2. Related Work
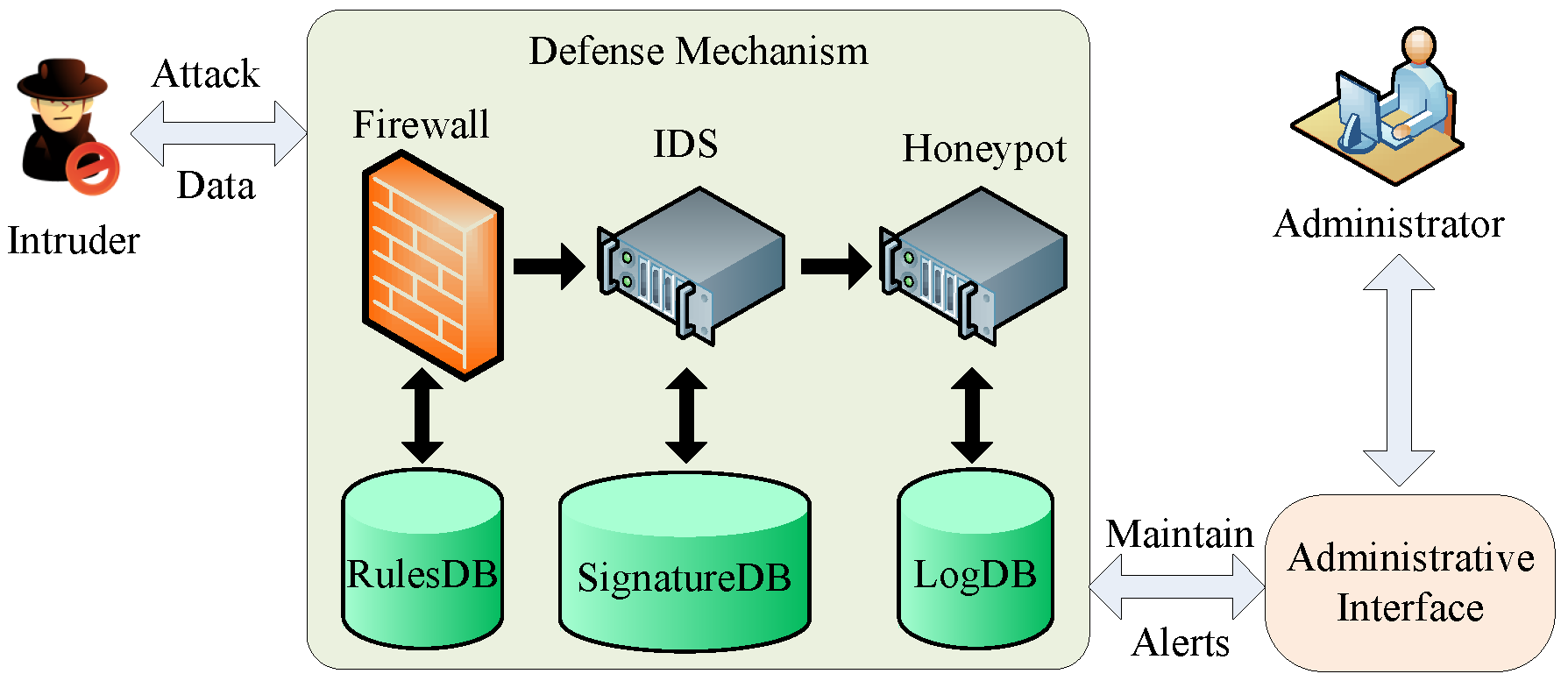
During the last decade, various viruses, worms, Trojan horses and malicious codes have puzzled the Internet. Many solutions have been proposed to solve these problems. However, most of the traditional countermeasures, such as firewall and Intrusion Detection Systems (IDS), are passive in nature. The adversaries can attack the conspicuous server at any time and any place. The honeypot has been proposed to act as a trap for the adversaries. It can disturb and confuse the intruders. Thus, the honeypot is considered as an active mechanism for the defenders.
With the scale of the Internet being much bigger and the related technologies being more complex, how to model them and evaluate their performance becomes a significant problem. Researchers have conducted much works on modeling and estimating the performance of the systems with Petri nets in information security.
Mixia et al. [
8] presented the system architecture of the network security situation and modeled it with the Colored Petri Nets (CPN) in order to analyze the network security in the view of the system. Hicham et al. [
9] proposed a novel approach to detect network security conflicts more generically and specified it with CPN to perform automatic conflict analysis. In [
10], a model of Address Resolution Protocol (ARP) spoofing with Petri nets was proposed to validate the feasibility of ARP spoofing. Hwang et al. [
11] described the inference rules of computer forensics with Fuzzy Petri Nets (FPN). They extracted and analyzed the collected data from the compromised systems to infer the intrusion information.
Aliannezhadi et al. [
12] presented the architecture for web service firewall to protect web security and developed a formal CPN model of access control of the proposed web service firewall architecture. The CPN model of access control was proven to be effective with the simulation results.
Dolgikh et al. used CPN as the backbone of the proposed approach to define the functionality of interest as behavior signatures and to serve as the mechanism for the signature detection in IDS [
13]. With Petri nets, Voron et al. [
14] described a formal reference behavior model of the proposed novel approach that automatically generates host-based IDS from program sources. Balaz et al. [
15] proposed a new IDS architecture based on partially ordered events and a novel detection method that matches the intrusion signature with Petri nets. Toktabayev et al. [
16] proposed the IDS based on obfuscation-resilient behavior with CPN describing specific malicious functionality. Nykodym et al. [
17] improved the IDS proposed in [
16]. They constructed a functional model with CPN that tracks how to access and modify kernel objects.
In [
18], an advanced model of the Intrusion Tolerance System (ITS) was proposed, in which the performance of the model with SPN and the Markov process was evaluated. The simulation results showed that the system was secure and efficient. Wang et al. [
19] constructed the models of three types of ITS with Generalized Stochastic Petri Nets (GSPN). They analyzed and compared the three kinds of ITS models. The numerical results showed the availability of the three kinds of systems. Yang et al. [
20] presented a hybrid IDS based on protocol analysis and detection tree algorithms. They estimated the performance of the proposed system with the GSPN model. Shi et al. [
21] proposed a performance evaluation model of a service hopping system with SPN. They inferred and analyzed some parameters to estimate the model’s performance, validating the effectiveness of synchronous delay and data transfer efficiency.
Teo et al. [
22] proposed a security framework called Jeponica, with a honeypot as an active entity to detect and deal with the unknown attacks dynamically. They described the model of the framework proposed with CPN to discover a uniform message exchange format among the entities. The results showed that the framework could work effectively.
Besides, there are some other works related to Petri nets. By combining a regular Petri nets with fuzzy rules, a software system model called Intelligent Petri Net (I-PN) was proposed [
23], in which the runtime environment and system behavior can be modeled. I-PN features a self-adaption ability. In [
24], Petri nets were used for the physiochemical model, which was related to EGFR-Ras-MAPK. Siphon and proteins were involved in identifying targets for multi-component therapies in signaling pathways. Wiśniewski et al. [
25] used interpreted Petri nets to describe a concurrent control system. A prototyping technique of the system was proposed, dominating in polynomial time.
However, the aforementioned works are almost related to intrusion detection, web service firewall, ARP spoofing and system architecture in network security. In this paper, we focus on the combination of Petri nets [
26] and honeypot. Only in [
22], the honeypot was used as a component of the proposed framework, and CPN was involved, which is different from SPN. Therefore, as far as we know, there is no work related to both the honeypot and SPN. Such a scheme is proposed in this paper to analyze the performance of honeypot.
