MODC: A Pareto-Optimal Optimization Approach for Network Traffic Classification Based on the Divide and Conquer Strategy
Abstract
:1. Introduction
2. Literature Review
- Reproducibility is not possible when the dataset used in the experiments is private and, therefore, hinders the benchmarking against different network traffic classifiers.
- The correct labeling (i.e., ground-truth or GT) of flow instances is necessary to build good classifiers.
- Port and IP information should be discarded from network datasets since applications can make use of random ports or the traffic can be encapsulated, and IP information in packets can be obfuscated by proxies.
- Some network administrators would be more concerned to correctly classify flows which require more bandwidth resources from a network; that is, the accuracy of bytes would be more important than the accuracy of flows.
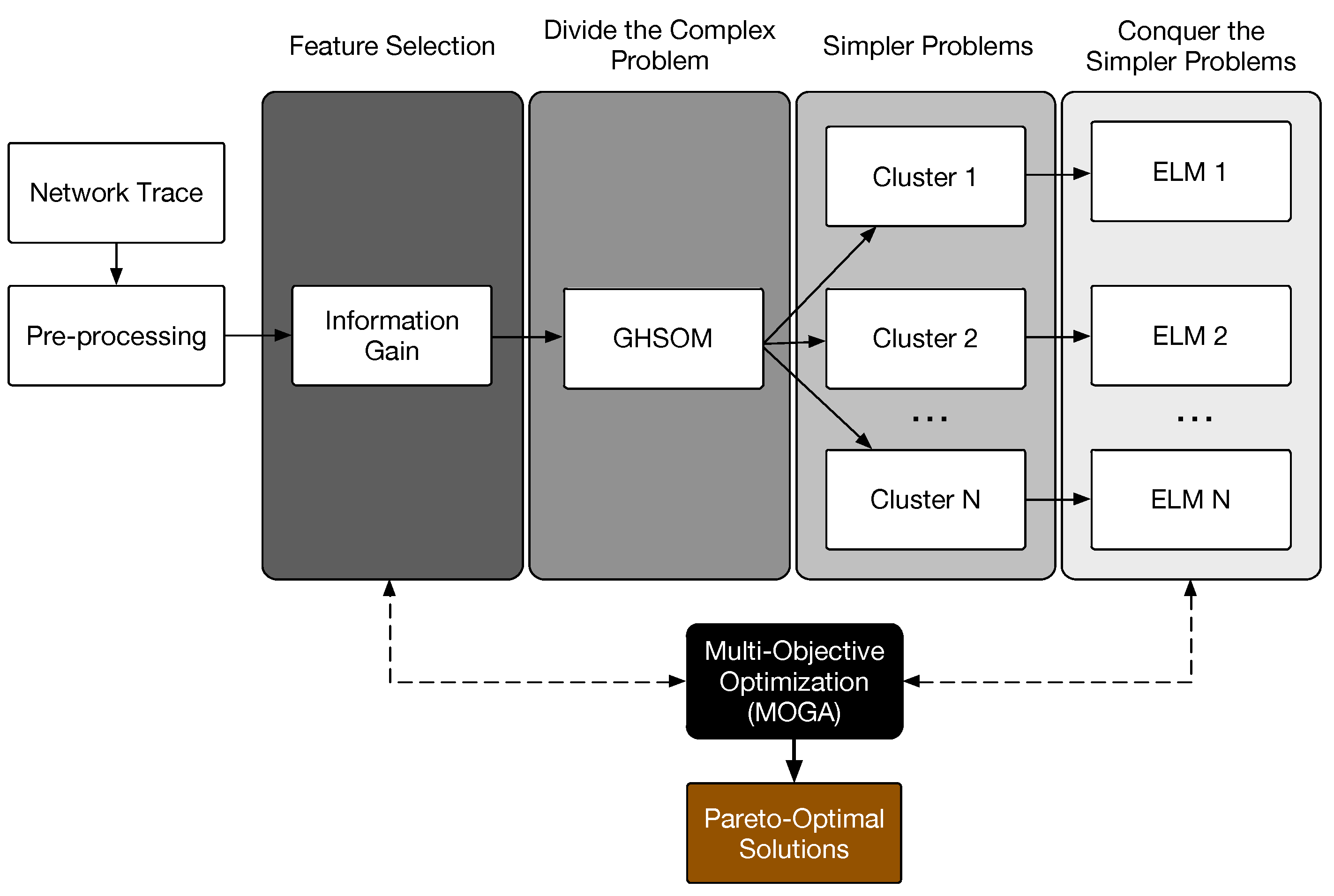
3. The Proposed Method
3.1. Feature Selection
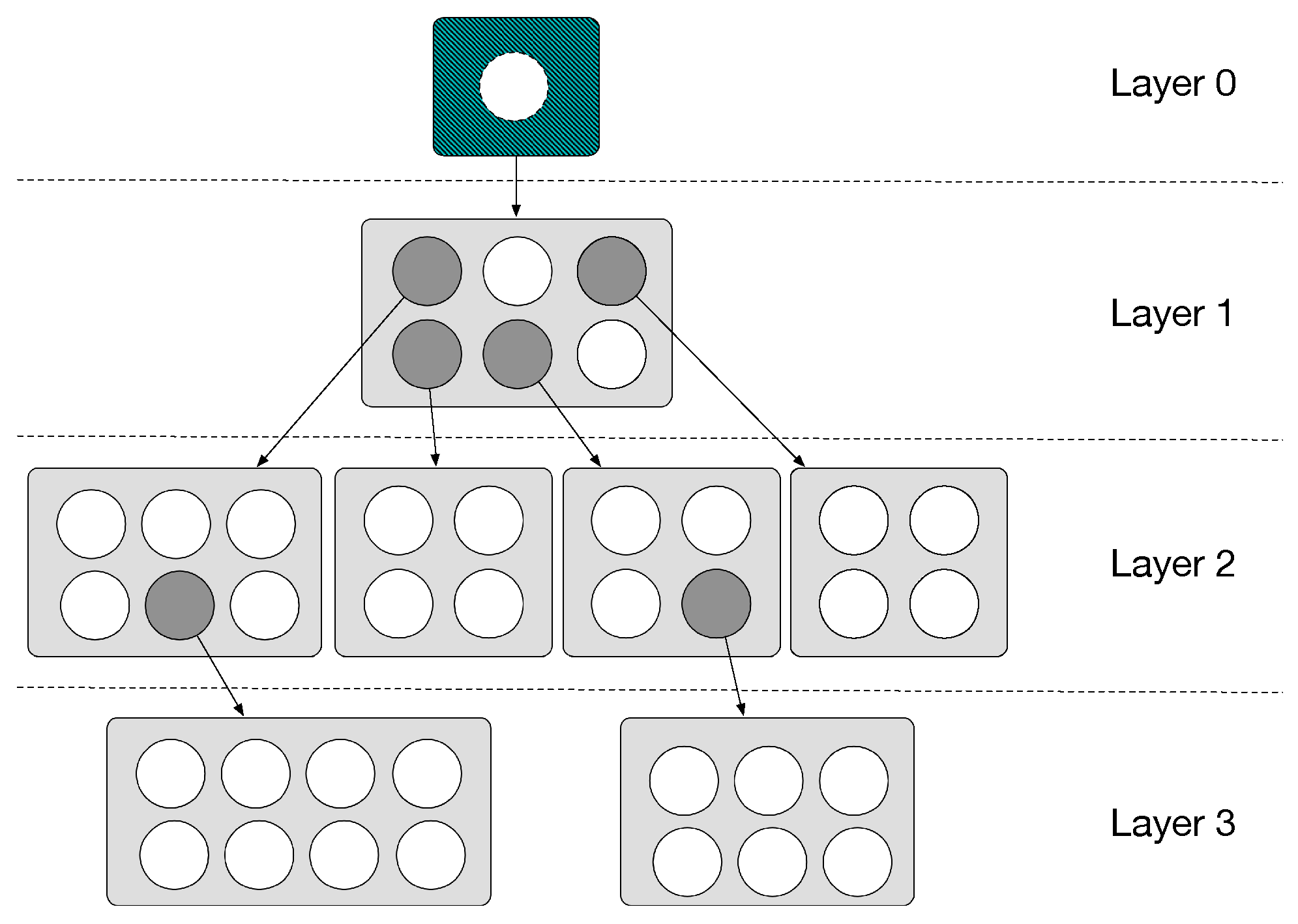
3.2. Divide
3.3. Conquer
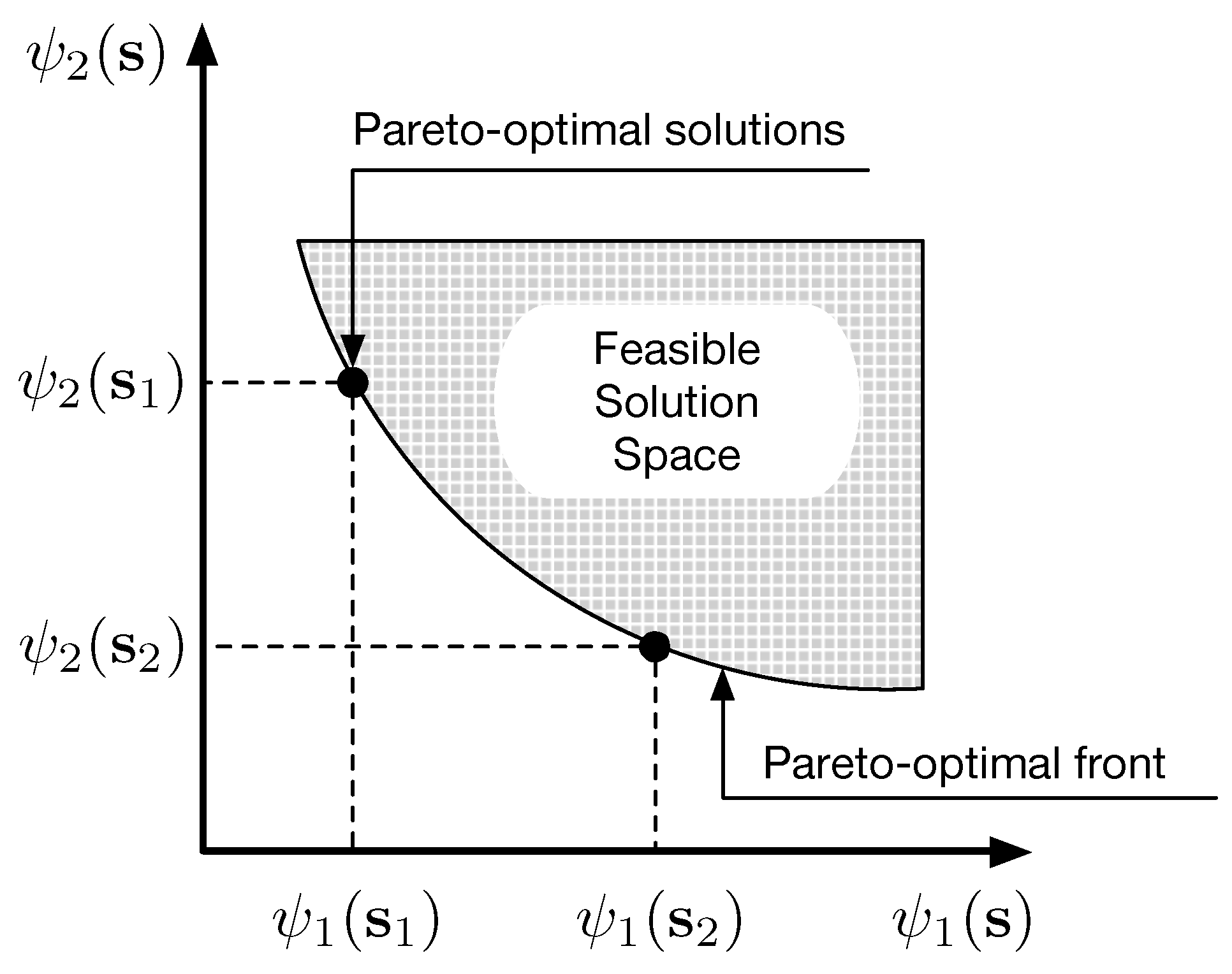
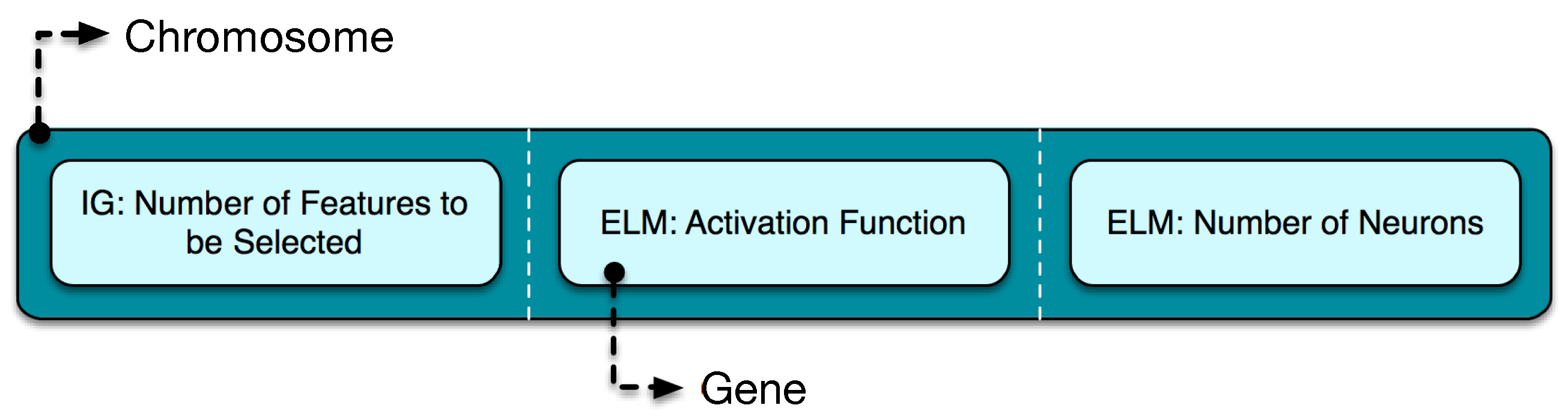
3.4. Multi-Objective Optimization
- Discrete crossover operator: If a discrete variable takes its values in a set , given two parents and such as and , a random number u is taken in and the indicesare generated, r being the rounding-off operator. This way, two children and with discrete variable and are produced, both and being in the range .
