THREATGET: Towards Automated Attack Tree Analysis for Automotive Cybersecurity
Abstract
1. Introduction
2. Materials and Methods
2.1. Generic Cybersecurity Management
- 1.
- Gather information on components that should be used during the design/development phase, or for productive systems, information on existing components.
- 2.
- Model the system with all communication channels and security assumptions as precisely as possible.
- 3.
- Define a threat model with information from experts, and known threats and derive them from available sources (e.g., threat intelligence).
- 4.
- Compare the threat model to the system model to identify potential threats and system weaknesses.
- 5.
- Evaluate the risks of identified threats and decide on the risk treatment options based on impact and likelihood.
- 6.
- Update the system model with mitigation strategies and security countermeasures.
- 7.
- Go back to step 4 to identify newly introduced threats or threats that remained untreated.
2.2. Automotive Cybersecurity Management
2.2.1. Research Projects
2.2.2. ISO/SAE 21434
- asset identification: identifies assets, including their relevant cybersecurity property (CIA), which leads to one or more damage scenarios if the cybersecurity property is violated.
- threat scenario identification: describe a potential threat that could cause the violation of a cybersecurity property of an asset.
- impact rating: rates the impact on different categories (safety, financial, operational, privacy) of a damage scenario. In the automotive domain, safety is normally rated in four levels adapted from ASIL. A detailed definition of the terms can be found in the ISO/SAE 21434.
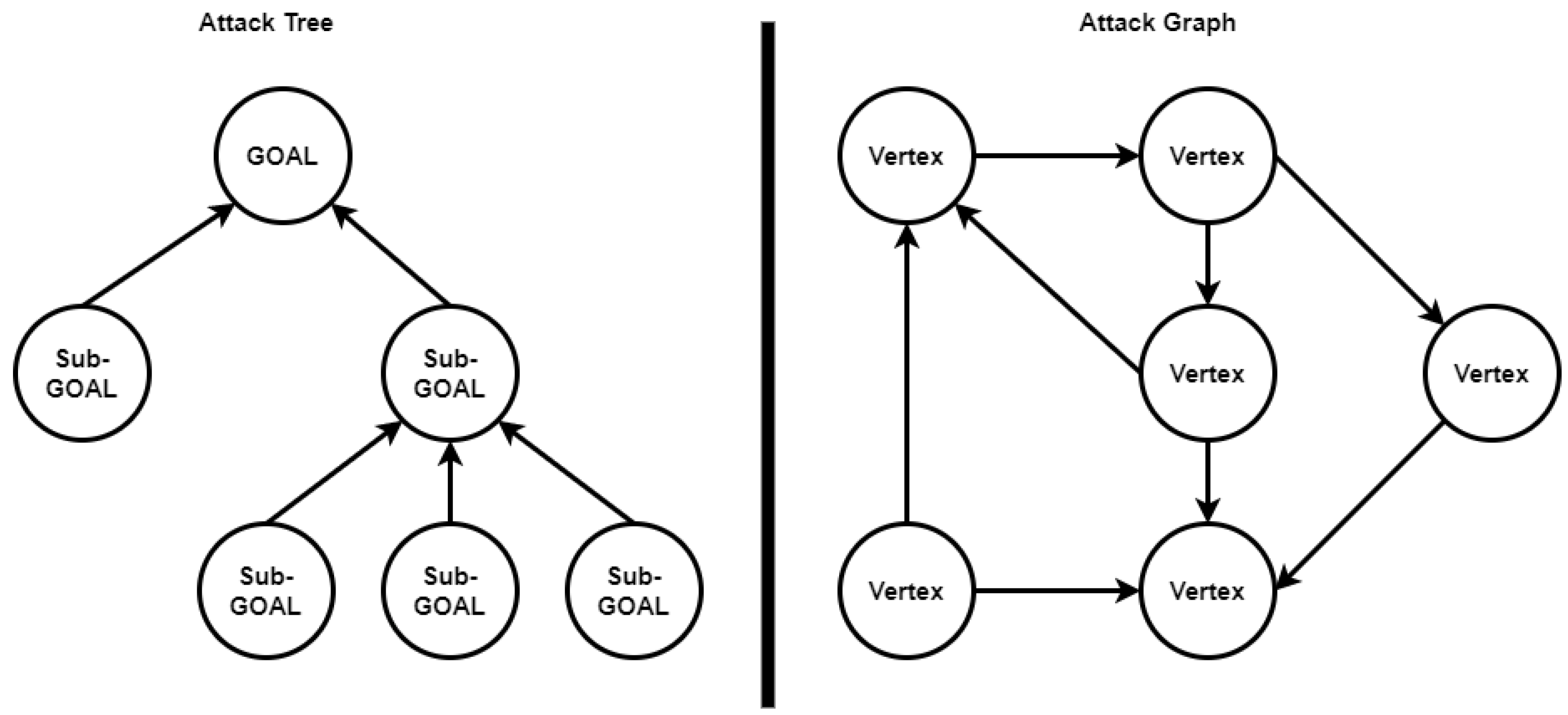
- attack path analysis: identifies a potential attack path or if multiple attack paths are possible an attack tree that could enable an attacker to execute an identified threat scenario.
- attack feasibility rating: rates the feasibility, e.g., the likelihood of an attack path based on a rating scheme and subfactors.
- risk value determination: uses a risk matrix to combine impact rating and attack feasibility rating to derive the risk for each combination of impact and attack feasibility.
- risk treatment decision: decides on the suggested course of action, e.g., if a risk is accepted or additional measures are needed.
