A Hybrid Classical-Quantum Neural Network Model for DDoS Attack Detection in Software-Defined Vehicular Networks
Abstract
1. Introduction
- Running complex quantum circuits in simulation can lead to memory overloads or crashes, especially when handling huge datasets [12].
- Quantum simulations, especially with hybrid models, can be significantly slower in notebook environments, causing delays in iterative experimentation and model tuning [13].
- PennyLane’s default simulators are CPU-based [9] and not optimized for speed. Accessing real quantum devices via plugins from notebooks can introduce additional latency or connection issues.
- We developed a hybrid C-QNN architecture that combines quantum circuits from PennyLane with classical input and output layers for effective DDoS attack detection in SDVNs.
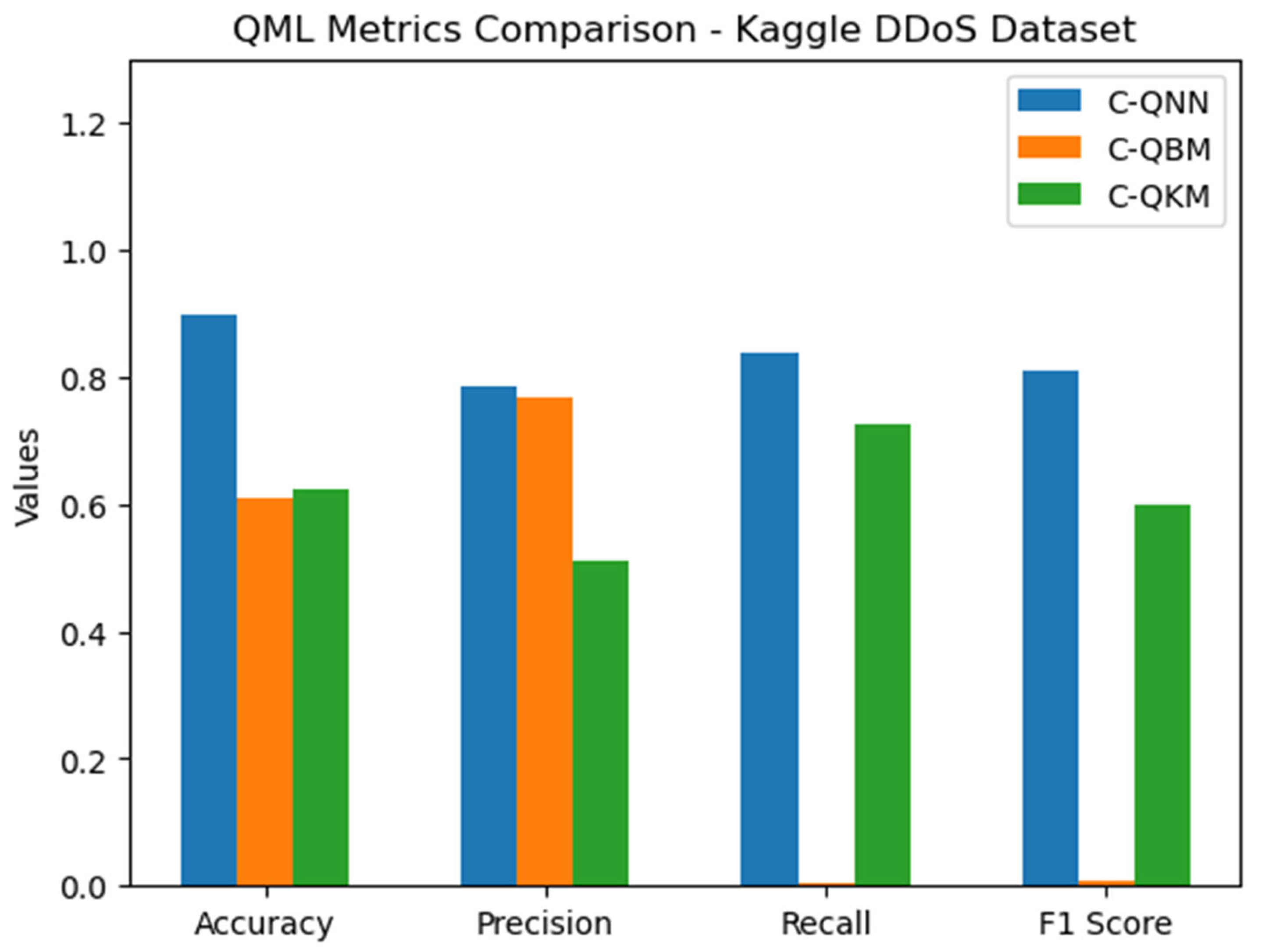
- We tested three different quantum machine learning approaches, C-QNN, C-QBM, and C-QKM, to determine DDoS attacks in vehicular networks.