- Discrete mutation operator: A discrete variable is mutated replacing it by a randomly chosen element of set.
3.5. Classification
4. Experiments
4.1. Experimental Settings
4.1.1. Dataset
4.1.2. Pre-Processing
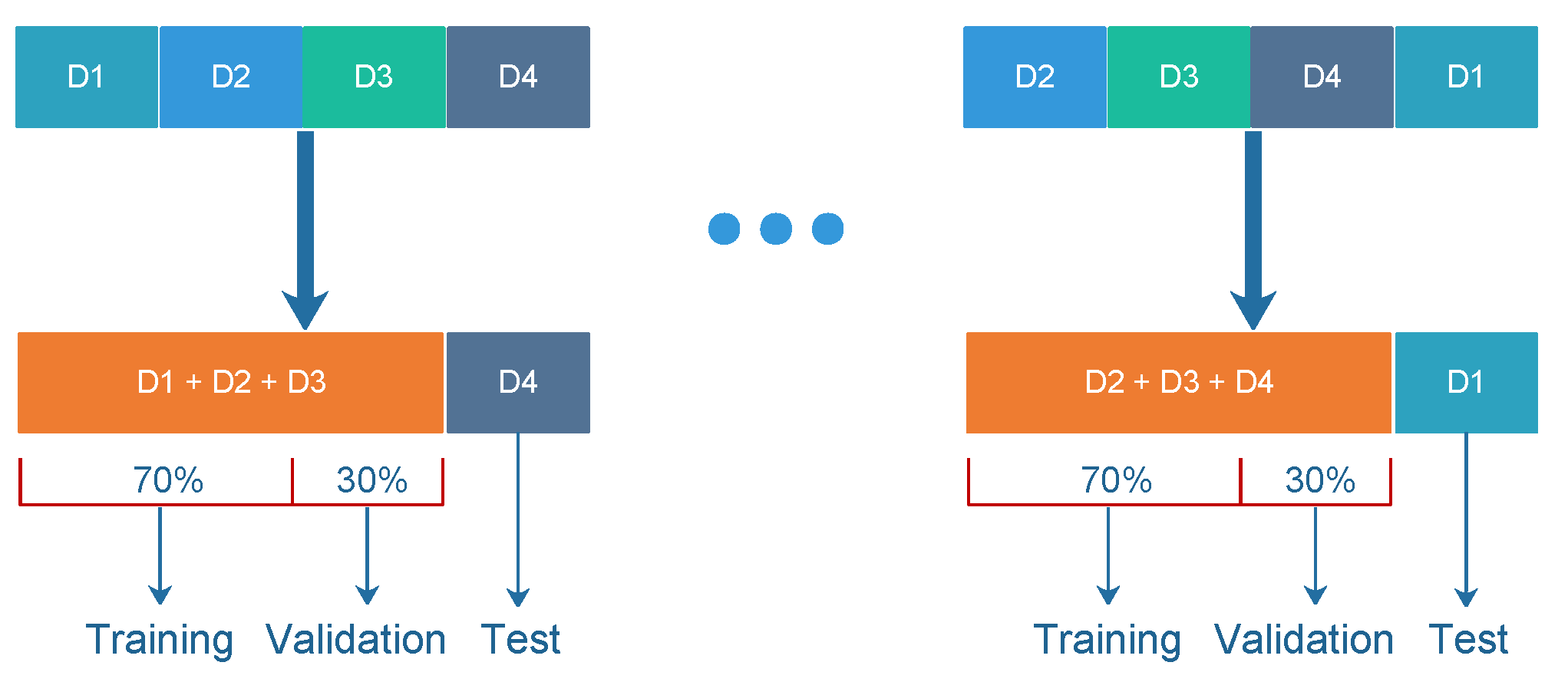
4.1.3. K-Fold Cross-Validation
4.1.4. Training Parameters
4.1.5. Performance Measures
4.2. Experimental Results
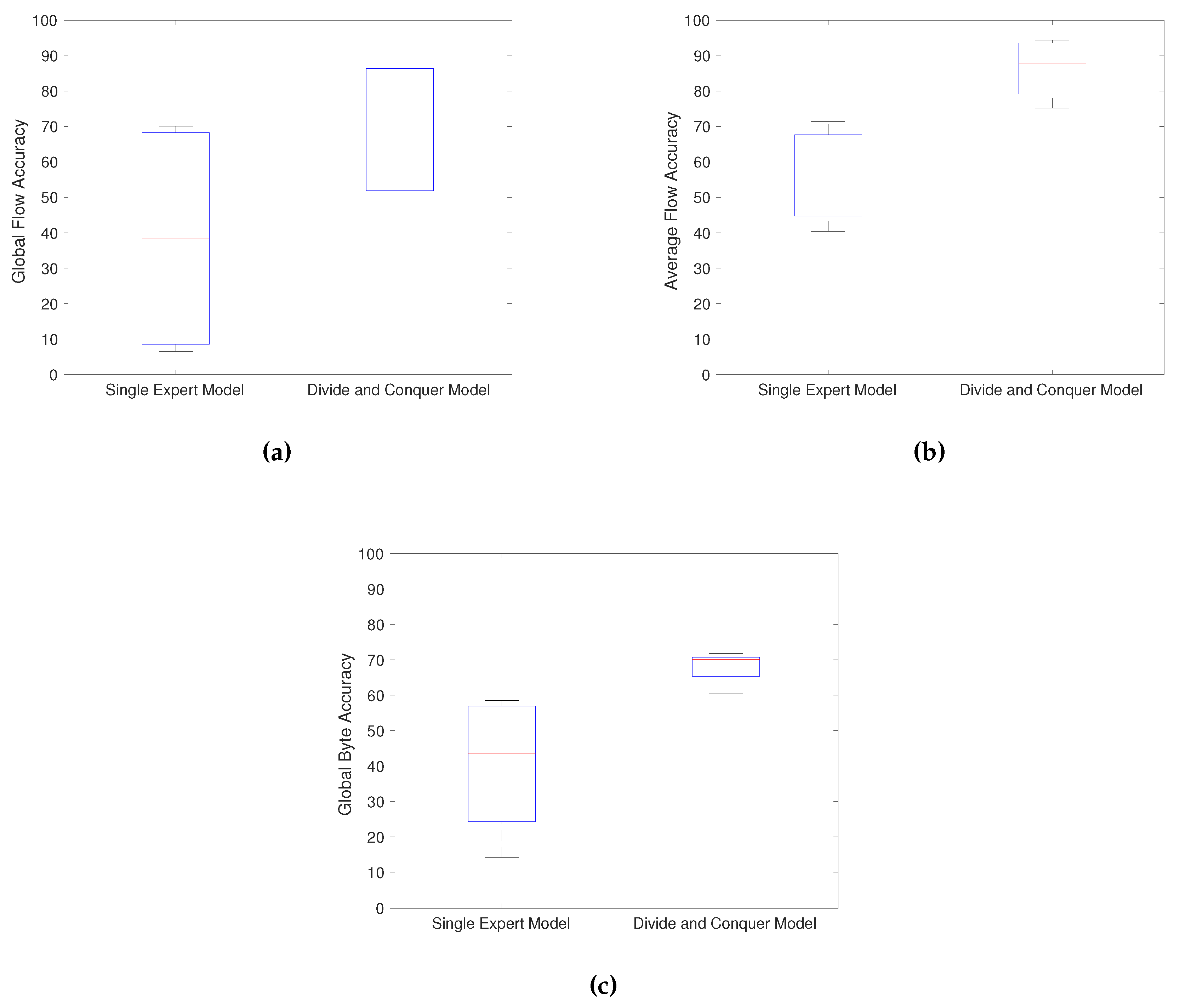
4.2.1. Analysis of the Divide and Conquer Strategy
4.2.2. Analysis of the Pareto-Optimal Solutions
4.2.3. Execution Time
4.2.4. Comparison between the MODC Model and DPI-Based Tools
4.2.5. A Deeper Analysis
4.2.6. Comparison with Other Machine Learning Methods
5. Conclusions
Author Contributions
Acknowledgments
Conflicts of Interest
Appendix A. Extracted Features
| Feature | Description |
| Proto | Transaction protocol |
| sTtl | Src dst TTL value |
| dTtl | Dst src TTL value |
| TotPkts | Total transaction packet count |
| SrcPkts | Src dst packet count |
| DstPkts | Dst src packet count |
| TotBytes | Total transaction bytes |
| SrcBytes | Src dst transaction bytes |
| DstBytes | Dst src transaction bytes |
| TotAppBytes | Total application bytes |
| SAppBytes | Src dst application bytes |
| DAppBytes | Dst src application bytes |
| Load | Bits per second |
| SrcLoad | Source bits per second |
| DstLoad | Destination bits per second |
| Loss | Pkts retransmitted or dropped |
| SrcLoss | Source pkts retransmitted or dropped |
| DstLoss | Destination pkts retransmitted or dropped |
| pLoss | Percent pkts retransmitted or dropped |
| SrcGap | Source bytes missing in the data stream |
| DstGap | Destination bytes missing in the data stream |
| Rate | Pkts per second |
| SrcRate | Source pkts per second |
| DstRate | Destination pkts per second |
| SIntPkt | Source interpacket arrival time (mSec) |
| SIntPktAct | Source active interpacket arrival time (mSec) |
| SIntPktIdl | Source idle interpacket arrival time (mSec) |
| DIntPkt | Destination interpacket arrival time (mSec) |
| DIntPktAct | Destination active interpacket arrival time (mSec) |
| DIntPktIdl | Destination idle interpacket arrival time (mSec) |
| TcpRtt | TCP connection setup round-trip time, the sum of “synack” and “ackdat” |
| SynAck | TCP conn. setup time, the time between the SYN and the SYN_ACK packets |
| AckDat | TCP conn. setup time, the time between the SYN_ACK and the ACK packets |
| sMaxPktSz | Maximum packet size for traffic transmitted by the src |
| dMaxPktSz | Maximum packet size for traffic transmitted by the dst |
| sMinPktSz | Minimum packet size for traffic transmitted by the src |
| dMinPktSz | Minimum packet size for traffic transmitted by the dst |
| Dur | Record total duration |
| RunTime | Total active flow run time |
| Mean | Average duration of aggregated records |
| Sum | Total accumulated durations of aggregated records |
| Min | Minimum duration of aggregated records |
| Max | Maximum duration of aggregated records |
References
- Wang, Y.; Ke, W.; Tao, X. A feature selection method for large-scale network traffic classification based on Spark. Information 2016, 7, 6. [Google Scholar] [CrossRef]
- Ertam, F.; Avcı, E. A new approach for internet traffic classification: GA-WK-ELM. Measurement 2017, 95, 135–142. [Google Scholar] [CrossRef]
- Schmidt, B.; Al-Fuqaha, A.; Gupta, A.; Kountanis, D. Optimizing an artificial immune system algorithm in support of flow-Based internet traffic classification. Appl. Soft Comput. 2017, 54, 1–22. [Google Scholar] [CrossRef]
- Shi, H.; Li, H.; Zhang, D.; Cheng, C.; Wu, W. Efficient and robust feature extraction and selection for traffic classification. Comput. Netw. 2017, 119, 1–16. [Google Scholar] [CrossRef]
- Peng, L.; Zhang, H.; Chen, Y.; Yang, B. Imbalanced traffic identification using an imbalanced data gravitation-based classification model. Compet. Comm. 2017, 102, 177–189. [Google Scholar] [CrossRef]
