Lightweight S-Box Architecture for Secure Internet of Things
Abstract
:1. Introduction
2. Properties of the Optimal S-Box
- (1)
- Bijective, i.e., for any .
- (2)
- Let the difference XOR propagation between the input XOR values (ΔI) and the output XOR values (ΔO) be given by NDs (ΔI, ΔO) = #{x |S(x) ⊕ S (x ⊕ ΔI) = ΔO}; it should be ≤4.
- (3)
- The differential uniformity: i.e., the diffusion of the S-box is given by the .
- (4)
- Let the linear imbalance of the S-box be denoted by Imbs (ΓI, ΓO) = #{x |ΓI .x = ΓO. S(x)} − 8|: it should be ≤4, where ΓI and ΓO are the input and output masks of the S-box linear approximation and “.” is the inner product on .
- (5)
- The linearity of the S-box is given by the
- (6)
- No fixed point, i.e., for any .
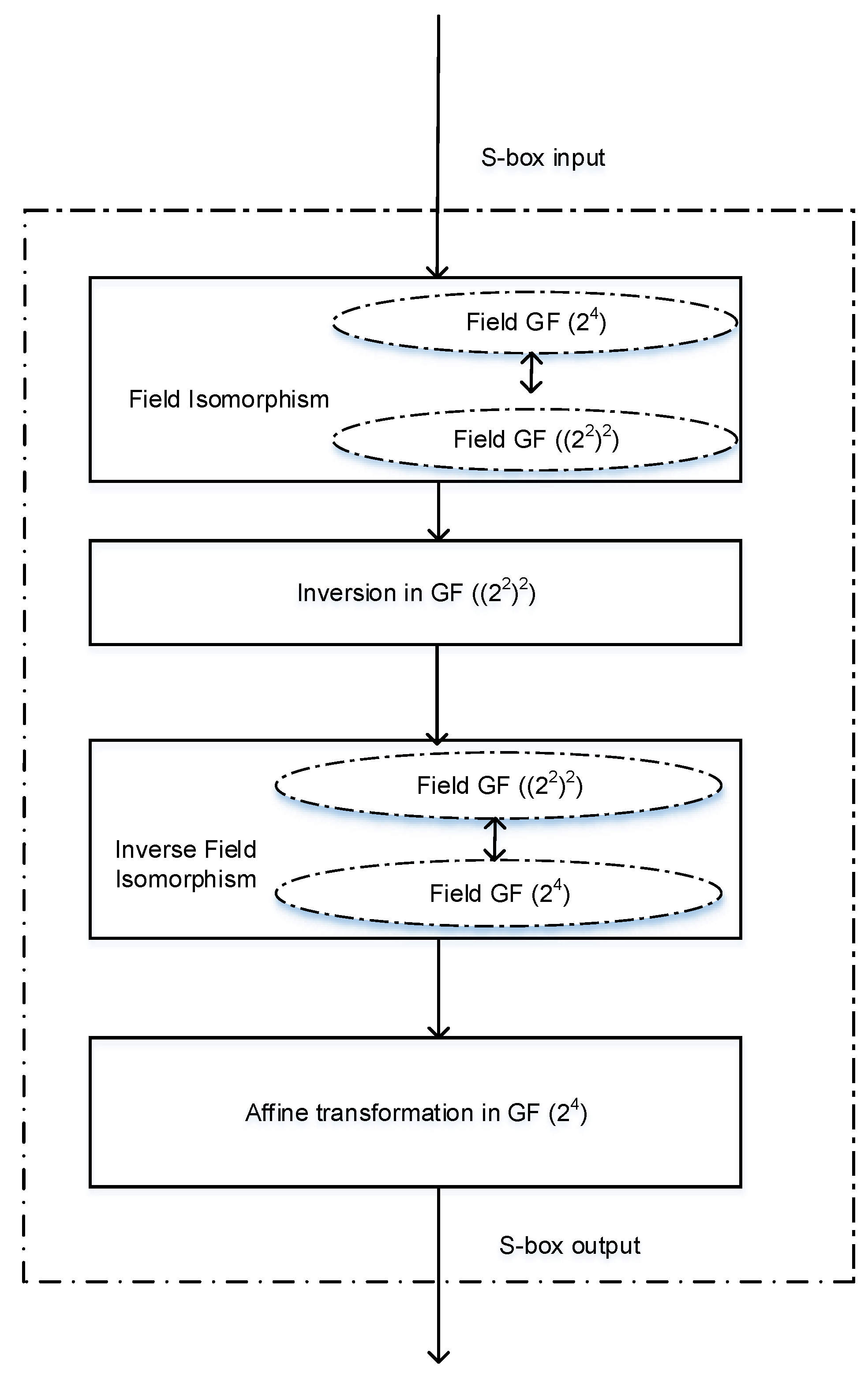
3. Design Methodology
- (1)
- The construction of the field GF (2nm=4) in the polynomial basis using the irreducible primitive polynomial of degree 4.