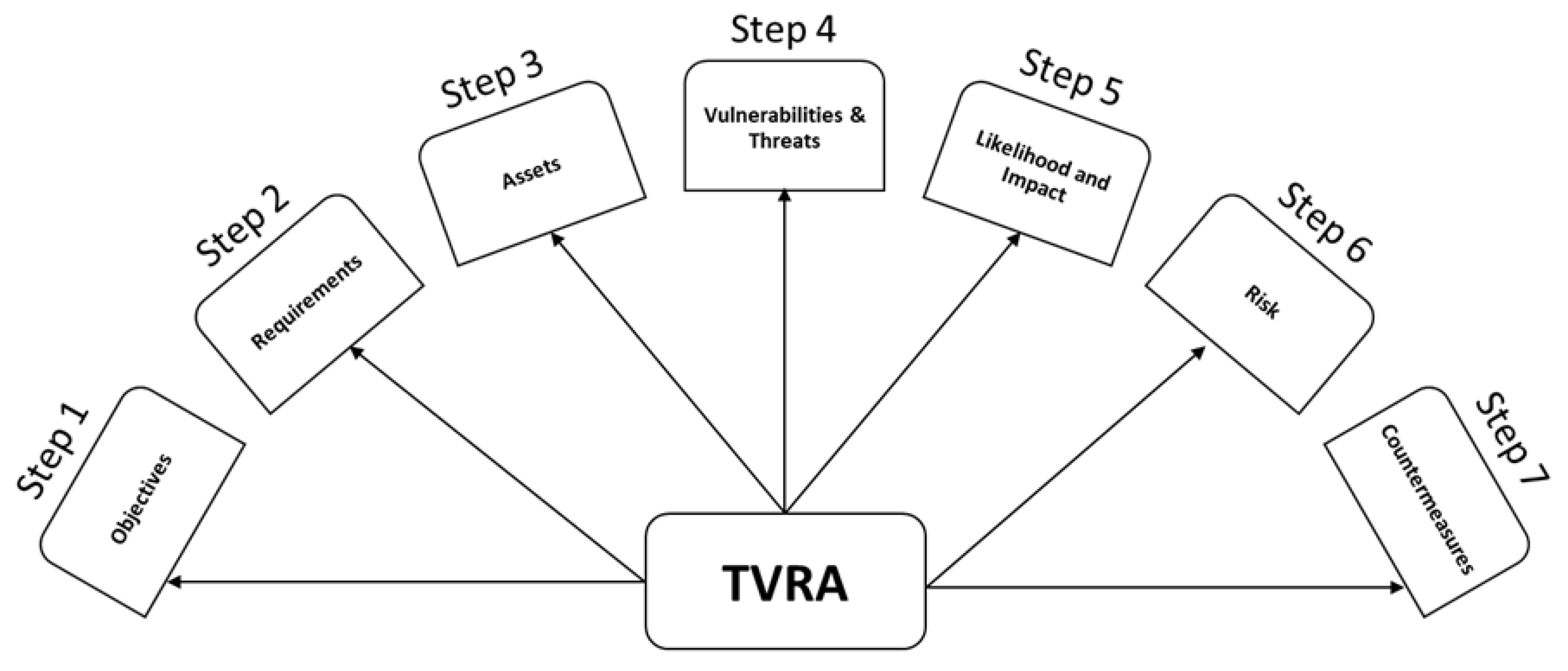
2.2.3. ETSI TVRA
- 1.
- Establish the objectives that need to be met in terms of security goals.
- 2.
- Establish what level of security requirements are required.
- 3.
- Create a checklist of all the system’s assets.
- 4.
- Identify the system vulnerabilities and potential cyber threats.
- 5.
- Determine how likely an attack is and the extent of its impact.
- 6.
- Determine the risk’s scope by combining the likelihood and impact calculation results.
- 7.
- Provide detailed guidance on the proper precautions against existing security issues.
