-Based Electronic Voting Protocol. Int. J. Inform. Vis. 2018, 2, 336–341. [Google Scholar]
- Chaum, D.L. Untraceable electronic mail, return addresses, and digital pseudonyms. Commun. ACM 1981, 24, 84–90. [Google Scholar] [CrossRef]
- Langer, L.; Jonker, H.; Pieters, W. Anonymity and Verifiability in Voting: Understanding (Un)Linkability. In Proceedings of the Information and Communications Security. ICICS 2010, Barcelona, Spain, 15−17 December 2010; Lecture Notes in Computer Science. Springer: Berlin/Heidelberg, Germany, 2010; Volume 6476, pp. 296–310. [Google Scholar]
- Dreier, J.; Lafourcade, P.; Lakhnech, Y. Vote-Independence: A Powerful Privacy Notion for Voting Protocols. In Proceedings of the Foundations and Practice of Security. FPS 2011, Paris, France, 12−13 May 2011; Lecture Notes in Computer Science. Springer: Berlin/Heidelberg, Germany, 2011; Volume 6888, pp. 164–180. [Google Scholar]
- Essex, A.; Clark, J.; Carback, R.; Popoveniuc, S. Punchscan in Practice: An E2E Election Case Study. In Proceedings of the 2007 IAVoSS Workshop on Trustworthy Elections (WOTE), Ottawa, ON, Canada, 20–21 June 2007. [Google Scholar]
- Lewis, K.M.; Rice, T.W. Voter Turnout in Undergraduate Student Government Elections. Political Sci. Politics 2005, 38, 723–729. [Google Scholar] [CrossRef] [Green Version]
- Thiga, M.; Chebon, V.; Kiptoo, S.; Okumu, E.; Onyango, D. Electronic Voting System for University Student Elections: The Case of Kabarak University, Kenya. In Proceedings of the 2018 IST-Africa Week Conference (IST-Africa), Gaborone, Botswana, 9–11 May 2018. [Google Scholar]
- Murthy, M. Full Stack Hello World Voting Ethereum Dapp Tutorial, Medium. 18 January 2017. Available online: https://medium.com/@mvmurthy/full-stack-hello-world-voting-ethereum-dapp-tutorial-part-1-40d2d0d807c2 (accessed on 16 December 2021).
- Wood, G. A Secure Decentralised Generalised Transaction Ledger, Petersburg Version 41c1837—2021-02-14. 2021. Available online: https://ethereum.github.io/yellowpaper/paper.pdf (accessed on 16 December 2021).
- Antonopoulos, M. Mastering Bitcoin, 2nd ed.; O’Reilly Media, Inc.: Sebastopol, CA, USA, 2017. [Google Scholar]
- Antonopoulos, A.M.; Wood, G. Mastering Ethereum—Building Smart Contracts and Dapps; O’Reilly, Inc.: Sebastopol, CA, USA, 2018. [Google Scholar]
- Konstantinos, C.; Devetsikiotis, M. Blockchains and Smart Contracts for the Internet of Things. IEEE Access 2016, 4, 2292–2303. [Google Scholar]
- Ethereum. Ethereum Whitepaper. 2022. Available online: https://ethereum.org/en/whitepaper/ (accessed on 20 February 2022).
- Ethereum Homestead Documentation. Account Types, Gas, and Transactions. 2016. Available online: https://ethdocs.org/en/latest/contracts-and-transactions/account-types-gas-and-transactions.html (accessed on 17 November 2021).