4. SPN-Based Modeling and Analysis
4.1. Stochastic Petri Nets
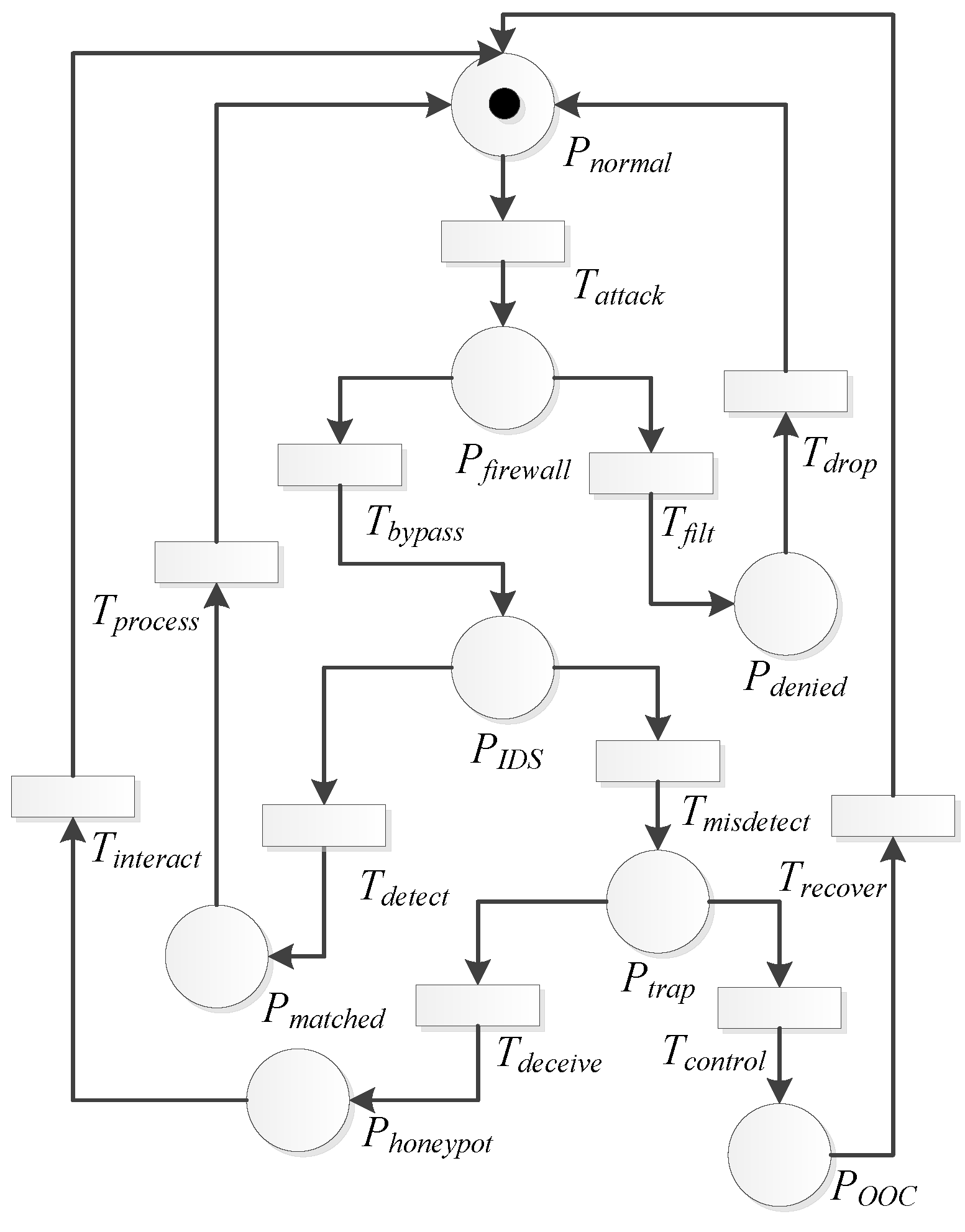
The SPN model is basically composed of three components: places, transitions and arcs. The places represent the states or resource of the system. The transitions represent the events that enable the system’s state transfer. The arcs illustrate the relationship between the places and transitions.
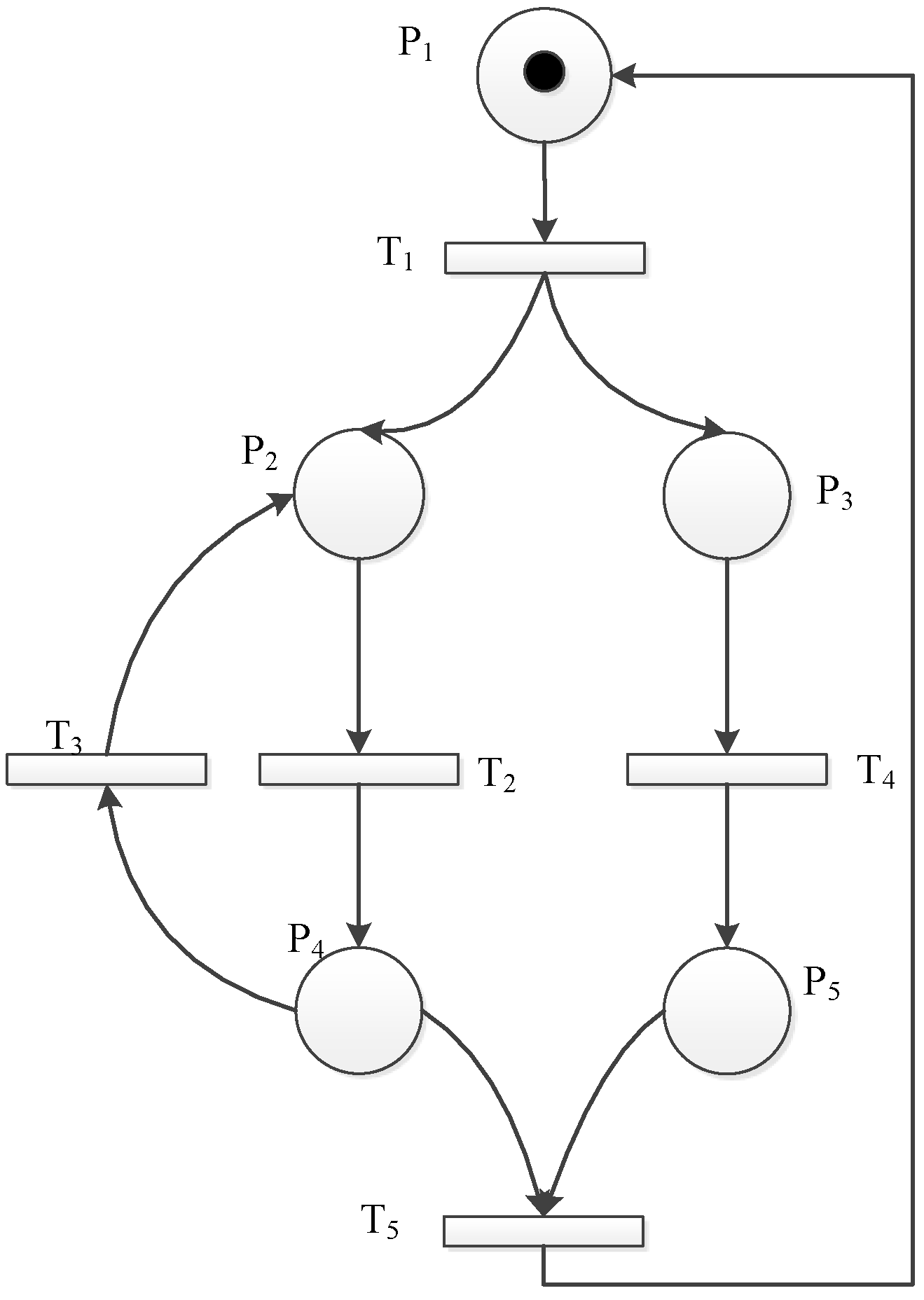
How can we estimate the performance of a system? Here, we give a sample to illustrate it.