2.2.4. UNECE WP29
3. THREATGET—Cybersecurity by Design
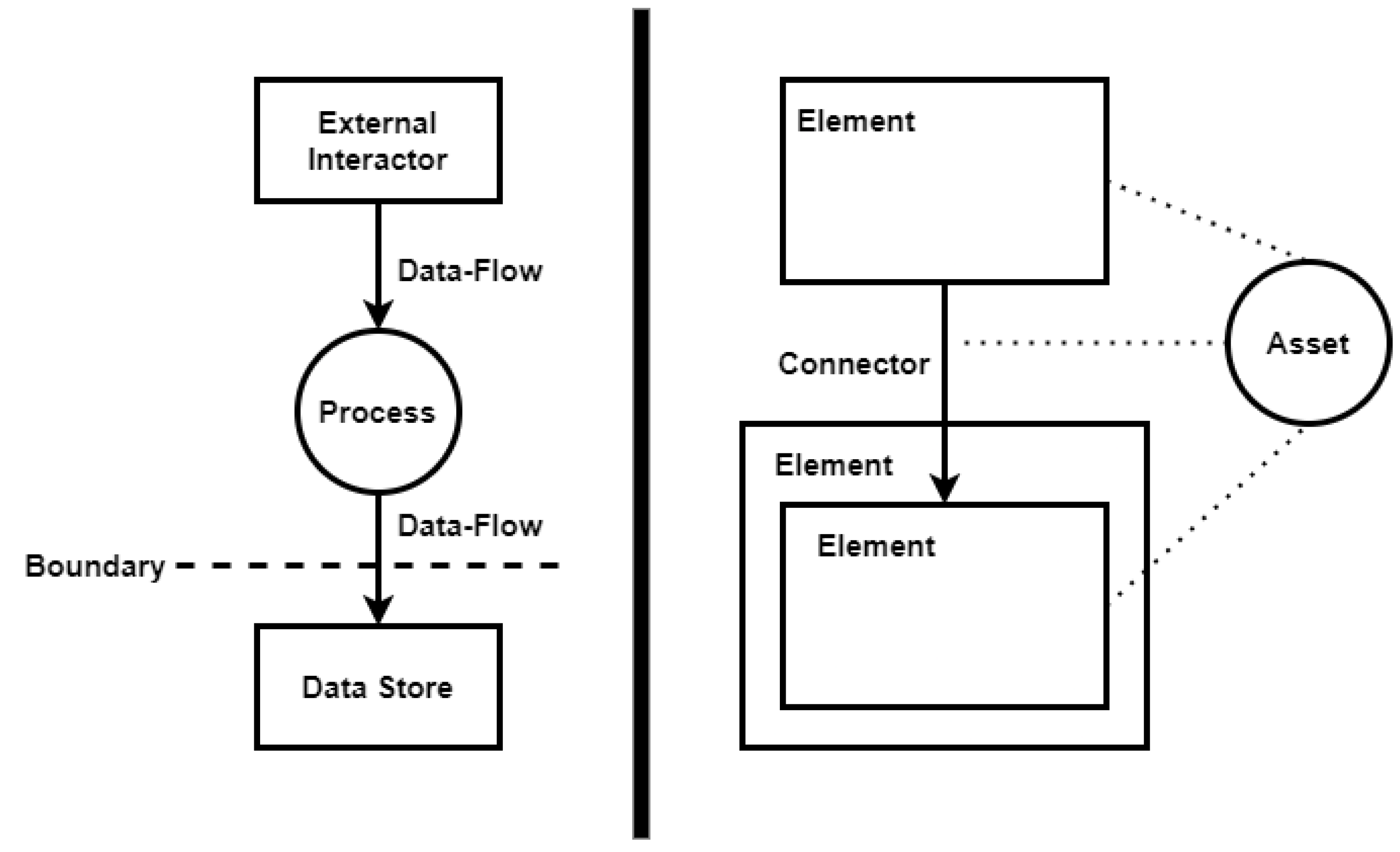
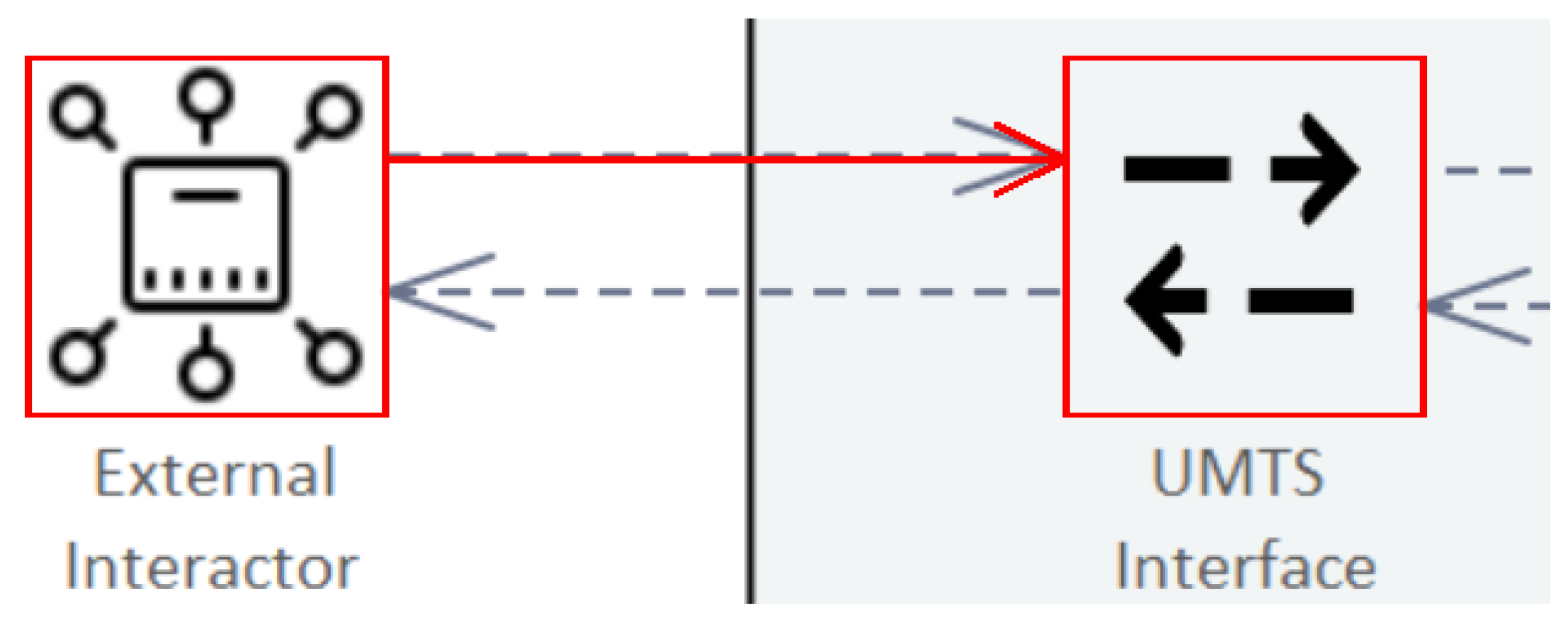
3.1. THREATGET’s Approach towards Threat Modeling
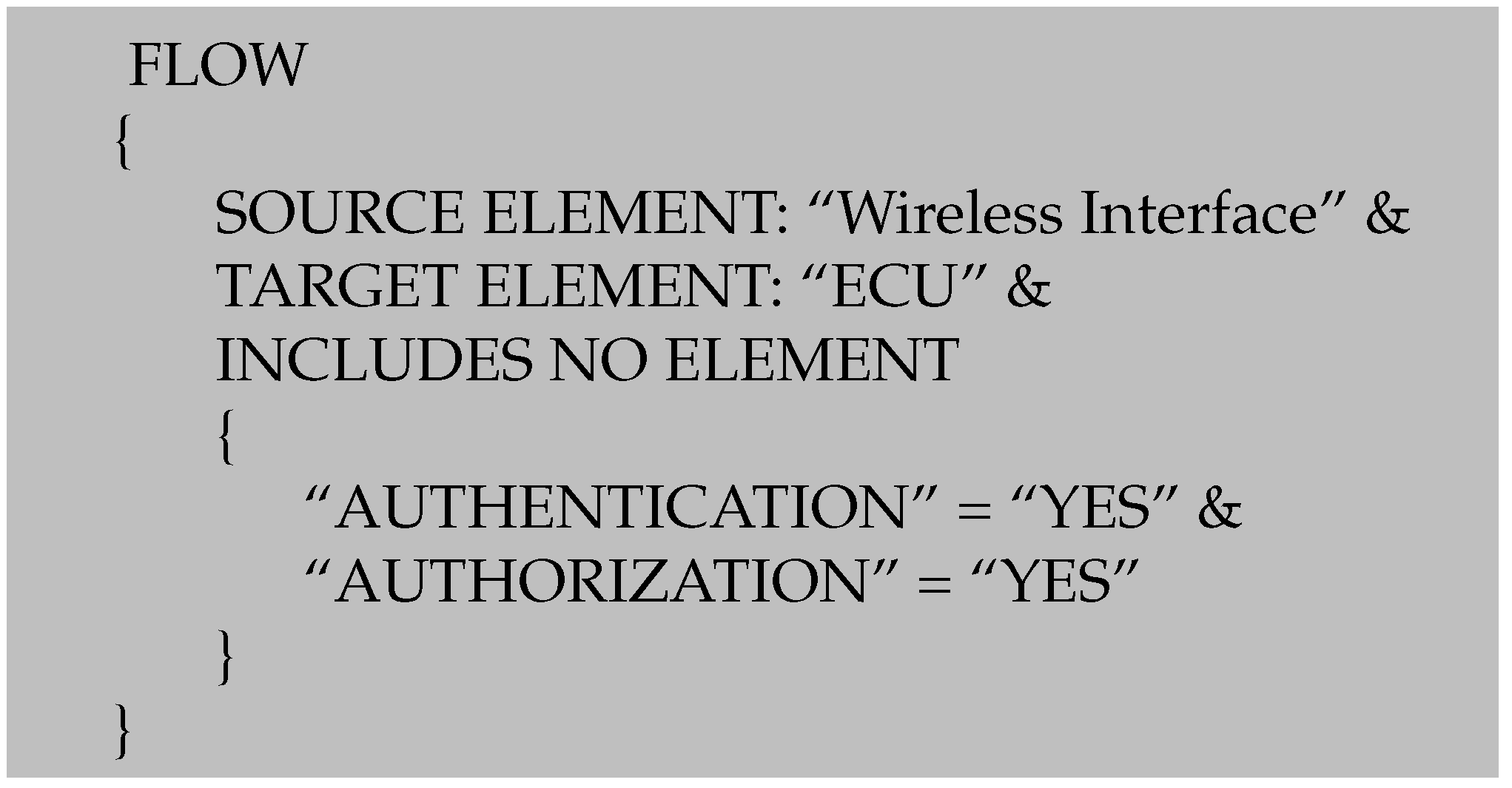
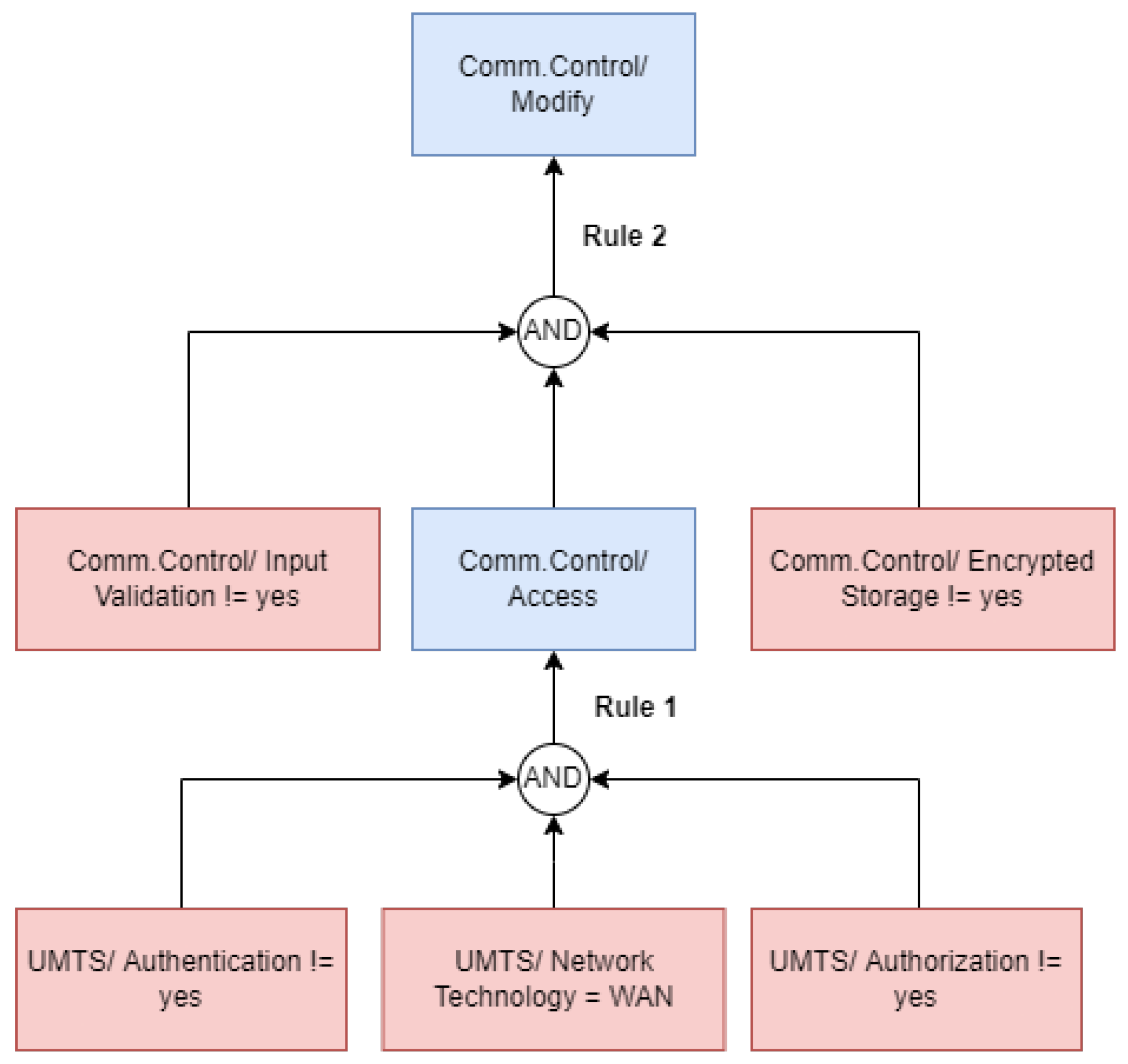
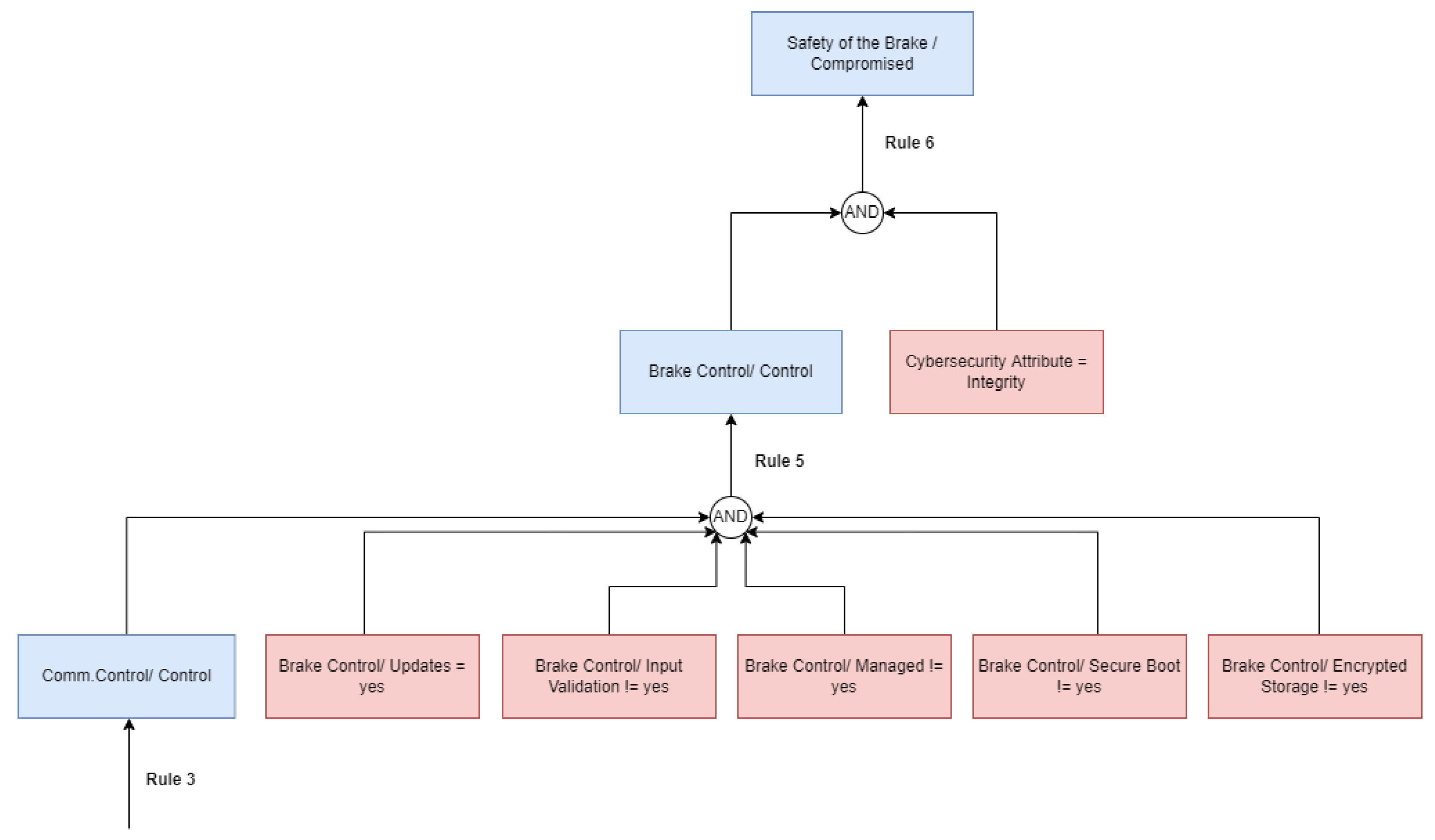
3.2. Automated Attack Tree Analysis
- 1.
- Manual generation, like all manual threat analyses, depends on expertise and experience. Analysis conducted by an expert in hardware security will look different from an analysis done by an expert in cryptography. Consequently, completeness is difficult to argue, and paths might be overlooked.