- Using a hybrid C-QNN model, a 99% accuracy on the UNB-CIC-DDoS dataset and about 90% on the Kaggle DDoS dataset was achieved, outperforming other existing quantum techniques.
2. Literature Survey
3. Model Formulation, Architecture, and Deployment
| Algorithm 1: Hybrid C-QNN for Classification |
| Input: A Dataset with features and labels Output: Trained model and performance measurement. 1. Standardize the dataset to normalize feature scales. Apply dimensionality reduction to project the original high-dimensional data to a lower dimension suitable for quantum embedding. 2. Initialize a quantum circuit with several qubits equal to the decreased feature dimensions. 3. Define quantum operations to encode the data and create entanglement between qubits. 4. Initialize classical neural network layers, including hidden layers with activation functions and a final output layer for binary classification. 5. Repeat for each epoch and each training batch: a. Pass the input sample through the quantum circuit to obtain intermediate quantum features. b. Feed the quantum output to the classical neural network layers. c. Compute the prediction and compare it with the actual label using a suitable loss function. d. Update the parameters of both the quantum circuit and classical layers using hybrid optimization techniques. 6. Evaluate the trained model on the test dataset. 7. Measure performance using metrics such as accuracy, precision, recall, and F1-score. 8. Deploy the trained hybrid model within the application plane of the SDVN Ryu controller. Use the model to analyze incoming traffic and classify it as normal or DDoS in real time. |

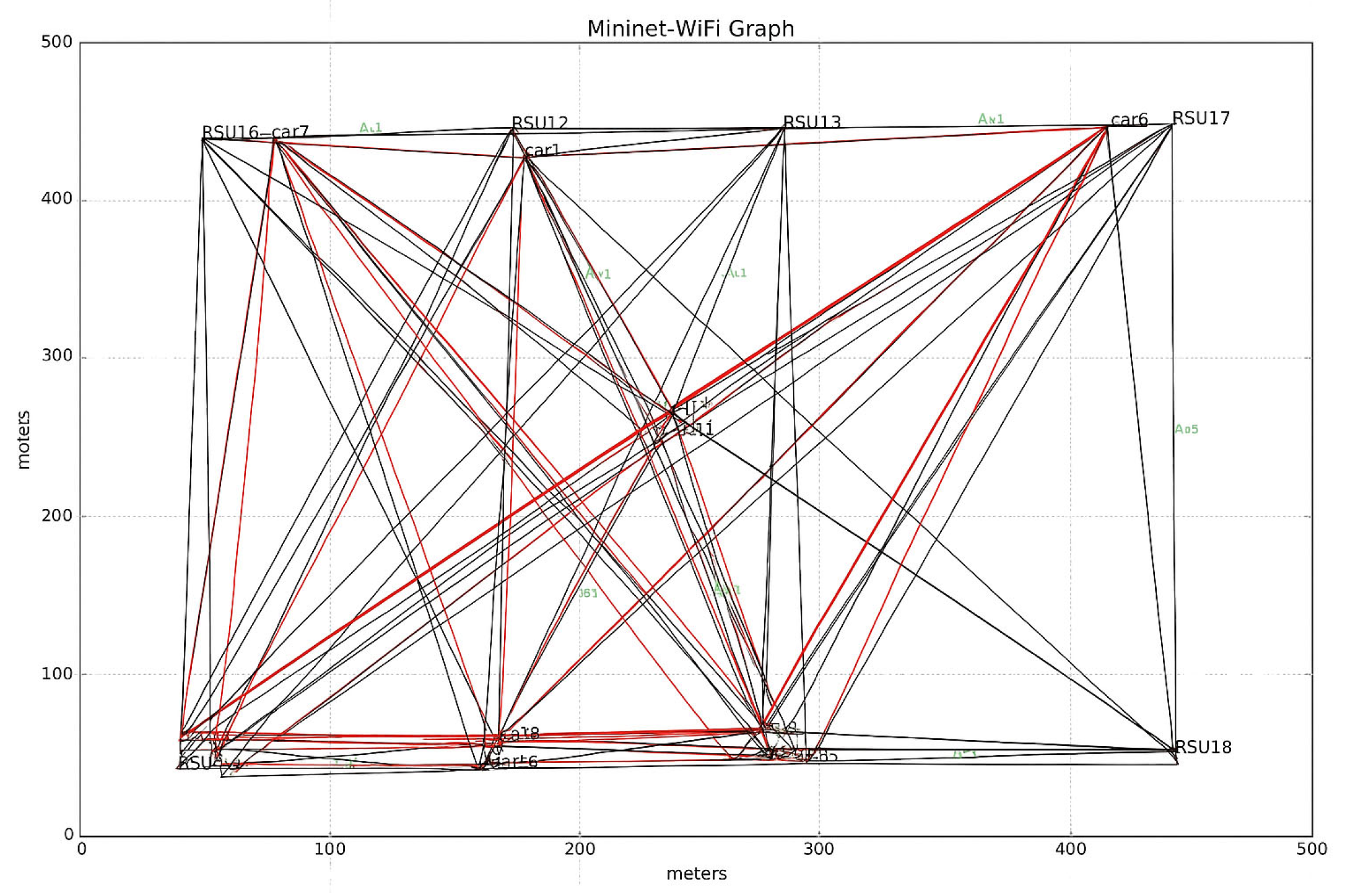
4. Simulation Environment Configuration
4.1. Simulation Objective
4.2. Simulation Tools Used
4.3. Performance Metrics
- Accuracy: It is the ratio of correctly predicted observations to the total observations, as presented in Equation (8) [40]. It is the most intuitive performance measure.where TP = True Positives, TN = True Negatives.Accuracy = (TN + TP)/(Total no. of samples)
