SPD-Safe: Secure Administration of Railway Intelligent Transportation Systems
Abstract
1. Introduction
2. Materials and Methods—Related Work
2.1. Management Platfroms and Reasoning Systems
2.2. Intelligent Railway Systems
2.3. Network Layer Protection
3. Administration of IoT Deployments
3.1. Agent Technologies & Middleware Solutions
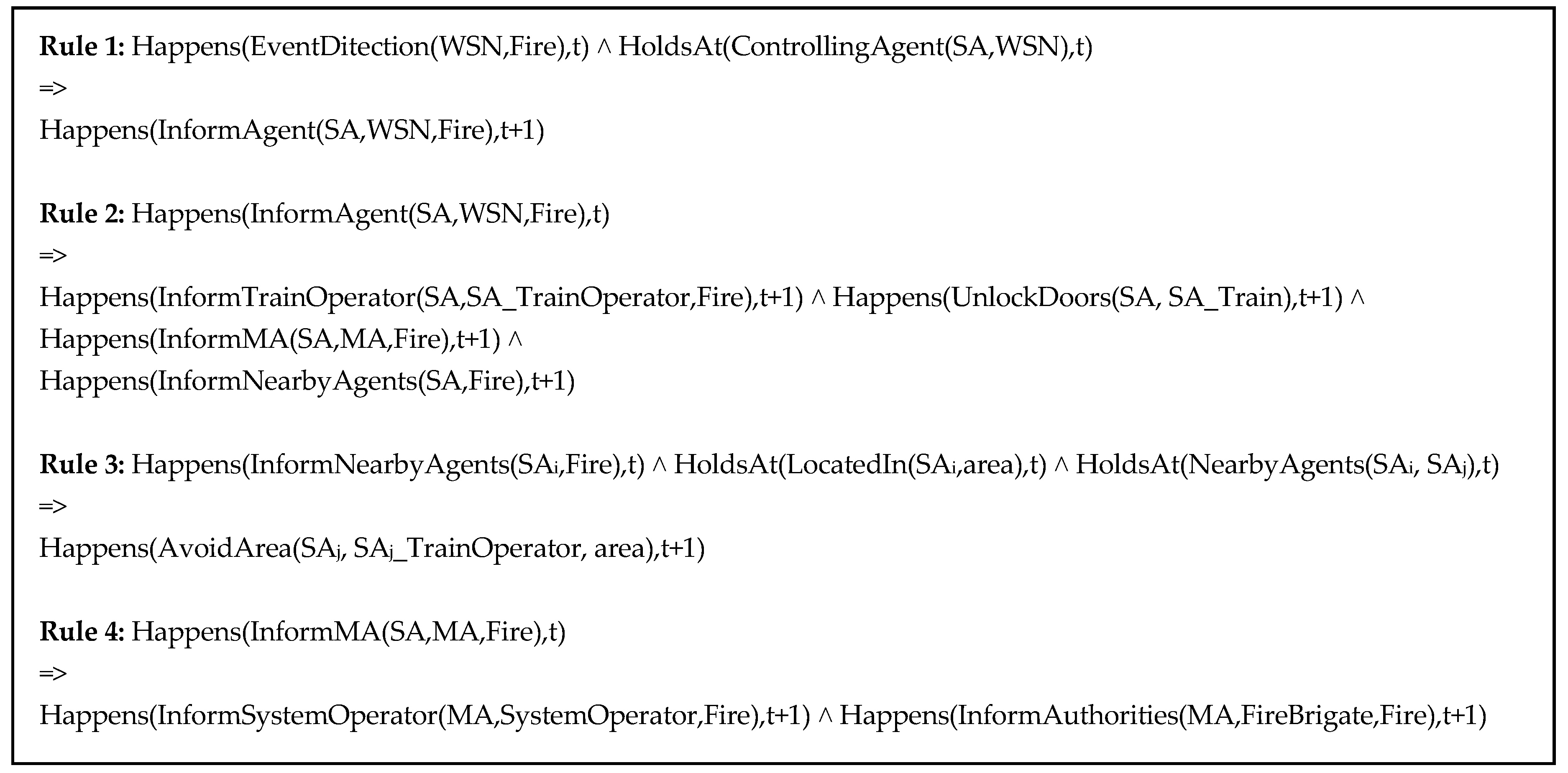
3.2. Reasoning Capabilities & Conflict Resolution
3.3. SPD Measurement
- -
- Required time: The time that it is required to perform a specific attack (e.g., in days or weeks);
- -
- Expertise: The technical skills and knowledge that the attacking group can exhibit (such as copy-cat, advanced, or expert);
- -
- Knowledge of the target: Familiarity with the targeted system and its operation (e.g., public, sensitive, or critical information concerning some subsystems, etc.);
- -
- Window of opportunity: The attacker may require appreciable access to the system in order to exploit a vulnerability and avoid detection;
- -
- Resources: The software, hardware, or other equipment that is necessary to perform an attack (such as specialized or common resources).
3.4. AI Processing & Performance
3.5. Relevant Methodologies for Secure IoT Modeling
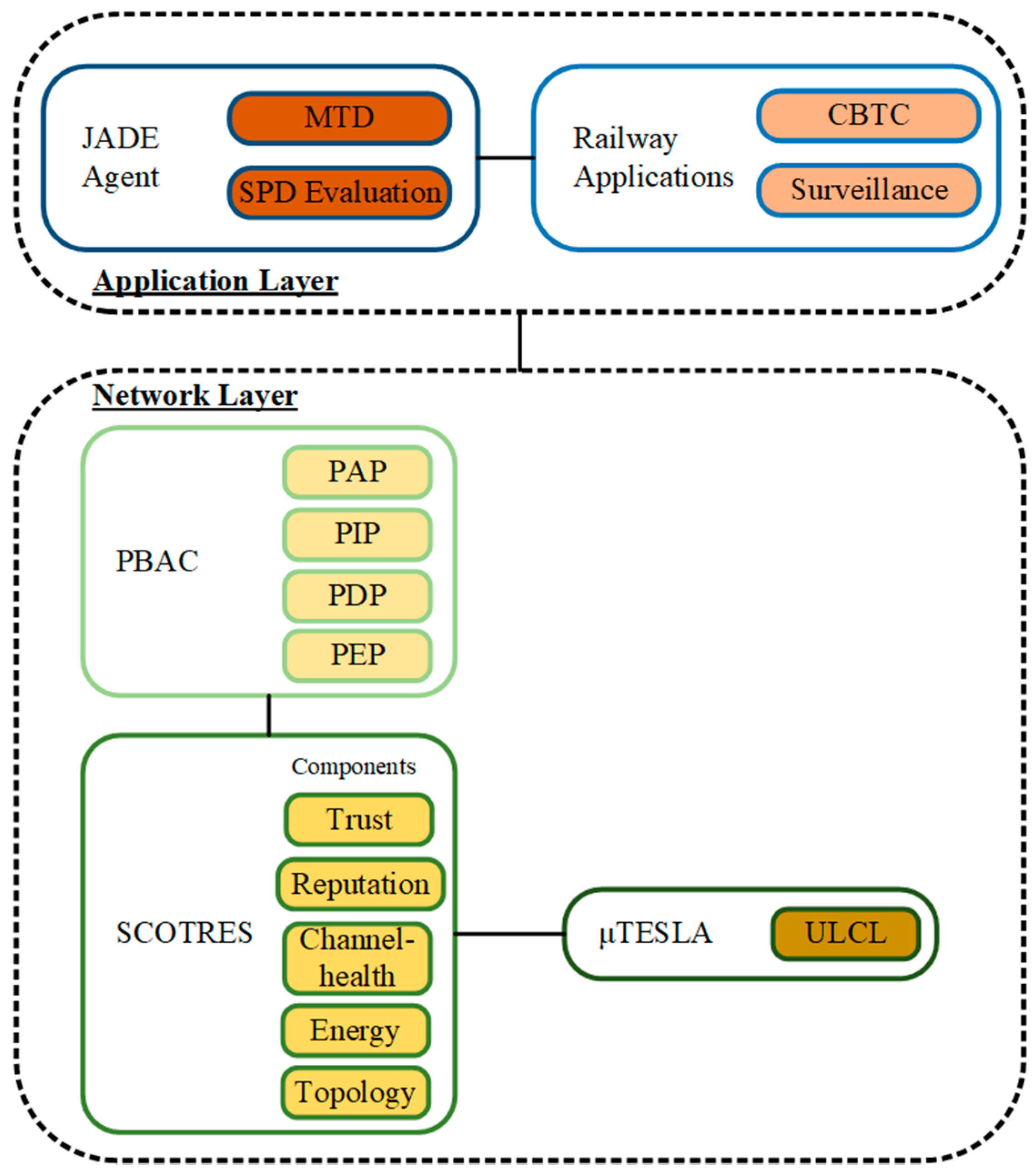
4. Network Layer Security
- The cryptographic service with the Timed Efficient Stream Less Tolerant Authentication protocol (μTESLA) [60], which implements message authentication, confidentiality, and integrity;
- The efficient secure routing service with the Self-Channel Observation Trust and Reputation System (SCOTRES) [62] that safeguards the communication link against ad-hoc routing attacks and network layer vulnerabilities;
- The authorization service with the Policy-Based Access Control framework (PBAC) [42], which offers authorization and access control based on policies.