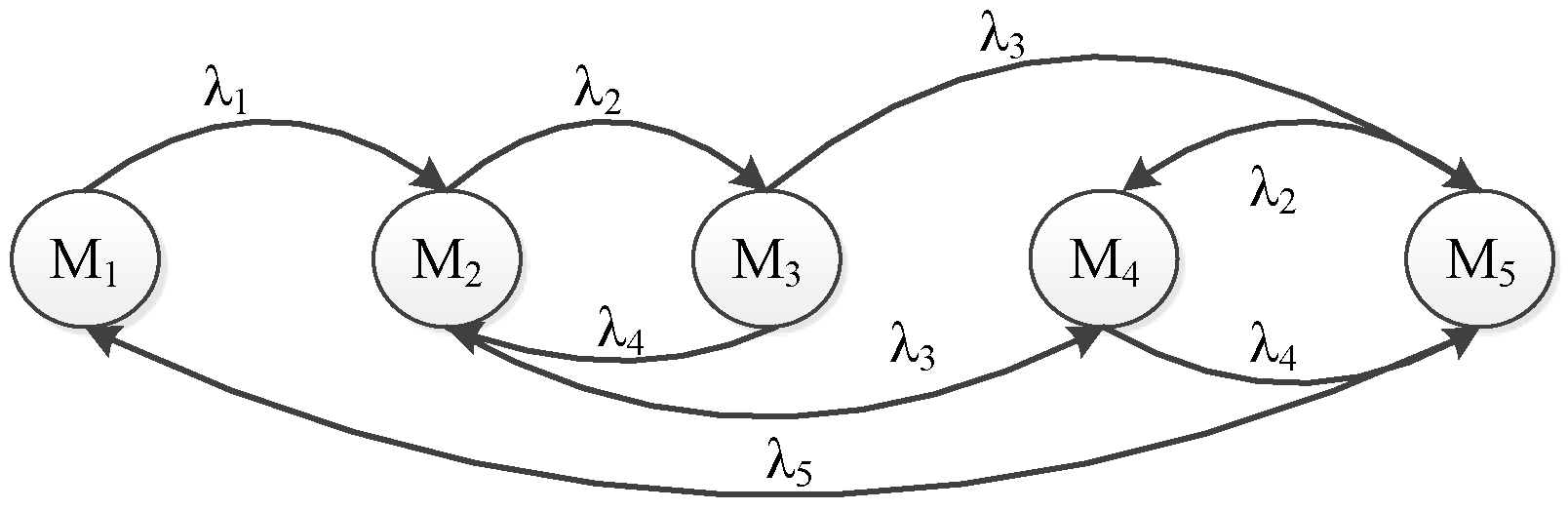
Firstly, we need to construct the performance evaluation model of the target system. That depends on the concrete system you want to analyze. Therefore, we directly give a sample model as shown in
Figure 4.
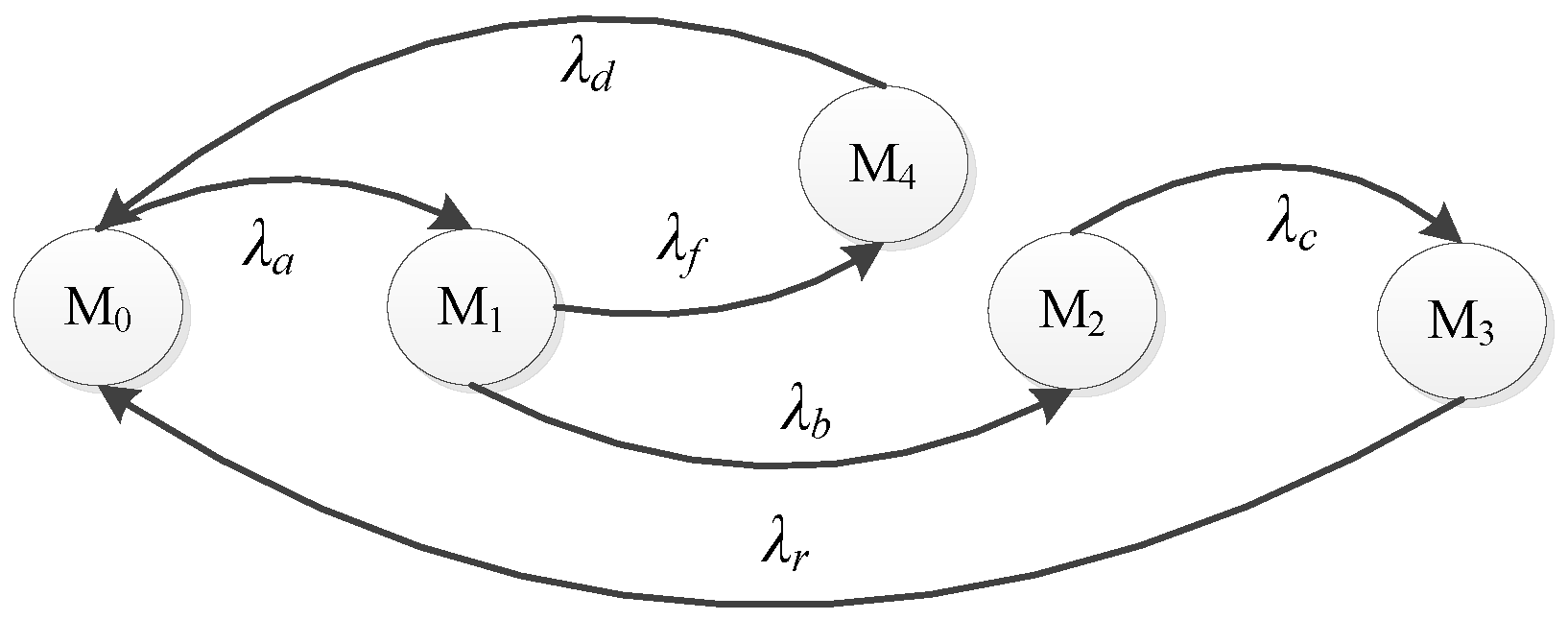
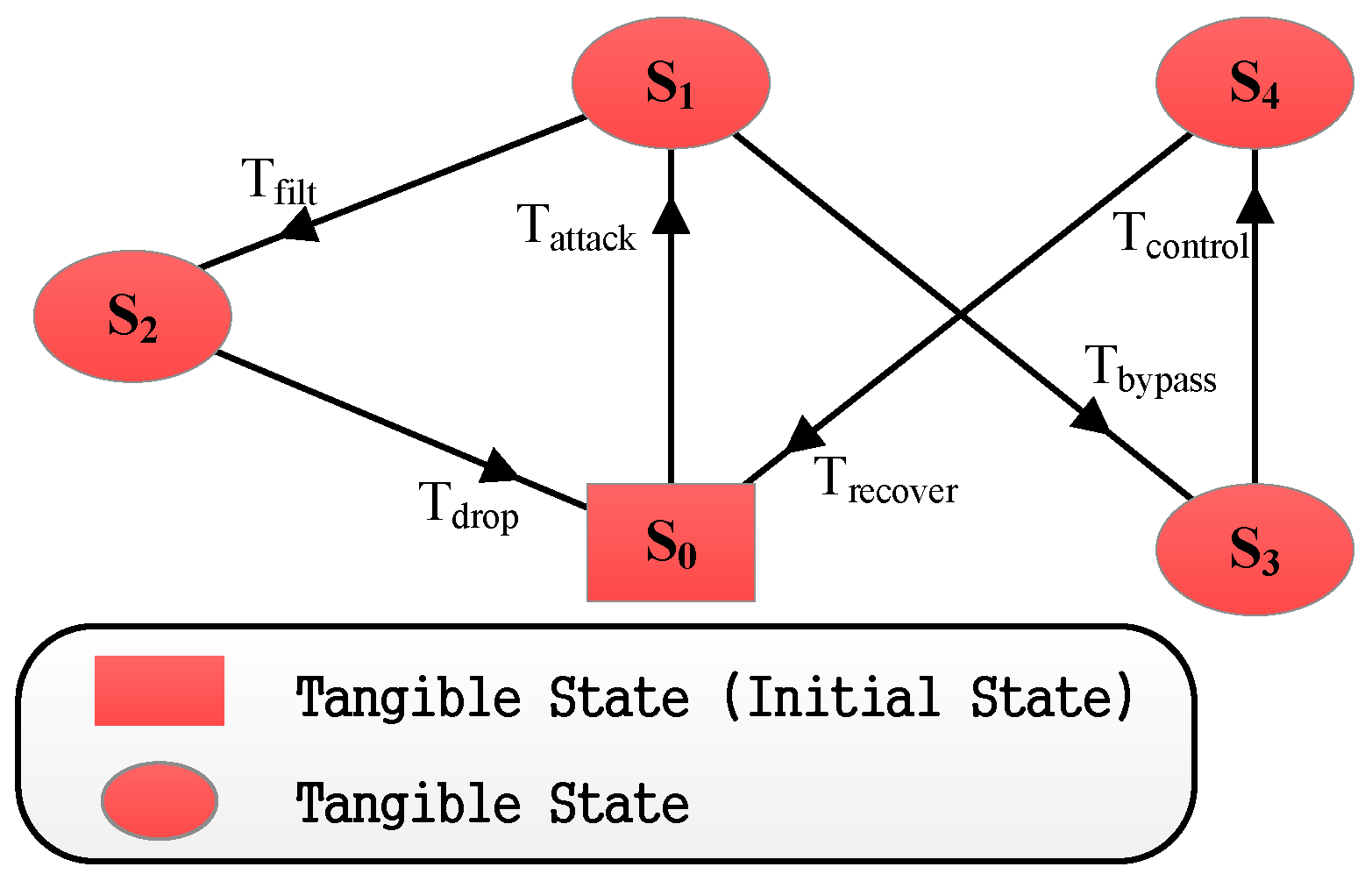
Secondly, we can construct the Markov Chain (MC) that is isomorphic to the SPN model. At first, we can easily get the reachable graph of the SPN model (as shown in
Figure 5). Then, we assume the transition firing rate average is
. Lastly, we get the MC by replacing the transition
with the corresponding
. The reachable markings’ set and the MC of the simple SPN model above are shown in
Table 1 and
Figure 6.
Thirdly, we can work on the system performance evaluation with the steady state probability based on the MC. There are some formulas that help the theoretical inference. They are as follows.