- Gómez, S.E.; Martínez, B.C.; Sánchez-Esguevillas, A.J.; Hernández Callejo, L. Ensemble network traffic classification: Algorithm comparison and novel ensemble scheme proposal. Comput. Netw. 2017, 127, 68–80. [Google Scholar] [CrossRef]
- Ijaz, S.; Hashmi, F.A.; Asghar, S.; Alam, M. Vector Based Genetic Algorithm to optimize predictive analysis in network security. Appl. Intell. 2017, 48, 1086–1096. [Google Scholar] [CrossRef]
- Benmessahel, I.; Xie, K.; Chellal, M. A new evolutionary neural networks based on intrusion detection systems using multiverse optimization. Appl. Intell. 2017, 48, 2315–2327. [Google Scholar] [CrossRef]
- Hajjar, A.; Khalife, J.; Díaz-Verdejo, J. Network traffic application identification based on message size analysis. J. Netw. Comput. Appl. 2015, 58, 130–143. [Google Scholar] [CrossRef]
- Peng, L.; Yang, B.; Chen, Y. Effective packet number for early stage internet traffic identification. Neurocomputing 2015, 156, 252–267. [Google Scholar] [CrossRef]
- Divakaran, D.M.; Su, L.; Liau, Y.S.; Vrizlynn, V.L. SLIC: Self-Learning Intelligent Classifier for network traffic. Comput. Netw. 2015, 91, 283–297. [Google Scholar] [CrossRef]
- Alshammari, R.; Nur Zincir-Heywood, A. Identification of VoIP encrypted traffic using a machine learning approach. J. King Saud Univ. Comput. Inf. Sci. 2015, 27, 77–92. [Google Scholar] [CrossRef]
- Megyesi, P.; Szabó, G.; Molnár, S. User behavior based traffic emulator: A framework for generating test data for DPI tools. Comput. Netw. 2015, 92, 41–54. [Google Scholar] [CrossRef]
- Bujlow, T.; Carela-Español, V.; Barlet-Ros, P. Independent comparison of popular DPI tools for traffic classification. Comput. Netw. 2015, 76, 75–89. [Google Scholar] [CrossRef] [Green Version]
- Singh, R.; Kumar, H.; Singla, R.K. An intrusion detection system using network traffic profiling and online sequential extreme learning machine. Expert Syst. Appl. 2015, 42, 8609–8624. [Google Scholar] [CrossRef]
- Rizzi, A.; Iacovazzi, A.; Baiocchi, A.; Colabrese, S. A low complexity real-time Internet traffic flows neuro-fuzzy classifier. Comput. Netw. 2015, 91, 752–771. [Google Scholar] [CrossRef]
- Namdev, N.; Agrawal, S.; Silkari, S. Recent Advancement in Machine Learning Based Internet Traffic Classification. Procedia Comput. Sci. 2015, 60, 784–791. [Google Scholar] [CrossRef]
- Biswas, A.R.; Giaffreda, R. IoT and Cloud Convergence: Opportunities and Challenges. In Proceedings of the 2014 IEEE World Forum on Internet of Things (WF-IoT), Seoul, Korea, 6–8 March 2014. [Google Scholar]
- Tsiropoulou, E.E.; Paruchuri, S.T.; Baras, J.S. Interest, energy and physical-aware coalition formation and resource allocation in smart IoT applications. In Proceedings of the 2017 51st Annual Conference on Information Sciences and Systems (CISS), Baltimore, MD, USA, 22–24 March 2017. [Google Scholar]
- Meidan, Y.; Bohadana, M.; Shabtai, A.; Guarnizo, J.D.; Ochoa, M.; Ole Tippenhauer, N.; Elovici, Y. ProfilIoT: A Machine Learning Approach for IoT Device Identification Based on Network Traffic Analysis. In Proceedings of the Symposium on Applied Computing (ACM), Marrakech, Morocco, 3–7 April 2017. [Google Scholar]
- Diro, A.A.; Chilamkurti, N. Distributed attack detection scheme using deep learning approach for Internet of Things. Future Gener. Comput. Syst. 2018, 82, 761–768. [Google Scholar] [CrossRef]
- Kim, J.Y.; Bu, S.J.; Cho, S.B. Zero-day malware detection using transferred generative adversarial networks based on deep autoencoders. Informing Sci. 2018, 460–461, 83–102. [Google Scholar] [CrossRef]
- Kozik, R. Distributing extreme learning machines with Apache Spark for NetFlow-based malware activity detection. Pattern Recogn. Lett. 2018, 101, 14–20. [Google Scholar] [CrossRef]
- Zhang, Q.; Yang, L.T.; Chen, Z.; Li, P. A survey on deep learning for big data. Inf. Fusion 2018, 42, 146–157. [Google Scholar] [CrossRef]