4.1. Cryptographic Service—μTESLAs
4.2. Secure Routing Service—SCOTRES
4.3. Authorization Service—PBAC
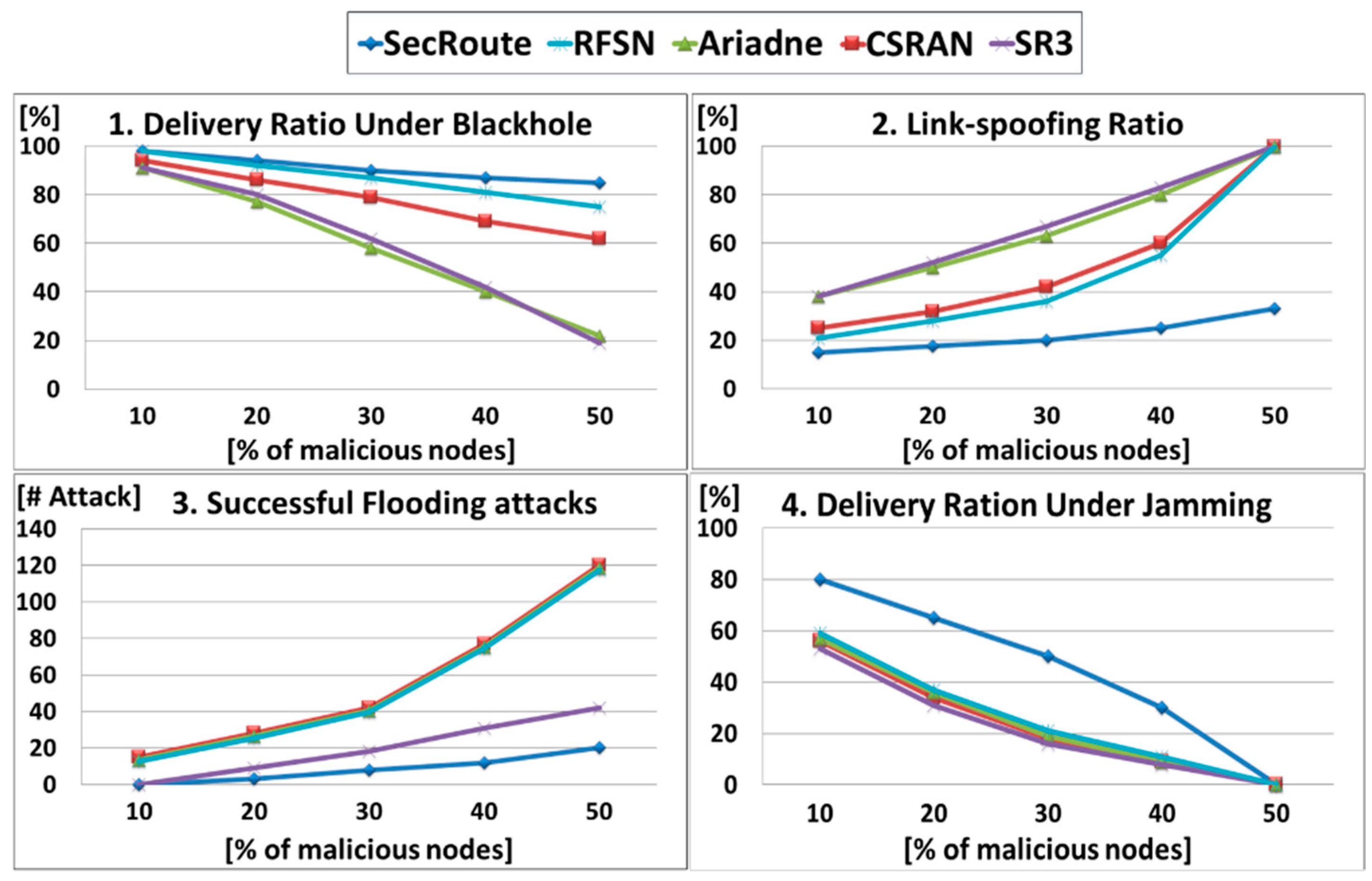
4.4. Performance Evaluation
4.5. Comparison with Other Protocols
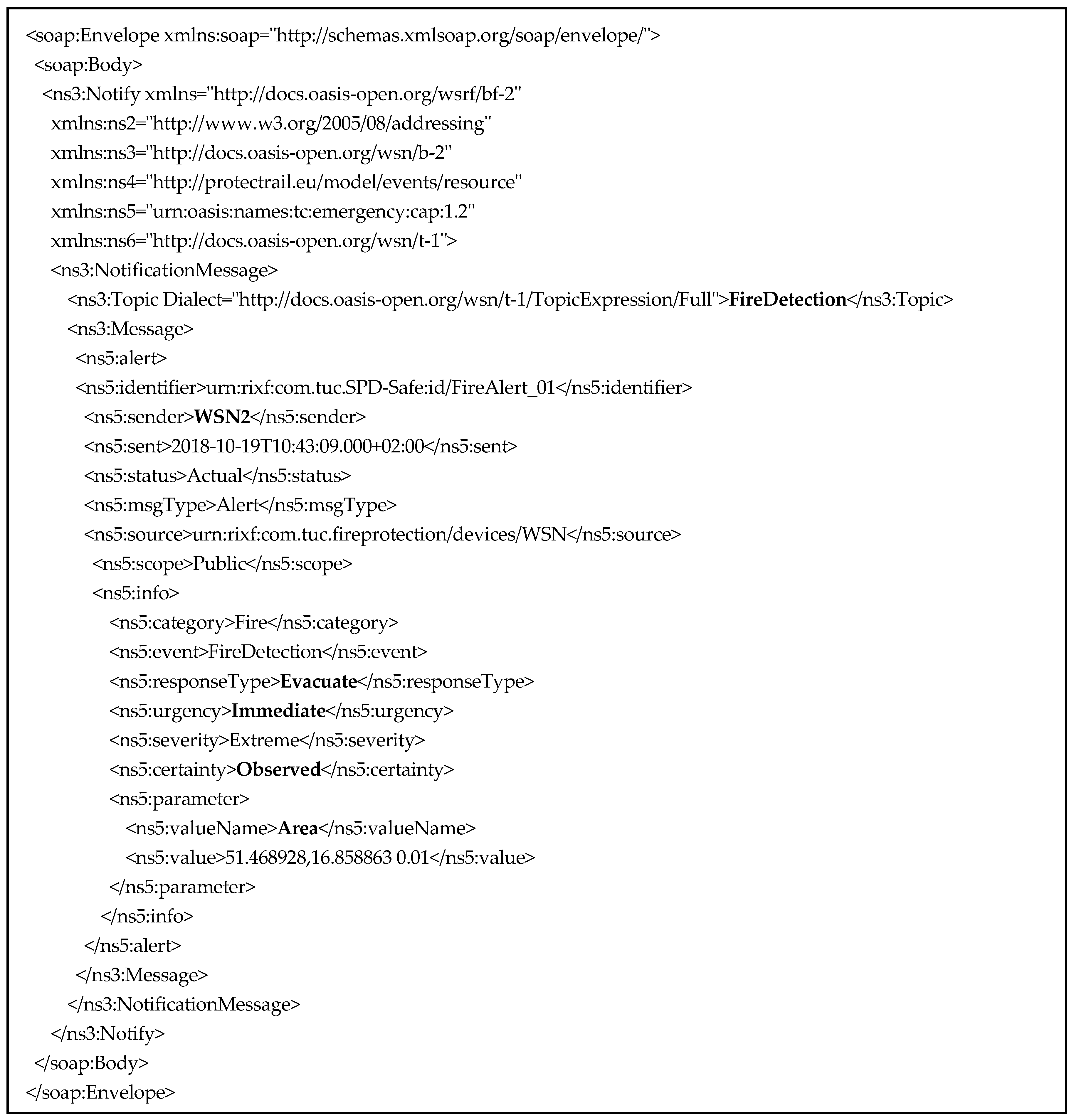
5. SPD-Safe Demonstration