- (2)
- The construction of the composite field GF ((2n=2)m=2) in the polynomial basis using the respective bases.
- (3)
- Derivation of the multiplicative inverse structure in the composite field GF ((2n=2)m=2) using the Euclidean algorithm. The multiplicative inversion involves the subfields GF (2), GF ((2n=2)m=2) and GF (2nm=4).
- (4)
- The isomorphic transformation of the sub fields based on the primitive element of the higher order field.
- (5)
- The affine transformation in the field GF (2nm=4).
- (6)
- Validation of the proposed S-box structure through the physical implementation of the proposed S-box in the one of the lightweight cipher algorithms, PRESENT, and estimation of its hardware performance.
- (7)
- Security analysis of the proposed S-box structure to prove its security strength.
4. Construction of the Fields
- B1: The binary extension field employed is the GF (24), and is defined over the prime field GF (2). If is a root of , then the set forms the basis for the field GF (24). Any element A in can be expressed as , where i for i = 0 to 3. The row vector () is called the representation of the element A in the basis B1. This is the polynomial basis for the representation of the field GF (24) over GF (2).
- B2: The irreducible polynomial of degree defined over GF (22) has root . Then, the set is the basis of GF ((22)2). Any element in the basis B2 can be expressed as , where for i = 0, 1. The row vector (, is called the composite field representation of the element A in the basis B2. The coefficients in the composite field representation are in the ground field GF (22).
- B3: The irreducible polynomial of degree over GF (2) constructs the ground field GF (22) with a root and the basis B3. Therefore, any element GF (22) can be written as , where . The row vector ( represents the element GF (22), in the basis B3.
5. Multiplicative Inverse in the Composite Field
- (1)
- Isomorphic transformation from the higher order field representation to the lower order composite field representation .
- (2)
- Multiplicative inversion in the composite field using the Euclidean theorem.
- (3)
- Inverse isomorphic transformation of the result obtained by the multiplicative inverse, to the higher order field .
6. Isomorphism and Field Polynomials
- (1)