- Precision: Also called the Positive Predictive Value, is the ratio of correctly predicted positive observations to the total predicted positives as presented in Equation (9) [40].where TP = True Positives, FP = False Positives.Precision = TP/(TP + FP)
- Recall (Sensitivity): It is the ratio of correctly predicted positive observations to all actual positives, as presented in Equation (10) [40].where TP = True Positives, FN = False Negatives.Recall = TP/(TP + FN)
- F1 Score: It is the harmonic mean of precision and recall values. It combines both metrics and is especially useful in imbalanced datasets, as shown in Equation (11) [40].F1 Score = 2 ∗ (Precision ∗ Recall)/(Precision + Recall)
- Adjusted Rand Index (ARI): It checks the similarity between two clustering by considering all pairs of samples and counting pairs that are assigned in the same or different clusters in the predicted and true labels [41], as represented in Equation (12). It adjusts for the chance grouping of elements.where RI is the Rand Index and E[RI] is the expected RI for random labeling.ARI = (RI − E[RI])/(max(RI) − E[RI])
- Normalized Mutual Information (NMI): It measures the amount of information shared between the predicted cluster assignments and the ground truth labels [42], as shown in Equation (13). It normalizes the Mutual Information score to scale between 0 (no mutual info) and 1 (perfect correlation). Let “U” and “V” be the sets of clusters and true labels, thenwhere: I(U, V) is the mutual information between U and V, andNMI(U,V) = 2 ∗ I(U,V)/(H(U) + H(V))H(U), H(V) are the entropies of clustering U and V.
- Silhouette Score (SS): In contrast to other clusters (separation), it evaluates how similar an object is to its cluster (cohesion) [43] as presented in Equation (14). The score ranges from −1 (incorrect clustering) to 1 (well clustered), with values near 0 indicating overlapping clusters.