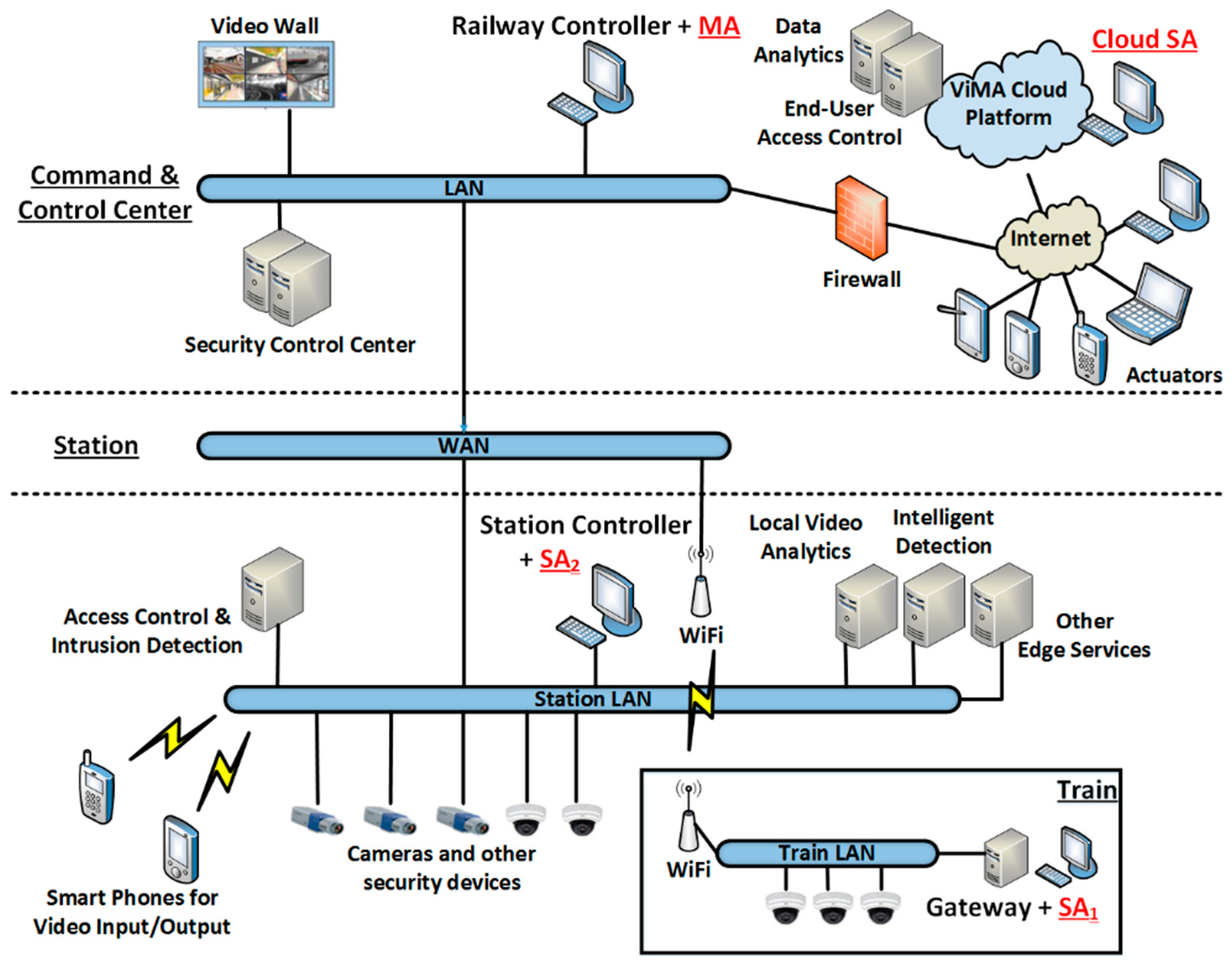
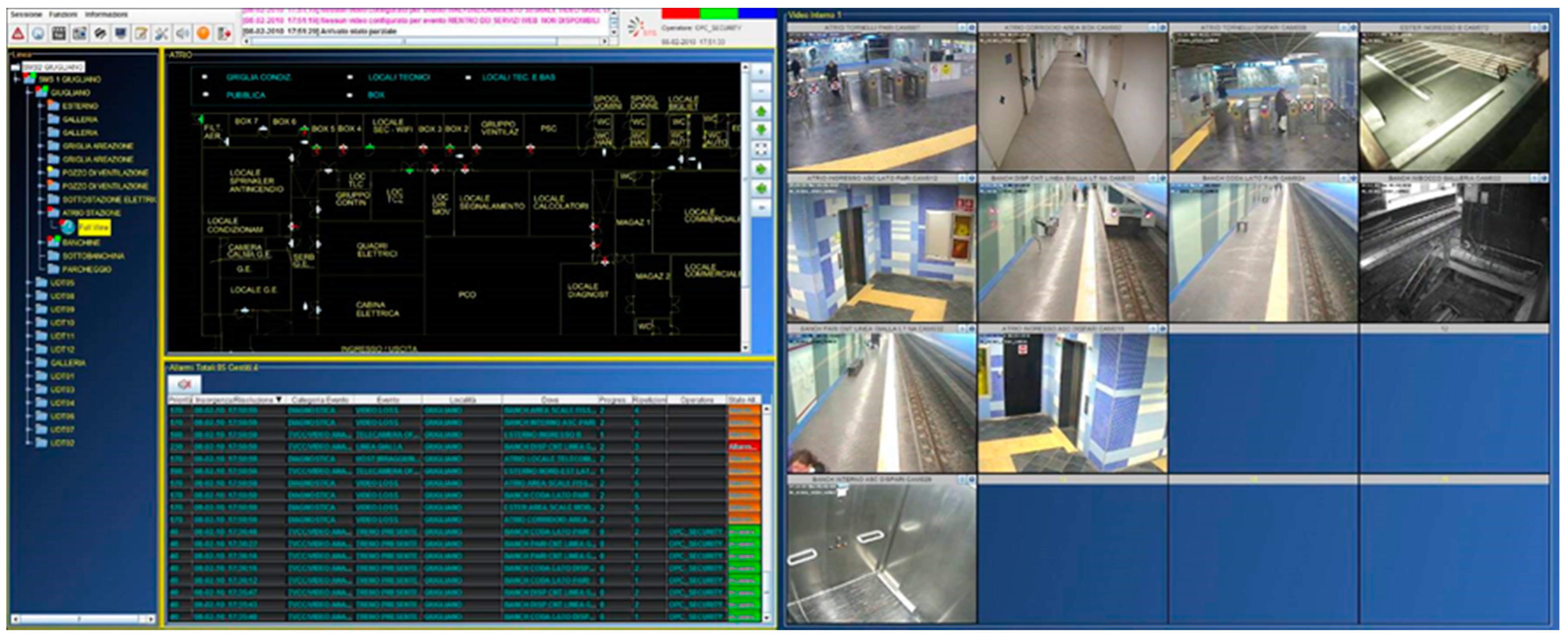
5.1. Railway CPS Architecture
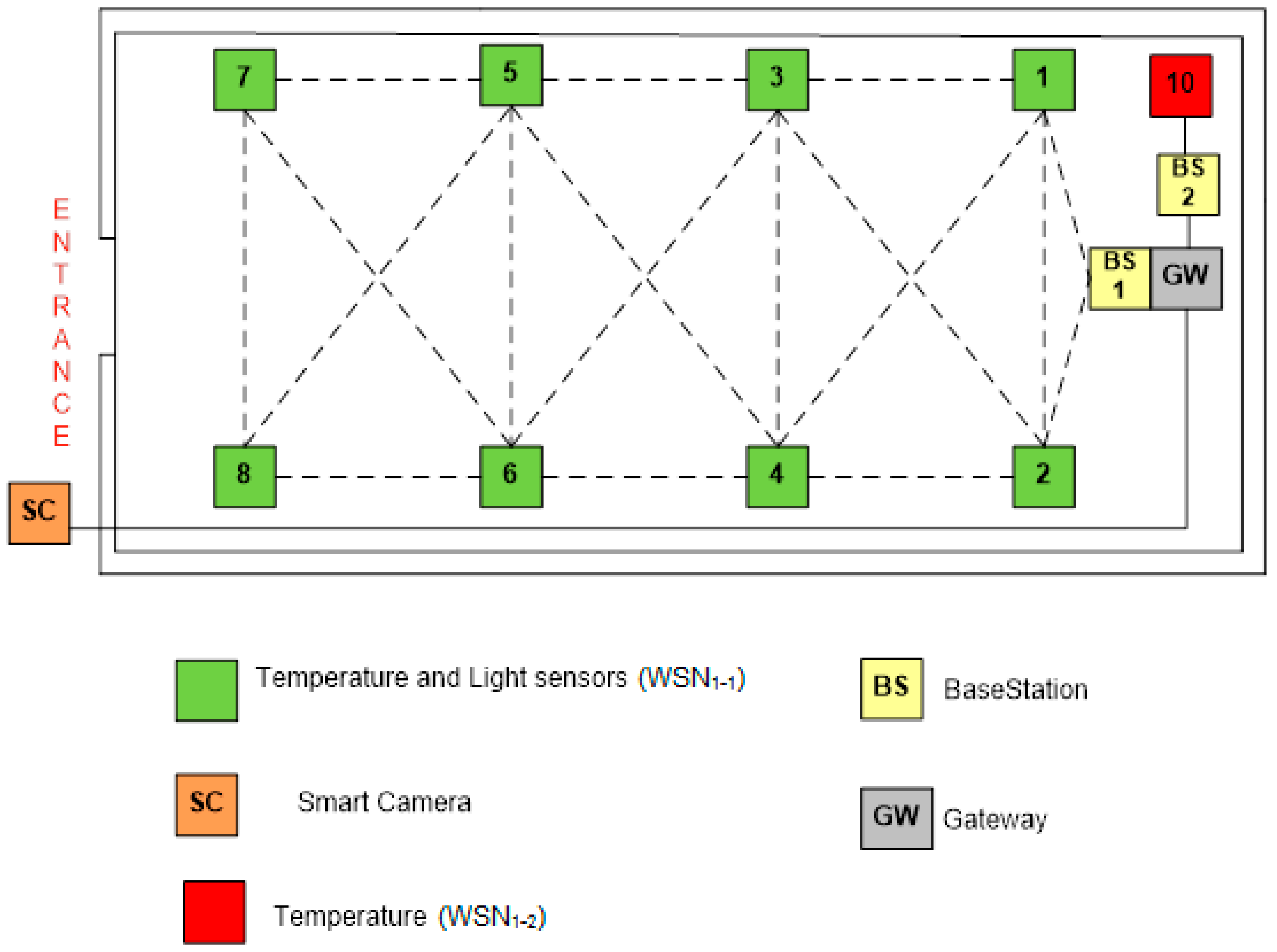
5.2. Indoor Setting—Cyber-Security
- At the entrance, the smart camera inspects for physical intrusion;
- Two WSNs are deployed in the shelter. WSN1-1 (green color) monitors light and temperature, and WSN1-2 (red color) senses temperature. WSN1-1 and WSN1-2 utilize different hardware to enhance diversity and ensure redundancy for the monitored factors;
- A gateway interconnects the rest of the components with the C&C.