- Construction of the conversion matrix between and , where the generation polynomials are known a priori through an exhaustive search method.
- (2)
- Construction of the conversion matrix, in which the generator polynomial is not known a priori nor fixed. In this field conversion, the isomorphism between the fields is derived based on the primitive or the non-primitive polynomials. The primitive elements of the irreducible polynomials are the key for the isomorphic transformations in this technique.
6.1. Minimal Polynomials for the Composite Field Conversion
- (1)
- With and the composite field is constructed with as the ground field. The minimal polynomial of for the composite field construction is given asThe polynomial is an irreducible polynomial of degree 2 with coefficients in . The subfield is . The operation in the field is performed in over .
- (2)
- The minimal polynomial of for the field over construction is given asThe polynomial is an irreducible polynomial of degree 4 with coefficients in . The primitive polynomial used for the field construction is a polynomial of degree whose coefficients are in .
6.2. Evaluation of the Conversion Matrix
7. Affine Transformation
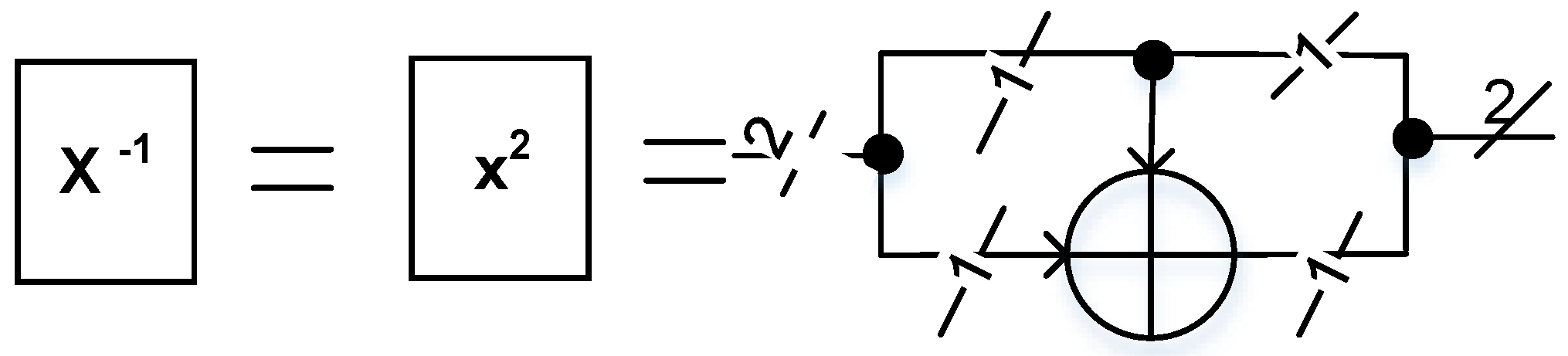
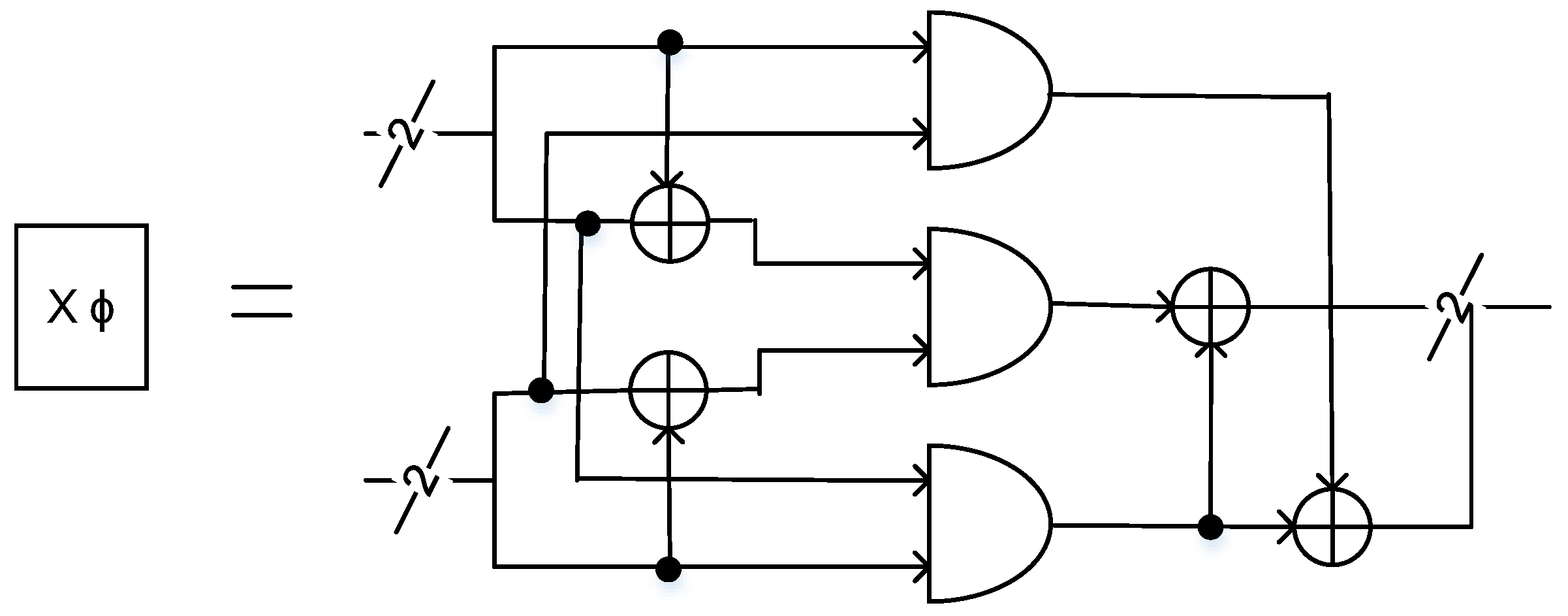
8. Overall S-Box Structure and Substructures
9. Hardware Performance in Block Ciphers
10. Security Analysis
10.1. Linear Cryptanalysis
10.2. Differential Cryptanalysis
11. Conclusions
Acknowledgments
Conflicts of Interest
References
- Singh, S.; Sharma, P.K.; Moon, S.Y.; Park, J.H. Advanced lightweight encryption algorithms for IoT devices: Survey, challenges and solutions. J. Ambient Intell. Hum. Comput. 2017, 1–18. [Google Scholar] [CrossRef]
- Katagi, M.; Moriai, S. Lightweight cryptography for the internet of things. Sony Corp. 2008, 7–10. [Google Scholar]
- Xu, T.; Wendt, J.B.; Potkonjak, M. Security of IoT systems: Design challenges and opportunities. In Proceedings of the 2014 IEEE/ACM International Conference on Computer-Aided Design, San Jose, CA, USA, 2–6 November 2014; pp. 417–423. [Google Scholar]
- Daniel, D.; Le Corre, Y.; Khovratovich, D.; Perrin, L.; Grobschadl, J.; Biryukov, A. Triathlon of Lightweight Block Ciphers for the Internet of Things. 2015. Available online: http://orbilu.uni.lu/bitstream/10993/25565/1/209.pdf (accessed on 1 January 2018).