We assume that there are
n states in the MC. The transition matrix can be defined as:
,
; there:
Then, we assume the steady state probability is a row vector
. According to the Markov process, we can get the system of linear equations as follows:
We can get the steady probability of each state by resolving the system of linear equations above. Ulteriorly, we can get further parameters, such as:
(1) Residence time in each state
M:
There, H is the transitions’ set that can be enforceable at M.
(2) Token density function:
There, , .
(3) Average number of tokens on a place:
The average number of tokens of a place set
is the sum of each place’s average number of tokens. It can be expressed as:
There, the place .
(4) Utilization rate of the transition:
There, E represents the set of all reachable markings that make t enforceable.
(5) Token velocity of the transition:
There, stands for the average transition firing rate of t.
On the basis of all the performance parameters mentioned above, we can do further research on the system response time and so on.
4.3. The SPN Model of Scenario I
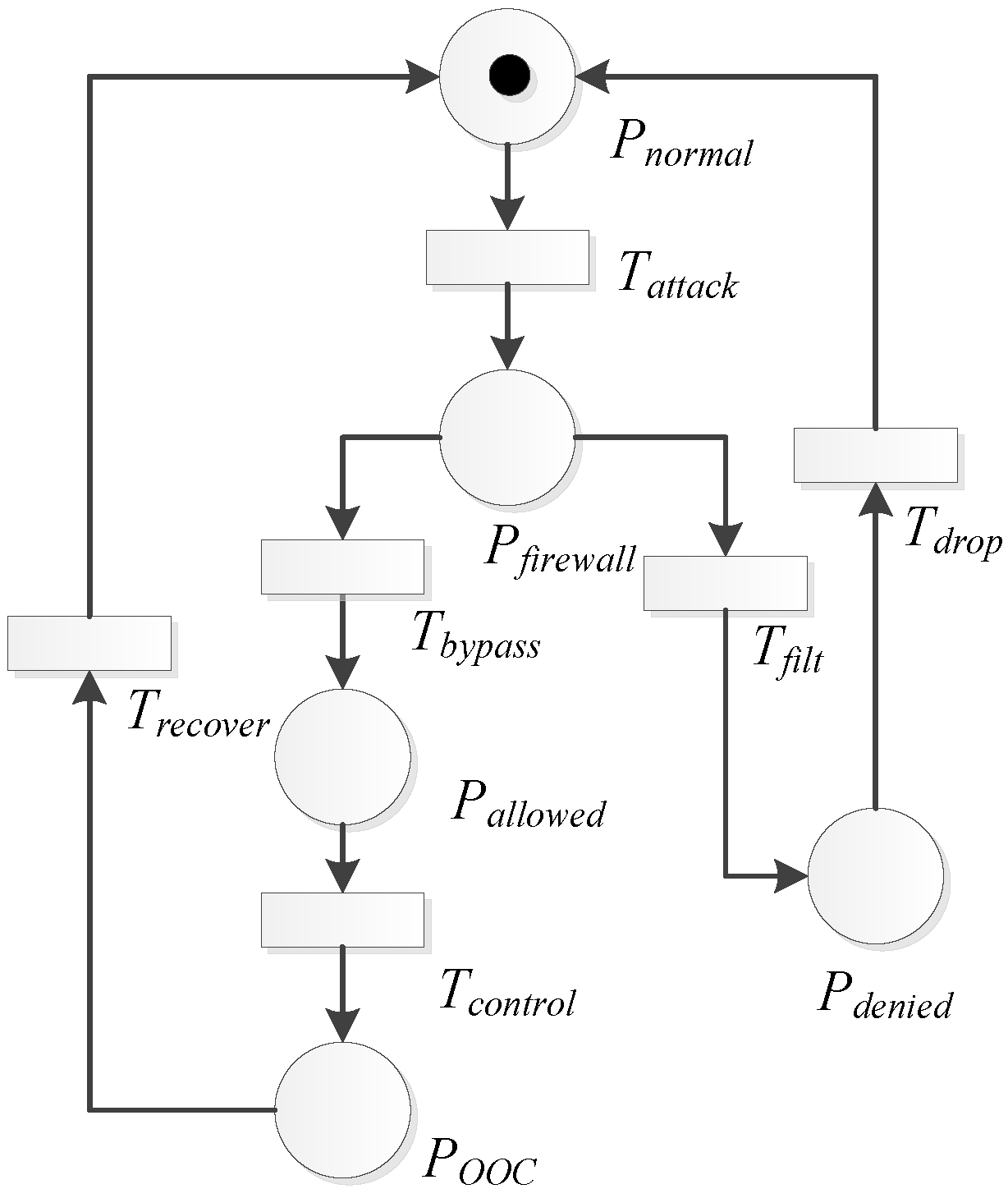
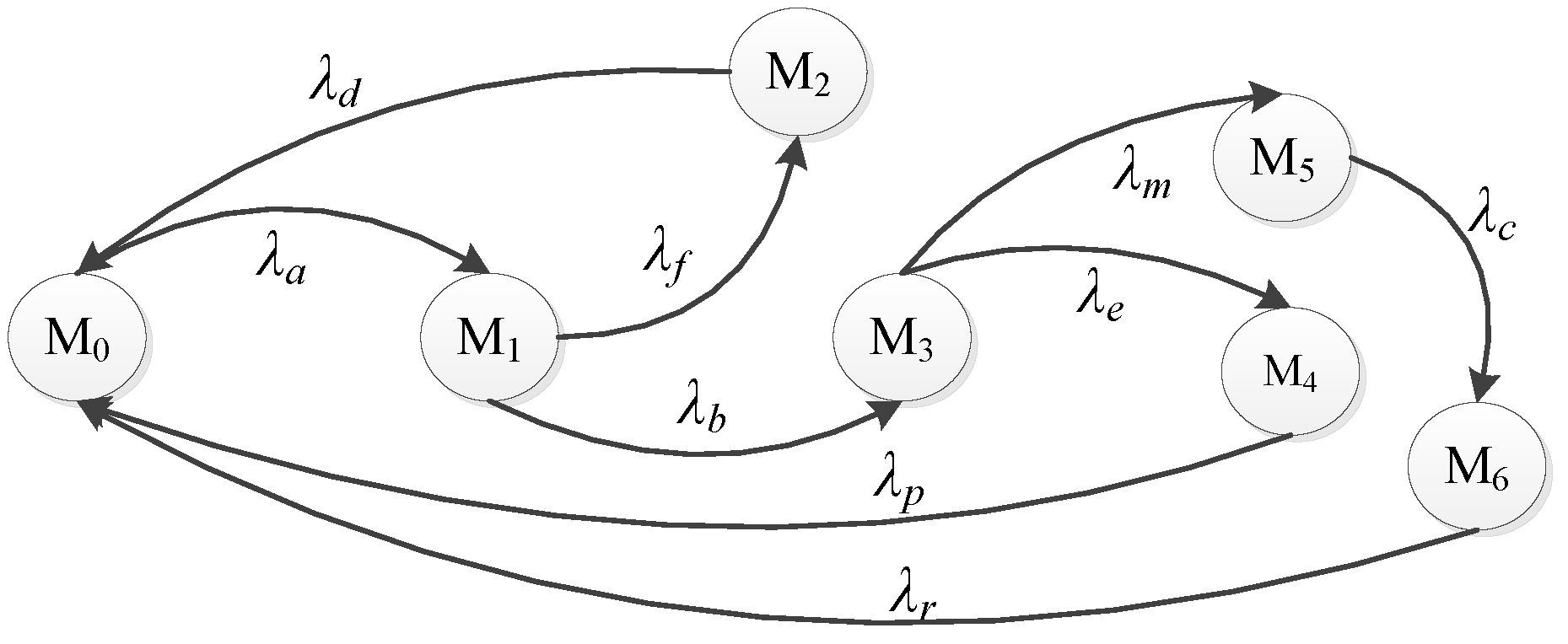
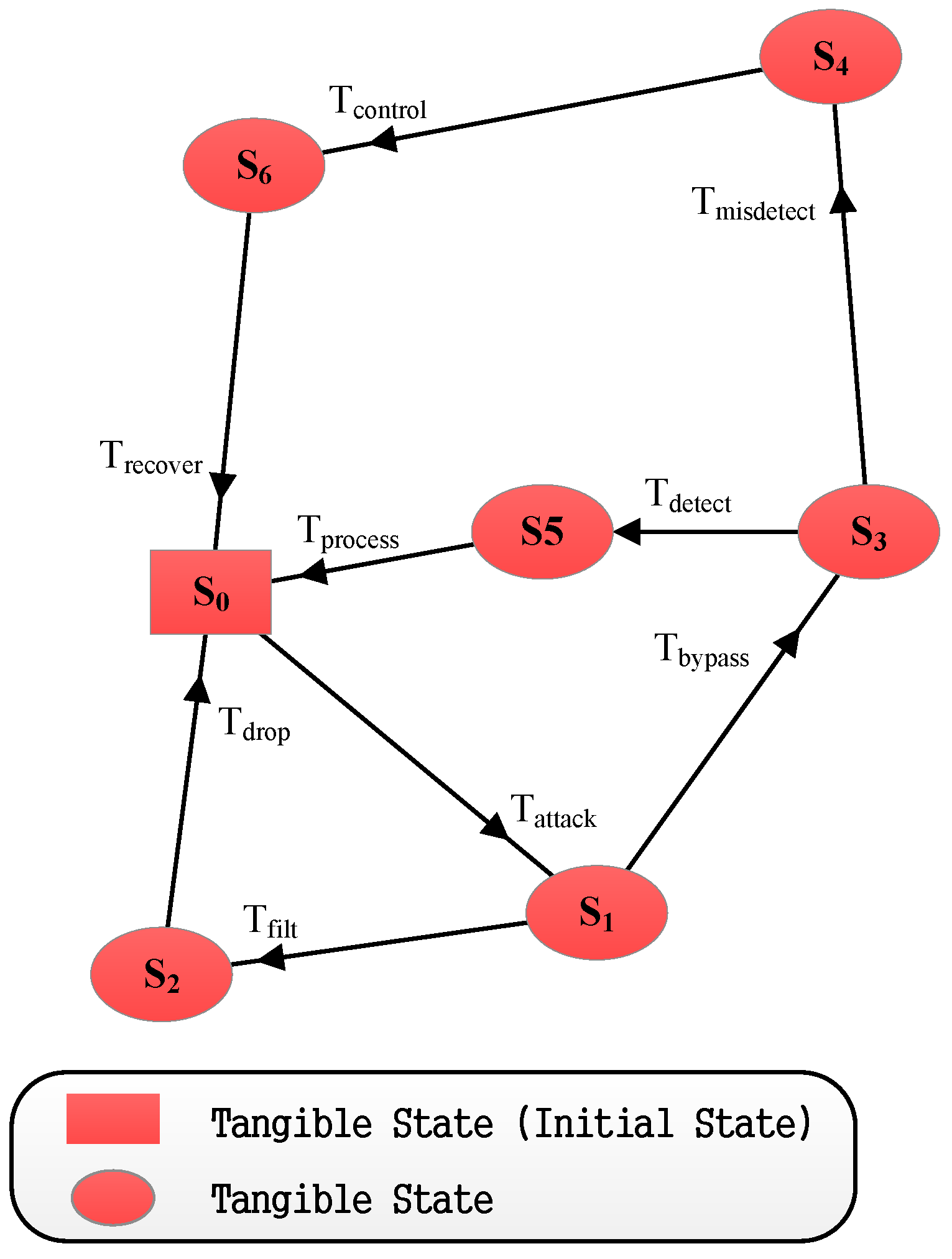
We construct the SPN model for the Defense Scenario I, as shown in
Figure 7. We denote
as the average transition triggering rate and
as the steady state probability. According to the performance evaluation process in [
29], we can get the set of reachable markings as
and the isomorphic model together with the Markov Chain (MC) and the process of SPN. The isomorphic model is shown in
Table 2 and
Figure 8.