4.4. Experimental Setup
4.5. Testbed Deployment
| Algorithm 2: Testing Quantum Models in SDVN Environment via Flooding |
| Input: Trained quantum and hybrid quantum-classical models (C-QNN, QBM, QKM), SDVN testbed (Mininet-WiFi with Ryu controller) Output: Classification of incoming traffic as benign or an attack. 1. Initialize the SDVN Testbed \\ Launch Mininet-WiFi and start Ryu controller 2. Deploy Monitoring Agents 3. Load the pretrained C-QNN model into the evaluation environment 4. Generate benign vehicular traffic using Iperf application flows. 5. Initiate a UDP flooding attack from vehicular nodes using the tool ‘hping3’ 6. Continue the attack for a predefined interval (e.g., 30–60 s) 7. For the hybrid classical quantum model: a. Feed preprocessed traffic data b. Capture predicted labels (benign or attack) 8. Repeat steps 4–7 for robustness analysis |
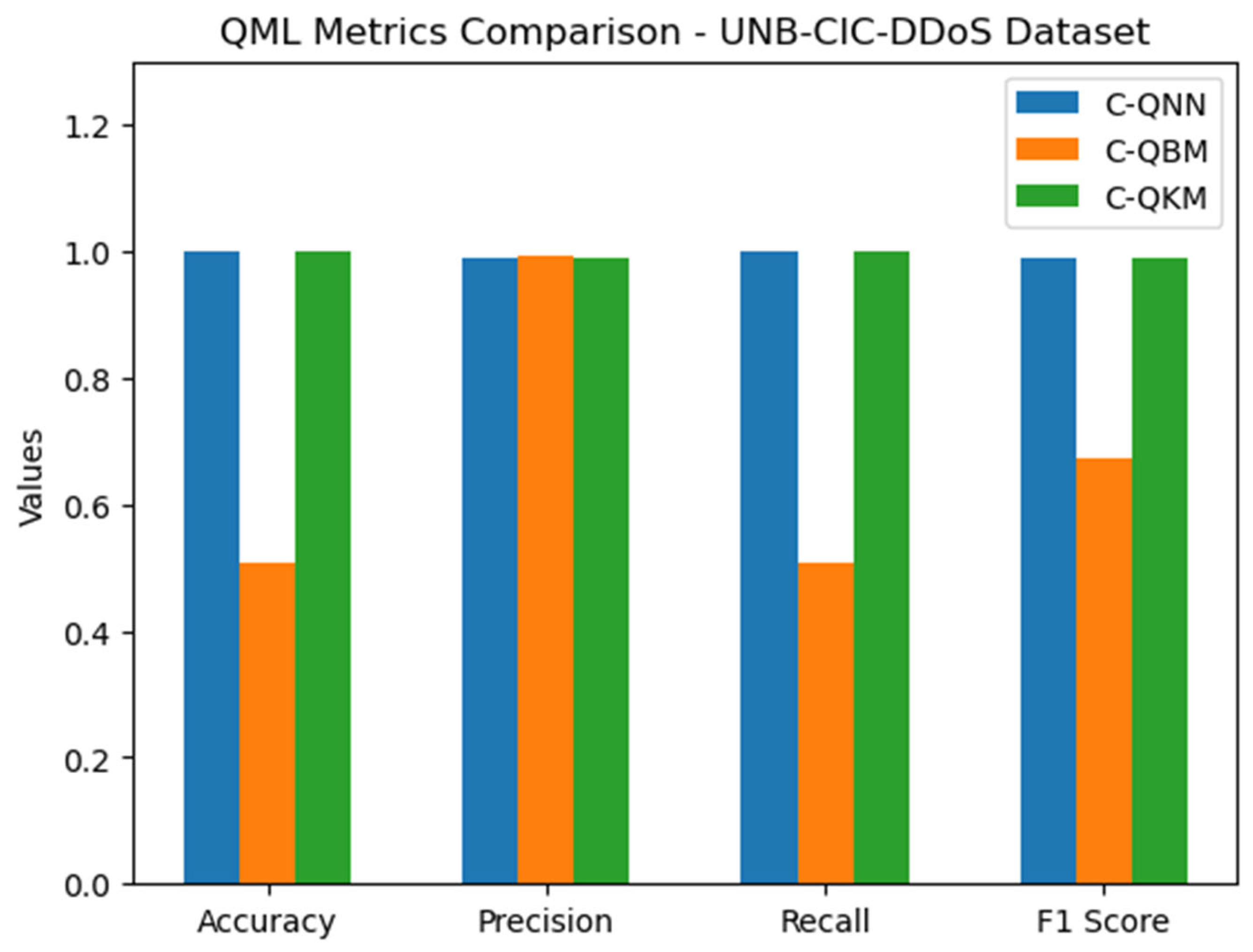
5. Result Analysis
6. Results Discussion
7. Conclusions and Future Work
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Hussein, N.H.; Koh, J.S.P.; Yaw, C.T.; Tiong, S.K.; Benedict, F.; Yusaf, T.; Kadirgama, K.; Hong, T.C. SDN-Based VANET Routing: A Comprehensive Survey on Architectures, Protocols, Analysis, and Future Challenges. IEEE Access 2024, 13, 126801–126861. [Google Scholar] [CrossRef]
- Chaudhary, R.; Aujla, G.S.; Kumar, N.; Chouhan, P.K. A comprehensive survey on software-defined networking for smart communities. Int. J. Commun. Syst. 2025, 38, e5296. [Google Scholar] [CrossRef]
- Alaya, B.; Sellami, L. Toward the Design of an Efficient and Secure System Based on the Software-Defined Network Paradigm for Vehicular Networks. IEEE Access 2023, 11, 43333–43348. [Google Scholar] [CrossRef]
- Kumar, R.; Agrawal, N. A survey on software-defined vehicular networks (SDVNs): A security perspective. J. Supercomput. 2022, 79, 8368–8400. [Google Scholar] [CrossRef]