5.3. Outdoor Setting—Safety Scenario
6. Discussion
6.1. Comparison
6.2. Future Work
7. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
Appendix A
References
- Xu, S.; Zhu, G.; Ai, B.; Zhong, Z. A Survey on High-Speed Railway Communications: A Radio Resource Management Perspective. Computer Communications; Elsevier: Amsterdam, The Netherlands, 2016; Volume 86, pp. 12–28. [Google Scholar]
- Chamoso, P.; González-Briones, A.; Rodríguez, S.; Corchado, J.M. Tendencies of Technologies and Platforms in Smart Cities: A State-of-the-Art Review. In Wirel. Commun. Mobile Comput.; 2018; Volume 2018, p. 3086854. [Google Scholar]
- Boudi, Z.; El Koursi, E.M.; Ghazel, M. The New Challenges of Rail Security. J. Traffic Logist. Eng. 2016, 4, 56–60. [Google Scholar] [CrossRef]
- Kour, R.; Thaduri, A.; Karim, R. Railway Defender Kill Chain to Predict and Detect Cyber-Attacks. J. Cyber Secur. Mobil. 2019, 9, 47–90. [Google Scholar] [CrossRef]
- Luxton, A.; Marinov, M. Terrorist Threat Mitigation Strategies for the Railways. Sustainability 2020, 12, 3408. [Google Scholar] [CrossRef]
- Zhang, J.; Hu, F.; Wang, S.; Dai, Y.; Wang, Y. Structural vulnerability and intervention of high speed railway networks. Phys. A Stat. Mech. Appl. 2016, 462, 743–751. [Google Scholar] [CrossRef]
- González-Briones, A.; Garcia-Martin, R.; de AlbaJuan, F.L.; Corchado, M. Agent-Based Platform for Monitoring the Pressure Status of Fire Extinguishers in a Building. In International Conference on Practical Applications of Agents and Multi-Agent Systems (PAAMS); Springer: Berlin/Heidelberg, Germany, 2020; Volume 1233, pp. 373–384. [Google Scholar]
- Catalano, A.; Bruno, F.A.; Galliano, C.; Pisco, M.; Persiano, G.V.; Cutolo, A.; Cusano, A. An optical fiber intrusion detection system for railway security. Sens. Actuators A Phys. 2017, 253, 91–100. [Google Scholar] [CrossRef]
- Fraga-Lamas, P.T.; Fernández-Caramés, M.; Castedo, L. Towards the Internet of Smart Trains: A Review on Industrial IoT-Connected Railways. Sensors 2017, 17, 1457. [Google Scholar] [CrossRef]
- Wang, Y.; Zhu, L.; Yu, Z.; Guo, B. An adaptive track segmentation algorithm for a railway intrusion detection system. Sensor 2019, 19, 2594. [Google Scholar] [CrossRef]
- Gai, K.; Qiu, M.; Hassan, H. Secure Cyber Incident Analytics Framework using Monte Carlo Simulations for Financial Cybersecurity Insurance in Cloud Computing. In Concurrency and Computation: Practice and Experience; Wiley: Hoboken, NJ, USA, 2017; Volume 29, issue 7. [Google Scholar]
- Chang, S.E.; Liu, A.Y.; Lin, S. Exploring privacy and trust for employee monitoring. Ind. Manag. Data Syst. 2015, 115, 88–106. [Google Scholar] [CrossRef]
- Paganini, P. Modern Railroad Systems Vulnerable to Cyber Attacks. Security Affairs. 2016. Available online: http://securityaffairs.co/wordpress/43196/hacking/railroad-systems-vulnerabilities.html (accessed on 18 November 2020).
- Bababeik, M.; Khademi, N.; Chen, A.; Nasiri, M.M. Vulnerability analysis of railway networks in case of multi-link blockage. Transp. Res. Procedia 2017, 22, 275–284. [Google Scholar] [CrossRef]
- Khanmohamadi, M.; Bagheri, M.; Khademi, N.; Ghannadpour, S.F. A security vulnerability analysis model for dangerous goods transportation by rail–Case study: Chlorine transportation in Texas-Illinois. Saf. Sci. 2018, 110, 230–241. [Google Scholar] [CrossRef]
- Salmane, H.; Khoudour, L.; Ruichek, Y. A Video-Analysis-Based Railway–Road Safety System for Detecting Hazard Situations at Level Crossings. IEEE Trans. Intell. Transp. Syst. 2015, 16, 596–609. [Google Scholar] [CrossRef]
- Chernov, A.V.; Savvas, I.K.; Butakova, M.A. Detection of Point Anomalies in Railway Intelligent Control System Using Fast Clustering Techniques. In Proceedings of the 3rd International Scientific Conference Intelligent Information Technologies for Industry, Sochi, Russia, 17–21 September 2018; pp. 267–276. [Google Scholar]
- Coppola, P.; Silvestri, F. Assessing travelers’ safety and security perception in railway stations. Case Stud. Transp. Policy 2020, 8, 1127–1136. [Google Scholar] [CrossRef]
- Mrazovic, P.; Eser, E.; Ferhatosmanoglu, H.; Larriba-Pey, J.L.; Matskin, M. Multi-vehicle Route Planning for Efficient Urban Freight Transport. In Proceedings of the 2018 International Conference on Intelligent Systems (IS), Funchal, Madeira, Portugal, 25–27 September 2018; pp. 744–753. [Google Scholar]
- Zhu, C.; Shu, L.; Leung, V.C.M.; Guo, S.; Zhang, Y.; Yang, L.T. Secure multimedia Big Data in trust-assisted sensor-cloud for smart city. IEEE Commun. Mag. 2017, 55, 24–30. [Google Scholar] [CrossRef]
- Chamoso, P.; De La Prieta, F.; De Paz, F.; Corchado, J.M. Swarm Agent-Based Architecture Suitable for Internet of Things and Smartcities. In Distributed Computing and Artificial Intelligence, 12th International Conference; Springer: Berlin/Heidelberg, Germany, 2015; Volume 373, pp. 21–29. [Google Scholar]
- Zhang, Q.; Chen, Z.; Leng, Y. Distributed fuzzy c-means algorithms for big sensor data based on cloud computing. Int. J. Sens. Networks 2015, 18, 32–39. [Google Scholar] [CrossRef]
- Tsaramirsis, G.; Karamitsos, I.; Apostolopoulos, C. Smart Parking: An IoT application for Smart City. In Proceedings of the 10th INDIACom-2016 International Conference, New Delhi, India, 16–18 March 2016; pp. 2271–2275. [Google Scholar]
- Yin, W.; He, S.; Zhang, Y.; Hou, J. A Product-Focused, Cloud-Based Approach to Door-to-Door Railway Freight Design. IEEE Access 2018, 6, 20822–20836. [Google Scholar] [CrossRef]
- Dong, Q.; Hayashi, K.; Kaneko, M. An Optimized Link Layer Design for Communication-Based Train Control Systems Using WLAN. IEEE Access 2017, 6, 6865–6877. [Google Scholar] [CrossRef]
- Fanian, F.; Rafsanjani, M.K. Cluster-based routing protocols in wireless sensor networks: A survey based on methodology. J. Netw. Comput. Appl. 2019, 142, 111–142. [Google Scholar] [CrossRef]
- Khanna, N.; Sachdeva, M. Study of trust-based mechanism and its component model in MANET: Current research state, issues, and future recommendation. Int. J. Commun. Syst. 2019, 32, 1–23. [Google Scholar] [CrossRef]