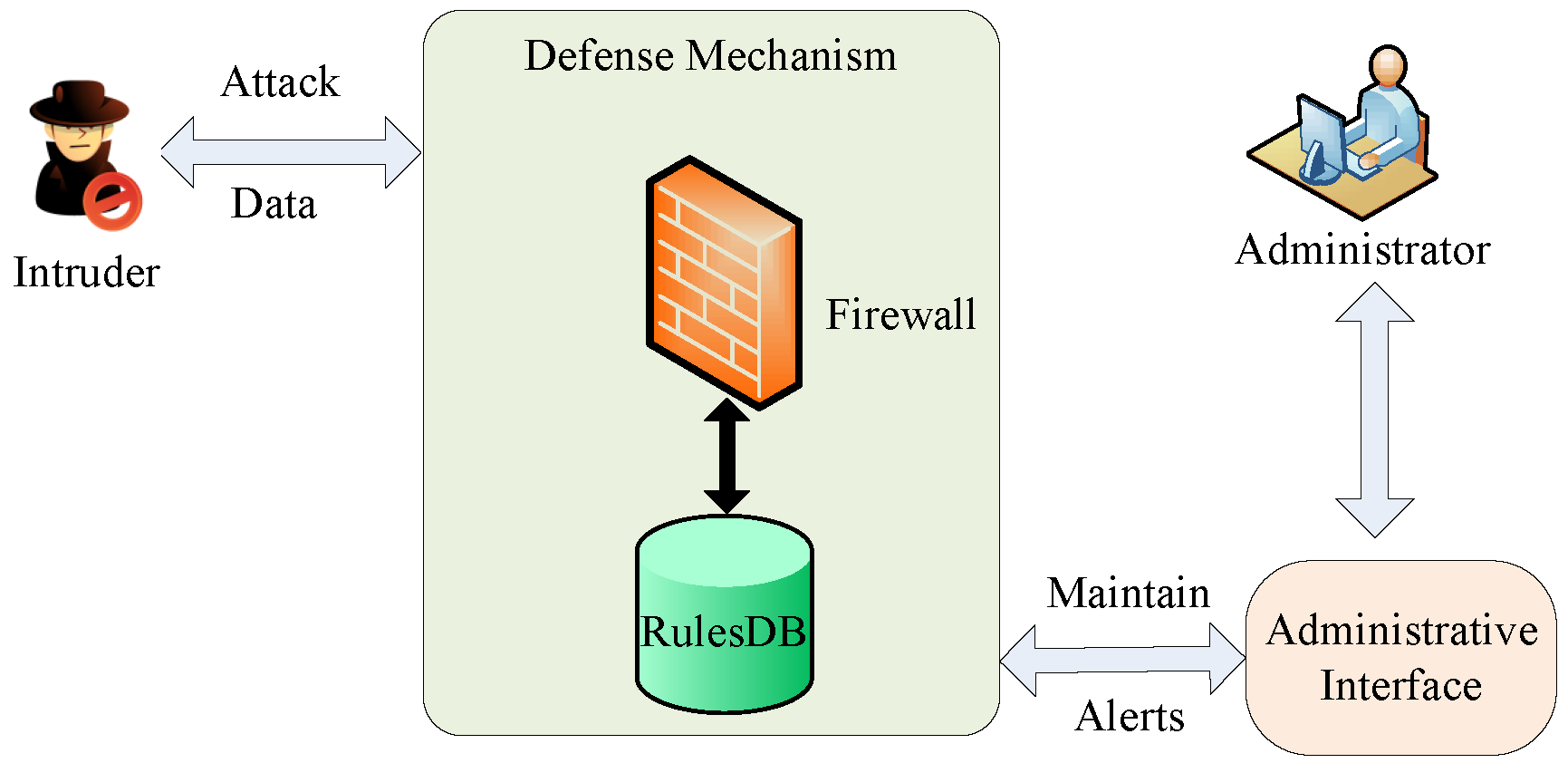
As shown in
Figure 7, the places
,
,
,
and
represent the system states, and the transitions
,
,
,
and
represent the events that enable the transfer of the system state. Initially, the system is in normal state
. When the transition
is triggered, the system transfers to the state
. If the firewall finds a matched filter rule from its rules’ database,
will be triggered, and the system will transfer into the denied state
. After that, the
transition will be triggered, and the legitimate data will be dropped. Then, the system transfers to the normal state. If the firewall does not find any corresponding filter rule, the transition
will be triggered, and the system will be in state
. By triggering the transition
, it will start the attack process, and finally, the system will be out of control, i.e., in state
. Then, the administrator recovers the system, and the transition
will be triggered. Finally, the system will recover to state
.
According to the definition of the transition matrix and other performance metrics in [
29], we can estimate the SPN model as follows. The transition matrix
Q of the SPN model is:
The steady state probability can be obtained as:
With the above steady state probability, the token density function can be obtained as:
The average number of the tokens in the place
and
is as follows:
In the subsystem in which the firewall filters out the legitimate data and makes the system transfer to the normal state, the average token number of the place set is the sum of and . That is, . The utilization rate of the transition is . Thus, the token velocity of the transition in the subsystem can be obtained as , where is set as one by default.
Moreover, we can estimate the performance of Defense Scenario I based on the above inferred parameters. The probability of the defense mechanism is the steady probability that the firewall successfully protects the system from attacking, i.e.,
The probability that the system falls is the steady probability that the intruder takes control of the system, i.e.,
The security probability, denoted as
, is the probability that the system is not exposed to the intruders and does not lose control, i.e.,
where
is the steady probability that the intruder bypasses the firewall and the target system is completely exposed to the intruder.
We also need to analyze the time that the firewall consumes to protect the system. In the subsystem mentioned above, we can get the average token number of the place set
and the token velocity of the transition
. According to the little rules and balance principle [
30], the delay for the firewall to detect and deal with the aggressive data can be formulated as:
Note that the analysis of the following two SPN models is similar to that of the first SPN model.