- Babbar, H.; Rani, S.; Driss, M. Effective DDoS attack detection in software-defined vehicular networks using statistical flow analysis and machine learning. PLoS ONE 2024, 19, e0314695. [Google Scholar] [CrossRef]
- Musa, N.S.; Mirza, N.M.; Rafique, S.H.; Abdallah, A.M.; Murugan, T. Machine Learning and Deep Learning Techniques for Distributed Denial of Service Anomaly Detection in Software Defined Networks—Current Research Solutions. IEEE Access 2024, 12, 17982–18011. [Google Scholar] [CrossRef]
- Zeguendry, A.; Jarir, Z.; Quafafou, M. Quantum machine learning: A review and case studies. Entropy 2023, 25, 287. [Google Scholar] [CrossRef]
- Abbas, A.; Sutter, D.; Zoufal, C.; Lucchi, A.; Figalli, A.; Woerner, S. The power of quantum neural networks. Nat. Comput. Sci. 2021, 1, 403–409. [Google Scholar] [CrossRef]
- Pennylane Documentation. Available online: https://pennylane.ai/qml (accessed on 17 June 2025).
- Küçükkara, M.Y.; Atban, F.; Bayılmış, C. Quantum-Neural Network Model for Platform Independent Ddos Attack Classification in Cyber Security. Adv. Quantum Technol. 2024, 7, 2400084. [Google Scholar] [CrossRef]
- Tychola, K.A.; Kalampokas, T.; Papakostas, G.A. Quantum Machine Learning—An Overview. Electronics 2023, 12, 2379. [Google Scholar] [CrossRef]
- Oftelie, L.B.; Urbanek, M.; Metcalf, M.; Carter, J.; Kemper, A.F.; de Jong, W.A. Simulating quantum materials with digital quantum computers. Quantum Sci. Technol. 2021, 6, 043002. [Google Scholar] [CrossRef]
- Aldoseri, A.; Al-Khalifa, K.N.; Hamouda, A.M. Re-Thinking Data Strategy and Integration for Artificial Intelligence: Concepts, Opportunities, and Challenges. Appl. Sci. 2023, 13, 7082. [Google Scholar] [CrossRef]
- DoS Evaluation Dataset (CIC-DDoS2019). Available online: https://www.unb.ca/cic/datasets/ddos-2019.html (accessed on 17 June 2025).
- DDoS SDN Dataset. Available online: https://www.kaggle.com/datasets/aikenkazin/ddos-sdn-dataset (accessed on 17 June 2025).