- Boutaba, R.; Salahuddin, M.A.; Limam, N.; Ayoubi, S.; Shahriar, N.; Estrada-solano, F.; Caicedo, O.M. A comprehensive survey on machine learning for networking: Evolution, applications and research opportunities. J. Internet Serv. Appl. 2018, 9, 16. [Google Scholar] [CrossRef]
- Antonello, R.; Fernandes, S.; Kamienski, C.; Sadok, D.; Kelner, J.; Gódor, I.; Szabó, G.; Westholm, T. Deep packet inspection tools and techniques in commodity platforms: Challenges and trends. J. Netw. Comput. Appl. 2012, 35, 1863–1878. [Google Scholar] [CrossRef]
- La Mantia, G.; Rossi, D.; Finamore, A.; Mellia, M.; Meo, M. Stochastic Packet Inspection for TCP Traffic. In Proceedings of the 2010 IEEE International Conference on Communications, Cape Town, South Africa, 23–27 May 2010; pp. 1–6. [Google Scholar]
- Sun, G.; Dong, H.; Li, D.; Xiao, F. NTCA: A high-performance network traffic classification architecture. Int. J. Future Gener. Commun. Netw. 2013, 6, 11–20. [Google Scholar] [CrossRef]
- Fernandes, S.; Antonello, R.; Lacerda, T.; Santos, A.; Sadok, D.; Westholm, T. Slimming Down Deep Packet Inspection Systems. In Proceedings of the IEEE INFOCOM Workshops 2009, Rio de Janeiro, Brazil, 19–25 April 2009; pp. 1–6. [Google Scholar]
- Callado, A.; Kelner, J.; Sadok, D.; Alberto Kamienski, C.; Fernandes, S. Better network traffic identification through the independent combination of techniques. J. Netw. Comput. Appl. 2010, 33, 433–446. [Google Scholar] [CrossRef]
- Khalife, J.; Hajjar, A.; Díaz-Verdejo, J.E. A multilevel taxonomy and requirements for an optimal traffic-classification model. Int. J. Netw. Manag. 2014, 24, 101–120. [Google Scholar] [CrossRef]
- Nascimento, Z.; Sadok, D.; Fernandes, S. Comparative study of a Hybrid Model for network traffic identification and its optimization using Firefly Algorithm. In Proceedings of the 2013 IEEE Symposium on Computers and Communications (ISCC), Split, Croatia, 7–10 July 2013; pp. 000862–000867. [Google Scholar]
- Shi, H.; Li, H.; Zhang, D.; Cheng, C.; Cao, X. An efficient feature generation approach based on deep learning and feature selection techniques for traffic classification. Comput. Netw. 2018, 132, 81–98. [Google Scholar] [CrossRef]
- Liu, Z.; Wang, R.; Tao, M.; Cai, X. A class-oriented feature selection approach for multi-class imbalanced network traffic datasets based on local and global metrics fusion. Neurocomputing 2015, 168, 365–381. [Google Scholar] [CrossRef]
- Dainotti, A.; Pescape, A.; Claffy, K. Issues and future directions in traffic classification. IEEE Netw. 2012, 26, 35–40. [Google Scholar] [CrossRef] [Green Version]
- Jacobs, R.A.; Jordan, M.I.; Nowlan, S.J.; Hinton, G.E. Adaptive Mixtures of Local Experts. Neural. Comput. 1991, 3, 79–87. [Google Scholar] [CrossRef]
- Rauber, A.; Merkl, D.; Dittenbach, M. The growing hierarchical self-organizing map: Exploratory analysis of high-dimensional data. IEEE Trans. Neural Netw. 2002, 13, 1331–1341. [Google Scholar] [CrossRef] [PubMed]
- Huang, G.B.; Zhu, Q.Y.; Siew, C.K. Extreme learning machine: Theory and applications. Neurocomputing 2006, 70, 489–501. [Google Scholar] [CrossRef] [Green Version]
- Wang, R.Y.; Liu, Z.; Zhang, L. Method of data cleaning for network traffic classification. J. China Univ. Posts Telecommun. 2014, 21, 35–45. [Google Scholar] [CrossRef]
- Nascimento, Z.; Sadok, D.; Fernandes, S. A Hybrid Model for Network Traffic Identification Based on Association Rules and Self-Organizing Maps (SOM). In Proceedings of the Ninth International Conference on Networking and Services, ICNS 2013, Lisbon, Portugal, 24–29 March 2013; pp. 213–219. [Google Scholar]
- Nascimento, Z.; Sadok, D.; Fernandes, S.; Kelner, J. Multi-objective optimization of a hybrid model for network traffic classification by combining machine learning techniques. In Proceedings of the 2014 International Joint Conference on Neural Networks (IJCNN), Beijing, China, 6–11 July 2014; pp. 2116–2122. [Google Scholar]