- 2.
- If an attacker can choose between different goals, or if multiple potential attackers need to be considered, generation, maintenance, and evaluation of the resulting trees are time-consuming. They need to be updated, depending on new vulnerability information or changes in the system architecture and larger system models result in an increased number of attack trees, which makes them grow in size.

- 1.
- The system model to be analyzed;
- 2.
- The set of anti-patterns to be used for the analysis;
- 3.
- (Optional) A set of initial capabilities defined by the user before the analysis to model assumptions of attacker capabilities.
- 1.
- A new component has been affected and is, therefore, inserted into the graph as a vertex;
- 2.
- A capability has changed because a rule has increased the assigned value;
- 3.
- A new rule is valid, which leads to a new edge inside the graph.
4. Evaluation Example
4.1. THREATGET and TARA
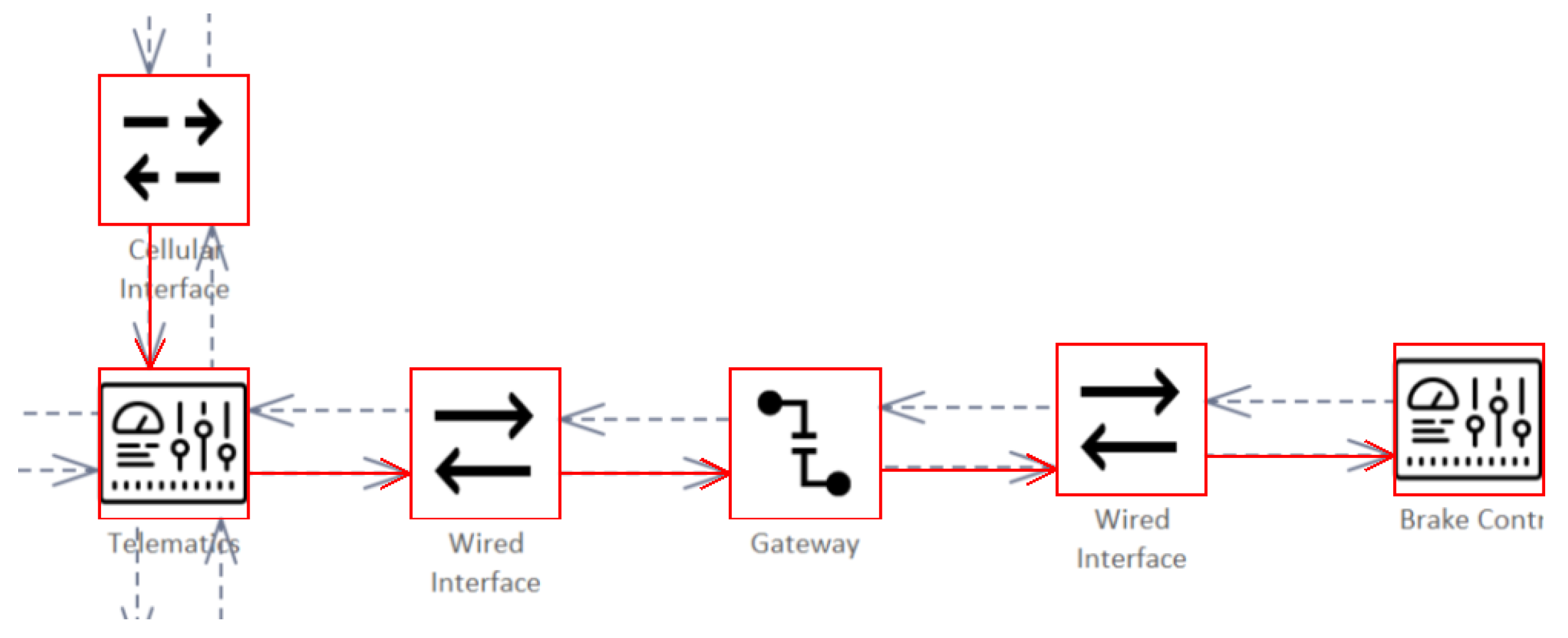
4.1.1. A Typical Automotive Architecture
4.1.2. Definition of Assets and Damage Scenarios
- 1.