- Devadas, R.M.; Sowmya, T. Quantum machine learning: A comprehensive review of integrating AI with quantum computing for computational advancements. MethodsX 2025, 14, 103318. [Google Scholar] [CrossRef]
- Rivas, P.; Orduz, J.; Jui, T.D.; DeCusatis, C.; Khanal, B. Quantum-Enhanced Representation Learning: A Quanvolutional Autoencoder Approach against DDoS Threats. Mach. Learn. Knowl. Extr. 2024, 6, 944–964. [Google Scholar] [CrossRef]
- Kadi, A.; Selamnia, A.; Houda, Z.A.E.; Moudoud, H.; Brik, B.; Khoukhi, L. An In-Depth Comparative Study of Quantum-Classical Encoding Methods for Network Intrusion Detection. IEEE Open J. Commun. Soc. 2025, 6, 1129–1148. [Google Scholar] [CrossRef]
- Said, D. Quantum Computing and Machine Learning for Cybersecurity: Distributed Denial of Service (DDoS) Attack Detection on Smart Micro-Grid. Energies 2023, 16, 3572. [Google Scholar] [CrossRef]
- Saritha, A.; Reddy, B.R.; Babu, A.S. QEMDD: Quantum Inspired Ensemble Model to Detect and Mitigate DDoS Attacks at Various Layers of SDN Architecture. Wirel. Pers. Commun. 2022, 127, 2365–2390. [Google Scholar] [CrossRef]
- Said, D.; Bagaa, M.; Oukaira, A.; Lakhssassi, A. Quantum Entropy and Reinforcement Learning for Distributed Denial of Service Attack Detection in Smart Grid. IEEE Access 2024, 12, 129858–129869. [Google Scholar] [CrossRef]
- Hasan, B.M.S.; Abdulazeez, A.M. A Review of Principal Component Analysis Algorithm for Dimensionality Reduction. J. Soft Comput. Data Min. 2021, 2, 20–30. [Google Scholar] [CrossRef]
- Gewers, F.L.; Ferreira, G.R.; Arruda, H.F.D.; Silva, F.N.; Comin, C.H.; Amancio, D.R.; Costa, L.D.F. Principal component analysis: A natural approach to data exploration. ACM Comput. Surv. (CSUR) 2021, 54, 1–34. [Google Scholar] [CrossRef]
- Mancilla, J.; Pere, C. A Preprocessing Perspective for Quantum Machine Learning Classification Advantage in Finance Using NISQ Algorithms. Entropy 2022, 24, 1656. [Google Scholar] [CrossRef] [PubMed]
- Hou, Y.-Y.; Li, J.; Xu, T.; Liu, X.-Y. A hybrid quantum-classical classification model based on branching multi-scale entanglement renormalization ansatz. Sci. Rep. 2024, 14, 18521. [Google Scholar] [CrossRef] [PubMed]
- Chen, S.Y.-C.; Huang, C.-M.; Hsing, C.-W.; Kao, Y.-J. An end-to-end trainable hybrid classical-quantum classifier. Mach. Learn. Sci. Technol. 2021, 2, 045021. [Google Scholar] [CrossRef]
- Ajagekar, A.; You, F. Variational quantum circuit based demand response in buildings leveraging a hybrid quantum-classical strategy. Appl. Energy 2024, 364, 123244. [Google Scholar] [CrossRef]
- Combarro, E.F.; González-Castillo, S.; Di Meglio, A. A Practical Guide to Quantum Machine Learning and Quantum Optimization: Hands-on Approach to Modern Quantum Algorithms; Packt Publishing Ltd.: Birmingham, UK, 2023. [Google Scholar]
- Zhou, X.; Qiu, D. Blind quantum machine learning based on quantum circuit model. Quantum Inf. Process. 2021, 20, 363. [Google Scholar] [CrossRef]
- Liu, Y.; Arunachalam, S.; Temme, K. A rigorous and robust quantum speed-up in supervised machine learning. Nat. Phys. 2021, 17, 1013–1017. [Google Scholar] [CrossRef]
- Daubechies, I.; DeVore, R.; Foucart, S.; Hanin, B. Nonlinear Approximation and (Deep) ReLU Networks. Constr. Approx. 2021, 55, 127–172. [Google Scholar] [CrossRef]
- Dubey, S.R.; Singh, S.K.; Chaudhuri, B.B. Activation functions in deep learning: A comprehensive survey and benchmark. Neurocomputing 2022, 503, 92–108. [Google Scholar] [CrossRef]
- Hurtik, P.; Tomasiello, S.; Hula, J.; Hynar, D. Binary cross-entropy with dynamical clipping. Neural Comput. Appl. 2022, 34, 12029–12041. [Google Scholar] [CrossRef]
- TensorFlow Documentation. Available online: https://www.tensorflow.org/ (accessed on 17 June 2025).