- Zhang, J.; Xiang, Y.; Zhou, W.; Wang, Y. Unsupervised traffic classification using flow statistical properties and {IP} packet payload. J. Comput. Syst. Sci. 2013, 79, 573–585. [Google Scholar] [CrossRef]
- Huang, S.Y.; Huang, Y.N. Network traffic anomaly detection based on growing hierarchical SOM. In Proceedings of the 2013 43rd Annual IEEE/IFIP International Conference on Dependable Systems and Networks (DSN), Budapest, Hungary, 24–27 June 2013; pp. 1–2. [Google Scholar]
- Liu, Y.; Li, W.; Li, Y.C. Network Traffic Classification Using K-means Clustering. In Proceedings of the Second International Multi-Symposiums on Computer and Computational Sciences (IMSCCS 2007), Iowa City, IA, USA, 13–15 August 2007; pp. 360–365. [Google Scholar]
- Li, D.; Hu, G.; Wang, Y.; Pan, Z. Network traffic classification via non-convex multi-task feature learning. Neurocomputing 2015, 152, 322–332. [Google Scholar] [CrossRef]
- Lin, G.Z.; Xin, Y.; Niu, X.X.; Jiang, H.B. Network traffic classification based on semi-supervised clustering. J. China Univ. Posts Telecommun. 2010, 17, 84–88. [Google Scholar] [CrossRef]
- De La Hoz, E.; De La Hoz, E.; Ortiz, A.; Ortega, J.; Martínez-Álvarez, A. Feature selection by multi-objective optimisation: Application to network anomaly detection by hierarchical self-organising maps. Knowl. Based Syst. 2014, 71, 322–338. [Google Scholar] [CrossRef]
- Ostaszewski, M.; Bouvry, P.; Seredynski, F. Multiobjective classification with moGEP: An application in the network traffic domain. In Proceedings of the 11th Annual Conference on Genetic and Evolutionary Computation, Montreal, QC, Canada, 8–12 July 2009; pp. 635–642. [Google Scholar]
- Bacquet, C.; Zincir-Heywood, A.N.; Heywood, M.I. Genetic optimization and hierarchical clustering applied to encrypted traffic identification. In Proceedings of the 2011 IEEE Symposium on Computational Intelligence in Cyber Security (CICS), Paris, France, 11–15 April 2011; pp. 194–201. [Google Scholar]
- Mitchell, T.M. Machine Learning; McGraw-Hill, Inc.: New York, NY, USA, 1997. [Google Scholar]
- Fayyad, U.M.; Irani, K.B. Multi-Interval Discretization of Continuous-Valued Attributes for Classification Learning. In Proceedings of the 13th International Joint Conference on Uncertainly in Artificial Intelligence (IJCAI93), Chambery, France, 28 August–3 September 1993; pp. 1022–1029. [Google Scholar]
- Kohonen, T. The Self-Organizing Map. Proc. IEEE 1990, 78, 1464–1480. [Google Scholar] [CrossRef]
- Konak, A.; Coit, D.W.; Smith, A.E. Multi-objective optimization using genetic algorithms: A tutorial. Reliab. Eng. Syst. Saf. 2006, 91, 992–1007. [Google Scholar] [CrossRef]
- Holland, J.H. Adaptation in Natural and Artificial Systems: An Introductory Analysis with Applications to Biology, Control, and Artificial Intelligence; MIT Press: Michigan, MI, USA, 1975; p. 183. [Google Scholar]
- Le Besnerais, J.; Lanfranchi, V.; Hecquet, M.; Brochet, P. Multiobjective Optimization of Induction Machines Including Mixed Variables and Noise Minimization. IEEE Trans. Magn. 2008, 44, 1102–1105. [Google Scholar] [CrossRef]
- Ren Cheng, Y. Evolutionary Game Theoretic Multi-Objective Optimization Algorithms and Their Applications. Ph.D. Thesis, University of Massachusetts Boston, Boston, MA, USA, May 2017. [Google Scholar]
- Tsiropoulou, E.E.; Katsinis, G.K.; Papavassiliou, S. Distributed uplink power control in multiservice wireless networks via a game theoretic approach with convex pricing. IEEE Trans. Parallel Distrib. Syst. 2012, 23, 61–68. [Google Scholar] [CrossRef]
- Saraydar, C.U.; Mandayam, N.B.; Goodman, D.J. Efficient power control via pricing in wireless data networks. IEEE Trans. Commun. 2002, 50, 291–303. [Google Scholar] [CrossRef] [Green Version]
- Wang, H.; Wang, W.; Cui, L.; Sun, H.; Zhao, J.; Wang, Y.; Xue, Y. A hybrid multi-objective firefly algorithm for big data optimization. Appl. Soft Comput. J. 2018, 69, 806–815. [Google Scholar] [CrossRef]