- Cesena, M. SHIELD Technology Demonstrators. In Measurable and Composable Security, Privacy, and Dependability for Cyberphysical Systems; CRC Press: Boca Raton, FL, USA, 2017; pp. 381–434. [Google Scholar]
- Brokalakis, A.; Tampouratzis, N.; Nikitakis, A.; Andrianakis, S.; Papaefstathiou, I.; Dollas, A. An Open-Source Extendable, Highly-Accurate and Security Aware CPS Simulator. In Proceedings of the 2017 13th International Conference on Distributed Computing in Sensor Systems (DCOSS), Ottawa, ON, Canada, 5–7 June 2017; pp. 81–88. [Google Scholar]
- Farooq, J.; Soler, J. Radio Communication for Communications-Based Train Control (CBTC): A Tutorial and Survey. IEEE Commun. Surv. Tutor. 2017, 19, 1377–1402. [Google Scholar] [CrossRef]
- Sun, W.; Yu, F.R.; Tang, T.; Bu, B. Energy-Efficient Communication-Based Train Control Systems with Packet Delay and Loss. IEEE Trans. Intell. Transp. Syst. 2016, 17, 452–468. [Google Scholar] [CrossRef]
- Garcia-Loygorri, J.M.; Val, I.; Arriola, A.; Briso-Rodriguez, C. 2.6 GHz Intra-Consist Channel Model for Train Control and Management Systems. IEEE Access 2017, 5, 23052–23059. [Google Scholar] [CrossRef]
- Fotso, S.J.T.; Frappier, M.; Laleau, R.; Mammar, A. Modeling the Hybrid ERTMS/ETCS Level 3 Standard Using a Formal Requirements Engineering Approach. In International Conference on Abstract State Machines; Alloy, B., Ed.; Springer: Berlin/Heidelberg, Germany, 2018; pp. 262–276. [Google Scholar]
- Chetty, K.; Chen, Q.; Woodbridge, K. Train monitoring using GSM-R based passive radar. In Proceedings of the 2016 IEEE Radar Conference (RadarConf), Philadelphia, PA, USA, 1–6 May 2016; pp. 1–4. [Google Scholar]
- Bates, R.J. GPRS: General Packet Radio Service. In Book GPRS: General Packet Radio Service; McGraw-Hill, Professional Telecom: New York, NY, USA, 2001. [Google Scholar]
- Proto, M.; Bavusi, M.; Bernini, R.; Bigagli, L.; Bost, M.; Bourquin, F.; Cottineau, L.-M.; Cuomo, V.; Della Vecchia, P.; Dolce, M.; et al. Transport Infrastructure Surveillance and Monitoring by Electromagnetic Sensing: The ISTIMES Project. Sensors 2010, 10, 10620–10639. [Google Scholar] [CrossRef] [PubMed]
- Crinière, A.; Dumoulin, J.; Mevel, L.; Andrade-Barroso, G. Cloud2IR an Infrared and Environmental SHM Information System. In Proceedings of the 13th Quantitative Infrared Thermography Conference (QIRT), Gdansk, Poland, 4–8 July 2016; pp. 226–235. [Google Scholar]
- Xie, J.; Liu, C.-C. Multi-agent systems and their applications. J. Int. Counc. Electr. Eng. 2017, 7, 188–197. [Google Scholar] [CrossRef]
- De la Prieta, F.; Rodríguez-González, S.; Chamoso, P.; Corchado, J.M.; Bajo, J. Survey of agent-based cloud computing applications. Future Gener. Comput. Syst. 2019, 100, 223–236. [Google Scholar] [CrossRef]
- Kravari, K.; Bassiliades, N. A Survey of Agent Platforms. J. Artif. Soc. Soc. Simul. 2015, 18, 11–29. [Google Scholar] [CrossRef]
- FIPA, “FIPA ACL Message Structure Specification,” Foundation for Intelligent Physical Agents. 2002. Available online: http://www.fipa.org/specs/fipa00061/SC00061G.html (accessed on 18 November 2020).
- Fysarakis, K.; Askoxylakis, I.; Soultatos, O.; Papaefstathiou, I.; Manifavas, C.; Katos, V. Which IoT Protocol? Comparing Standardized Approaches over a Common M2M Application. In Proceedings of the 2016 IEEE Global Communications Conference (GLOBECOM), Washington, DC, USA, 4–8 December 2016; pp. 1–6. [Google Scholar]
- OASIS. “Devices Profile for Web Services Version 1.1,” Organization for the Advancement of Structured Information Standards. 2009. Available online: http://docs.oasis-open.org/ws-dd/dpws/1.1/os/wsdd-dpws-1.1-spec-os.pdf (accessed on 18 November 2020).
- Thirumalainambi, R. Pitfalls of Jess for dynamic systems. In Proceedings of the International Conference on Artificial Intelligence and Pattern Recognition (AIPR), Orlando, FL, USA, 9–12 July 2007; Volume 1, pp. 491–494. [Google Scholar]
- Kumar, S.; Prasad, R. Importance of expert system shell in development of expert system. Int. J. Innov. Res. Dev. 2015, 4, 128–133. [Google Scholar]
- Semmel, G.; Davis, S.; Leucht, K.; Rowe, D.; Kelly, A.; Boloni, L. Launch commit criteria monitoring agent. In Proceedings of the 4th International Joint Conference on Autonomous Agents and MultiAgent Systems (AAMAS), Utrecht, The Netherlands, 25–29 July 2005; pp. 3–10. [Google Scholar]
- Goseva-Popstojanova, K.; Tyo, J. Experience Report: Security Vulnerability Profiles of Mission Critical Software: Empirical Analysis of Security Related Bug Reports. In Proceedings of the 28th International Symposium on Software Reliability Engineering (ISSRE), Toulouse, France, 23–26 October 2017; pp. 152–163. [Google Scholar]
- Leitao, P.; Karnouskos, S. Industrial Agents: Emerging Applications of Software Agents in Industry, 1st ed.; Elsevier Science: Amsterdam, The Netherlands, 2015; pp. 1–476. [Google Scholar]
- Ghadimi, P.; Wang, C.; Lim, M.K.; Heavey, C. Intelligent sustainable supplier selection using multi-agent technology: Theory and application for Industry 4.0 supply chains. Comput. Ind. Eng. 2019, 127, 588–600. [Google Scholar] [CrossRef]
- Scholten, H.; Westenberg, R.; Schoemaker, M. Sensing Train Integrity. In Proceedings of the IEEE Sensors Conference, Christchurch, New Zealand, 25–28 October 2009. [Google Scholar]
- Firlik, B.; Chudzikiewicz, A. Condition monitoring of a light rail vehicle—From concept to implementation. Key Eng. Mater. 2012, 518, 66–75. [Google Scholar] [CrossRef]
- Flammini, F.; Gaglione, A.; Ottello, F.; Pappalardo, A.; Pragliola, C.; Tedesco, A. Towards wireless sensor networks for railway infrastructure monitoring. In Proceedings of the Electrical Systems for Aircraft, Railway and Ship Propulsion (ESARS), Bologna, Italy, 19–21 October 2010. [Google Scholar]
- Casola, V.; Gaglione, A.; Mazzeo, A. A reference architecture for sensor networks integration and management. In Proceedings of the 3rd International Conference on Geosensor Networks, Oxford, UK, 13–14 July 2009; pp. 158–168. [Google Scholar]