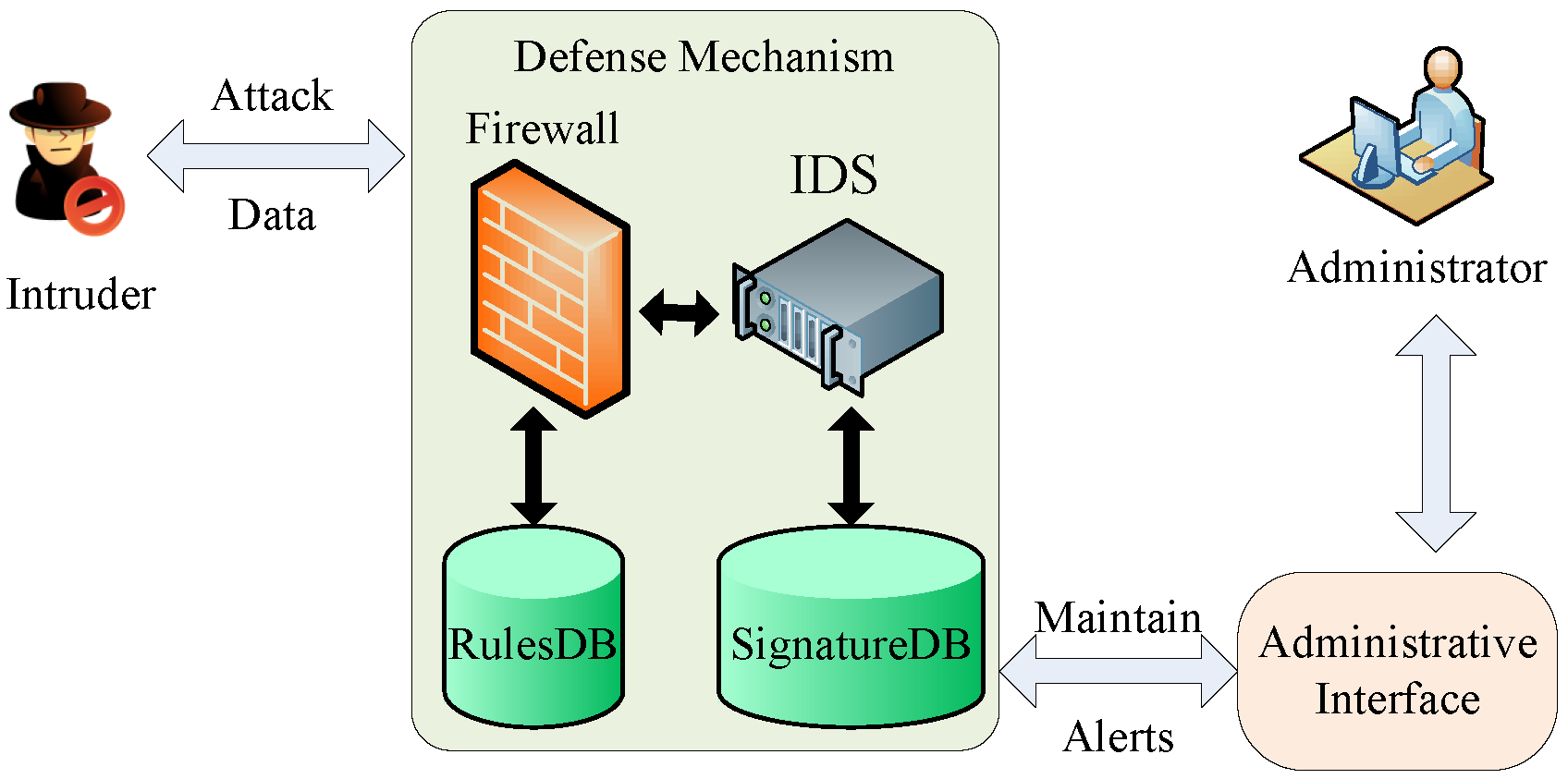
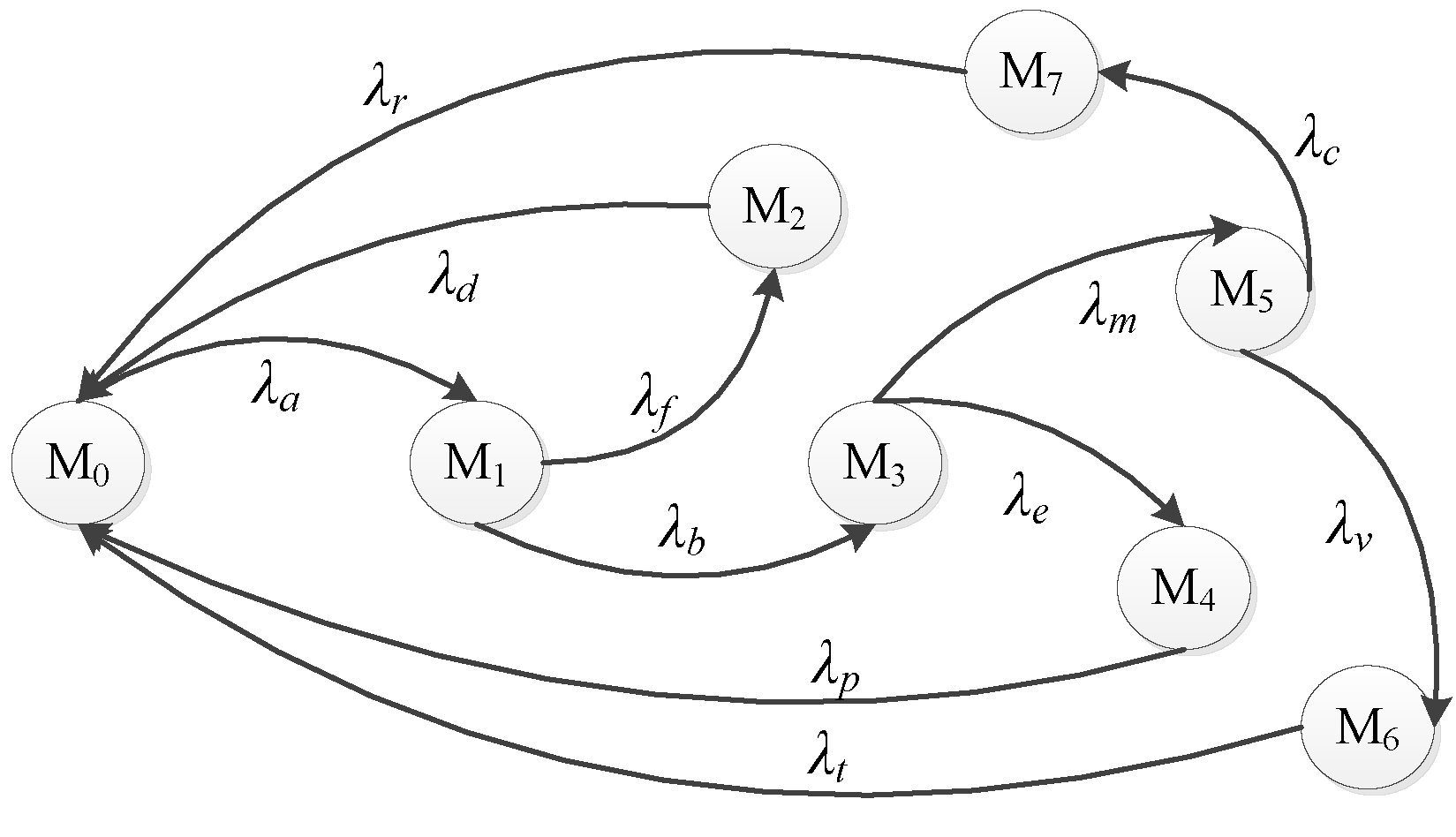
4.4. The SPN Model of Scenario II
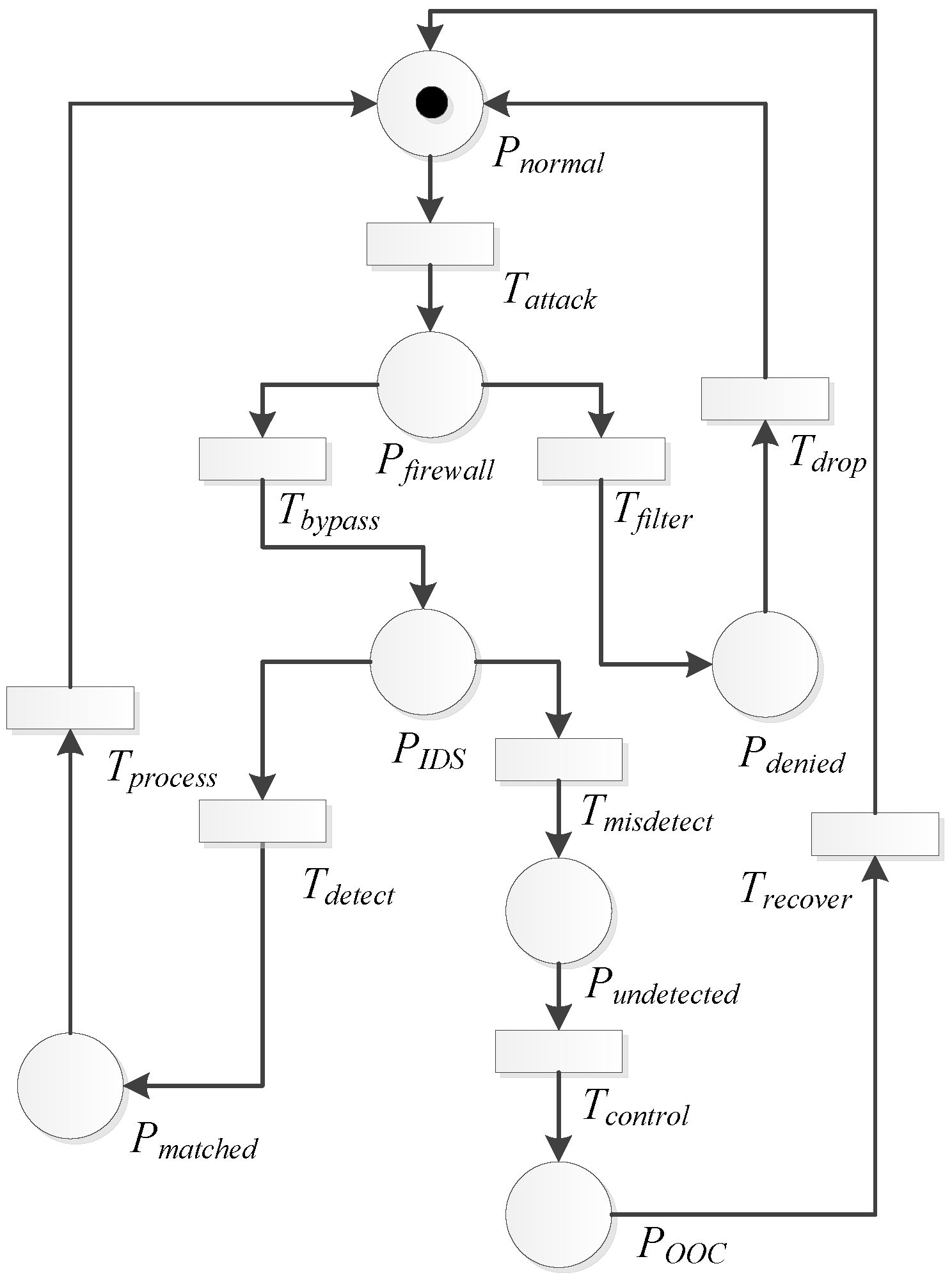
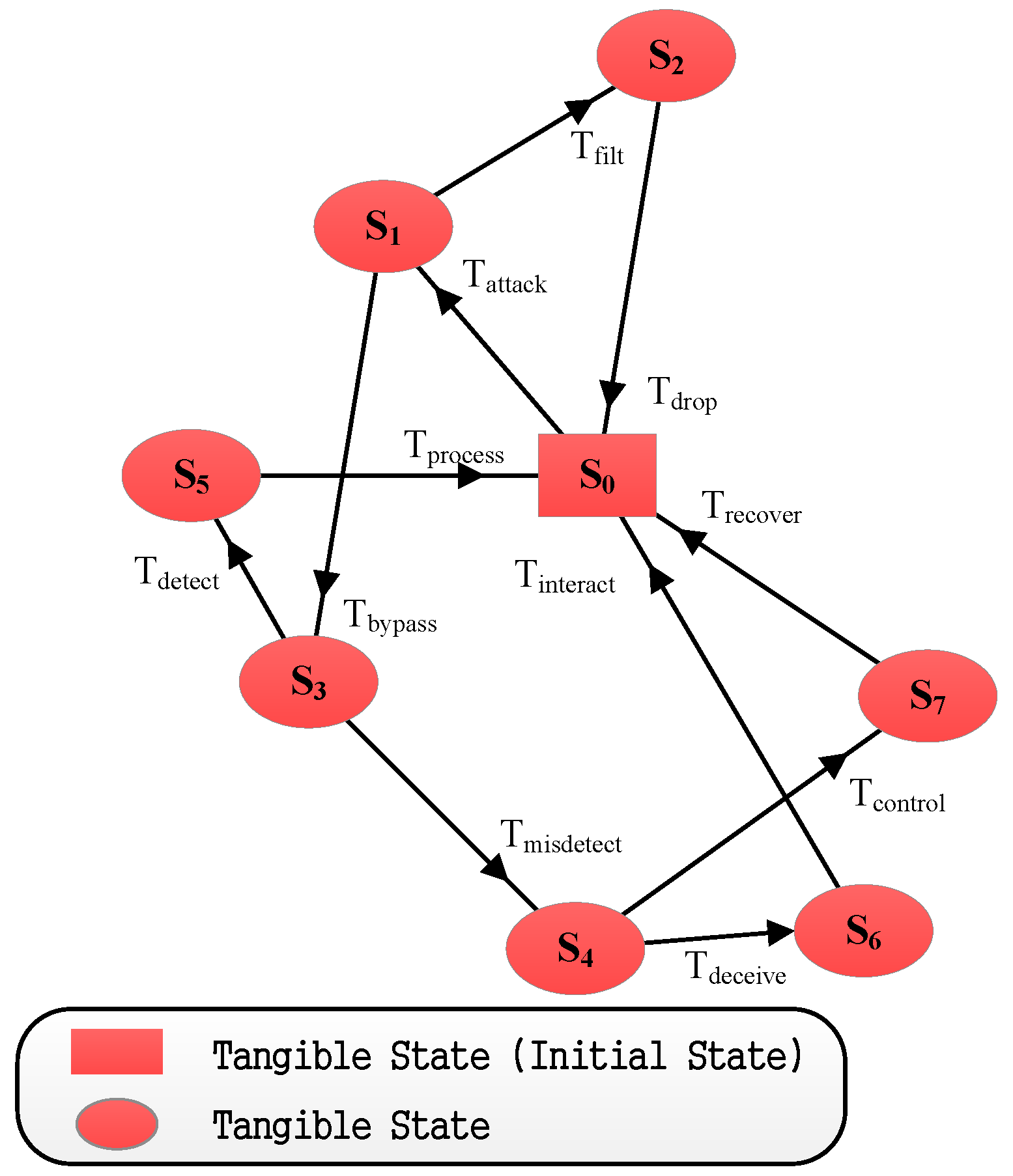
The SPN model of Defense Scenario II is shown in
Figure 9, in which the system is in the detection state of IDS, i.e.,
, after the firewall is bypassed. If the database of IDS has the matched signature, the transition
will be triggered. The system will be in state
. Then, the system will return to the normal state after the transition
is enabled. If the IDS cannot identify the intruder, the transition
is enabled, and the system will be in state
. After that,
will be triggered, and the system state will be transferred as that in Defense Scenario I, shown in
Figure 7.
We denote
as the average transition triggering rate and
as the steady state probability. According to the SPN model in
Figure 9, we can obtain the reachable markings’ set
and MC as shown in
Table 3 and
Figure 10.
The transition matrix
Q is:
The state steady probability is:
The token density function is:
The average number of the tokens in a place is:
The utilization rate of the transition is:
Then, we can get the token velocity of the transition as:
The probability
that the defense mechanism works effectively is the sum of the steady probability
and
, where
represents the probability that the firewall detects the attack and
represents the probability that the IDS detects the attack. Then, we can get:
The fall probability of the system, denoted as , is the steady state probability that the intruder takes control of the system, i.e.,
The security probability, denoted as
, that the system is not exposed to the intruder and does not lose control, can be formulated as:
The subsystem in which the firewall detects and deals with the attack is the same as that mentioned in Scenario I. The average token number of the place set
is the sum of
and
, i.e.,
. Therefore, the delay
introduced by the firewall is:
The delay for the IDS to detect and process the attack behavior can be formulated as:
When the IDS works, it indicates that the intruder has bypassed the firewall without being detected.