- Azodolmolky, S.; Perelló, J.; Angelou, M.; Agraz, F.; Velasco, L.; Spadaro, S.; Pointurier, Y.; Francescon, A.; Saradhi, C.V.; Kokkinos, P.; et al. Experimental Demonstration of an Impairment Aware Network Planning and Operation Tool for Transparent/Translucent Optical Networks. J. Lightwave Technol. 2011, 29, 439–448. [Google Scholar] [CrossRef]
- Armando, A.; Basin, D.; Boichut, Y.; Chevalier, Y.; Compagna, L.; Cuellar, J.; Drielsma, P.H.; Heám, P.C.; Kouchnarenko, O.; Mantovani, J.; et al. The AVISPA Tool for the Automated Validation of Internet Security Protocols and Applications. In Proceedings of the International Conference on Computer Aided Verification, Edinburgh, UK, 6–10 July 2005; Lecture Notes in Computer Science. Springer: Berlin/Heidelberg, Germany, 2005; Volume 3576, pp. 281–285. [Google Scholar]
- Armando, A.; Basin, D.A.; Bouallagui, M.; Chevalier, Y.; Compagna, L.; Mödersheim, S.; Rusinowitch, M.; Turuani, M.; Viganò, L.; Vigneron, L. The AVISS Security Protocol Analysis Tool. In Proceedings of the 14th International Conference on Computer Aided Verification, Copenhagen, Denmark, 27–31 July 2002. [Google Scholar]
- Lai, W.; Hsieh, Y.; Hsueh, C.; Wu, J. Date: A decentralized, anonymous, and transparent e-voting system. In Proceedings of the 2018 1st IEEE International Conference on Hot Information-Centric Networking (HotICN), Shenzhen, China, 15–17 August 2018. [Google Scholar]
- Jafar, M.J.A.A.U.; Shukur, Z. Blockchain for Electronic Voting System—Review and Open Research Challenges. Sensors 2021, 21, 5874. [Google Scholar] [CrossRef] [PubMed]
- NIST. Post-Quantum Cryptography PQC. 2021. Available online: https://csrc.nist.gov/projects/post-quantum-cryptography/round-3-submissions (accessed on 22 October 2021).
- NIST. NISTIR 8309 Status Report on the Second Round of the NIST Post-Quantum Cryptography Standardization Process. July 2020. Available online: https://nvlpubs.nist.gov/nistpubs/ir/2020/NIST.IR.8309.pdf (accessed on 24 September 2021).
- Canetti, R.; Goldreich, O.; Halevi, S. The random oracle methodology, revisited. J. ACM 2004, 51, 557–594. [Google Scholar] [CrossRef] [Green Version]
- Iovino, V.; Rial, A.; Rønne, P.B.; Ryan, P.Y.A. Universal Unconditional Verifiability in E-Voting without Trusted Parties. In Proceedings of the 2020 IEEE 33rd Computer Security Foundations Symposium (CSF), Boston, MA, USA, 22–26 June 2020. [Google Scholar]
- Standards for Efficient Cryptography 2 (SEC 2), SEC 2: Recommended Elliptic Curve Domain Parameters, Version 2.0. 27 January 2010. Available online: http://www.secg.org/sec2-v2.pdf (accessed on 16 December 2021).
- Hao, F.; Ryan, P.; Zielinski, P. Anonymous voting by two-round public discussion. IET Inf. Secur. 2008, 4, 62–67. [Google Scholar] [CrossRef] [Green Version]
- Hao, F.; Zielinski, P. A 2-Round Anonymous Veto Protocol. In Security Protocols 2006, LNCS 5087; Christianson, B., Ed.; Springer: Berlin/Heidelberg, Germany, 2009; pp. 202–211. [Google Scholar]
- Hjálmarsson, F.Þ.; Hreiðarsson, G.K.; Hamdaqa, M.; Hjálmtýsson, G. Blockchain-Based E-Voting System. In Proceedings of the 2018 IEEE 11th International Conference on Cloud Computing (CLOUD), San Francisco, CA, USA, 2–7 July 2018. [Google Scholar]
- Ko, T. A guide to developing an Ethereum Decentralized Voting Application, FreeCodeCamp. March 2018. Available online: https://www.freecodecamp.org/news/developing-an-ethereum-decentralized-voting-application-a99de24992d9 (accessed on 24 November 2021).
- Ng, J. Voting on a Blockchain: DApp Demonstration, Medium. 11 May 2019. Available online: https://medium.com/coinmonks/voting-on-a-blockchain-dapp-demonstration-dfb5944a0c9e (accessed on 16 December 2021).