- Bhardwaj, S.; Panda, S.N. Performance Evaluation Using RYU SDN Controller in Software-Defined Networking Environment. Wirel. Pers. Commun. 2022, 122, 701–723. [Google Scholar] [CrossRef]
- Sarvade, V.P.; Kulkarni, S.A. Support vector machine empowered Ryu controller for enhanced multimedia QoS in a realistic software defined vehicular networks. In Data Science & Exploration in Artificial Intelligence: CODE-AI; CRC Press: Boca Raton, FL, USA, 2025. [Google Scholar] [CrossRef]
- Fontes, R.R.; Afzal, S.; Brito, S.H.B.; Santos, M.A.S.; Rothenberg, C.E. Mininet-WiFi: Emulating software-defined wireless networks. In Proceedings of the International Conference on Network and Service Management (CNSM), Barcelona, Spain, 9–13 November 2015; IEEE: New York, NY, USA, 2016; pp. 384–389. [Google Scholar] [CrossRef]
- Ryu Controller. Available online: https://ryu-sdn.org/ (accessed on 17 June 2025).
- Keras Documentation. Available online: https://keras.io/ (accessed on 17 June 2025).
- Classification: Accuracy, Recall, Precision, and Related Metrics, Google for Developers. Available online: https://developers.google.com/machine-learning/crash-course/classification/accuracy-precision-recall (accessed on 17 June 2025).
- Sundqvist, M.; Chiquet, J.; Rigaill, G. Adjusting the adjusted Rand Index. Comput. Stat. 2022, 38, 327–347. [Google Scholar] [CrossRef]
- Islam, M.R.; Ahmed, B.; Hossain, M.A.; Uddin, M.P. Mutual Information-Driven Feature Reduction for Hyperspectral Image Classification. Sensors 2023, 23, 657. [Google Scholar] [CrossRef]
- Shutaywi, M.; Kachouie, N.N. Silhouette Analysis for Performance Evaluation in Machine Learning with Applications to Clustering. Entropy 2021, 23, 759. [Google Scholar] [CrossRef]
- Sarvade, V.P.; Kulkarni, S.A. Deep learning based adaptive Ryu controller model for quality of experience issues in multimedia streaming for software defined vehicular networks. Appl. Int. 2024, 54, 9543–9564. [Google Scholar] [CrossRef]

| Aspect | Our Contribution | Difference from Existing Literature |
|---|---|---|
| Target Domain | Focused on Software-Defined Vehicular Networks (SDVNs) | Other works mainly address Smart Micro-Grids (SMG), generic SDNs, or NIDS. |
| Model Type | Hybrid Classical-Quantum Neural Network (C-QNN), QBM, and QKM | Other studies use single models like QSVM, QAOA, or conceptually inspired methods. |
| Quantum Integration | Implemented real quantum circuits using PennyLane | Many existing works are quantum-inspired only or rely on classical simulations. |
| Learning Paradigms | Combination of supervised (C-QNN), unsupervised (QKM), and probabilistic (QBM) models | Most papers focus on only one paradigm (e.g., QSVM or Ensemble methods). |
| Benchmark Datasets | Tested on two real-world DDoS datasets: UNB-CIC-DDoS and Kaggle DDoS | Some existing works use limited or synthetic datasets; not all benchmark multiple datasets. |
| Performance | Achieves ~99% accuracy on UNB-CIC and ~90% on the Kaggle dataset | Higher or comparable performance, with broader applicability to vehicular networks. |
| Scalability and Realism | Addresses realistic traffic in SDVN, including multi-model performance | Other methods often lack domain-specific tuning or real deployment scenarios. |
| Aspect | Kaggle DDoS SDN Dataset [15] | CIC-DDoS2019 Dataset [14] |
|---|---|---|
| Source | Kaggle (Contributed by Aiken Kazin) | Canadian Institute for Cybersecurity (CIC) |
| Year of Release | 2020 | 2019 |