- Asset: Availability of the Brake depicts that if an attacker gains control over the component holding the asset, they can disrupt the availability of the brake. It refers to the brake control becoming unavailable. This becomes relevant when the vehicle does a self-check at startup to verify that all vehicle control units are reachable. With regard to the availability of the brake, if e.g., the brake is not reachable the vehicle does not start. This could happen in case a trojan was placed within the vehicle network, thus, flooding the CAN Bus with messages. It is not required to take over a control unit, a simple blocking of the CAN Bus is sufficient. The availability of the brake was rated with an impact value of “Major”.
- 2.
- Asset: Safety of the Brake describes an asset that may be affected by integrity breaches. In case an attacker disrupts the correct functionality of the brake, even for a short time, this might result in an accident. The attacker could wait until the driver intends to do an emergency braking and prohibit the action or they could wait until the car reaches a certain velocity and force an emergency braking. Both ways most likely result in an accident. Therefore, this asset was rated with the maximum impact level “Severe” which represents the maximum impact.
4.1.3. System Architecture
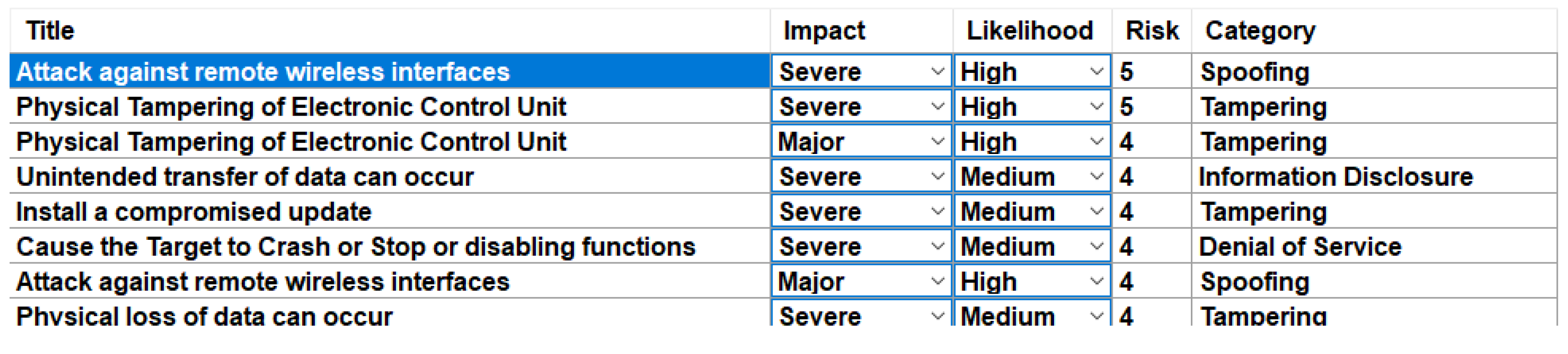
4.1.4. Identification of Threats
4.1.5. Identification of Attack Scenarios—Attack Trees
5. Results
6. Discussion
7. Patents
Author Contributions
Funding
Data Availability Statement
Acknowledgments
Conflicts of Interest
Abbreviations
| AIT | Austrian Institute of Technology |
| CCAM | Cooperative Connected and Automated Mobility |
| CAN | Controller Area Network |
| CIA | Confidentiality, Integrity, Availability |
| C-ITS | Cooperative Intelligent Transport System |
| CPS | Cyber–Physical System |
| CSMS | Cybersecurity Management System |
| DDoS | Distributed Denial of Service |
| DFD | Data-Flow Diagram |
| DSL | Domain Specific Language |
| DREAD | Damage Potential, Reproducibility, Exploitability, Affected Users, and Discoverability |
| ECU | Electronic Control Unit |
| EDFD | Extended Data-Flow Diagram |
| ETSI | European Telecommunications Standards Institute |
| EVITA | E-safety vehicle intrusion protected applications |
| OBD | On-Board Diagnostics |
| GPS | Global Positioning System |
| HEAVENS | HEAling Vulnerabilities to ENhance Software Security and Safety |
| ISO | International Standardization Organization |
| OEM | Original Equipment Manufacturer |
| OVERSEE | Open VEhiculaR SEcurE platform |
| SAE | Society of Automotive Engineers |
| SuC | System Under Consideration |
| STRIDE | Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, and Elevation of Privilege |
| TARA | Threat Analysis and Risk Assessment |
| TVRA | Threat, Vulnerability, and Risk Assessment |
| UMTS | Universal Mobile Telecommunications System |
| UNECE | United Nations Economic Commission for Europe |
Appendix A
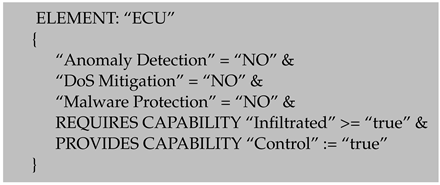
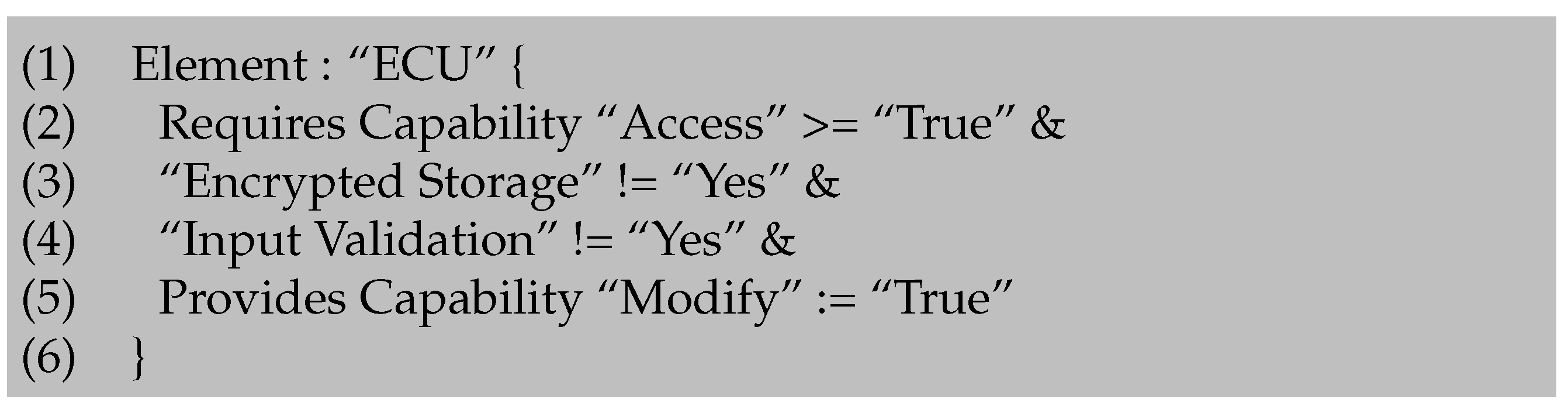
Appendix A.1. Attack Tree Rules





References
- Bradley, T. Cyber Attacks on Cars up 225 Percent: How Hackers Could be Targeting Your Vehicle. Section: Cars. 2022. Available online: https://www.express.co.uk/life-style/cars/1632500/hackers-target-drivers-cyber-attacks-cars (accessed on 15 August 2022).