- Flammini, F.; Gaglione, A.; Mazzocca, N.; Pragliola, C. DETECT: A novel framework for the detection of attacks to critical infrastructures. In Safety, Reliability and Risk Analysis: Theory, Methods and Applications; Taylor & Francis: Abingdon, UK, 2008; pp. 105–112. [Google Scholar]
- Chakravarthy, S.; Mishra, D. Snoop: An expressive event specification language for active databases. Data Knowl. Eng. 1994, 14, 1–26. [Google Scholar] [CrossRef]
- Ganeriwal, S.; Balzano, L.; Srivastava, M. Reputation-based framework for high integrity sensor networks. ACM Trans. Sen. Netw. 2008, 4. [Google Scholar] [CrossRef]
- Hu, Y.-C.; Perrig, A.; Johnson, D.B. Ariadne: A secure on-demand routing protocol for ad hoc networks. Wirel. Netw. 2005, 11, 21–38. [Google Scholar] [CrossRef]
- Zhang, Y.; Xu, L.; Wang, X. A Cooperative Secure Routing Protocol based on Reputation System for Ad Hoc Networks. J. Commun. 2008, 3, 43–50. [Google Scholar] [CrossRef]
- Altisen, K.; Devismes, S.; Jamet, R.; Lafourcade, P. SR3: Secure resilient reputation-based routing. In Proceedings of the 2013 IEEE International Conference on Distributed Computing in Sensor Systems (DCOSS), Cambridge, MA, USA, 20–23 May 2013; pp. 258–265. [Google Scholar]
- Dhaheri, A.A.; Yeum, C.Y.; Damiani, E. New Two-Level µTESLA Protocol for IoT Environments. In Proceedings of the 2019 IEEE World Congress on Services (SERVICES), Milan, Italy, 8–13 July 2019; pp. 84–91. [Google Scholar]
- Hatzivasilis, G.; Papaefstathiou, I.; Askoxylakis, I.; Fysarakis, K. SecRoute: End-to-end secure communications for wireless ad-hoc networks. In Proceedings of the 22nd IEEE Symposium on Computers and Communications (ISCC), Heraklion, Crete, Greece, 3–6 July 2017; pp. 558–563. [Google Scholar]
- Hatzivasilis, G.; Papaefstathiou, I.; Manifavas, C. SCOTRES: Secure Routing for IoT and CPS. IEEE Internet Things J. 2017, 4, 2129–2141. [Google Scholar] [CrossRef]
- Hatzivasilis, G.; Papaefstathiou, I.; Plexousakis, D.; Manifavas, C.; Papadakis, N. AmbISPDM: Managing embedded systems in ambient environment and disaster mitigation planning. In Applied Intelligence; Springer: Berlin/Heidelberg, Germany, 2017; pp. 1–21. [Google Scholar]
- Java Agent Development (JADE) Framework. Available online: http://jade.tilab.com/ (accessed on 18 November 2020).
- Tilab, S.P.A. JADE Security Add-On Guide. 2005. Available online: http://jade.tilab.com/doc/tutorials/JADE_Security.pdf (accessed on 18 November 2020).
- Ali, B.; Manzoor, U.; Zafar, B. eJADE-S: Encrypted JADE-S for Securing Multi-Agent Applications. In Proceedings of the International Conference on Artificial Intelligence (ICAI), Athens, Greece, 27–30 July 2015; pp. 548–554. [Google Scholar]
- Open Services Gateway Initiative (OSGi). Available online: http://www.osgi.org/ (accessed on 18 November 2020).
- OASIS. Common Alerting Protocol Version 1.2, Organization for the Advancement of Structured Information Standards. 2010. Available online: http://docs.oasis-open.org/emergency/cap/v1.2/CAP-v1.2-os.pdf (accessed on 18 November 2020).
- Hatzivasilis, G.; Papadakis, N.; Hatzakis, I.; Ioannidis, S.; Vardakis, G. AI-driven composition and security validation of an IoT ecosystem. Appl. Sci. 2020, 10, 4862. [Google Scholar] [CrossRef]
- Friedman-Hill, E.J. Jess: The Rule Engine for Java Platform. Sandia National Laboratories. 2008. Available online: http://www.jessrules.com/docs/71/ (accessed on 18 November 2020).
- Lu, Y.; Li, Q.; Zhou, Z.; Deng, Y. Ontology-based knowledge modeling for automated construction safety checking. Saf. Sci. 2015, 79, 11–18. [Google Scholar] [CrossRef]
- Patkos, T.; Plexousakis, D.; Chibani, A.; Amirat, Y. An event calculus production rule system for reasoning in dynamic and uncertain domains. In Theory and Practice of Logic Programming; Cambridge University Press: Cambridge, UK, 2016; Volume 16, pp. 325–352. [Google Scholar]
- Mueller, E.T. Commonsense Reasoning, 2nd ed.; Kaufmann, M., Ed.; Elsevier: Amsterdam, The Netherlands, 2015; pp. 1–516. [Google Scholar]
- Lei, C.; Zhang, H.-Q.; Tan, J.-L.; Zhang, Y.-C.; Liu, X. Moving Target Defense Techniques: A Survey. Secur. Commun. Netw. 2018, 2018, 1–25. [Google Scholar] [CrossRef]
- Berstel, B. Extending the RETE algorithm for event management. In Proceedings of the 9th International Symposium on Temporal Representation and Reasoning, Manchester, UK, 7–9 July 2002; pp. 49–51. [Google Scholar]
- Eby, M.; Werner, J.; Karsai, G.; Ledeczi, A. Integrating security modeling into embedded system design. In Proceedings of the 14th Annual IEEE International Conference and Workshops on the Engineering of Computer-Based Systems (ECBS), Tucson, AZ, USA, 26–29 March 2007; pp. 221–228. [Google Scholar]
- Kelly, S.; Tolvanen, J.-P. Domain-Specific Modeling: Enabling Full Code Generation; Wiley-IEEE Computer Society Pr.: Hoboken, NJ, USA, 2008; pp. 1–444. [Google Scholar]
- Ko, H.; Jin, J.; Keoh, S.L. Secure Service Virtualization in IoT by Dynamic Service Dependency Verification. IEEE Internet Things J. 2016, 3, 1006–1014. [Google Scholar] [CrossRef]
- Albanese, M.; Battista, E.; Jajodia, S.; Casola, V. Manipulating the Attacker’s View of a System’s Attack Surface. In Proceedings of the IEEE Conference on Communications and Network Security, San Francisco, CA, USA, 29–31 October 2014; pp. 472–480. [Google Scholar]
- Savola, R.M.; Sihvonen, M. Metrics driven security management framework for e-health digital ecosystem focusing on chronic diseases. In Proceedings of the MEDES ’12: International Conference on Management of Emergent Digital EcoSystems, Addis Ababa, Ethiopia, 28–31 October 2012; pp. 75–79. [Google Scholar] [CrossRef]
- Ayyappan, B.; Kumar, P.M. Security protocols in WSN: A survey. In Proceedings of the 2017 Third International Conference on Science Technology Engineering & Management (ICONSTEM), Chennai, India, 23–24 March 2017; pp. 301–304. [Google Scholar]
- Parducci, B.; Lockhart, H. eXtensible Access Control Markup Language (XACML) Version 3.0; OASIS Standard: Burlington, MA, USA, 2013; pp. 1–154. [Google Scholar]


| Feature | SPD-Safe [This Paper] | SMoLES-SEC [76] | SDT [78] | Attack Surface MTD [79] | Multi-Metric-Driven MTD [80] |