| Environment | Simulated SDN environment using Mininet emulator with Ryu controller. | Realistic testbed simulating a victim network with multiple operating systems and a firewall. |
| Features | 23 features including switch ID, packet count, byte count, duration, source/destination IPs, ports, tx_bytes, rx_bytes, and timestamp. | Over 80 features, including flow duration, packet counts, byte counts, and various statistical measures. |
| Data Format | CSV files with labelled flows. | CSV files with labelled flows. |
| Labeling | Binary labels indicating normal or attack traffic. | Detailed labelling with specific attack types and timestamps. |
| Use Case | Designed for evaluating DDoS detection mechanisms in SDN environments. | Suitable for developing and evaluating intrusion detection systems, especially for DDoS attack determination and taxonomy studies. |
| Model Type | Dataset | Qubits | Layers | Learning Rate | Epochs | Batch Size | Optimizer | PCA Components |
|---|---|---|---|---|---|---|---|---|
| C-QNN | UNB-CIC-DDoS | 2 | 1 | 0.01 | 30 | 5 | Adam (PennyLane) | 2 |
| C-QNN | Kaggle DDoS | 4 | 3 | default (Adam) | 30 | 5 | Adam (PennyLane) | 2 |
| C-QKM | UNB-CIC-DDoS | 4 | – | – | 30 | – | – (iterative update) | 2 |
| C-QKM | Kaggle DDoS | 2 | – | – | 30 | – | – (iterative update) | 2 |
| C-QBM | UNB-CIC-DDoS | 2 | – | 0.005 | 30 | – | Adam (PennyLane) | 2 |
| C-QBM | Kaggle DDoS | 2 | – | 0.05 | 30 | – | Adam (PennyLane) | 2 |
| Parameter | Value/Setting |
|---|---|
| Simulator | Mininet-Wifi (Python-based network simulator) |
| Controller | Ryu SDVN Controller |
| Number of Vehicles (Nodes) | 10 |
| Number of APs (RSUs) | 9 |
| Vehicle Interfaces | WLAN interfaces |
| Vehicle speed range | min_speed = 0 kmph, max_speed = 100 kmph (randomised input mobility model) |
| RSU Mode | 802.11 n/ac |
| Propagation Model | Friss (path loss model) |
| Wireless link type | wmediumd (interference mode: Realistic link quality modelling) |
| QML Method | Accuracy | Precision | Recall | F1 Score | ARI | NMI | Silhouette Score |
|---|---|---|---|---|---|---|---|
| C-QNN | 0.9989 | 0.99 | 0.9994 | 0.99 | - | - | - |
| C-QBM | 0.5062 | 0.9933 | 0.5068 | 0.6712 | - | - | - |
| C-QKM | 0.9988 | 0.99 | 0.9988 | 0.99 | 0.9075 | 0.8431 | 0.9772 |
| QML Method | Accuracy | Precision | Recall | F1 Score | ARI | NMI | Silhouette Score |
|---|---|---|---|---|---|---|---|
| C-QNN | 0.8996 | 0.7855 | 0.8364 | 0.8109 | - | - | - |
| C-QBM | 0.6108 | 0.7692 | 0.0039 | 0.0065 | - | - | - |
| C-QKM | 0.6219 | 0.5107 | 0.7247 | 0.5992 | 0.0588 | 0.05746 | 0.1791 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Sarvade, V.P.; Kulkarni, S.A.; Raj, C.V. A Hybrid Classical-Quantum Neural Network Model for DDoS Attack Detection in Software-Defined Vehicular Networks. Information 2025, 16, 722. https://doi.org/10.3390/info16090722
Sarvade VP, Kulkarni SA, Raj CV. A Hybrid Classical-Quantum Neural Network Model for DDoS Attack Detection in Software-Defined Vehicular Networks. Information. 2025; 16(9):722. https://doi.org/10.3390/info16090722
Chicago/Turabian StyleSarvade, Varun P., Shrirang Ambaji Kulkarni, and C. Vidya Raj. 2025. "A Hybrid Classical-Quantum Neural Network Model for DDoS Attack Detection in Software-Defined Vehicular Networks" Information 16, no. 9: 722. https://doi.org/10.3390/info16090722
APA StyleSarvade, V. P., Kulkarni, S. A., & Raj, C. V. (2025). A Hybrid Classical-Quantum Neural Network Model for DDoS Attack Detection in Software-Defined Vehicular Networks. Information, 16(9), 722. https://doi.org/10.3390/info16090722