| Field Name | Field Length (Bytes) | Description |
|---|---|---|
| Nonce | Up to 32 bytes | A random number to prevent reply attacks |
| Gas Price | Up to 32 bytes | The price in Wei per “gallon” of gas to record the transaction in each database of the Ethereum nodes |
| Gas Limit | Up to 32 bytes | The maximum “gallons” of gas used for recording the transaction into the database |
| To | 20 bytes | EOA that is receiving ethers or contract address, which is in charge of the reception of the transaction that triggers running the e-vote smart contract in all EVMs of the full nodes. It could be zero for the contract creation. |
| Value | Up to 32 bytes | The value in Wei (subdivision of the Ether) for the transfer. It could be zero for the contract creation. |
| Data | 0 to unlimited | It can contain the ABI/bytecode for the contract execution. |
| V | 1 | Usually, 1 byte is the recovery ID in ECDSA. |
| r | 32 bytes | ECDSA r for the e-Vote signature. |
| s | 32 bytes | ECDSA s for the e-Vote signature. |
| Blockchain | Consensus Algorithm | Transactions per Second | Smart Contract Language | Platform Programming Language | Decentralized |
|---|---|---|---|---|---|
| Ethereum (Go/Parity) | PoW, PoS, and PoA | 15–30 (PoW) and up to 100 k (Ethereum 2.0) | Solidity/Vyper | Go/Rust, JavaScript | Yes |
| Quorum | QuorumChain, IBFT, and Raft-based consensus | Around 100 | Solidity | Go, C, JavaScript | Partially |
| Exonum | Custom-built BFT algorithm | Up to 5000 | Rust | Rust | Yes |
| Hyperledger Fabric | Decoupled in 3 phases: Endorsement, Ordering, Validation | Up to 3000 | Go/JavaScript/Java | Go | Yes |
| Bitcoin | PoW | 4–7 | N/A | C++ | Yes |
| Characteristics/Solutions | e-VoteD-App Proposed Solution (Ethereum) | Follow My Vote (Bitcoin) | Voatz (HyperLedger Fabric) | Polys (Ethereum) | Agora (Custom Blockchain Based on Bitcoin) | Lai, Hsieh [30] (Ethereum) |
|---|---|---|---|---|---|---|
| Anonymity | X (Based on e-VUID and blind signature) | X (Claimed but not described) | X (Claimed, with mix net based on homomorphic crypto, therefore not implemented) | X (Claimed based on blind signatures but not-described) | X (Claimed but not described) | X (Claimed but not implemented) |
| Audit | X | X | X | X | X | - |
| Accuracy | X | X | X | X | X | X |
| Integrity | X | X | X | X | X | - |
| Verifiability by Voter/Transparency | X | X | X | X | X | X |
| Scheme | Device | Chip | EEPROM (KB) | RAM (KB) |
|---|---|---|---|---|
| McEllice (code-based) | SC Chip | 16 bit Infineon SLE76 | 310 | 4.5 |
| NTRU (lattice-based) | FPGA | 32 bit ARM7TDMI | 13.5 | 3.5 |
| Crystals-Kyber (lattice-based) | SC Chip | Infineon SLE76 | <500 | 16 |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Toma, C.; Popa, M.; Boja, C.; Ciurea, C.; Doinea, M. Secure and Anonymous Voting D-App with IoT Embedded Device Using Blockchain Technology. Electronics 2022, 11, 1895. https://doi.org/10.3390/electronics11121895
Toma C, Popa M, Boja C, Ciurea C, Doinea M. Secure and Anonymous Voting D-App with IoT Embedded Device Using Blockchain Technology. Electronics. 2022; 11(12):1895. https://doi.org/10.3390/electronics11121895
Chicago/Turabian StyleToma, Cristian, Marius Popa, Catalin Boja, Cristian Ciurea, and Mihai Doinea. 2022. "Secure and Anonymous Voting D-App with IoT Embedded Device Using Blockchain Technology" Electronics 11, no. 12: 1895. https://doi.org/10.3390/electronics11121895
APA StyleToma, C., Popa, M., Boja, C., Ciurea, C., & Doinea, M. (2022). Secure and Anonymous Voting D-App with IoT Embedded Device Using Blockchain Technology. Electronics, 11(12), 1895. https://doi.org/10.3390/electronics11121895