- McKay, K.A.; Bassham, L.; Turan, M.S.; Mouha, N. Report on Lightweight Cryptography; NIST DRAFT NISTIR 8114; National Institute of Standards and Technology (NIST): Gaithersburg, MD, USA, 2016. [Google Scholar]
- Batra, I.; Luhach, A.K.; Pathak, N. Research and Analysis of Lightweight Cryptographic Solutions for Internet of Things. In Proceedings of the Second International Conference on Information and Communication Technology for Competitive Strategies, Udaipur, India, 4–5 March 2016; p. 23. [Google Scholar]
- Patil, A.; Bansod, G.; Pisharoty, N. Hybrid Lightweight and Robust Encryption Design for Security in IoT. Int. J. Secur. Its Appl. 2015, 9, 85–98. [Google Scholar] [CrossRef]
- Lightweight Cryptography for the IoE. Available online: http://semiengineering.com/lightweight-cryptography-for-the-ioe/ (accessed on 10 January 2016).
- Shamir, A.; Biryukov, A.; Perrin, L.P. Summary of an Open Discussion on IoT and Lightweight Cryptography. In Proceedings of Early Symmetric Crypto Workshop; University of Luxembourg: Luxembourg, 2017. [Google Scholar]
- Biryukov, A.; Perrin, L. State of the Art in Lightweight Symmetric Cryptography; International Association for Cryptologic Research: Esch-sur-Alzette, Luxembourg, 2017. [Google Scholar]
- Wang, Y.; Ha, Y. FPGA-based 40.9-Gbits/s masked AES with area optimization for storage area network. IEEE Trans. Circuits Syst. II Express Briefs 2013, 60, 36–40. [Google Scholar] [CrossRef]
- McLoone, M.; McCanny, J.V. Rijndael FPGA implementations utilising look-up tables. J. VLSI Signal Process. Syst. Signal Image Video Technol. 2003, 34, 261–275. [Google Scholar] [CrossRef]
- Liu, F.; Ji, W.; Hu, L.; Ding, J.; Lv, S.; Pyshkin, A.; Weinmann, R.-P. Analysis of the SMS4 block cipher. ACISP 2007, 4586, 158–170. [Google Scholar]
- Lee, S.W.; Moon, S.-J.; Kim, J.N. High-Speed Hardware Architectures for ARIA with Composite Field Arithmetic and Area-Throughput Trade-Offs. ETRI J. 2008, 30, 707–717. [Google Scholar] [CrossRef]
- Bansod, G.; Raval, N.; Pisharoty, N. Implementation of a new lightweight encryption design for embedded security. IEEE Trans. Inf. Forensics Secur. 2015, 10, 142–151. [Google Scholar] [CrossRef]
- Kitsos, P.; Sklavos, N.; Parousi, M.; Skodras, A.N. A comparative study of hardware architectures for lightweight block ciphers. Comput. Electr. Eng. 2012, 38, 148–160. [Google Scholar] [CrossRef]
- Standaert, F.-X.; Piret, G.; Rouvroy, G.; Quisquater, J.-J. FPGA implementations of the ICEBERG block cipher. Integr. VLSI J. 2007, 40, 20–27. [Google Scholar]