- Gunantara, N. A review of multi-objective optimization: Methods and its applications. Cogent Eng. 2018, 1–16, (Paper accepted). [Google Scholar] [CrossRef]
- Cui, Y.; Geng, Z.; Zhu, Q.; Han, Y. Review: Multi-objective optimization methods and application in energy saving. Energy 2017, 125, 681–704. [Google Scholar] [CrossRef]
- Vachhani, V.L.; Dabhi, V.K.; Prajapati, H.B. Survey of multi objective evolutionary algorithms. In Proceedings of the 2011 IEEE Symposium on Computational Intelligence in Cyber Security (CICS), Paris, France, 11–15 April 2011; pp. 1–9. [Google Scholar]
- Fazzolari, M.; Alcala, R.; Nojima, Y.; Ishibuchi, H.; Herrera, F. A review of the application of multiobjective evolutionary fuzzy systems: Current status and further directions. IEEE Trans. Fuzzy Syst. 2013, 21, 45–65. [Google Scholar] [CrossRef]
- Carela-español, V.; Bujlow, T.; Barlet-Ros, P. Is Our Ground-Truth for Traffic Classification Reliable? In Passive and Active Measurement; Springer International Publishing: New York, NY, USA, 2014; pp. 98–108. [Google Scholar]
- Catalunya. Traffic Classification at the Universitat Politècnica de Catalunya (UPC). Available online: http://www.cba.upc.edu/monitoring/traffic-classification (accessed on 9 August 2018).
- Bujlow, T.; Balachandran, K.; Riaz, T.; Pedersen, J.M. Volunteer-based system for classification of traffic in computer networks. In Proceedings of the 19th Telecommunications Forum TELFOR 2011, Belgrade, Serbia, 22–24 November 2011; pp. 210–213. [Google Scholar]
- Bujlow, T.; Carela-espa, V.; Barlet-ros, P. Comparison of Deep Packet Inspection (DPI) Tools for Traffic Classification. Available online: vbn.aau.dk/ws/files/78068418/report.pdf (accessed on 12 September 2018).
- He, H.; Garcia, E.A. Learning from imbalanced data. IEEE Trans. Knowl. Data Eng. 2009, 21, 1263–1284. [Google Scholar]

| Application | Flows | Megabytes (MB) |
|---|---|---|
| Edonkey | 176,584 | 2815.1 |
| BitTorrent | 62,951 | 2457 |
| FTP | 882 | 3118.1 |
| DNS | 6600 | 1.91 |
| NTP | 27,786 | 4.77 |
| RDP | 132,934 | 11,396 |
| NETBIOS | 9445 | 5.99 |
| SSH | 26,219 | 100.88 |
| Browser HTTP | 46,669 | 5813.6 |
| Browser RTMP | 427 | 3103 |
| Unclassified | 44,941 | 5617.5 |
| TOTAL | 535,438 | 34,433.85 |
| Performance Measure | Description |
|---|---|
| Global Flow Accuracy | |
| Global Byte Accuracy | |
| Recall in Flows | |
| Recall in Bytes | |
| Precision | |
| Average Flow Accuracy | |
| Average Precision Accuracy |
| D1 | D2 | D3 | D4 | |
|---|---|---|---|---|
| # Neurons | 299 | 218 | 252 | 391 |
| Act. Func. | Sig. | Rad. | Rad. | Sine |
| # Features | 41 | 41 | 42 | 43 |
| 89.12 | 89.47 | 89.87 | 89.88 | |
| 94.38 | 94.27 | 93.90 | 93.17 | |
| 69.56 | 78.29 | 70.40 | 67.61 |
| D1 | D2 | D3 | D4 | |
|---|---|---|---|---|
| # Neurons | 358 | 262 | 223 | 274 |
| Act. Func. | Rad. | Sine | Tri. | Sine |
| # Features | 34 | 41 | 37 | 26 |
| 87.87 | 89.41 | 85.84 | 74.88 | |
| 92.97 | 94.18 | 92.48 | 88.06 | |
| 78.43 | 82.42 | 80.65 | 73.33 |
| D1 | D2 | D3 | D4 | |
|---|---|---|---|---|
| GHSOM | ||||
| ELM | ||||
| MOGA | ||||
| Classification |
| App. | Clas. | Cor. | Wro. | Unc. | App. | Clas. | Cor. | Wro. | Unc. |
|---|---|---|---|---|---|---|---|---|---|
| EDK | PACE | 94.80 | 0.02 | 5.18 | SSH | PACE | 95.57 | 0.00 | 4.43 |
| ODPI | 0.45 | 0.00 | 99.55 | ODPI | 95.59 | 0.00 | 4.41 | ||
| L7F | 34.21 | 13.70 | 52.09 | L7F | 95.71 | 0.00 | 4.29 | ||
| NDPI | 0.45 | 6.72 | 92.83 | NDPI | 95.59 | 0.00 | 4.41 | ||
| LIB | 98.39 | 0.00 | 1.60 | LIB | 95.71 | 0.00 | 4.30 | ||
| NBAR | 0.38 | 10.81 | 88.81 | NBAR | 99.24 | 0.05 | 0.70 | ||
| MODC | 96.48 | 3.41 | 0.11 | MODC | 99.50 | 0.31 | 0.19 | ||
| BTR | PACE | 81.44 | 0.01 | 18.54 | RDP | PACE | 99.04 | 0.02 | 0.94 |
| ODPI | 27.23 | 0.00 | 72.77 | ODPI | 99.07 | 0.02 | 0.91 | ||
| L7F | 42.17 | 8.78 | 49.05 | L7F | 0.00 | 91.21 | 8.79 | ||
| NDPI | 56.00 | 0.43 | 43.58 | NDPI | 99.05 | 0.08 | 0.87 | ||
| LIB | 77.24 | 0.06 | 22.71 | LIB | 98.83 | 0.16 | 1.01 | ||