- Blum, B. Cyberattacks on Cars Increased 225% in Last Three Years. 2022. Available online: https://www.israel21c.org/cyberattacks-on-cars-increased-225-in-last-three-years/ (accessed on 15 August 2022).
- 1 in 3 Automotive Cyber Incidents Result in Car Theft or Break-Ins—Atlas VPN. Available online: https://atlasvpn.com/blog/1-in-3-automotive-cyber-incidents-result-in-car-theft-or-break-ins (accessed on 16 August 2022).
- Schmittner, C.; Schrammel, B.; König, S. Asset Driven ISO/SAE 21434 Compliant Automotive Cybersecurity Analysis with ThreatGet. In Proceedings of the European Conference on Software Process Improvement, Krems, Austria, 1–3 September 2021; Springer: Berlin/Heidelberg, Germany, 2021; pp. 548–563. [Google Scholar]
- Schmittner, C.; Dobaj, J.; Macher, G.; Brenner, E. A preliminary view on automotive cyber security management systems. In Proceedings of the 2020 Design, Automation & Test in Europe Conference & Exhibition (DATE), Grenoble, France, 9–13 March 2020; IEEE: Piscataway, NJ, USA, 2020; pp. 1634–1639. [Google Scholar]
- Schmittner, C.; Tummeltshammer, P.; Hofbauer, D.; Shaaban, A.; Meidlinger, M.; Tauber, M.; Bonitz, A.; Hametner, R.; Brandstetter, M. Threat Modeling in the Railway Domain. In Proceedings of the International Conference on Reliability, Safety, and Security of Railway Systems, Lille, France, 4–6 June 2019; pp. 261–271. [Google Scholar]
- Shevchenko, N. Threat Modeling: 12 Available Methods. 2018. Available online: https://insights.sei.cmu.edu/sei_blog/2018/12/threat-modeling-12-available-methods.html (accessed on 14 December 2022).
- Lautenbach, A.; Islam, M. The HEAling Vulnerabilities to ENhance Software Security and Safety (HEAVENS) Project—Security Models. 2016. Available online: https://autosec.se/wp-content/uploads/2018/03/HEAVENS_D2_v2.0.pdf (accessed on 11 August 2022).
- Shostack, A. Threat Modeling: Designing for Security; Wiley: Indianapolis, IN, USA, 2014; OCLC: 855043351. [Google Scholar]
- Hamad, M. A Multilayer Secure Framework for Vehicular Systems; Technische Universität Braunschweig: Braunschweig, Germany, 2020. [Google Scholar]
- Khan, R.; McLaughlin, K.; Laverty, D.; Sezer, S. STRIDE-based threat modeling for cyber-physical systems. In Proceedings of the 2017 IEEE PES Innovative Smart Grid Technologies Conference Europe (ISGT-Europe), Torino, Italy, 26–29 September 2017; pp. 1–6. [Google Scholar] [CrossRef]
- The Ultimate Beginner’s Guide to Threat Modeling. Available online: https://shostack.org/resources/threat-modeling.html (accessed on 12 August 2022).
- Allen-Addy, C. Threat Modeling Methodology: TRIKE. Available online: https://www.iriusrisk.com/resources-blog/trike-threat-modeling-methodologies (accessed on 14 December 2022).
- Threatmodeler. Threat Modeling Methodologies: What is VAST? 2018. Available online: https://threatmodeler.com/threat-modeling-methodologies-vast/ (accessed on 14 December 2022).
- Smith, C. The Car Hacker’s Handbook: A Guide for the Penetration Tester; No Starch Press: San Francisco, CA, USA, 2016. [Google Scholar]
- Shaaban, A. An Ontology-Based Cybersecurity Framework for the Automotive Domain-Design, Implementation, and Evaluation. Ph.D. Thesis, Faculty of Computer Science, University of Vienna, Vienna, Austria, 2021. Available online: https://utheses.univie.ac.at/detail/59948 (accessed on 17 August 2022).
- Goswami, D.; Schneider, R.; Masrur, A.; Lukasiewycz, M.; Chakraborty, S.; Voit, H.; Annaswamy, A. Challenges in automotive cyber-physical systems design. In Proceedings of the 2012 International Conference on Embedded Computer Systems (SAMOS), Samos, Greece, 16–18 July 2012; IEEE: Piscataway, NJ, USA, 2012; pp. 346–354. [Google Scholar]
- Pauker, F.; Mangler, J.; Rinderle-Ma, S.; Pollak, C. Centurio. work-modular secure manufacturing orchestration. In Proceedings of the 16th International Conference on Business Process Management 2018, Sydney, Australia, 9–14 September 2018. [Google Scholar]
- AVL. Automotive Cybersecurity—A Holistic Approach to the Protection of Vehicles. 2020. Available online: https://www.avl.com/web/guest/services1/-/asset_publisher/gYjUpY19vEA8/content/automotive-cyber-security (accessed on 10 October 2020).
- EVITA. E-Safety Vehicle Intrusion Protected Application—FINAL DRAFT. 2008. Available online: https://trimis.ec.europa.eu/sites/default/files/project/documents/20130702_175923_78998_EVITA_ProjectSummary.pdf (accessed on 15 August 2022).
- OVERSEE. The Application Store for Cars: Secure Download of Your Favorite Apps into Your Car. 2010. Available online: https://www.oversee-project.com/fileadmin/oversee/press_releases/OVERSEE-Pressrelease-1-EN.pdf (accessed on 15 August 2022).