- Li, Z.-R.; Zhuang, Y.-Q.; Zhang, C.; Gang, J.I.N. Low-power and area-optimized VLSI implementation of AES coprocessor for Zigbee system. J. China Univ. Posts Telecommun. 2009, 16, 89–94. [Google Scholar] [CrossRef]
- Good, T.; Benaissa, M. 692-nW Advanced Encryption Standard (AES) on a 0.13-µm CMOS. IEEE Trans. Very Large Scale Integr. Syst. 2010, 18, 1753–1757. [Google Scholar] [CrossRef]
- Wong, M.M.; Wong, M.L.D.; Nandi, A.K.; Hijazin, I. Construction of optimum composite field architecture for compact high-throughput aes s-boxes. IEEE Trans. Very Large Scale Integr. Syst. 2012, 20, 1151–1155. [Google Scholar] [CrossRef]
- Zhang, X.; Parhi, K.K. High-speed VLSI architectures for the AES algorithm. IEEE Trans. Very Large Scale Integr. Syst. 2004, 12, 957–967. [Google Scholar] [CrossRef]
- Satoh, A.; Morioka, S.; Takano, K.; Munetoh, S. A compact Rijndael hardware architecture with S-box optimization. Asiacrypt 2001, 2248, 239–254. [Google Scholar]
- Rudra, A.; Dubey, P.K.; Jutla, C.S.; Kumar, V.; Rao, J.R.; Rohatgi, P. Efficient Rijndael encryption implementation with composite field arithmetic. CHES 2001, 2162, 171–184. [Google Scholar]
- Canright, D. A very compact S-box for AES. In International Workshop on Cryptographic Hardware and Embedded Systems; Springer: Berlin/Heidelberg, Germany, 2005; pp. 441–455. [Google Scholar]
- Wong, M.M.; Wong, M.L.D.; Nandi, A.K.; Hijazin, I. Composite field GF (((22)2)2) Advanced Encryption Standard (AES) S-box with algebraic normal form representation in the subfield inversion. IET Circuits Dev. Syst. 2011, 5, 471–476. [Google Scholar] [CrossRef]
- Savas, E.; Koç, Ç.K. Finite field arithmetic for cryptography. IEEE Circuits Syst. Mag. 2010, 10, 40–56. [Google Scholar] [CrossRef]
- Deschamps, J.-P.; Imaña, J.L.; Sutter, G.D. Hardware Implementation of Finite-Field Arithmetic; McGraw-Hill: New York, NY, USA, 2009. [Google Scholar]
- Baktir, S.; Sunar, B. Optimal tower fields. IEEE Trans. Comput. 2004, 53, 1231–1243. [Google Scholar] [CrossRef]
- Bailey, D.V.; Paar, C. Efficient arithmetic in finite field extensions with application in elliptic curve cryptography. J. Cryptol. 2001, 14, 153–176. [Google Scholar] [CrossRef]
- Olofsson, M. VLSI Aspects on Inversion in Finite Fields; Department of Electrical Engineering, Linköpings Universitet: Linköpings, Sweden, 2002. [Google Scholar]
- Guajardo, J.; Paar, C. Itoh-Tsujii inversion in standard basis and its application in cryptography and codes. Des. Codes Cryptogr. 2002, 25, 207–216. [Google Scholar] [CrossRef]