| NBAR | 27.44 | 1.49 | 71.07 | NBAR | 0.00 | 0.66 | 99.34 | ||
| MODC | 92.26 | 7.23 | 0.51 | MODC | 98.86 | 1.04 | 0.10 | ||
| FTP | PACE | 95.92 | 0.00 | 4.08 | NETB | PACE | 66.66 | 0.08 | 33.26 |
| ODPI | 96.15 | 0.00 | 3.85 | ODPI | 24.63 | 0.00 | 75.37 | ||
| L7F | 6.11 | 93.31 | 0.57 | L7F | 0.00 | 8.45 | 91.55 | ||
| NDPI | 95.69 | 0.45 | 3.85 | NDPI | 100.00 | 0.00 | 0.00 | ||
| LIB | 95.58 | 0.00 | 4.42 | LIB | 0.00 | 5.03 | 94.97 | ||
| NBAR | 40.59 | 0.00 | 4.42 | NBAR | 100.00 | 0.00 | 0.00 | ||
| MODC | 86.62 | 5.10 | 8.28 | MODC | 99.67 | 0.33 | 0.00 | ||
| DNS | PACE | 99.97 | 0.00 | 0.03 | RTMP | PACE | 80.56 | 0.00 | 19.44 |
| ODPI | 99.97 | 0.00 | 0.03 | ODPI | 82.44 | 0.00 | 17.56 | ||
| L7F | 98.95 | 0.13 | 0.92 | L7F | 0.00 | 24.12 | 75.88 | ||
| NDPI | 99.88 | 0.09 | 0.03 | NDPI | 78.92 | 8.90 | 12.18 | ||
| LIB | 99.97 | 0.00 | 0.04 | LIB | 77.28 | 0.47 | 22.25 | ||
| NBAR | 99.97 | 0.00 | 0.04 | NBAR | 0.23 | 0.23 | 99.53 | ||
| MODC | 94.29 | 0.50 | 5.21 | MODC | 77.05 | 14.75 | 8.20 | ||
| NTP | PACE | 100.00 | 0.00 | 0.00 | HTTP | PACE | 96.16 | 1.85 | 1.99 |
| ODPI | 100.00 | 0.00 | 0.00 | ODPI | 98.01 | 0.00 | 1.99 | ||
| L7F | 99.83 | 0.15 | 0.02 | L7F | 4.31 | 95.67 | 0.02 | ||
| NDPI | 100.00 | 0.00 | 0.00 | NDPI | 99.18 | 0.76 | 0.06 | ||
| LIB | 100.00 | 0.00 | 0.00 | LIB | 98.66 | 0.00 | 1.34 | ||
| NBAR | 0.40 | 0.00 | 99.60 | NBAR | 99.58 | 0.00 | 0.42 | ||
| MODC | 99.91 | 0.05 | 0.04 | MODC | 96.73 | 2.12 | 1.14 |
| Classifier | ||
|---|---|---|
| PACE | 94.22 | 91.01 |
| OpenDPI | 52.67 | 72.35 |
| L7-filter | 30.26 | 38.13 |
| NDPI | 57.91 | 82.48 |
| Libprotoident | 93.86 | 84.16 |
| NBAR | 21.79 | 46.72 |
| MODC | 89.60 | 94.14 |
| Application | Precision | ||
|---|---|---|---|
| Edonkey | 82.85 | 96.48 | 41.31 |
| BitTorrent | 88.73 | 92.26 | 43.91 |
| FTP | 33.00 | 86.62 | 83.42 |
| DNS | 11.31 | 94.29 | 94.15 |
| NTP | 94.30 | 99.91 | 99.93 |
| SSH | 82.10 | 99.50 | 99.57 |
| RDP | 99.21 | 98.86 | 99.87 |
| NETBIOS | 93.20 | 99.67 | 99.77 |
| RTMP | 13.24 | 77.05 | 65.17 |
| HTTP | 64.07 | 96.73 | 69.54 |
| Application | Precision | ||
|---|---|---|---|
| Edonkey | 78.60 | 89.67 | 91.27 |
| BitTorrent | 84.63 | 90.04 | 92.24 |
| FTP | 58.14 | 80.16 | 91.95 |
| DNS | 10.14 | 81.46 | 89.24 |
| NTP | 76.09 | 99.94 | 99.98 |
| SSH | 83.29 | 99.37 | 99.47 |
| RDP | 99.48 | 98.82 | 98.31 |
| NETBIOS | 71.85 | 98.92 | 98.48 |
| RTMP | 23.16 | 63.93 | 86.57 |
| HTTP | 87.68 | 85.65 | 88.67 |
| S-MODC | M-MODC | |
|---|---|---|
| GFA | 89.60 | 88.97 |
| GBA | 72.69 | 89.59 |
| AFA | 94.14 | 88.80 |
| APA | 69.25 | 70.11 |
| S-MODC | M-MODC | ELM | Naïve B. | kNN | C4.5 | Softmax | |
|---|---|---|---|---|---|---|---|
| GFA | 89.60 | 88.97 | 81.37 | 58.05 | 82.70 | 86.37 | 76.39 |
| GBA | 72.69 | 89.59 | 51.90 | 44.36 | 60.60 | 61.29 | 60.90 |
| AFA | 94.14 | 88.80 | 84.07 | 60.18 | 88.21 | 88.79 | 79.36 |
| APA | 69.25 | 70.11 | 61.62 | 55.58 | 63.27 | 70.67 | 57.75 |
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Nascimento, Z.; Sadok, D. MODC: A Pareto-Optimal Optimization Approach for Network Traffic Classification Based on the Divide and Conquer Strategy. Information 2018, 9, 233. https://doi.org/10.3390/info9090233
Nascimento Z, Sadok D. MODC: A Pareto-Optimal Optimization Approach for Network Traffic Classification Based on the Divide and Conquer Strategy. Information. 2018; 9(9):233. https://doi.org/10.3390/info9090233
Chicago/Turabian StyleNascimento, Zuleika, and Djamel Sadok. 2018. "MODC: A Pareto-Optimal Optimization Approach for Network Traffic Classification Based on the Divide and Conquer Strategy" Information 9, no. 9: 233. https://doi.org/10.3390/info9090233
APA StyleNascimento, Z., & Sadok, D. (2018). MODC: A Pareto-Optimal Optimization Approach for Network Traffic Classification Based on the Divide and Conquer Strategy. Information, 9(9), 233. https://doi.org/10.3390/info9090233