- Olsson, M. HEAling Vulnerabilities to ENhance Software Security and Safety. 2016. Available online: https://www.vinnova.se/globalassets/mikrosajter/ffi/dokument/slutrapporter-ffi/elektronik-mjukvara-och-kommunikation-rapporter/2012-04625eng.pdf (accessed on 15 August 2022).
- J3061_202112; Cybersecurity Guidebook for Cyber-Physical Vehicle Systems. SAE International: Warrendale, PA, USA, 2021.
- ISO/SAE 21434 Road; Vehicles—Cybersecurity Engineering. ISO—International Standardization Organization: Geneva, Switzerland, 2021.
- ETSI. Intelligent Transport Systems (ITS); Security; Threat, Vulnerability and Risk Analysis (TVRA); Technical Report; European Telecommunications Standards Institute (ETSI): Sophia, France, 2010. [Google Scholar]
- UNECE, U.N.E.C.f.E. Draft New UN Regulation on Uniform Provisions Concerning the Approval of Vehicles with Regard to Cyber Security and of Their Cybersecurity Management Systems. 2020. Available online: https://unece.org/DAM/trans/doc/2020/wp29grva/GRVA-05-05r1e.pdf (accessed on 25 February 2020).
- Microsoft. Microsoft Threat Modeling Tool Getting Started Guide, Microsoft Trustworthy Computing. 2016. Available online: https://download.microsoft.com/download/4/F/D/4FDDEA98-4ABD-47A7-AA0E-815CE8660A76/Threat%20Modeling%20Tool%202016%20Getting%20Started%20Guide.docx (accessed on 20 December 2022).
- Microsoft. Microsoft Threat Modeling Tool User Guide, Microsoft Trustworthy Computing. 2016. Available online: https://download.microsoft.com/download/4/F/D/4FDDEA98-4ABD-47A7-AA0E-815CE8660A76/Threat%20Modeling%20Tool%202016%20User%20Guide.docx (accessed on 20 December 2022).
- Eng, D. Integrated Threat Modelling. Master Dissertation, Universitetet i Oslo, Oslo, Norway, 2017. [Google Scholar]
- Wolf, M. Combining Safety and Security Threat Modeling to Improve Automotive Penetration Testing. Master’s Thesis, Universität Ulm, Ulm, Germany, 2019. [Google Scholar]
- OWASP Threat Dragon | OWASP Foundation. Available online: https://owasp.org/www-project-threat-dragon/ (accessed on 18 July 2022).
- Williams, I.; Yuan, X. Evaluating the effectiveness of Microsoft threat modeling tool. In Proceedings of the 2015 Information Security Curriculum Development Conference on—InfoSec ’15, Kennesaw, Georgia, 15–17 November 2015; ACM Press: Kennesaw, Georgia, 2015; pp. 1–6. [Google Scholar]
- Christl, K.; Tarrach, T. The analysis approach of ThreatGet. arXiv 2021, arXiv:2107.09986. [Google Scholar] [CrossRef]
- Jang-Jaccard, J.; Nepal, S. A survey of emerging threats in cybersecurity. J. Comput. Syst. Sci. 2014, 80, 973–993. [Google Scholar] [CrossRef]
- Navarro, J.; Deruyver, A.; Parrend, P. A systematic survey on multi-step attack detection. Comput. Secur. 2018, 76, 214–249. [Google Scholar] [CrossRef]
- Paul, S. Towards Automating the Construction & Maintenance of Attack Trees: A Feasibility Study. Electron. Proc. Theor. Comput. Sci. 2014, 148, 31–46. [Google Scholar]
- Lallie, H.S.; Debattista, K.; Bal, J. A review of attack graph and attack tree visual syntax in cyber security. Comput. Sci. Rev. 2020, 35, 100219. [Google Scholar] [CrossRef]
- Schneier, B. Academic: Attack Trees—Schneier on Security. 1999. Available online: https://www.schneier.com/academic/archives/1999/12/attack_trees.html (accessed on 20 December 2022).
- Shanker, S. Enhancing Automotive Embedded Systems with FPGAs. Ph.D. Thesis, Nanyang Technological University, Singapore, 2016. [Google Scholar] [CrossRef]









| Method | Short Description | Discussion |
|---|---|---|
| PASTA |
| PASTA requires a strict and weighty process while STRIDE is mainly used for the identification of threats and countermeasures as part of a process. The approach that will be presented remains flexible and can be used in all development phases, even when new objectives or requirements are introduced. |
| LINDDUN |
| LINDDUN is targeted at privacy. For our use case, a more generic approach also including operational, safety, and financial aspects is required. |
| OCTAVE |
| Technological risks represent the main focus of our methodology. However, organizational risks may be deduced. |
| TRIKE |
| This method focuses mainly on IT and auditing and is, therefore, not suitable for our application field. |
| VAST |
| In contrast to a generic approach, VAST is targeted at processes on the organizational level and large-scale IT systems. |
| Persona non Grata |
| Persona non Grata is a manual method and does not include potential automated propagation of attacks throughout the system. |
| CVSS |
| Represents a method for rating potential risks but not for the identification of threats or mitigation measures. However, it incorporates a detailed scheme for assigning a score to certain threats and will, therefore, be considered for integration with our method in the future. |
| DREAD |
| Like CVSS, DREAD represents a scoring system to classify the criticality of threats. However, when it comes to impact and likelihood it lacks a standardized definition of factors. Therefore, it is rarely used. |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Chlup, S.; Christl, K.; Schmittner, C.; Shaaban, A.M.; Schauer, S.; Latzenhofer, M. THREATGET: Towards Automated Attack Tree Analysis for Automotive Cybersecurity. Information 2023, 14, 14. https://doi.org/10.3390/info14010014
Chlup S, Christl K, Schmittner C, Shaaban AM, Schauer S, Latzenhofer M. THREATGET: Towards Automated Attack Tree Analysis for Automotive Cybersecurity. Information. 2023; 14(1):14. https://doi.org/10.3390/info14010014
Chicago/Turabian StyleChlup, Sebastian, Korbinian Christl, Christoph Schmittner, Abdelkader Magdy Shaaban, Stefan Schauer, and Martin Latzenhofer. 2023. "THREATGET: Towards Automated Attack Tree Analysis for Automotive Cybersecurity" Information 14, no. 1: 14. https://doi.org/10.3390/info14010014
APA StyleChlup, S., Christl, K., Schmittner, C., Shaaban, A. M., Schauer, S., & Latzenhofer, M. (2023). THREATGET: Towards Automated Attack Tree Analysis for Automotive Cybersecurity. Information, 14(1), 14. https://doi.org/10.3390/info14010014