- Sunar, B.; Savas, E.; Koç, Ç.K. Constructing composite field representations for efficient conversion. IEEE Trans. Comput. 2003, 52, 1391–1398. [Google Scholar] [CrossRef]
- Lv, J.; Kalla, P.; Enescu, F. Efficient gröbner basis reductions for formal verification of Galois field multipliers. In Proceedings of the Design, Automation & Test in Europe Conference & Exhibition (DATE), Dresden, Germany, 12–16 March 2012; pp. 899–904. [Google Scholar]
- Youssef, A.M.; Tavares, S.E. Affine equivalence in the AES round function. Discrete Appl. Math. 2005, 148, 161–170. [Google Scholar] [CrossRef]
- El-Sheikh, H.M.; El-Mohsen, O.A.; Elgarf, S.T.; Zekry, A. A new approach for designing key-dependent S-box defined over GF (24) in AES. Int. J. Comput. Theory Eng. 2012, 4, 158. [Google Scholar] [CrossRef]
- Kong, J.H.; Ang, L.-M.; Seng, K.P. A comprehensive survey of modern symmetric cryptographic solutions for resource constrained environments. J. Netw. Comput. Appl. 2015, 49, 15–50. [Google Scholar] [CrossRef]
- Eisenbarth, T.; Kumar, S. A survey of lightweight-cryptography implementations. IEEE Des. Test Comput. 2007, 24, 522–533. [Google Scholar] [CrossRef]
- Sbeiti, M.; Silbermann, M.; Poschmann, A.; Paar, C. Design space exploration of present implementations for FPGAs. In Proceedings of the 5th Southern Conference on Programmable Logic, Sao Carlos, Brazil, 1–3 April 2009; pp. 141–145. [Google Scholar]
- Guo, X.; Chen, Z.; Schaumont, P. Energy and performance evaluation of an FPGA-based SoC platform with AES and PRESENT coprocessors. Lect. Notes Comput. Sci. 2008, 5114, 106–115. [Google Scholar]
- Tay, J.J.; Wong, M.L.D.; Wong, M.M.; Zhang, C.; Hijazin, I. Compact FPGA implementation of PRESENT with Boolean S-Box. In Proceedings of the 6th Asia Symposium on Quality Electronic Design (ASQED), Kula Lumpur, Malaysia, 4–9 August 2015; pp. 144–148. [Google Scholar]
- Bogdanov, A.; Knudsen, L.R.; Leander, G.; Paar, C.; Poschmann, A.; Robshaw, M.J.B.; Seurin, Y.; Vikkelsoe, C. PRESENT: An ultra-lightweight block cipher. CHES 2007, 4727, 450–466. [Google Scholar]
- Leander, G.; Poschmann, A. On the classification of 4 bit S-boxes. In Proceedings of the 1st international Workshop on Arithmetic of Finite Fields, Madrid, Spain, 21–22 June 2007; pp. 159–176. [Google Scholar]
- Zhang, W.; Bao, Z.; Rijmen, V.; Liu, M. A New Classification of 4-bit Optimal S-boxes and its Application to PRESENT, RECTANGLE and SPONGENT. In International Workshop on Fast Software Encryption; Springer: Berlin/Heidelberg, Germany, 2015; pp. 494–515. [Google Scholar]