|---|---|---|---|---|---|
| System composition | |||||
| Expressiveness generality | Y | N | Y | N | N |
| Dynamicity | Y | Y | Y | N | N |
| Validation | |||||
| Pre-composition | Y | Y | Y | N | N |
| Post-composition | Y | N | N | N | N |
| Evaluated Properties | |||||
| Security | Y | Y | Y | Y | Y |
| Privacy | Y | N | N | N | N |
| Dependability | Y | P | P | N | P |
| Artificial Intelligence | |||||
| Distributed reasoning/processing | Y | N | Y | N | Y |
| Conflict resolution | Y | N | N | N | N |
| MTD | Y | N | N | Y | Y |
| Primitive | System Property | Countered Threats |
|---|---|---|
| μTESLA | Authentication | Impersonation, Sybil attacks |
| Integrity | Data tampering, modification, interruption | |
| Forward security | Replay attacks | |
| Confidentiality (optional) | Disclosure | |
| SCOTRES | Topology-awareness | Attacks on topology-significant entities |
| Energy-awareness & Load-balancing | Energy dissipation, overloading attacks on congested periods | |
| Channel health | Jamming attacks | |
| Reputation | Malicious or selfish activity on the network operations of:
| |
| Trust | Overall misbehavior on the previously mentioned networking perspectives | |
| Secure routing | General attacks on the pure routing protocol (e.g., Denial of Service (DoS), inject arbitrary packets) | |
| PBAC | Authorization based on policies | Unauthorized access |
| Component | ROM (KB) | RAM (KB) | CPU (ms) |
|---|---|---|---|
| Cryptographic service | |||
| Authentication | 3.7 | 2.22 | 0.0020 |
| Encryption | 25.0 | 10.41 | 0.0028 |
| Authenticated encryption | 28.7 | 12.63 | 0.0048 |
| Secure routing service | |||
| Direct trust | 5.6 | 4899.00 | 677.52 |
| Reputation evaluation | 20.0 | 1621.00 | 108.97 |
| Indirect trust (recommendations) | 30.0 | 185.00 | 37.90 |
| Total trust | 2.9 | 45,756.00 | 9.48 |
| Accept route request | 2.0 | 0.00 | 104.23 |
| Suitable route selection | 15.0 | 40.00 | 33.17 |
| Authorization service | |||
| PBAC policy check | 24.7 | 36.00 | 7.50 |
| Total resource consumption | |||
| Total SecRoute | 210.4 | 46,000.00 | 1652.50 |
| DSR | 310.0 | 90,000.00 | 2300.00 |
| SecRoute_DSR | 520.4 | 136,000.00 | 3952.50 |
| Property | SecRoute | RFSN | Ariadne | CSRAN | SR3 |
|---|---|---|---|---|---|
| Authentication | μTESLA | μTESLA | TESLA | Certificates | LWC |
| Routing method | DSR | DSR | DSR | ARAN | Random walk |
| Reputation Fading | Bayesian | Bayesian | NO | Bayesian | FIFO * |
| Load-balancing | YES | NO | NO | NO | Partially |
| Energy-aware | YES | NO | NO | NO | NO |
| Anti-jamming | YES | NO | NO | NO | NO |
| Authorization | YES | NO | NO | NO | NO |
| Event | Description | SPD State | Total <S, P, D> Value | SPD Visualization |
|---|---|---|---|---|
| 1 | Start of all components and services.Discovery/registration operations. | Initial State | <80, 70, 65> |  |
| 2 | Bad-mouthing attack to WSN1-1. MA (master agent) is alerted for the attack and commands the rest agents to increase security. | Security level decreases | <60, 70, 65> |  |
| 3 | Security status is enhanced on all SAs (simple agents). MA is notified. | Security level increases | <85, 70, 65> |  |
| 4 | WSN1-1 counters bad-mouthing and SA1-1 informs the MA.The MA requests from the SAs to restore the normal state (to conserve resources). | Security level returns to initial state | <80, 70, 65> |  |
| 5 | Blackhole attack to WSN1-2. MA is alerted for the attack and commands the rest agents to increase security. | Security level decreases | <50, 70, 65> |  |
| 6 | Security status is enhanced on all SAs. MA is notified. | Security level increases | <85, 70, 65> |  |
| 7 | WSN1-2 counters the blackhole attack and SA1-2 informs the MA. The MA requests from the SAs to restore the normal state (to conserve resources). | Security level returns to initial state | <80, 70, 65> |  |
| 8 | A node has died in WSN1-2. MA is informed. | Dependability level decreases | <80, 70, 30> |  |
| 9 | The dead node is replaced by the personnel. Dependability is restored.SA1-1 reports the new status to MA. | Dependability level returns to initial state | <80, 70, 65> |  |
| 10 | Simulated jamming attack against the network layer of WSN1-2. MA is informed. | S & D levels decrease | <40, 70, 40> |  |
| 11 | The trust-based routing component counters the attack. SA1-2 reports new state to MA. | S & D levels return to initial state | <80, 70, 65> |  |
| Property | SDP-Safe | TrainIntegrity | CMLRVT | SENSORAIL |
|---|---|---|---|---|
| AI technologies | JADE/Jess | NO | NO | SeNsIM |
| Reasoning & processing | Distributed | Centralized | Centralized | Centralized |
| Conflict resolution | YES | NO | NO | NO |
| Security management | YES | NO | NO | NO |
| Safety management | YES | YES | YES | YES |
| Middleware | OSGi | NO | NO | NO |
| Network layer protection | SecRoute | NO | NO | NO |
| Cloud management | ViMA | NO | NO | NO |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Hatzivasilis, G.; Fysarakis, K.; Ioannidis, S.; Hatzakis, I.; Vardakis, G.; Papadakis, N.; Spanoudakis, G. SPD-Safe: Secure Administration of Railway Intelligent Transportation Systems. Electronics 2021, 10, 92. https://doi.org/10.3390/electronics10010092
Hatzivasilis G, Fysarakis K, Ioannidis S, Hatzakis I, Vardakis G, Papadakis N, Spanoudakis G. SPD-Safe: Secure Administration of Railway Intelligent Transportation Systems. Electronics. 2021; 10(1):92. https://doi.org/10.3390/electronics10010092
Chicago/Turabian StyleHatzivasilis, George, Konstantinos Fysarakis, Sotiris Ioannidis, Ilias Hatzakis, George Vardakis, Nikos Papadakis, and George Spanoudakis. 2021. "SPD-Safe: Secure Administration of Railway Intelligent Transportation Systems" Electronics 10, no. 1: 92. https://doi.org/10.3390/electronics10010092
APA StyleHatzivasilis, G., Fysarakis, K., Ioannidis, S., Hatzakis, I., Vardakis, G., Papadakis, N., & Spanoudakis, G. (2021). SPD-Safe: Secure Administration of Railway Intelligent Transportation Systems. Electronics, 10(1), 92. https://doi.org/10.3390/electronics10010092