- Zhang, W.; Bao, Z.; Lin, D.; Rijmen, V.; Yang, B.; Verbauwhede, I. RECTANGLE: A bit-slice lightweight block cipher suitable for multiple platforms. Sci. China Inf. Sci. 2015, 58, 1–15. [Google Scholar] [CrossRef]
- Poschmann, A.Y. Lightweight Cryptography: Cryptographic Engineering for a Pervasive World. Ph.D. Thesis, Ruhr University Bochum, Germany, 2009. [Google Scholar]
- Satoh, A.; Morioka, S. Hardware-focused performance comparison for the standard block ciphers AES, CAMELIA, and Triple-DES. In International Conference on Information Security; Springer: Berlin/Heidelberg, Germany, 2003; pp. 252–266. [Google Scholar]
- Shirai, T.; Shibutani, K.; Akishita, T.; Moriai, S.; Iwata, T. The 128-bit blockcipher CLEFIA. In Proceedings of the 14th International Workshop on Fast Software Encryption—FSE’07, Luxembourg, 26–28 March 2007; pp. 181–195. [Google Scholar]
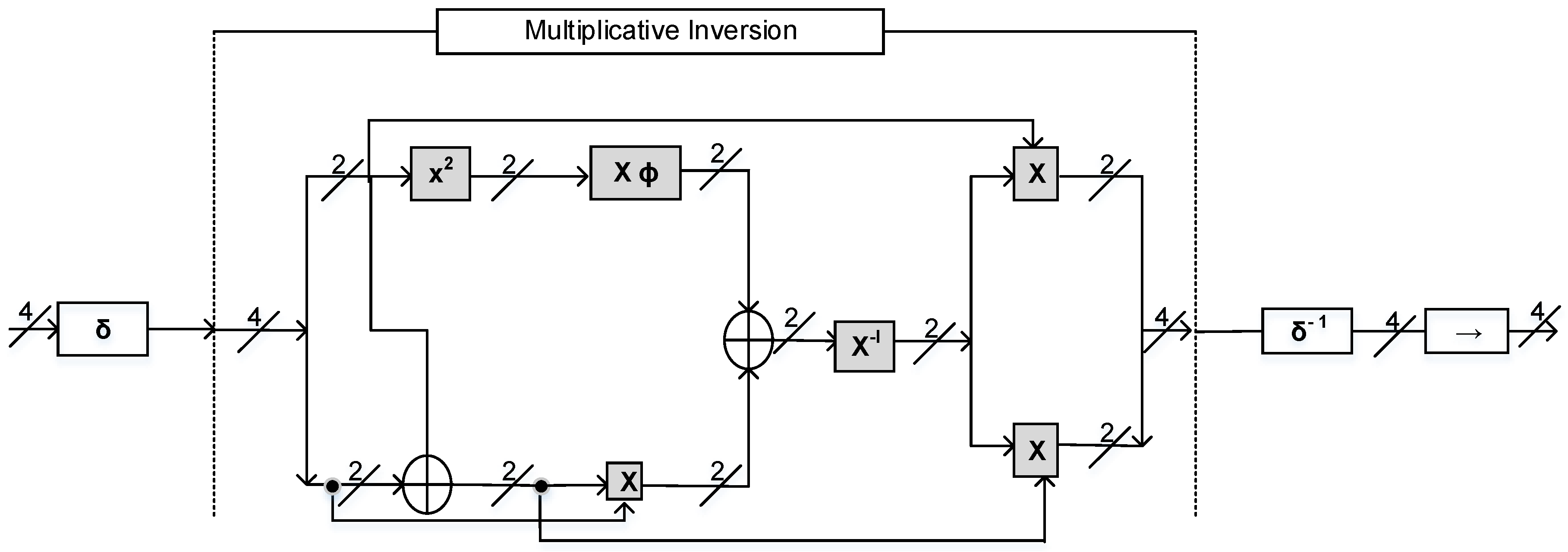
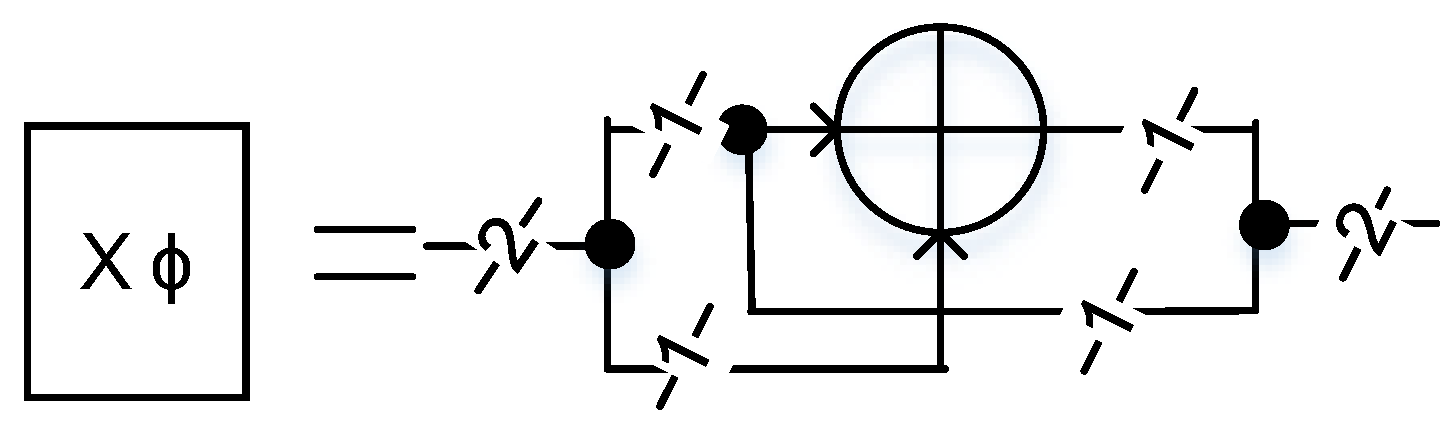
| Symbol | Operation |
|---|---|
| x2 | Squaring operation in |
| X | Multiplication in |
| Xø | Multiplication with constant in |
| ⊕ | Bitwise addition in |
| X−1 | Inversion in Fermat’s with m = 2 |
| δ | Isomorphism from to |
| δ−1 | Inverse isomorphism from |
| → | Affine transformation in |
| X | 0 | 1 | 2 | 3 | 4 | 5 | 6 | 7 | 8 | 9 | A | B | C | D | E | F |
| S[x] | 7 | E | F | 0 | D | B | 8 | 1 | 9 | 3 | 4 | C | 2 | 5 | A | 6 |
| Operations | [PROPOSED] | |
|---|---|---|
| Squaring | 1 XOR | 4 XOR |
| Multiplication with constant | 1 XOR (× | 3 XOR ( |
| Multiplication | 4 XOR + 3 AND | 21 XOR + 9 AND |
| Reference Work | Block Size | Key Size | Cycles per Block | Logic Process | Area (GE) |
|---|---|---|---|---|---|
| PRESENT-80 [31] | 64 | 80 | 32 | 0.18 µm | 1570 |
| PRESENT-128 [45] | 128 | 128 | 32 | 0.18 µm | 1884 |
| CLEFIA [46] | 128 | 128 | 36 | 0.09 µm | 4950 |
| CLEFIA [47] | 128 | 128 | 18 | 0.09 µm | 5979 |
| AES [46] | 128 | 128 | 11 | 0.13 µm | 12,454 |
| AES [46] | 128 | 128 | 54 | 0.13 µm | 5398 |
| PRESENT-80 [Proposed] | 64 | 80 | 32 | 0.18 µm | 1486 |
| 0 | 1 | 2 | 3 | 4 | 5 | 6 | 7 | 8 | 9 | A | B | C | D | E | F | |
| 0 | 8 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 |
| 1 | 0 | 0 | 0 | 0 | 0 | −4 | 0 | 4 | 2 | −2 | 2 | −2 | 2 | 2 | 2 | 2 |
| 2 | 0 | 4 | 2 | 2 | 0 | 0 | 2 | −2 | 0 | 0 | 2 | −2 | 0 | −4 | 2 | 2 |
| 3 | 0 | 0 | −2 | 2 | 0 | 0 | −2 | 2 | −2 | −2 | 4 | 0 | −2 | −2 | −4 | 0 |
| 4 | 0 | 0 | 0 | −4 | 2 | −2 | −2 | 2 | 0 | 0 | 0 | −4 | −2 | −2 | 2 | −2 |
| 5 | 0 | 4 | 0 | 0 | 2 | 2 | −2 | 2 | −2 | −2 | −2 | 2 | 4 | 0 | 0 | 0 |
| 6 | 0 | 0 | 2 | 2 | −2 | 2 | −4 | 0 | 0 | 4 | 2 | −2 | 2 | 2 | 0 | 0 |
| 7 | 0 | 0 | −2 | −2 | −2 | −2 | 0 | 0 | 2 | 2 | 0 | 0 | 4 | −4 | −2 | −2 |
| 8 | 0 | 2 | 0 | −2 | 0 | −2 | −4 | −2 | 2 | 0 | −2 | 0 | −2 | 0 | −2 | 4 |
| 9 | 0 | 2 | 0 | −2 | 4 | −2 | 0 | −2 | 0 | 2 | 4 | 2 | 0 | 2 | 0 | −2 |
| A | 0 | −2 | 2 | 0 | 4 | 2 | 2 | 0 | 2 | 0 | 0 | −2 | 2 | 0 | −4 | 2 |
| B | 0 | 2 | −2 | 0 | 0 | −2 | 2 | 0 | −4 | 2 | −2 | −4 | 0 | 2 | −2 | 0 |
| C | 0 | −2 | 4 | 2 | 2 | −4 | −2 | 0 | −2 | 0 | −2 | 0 | 0 | −2 | 0 | −2 |
| D | 0 | 2 | 4 | −2 | −2 | 0 | 2 | 4 | 0 | 2 | 0 | 2 | −2 | 0 | −2 | 0 |
| E | 0 | −2 | −2 | 0 | 2 | 0 | 0 | 2 | −2 | 4 | 0 | 2 | 0 | −2 | 2 | 4 |
| F | 0 | −2 | 2 | −4 | −2 | 0 | 0 | −2 | −4 | −2 | 2 | 0 | 2 | 0 | 0 | 2 |
| 0 | 1 | 2 | 3 | 4 | 5 | 6 | 7 | 8 | 9 | A | B | C | D | E | F | |
| 0 | 16 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 |
| 1 | 0 | 0 | 0 | 0 | 0 | 0 | 2 | 2 | 2 | 4 | 2 | 0 | 2 | 0 | 0 | 2 |
| 2 | 0 | 0 | 0 | 2 | 0 | 2 | 0 | 0 | 4 | 0 | 2 | 0 | 0 | 2 | 2 | 2 |
| 3 | 0 | 2 | 0 | 2 | 2 | 2 | 0 | 4 | 0 | 0 | 0 | 0 | 2 | 0 | 0 | 2 |
| 4 | 0 | 2 | 0 | 0 | 0 | 2 | 2 | 2 | 0 | 0 | 4 | 2 | 0 | 0 | 2 | 0 |
| 5 | 0 | 2 | 2 | 2 | 0 | 0 | 2 | 0 | 2 | 0 | 0 | 0 | 4 | 0 | 2 | 0 |
| 6 | 0 | 0 | 2 | 2 | 0 | 2 | 2 | 0 | 0 | 2 | 0 | 2 | 0 | 0 | 0 | 4 |
| 7 | 0 | 2 | 0 | 0 | 2 | 0 | 4 | 0 | 0 | 2 | 0 | 0 | 0 | 2 | 2 | 2 |
| 8 | 0 | 0 | 2 | 0 | 0 | 0 | 0 | 2 | 0 | 0 | 0 | 2 | 2 | 2 | 4 | 2 |
| 9 | 0 | 0 | 0 | 2 | 4 | 0 | 0 | 2 | 2 | 2 | 0 | 2 | 0 | 0 | 2 | 0 |
| A | 0 | 0 | 2 | 4 | 2 | 0 | 0 | 2 | 0 | 0 | 2 | 0 | 0 | 2 | 0 | 0 |
| B | 0 | 2 | 0 | 2 | 0 | 0 | 0 | 0 | 0 | 2 | 2 | 4 | 2 | 2 | 0 | 0 |
| C | 0 | 0 | 0 | 0 | 2 | 4 | 2 | 0 | 2 | 0 | 0 | 2 | 2 | 2 | 0 | 0 |
| D | 0 | 0 | 4 | 0 | 2 | 2 | 0 | 0 | 0 | 2 | 2 | 0 | 2 | 0 | 2 | 0 |
| E | 0 | 2 | 2 | 0 | 0 | 2 | 0 | 2 | 2 | 2 | 0 | 0 | 0 | 4 | 0 | 0 |
| F | 0 | 4 | 2 | 0 | 2 | 0 | 0 | 0 | 2 | 0 | 2 | 2 | 0 | 0 | 0 | 2 |
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Prathiba, A.; Bhaaskaran, V.S.K. Lightweight S-Box Architecture for Secure Internet of Things. Information 2018, 9, 13. https://doi.org/10.3390/info9010013
Prathiba A, Bhaaskaran VSK. Lightweight S-Box Architecture for Secure Internet of Things. Information. 2018; 9(1):13. https://doi.org/10.3390/info9010013
Chicago/Turabian StylePrathiba, A., and V. S. Kanchana Bhaaskaran. 2018. "Lightweight S-Box Architecture for Secure Internet of Things" Information 9, no. 1: 13. https://doi.org/10.3390/info9010013
APA StylePrathiba, A., & Bhaaskaran, V. S. K. (2018). Lightweight S-Box Architecture for Secure Internet of Things. Information, 9(1), 13. https://doi.org/10.3390/info9010013





